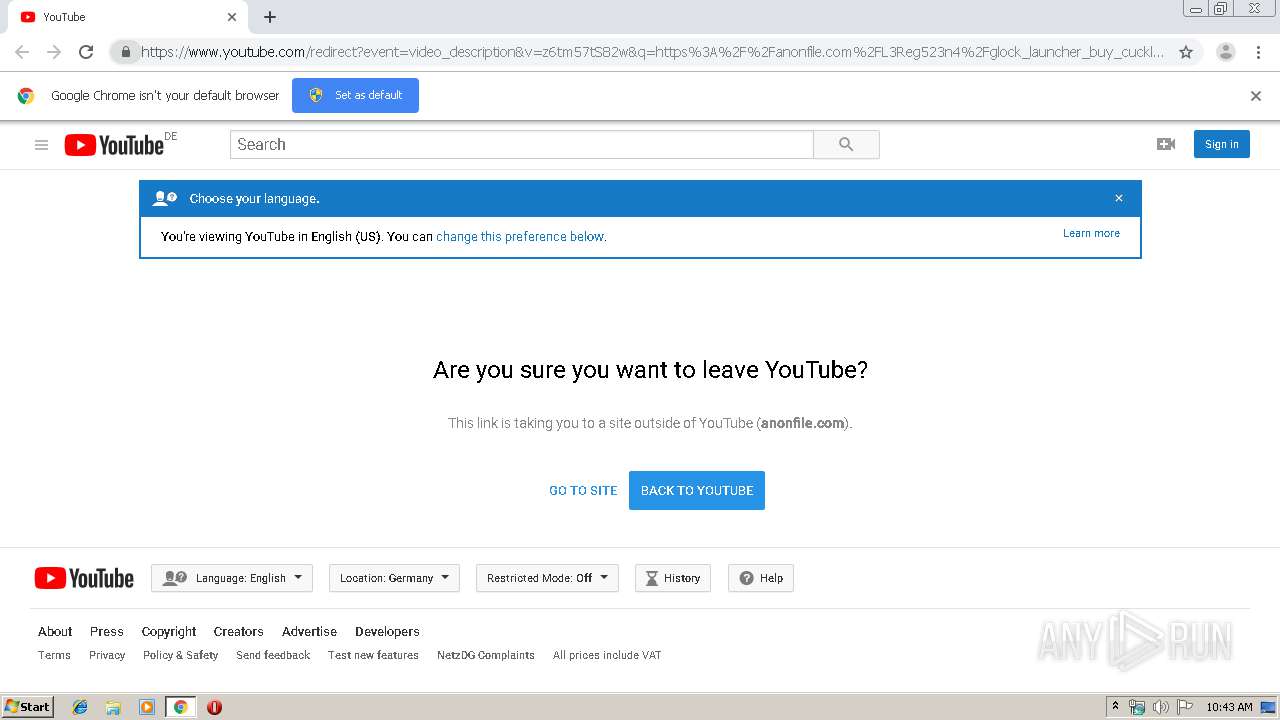
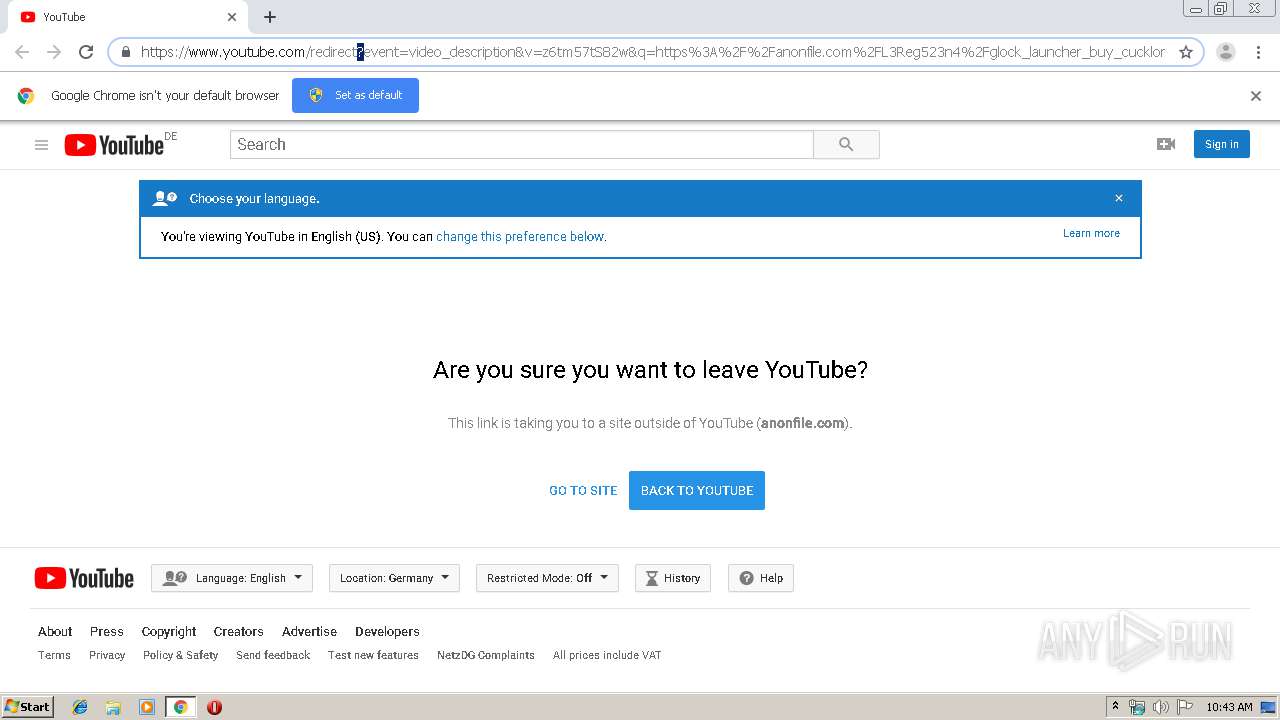
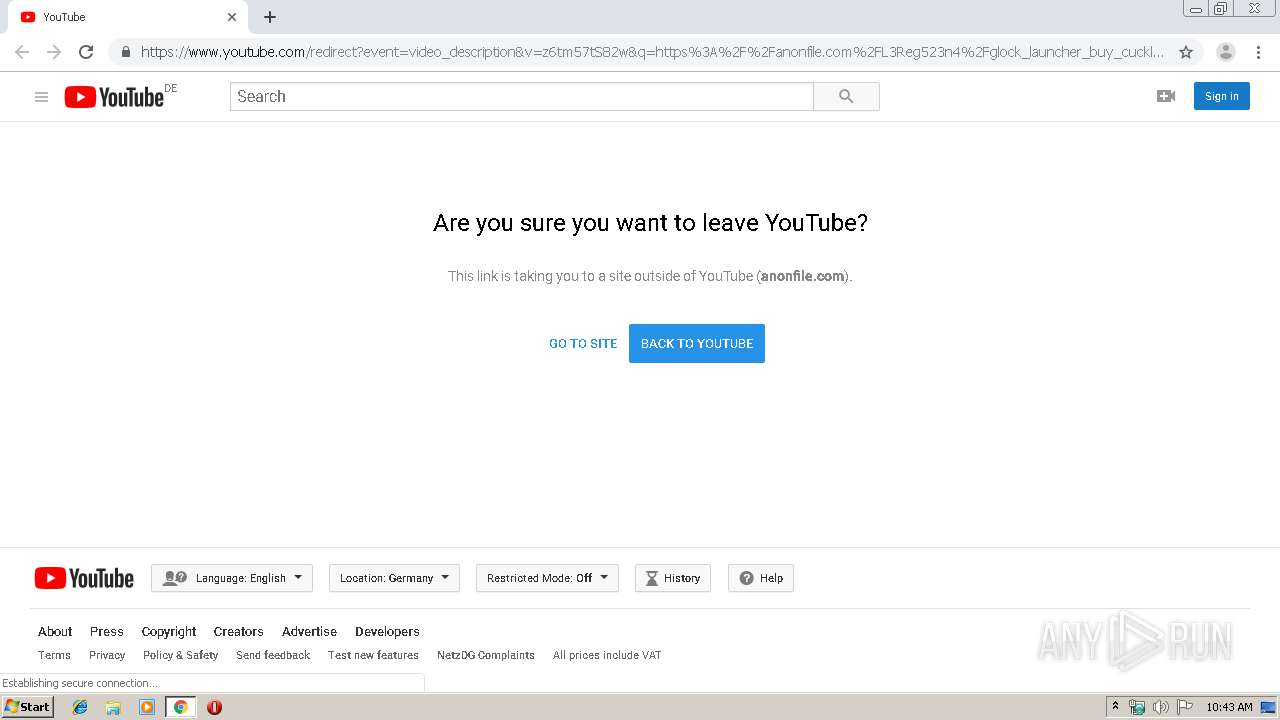
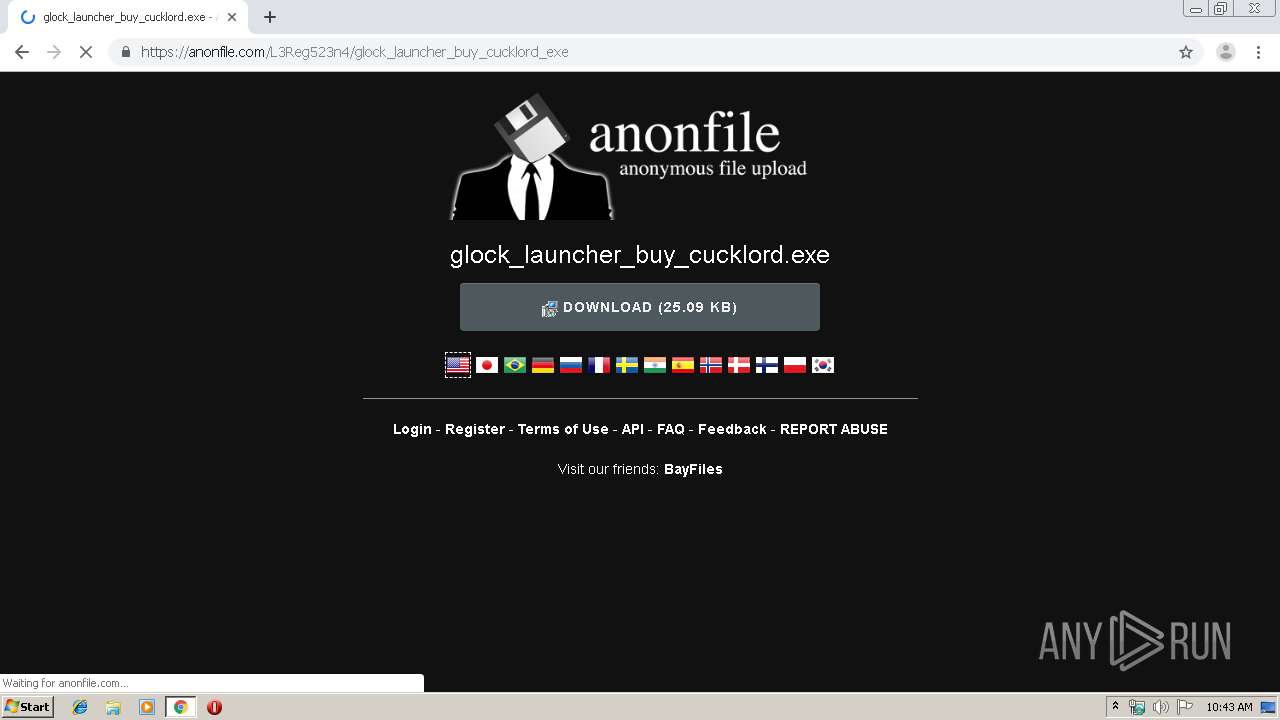
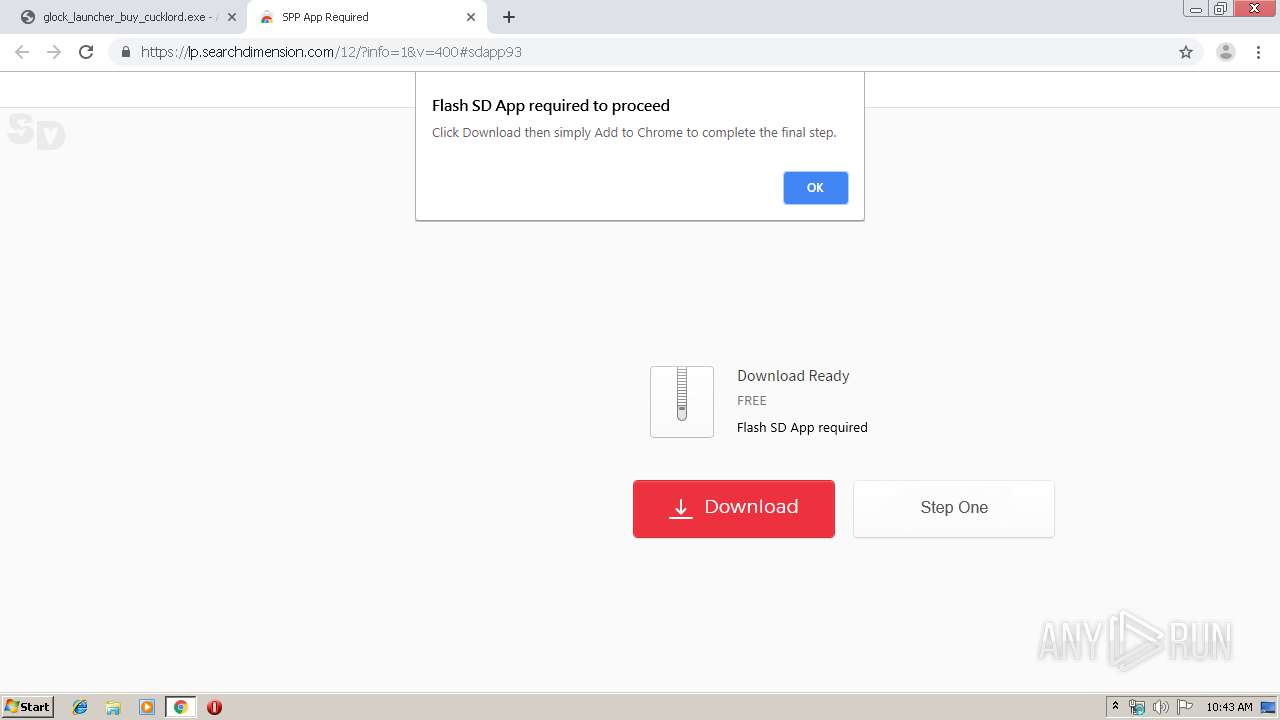
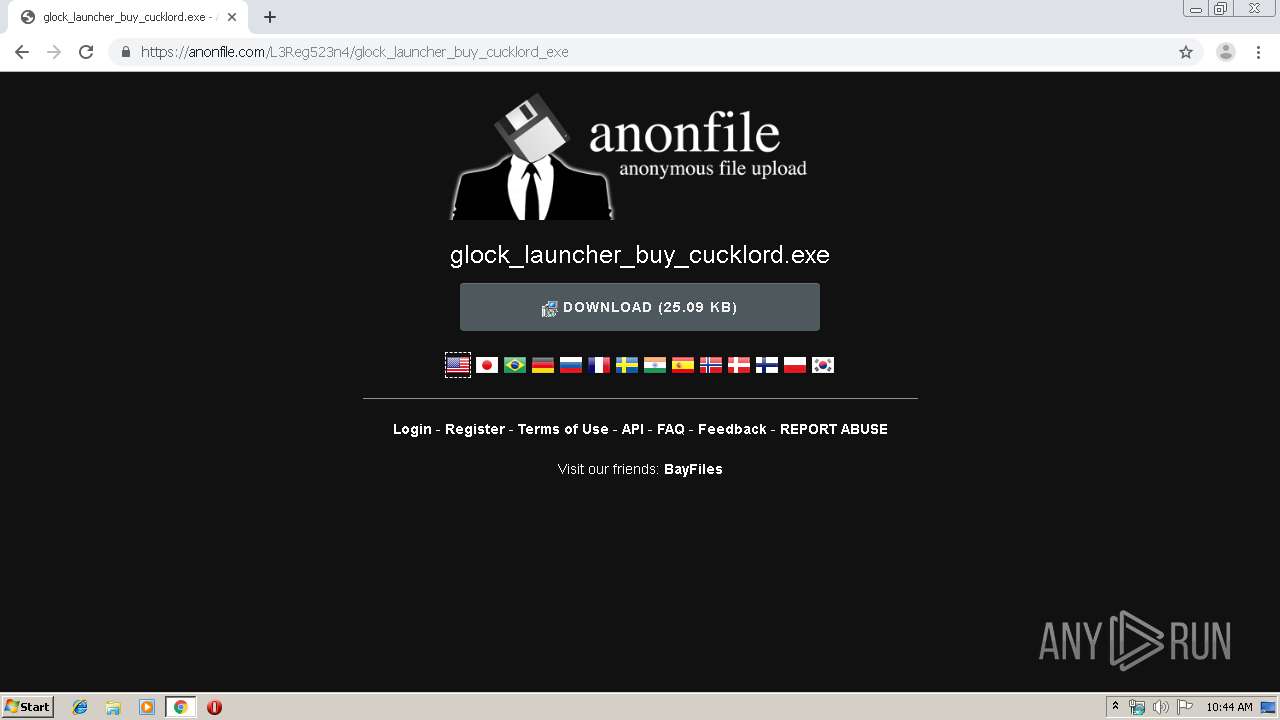
| URL: | https://www.youtube.com/redirect?event=video_description&v=z6tm57tS82w&q=https%3A%2F%2Fanonfile.com%2FL3Reg523n4%2Fglock_launcher_buy_cucklord_exe&redir_token=RIDx7yvXYa4YtHZDQF5jX4IJLQt8MTU2NjgxMjQ5MUAxNTY2NzI2MDkx |
| Full analysis: | https://app.any.run/tasks/e60098a1-1f6c-43a3-abe8-409374c37e1b |
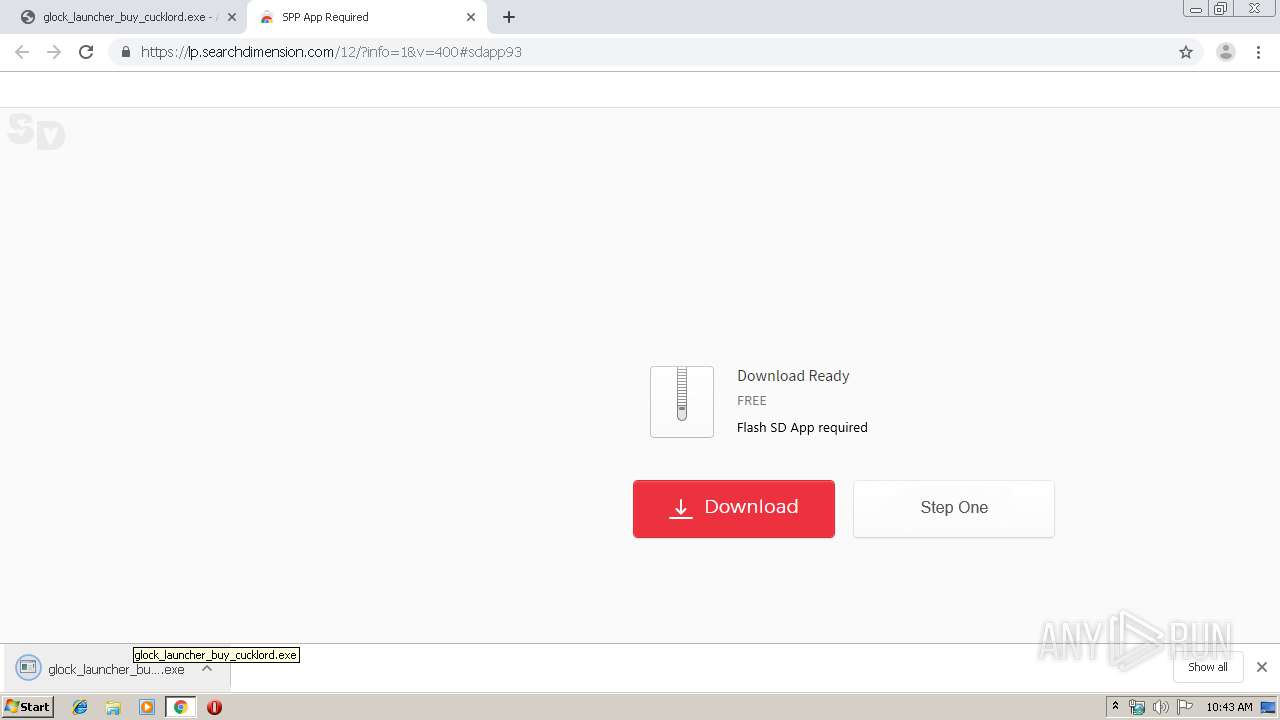
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2019, 09:43:04 |
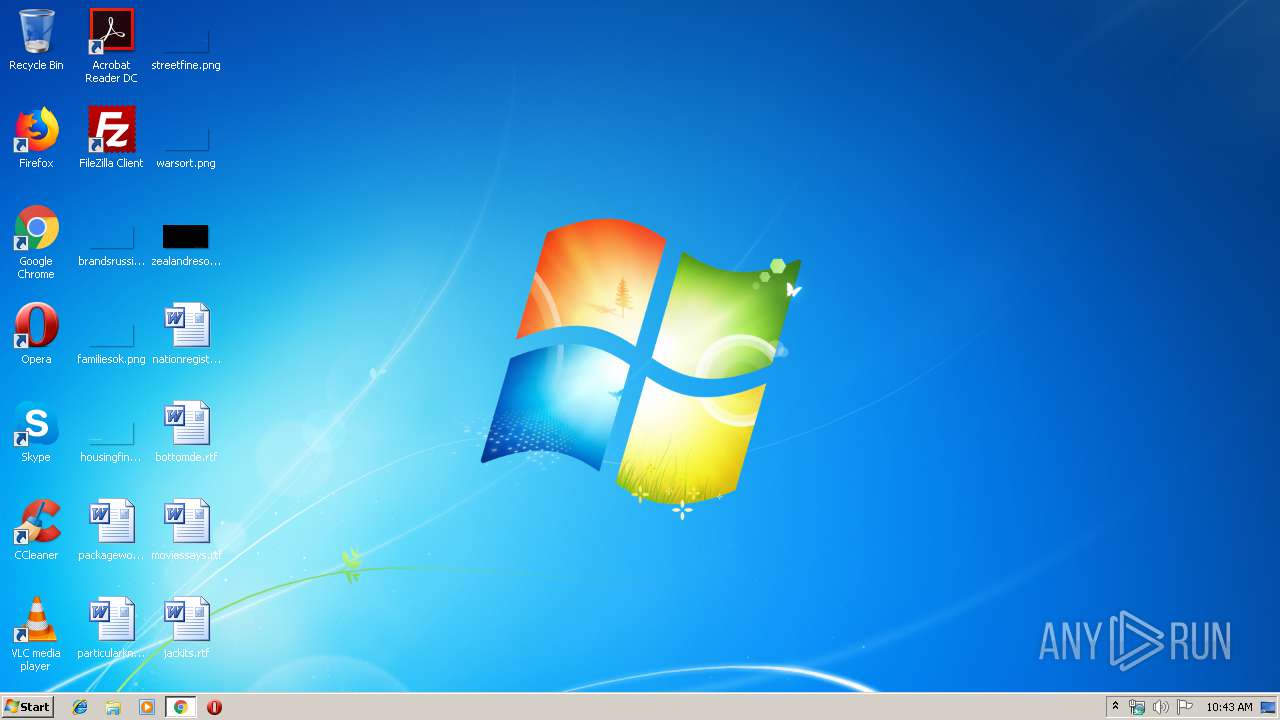
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C38FF08AFBC77AE061092CF5F90D5B5E |
