| File name: | CRICFy_v5.6.apk |
| Full analysis: | https://app.any.run/tasks/c1bb16de-dc14-4010-8048-0392e74f0941 |
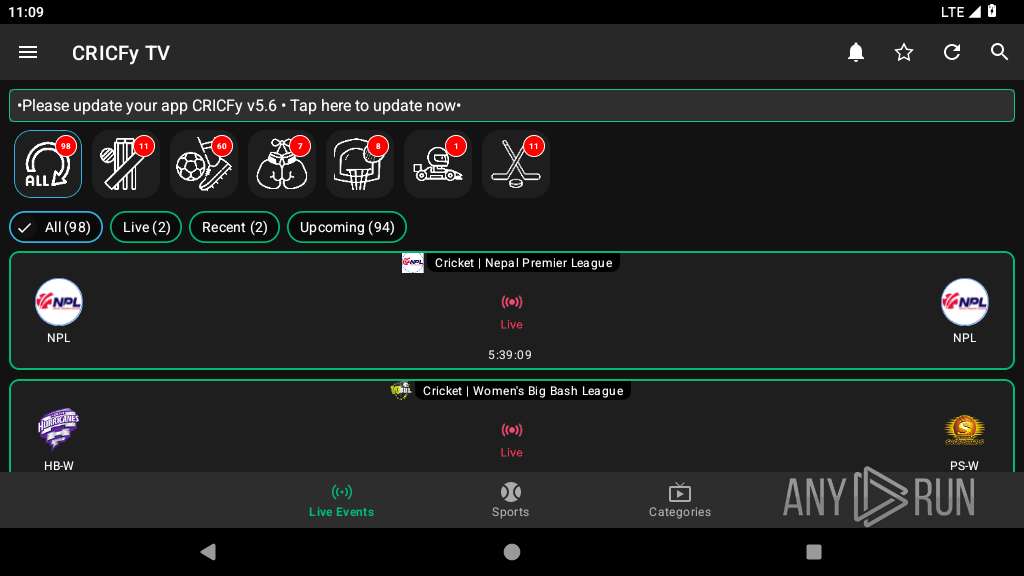
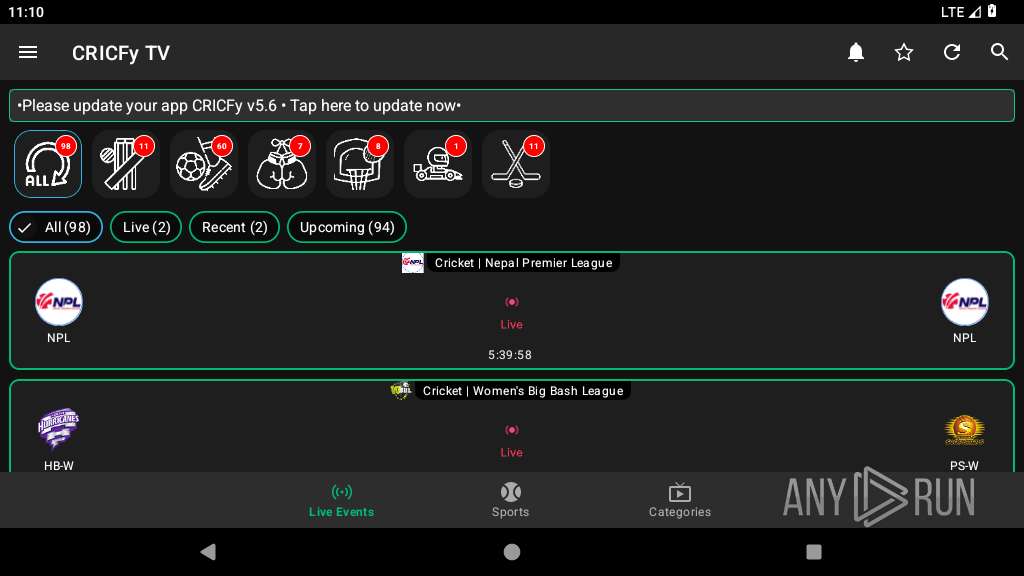
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2025, 11:08:42 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with AndroidManifest.xml |
| MD5: | E434BFD05FD5EF38667AE12968B58A14 |
| SHA1: | 73C933B9B8DDD1E07C7A77B148F44EEBCB5FA732 |
| SHA256: | BB20F076894B26A4E0EFB98192AE4CE9809E4C00ED535D505B099452F5A0A86F |
| SSDEEP: | 196608:IeV3YFr99gjMdTZAKaOyIgOou3CahznZ/Ws5JD7S6+w3CB1:Iv9RdNA97O/3CMznZ/Wop7BP381 |
MALICIOUS
PHISHING has been detected (SURICATA)
- netd (PID: 339)
SUSPICIOUS
Acquires a wake lock to keep the device awake
- app_process64 (PID: 2840)
Creates a WakeLock to manage power state
- app_process64 (PID: 2840)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 2840)
Accesses system-level resources
- app_process64 (PID: 2840)
Retrieves Android OS build information
- app_process64 (PID: 2840)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 2840)
Abuses foreground service for persistence
- app_process64 (PID: 2840)
Returns the name of the current network operator
- app_process64 (PID: 2840)
Uses encryption API functions
- app_process64 (PID: 2840)
Checks for external IP
- netd (PID: 339)
Connects to unusual port
- app_process64 (PID: 2840)
Launches a new activity
- app_process64 (PID: 2840)
Connects to SMTP port
- app_process64 (PID: 2840)
Executes dynamic code using class loader
- app_process64 (PID: 2840)
Establishing a connection
- app_process64 (PID: 2840)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 2840)
Loads a native library into the application
- app_process64 (PID: 2840)
Dynamically loads a class in Java
- app_process64 (PID: 2840)
Returns elapsed time since boot
- app_process64 (PID: 2840)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 2840)
Handles throwable exceptions in the app
- app_process64 (PID: 2840)
Stores data using SQLite database
- app_process64 (PID: 2840)
Verifies whether the device is connected to the internet
- app_process64 (PID: 2840)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 2840)
Checks if Wi-Fi is enabled
- app_process64 (PID: 2840)
Gets file name without full path
- app_process64 (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (62.8) |
|---|---|---|
| .jar | | | Java Archive (17.3) |
| .vym | | | VYM Mind Map (14.9) |
| .zip | | | ZIP compressed archive (4.7) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:11:22 12:19:32 |
| ZipCRC: | 0x02b2dc0f |
| ZipCompressedSize: | 8728 |
| ZipUncompressedSize: | 47788 |
| ZipFileName: | AndroidManifest.xml |
Total processes
134
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 339 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2840 | com.cricfy.tv | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2874 | cat /proc/self/status | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3066 | getprop | /system/bin/toolbox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3073 | ps -ef | /system/bin/toybox | — | app_process64 |
User: u0_a108 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3109 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3112 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3143 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 3168 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
