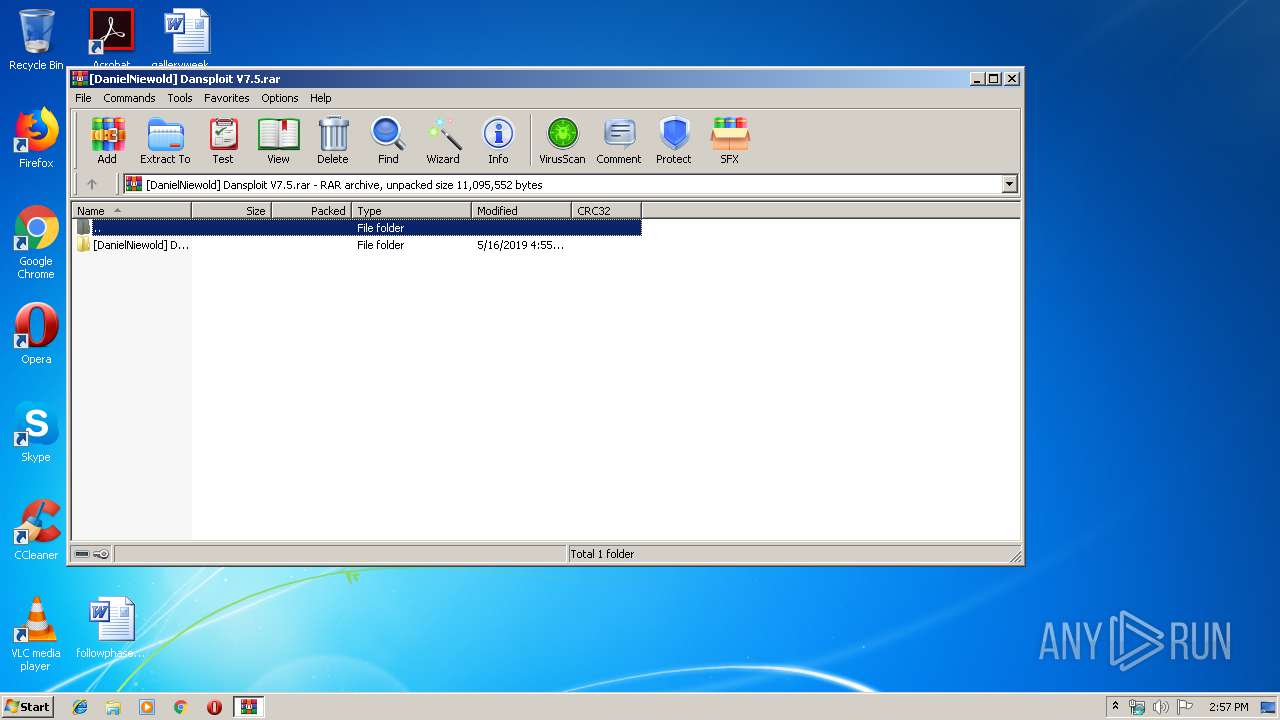
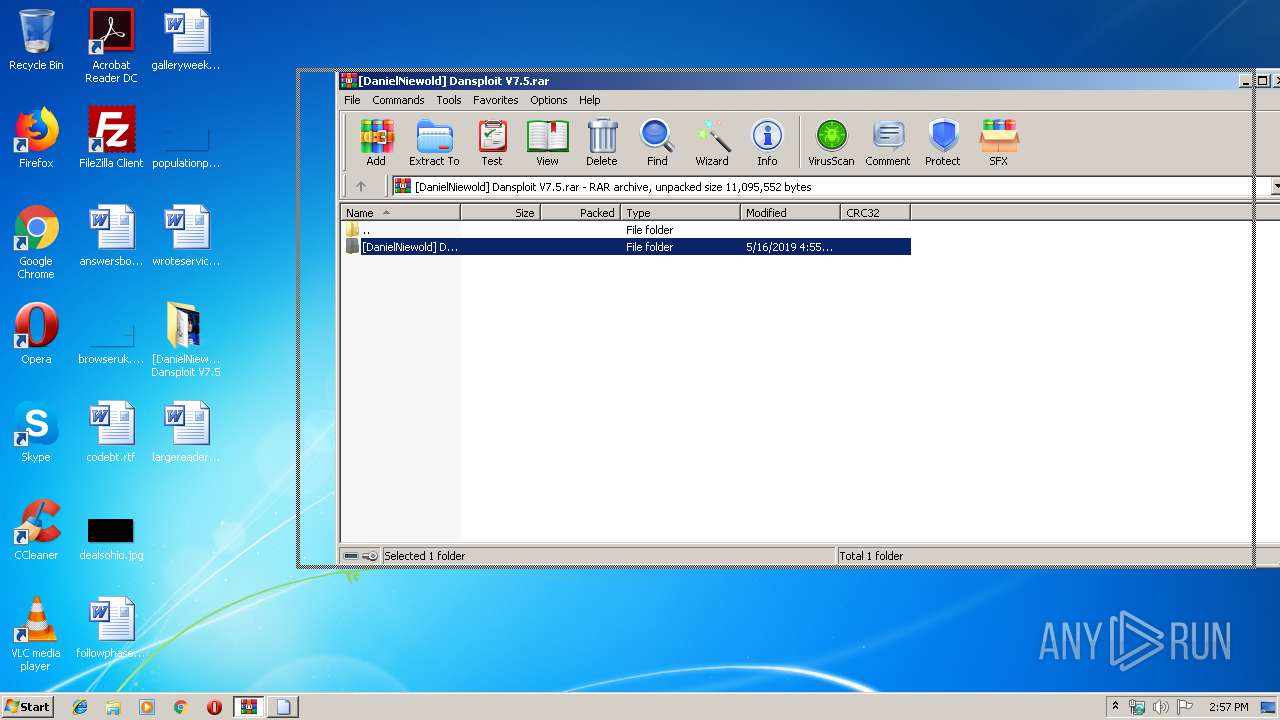
| File name: | [DanielNiewold] Dansploit V7.5.rar |
| Full analysis: | https://app.any.run/tasks/a49b4764-3ab3-4df6-88bf-1426b11cead5 |
| Verdict: | No threats detected |
| Analysis date: | June 23, 2019, 13:56:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 