| SHA1: | BD885300CB602DA1ED7E7EA6036152D9D2862C36 |
| SHA256: | BB24D8B6E5A2FA16FEDCF6893190FE969CACC02D5E72D8CA2DF16B62515AE9CB |
| SSDEEP: | 6:2OLUxGKmKLQnC3zOE8wKd4VvGw4HqMdJd:2jGRi1Kd4JENB |
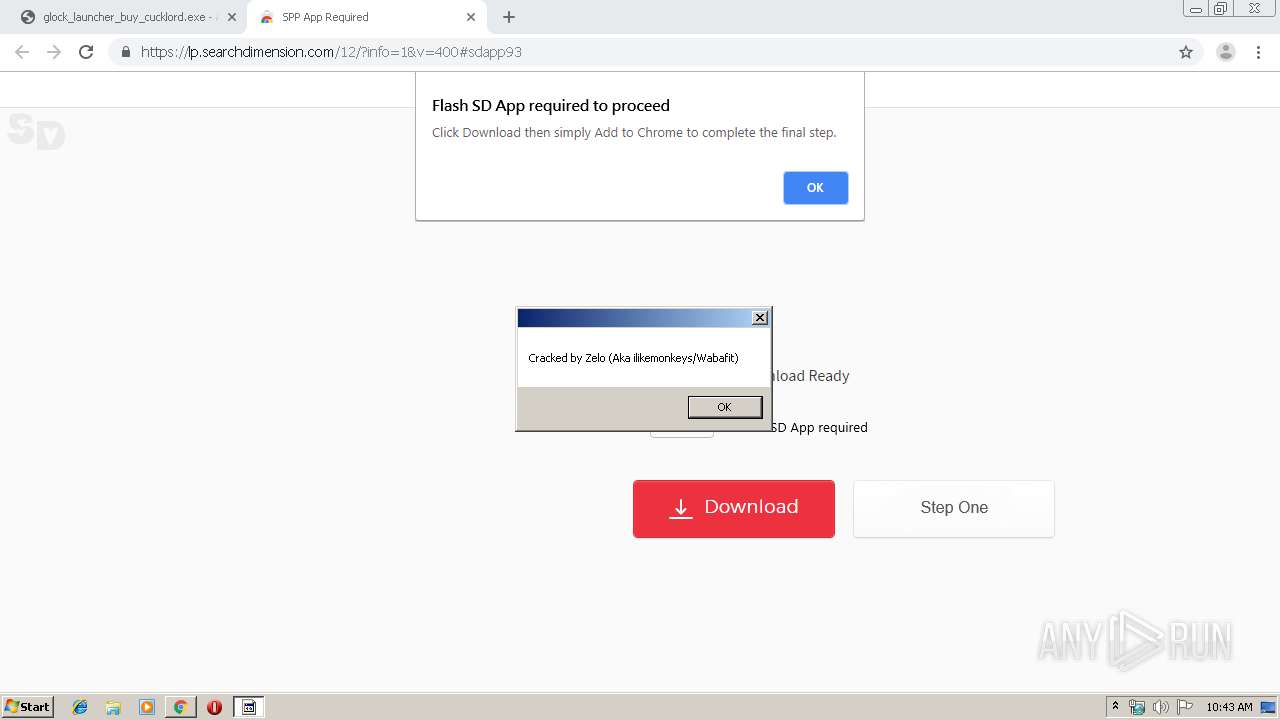
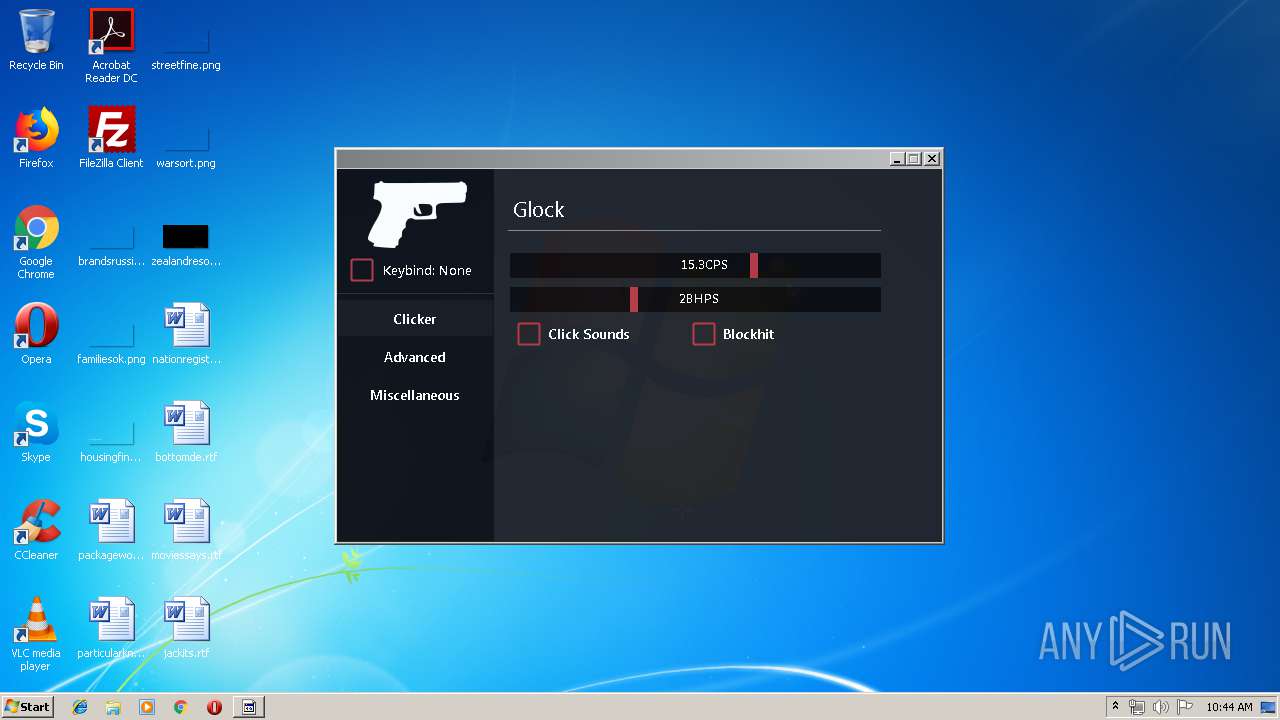
MALICIOUS
Application was dropped or rewritten from another process
- glock_launcher_buy_cucklord.exe (PID: 3312)
- glock_launcher_buy_cucklord.exe (PID: 3828)
- hexkhasautism.exe (PID: 3536)
- dev4338.exe (PID: 3016)
Changes settings of System certificates
- glock_launcher_buy_cucklord.exe (PID: 3828)
Loads dropped or rewritten executable
- dev4338.exe (PID: 3016)
- hexkhasautism.exe (PID: 3536)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2796)
- chrome.exe (PID: 2452)
- glock_launcher_buy_cucklord.exe (PID: 3828)
- hexkhasautism.exe (PID: 3536)
- dev4338.exe (PID: 3016)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2796)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3884)
Adds / modifies Windows certificates
- glock_launcher_buy_cucklord.exe (PID: 3828)
Starts CMD.EXE for commands execution
- glock_launcher_buy_cucklord.exe (PID: 3828)
- hexkhasautism.exe (PID: 3536)
Loads DLL from Mozilla Firefox
- dev4338.exe (PID: 3016)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2452)
Application launched itself
- chrome.exe (PID: 2796)
Reads Internet Cache Settings
- chrome.exe (PID: 2796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
73
Monitored processes
33
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6660624486099013222 --mojo-platform-channel-handle=936 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 4294967295 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Windows\System32\cmd.exe" /c cd "C:\Users\admin\AppData\Local\Temp\" & del /f /q dev4338.exe & rmdir /q /s x86 | C:\Windows\System32\cmd.exe | — | hexkhasautism.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5053429112806620923 --mojo-platform-channel-handle=4032 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7659394164339941131 --mojo-platform-channel-handle=2172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5486276594126163487 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3443557107550614894 --mojo-platform-channel-handle=4208 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11358544352013641242 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5219683983997778016 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12652882962328595837 --mojo-platform-channel-handle=3520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.youtube.com/redirect?event=video_description&v=z6tm57tS82w&q=https%3A%2F%2Fanonfile.com%2FL3Reg523n4%2Fglock_launcher_buy_cucklord_exe&redir_token=RIDx7yvXYa4YtHZDQF5jX4IJLQt8MTU2NjgxMjQ5MUAxNTY2NzI2MDkx" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 4294967295 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 955
Read events
1 718
Write events
232
Delete events
5
Modification events
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2796-13211199799411375 |