79
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | app_process64 | /data/data/com.cricfy.tv/.jiagu/libjiagu.so | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/.jiagu/libjiagu_64.so | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/files/jgobfppppp | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/files/.jglogs/.jg.ri | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/files/.jglogs/.jg.store.report_pid | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/.oabugaij/.fsgkea | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/shared_prefs/com.google.firebase.messaging.xml | xml | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/files/.jglogs/.jg.store.report_cf | binary | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/shared_prefs/FirebaseHeartBeatW0RFRkFVTFRd+MTo5NjMwMjAyMTg1MzU6YW5kcm9pZDo0N2VjNTMyNTJjNjRmYjNjOWM3Yjgy.xml | xml | |
MD5:— | SHA256:— | |||
| 2840 | app_process64 | /data/data/com.cricfy.tv/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
48
DNS requests
41
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.185.68:80 | http://www.google.com/gen_204 | US | — | — | whitelisted |
822 | app_process64 | GET | 204 | 216.58.206.67:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
2840 | app_process64 | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json/?fields=66842623&lang=en | US | binary | 504 b | unknown |
2840 | app_process64 | GET | — | 142.250.185.68:80 | http://www.google.com/ | US | — | — | whitelisted |
2840 | app_process64 | GET | 200 | 208.95.112.1:80 | http://208.95.112.1:80/json | US | binary | 352 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
443 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.185.68:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
2840 | app_process64 | 142.250.185.234:443 | firebaseinstallations.googleapis.com | GOOGLE | US | whitelisted |
822 | app_process64 | 216.58.206.67:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
822 | app_process64 | 142.250.185.68:443 | www.google.com | GOOGLE | US | whitelisted |
1756 | app_process64 | 142.250.27.129:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
571 | app_process64 | 216.239.35.12:123 | time.android.com | GOOGLE | US | whitelisted |
2840 | app_process64 | 142.250.184.202:443 | firebaseinstallations.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
firebaseinstallations.googleapis.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
firebaseremoteconfigrealtime.googleapis.com |
| whitelisted |
dns.google |
| whitelisted |
ip-api.com |
| whitelisted |
ipv6.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
822 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
339 | netd | Misc activity | INFO [ANY.RUN] Google DNS-over-HTTPS service requested (dns. google) |
2840 | app_process64 | A Network Trojan was detected | ET HUNTING Terse Unencrypted Request for Google - Likely Connectivity Check |
2840 | app_process64 | Misc activity | ET INFO Google DNS Over HTTPS Certificate Inbound |
339 | netd | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
339 | netd | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
339 | netd | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
339 | netd | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
339 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
339 | netd | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing |