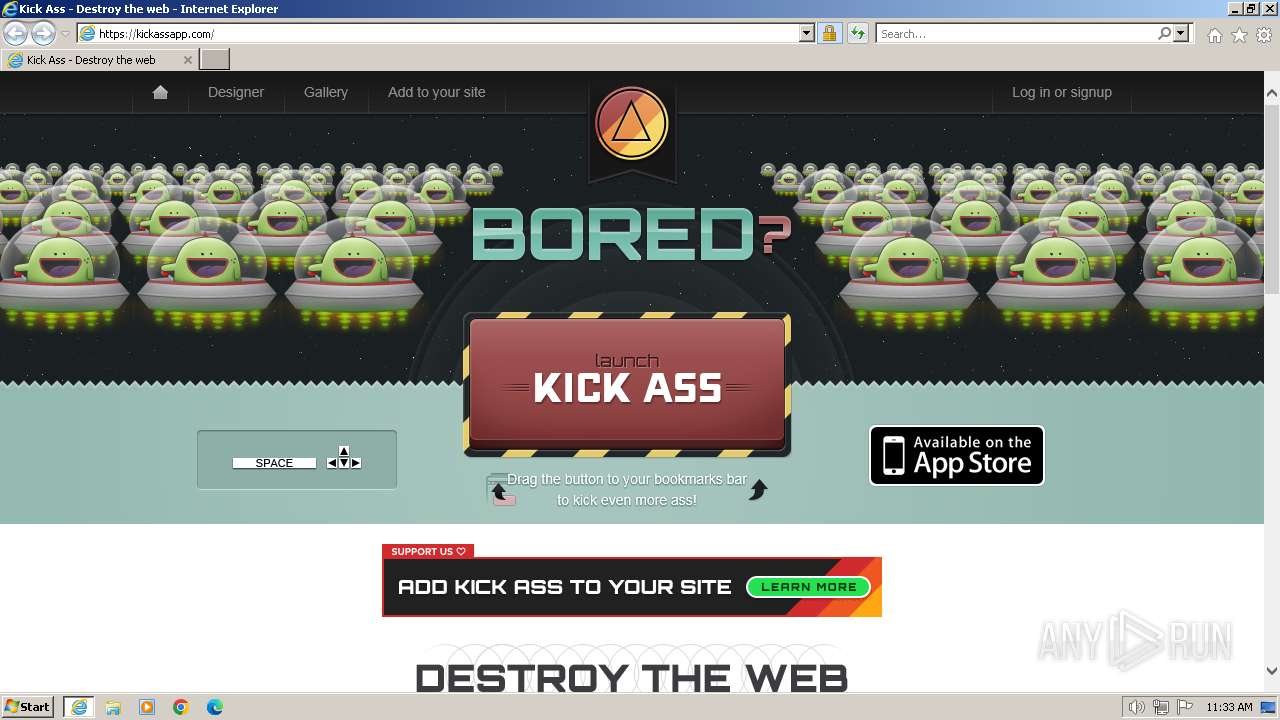
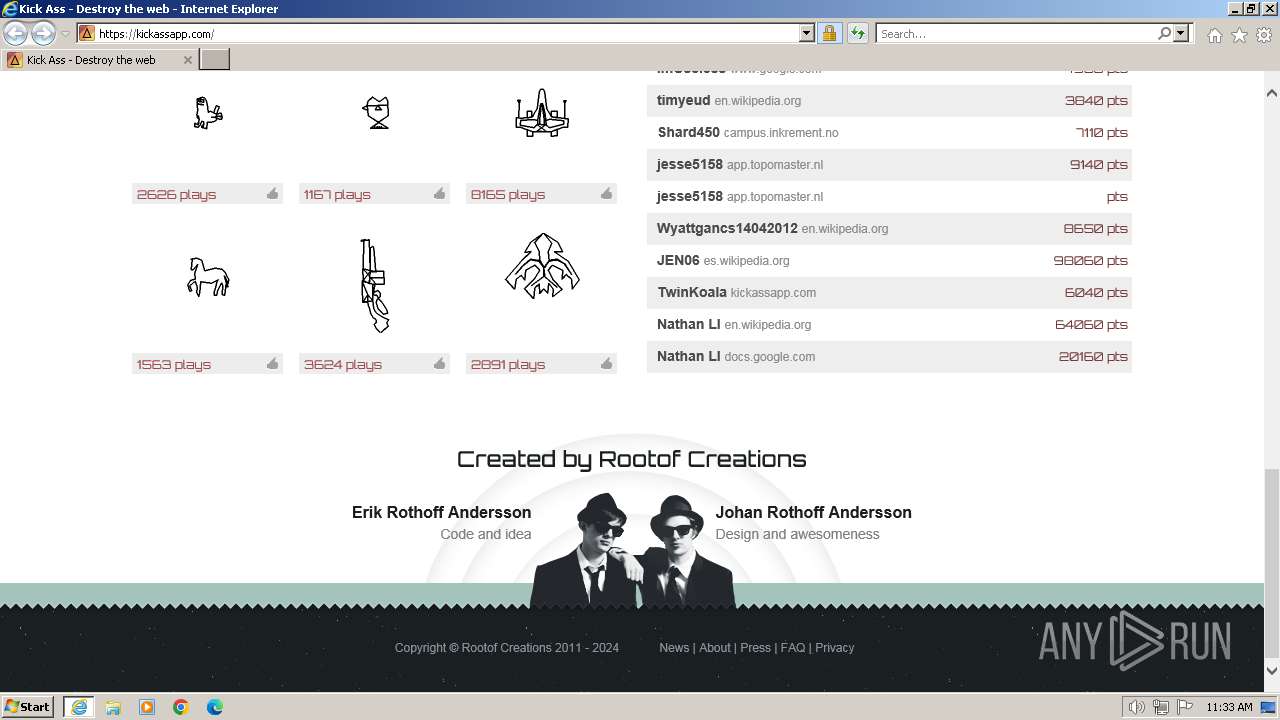
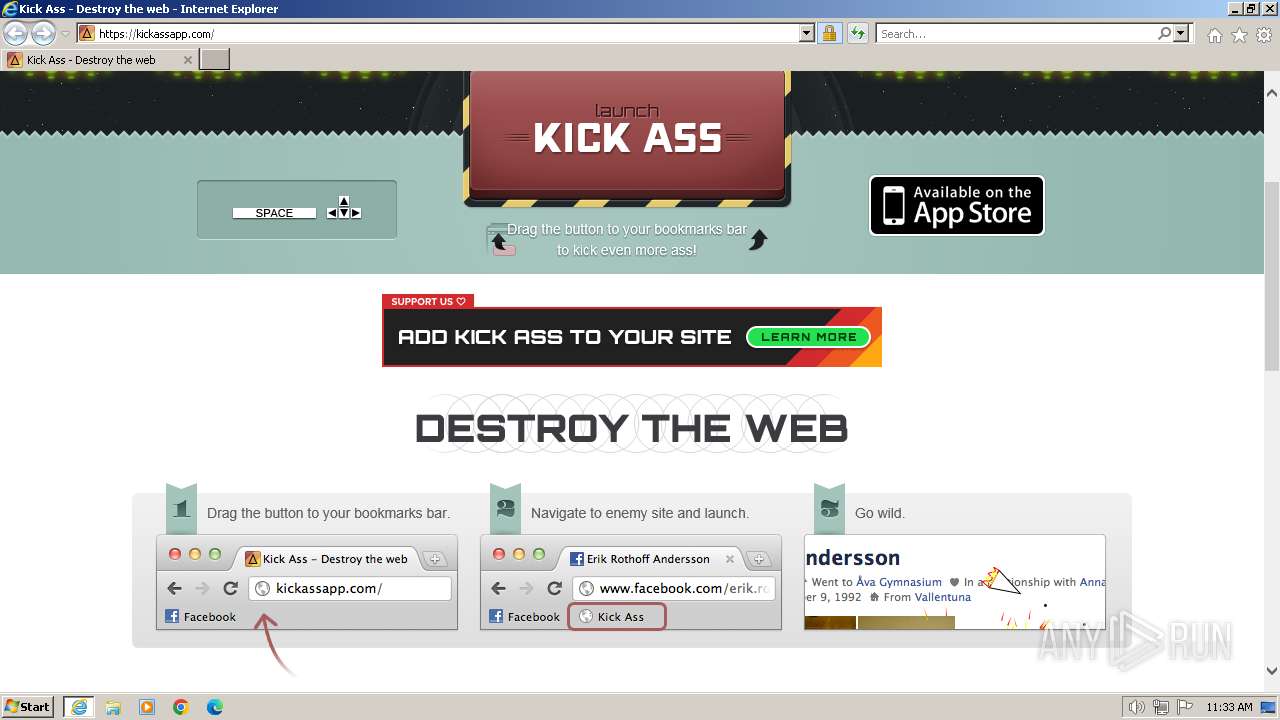
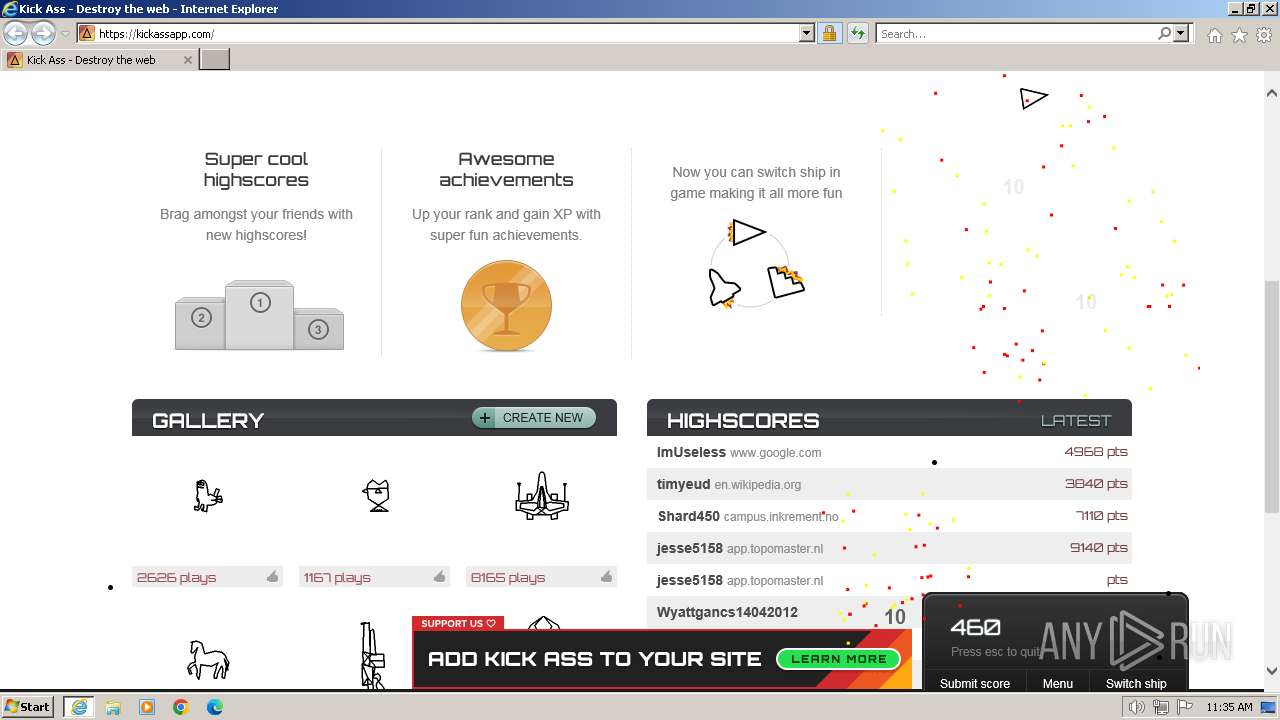
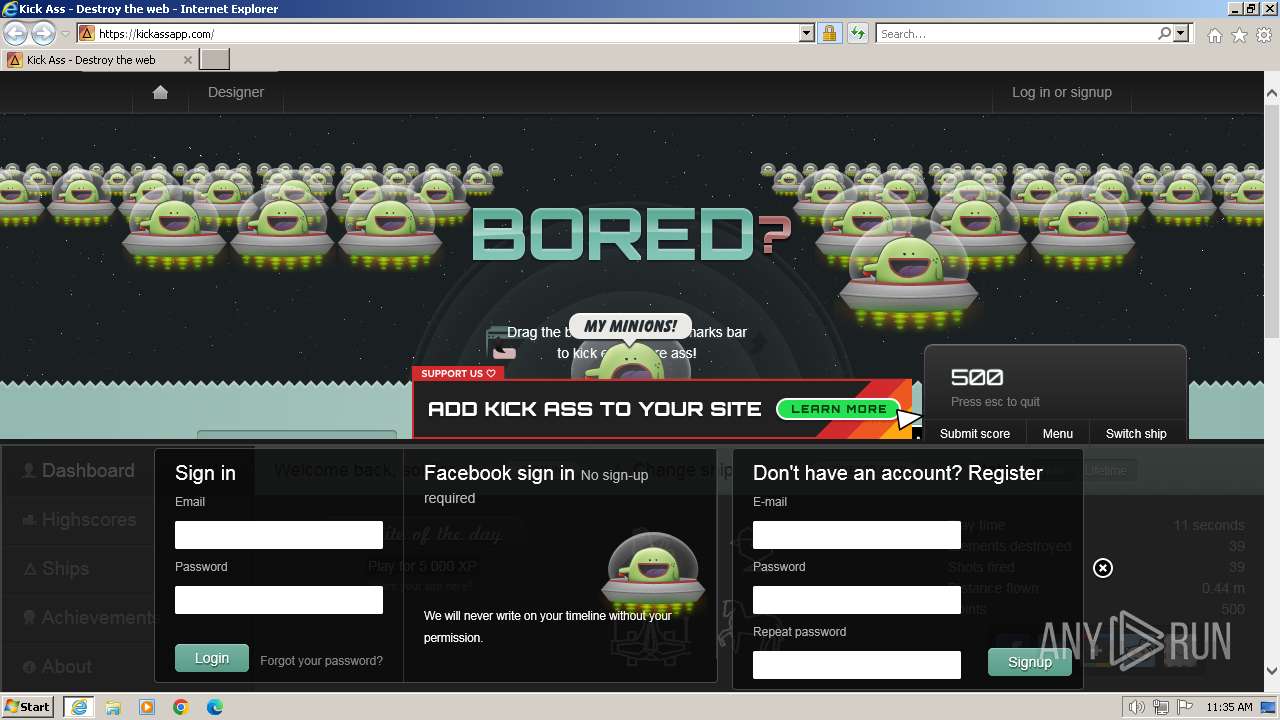
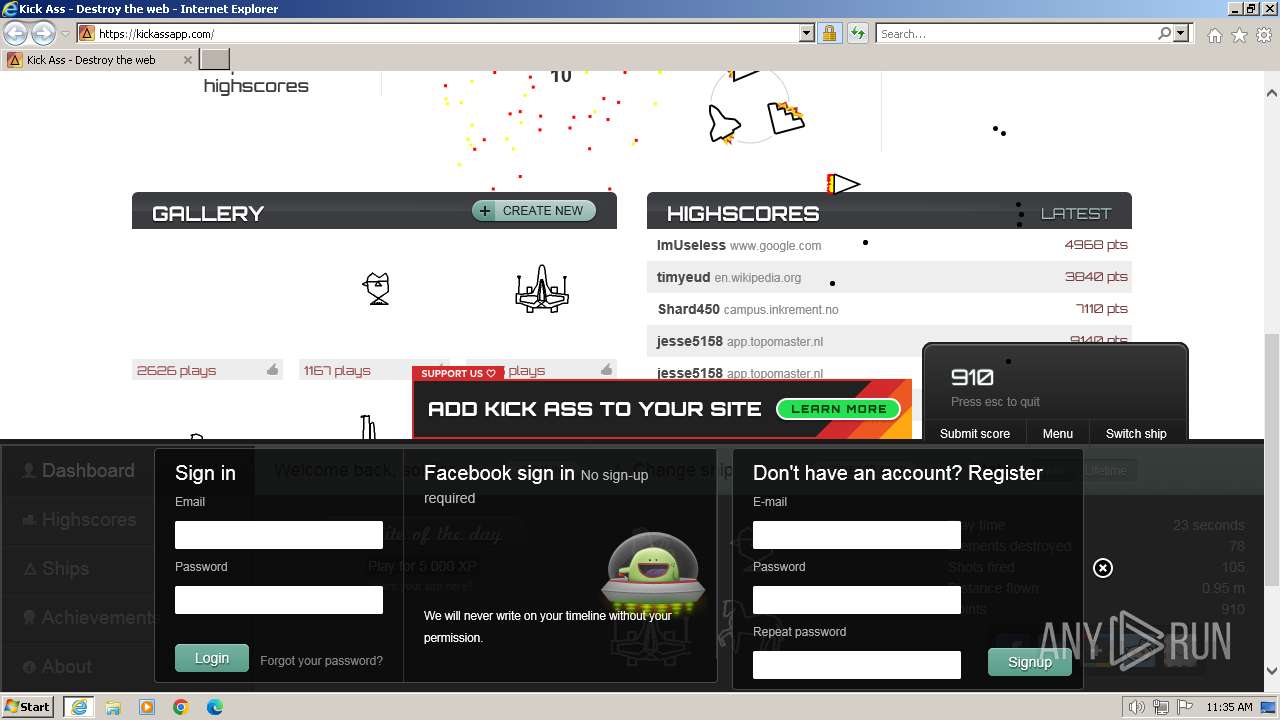
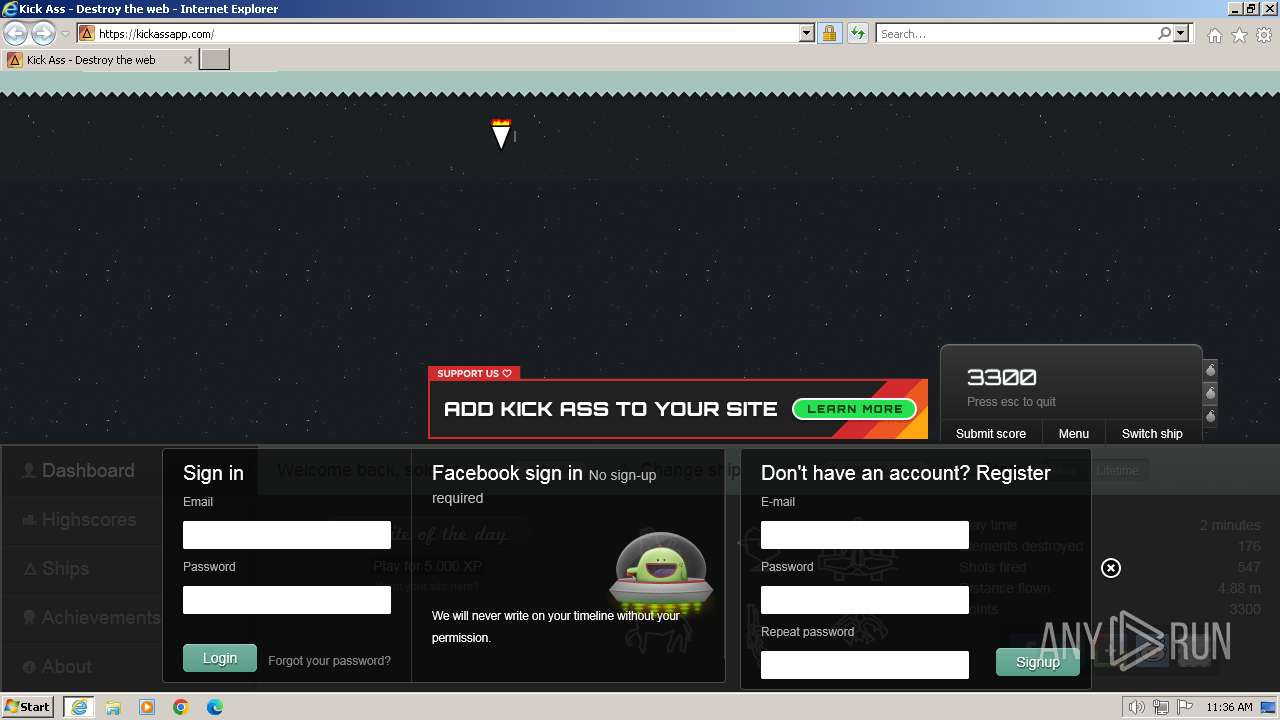
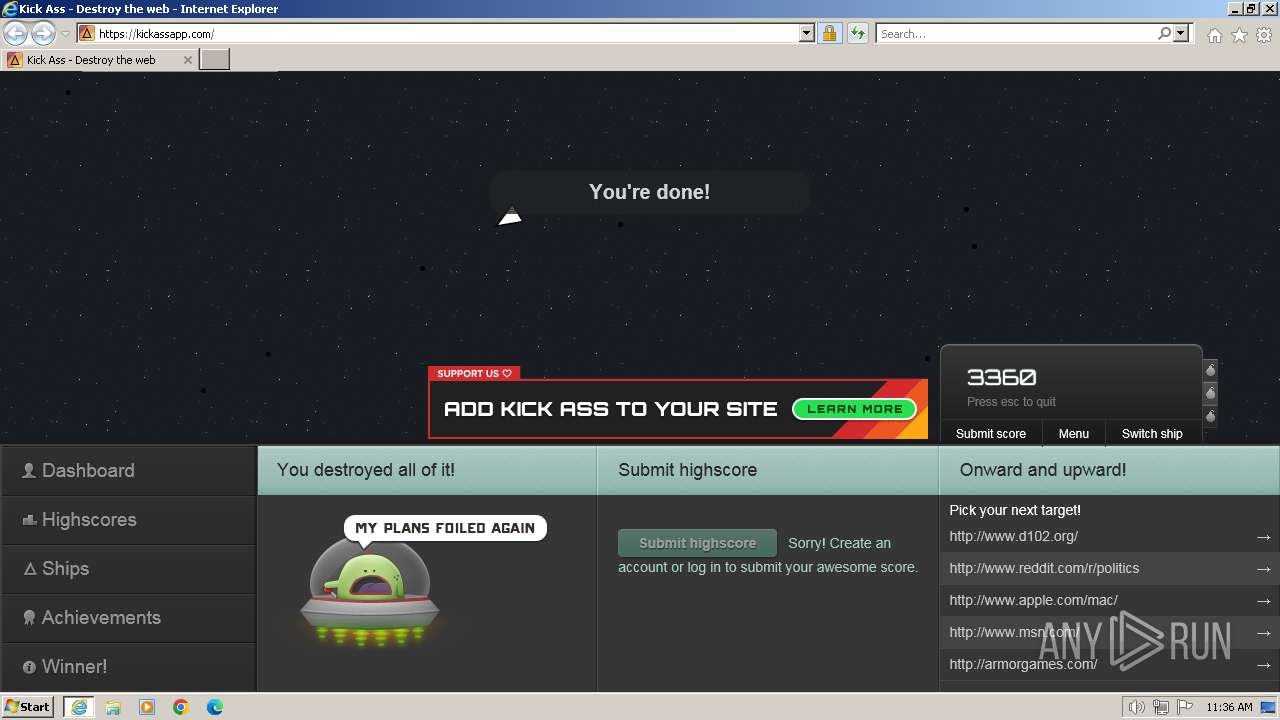
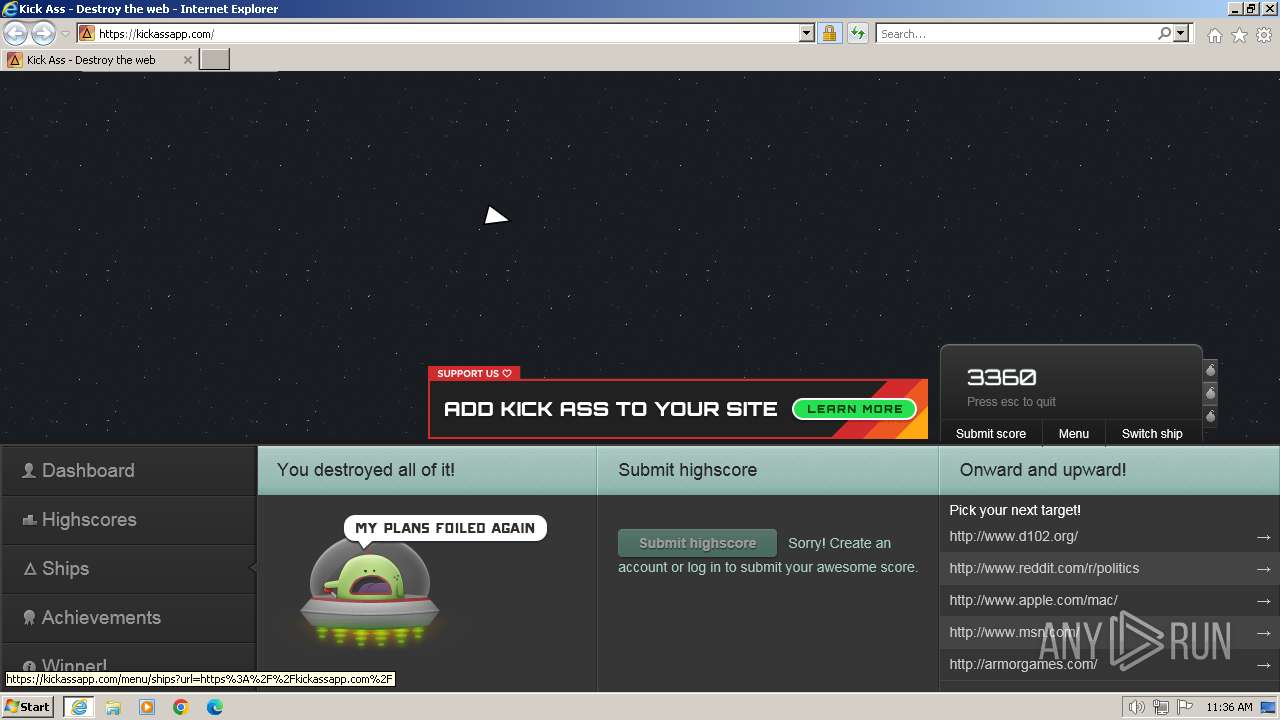
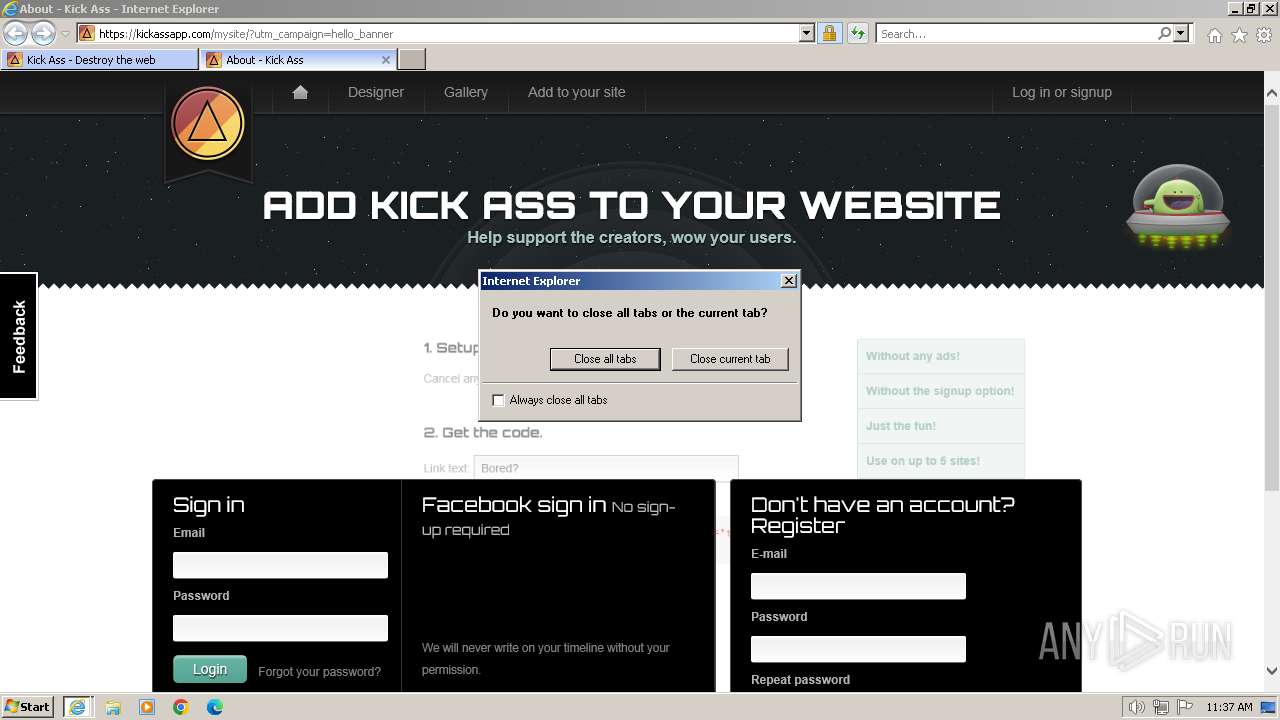
| URL: | https://kickassapp.com/ |
| Full analysis: | https://app.any.run/tasks/1f11c6ad-155f-4c80-afc3-326c08b1a3ec |
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2024, 11:33:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5DB3F12E112073FEFBEB7926787C744F |
| SHA1: | 3A433E84D73FB64980D347A4A9123D87CDDF2509 |
| SHA256: | BAFAF0C7454863958565EEC190AC7D811479D8DD03CE71B2A059883C0E2F30BC |
| SSDEEP: | 3:N8JZxP:2VP |
MALICIOUS
Drops the executable file immediately after the start
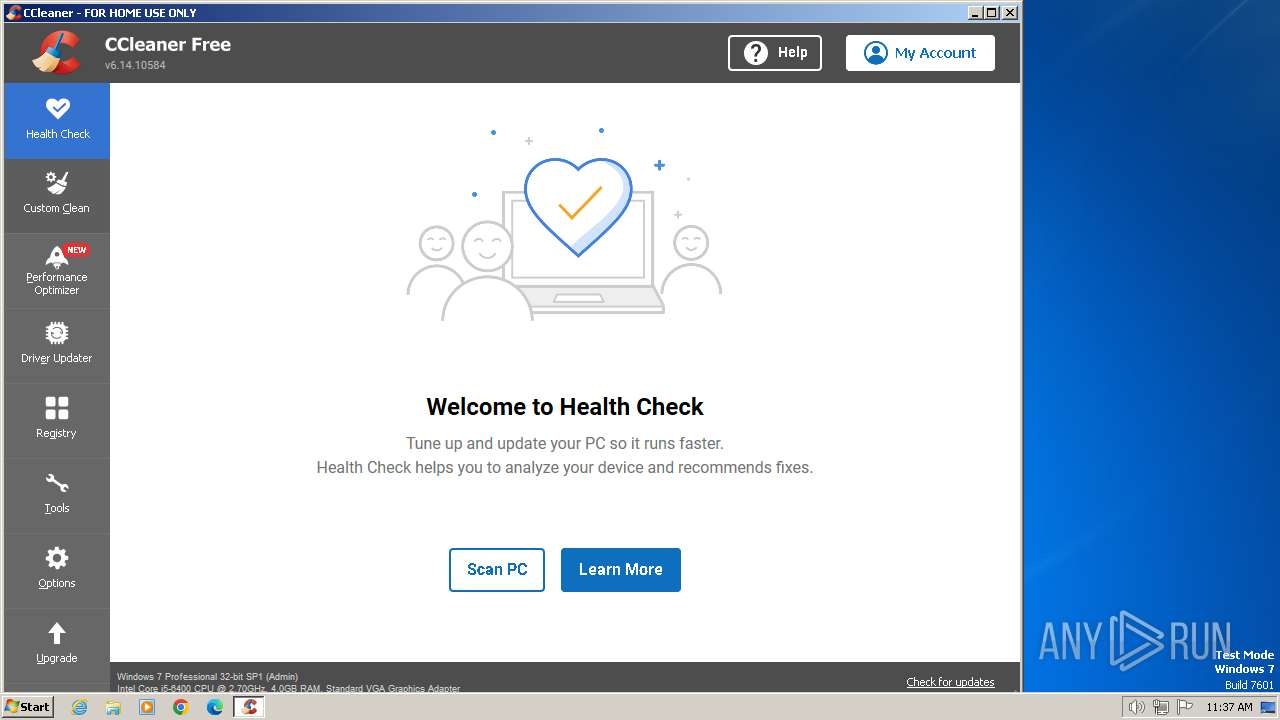
- CCleaner.exe (PID: 968)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 968)
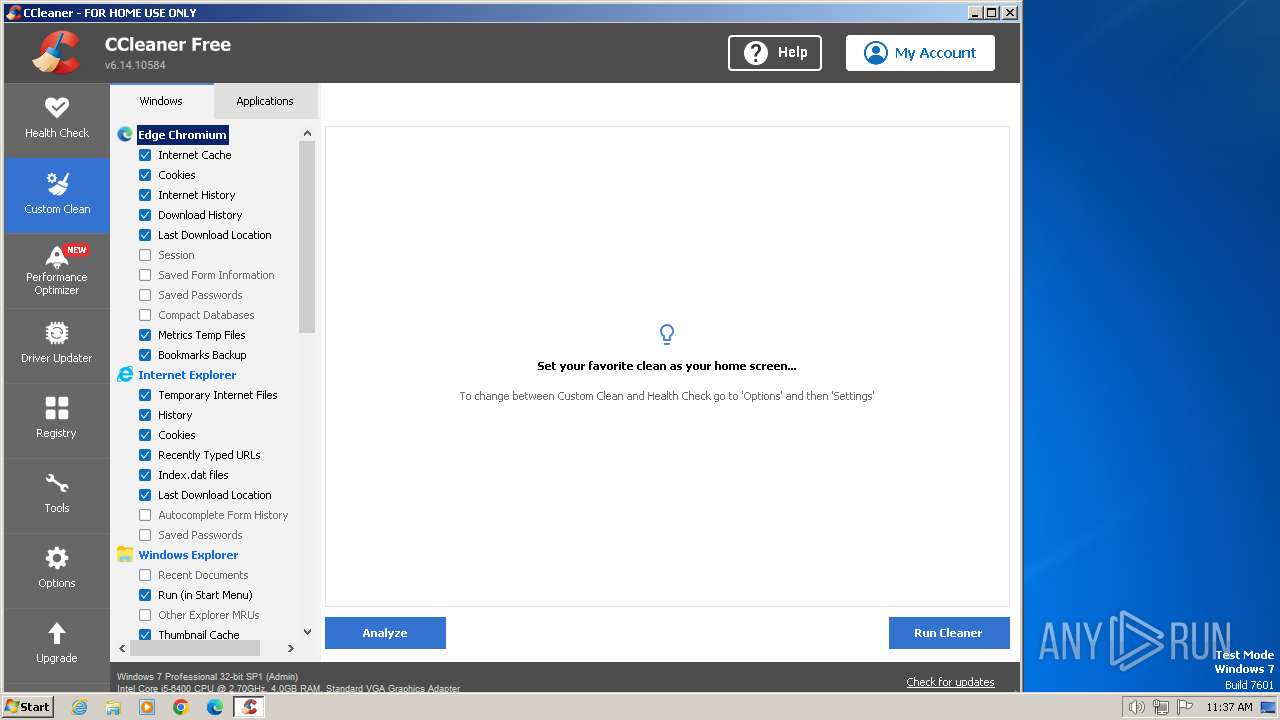
Steals credentials from Web Browsers
- CCleaner.exe (PID: 968)
SUSPICIOUS
The process executes via Task Scheduler
- CCleaner.exe (PID: 968)
Reads Internet Explorer settings
- CCleaner.exe (PID: 968)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 968)
Checks Windows Trust Settings
- CCleaner.exe (PID: 968)
Reads settings of System Certificates
- CCleaner.exe (PID: 968)
Reads security settings of Internet Explorer
- CCleaner.exe (PID: 968)
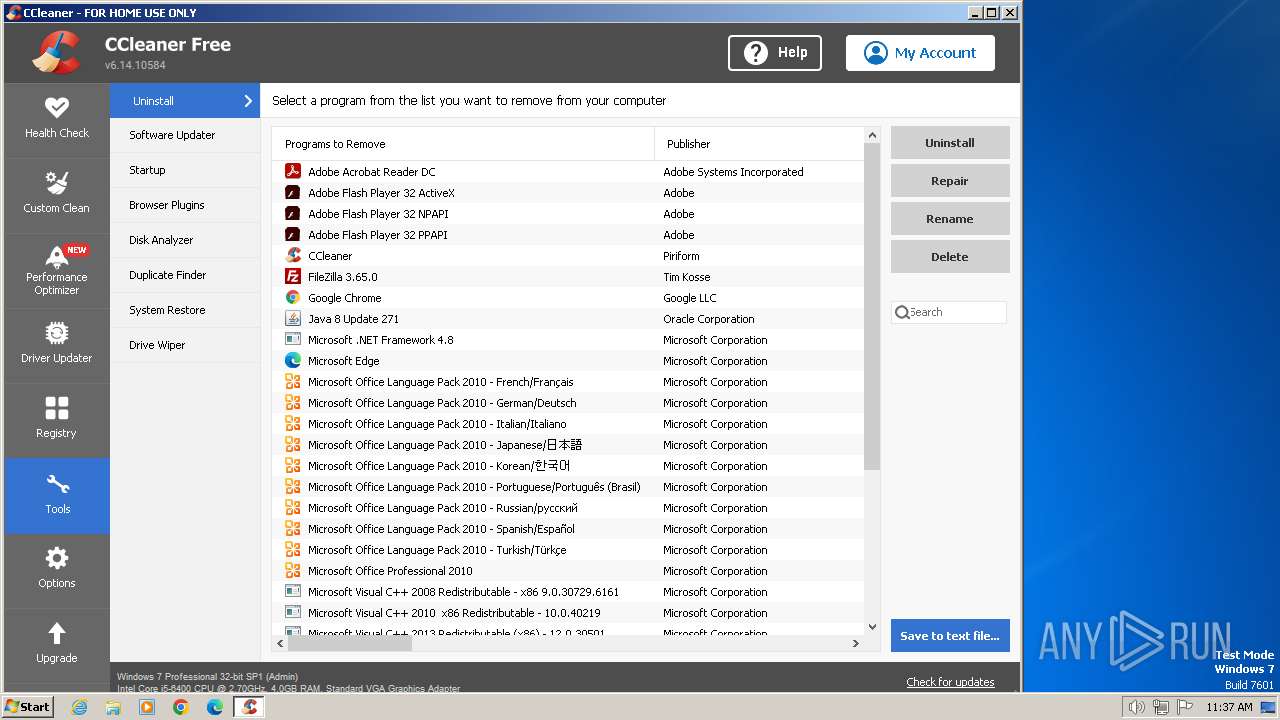
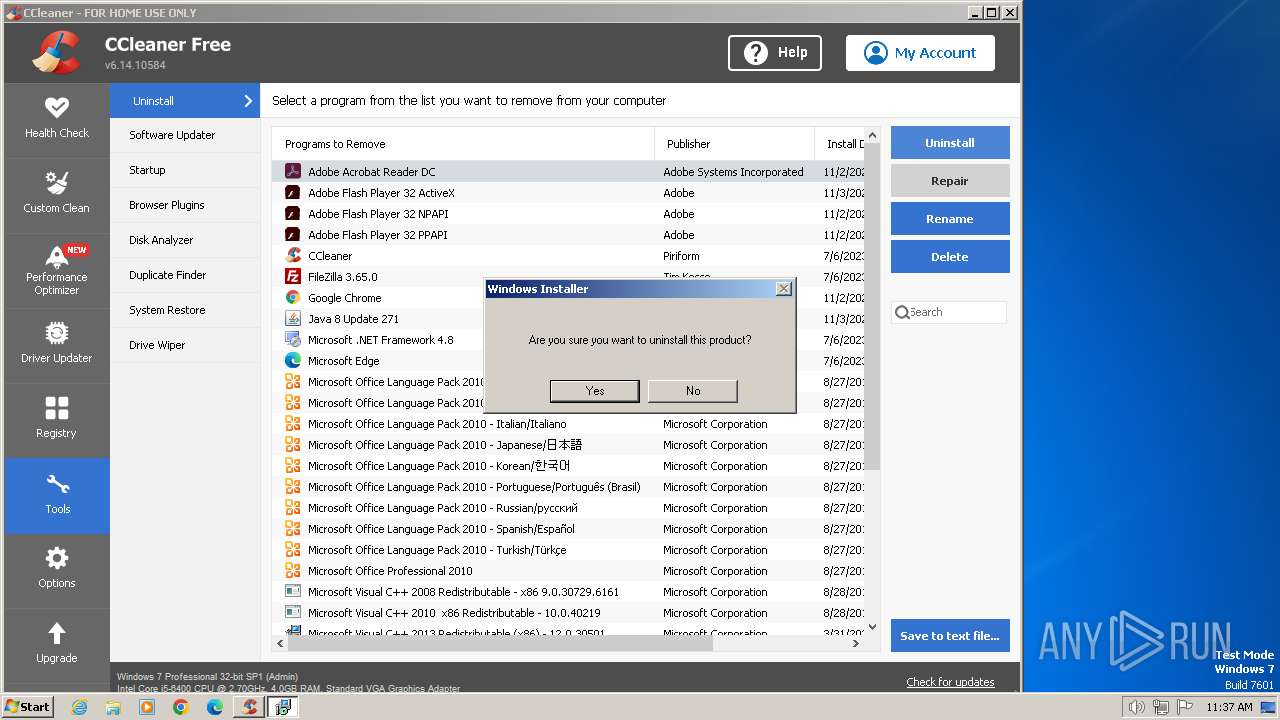
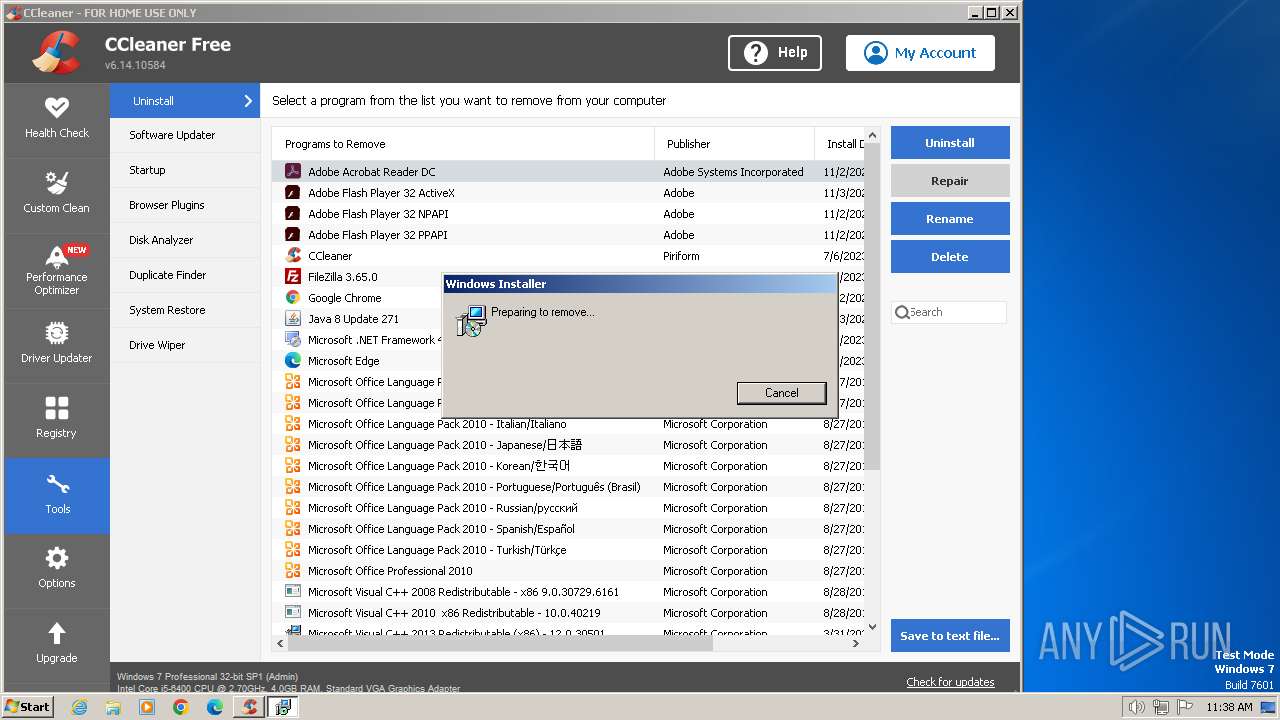
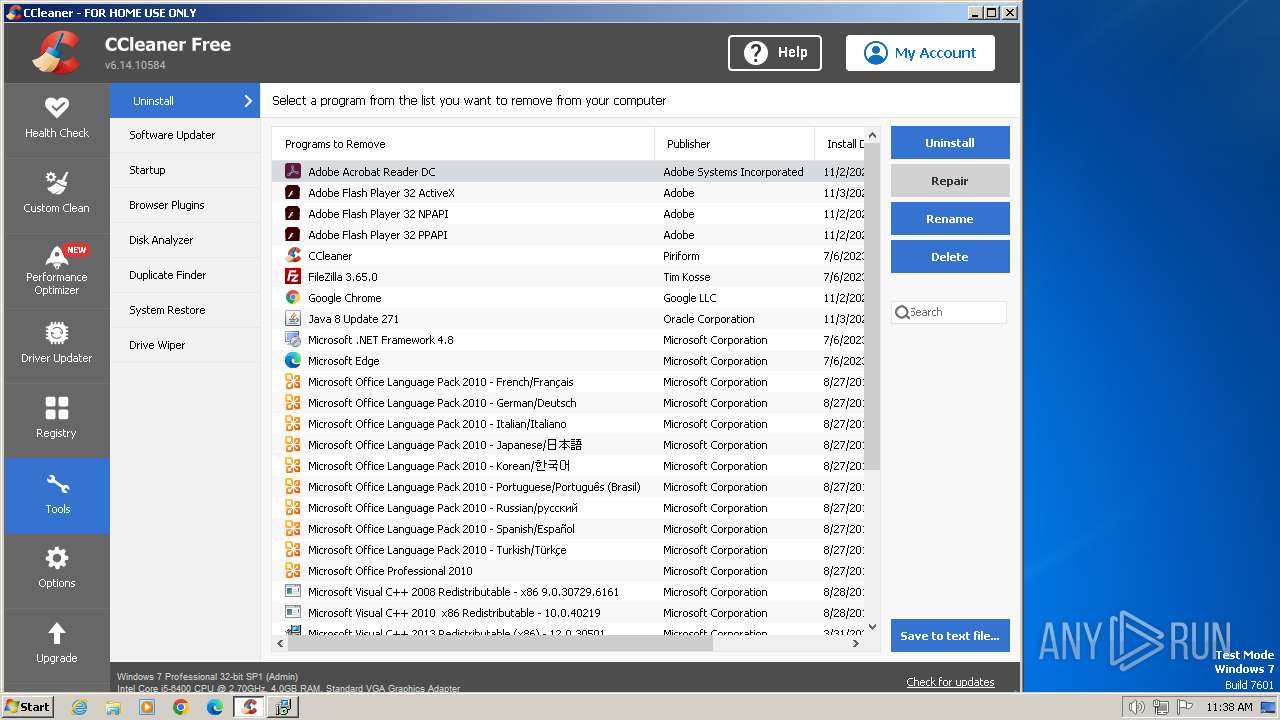
Searches for installed software
- CCleaner.exe (PID: 968)
Executes as Windows Service
- VSSVC.exe (PID: 3292)
Reads the Internet Settings
