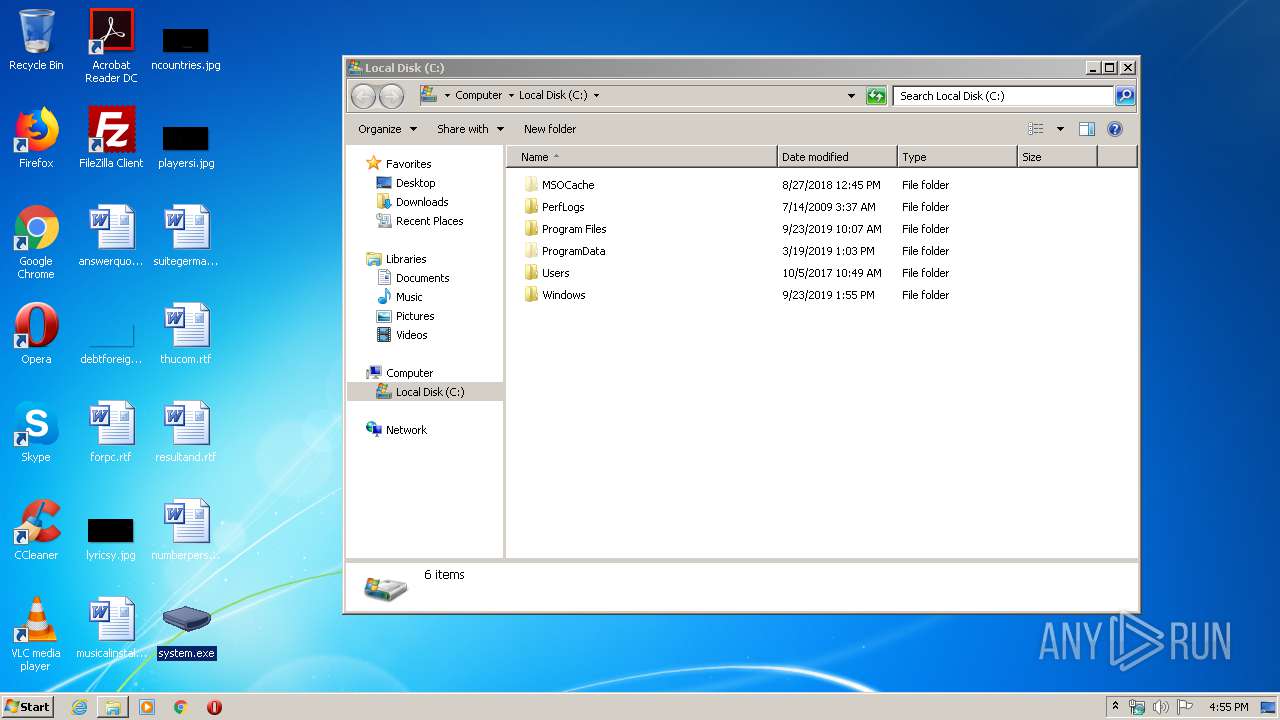
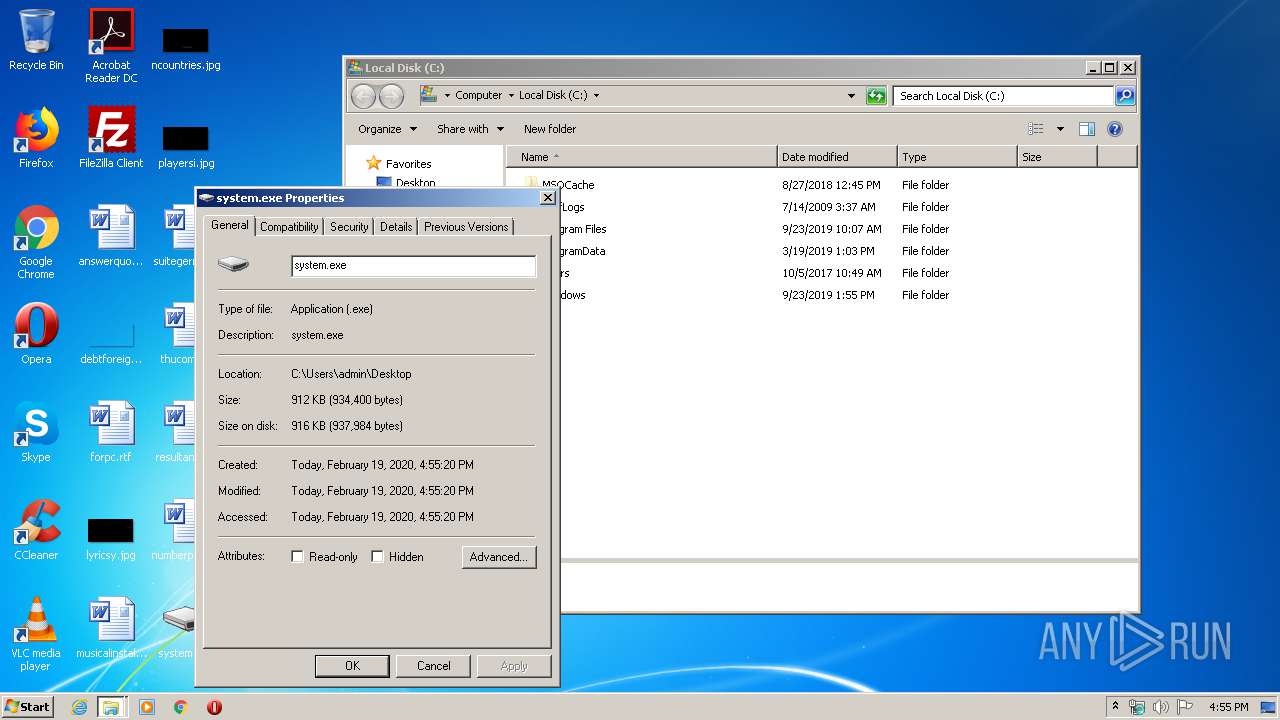
| File name: | system.exe |
| Full analysis: | https://app.any.run/tasks/a5754aff-7024-465d-8621-240674cbfe69 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2020, 16:55:02 |
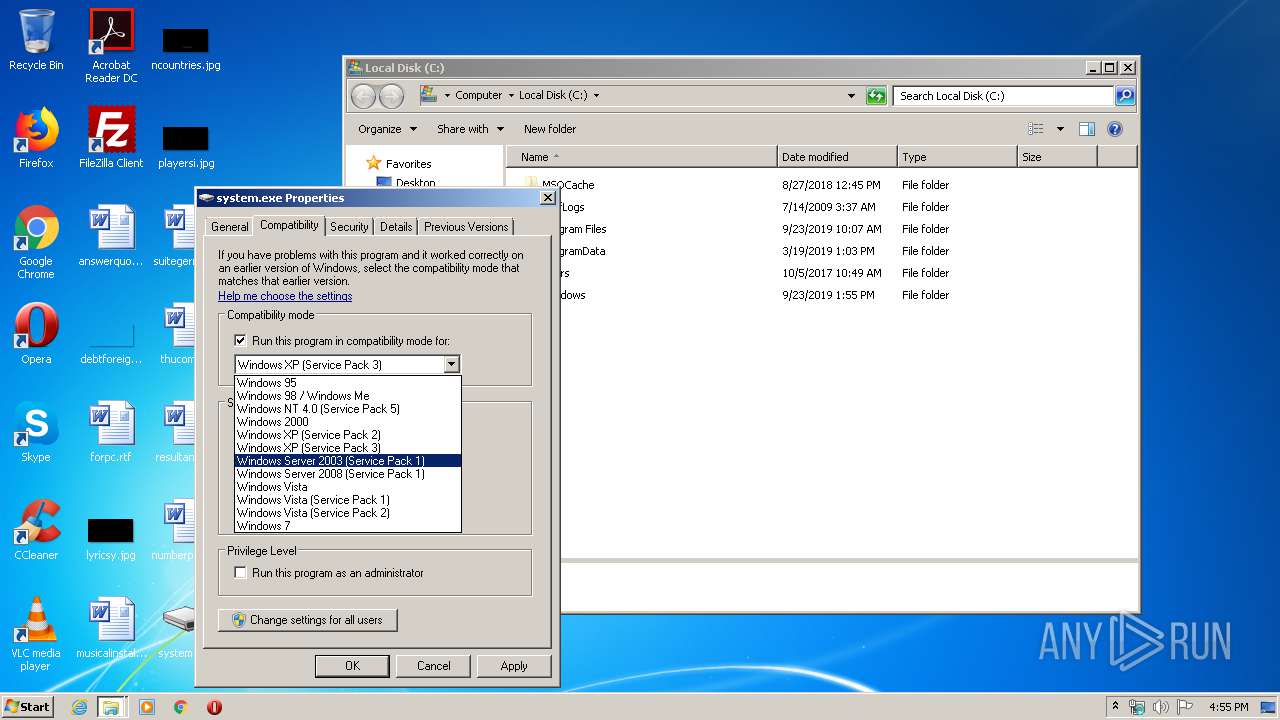
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 54180A40AE9CC2732429EC6CC16E066A |
| SHA1: | 31AE5B8EF41B2913BD119FC15C13115C5EEE86E0 |
| SHA256: | BB432A2E43003D0605A8989C589B96055331A38FE78320E5747DC4634182A2CB |
| SSDEEP: | 24576:Ts76cHLsH4rAKKBvX3otaNHM5Sc+wEPwFG:THcQYJ2vLaa4 |
MALICIOUS
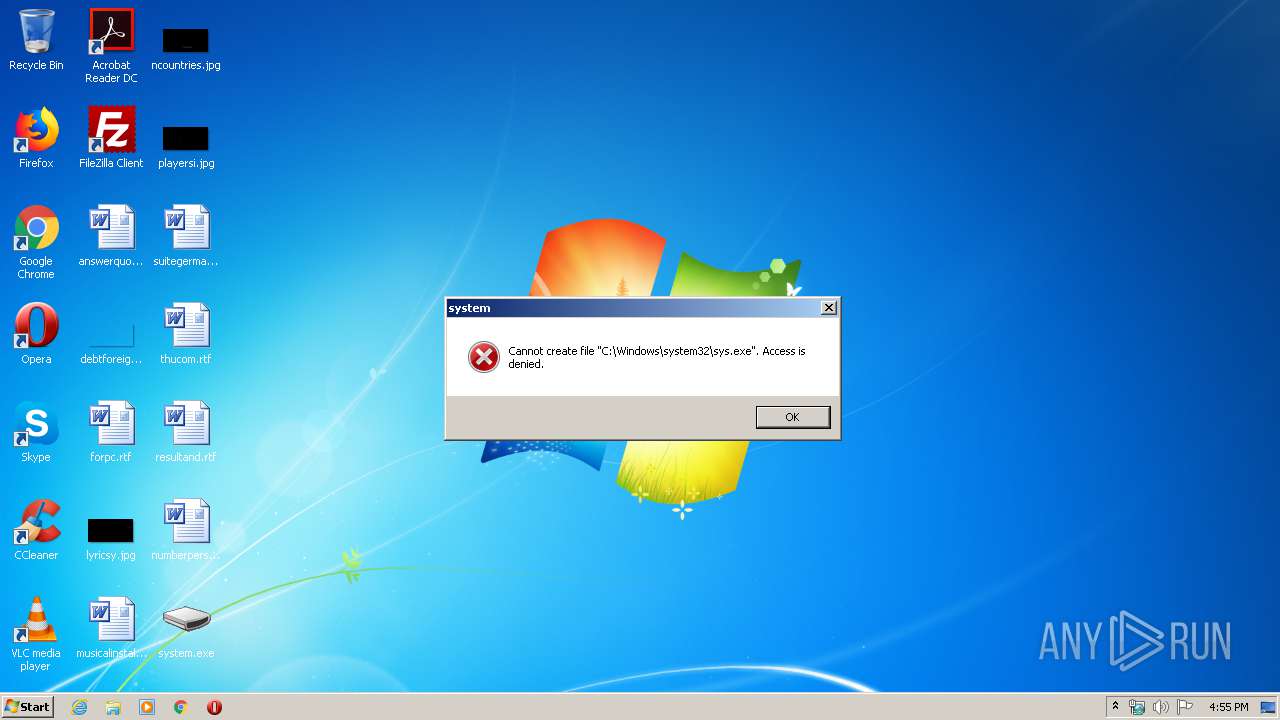
