| File name: | RMM_Client.exe |
| Full analysis: | https://app.any.run/tasks/f397326c-f7f8-43c4-9405-c2886ea500b0 |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2020, 06:13:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FF4A6E034E978934D2C8CF7746B973C8 |
| SHA1: | C7F27DF1F671118B5C779831AC80188D833F00FD |
| SHA256: | BB3B8622780D60E6C3C53DA2C9E9B74FE34146188B2418EB86A7C541E283BD83 |
| SSDEEP: | 393216:z2uuDAuFo0oj+HiuyBk9u8YWZose825kzxYO5u:C2uFTooiuyBwu8he825kzxYO5u |
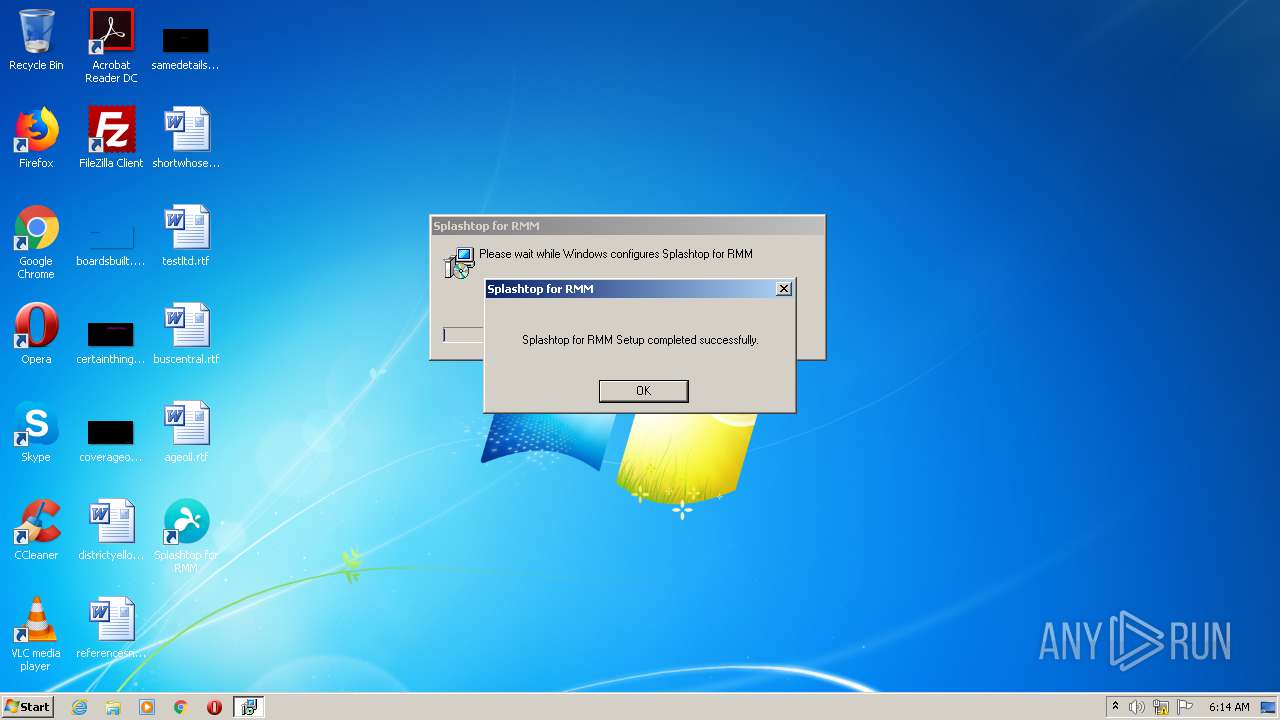
MALICIOUS
Application was dropped or rewritten from another process
- PreVerCheck.exe (PID: 3768)
- ClientUtil.exe (PID: 3712)
- Splashtop_Software_Updater.exe (PID: 3832)
- ClientUtil.exe (PID: 3248)
- SSU_Clean.exe (PID: 3804)
- SSUService.exe (PID: 2464)
- PreVerCheck.exe (PID: 1772)
- clientoobe.exe (PID: 628)
- strwinclt.exe (PID: 2360)
- strwinchat.exe (PID: 3528)
- SRUpdate.exe (PID: 3680)
- SRUpdate.exe (PID: 3084)
Changes settings of System certificates
- msiexec.exe (PID: 3536)
Drops executable file immediately after starts
- RMM_Client.exe (PID: 312)
- MsiExec.exe (PID: 3304)
- Splashtop_Software_Updater.exe (PID: 3832)
Loads dropped or rewritten executable
- Splashtop_Software_Updater.exe (PID: 3832)
- strwinclt.exe (PID: 2360)
- SRUpdate.exe (PID: 3084)
SUSPICIOUS
Executable content was dropped or overwritten
- RMM_Client.exe (PID: 312)
- msiexec.exe (PID: 3536)
- MsiExec.exe (PID: 2116)
- MsiExec.exe (PID: 3304)
- Splashtop_Software_Updater.exe (PID: 3832)
Creates a directory in Program Files
- msiexec.exe (PID: 3536)
- Splashtop_Software_Updater.exe (PID: 3832)
Executed as Windows Service
- vssvc.exe (PID: 964)
- SSUService.exe (PID: 2464)
Starts CMD.EXE for commands execution
- RMM_Client.exe (PID: 312)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3536)
Drops a file that was compiled in debug mode
- RMM_Client.exe (PID: 312)
- MsiExec.exe (PID: 2116)
- msiexec.exe (PID: 3536)
- MsiExec.exe (PID: 3304)
- Splashtop_Software_Updater.exe (PID: 3832)
Drops a file with too old compile date
- MsiExec.exe (PID: 2116)
- Splashtop_Software_Updater.exe (PID: 3832)
Modifies the open verb of a shell class
- MsiExec.exe (PID: 3304)
Creates a software uninstall entry
- Splashtop_Software_Updater.exe (PID: 3832)
Creates files in the program directory