- CCleaner.exe (PID: 968)
The process verifies whether the antivirus software is installed
- CCleaner.exe (PID: 968)
INFO
Checks supported languages
- CCleaner.exe (PID: 2856)
- CCleaner.exe (PID: 968)
- msiexec.exe (PID: 3284)
Reads the computer name
- CCleaner.exe (PID: 2856)
- CCleaner.exe (PID: 968)
- msiexec.exe (PID: 3284)
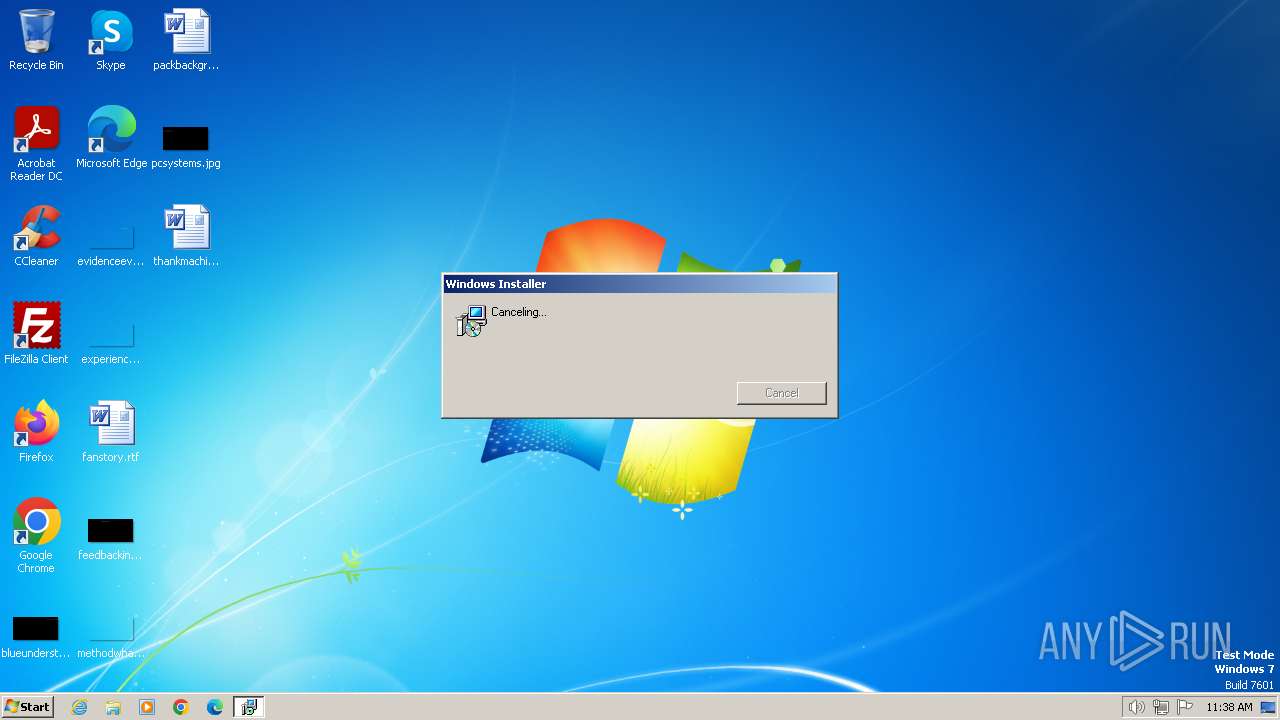
Manual execution by a user
- CCleaner.exe (PID: 2856)
Application launched itself
- iexplore.exe (PID: 124)
Reads Environment values
- CCleaner.exe (PID: 2856)
- CCleaner.exe (PID: 968)
Reads CPU info
- CCleaner.exe (PID: 968)
Reads the machine GUID from the registry
- CCleaner.exe (PID: 968)
- msiexec.exe (PID: 3284)
Reads product name
- CCleaner.exe (PID: 968)
Creates files in the program directory
- CCleaner.exe (PID: 968)
Checks proxy server information
- CCleaner.exe (PID: 968)
Creates files or folders in the user directory
- CCleaner.exe (PID: 968)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://kickassapp.com/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 968 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 6.14.0.10584 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:124 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:124 CREDAT:3347723 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2856 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 6.14.0.10584 Modules
| |||||||||||||||
| 3204 | msiexec.exe /X{AC76BA86-7AD7-1033-7B44-AC0F074E4100} | C:\Windows\System32\msiexec.exe | — | CCleaner.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1602 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3284 | C:\Windows\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3292 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
42 014
Read events
41 727
Write events
233
Delete events
54
Modification events
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (124) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
75
Text files
609
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab3A.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:C3E61117255FDF6FC8782B7DF277BAD0 | SHA256:3E36DA22A2CF6FE99DD60031DFBC89307E3D6442F18CFCE596BDF09AB2C8200E | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\C4XYTWOR.txt | text | |
MD5:83EE356886D601944FF9B45B1CB684FD | SHA256:9711552E1C4AC073690EAFFF362B808E64596D3E5ABA456186B09208BD6BBA79 | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:4B194F06D3EA4D5CA24C306581FC5FCF | SHA256:208AF68929DB41EF99BDD0D02EC468A4AC7C971B8EC57647A972276B52018E45 | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4D.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\highscore-icon[1].png | image | |
MD5:45C1D01FC7DFCD85F0B0B6C3F15B2513 | SHA256:2C06B361E92AABC7B92DCF1AE8024E78B51688AF4F20CBFDB9F955F2704A4715 | |||
| 2088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\S0GAMTBD.htm | html | |
MD5:E4247C4212F2179CA76ECC5E3346AEE3 | SHA256:09245BF4434E47313547ECBADF49C6AA1BAD8E80FDF7512ED1A2F60FF79F89CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
99
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2088 | iexplore.exe | GET | 200 | 23.53.40.73:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
124 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
124 | iexplore.exe | GET | 304 | 23.53.40.73:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | unknown | — | — | unknown |
2088 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAly1V%2BI4yyBkCD%2FXJL5eCs%3D | unknown | binary | 471 b | unknown |
2808 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | unknown | binary | 471 b | unknown |