7894482F5B65DE5B59C39FBBA7EDEAA7 |
| SHA1: | D9E2262201BC4EA3EEA28ADB37A750981C564771 |
| SHA256: | BB316C4692D2BC8B319470F34F5B9B7D159670CED42AC8A7122F0D2D42681328 |
| SSDEEP: | 196608:4gd03DmtjgPvk99UCNAZue0XsJeb+2EcDu5j3bYjJblPC1bRMgpmkD:4LTC2MDiJey2EeSLUdlOmkD |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3172)
INFO
Manual execution by user
- Dansploit.exe (PID: 2444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2444 | "C:\Users\admin\Desktop\[DanielNiewold] Dansploit V7.5\Dansploit.exe" | C:\Users\admin\Desktop\[DanielNiewold] Dansploit V7.5\Dansploit.exe | — | explorer.exe | |||||||||||
User: admin Company: HP Inc. Integrity Level: MEDIUM Description: Dansploit Rewrite Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
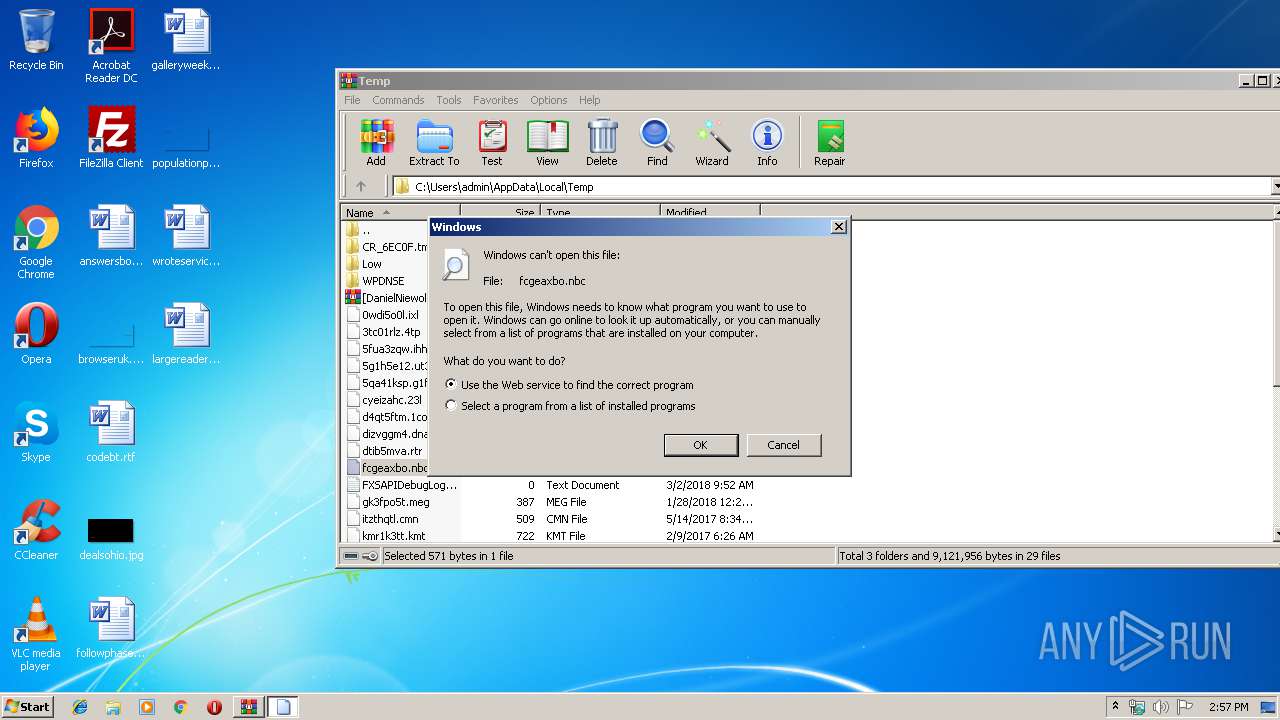
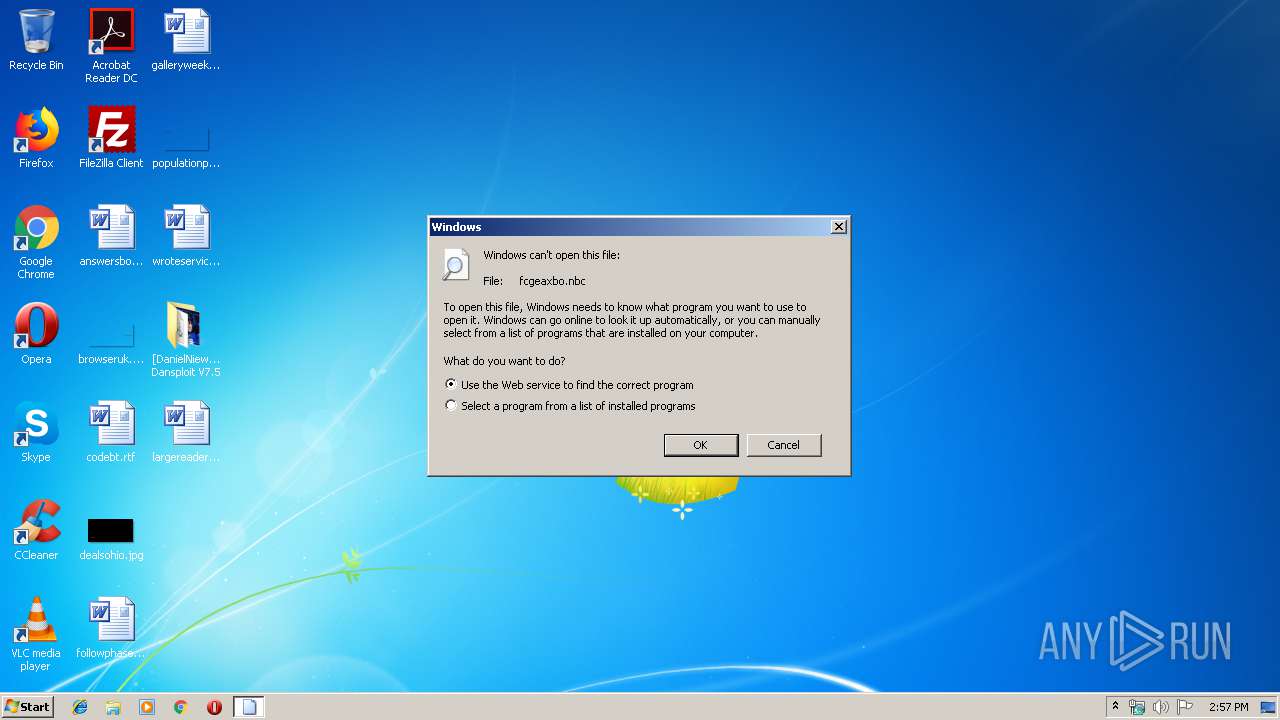
| 3068 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\fcgeaxbo.nbc | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
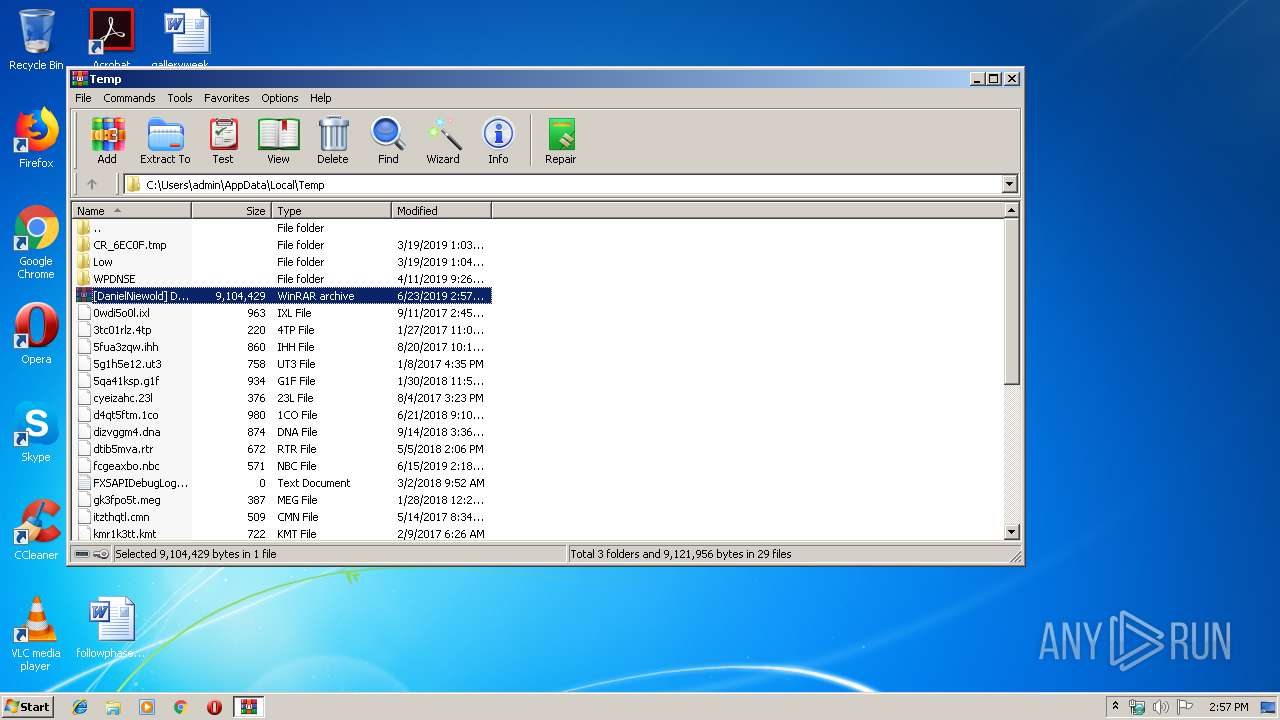
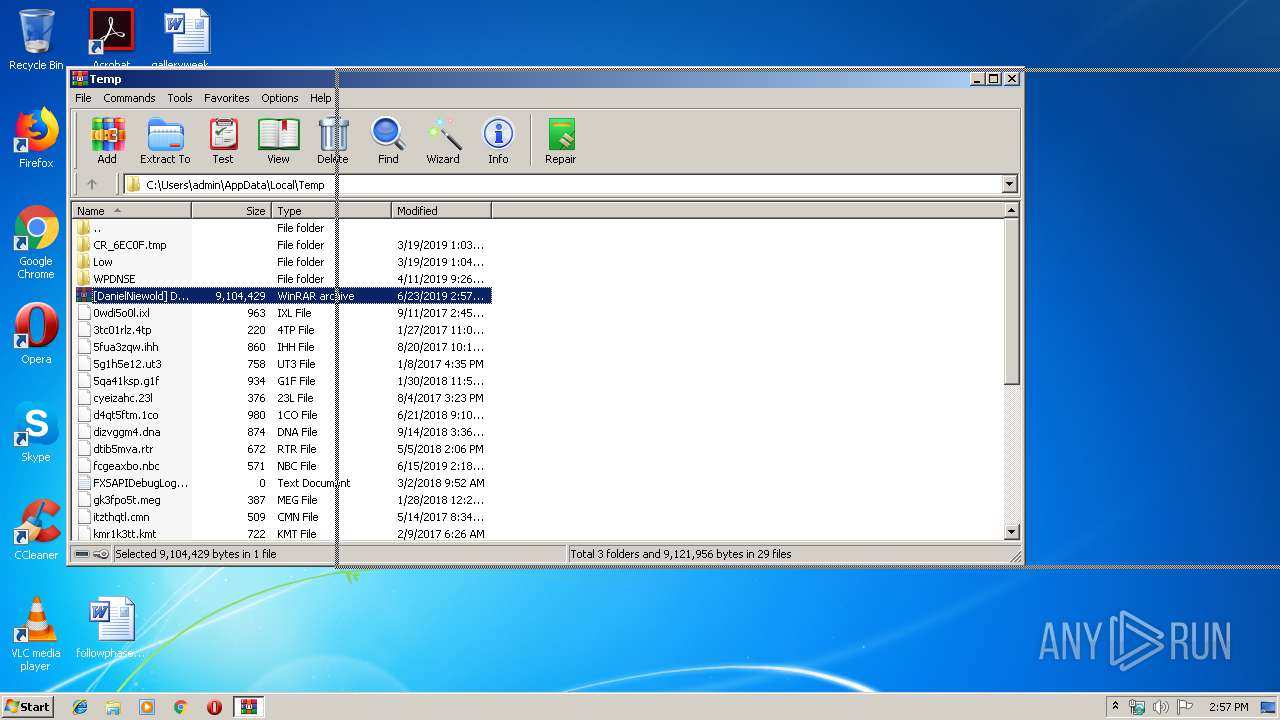
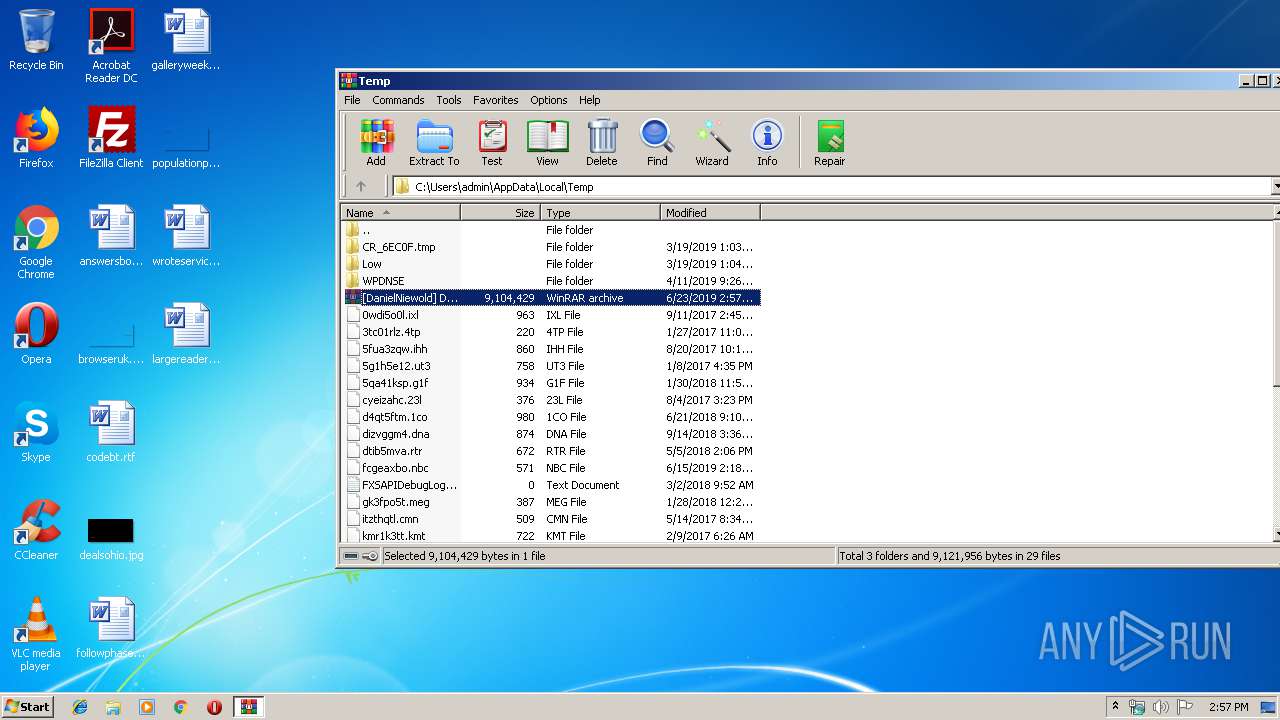
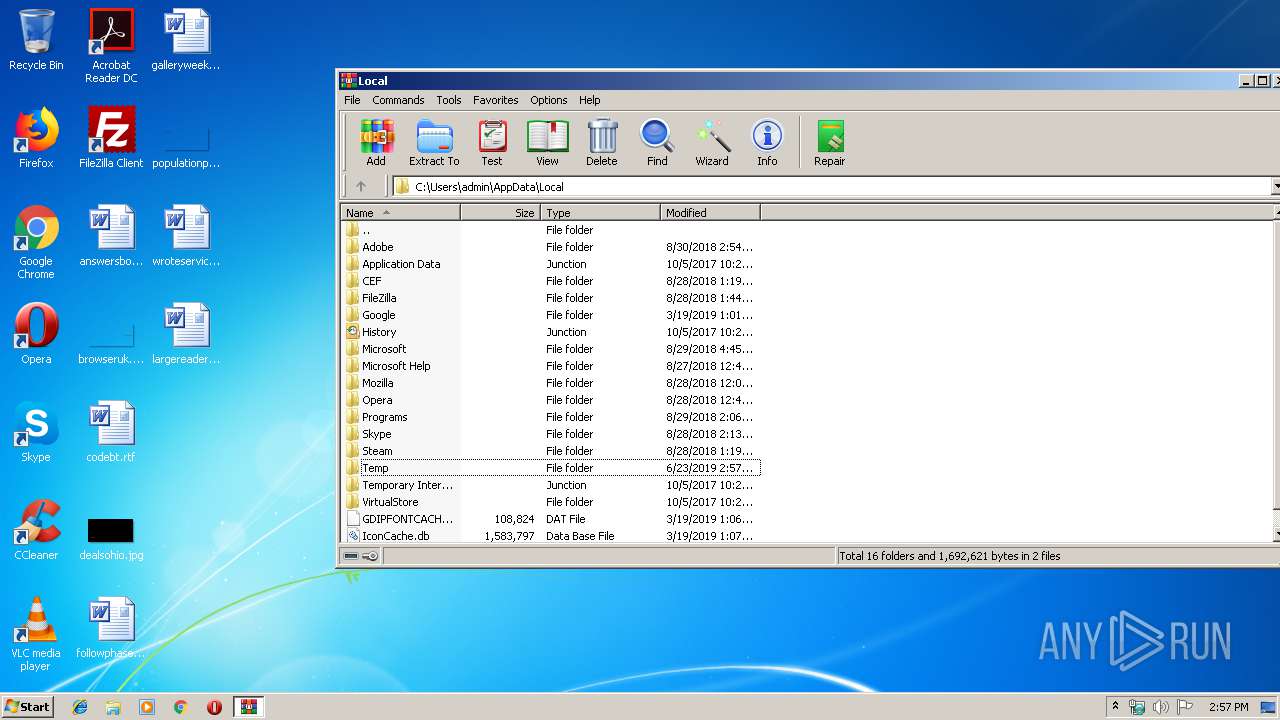
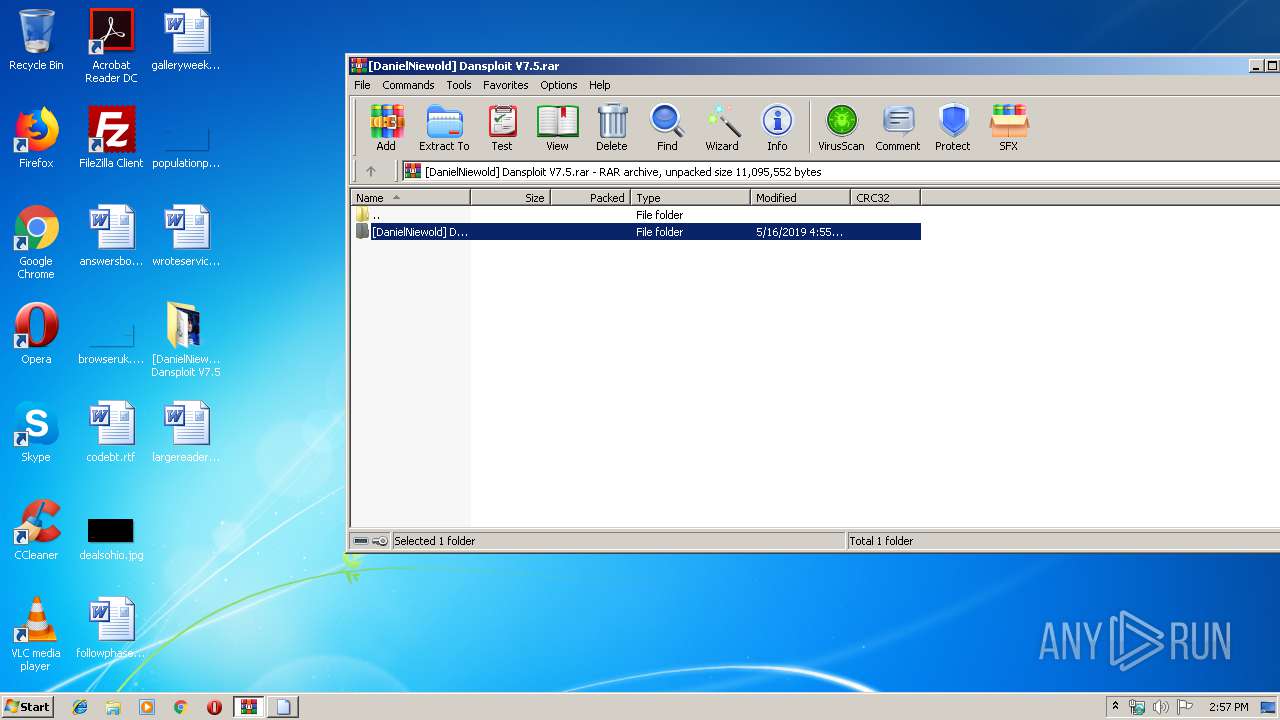
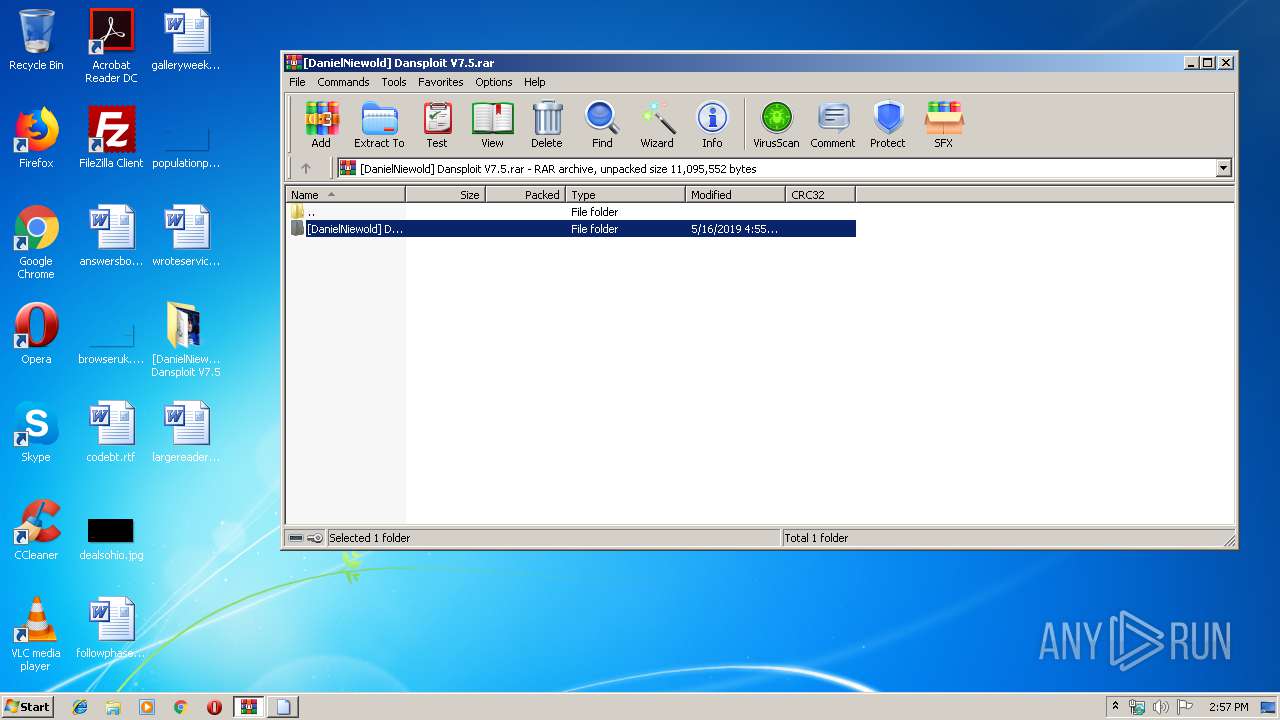
| 3172 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\[DanielNiewold] Dansploit V7.5.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
474
Read events
442
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\[DanielNiewold] Dansploit V7.5.rar | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3172) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
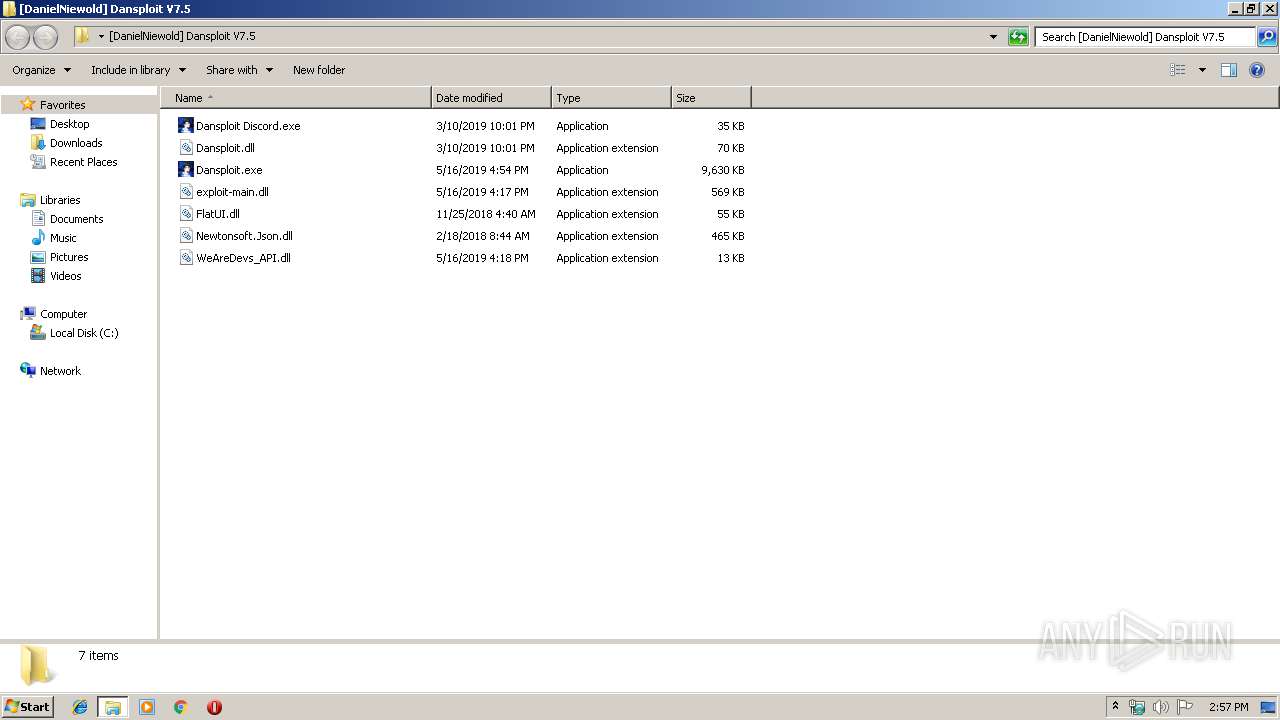
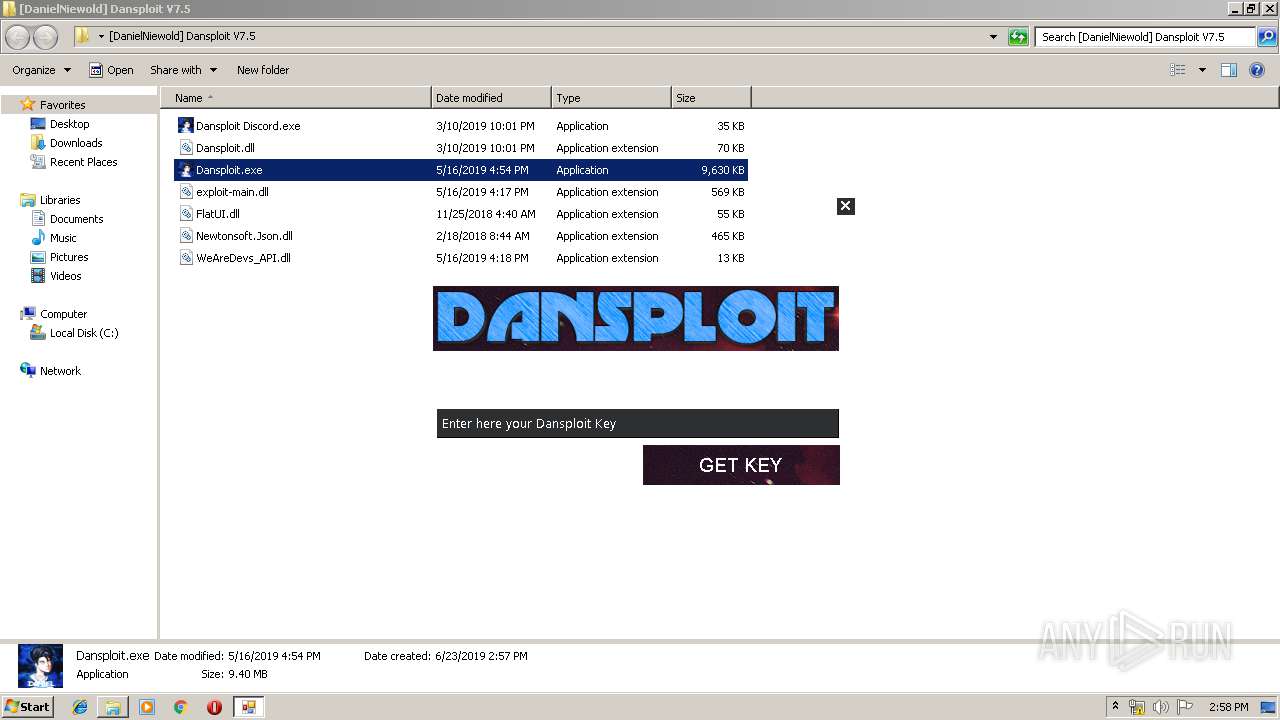
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\Dansploit Discord.exe | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\Dansploit.dll | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\Dansploit.exe | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\exploit-main.dll | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\FlatUI.dll | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\Newtonsoft.Json.dll | — | |
MD5:— | SHA256:— | |||
| 3172 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3172.26110\[DanielNiewold] Dansploit V7.5\WeAreDevs_API.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report