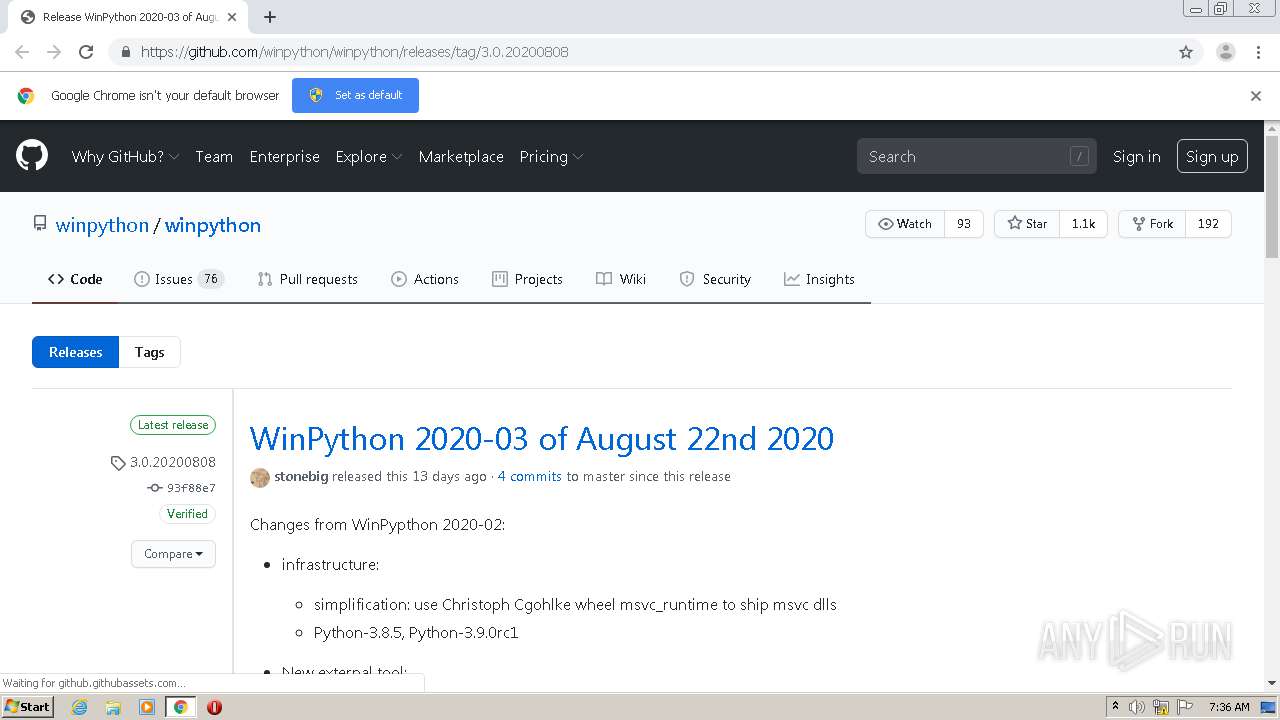
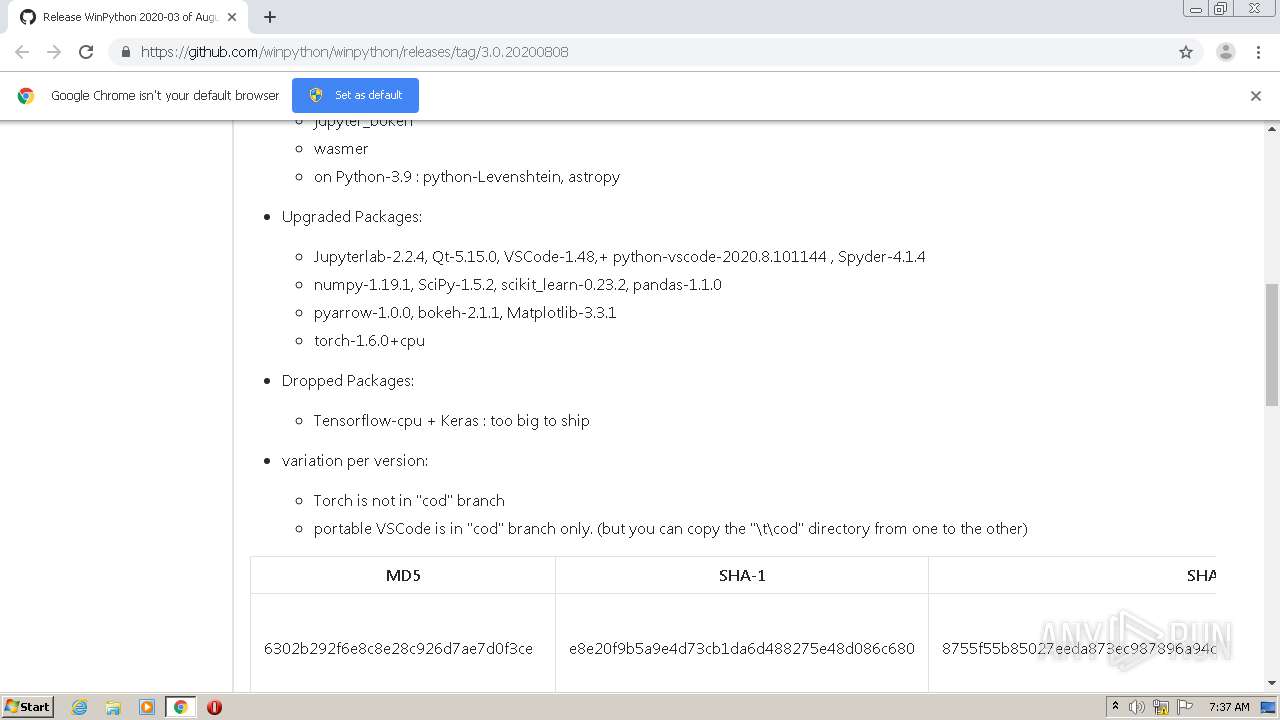
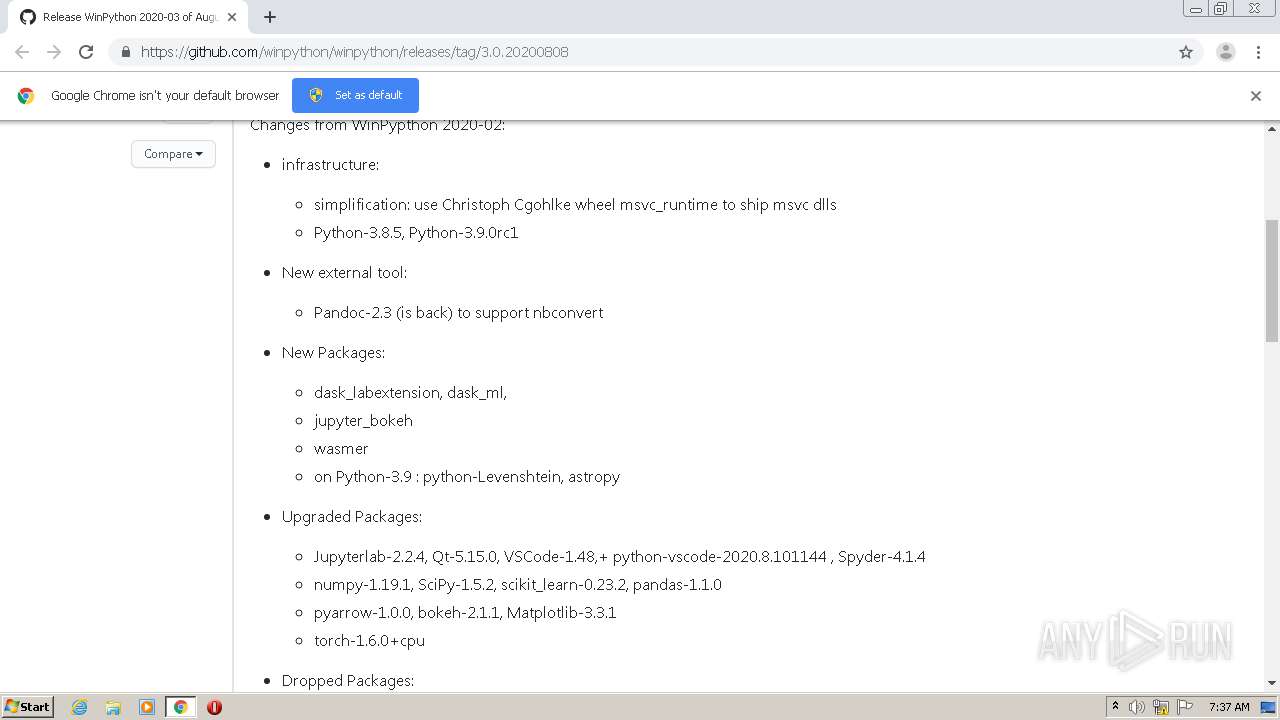
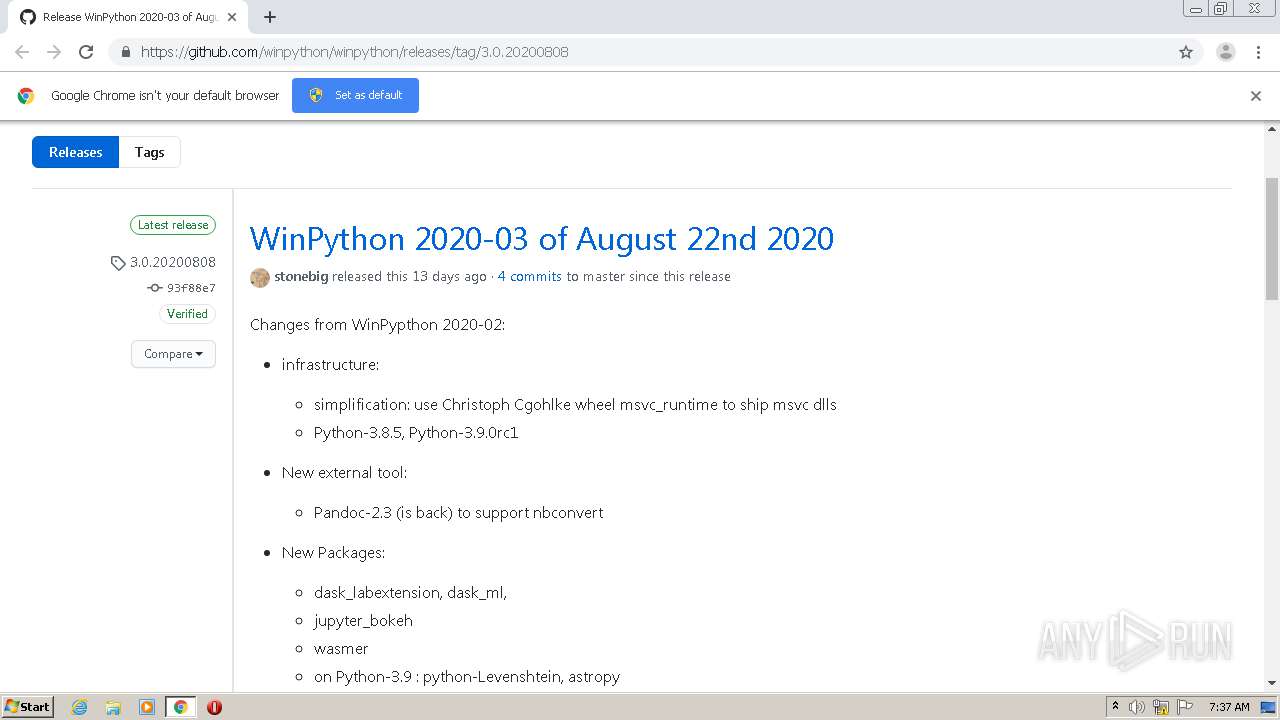
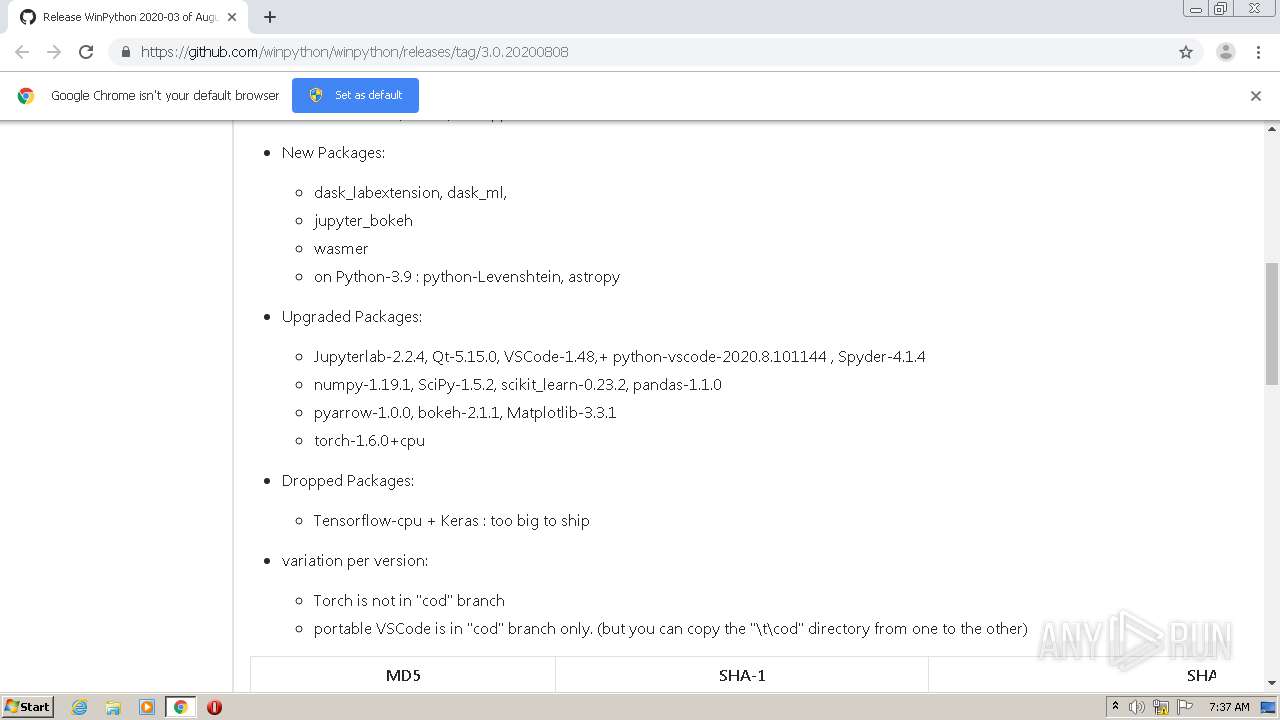
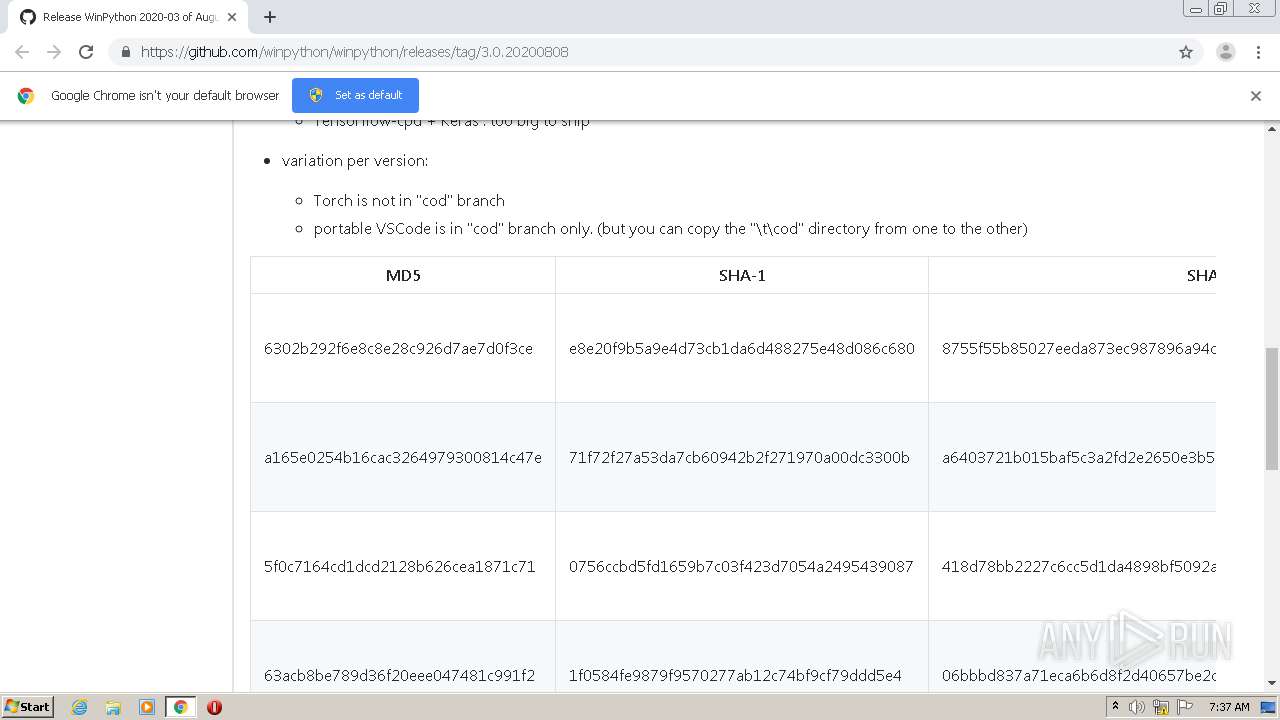
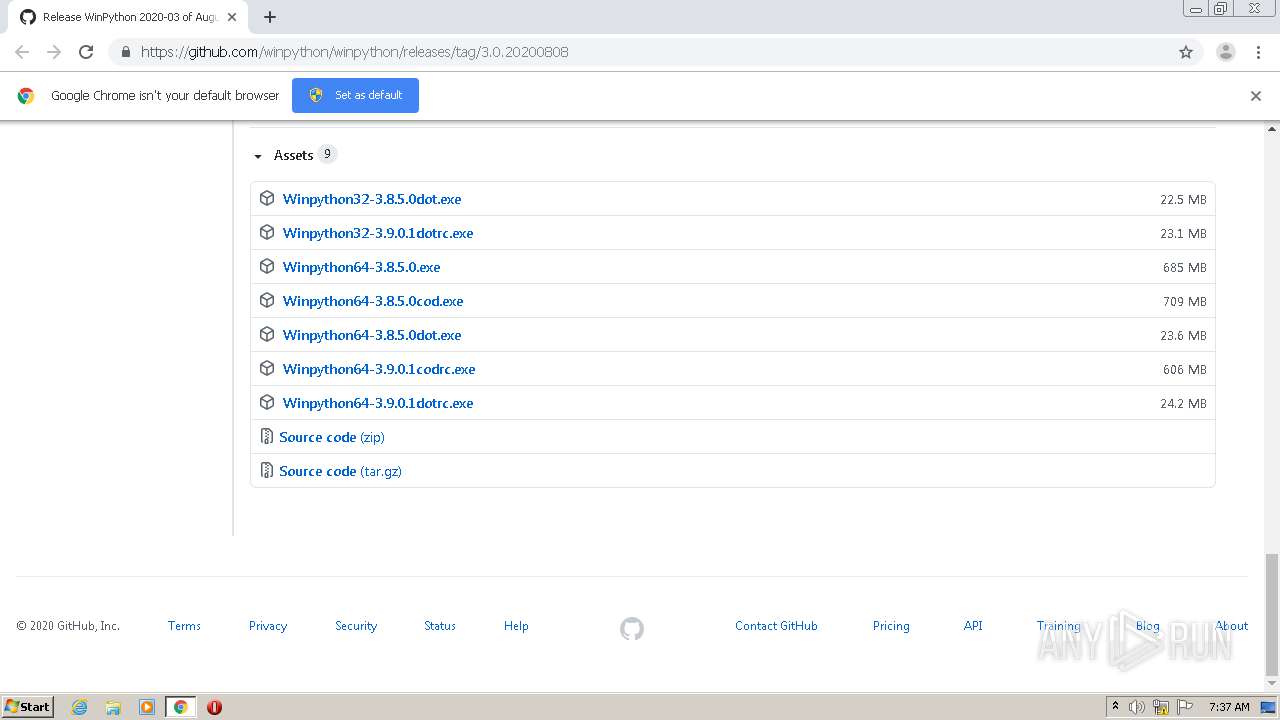
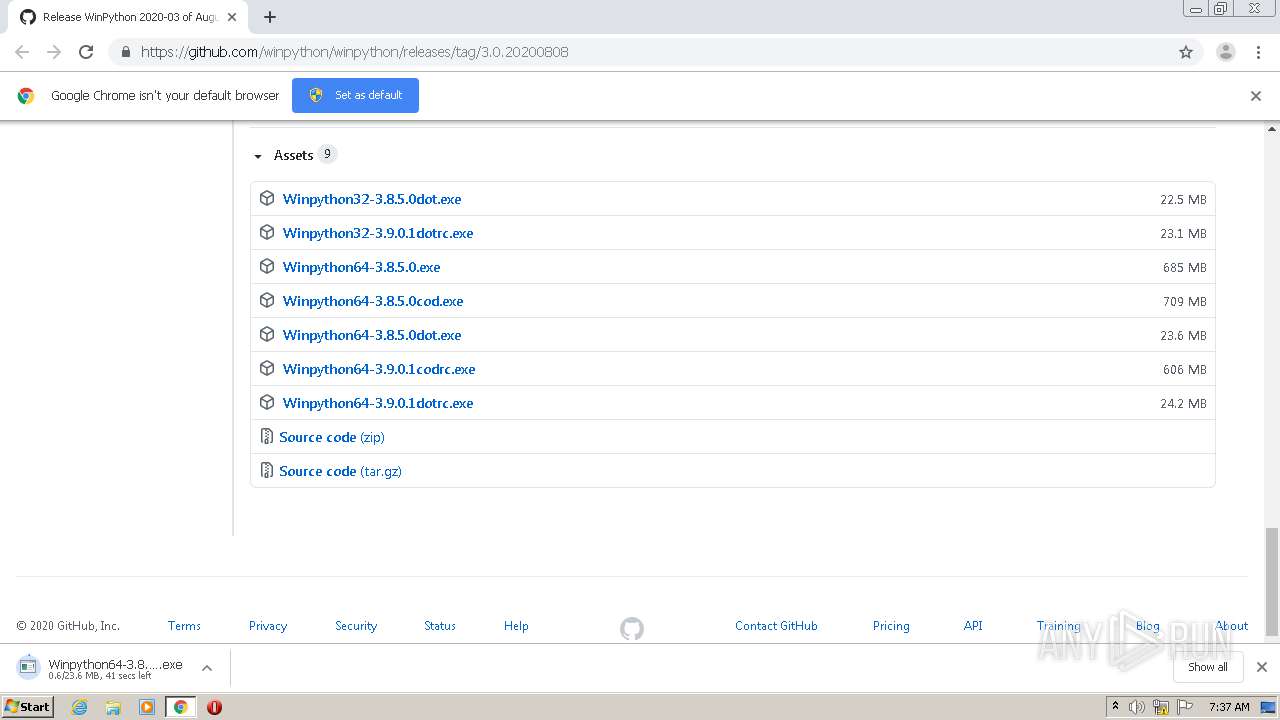
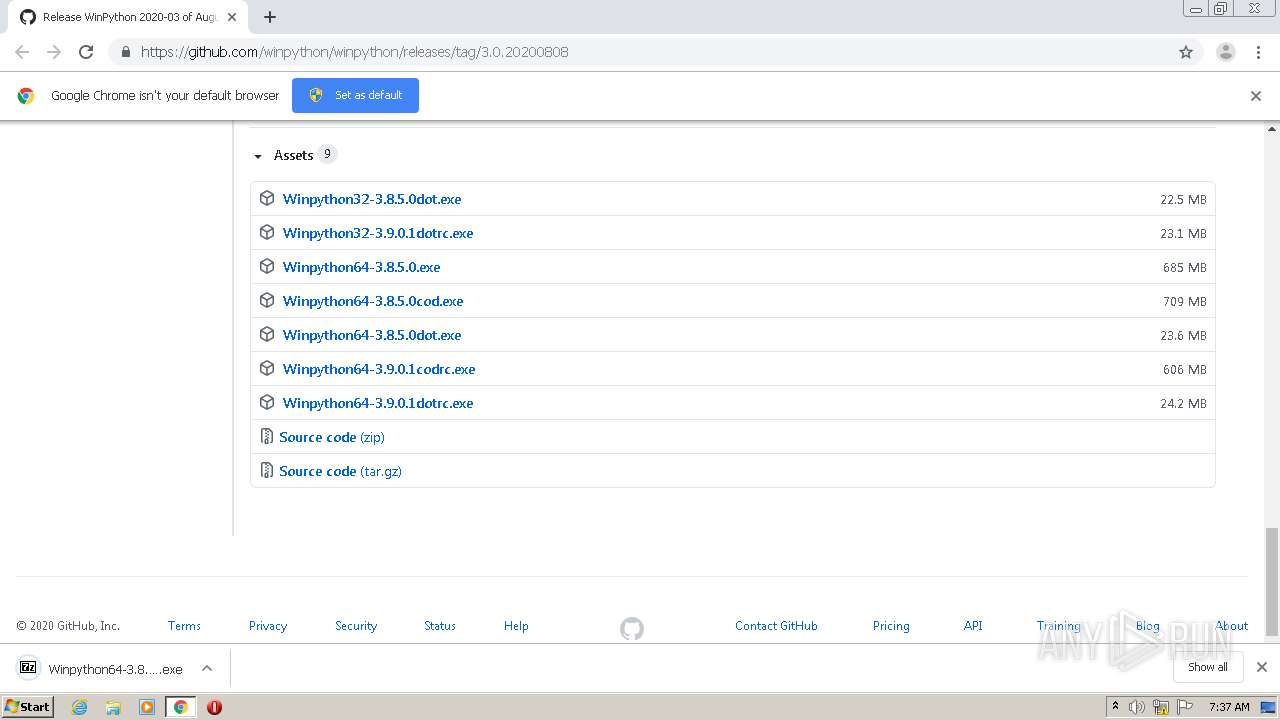
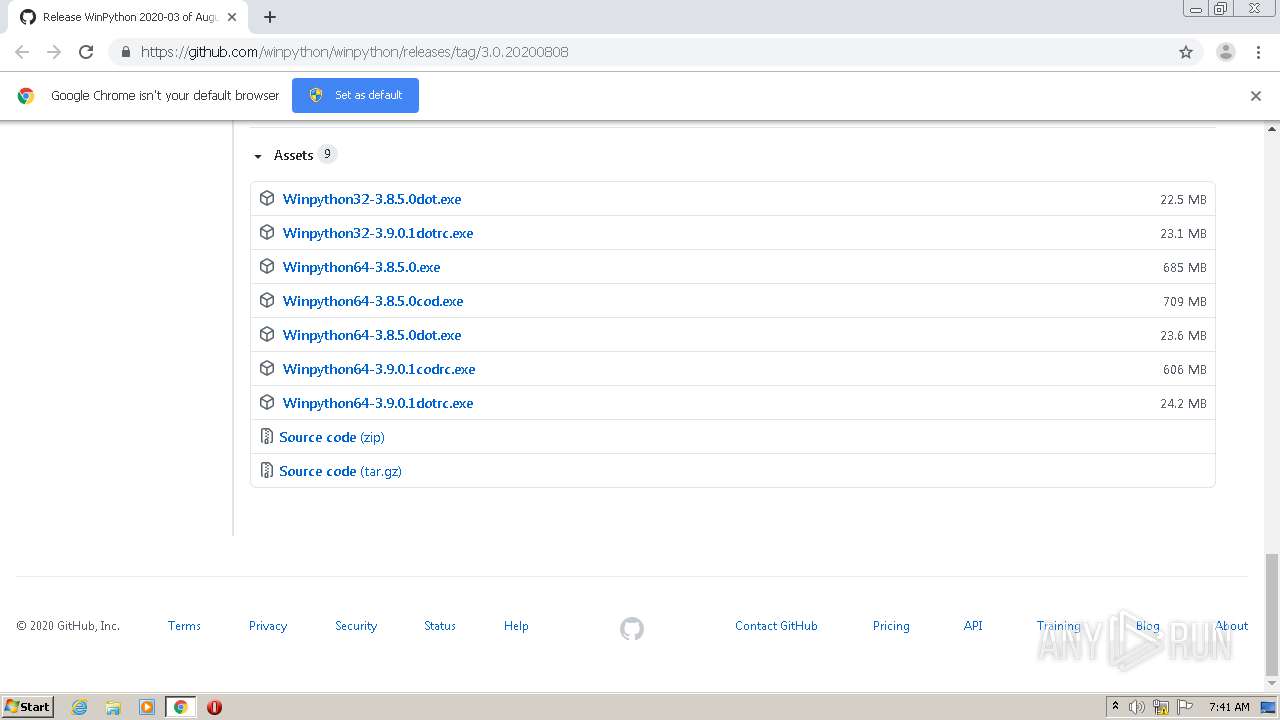
| URL: | https://github.com/winpython/winpython/releases/tag/3.0.20200808 |
| Full analysis: | https://app.any.run/tasks/76507c62-3caf-49aa-b77f-6994d345cfec |
| Verdict: | Malicious activity |
| Analysis date: | September 04, 2020, 06:35:53 |
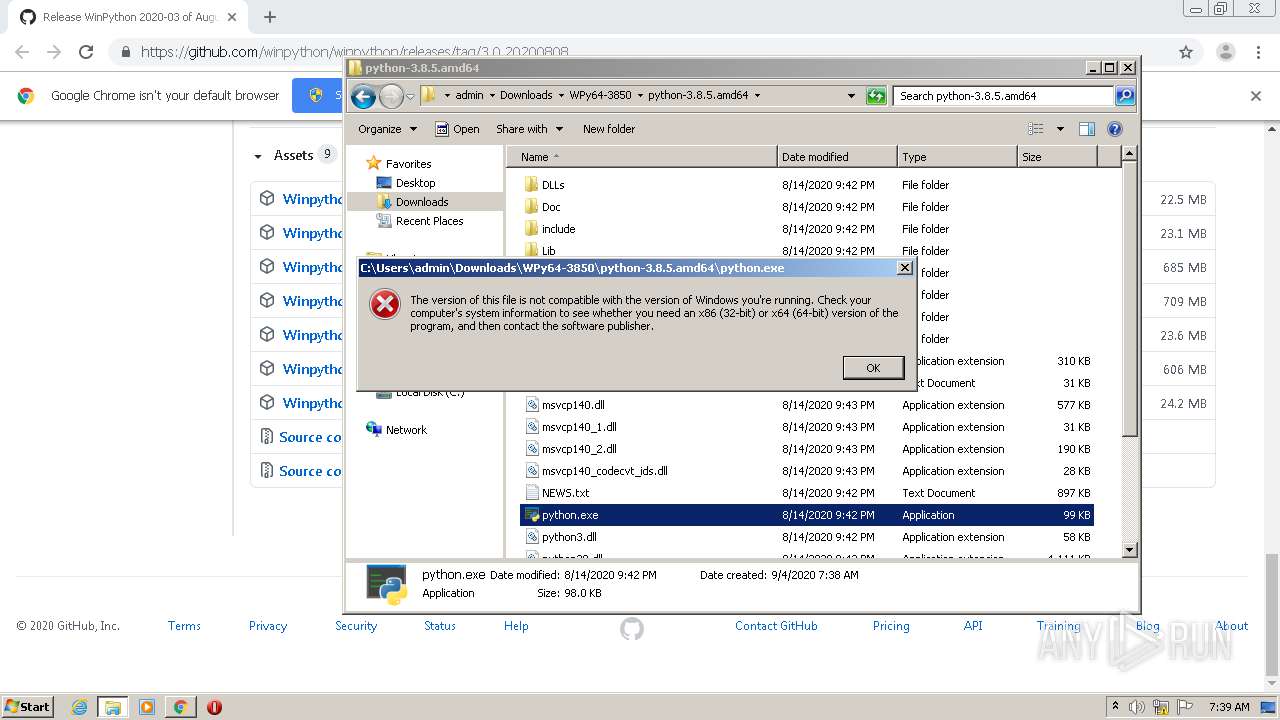
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EDD7835A4EF065FFA759E57A78B910ED |
| SHA1: | 6B2DFE9F05E88AF100F5F06C7ACC3EE4AA26089D |
| SHA256: | BB0B10C32CD488414174EECADE3A440BC1CB2E4B9F9084B2A4E8DA7AFCF0B4E6 |
| SSDEEP: | 3:N8tEdiMNLJK2eLMsMqKk3VN:2u04JK2U/MxkX |
MALICIOUS
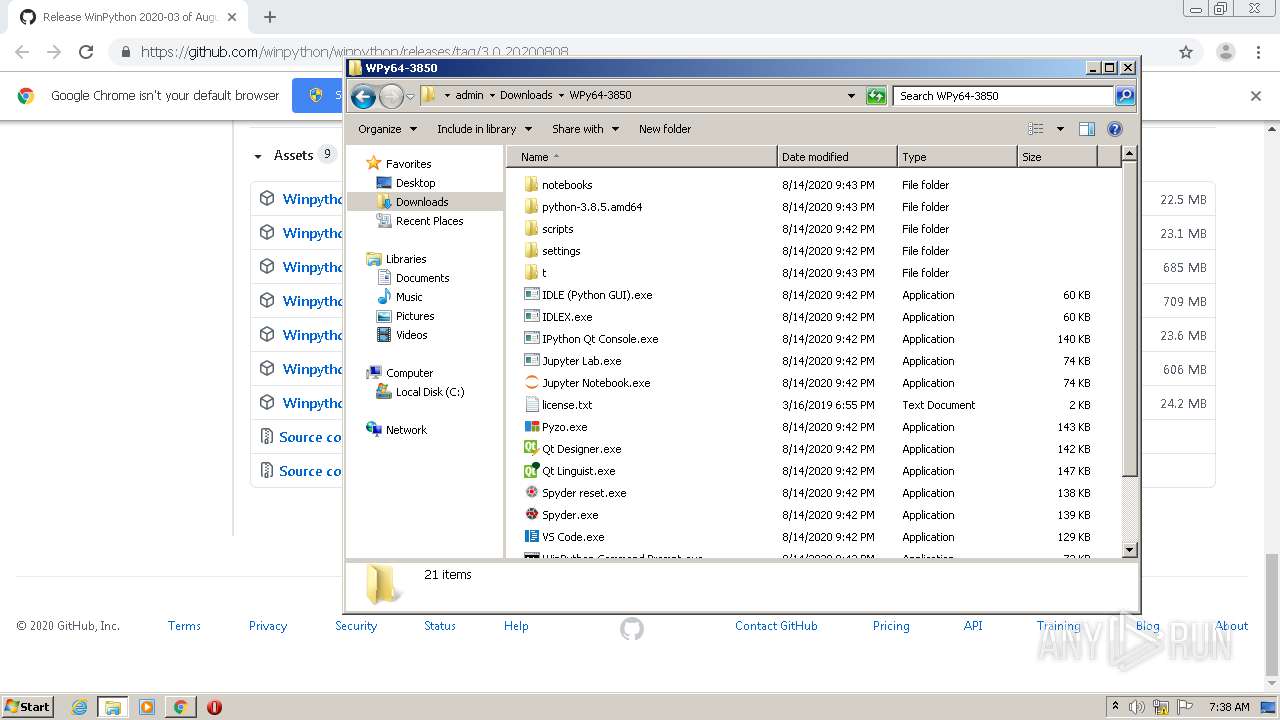
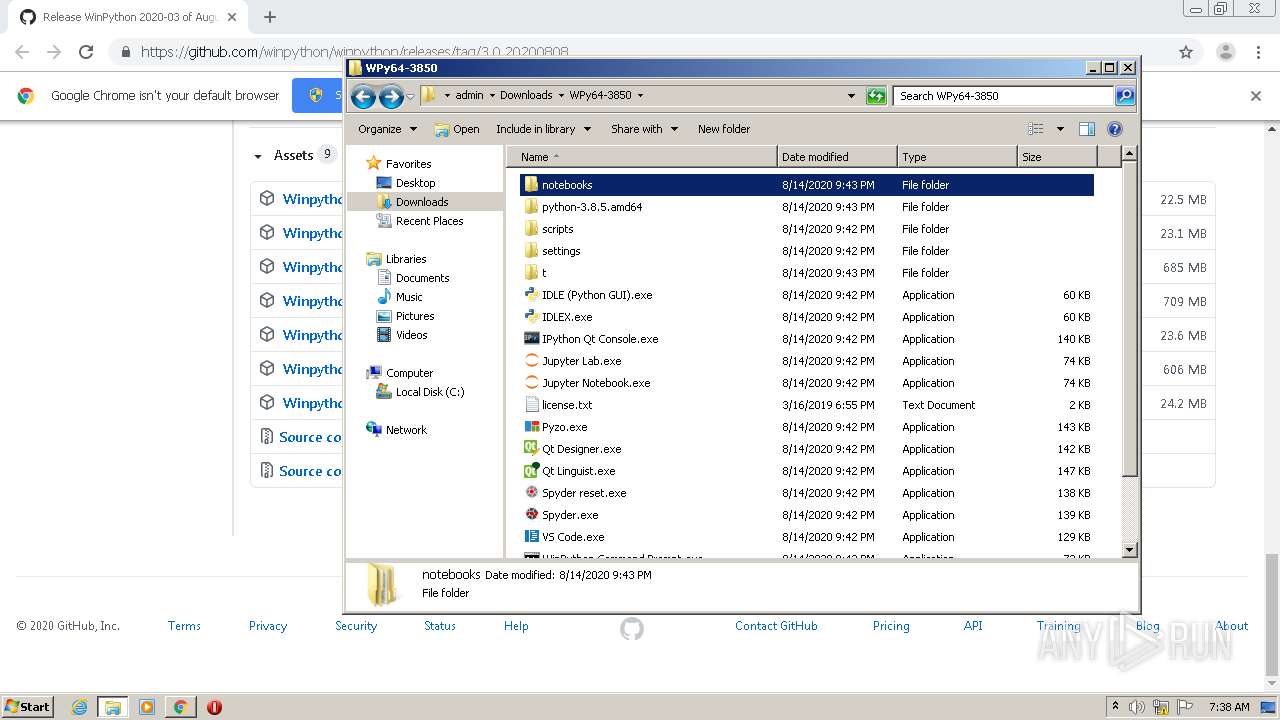
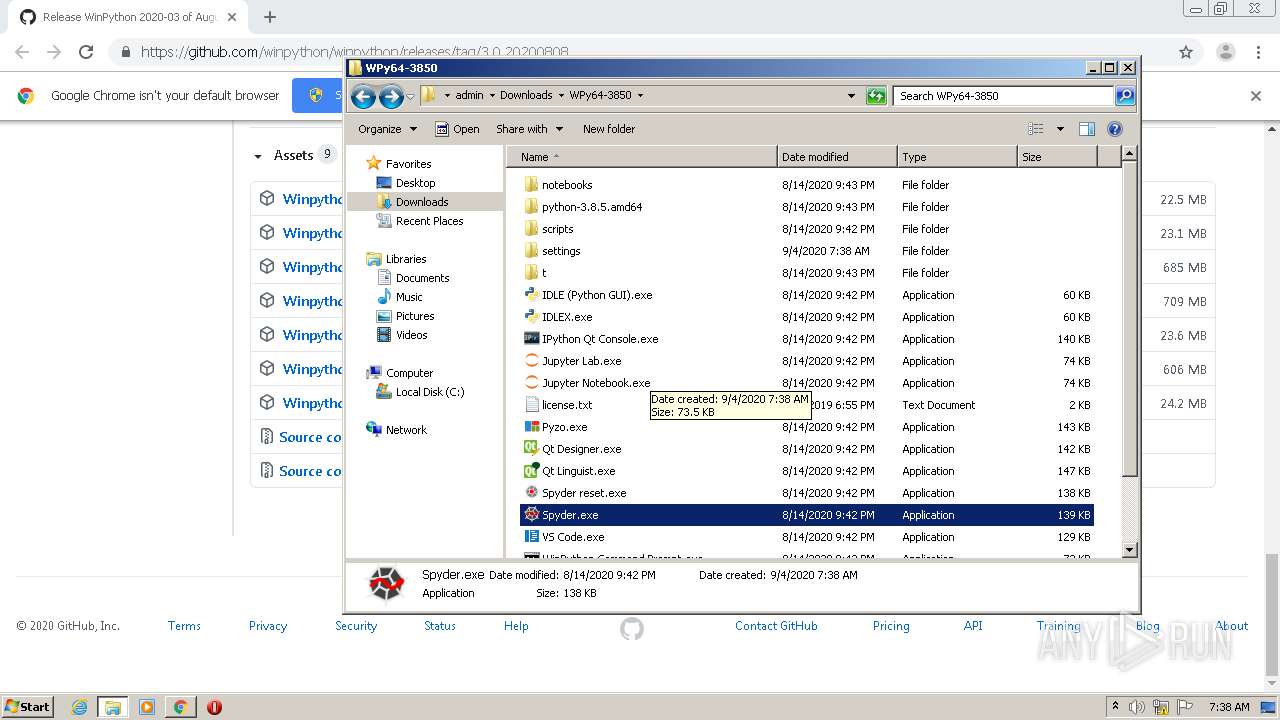
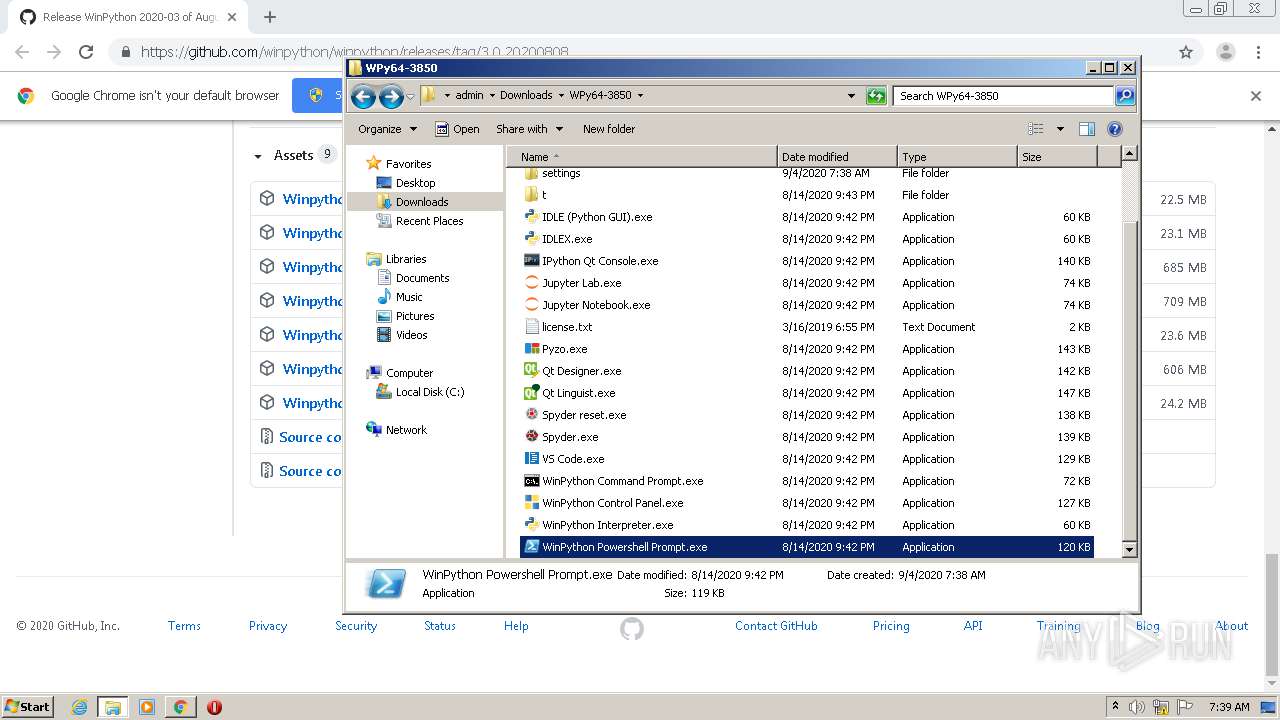
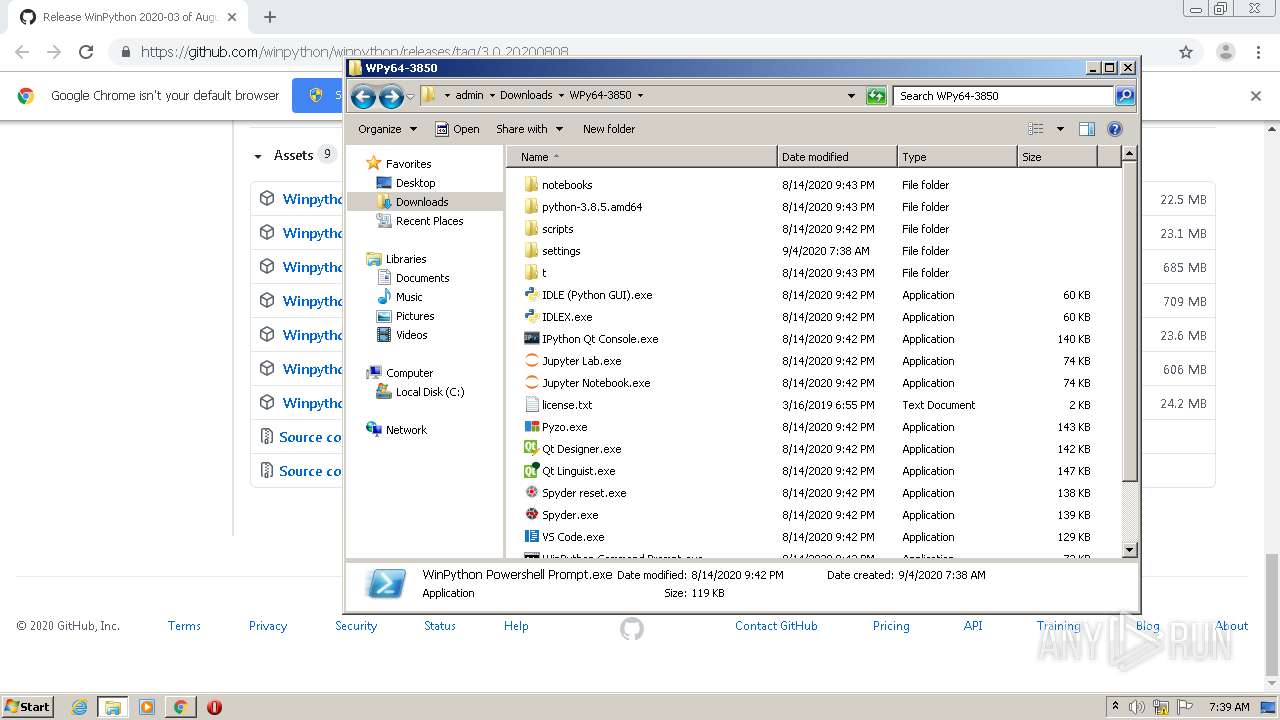
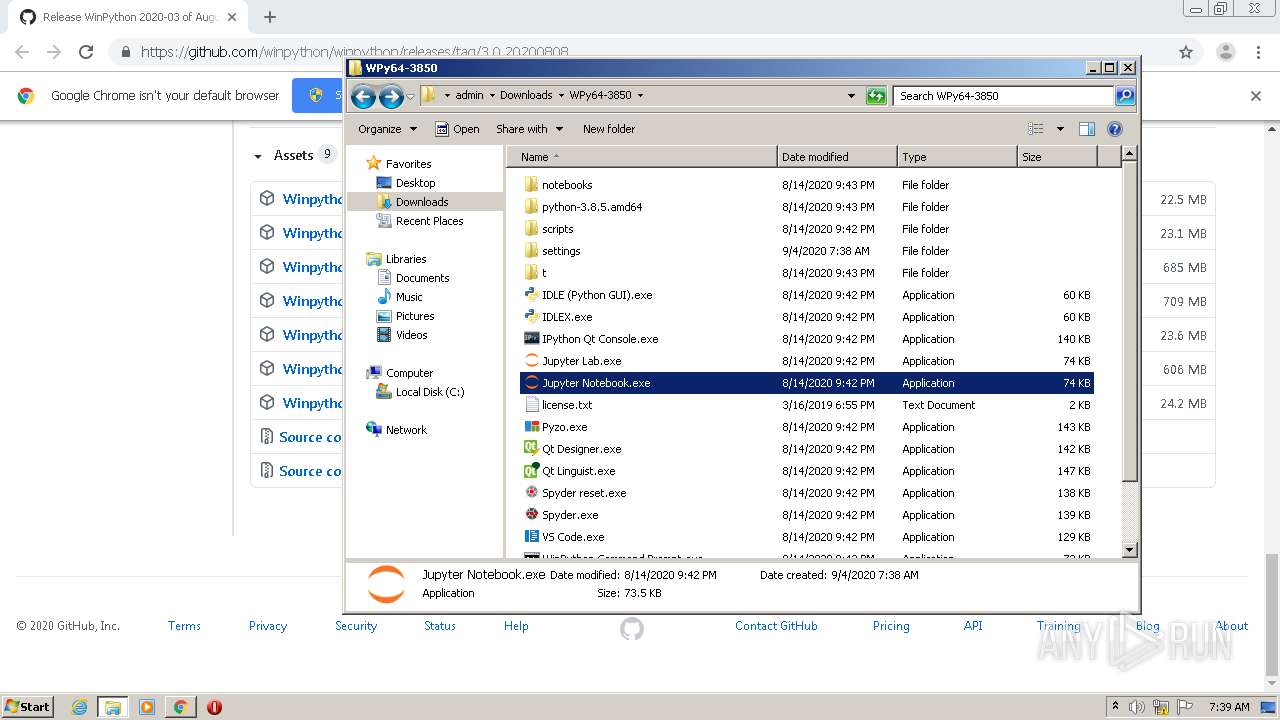
Application was dropped or rewritten from another process
- Spyder.exe (PID: 2608)
- Spyder.exe (PID: 1884)
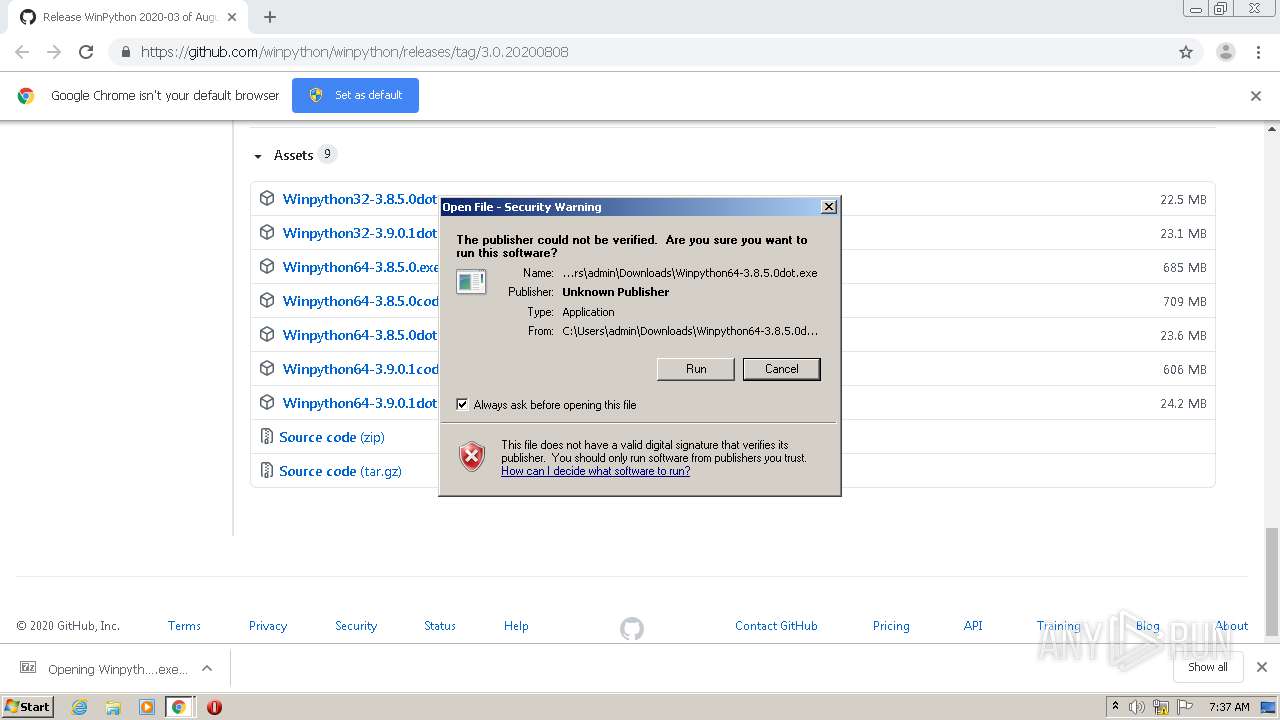
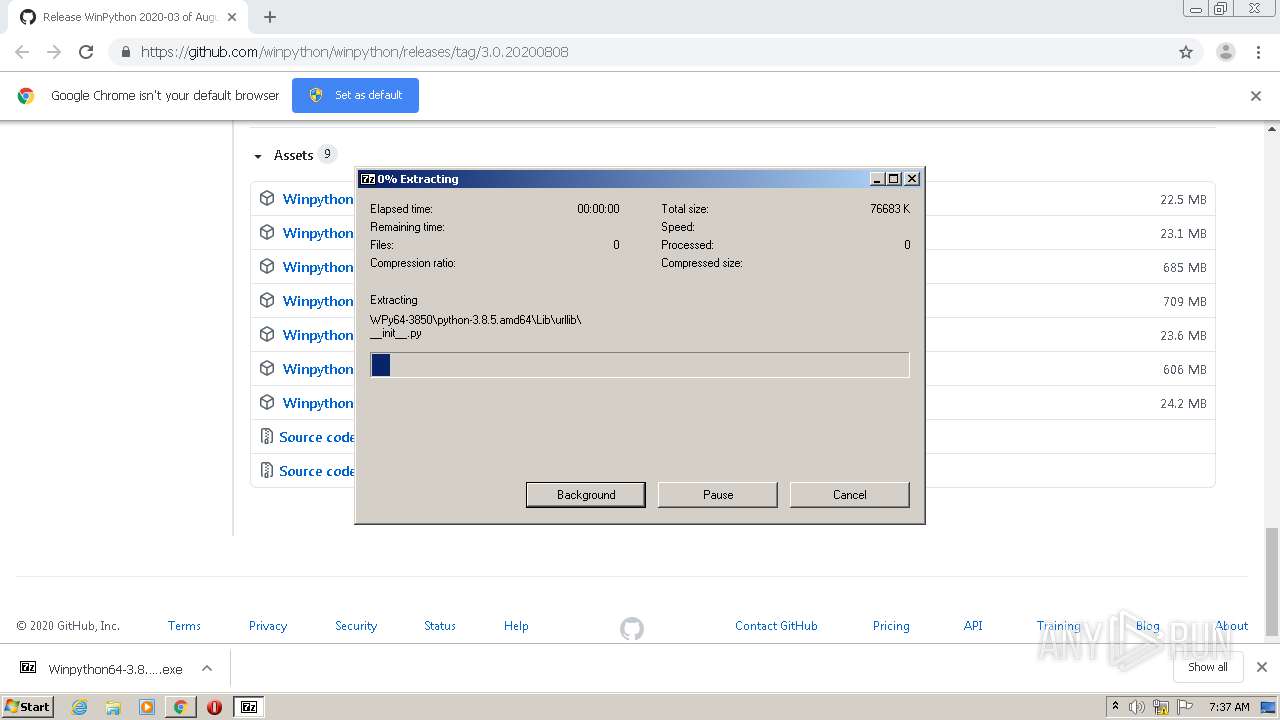
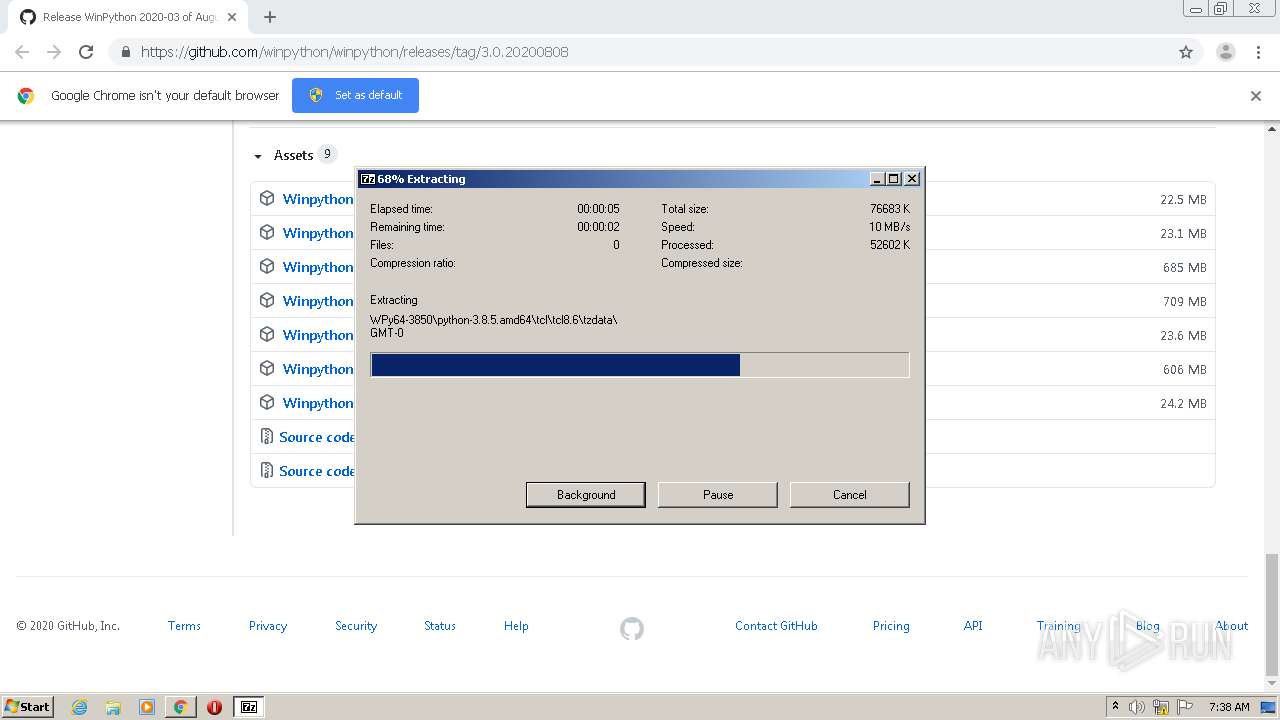
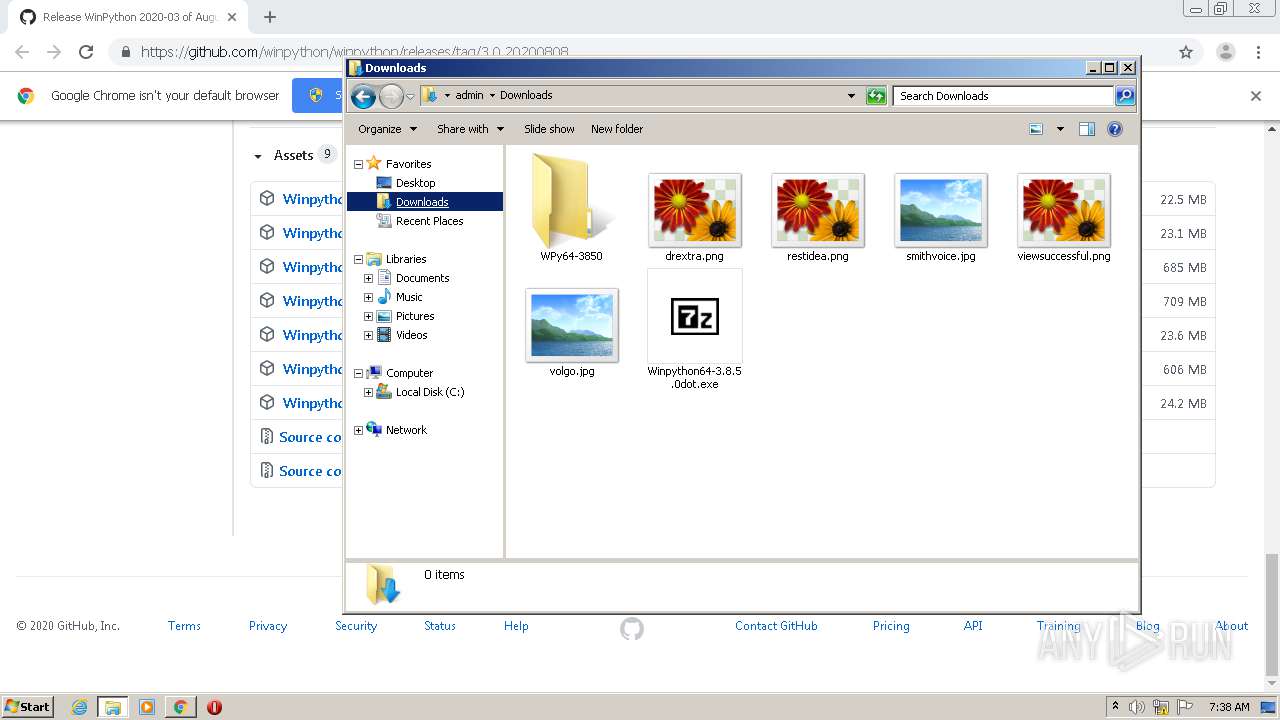
- Winpython64-3.8.5.0dot.exe (PID: 2572)
- Pyzo.exe (PID: 1120)
- WinPython Powershell Prompt.exe (PID: 1436)
- Jupyter Notebook.exe (PID: 4076)
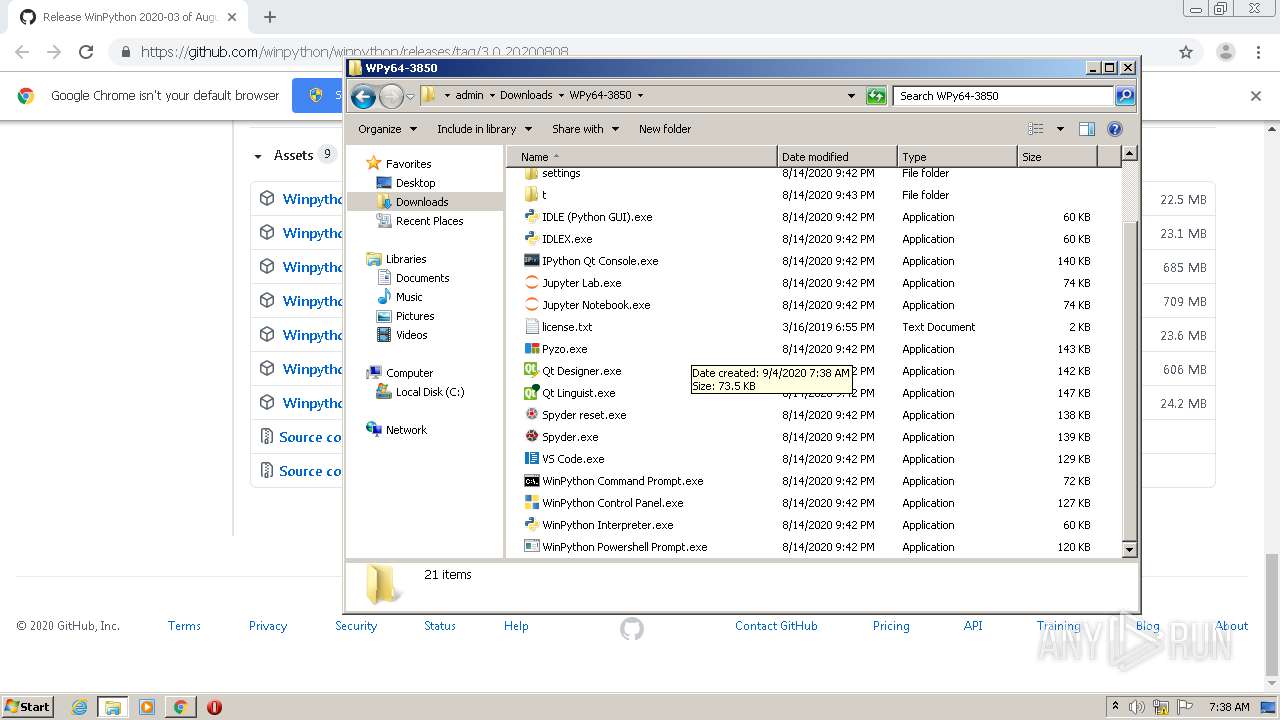
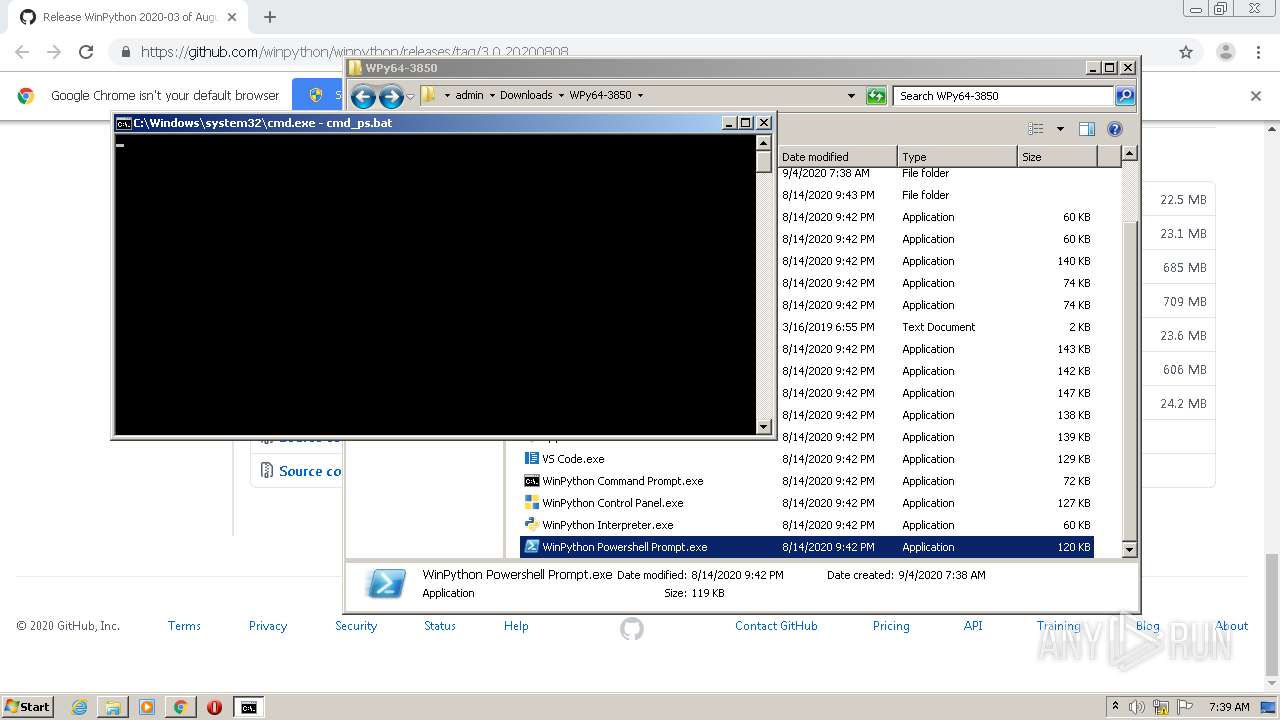
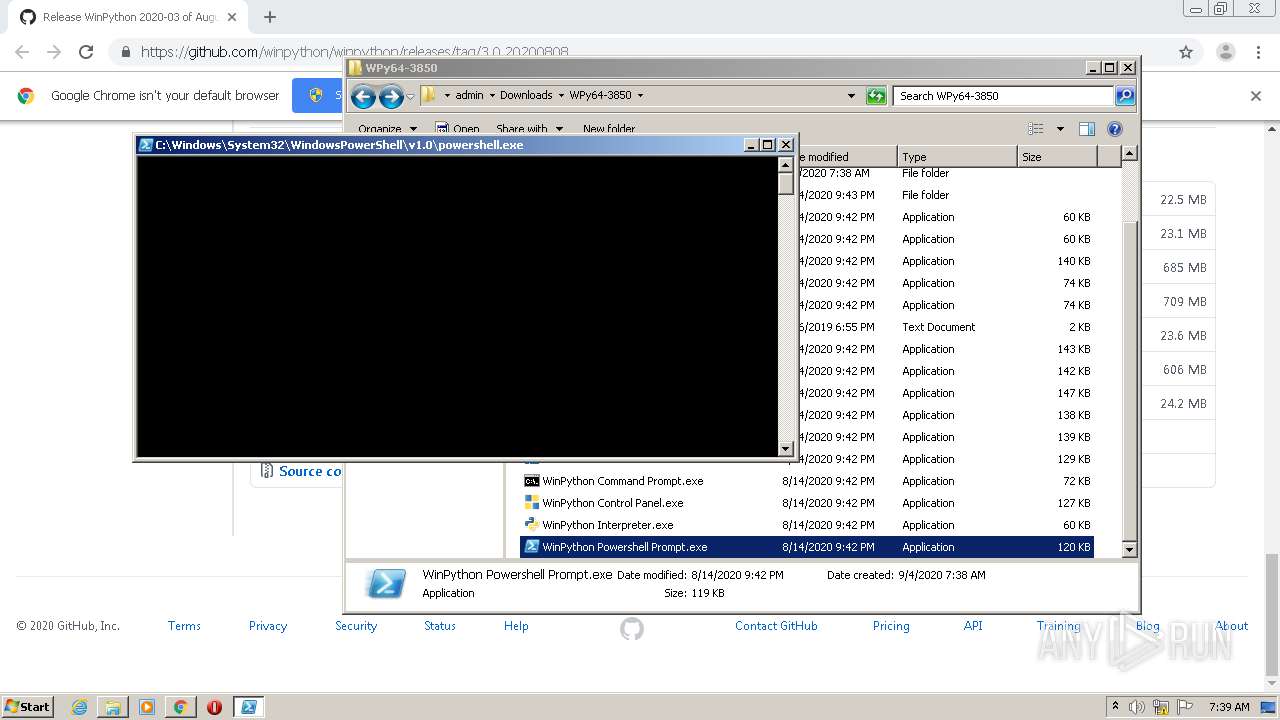
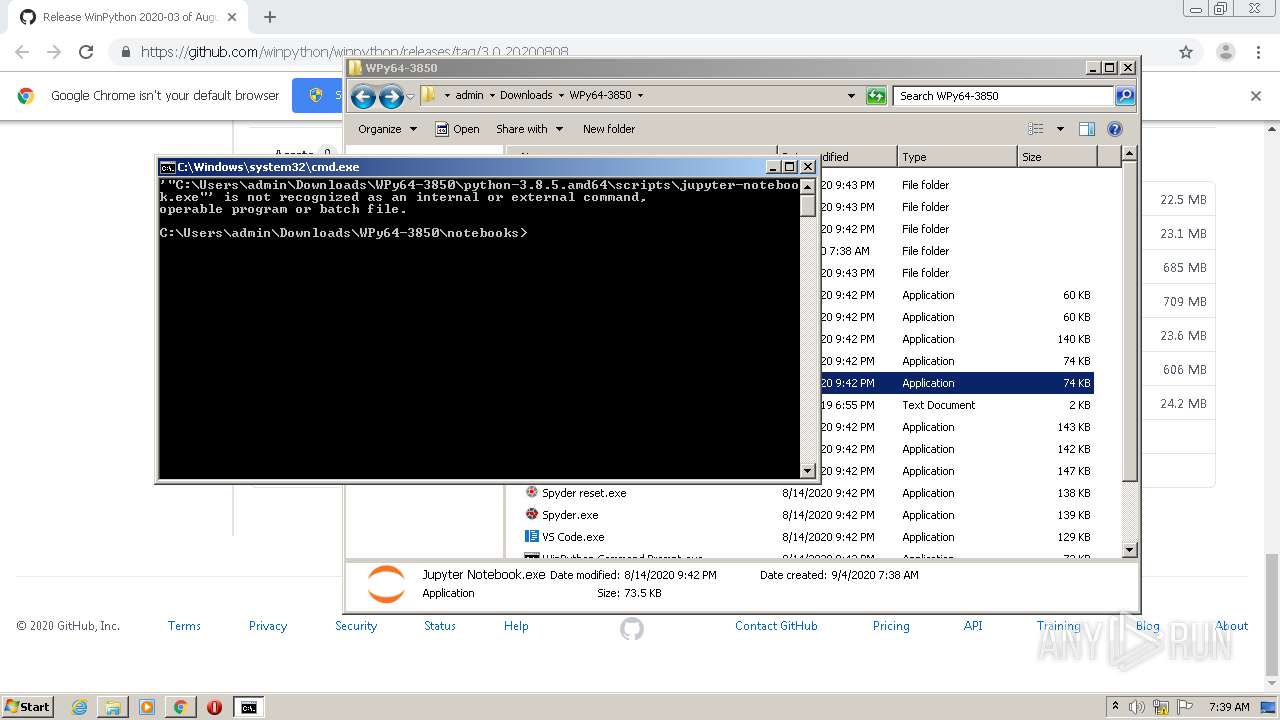