Value: 259 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2796) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
14
Suspicious files
80
Text files
213
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f95c79be-5ed8-4d16-9d8a-5d0521c9bf14.tmp | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169d1f.TMP | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2796 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169d1f.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
57
DNS requests
56
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2452 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 523 b | whitelisted |
2452 | chrome.exe | GET | 200 | 2.16.106.186:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.6 Kb | whitelisted |
2452 | chrome.exe | GET | 200 | 2.16.106.233:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 56.6 Kb | whitelisted |
3828 | glock_launcher_buy_cucklord.exe | GET | 404 | 149.56.233.9:80 | http://zeloverification.freeshells.org/glock/hexkhasautism.zip | CA | html | 318 b | unknown |
2452 | chrome.exe | GET | 200 | 8.241.121.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.6 Kb | whitelisted |
2452 | chrome.exe | GET | 200 | 195.95.178.177:80 | http://r6---sn-pouxga5o-vu2s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=5.254.82.116&mm=28&mn=sn-pouxga5o-vu2s&ms=nvh&mt=1566725952&mv=u&mvi=5&pl=27&shardbypass=yes | RO | crx | 862 Kb | whitelisted |
2452 | chrome.exe | GET | 200 | 54.192.185.242:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2452 | chrome.exe | 172.217.18.14:80 | www.youtube.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 195.95.178.177:80 | r6---sn-pouxga5o-vu2s.gvt1.com | Asociatia Interlan | RO | whitelisted |
2452 | chrome.exe | 194.32.146.60:443 | anonfile.com | — | — | unknown |
2452 | chrome.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2452 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.18.14:443 | www.youtube.com | Google Inc. | US | whitelisted |
2452 | chrome.exe | 172.217.22.110:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.gstatic.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3536 | hexkhasautism.exe | Generic Protocol Command Decode | SURICATA Applayer Protocol detection skipped |
Process | Message |
|---|---|
dev4338.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\AppData\Local\Temp\x86\SQLite.Interop.dll"...
|