- Splashtop_Software_Updater.exe (PID: 3832)
- SSUService.exe (PID: 2464)
- strwinclt.exe (PID: 2360)
- SRUpdate.exe (PID: 3084)
Removes files from Windows directory
- SSUService.exe (PID: 2464)
Creates or modifies windows services
- Splashtop_Software_Updater.exe (PID: 3832)
Creates files in the Windows directory
- SSUService.exe (PID: 2464)
Reads internet explorer settings
- SRUpdate.exe (PID: 3084)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 964)
Application launched itself
- msiexec.exe (PID: 3536)
Searches for installed software
- msiexec.exe (PID: 3536)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2116)
- MsiExec.exe (PID: 3304)
Creates files in the program directory
- msiexec.exe (PID: 3536)
- MsiExec.exe (PID: 3304)
Creates a software uninstall entry
- msiexec.exe (PID: 3536)
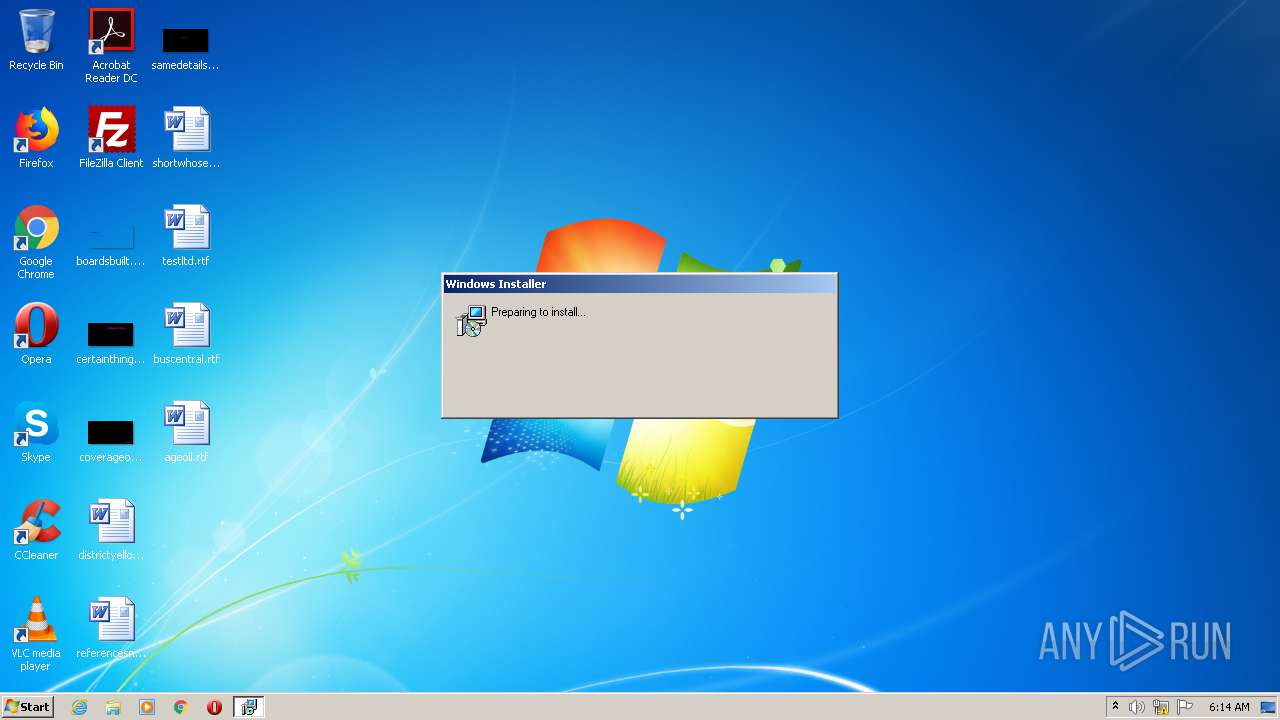
Manual execution by user
- clientoobe.exe (PID: 628)
Reads settings of System Certificates
- strwinclt.exe (PID: 2360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (64.5) |
|---|---|---|
| .ax | | | DirectShow filter (15.3) |
| .exe | | | Win32 EXE PECompact compressed (v2.x) (4.5) |
| .exe | | | Win32 EXE PECompact compressed (generic) (3.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:21 13:05:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 165376 |
| InitializedDataSize: | 237568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11009 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
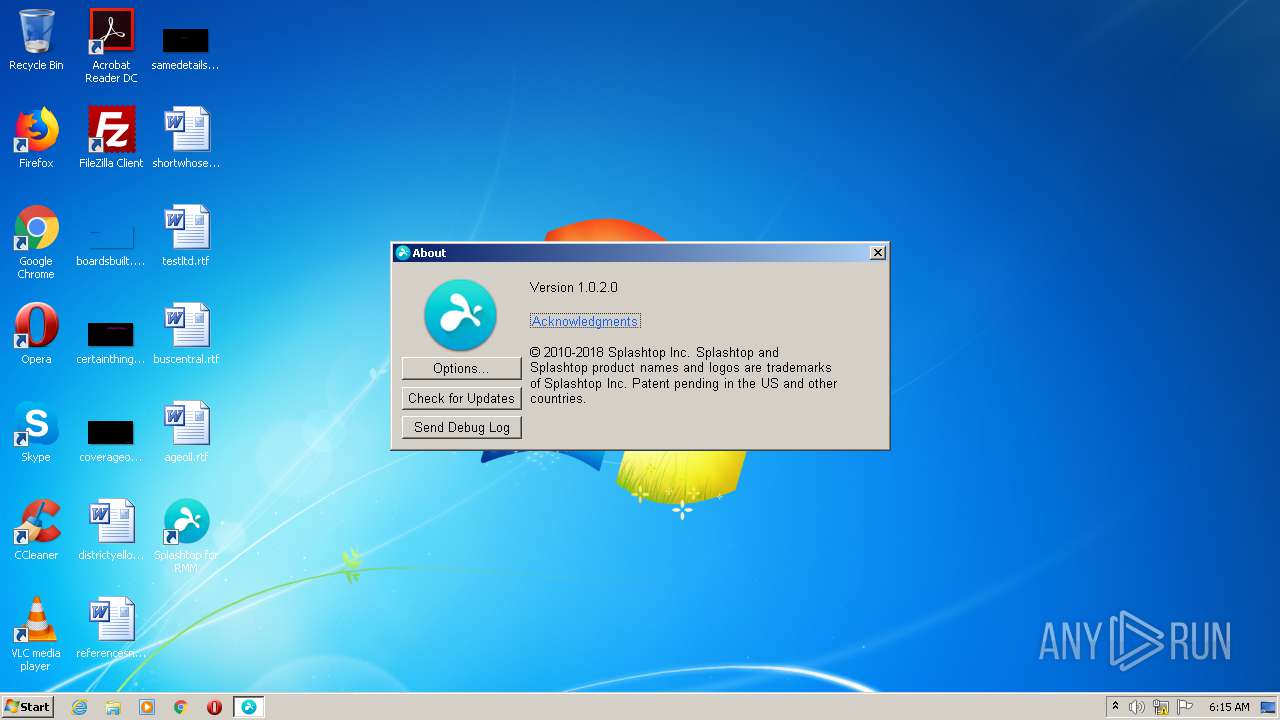
| FileVersionNumber: | 3.2.8.9465 |
| ProductVersionNumber: | 1.0.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Splashtop Inc. |
| FileDescription: | Splashtop for RMM |
| FileVersion: | 3.02.8.9465 |
| LegalCopyright: | Copyright © Splashtop Inc. All Rights Reserved. |
| ProductName: | Splashtop for RMM |
| ProductVersion: | 1.0.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jun-2018 11:05:44 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Splashtop Inc. |
| FileDescription: | Splashtop for RMM |
| FileVersion: | 3.02.8.9465 |
| LegalCopyright: | Copyright © Splashtop Inc. All Rights Reserved. |
| ProductName: | Splashtop for RMM |
| ProductVersion: | 1.0.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 21-Jun-2018 11:05:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000284A0 | 0x00028600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59432 |
.rdata | 0x0002A000 | 0x0000A5B0 | 0x0000A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78831 |
.data | 0x00035000 | 0x00006318 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.90659 |
.rsrc | 0x0003C000 | 0x0002D59C | 0x0002D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16828 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.77792 | 357 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.00415 | 67624 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
3 | 4.14745 | 38056 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
4 | 4.26677 | 16936 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
5 | 4.42207 | 9640 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
6 | 4.6339 | 4264 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
7 | 5.03087 | 1128 | Latin 1 / Western European | Chinese - Taiwan | RT_ICON |
8 | 3.02695 | 308 | Latin 1 / Western European | Chinese - Taiwan | RT_CURSOR |
9 | 2.93229 | 352 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.34038 | 308 | Latin 1 / Western European | Chinese - Taiwan | RT_CURSOR |
Imports
ADVAPI32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
Total processes
67
Monitored processes
21
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Users\admin\AppData\Local\Temp\RMM_Client.exe" | C:\Users\admin\AppData\Local\Temp\RMM_Client.exe | explorer.exe | ||||||||||||
User: admin Company: Splashtop Inc. Integrity Level: HIGH Description: Splashtop for RMM Exit code: 0 Version: 3.02.8.9465 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Splashtop\Splashtop Remote\Client for RMM\clientoobe.exe" | C:\Program Files\Splashtop\Splashtop Remote\Client for RMM\clientoobe.exe | — | explorer.exe | |||||||||||
User: admin Company: Splashtop Inc. Integrity Level: MEDIUM Description: Splashtop for RMM OOBE Exit code: 0 Version: 3.02.8.9465 Modules
| |||||||||||||||
| 964 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | PreVerCheck.exe -a | C:\Users\admin\AppData\Local\Temp\unpack\PreVerCheck.exe | cmd.exe | ||||||||||||
User: admin Company: Splashtop Inc. Integrity Level: MEDIUM Description: Splashtop for RMM Exit code: 0 Version: 3.02.8.9465 Modules
| |||||||||||||||
| 2116 | C:\Windows\system32\MsiExec.exe -Embedding 5EDE56D0DFA80FAD51A7BCF3B606C7C4 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | strwinclt.exe -f | C:\Program Files\Splashtop\Splashtop Remote\Client for RMM\strwinclt.exe | clientoobe.exe | ||||||||||||
User: admin Company: Splashtop Inc. Integrity Level: MEDIUM Description: Splashtop for RMM Exit code: 0 Version: 3.02.8.9465 Modules
| |||||||||||||||
| 2416 | msiexec /norestart /i "setup.msi" /qb!+ /l*v "C:\Users\admin\AppData\Local\Temp\PreVerC.log.txt" | C:\Windows\system32\msiexec.exe | — | PreVerCheck.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Splashtop\Splashtop Software Updater\SSUService.exe" | C:\Program Files\Splashtop\Splashtop Software Updater\SSUService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Splashtop Inc. Integrity Level: SYSTEM Description: Splashtop Software Updater Service Exit code: 0 Version: 1.5.5.7 Modules
| |||||||||||||||
| 3008 | "C:\Users\admin\AppData\Local\Temp\RMM_Client.exe" | C:\Users\admin\AppData\Local\Temp\RMM_Client.exe | — | explorer.exe | |||||||||||
User: admin Company: Splashtop Inc. Integrity Level: MEDIUM Description: Splashtop for RMM Exit code: 3221226540 Version: 3.02.8.9465 Modules
| |||||||||||||||
| 3060 | "C:\Windows\System32\cmd.exe" /c run.bat | C:\Windows\System32\cmd.exe | — | RMM_Client.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 428
Read events
1 023
Write events
386
Delete events
19
Modification events
| (PID) Process: | (312) RMM_Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (312) RMM_Client.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3536) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000008CCC243260CCD601D00D0000680A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3536) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000E62E273260CCD601D00D0000680A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3536) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 43 | |||
| (PID) Process: | (3536) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000DA3E783260CCD601D00D0000680A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3536) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000034A17A3260CCD601D00D0000340A0000E8030000010000000000000000000000DE6F9772943FCD40802B9E8FA41DAF230000000000000000 | |||