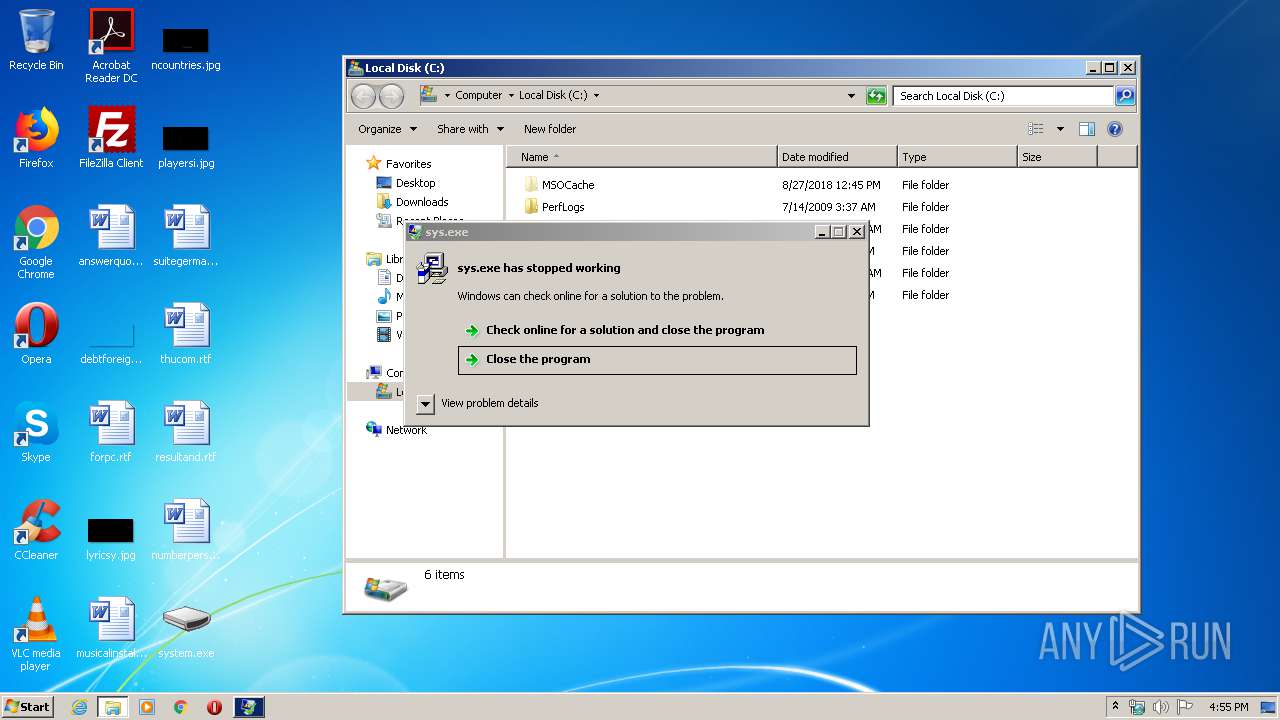
Application was dropped or rewritten from another process
- sys.exe (PID: 3452)
Changes the login/logoff helper path in the registry
- sysos.exe (PID: 2604)
SUSPICIOUS
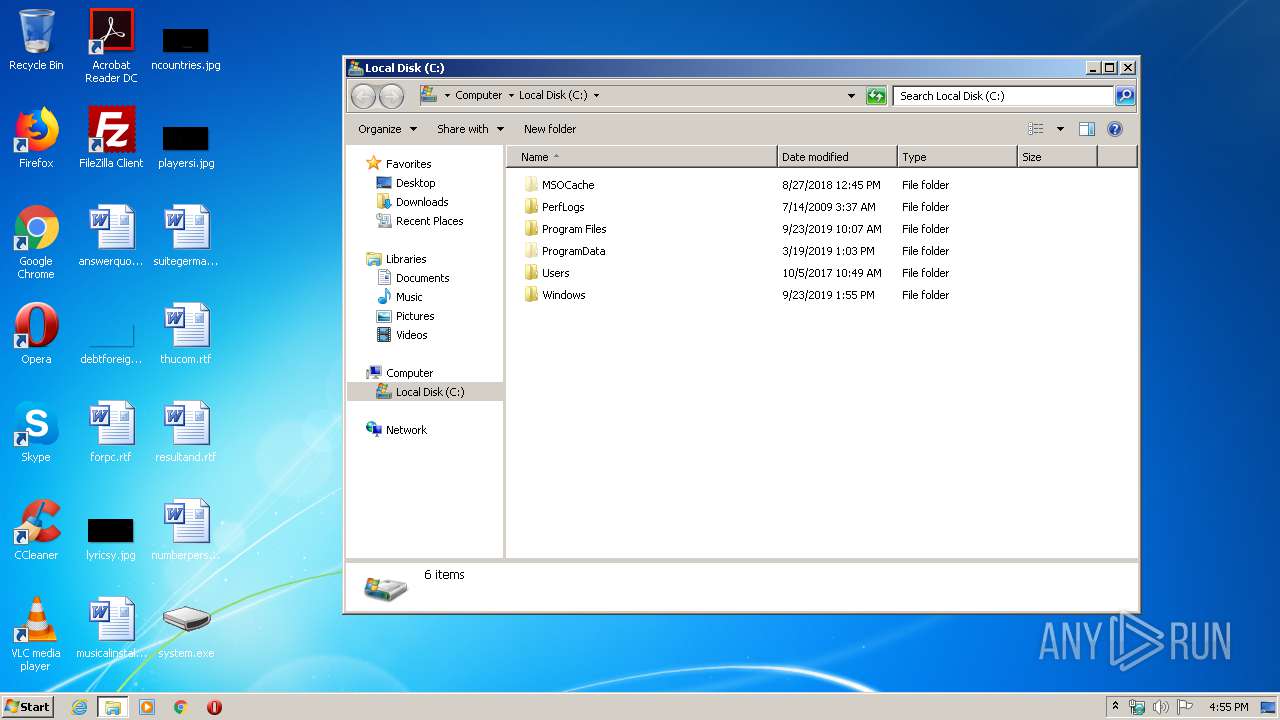
Creates files in the Windows directory
- system.exe (PID: 3740)
Executable content was dropped or overwritten
- system.exe (PID: 3740)
INFO
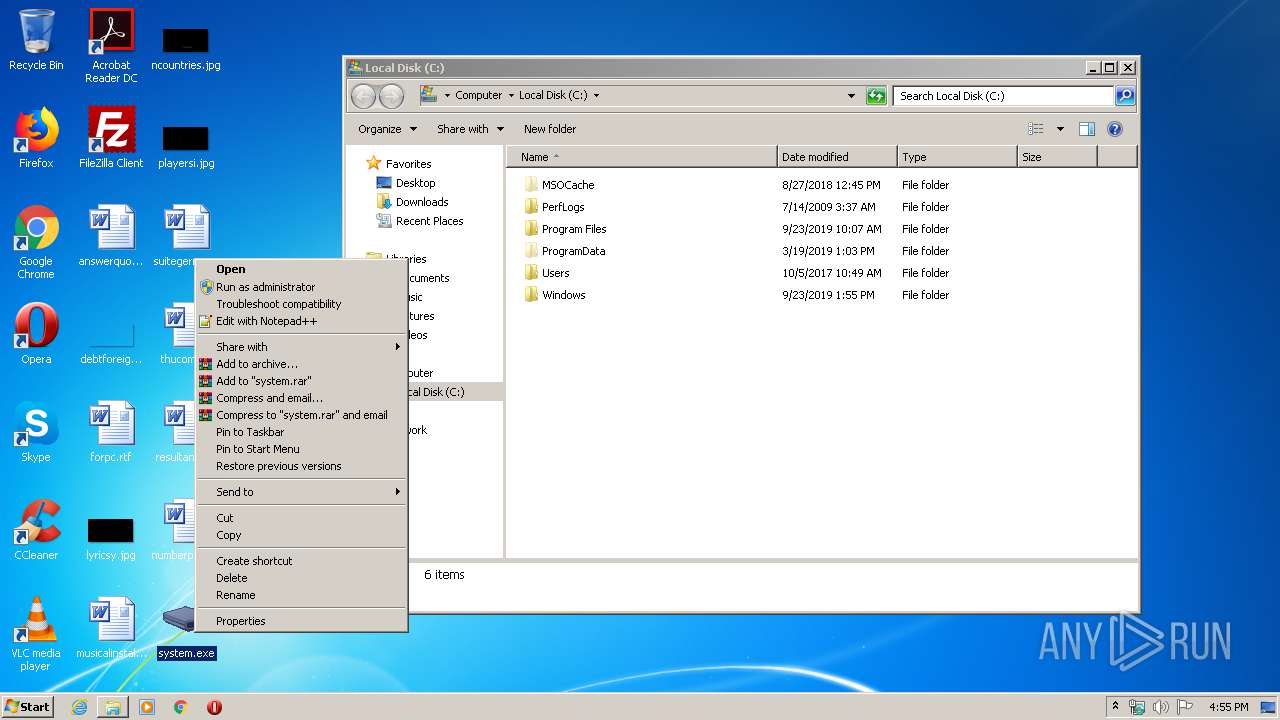
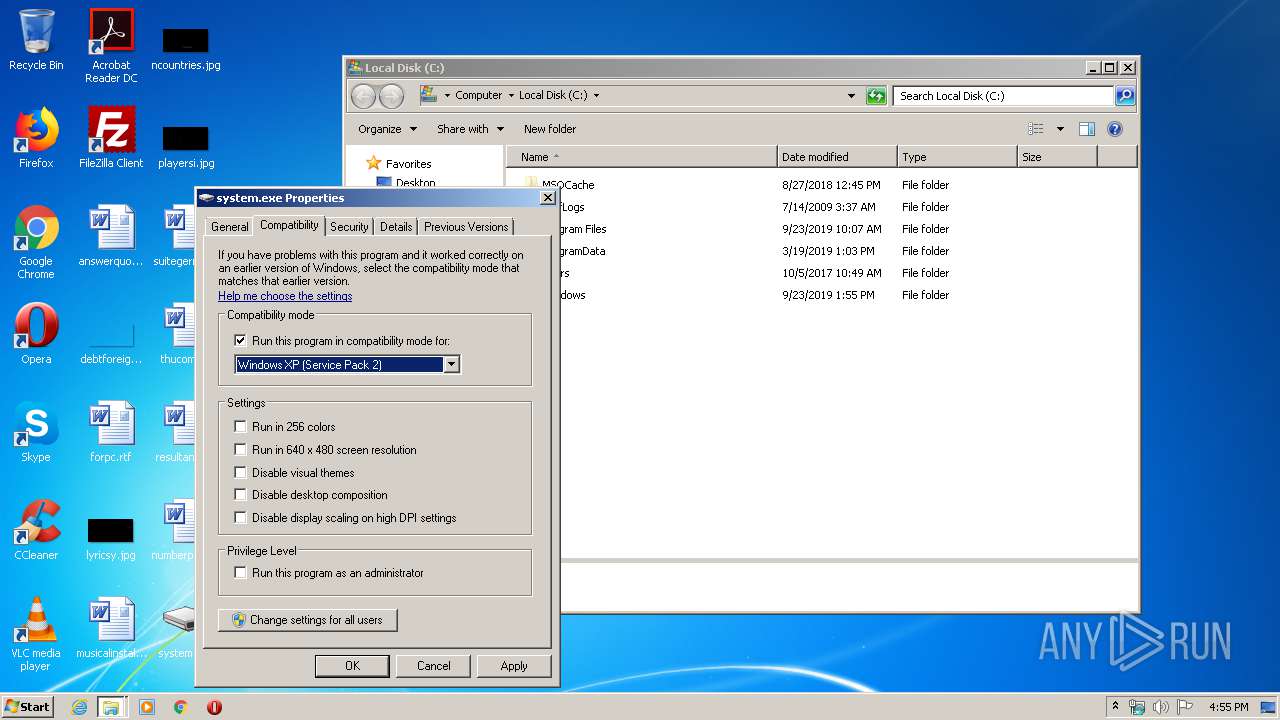
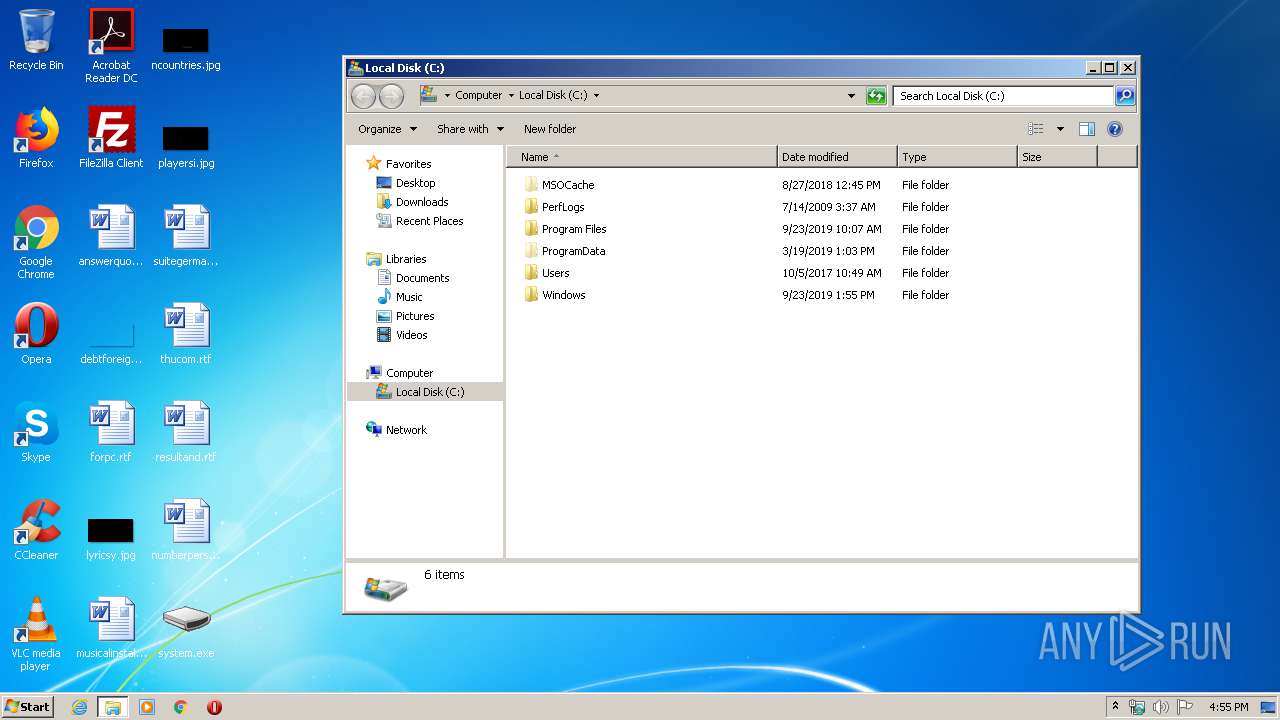
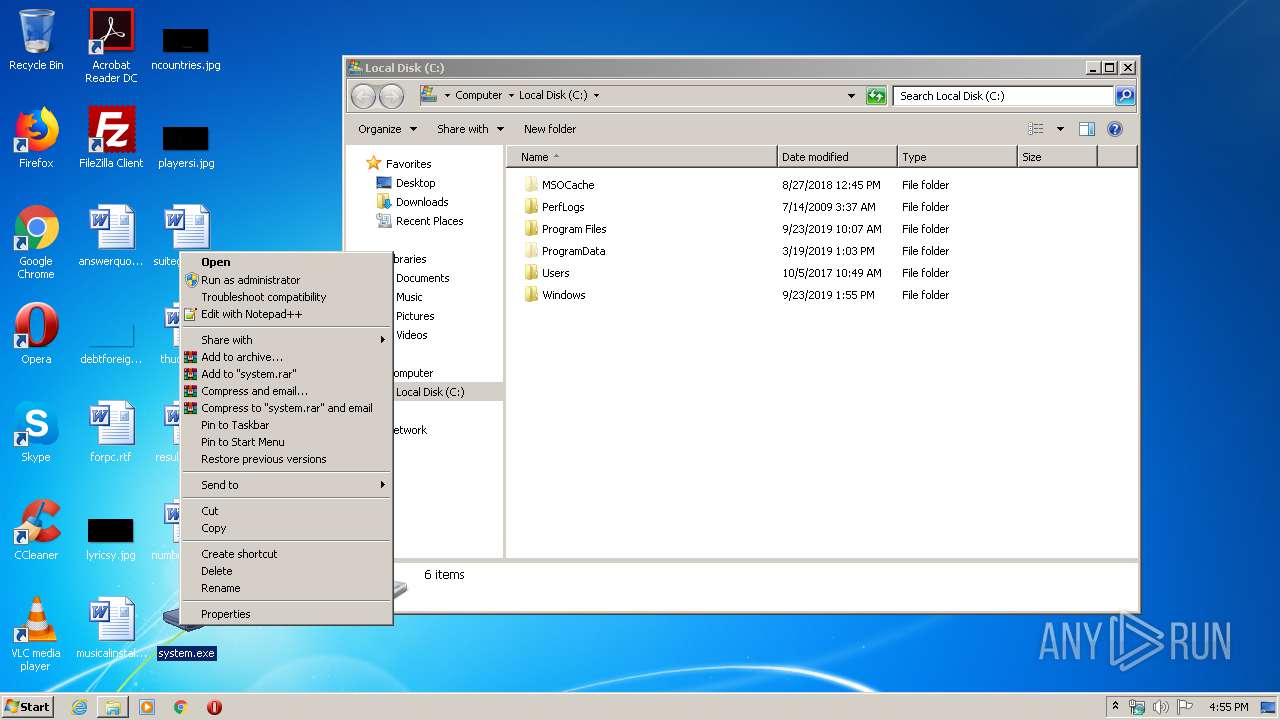
Manual execution by user
- wermgr.exe (PID: 3508)
- system.exe (PID: 3740)
- taskmgr.exe (PID: 3980)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (68.8) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 6 (27.2) |
| .exe | | | Win32 Executable Delphi generic (1.4) |
| .scr | | | Windows screen saver (1.3) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 320000 |
| InitializedDataSize: | 613376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4eda8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0004E02C | 0x0004E200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.52917 |
DATA | 0x00050000 | 0x000011D4 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15605 |
BSS | 0x00052000 | 0x00000E09 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00053000 | 0x00002184 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.9185 |
.tls | 0x00056000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00057000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.180244 |
.reloc | 0x00058000 | 0x000057DC | 0x00005800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.68614 |
.rsrc | 0x0005E000 | 0x0008CE00 | 0x0008CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.85414 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.08375 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
2 | 5.39947 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.8665 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4081 | 3.2916 | 400 | UNKNOWN | UNKNOWN | RT_STRING |
4082 | 3.26036 | 492 | UNKNOWN | UNKNOWN | RT_STRING |
4083 | 3.10183 | 236 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
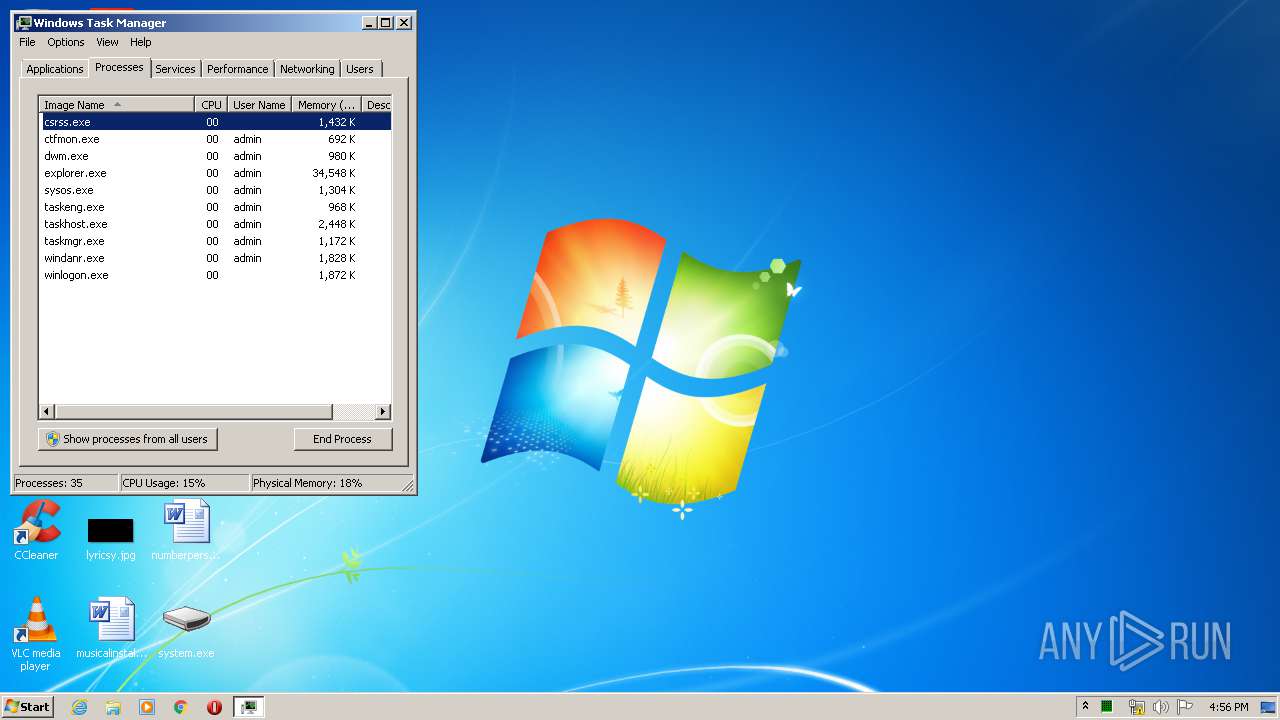
Total processes
45
Monitored processes
6
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2604 | C:\Windows\system32\sysos.exe | C:\Windows\system32\sysos.exe | system.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3368 | "C:\Users\admin\Desktop\system.exe" | C:\Users\admin\Desktop\system.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3452 | C:\Windows\system32\sys.exe | C:\Windows\system32\sys.exe | system.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225477 Modules