Executes PowerShell scripts
- cmd.exe (PID: 500)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1560)
- chrome.exe (PID: 448)
- Winpython64-3.8.5.0dot.exe (PID: 2572)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2200)
- wscript.exe (PID: 2196)
- cmd.exe (PID: 2192)
- wscript.exe (PID: 348)
- cmd.exe (PID: 2552)
- WinPython Powershell Prompt.exe (PID: 1436)
- cmd.exe (PID: 500)
- Jupyter Notebook.exe (PID: 4076)
- cmd.exe (PID: 1440)
- wscript.exe (PID: 2588)
Executes scripts
- cmd.exe (PID: 2968)
- Spyder.exe (PID: 1884)
- Spyder.exe (PID: 2608)
- cmd.exe (PID: 3168)
- cmd.exe (PID: 3084)
- cmd.exe (PID: 1432)
- cmd.exe (PID: 2816)
- Pyzo.exe (PID: 1120)
Application launched itself
- cmd.exe (PID: 2200)
- cmd.exe (PID: 2192)
- cmd.exe (PID: 2552)
- cmd.exe (PID: 500)
- powershell.exe (PID: 3016)
- cmd.exe (PID: 1440)
Creates files in the user directory
- powershell.exe (PID: 3016)
- powershell.exe (PID: 2976)
Executes PowerShell scripts
- powershell.exe (PID: 3016)
INFO
Reads the hosts file
- chrome.exe (PID: 448)
- chrome.exe (PID: 1560)
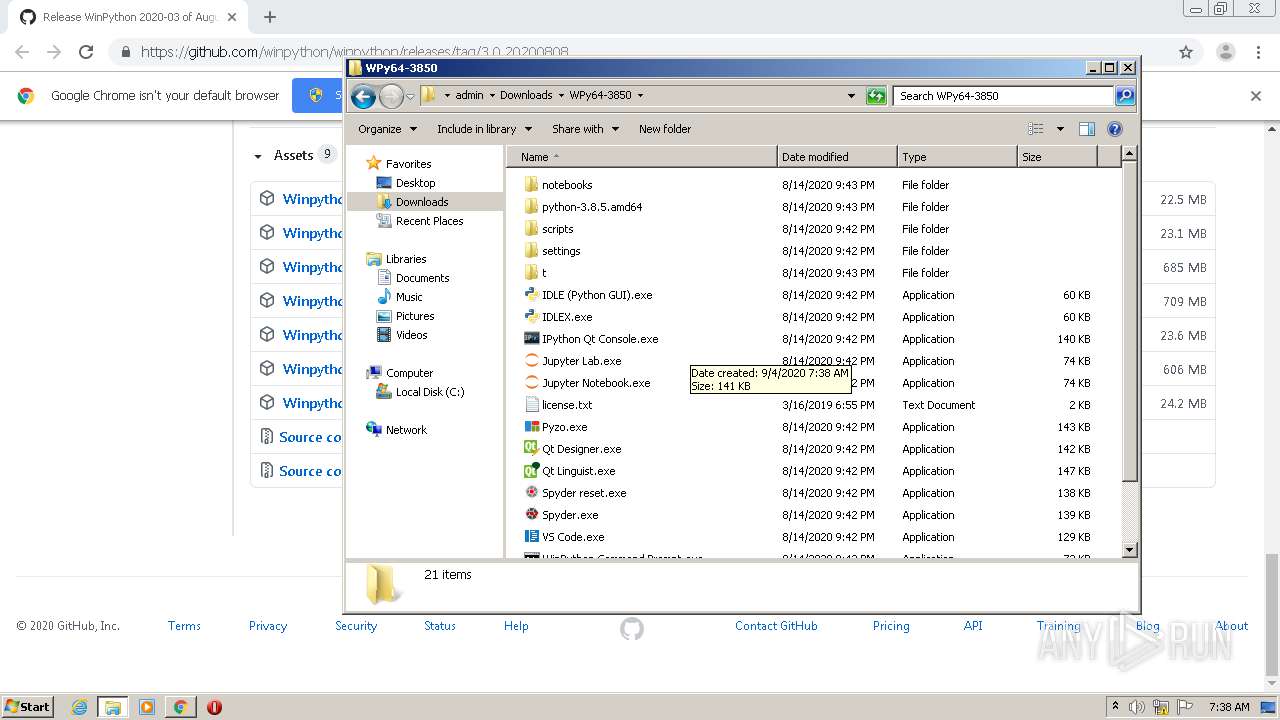
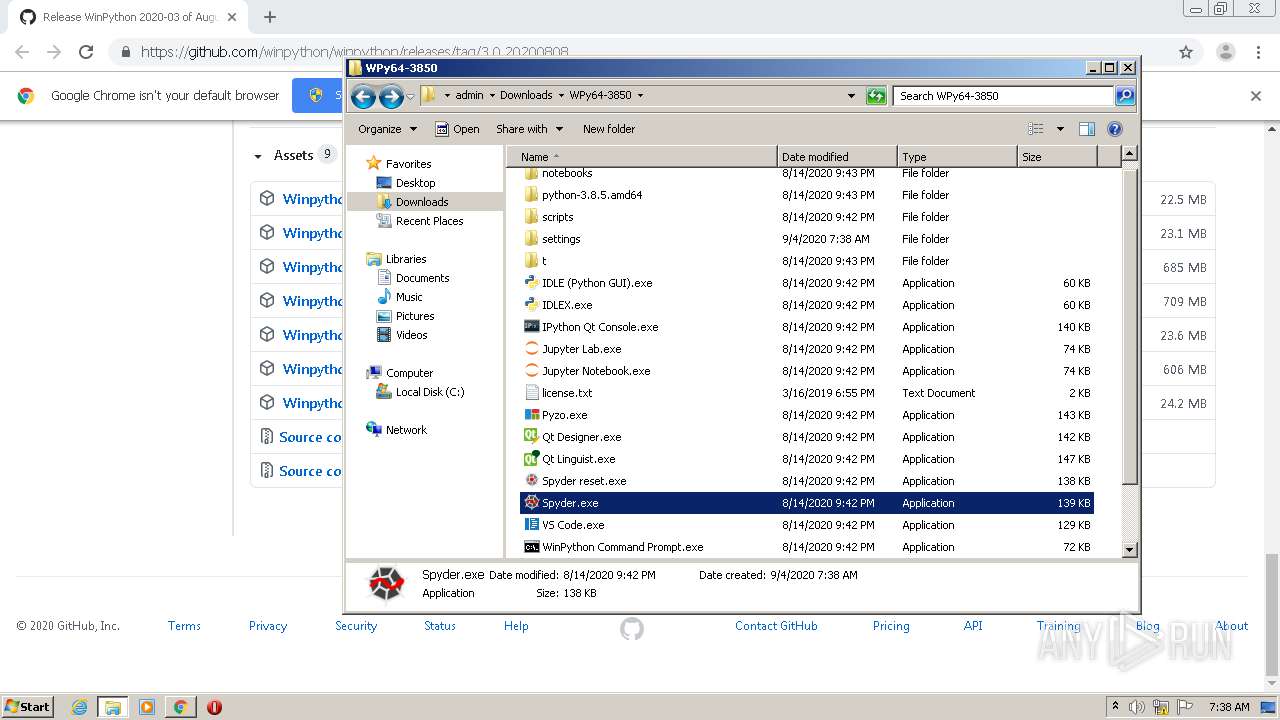
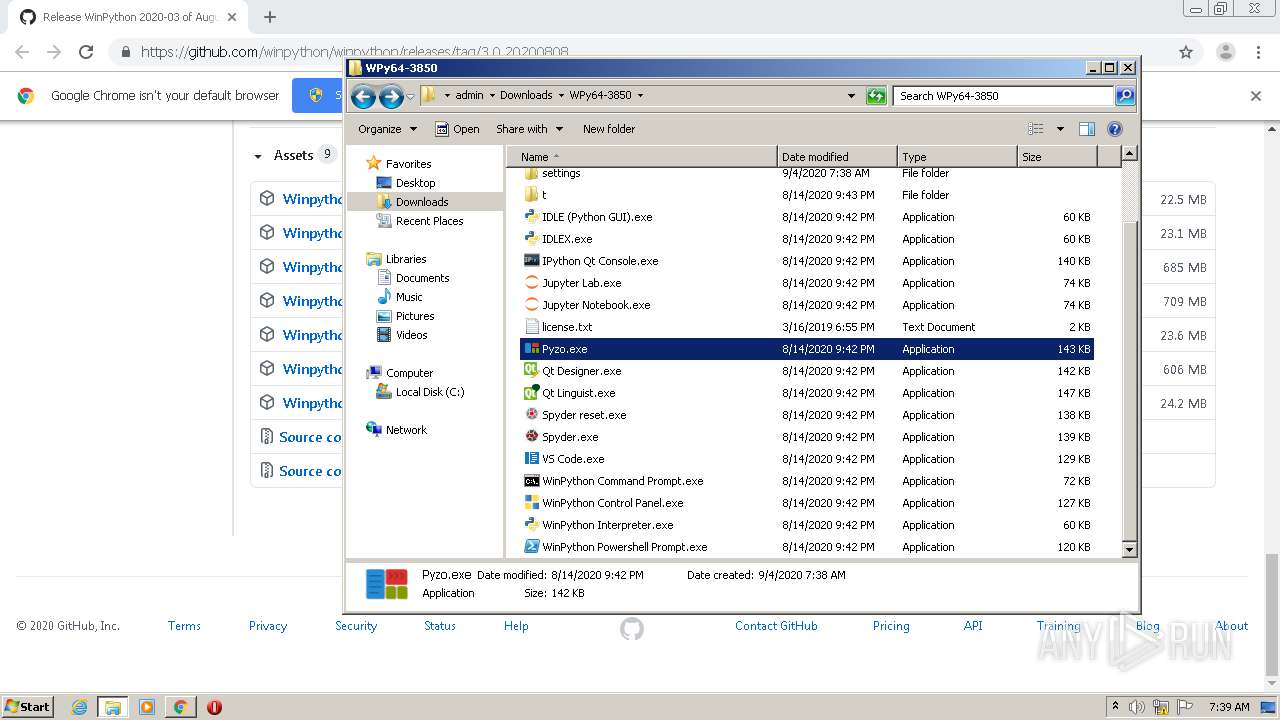
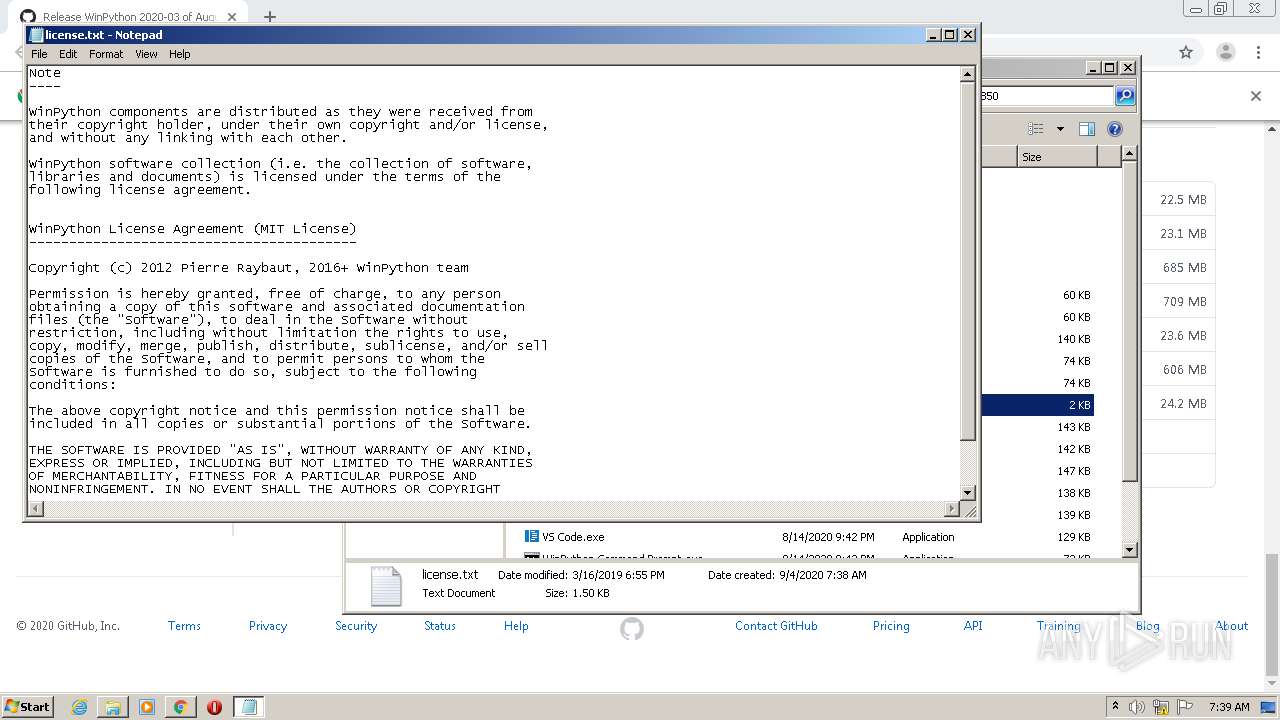
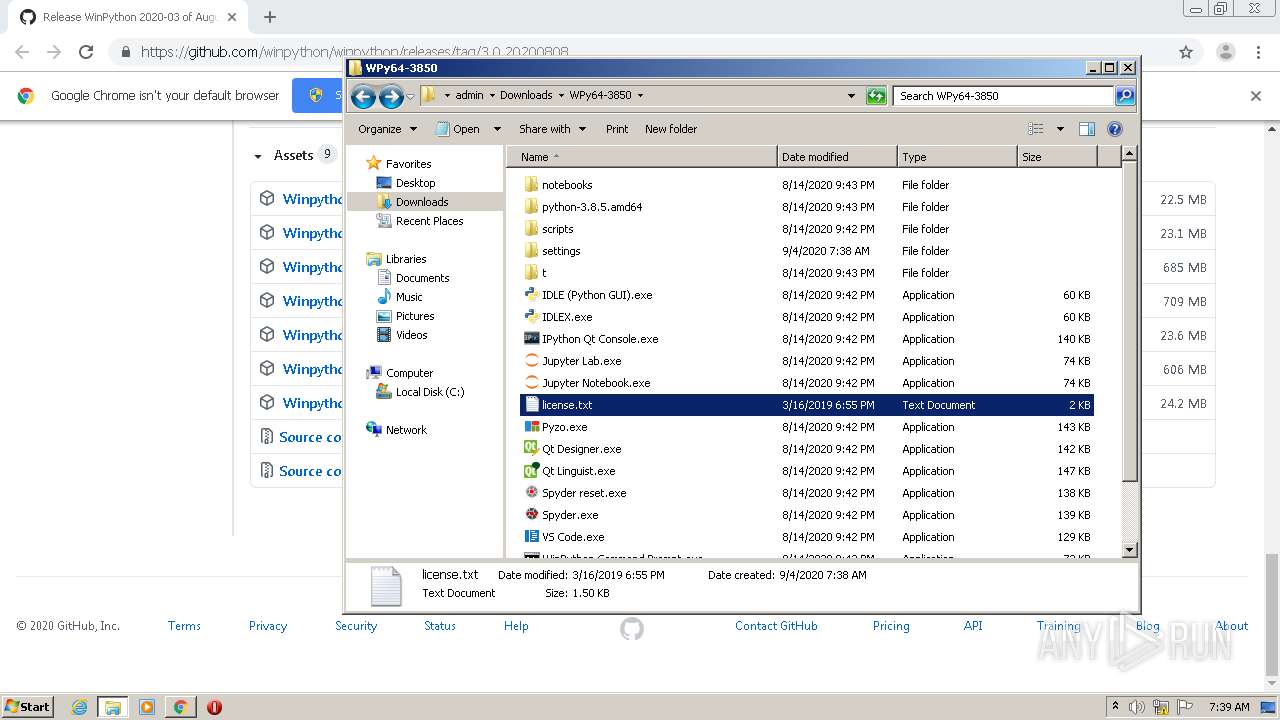
Manual execution by user
- Spyder.exe (PID: 1884)
- explorer.exe (PID: 4084)
- Pyzo.exe (PID: 1120)
- WinPython Powershell Prompt.exe (PID: 1436)
- Jupyter Notebook.exe (PID: 4076)
- NOTEPAD.EXE (PID: 3020)
- Spyder.exe (PID: 2608)
Reads Internet Cache Settings
- chrome.exe (PID: 1560)
Dropped object may contain Bitcoin addresses
- Winpython64-3.8.5.0dot.exe (PID: 2572)
Application launched itself
- chrome.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
50
Malicious processes
7
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | "wscript.exe" Noshell.vbs winpyzo.bat | C:\Windows\system32\wscript.exe | — | Pyzo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,15110211244207637544,2585922925296545288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14159674540311606716 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 500 | "C:\Windows\system32\cmd.exe" /k cmd_ps.bat | C:\Windows\system32\cmd.exe | — | WinPython Powershell Prompt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
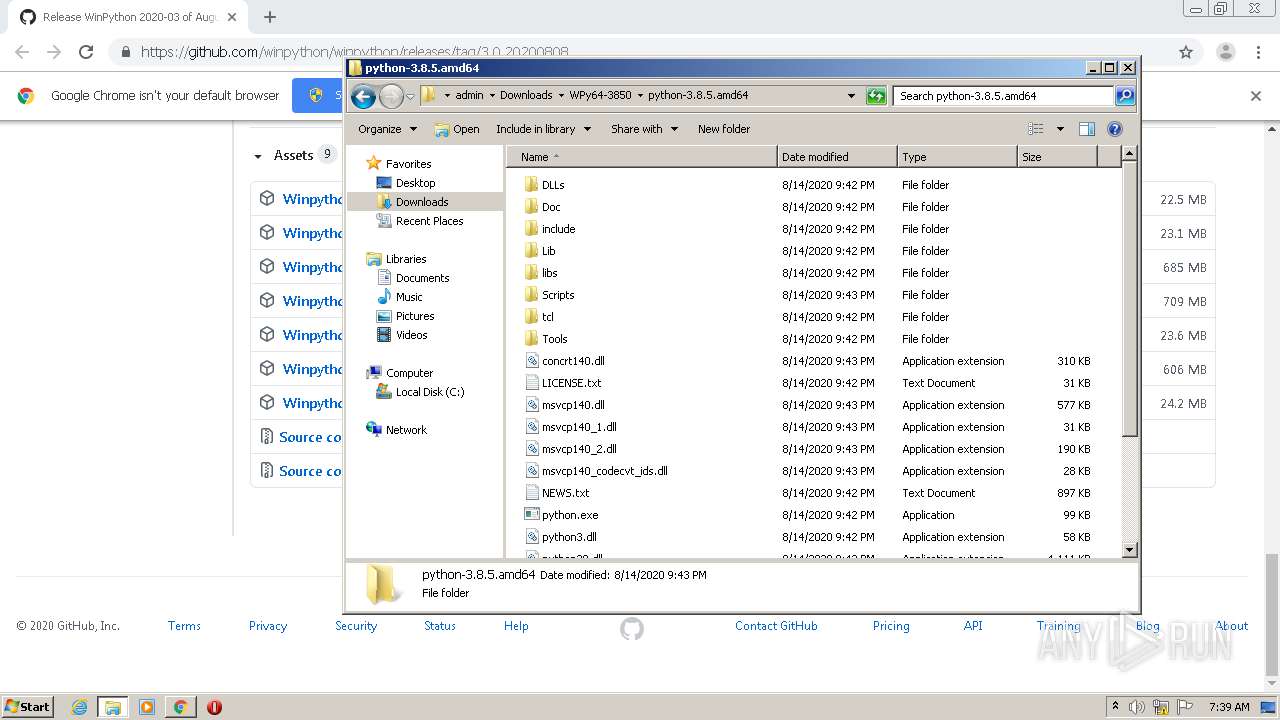
| 500 | C:\Windows\system32\find.exe /C /I ";C:\Users\admin\Downloads\WPy64-3850\python-3.8.5.amd64\;" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
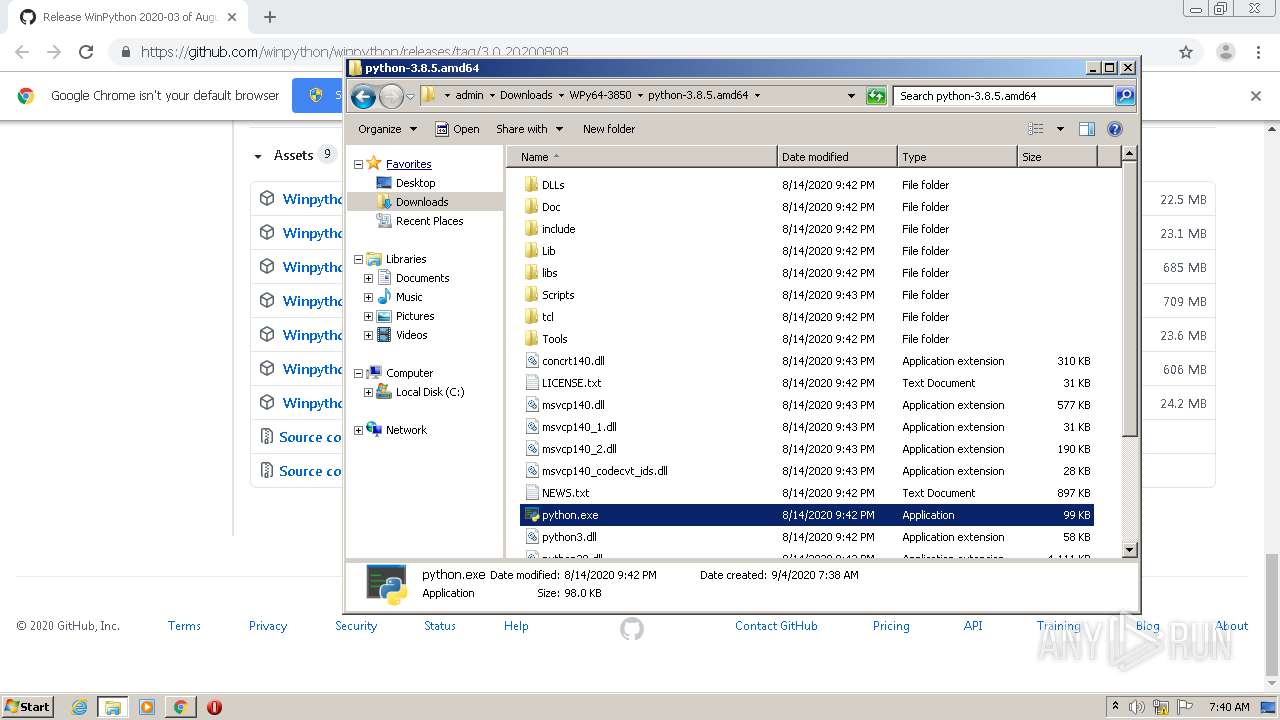
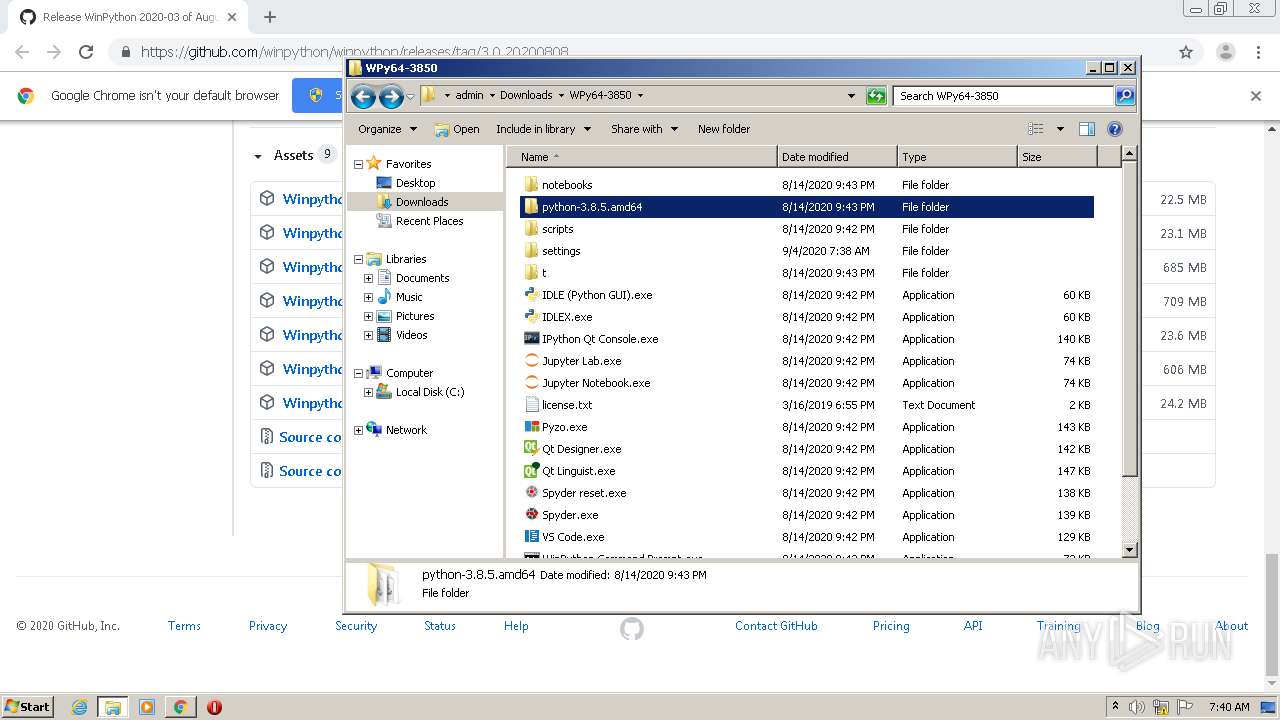
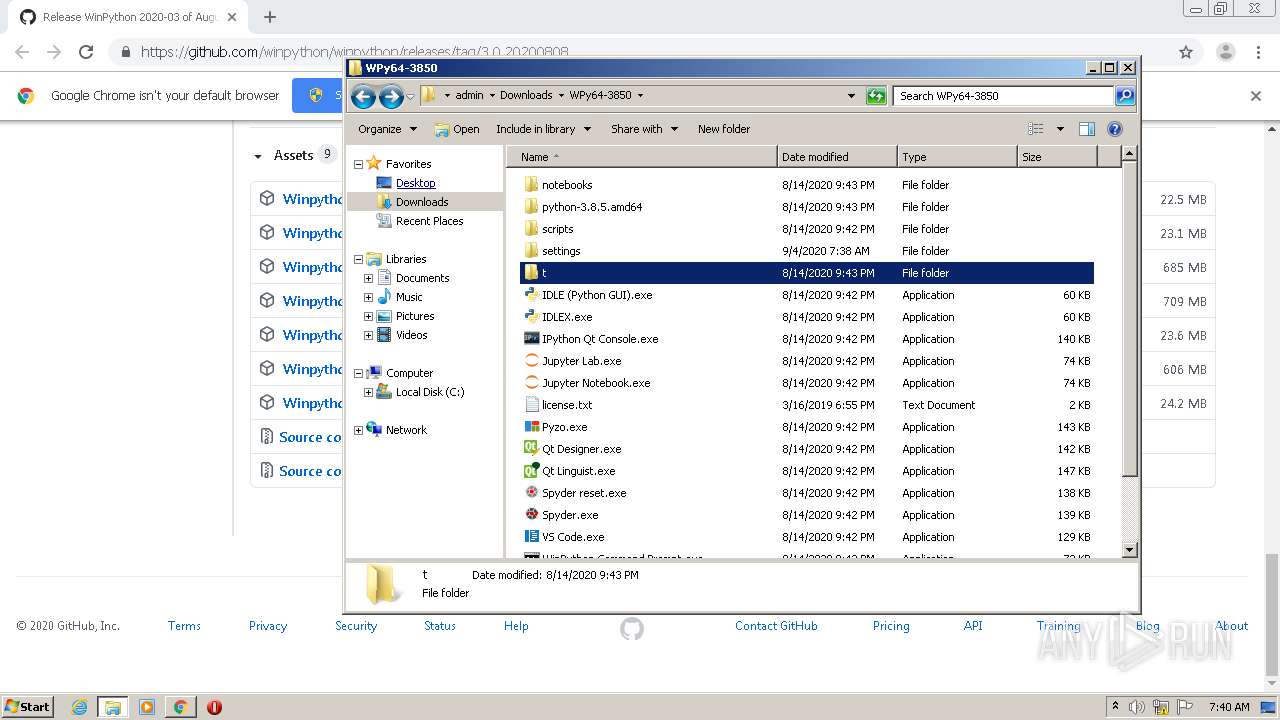
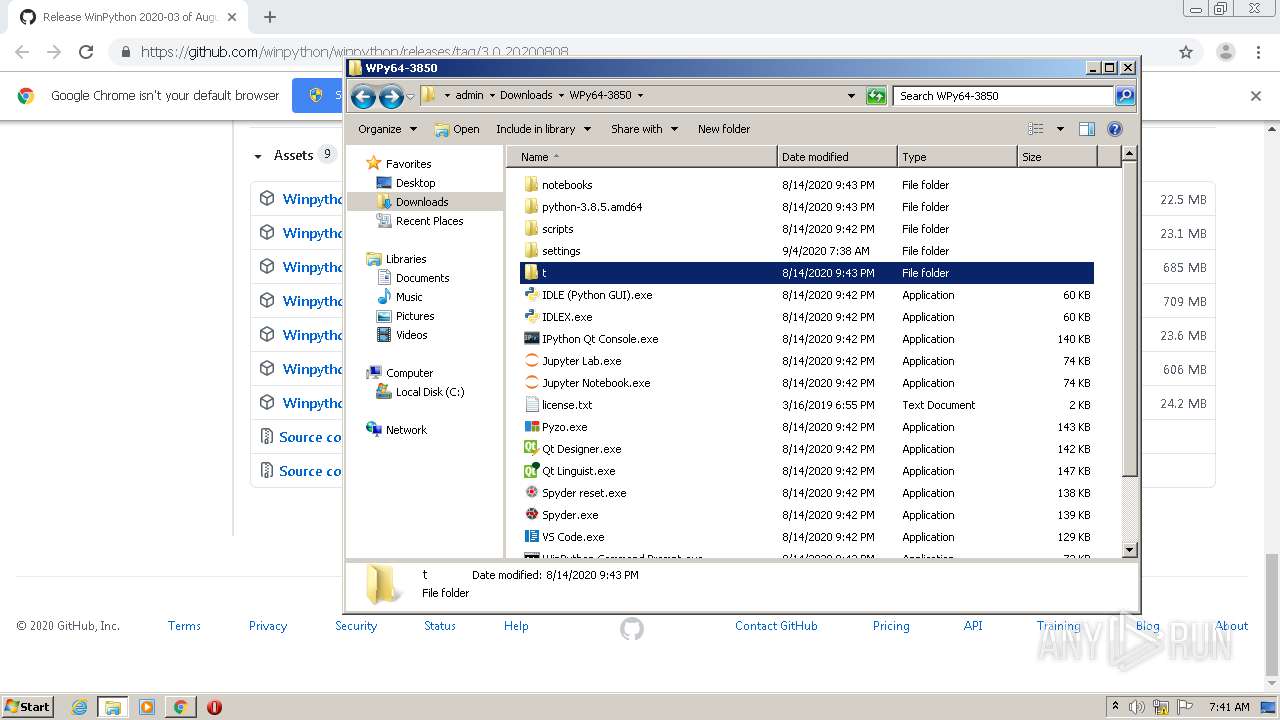
| 1120 | "C:\Users\admin\Downloads\WPy64-3850\Pyzo.exe" | C:\Users\admin\Downloads\WPy64-3850\Pyzo.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1332 | C:\Windows\system32\cmd.exe /S /D /c" echo ";C:\ProgramData\Oracle\Java\javapath;C:\Windows\system32;C:\Windows;C:\Windows\System32\Wbem;C:\Windows\System32\WindowsPowerShell\v1.0\;" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1432 | C:\Windows\system32\cmd.exe /c cscript /nologo "C:\Users\admin\Downloads\WPy64-3850\scripts\WinpythonIni.vbs" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
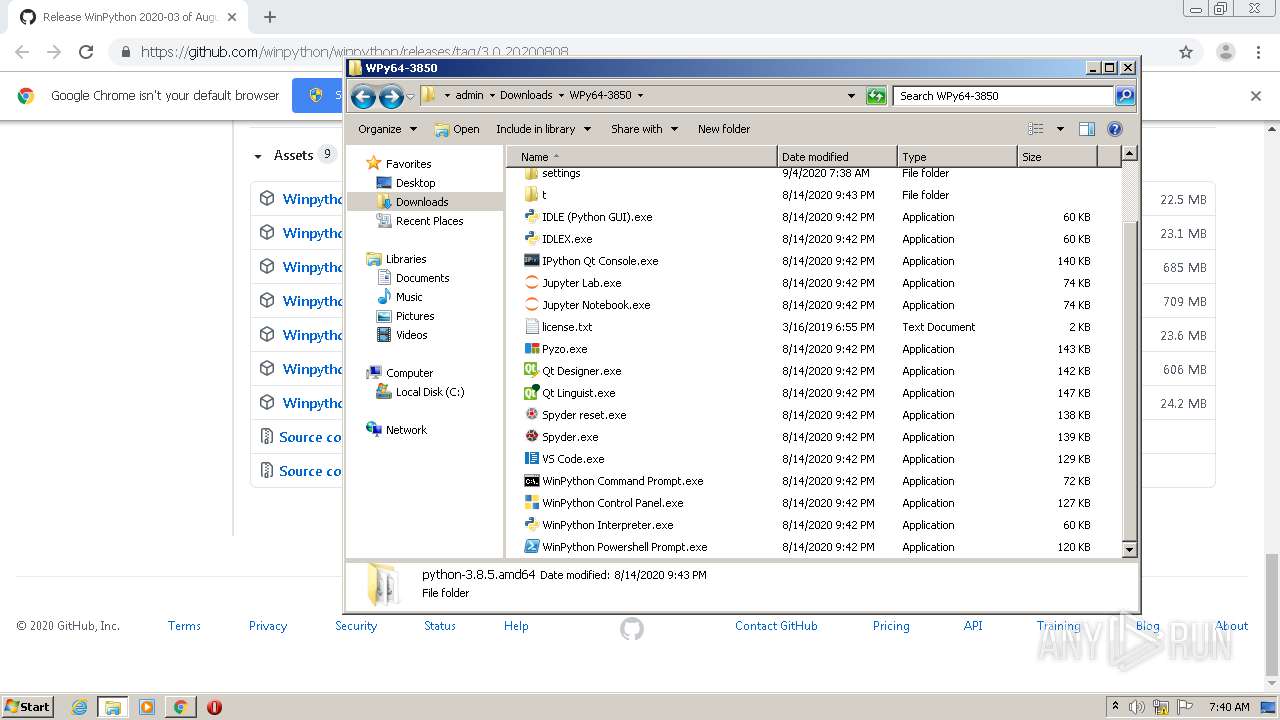
| 1436 | "C:\Users\admin\Downloads\WPy64-3850\WinPython Powershell Prompt.exe" | C:\Users\admin\Downloads\WPy64-3850\WinPython Powershell Prompt.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1440 | "C:\Windows\system32\cmd.exe" /k winipython_notebook.bat | C:\Windows\system32\cmd.exe | — | Jupyter Notebook.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
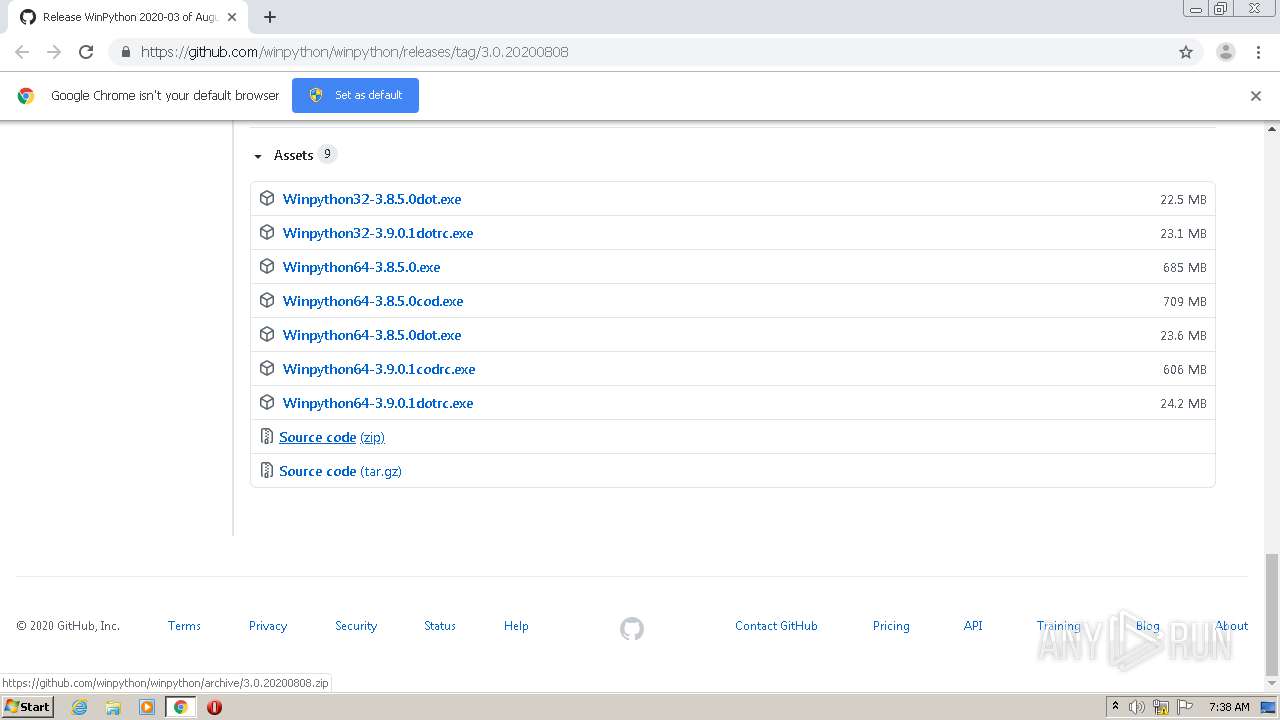
| 1560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://github.com/winpython/winpython/releases/tag/3.0.20200808" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 496
Read events
4 277
Write events
215
Delete events
4
Modification events
| (PID) Process: | (2948) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1560-13243674972648000 |
Value: 259 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (1560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
103
Suspicious files
807
Text files
3 232
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15da8b.TMP | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a8a19bcb-e21e-4562-8ff6-631d3ef5191d.tmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15da7b.TMP | text | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15dc40.TMP | — | |
MD5:— | SHA256:— | |||
| 1560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
31
DNS requests
23
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
448 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 185.199.111.154:443 | github.githubassets.com | GitHub, Inc. | NL | suspicious |
448 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 172.217.23.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 216.58.208.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 172.217.16.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 172.217.18.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
448 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
github.githubassets.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
avatars3.githubusercontent.com |
| whitelisted |
avatars2.githubusercontent.com |
| whitelisted |
avatars1.githubusercontent.com |
| whitelisted |
avatars0.githubusercontent.com |
| whitelisted |
github-cloud.s3.amazonaws.com |
| shared |