| (PID) Process: | (964) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005E16903260CCD601C4030000A0080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (964) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005E16903260CCD601C4030000B0080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (964) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005E16903260CCD601C4030000E40C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
37
Suspicious files
13
Text files
72
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 312 | RMM_Client.exe | C:\Users\admin\AppData\Local\Temp\unpack\setup.msi | — | |
MD5:— | SHA256:— | |||
| 3536 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3536 | msiexec.exe | C:\Windows\Installer\15f95d.msi | — | |
MD5:— | SHA256:— | |||
| 3536 | msiexec.exe | C:\Windows\Installer\MSIFFD7.tmp | — | |
MD5:— | SHA256:— | |||
| 2116 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{BBADEBE5-DCF9-41A6-B428-5A87CD1A8A37}\_isres_0x0409.dll | — | |
MD5:— | SHA256:— | |||
| 2116 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{BBADEBE5-DCF9-41A6-B428-5A87CD1A8A37}\String1033.txt | — | |
MD5:— | SHA256:— | |||
| 964 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2116 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{6E58AD63-73EB-465D-A8E0-682E953D1618}\IsConfig.ini | — | |
MD5:— | SHA256:— | |||
| 312 | RMM_Client.exe | C:\Users\admin\AppData\Local\Temp\unpack\autolaunch.bat | text | |
MD5:— | SHA256:— | |||
| 2116 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{6E58AD63-73EB-465D-A8E0-682E953D1618}\ISRT.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
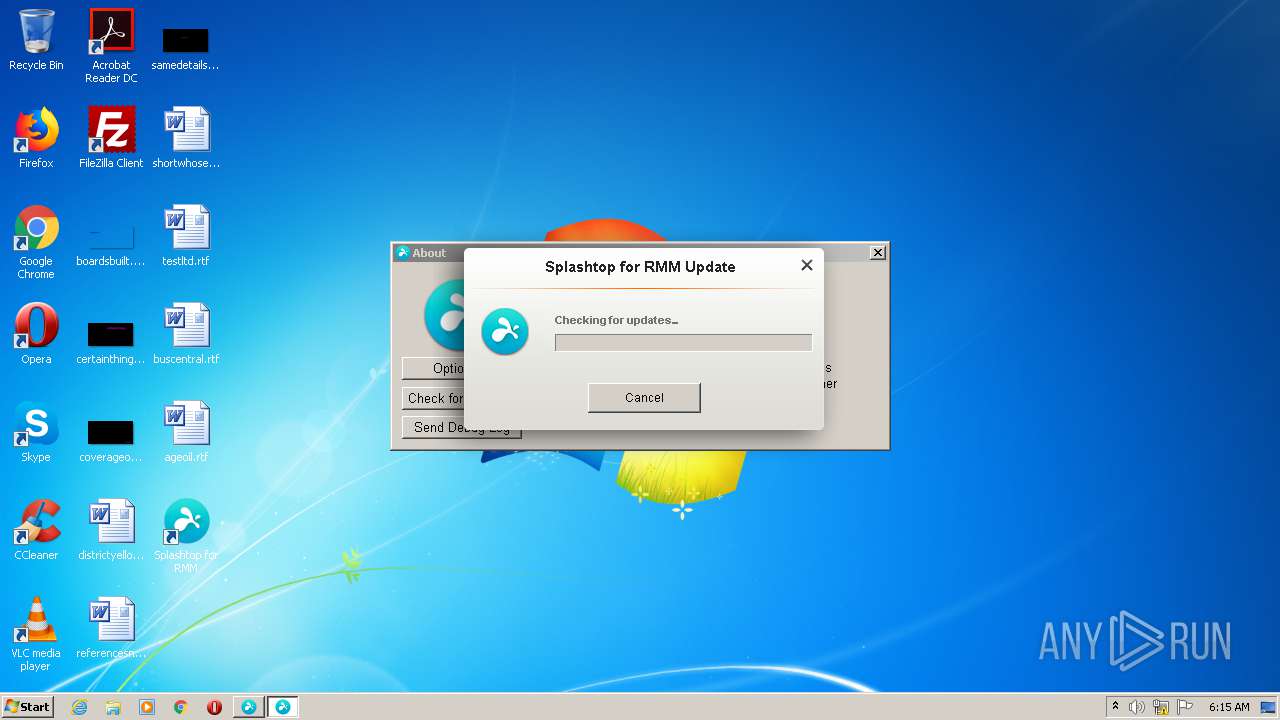
HTTP(S) requests
7
TCP/UDP connections
9
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2360 | strwinclt.exe | GET | 403 | 65.9.68.112:80 | http://st2-v3-dc.splashtop.com/api/fulong | US | xml | 243 b | whitelisted |
2464 | SSUService.exe | POST | — | 107.22.247.100:80 | http://ds1.devicevm.com/ | US | — | — | suspicious |
2360 | strwinclt.exe | GET | 403 | 65.9.68.112:80 | http://st2-v3-dc.splashtop.com/api/fulong | US | xml | 243 b | whitelisted |
2464 | SSUService.exe | GET | 200 | 107.20.0.96:80 | http://sn.splashtop.com/file_system/apt_repository/dists/RMRD00/released/binary-i386/Packages.gz | US | compressed | 1.58 Kb | unknown |
2464 | SSUService.exe | GET | 200 | 65.9.68.70:80 | http://sdrs.splashtop.com/RMRD00/updatenotes/en-US/RMRD00.xml | US | xml | 684 b | suspicious |
3084 | SRUpdate.exe | GET | 200 | 65.9.68.70:80 | http://sdrs.splashtop.com/RMRD00/updatenotes/en-US/RMRD00.xml | US | xml | 684 b | suspicious |
2464 | SSUService.exe | GET | 200 | 107.20.0.96:80 | http://sn.splashtop.com/file_system/apt_repository/dists/ProtoSSU01/released/binary-i386/Packages.gz | US | compressed | 830 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2464 | SSUService.exe | 107.20.0.96:80 | sn.splashtop.com | Amazon.com, Inc. | US | unknown |
2464 | SSUService.exe | 107.22.247.100:80 | ds1.devicevm.com | Amazon.com, Inc. | US | suspicious |
2360 | strwinclt.exe | 13.56.106.108:443 | st-v3-rmm-src-win-1020.api.splashtop.com | Amazon.com, Inc. | US | unknown |
2360 | strwinclt.exe | 65.9.68.112:80 | st2-v3-dc.splashtop.com | AT&T Services, Inc. | US | malicious |
2464 | SSUService.exe | 65.9.68.70:80 | sdrs.splashtop.com | AT&T Services, Inc. | US | malicious |
3084 | SRUpdate.exe | 65.9.68.70:80 | sdrs.splashtop.com | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sn.splashtop.com |
| unknown |
ds1.devicevm.com |
| suspicious |
st-v3-rmm-src-win-1020.api.splashtop.com |
| unknown |
st2-v3-dc.splashtop.com |
| whitelisted |
sdrs.splashtop.com |
| suspicious |
Threats
Process | Message |
|---|---|
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUtility::OSInfo] OS 6.1(7601) Service Pack 1 x64:0 Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::FindHeader] Name:C:\Users\admin\AppData\Local\Temp\RMM_Client.exe Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::FindHeader] Sign Size:6096 Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::FindHeader] Header offset:403968 Err:183 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] FreeSpace:238189334528 FileSize:13533184 Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] (1/5)UnPack file name:C:\Users\admin\AppData\Local\Temp\unpack\setup.msi (13533184) Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] UnPack count:1 len:13533184 File:(null) Err:0 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] FreeSpace:238175801344 FileSize:15 Err:183 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] (2/5)UnPack file name:C:\Users\admin\AppData\Local\Temp\unpack\run.bat (15) Err:122 |
RMM_Client.exe | [312]2020-12-07 06:14:17 [CUnPack::UnPackFiles] UnPack count:2 len:15 File:(null) Err:0 |