| |||||||||||||||
| 3508 | "C:\Windows\system32\wermgr.exe" "-outproc" "372" "4664" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\Desktop\system.exe" | C:\Users\admin\Desktop\system.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3980 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
148
Read events
147
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2604) sysos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | shell |
Value: Explorer.exe C:\Windows\system32\sysos.exe | |||
Executable files
2
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3508 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_system.exe_5befc971b4bead33e4457e5c6c8eefe9215242_cab_0d12a253\appcompat.txt | xml | |
MD5:198A24247B0D97A2112F566AE9D7AE55 | SHA256:C61CD3FDCD665C0E711D9668284470D1C62670F5BE7CF87C36A09C70F299A883 | |||
| 3740 | system.exe | C:\Windows\system32\sys.exe | executable | |
MD5:DDF921907EE5D382A76E4D7324C01AAC | SHA256:F0389461273FC18F679ECC0C49836492B132BA3972D7F60795AE392ED6F78116 | |||
| 3740 | system.exe | C:\Windows\system32\sysos.exe | executable | |
MD5:54180A40AE9CC2732429EC6CC16E066A | SHA256:BB432A2E43003D0605A8989C589B96055331A38FE78320E5747DC4634182A2CB | |||
| 3508 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_system.exe_5befc971b4bead33e4457e5c6c8eefe9215242_cab_0d12a253\Report.wer | binary | |
MD5:D3FED099AB87A4C271CC7AC3E3234106 | SHA256:2413FACC38FD1D0360CEAB8EC7C629439B39492761BDA1690B33A3E428F87581 | |||
| 3508 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_system.exe_5befc971b4bead33e4457e5c6c8eefe9215242_cab_0d12a253\TabA1E6.tmp | text | |
MD5:77EC408F49FCBFEB485B5A343A19C211 | SHA256:B5049E5B6037E3206B5CE7B77F098CFE8F8EEB7442E58EC6C14C9E312151A319 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
system.exe | FTH: (3740): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|