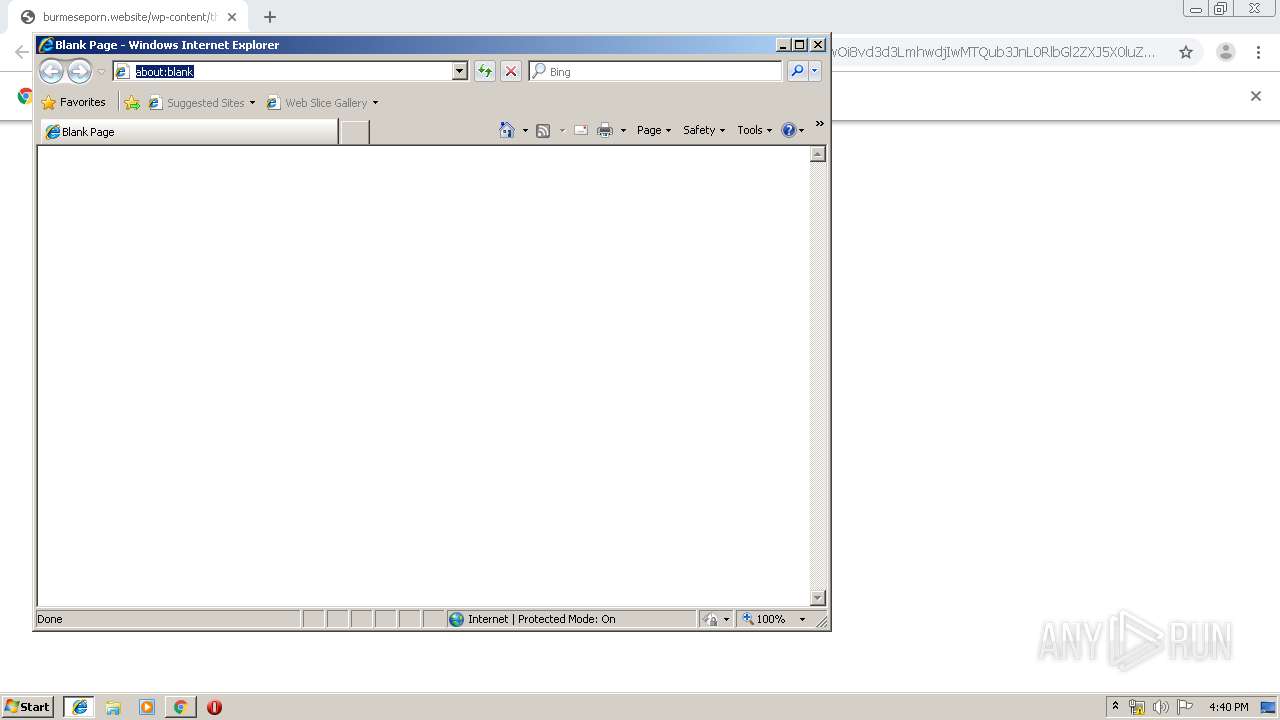
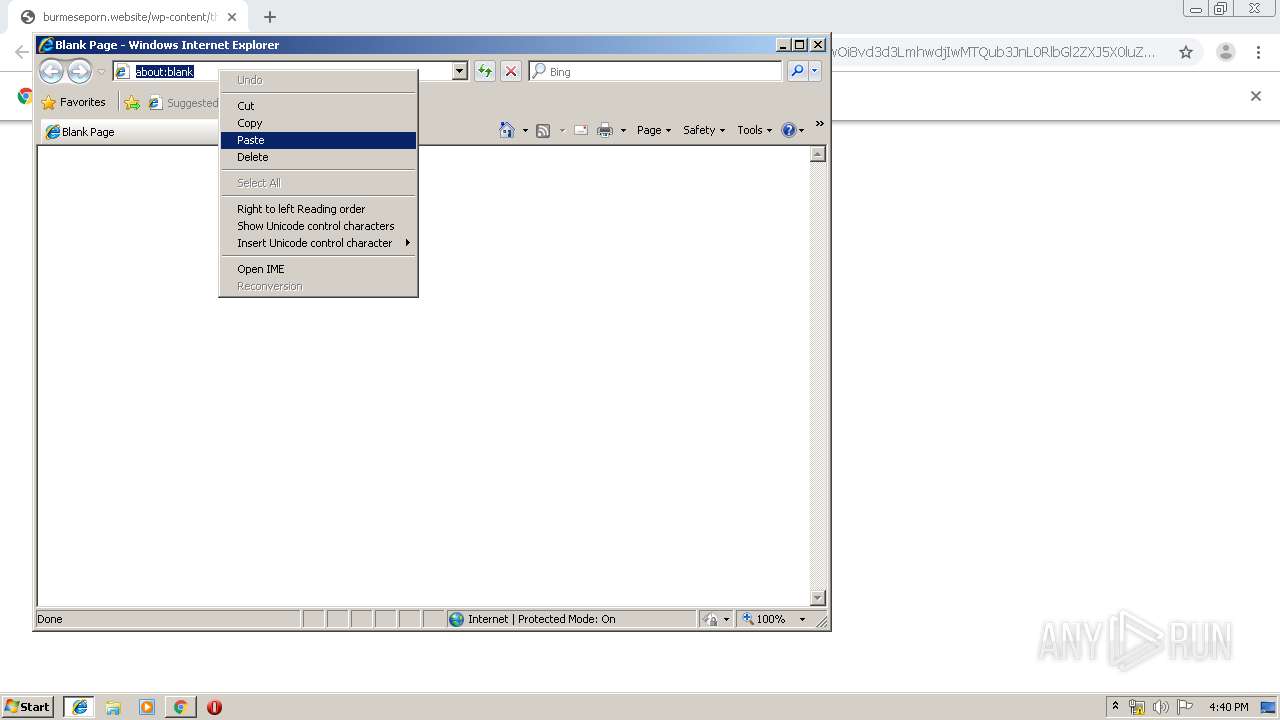
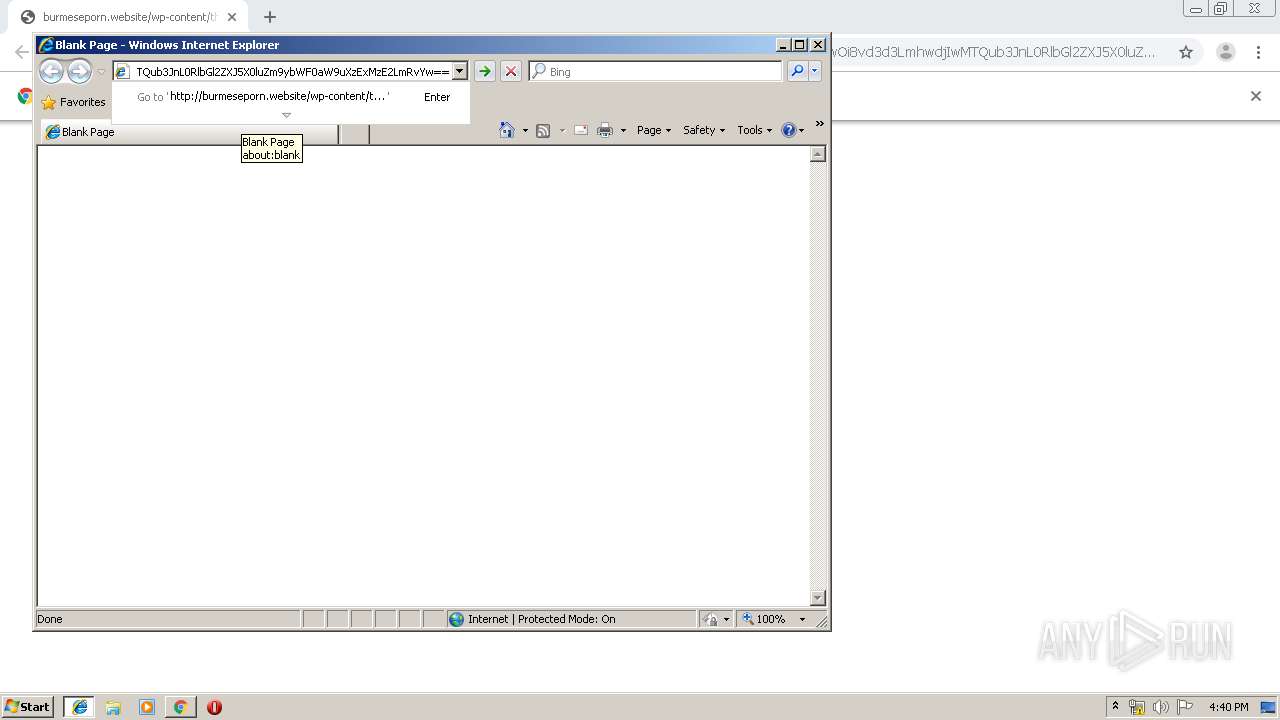
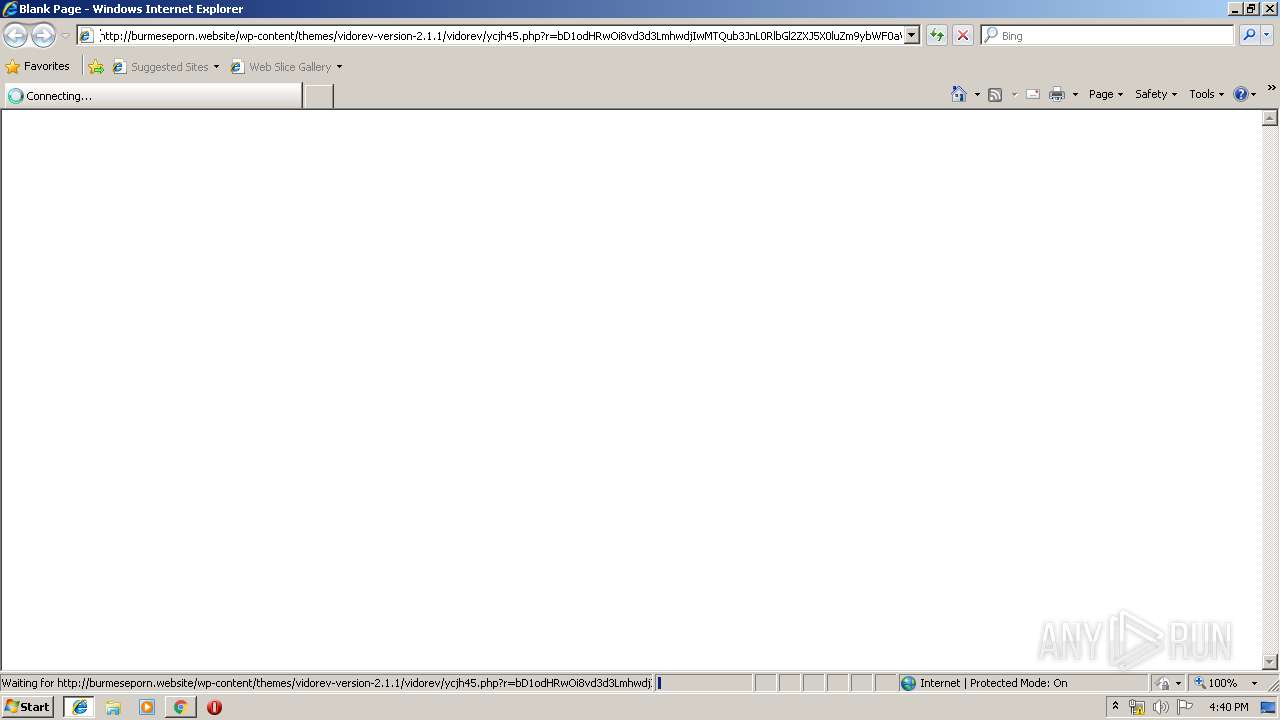
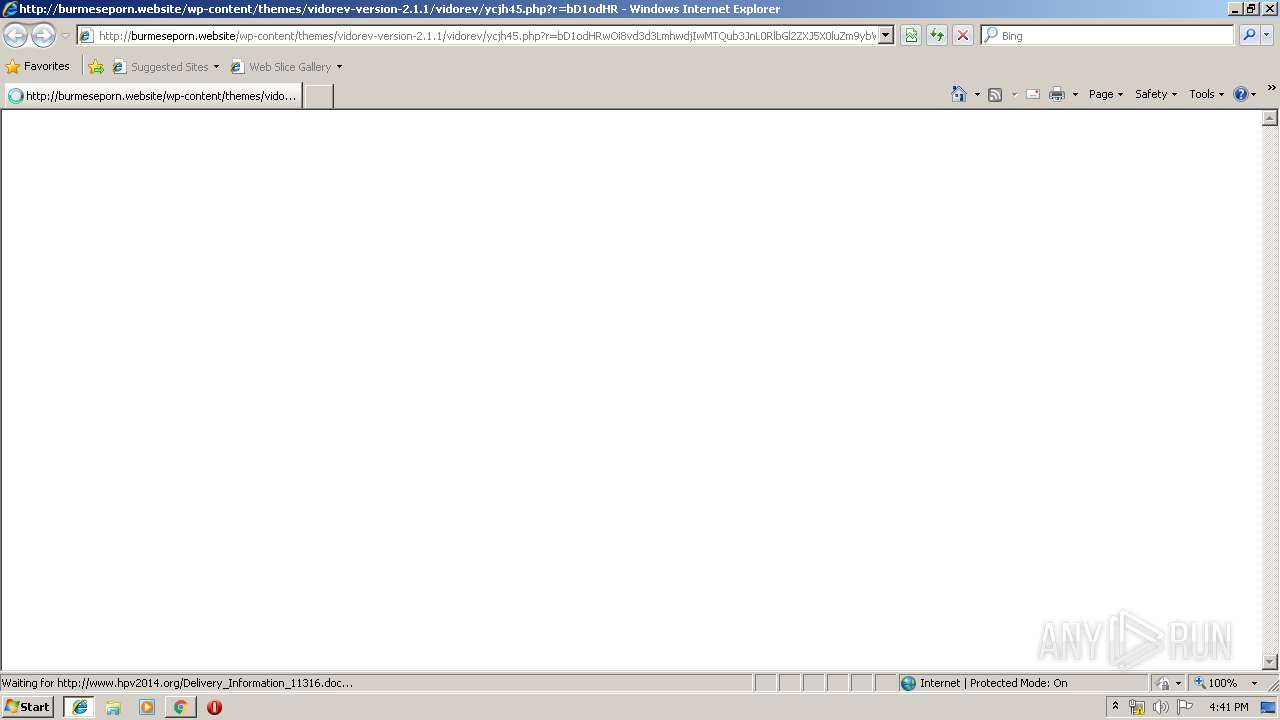
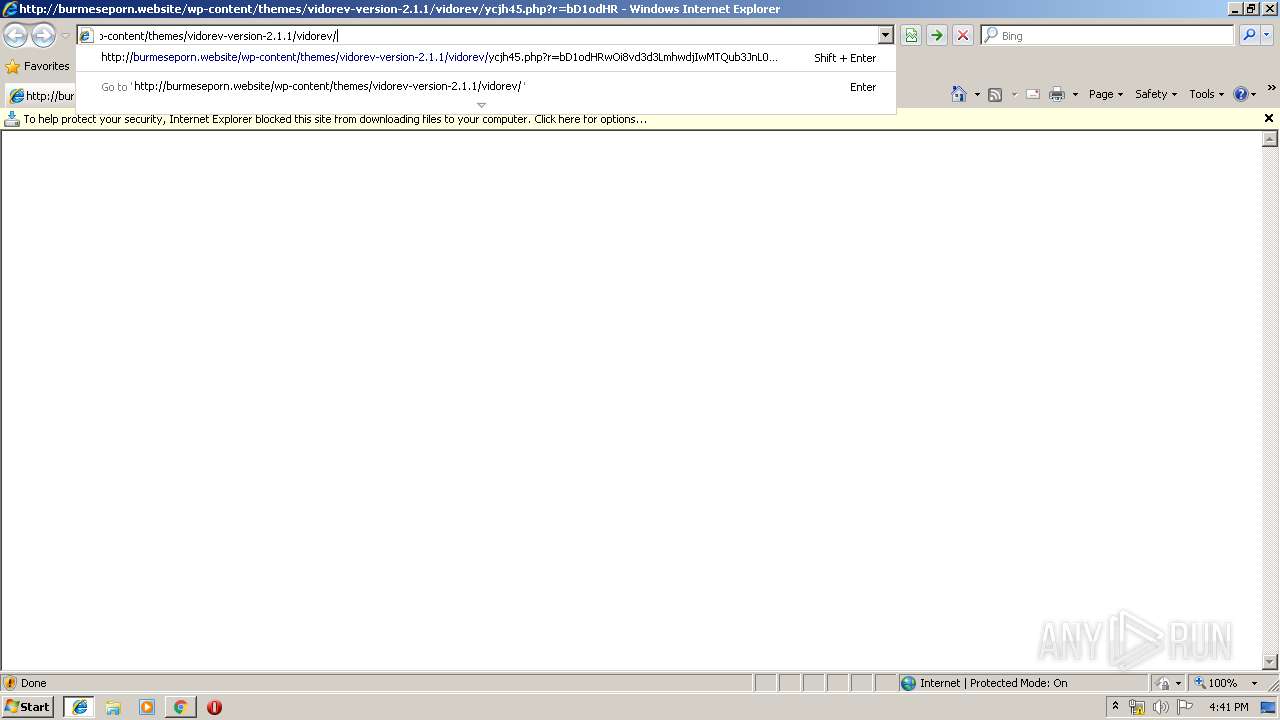
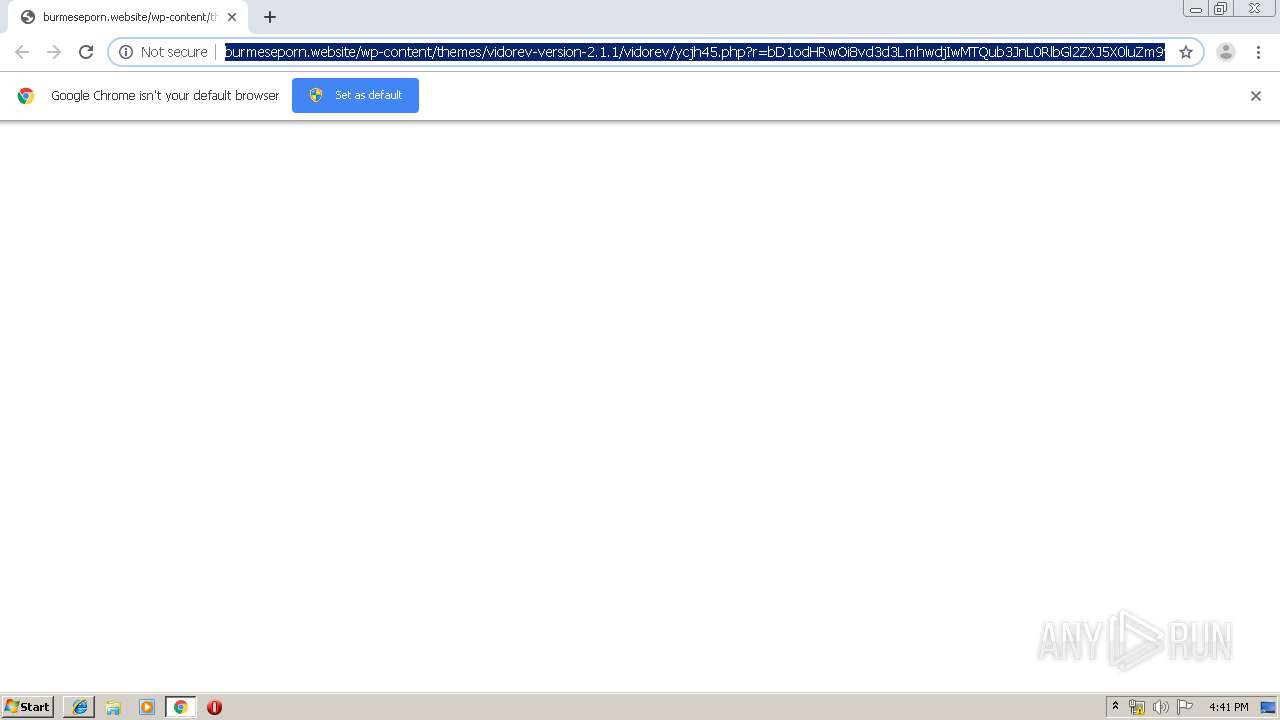
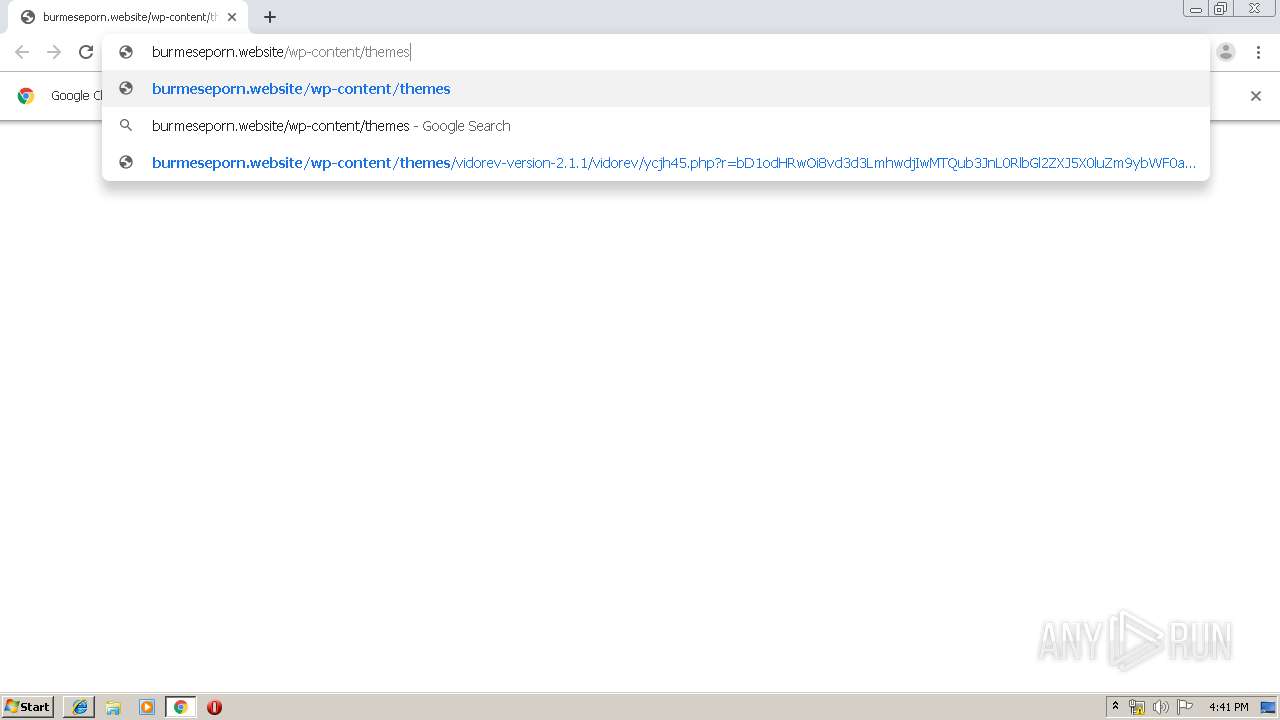
| URL: | http://burmeseporn.website/wp-content/themes/vidorev-version-2.1.1/vidorev/ycjh45.php?r=bD1odHRwOi8vd3d3LmhwdjIwMTQub3JnL0RlbGl2ZXJ5X0luZm9ybWF0aW9uXzExMzE2LmRvYw== |
| Full analysis: | https://app.any.run/tasks/4e128125-59ac-4a5f-8d4f-5e21e3d51958 |
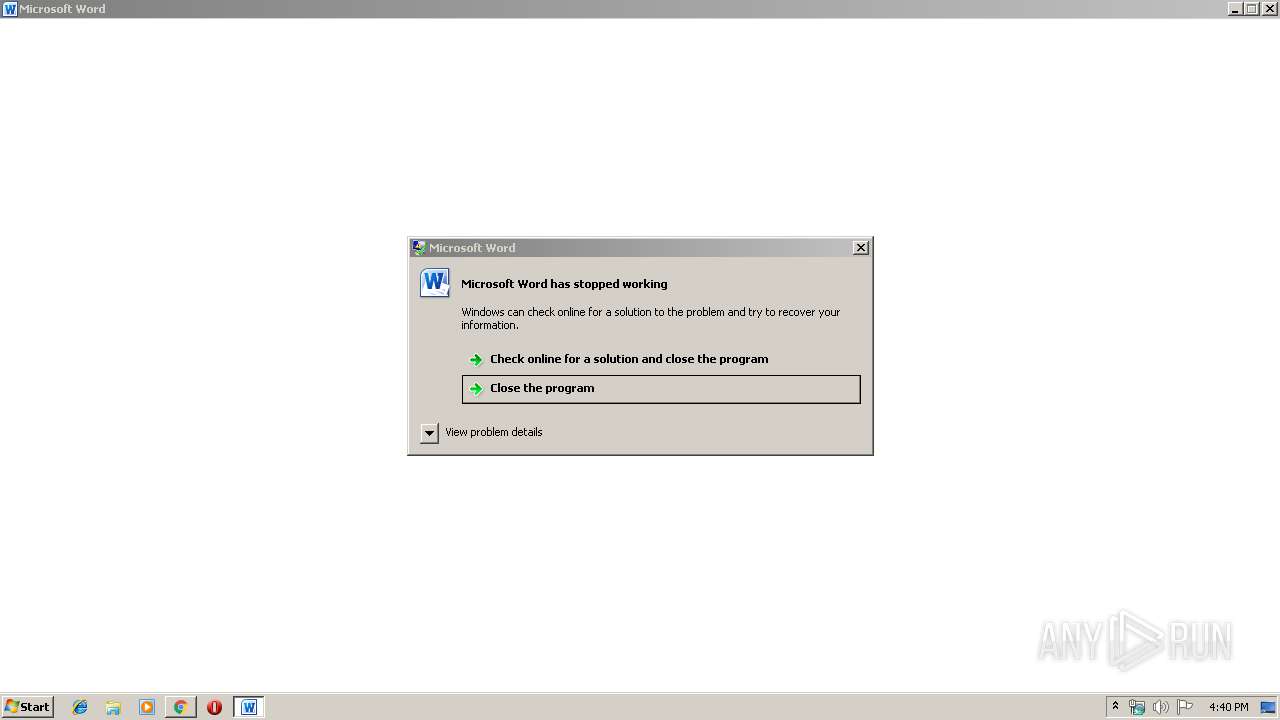
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 16:39:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CCEBE75FC9D44E904A88FE91319C5023 |