2088 | iexplore.exe | GET | 200 | 23.53.40.73:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0a8775331b03f167 | unknown | compressed | 65.2 Kb | unknown |
2088 | iexplore.exe | GET | 200 | 23.53.40.73:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
2088 | iexplore.exe | GET | 200 | 23.53.40.73:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9d5a8551135e8119 | unknown | compressed | 65.2 Kb | unknown |
2088 | iexplore.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2088 | iexplore.exe | GET | 200 | 142.250.74.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2088 | iexplore.exe | 178.79.187.156:443 | kickassapp.com | Linode, LLC | GB | unknown |
2088 | iexplore.exe | 23.53.40.73:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2088 | iexplore.exe | 23.192.153.142:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
2088 | iexplore.exe | 216.58.206.42:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2088 | iexplore.exe | 142.250.74.195:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
2088 | iexplore.exe | 142.250.185.136:443 | ssl.google-analytics.com | GOOGLE | US | unknown |
2088 | iexplore.exe | 142.250.185.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kickassapp.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
hi.kickassapp.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
CCleaner.exe | [2024-01-19 11:37:37.496] [error ] [settings ] [ 968: 1484] [6000C4: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | [2024-01-19 11:37:38.262] [error ] [settings ] [ 968: 3016] [9434E9: 359] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | [2024-01-19 11:37:38.277] [error ] [Burger ] [ 968: 3016] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | [2024-01-19 11:37:38.277] [error ] [Burger ] [ 968: 3016] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|