| SHA1: | 1ECBD4170ACDCD1925AA92DC0E8B5CBA10330E6B |
| SHA256: | BB22BA162CFBD797D9EF4FB488AC1197E07A235275E12A9954EFEB456CC9146D |
| SSDEEP: | 3:N1KcC+XzcYAQrFHKX2ITt8XOTeK3bScvRgBWpINcsVpILpdK1vpAtHwVEPQ9gqqQ:CcHXzcYAkFHM2ITQOTeK9p/mNd+zWpAC |
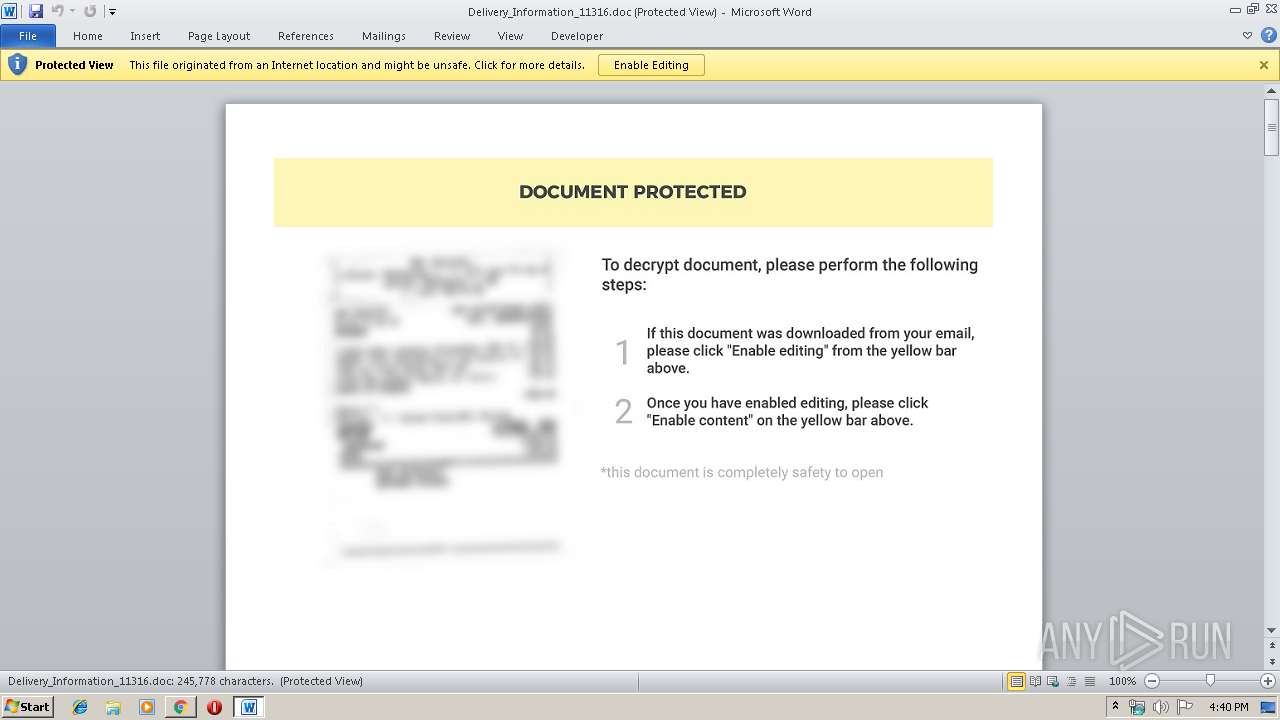
MALICIOUS
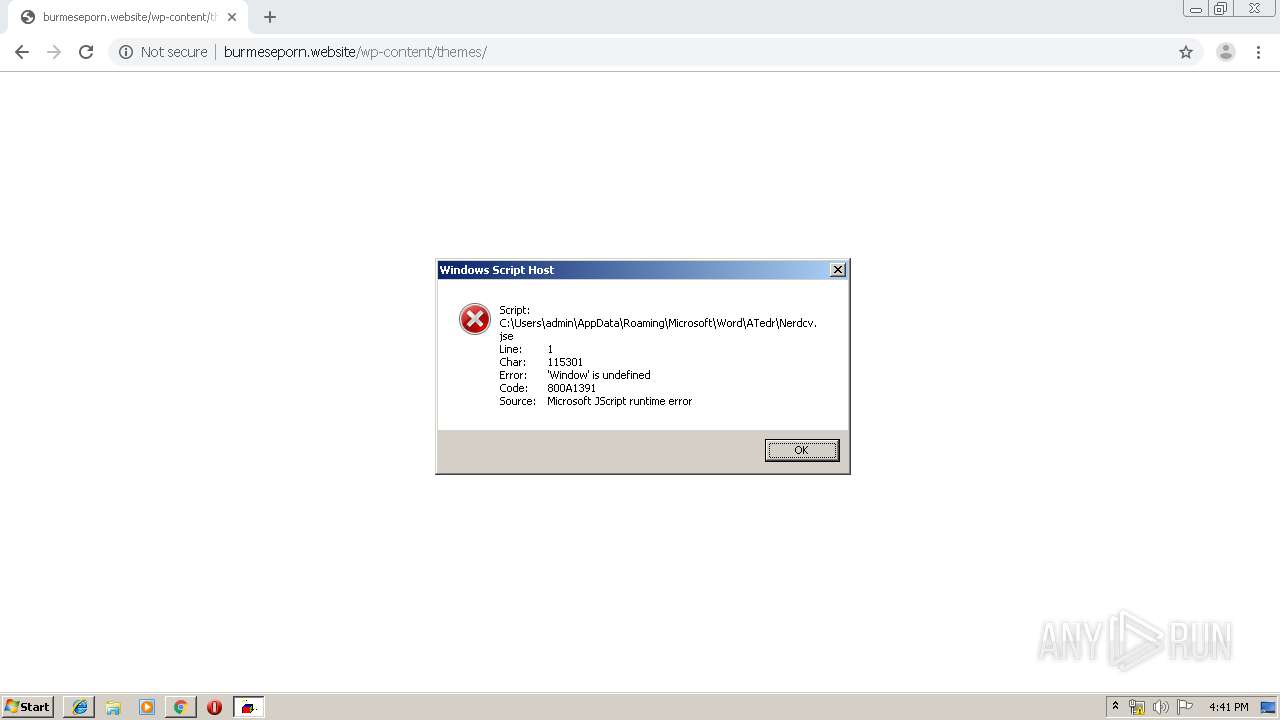
Executes scripts
- WINWORD.EXE (PID: 1704)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1704)
SUSPICIOUS
Starts Microsoft Office Application
- chrome.exe (PID: 884)
- WINWORD.EXE (PID: 1704)
Modifies files in Chrome extension folder
- chrome.exe (PID: 884)
Application launched itself
- WINWORD.EXE (PID: 1704)
INFO
Application launched itself
- chrome.exe (PID: 884)
- iexplore.exe (PID: 2860)
Reads Internet Cache Settings
- chrome.exe (PID: 884)
- iexplore.exe (PID: 2144)
Creates files in the user directory
- WINWORD.EXE (PID: 1704)
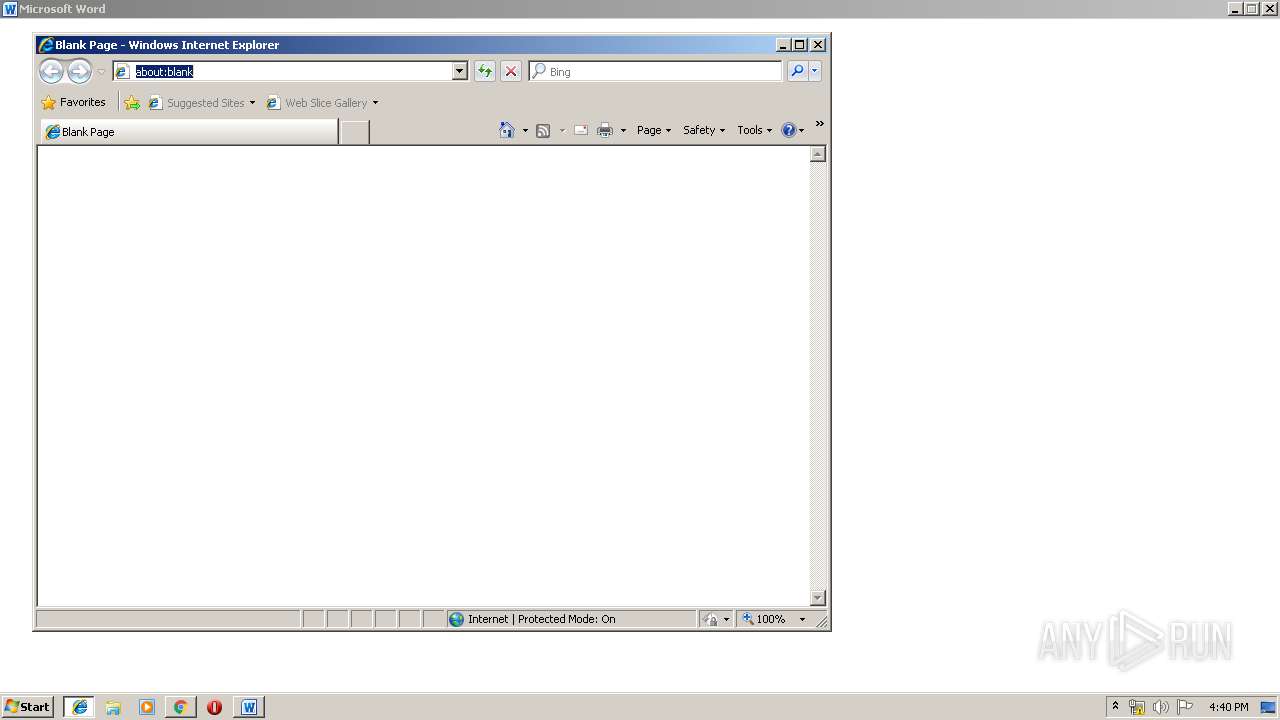
Manual execution by user
- iexplore.exe (PID: 2860)
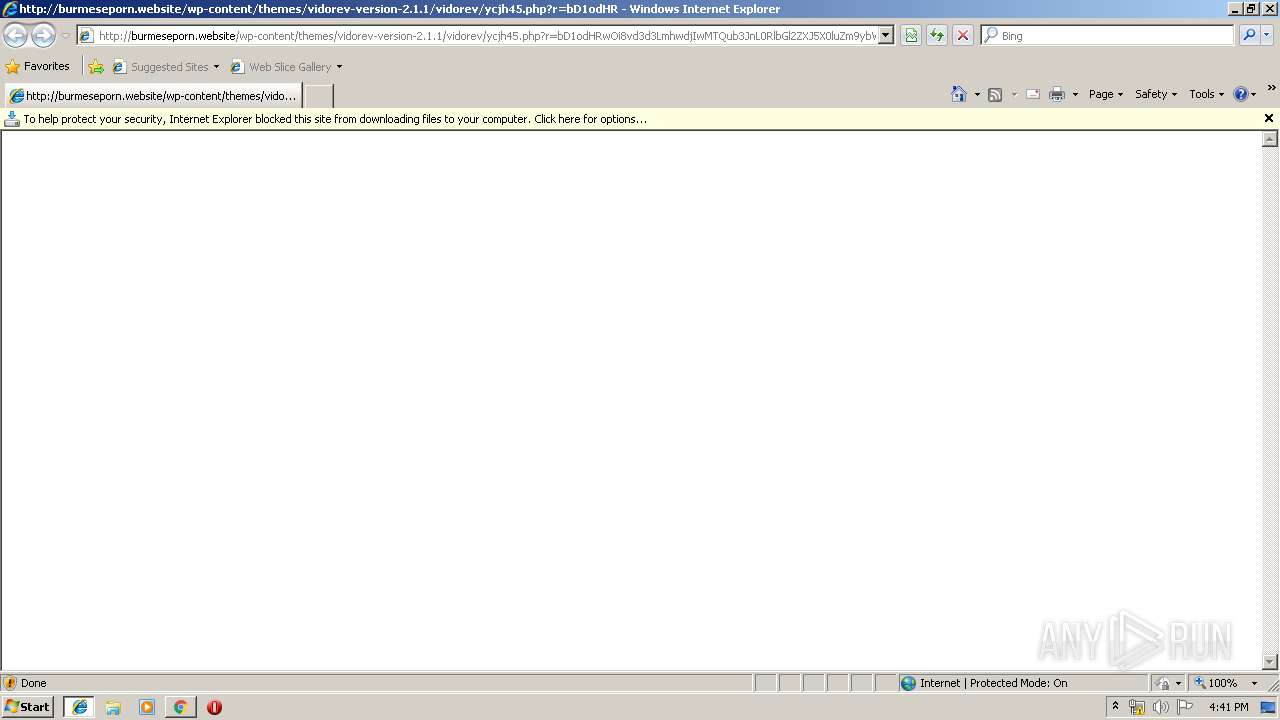
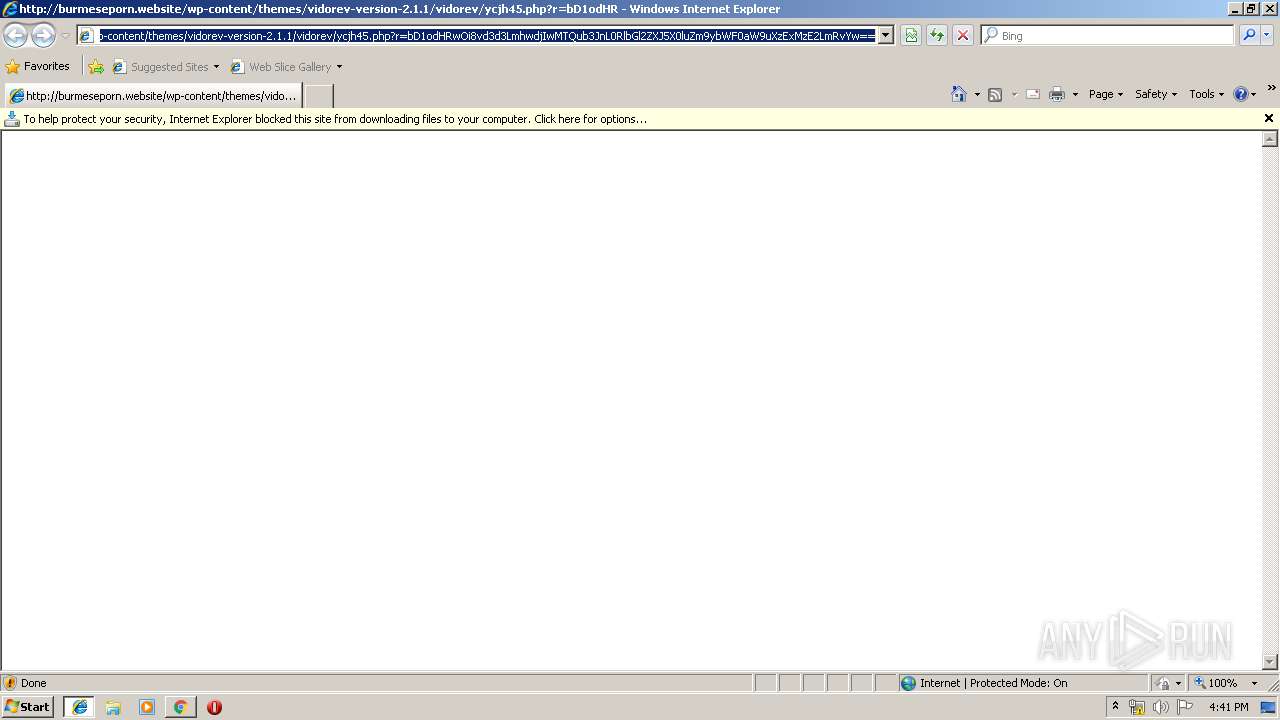
Changes internet zones settings
- iexplore.exe (PID: 2860)
Reads internet explorer settings
- iexplore.exe (PID: 2144)
Reads the hosts file
- chrome.exe (PID: 884)
- chrome.exe (PID: 2212)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1704)
- WINWORD.EXE (PID: 520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
34
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6952101467899169143 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9562409053787073277 --mojo-platform-channel-handle=4272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16790327570575362680 --mojo-platform-channel-handle=4152 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://burmeseporn.website/wp-content/themes/vidorev-version-2.1.1/vidorev/ycjh45.php?r=bD1odHRwOi8vd3d3LmhwdjIwMTQub3JnL0RlbGl2ZXJ5X0luZm9ybWF0aW9uXzExMzE2LmRvYw==" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=964 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3987731657156330084 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,314740921139912077,6852643483249543325,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16250562945057973919 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
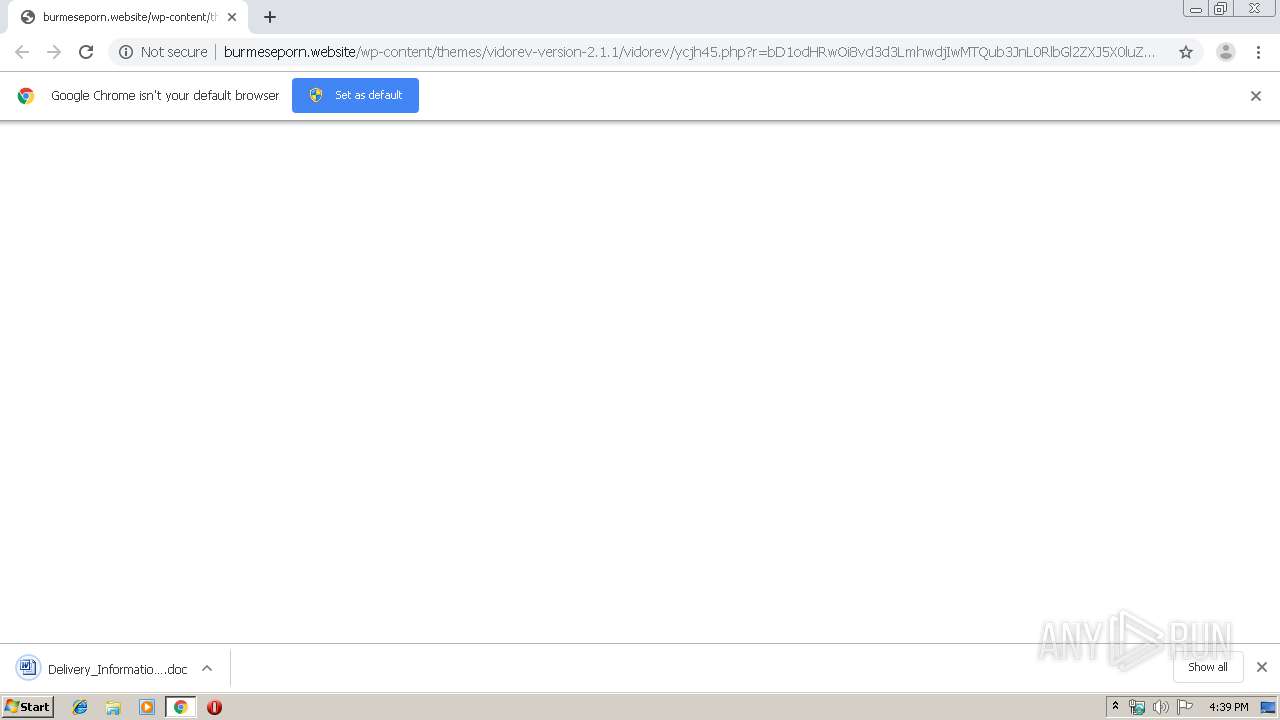
| 1704 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\Delivery_Information_11316.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1788 | C:\Windows\system32\dwwin.exe -x -s 404 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 709
Read events
3 025
Write events
469
Delete events
215
Modification events
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 884-13220123993953125 |
Value: 259 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (884) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
278
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0ac83f61-9db0-4fd5-aae7-f95fcda78046.tmp | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a92b.TMP | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 884 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
31
DNS requests
23
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2212 | chrome.exe | GET | 200 | 156.67.222.189:80 | http://burmeseporn.website/wp-content/themes/ | CY | — | — | malicious |
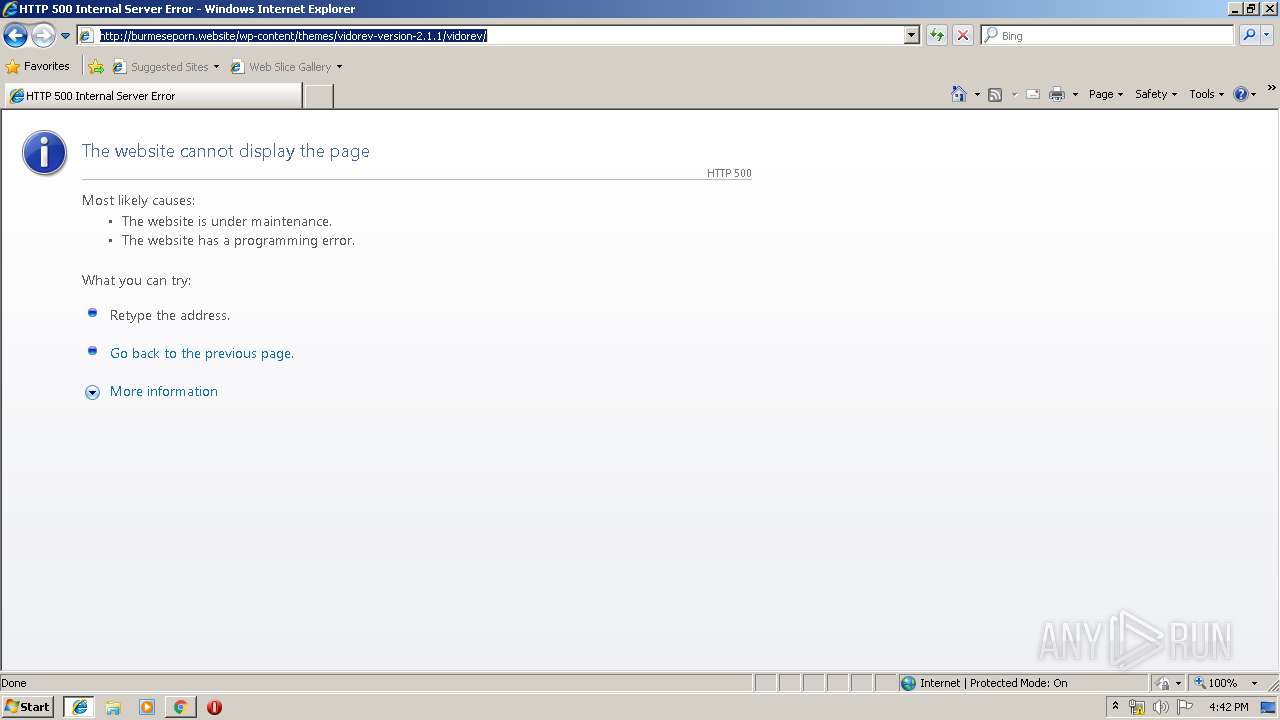
2144 | iexplore.exe | GET | — | 156.67.222.189:80 | http://burmeseporn.website/wp-content/themes/vidorev-version-2.1.1/vidorev/ycjh45.php?r=bD1odHRwOi8vd3d3LmhwdjIwMTQub3JnL0RlbGl2ZXJ5X0luZm9ybWF0aW9uXzExMzE2LmRvYw== | CY | — | — | malicious |
2144 | iexplore.exe | GET | — | 185.13.42.55:80 | http://www.hpv2014.org/Delivery_Information_11316.doc | GB | — | — | unknown |
2144 | iexplore.exe | GET | 500 | 156.67.222.189:80 | http://burmeseporn.website/wp-content/themes/vidorev-version-2.1.1/vidorev/ | CY | — | — | malicious |
2212 | chrome.exe | GET | 200 | 185.13.42.55:80 | http://www.hpv2014.org/Delivery_Information_11316.doc | GB | document | 649 Kb | unknown |
2212 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
2212 | chrome.exe | GET | 200 | 156.67.222.189:80 | http://burmeseporn.website/favicon.ico | CY | — | — | malicious |
2212 | chrome.exe | GET | 200 | 185.180.12.140:80 | http://r1---sn-n02xgoxufvg3-8pxe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.183.107.227&mm=28&mn=sn-n02xgoxufvg3-8pxe&ms=nvh&mt=1575650295&mv=m&mvi=0&pl=24&shardbypass=yes | AT | crx | 862 Kb | whitelisted |
2860 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2212 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 534 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 156.67.222.189:80 | burmeseporn.website | Hostinger International Limited | CY | malicious |
2212 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.18.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 185.13.42.55:80 | www.hpv2014.org | Portlane AB | GB | unknown |
2212 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.23.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2212 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
burmeseporn.website |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.hpv2014.org |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r2---sn-n02xgoxufvg3-8pxe.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2212 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |