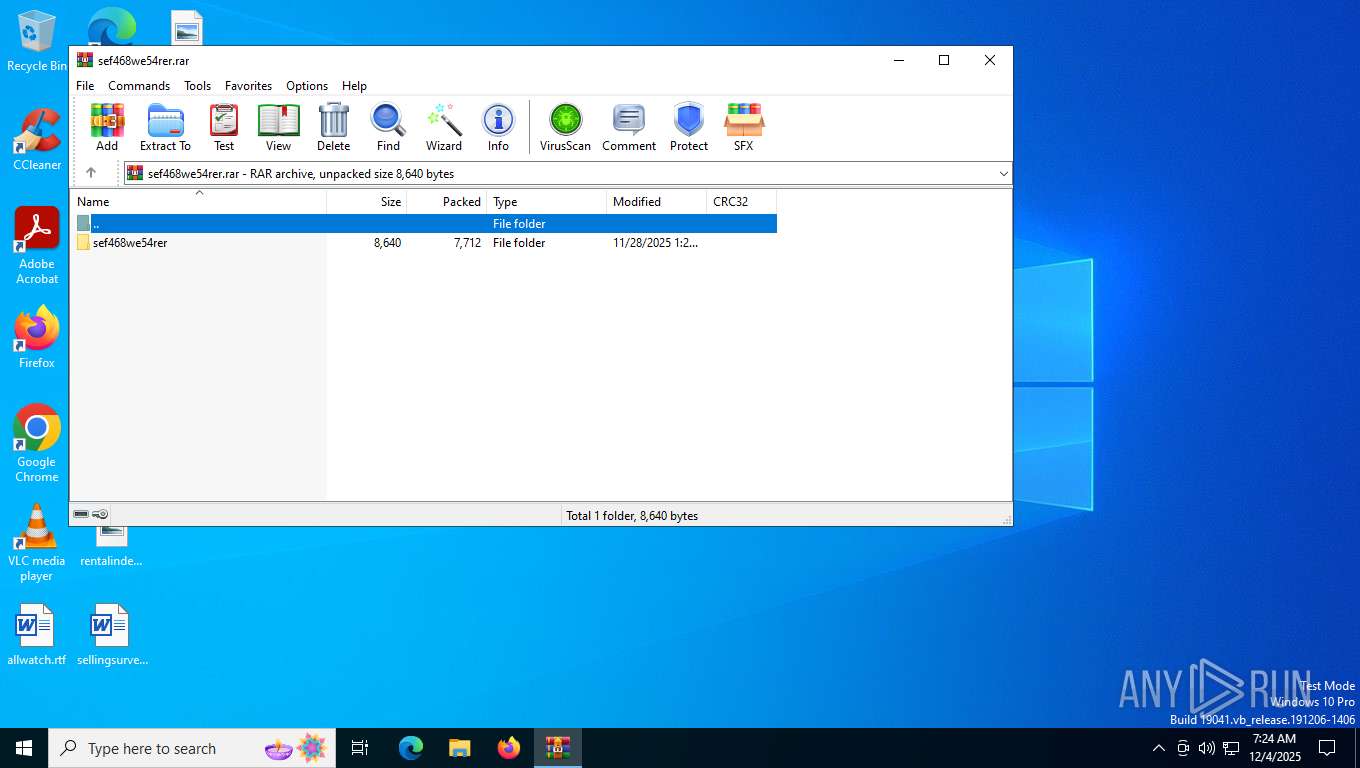
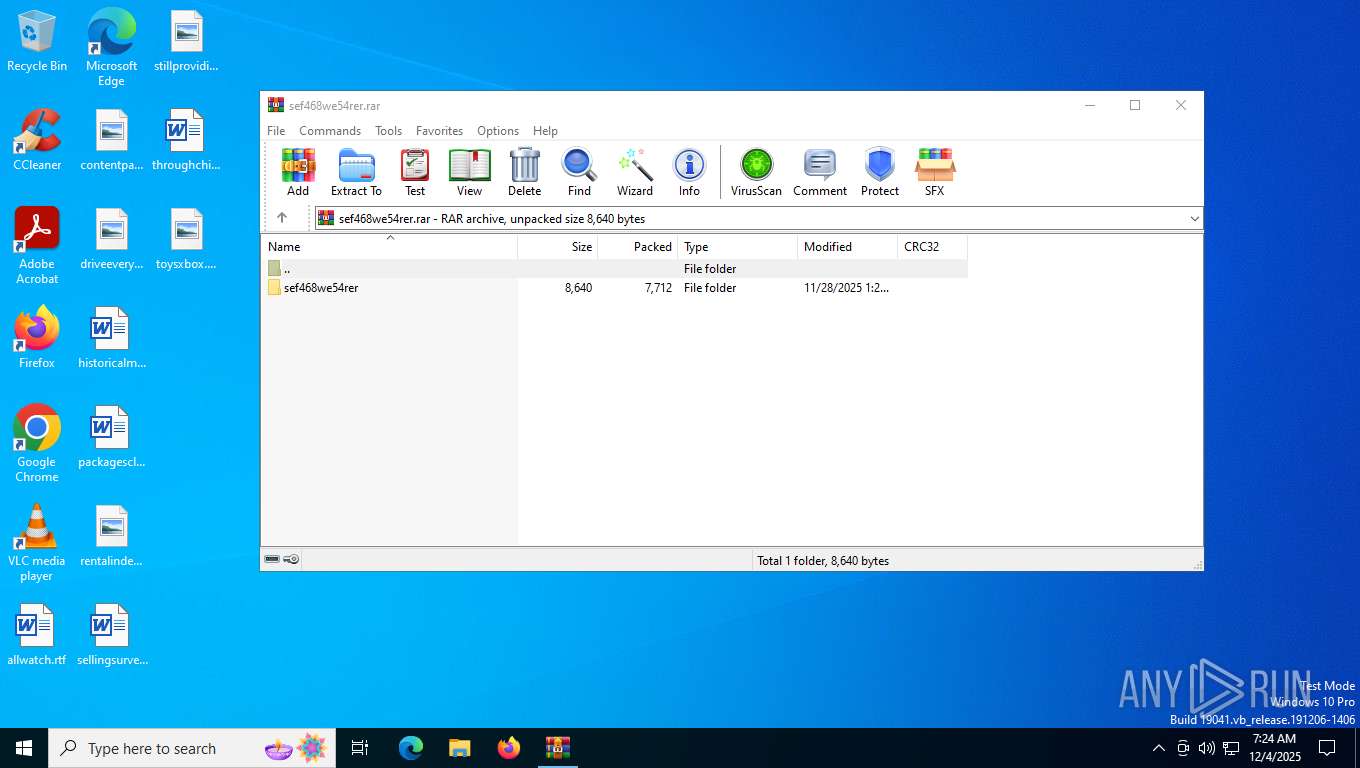
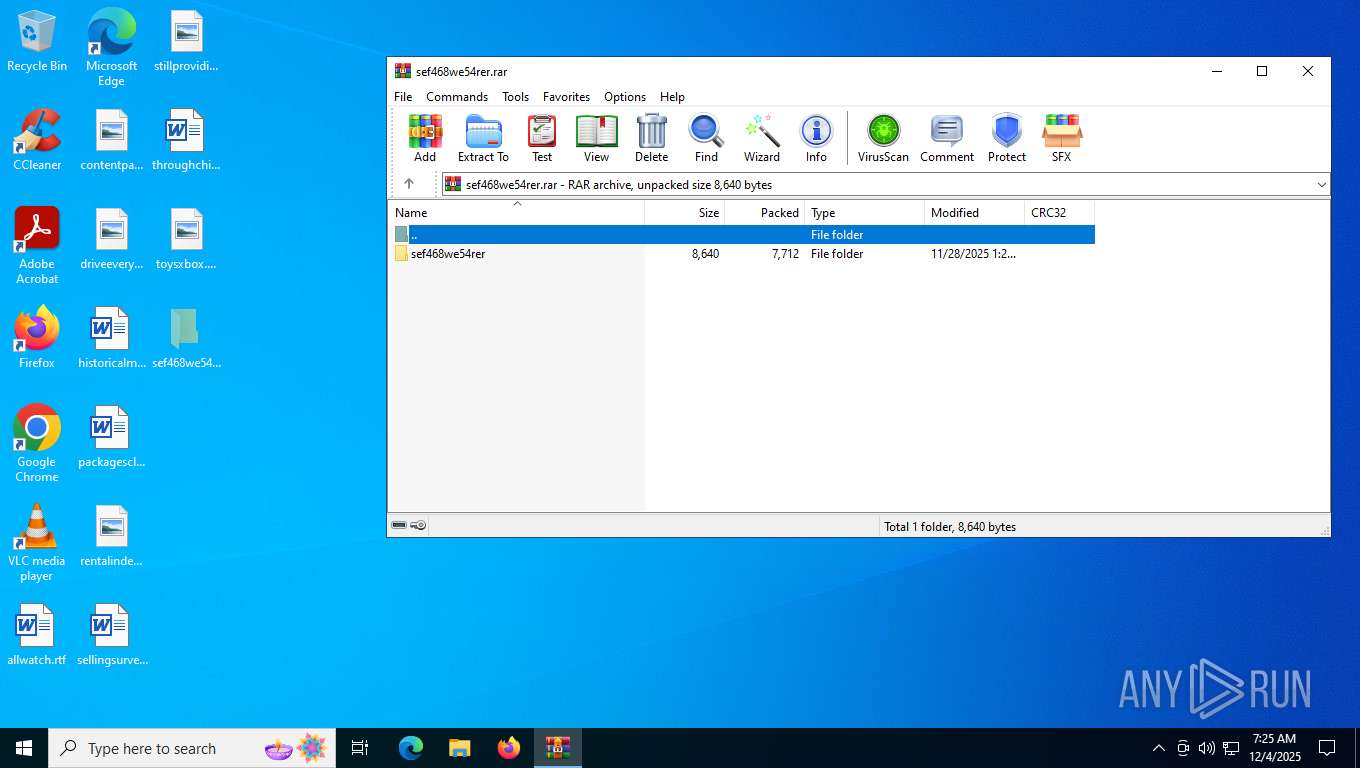
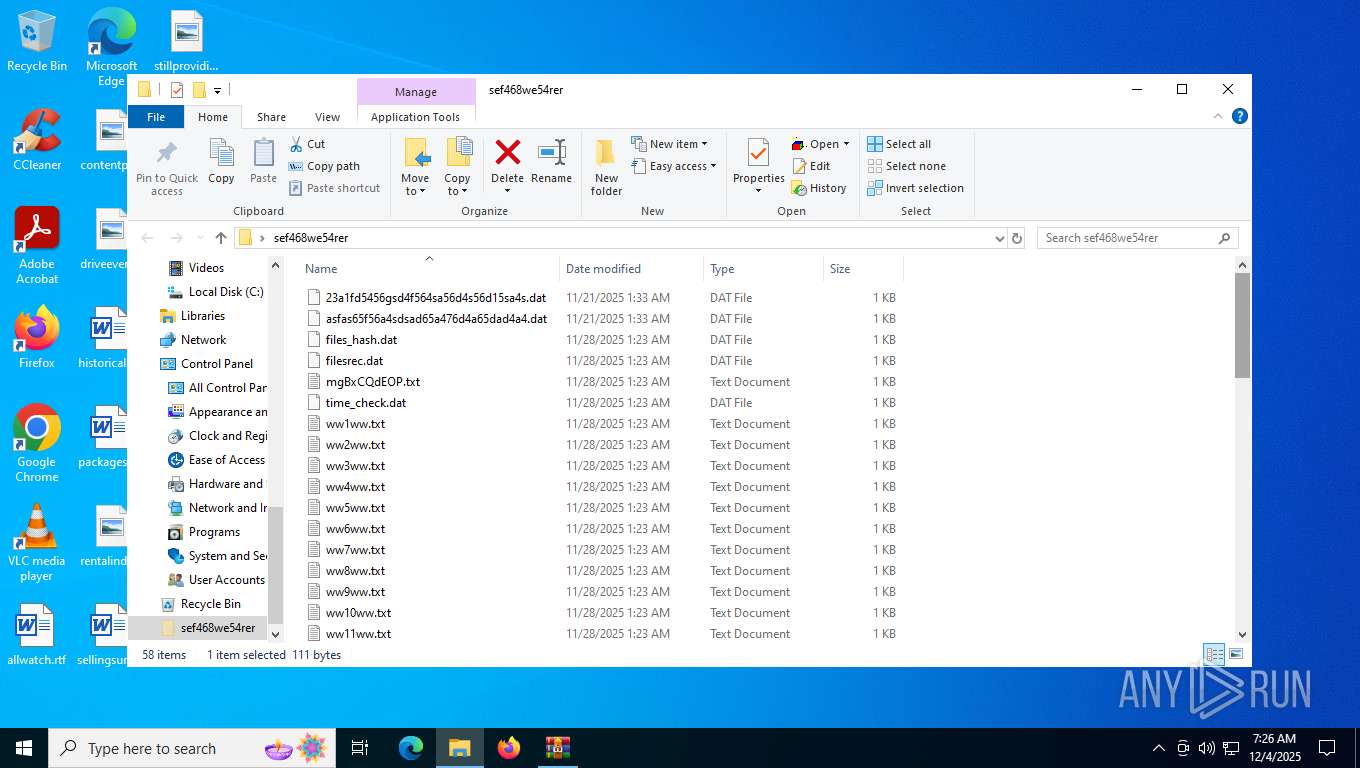
| File name: | sef468we54rer.rar |
| Full analysis: | https://app.any.run/tasks/edd1c6b5-a2ff-47ff-9789-31a5c53b5cb1 |
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2025, 07:24:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 0CEC6260C3ED918203BBB31F4CC53A44 |
| SHA1: | 7644FD8D4BD138D4D696423BC3BFB43A72C733A9 |
| SHA256: | BAEBC0FC22F337DF4AAA5FBCCA9F571F9C9F21F21C8CE48C3187ED34AAD92B34 |
| SSDEEP: | 384:nj9NjHe32nV0F61W7mSQDt7CBH1wdDqx2Hc:nZNjHe32nVnW7mS1BVCOQ8 |
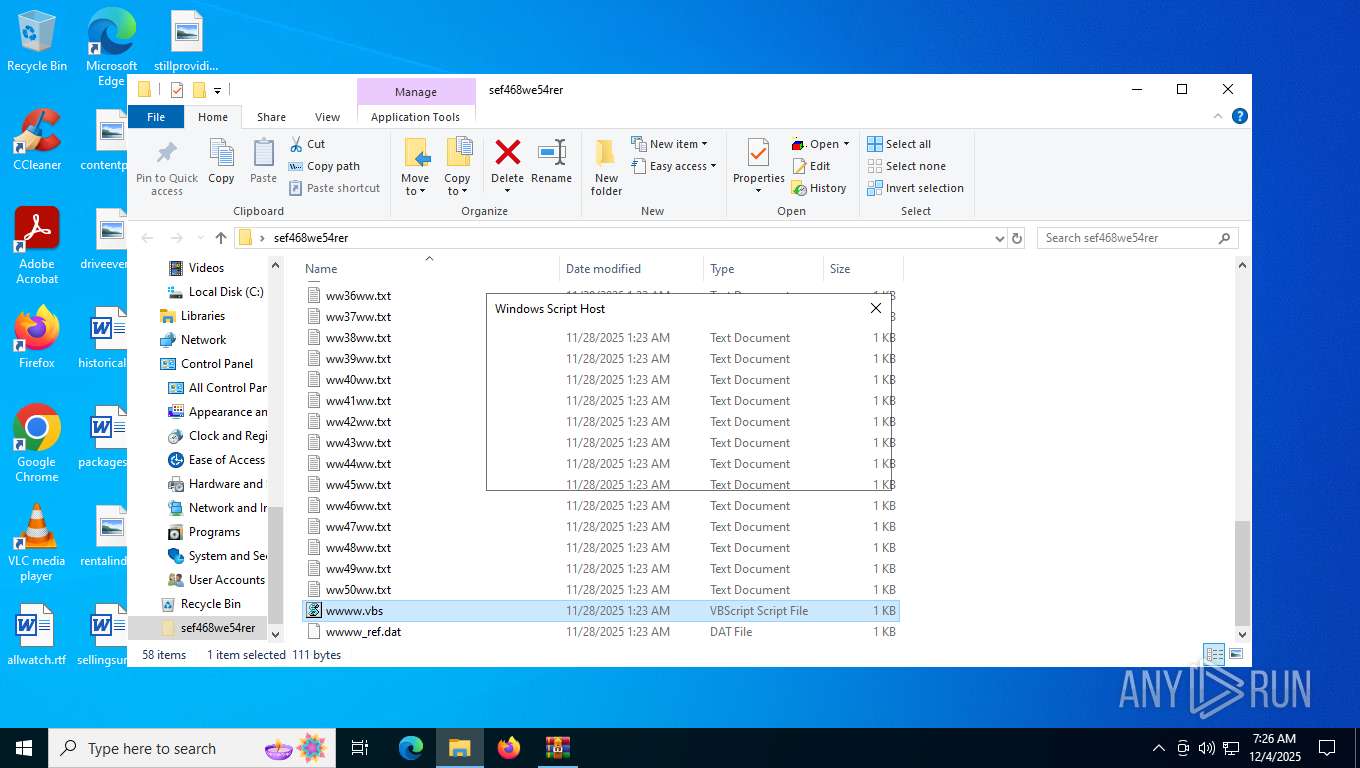
MALICIOUS
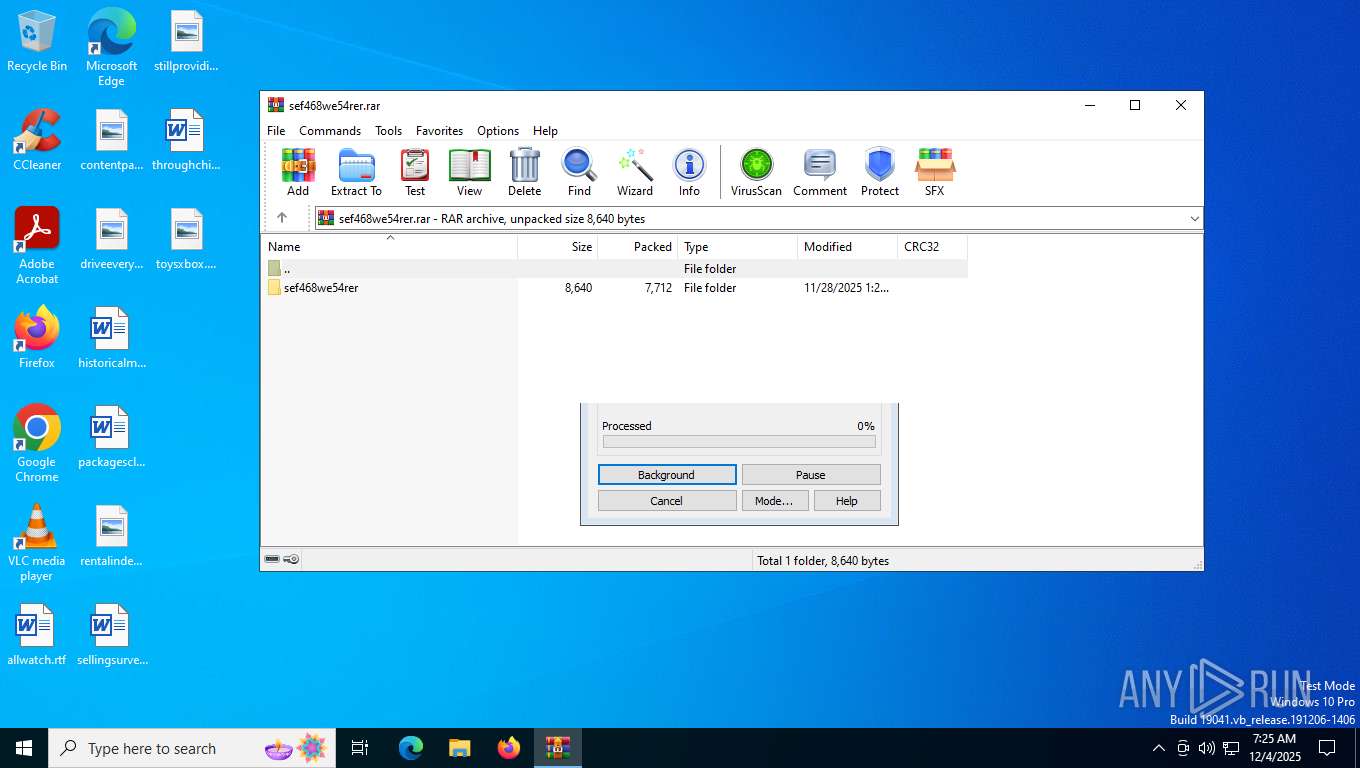
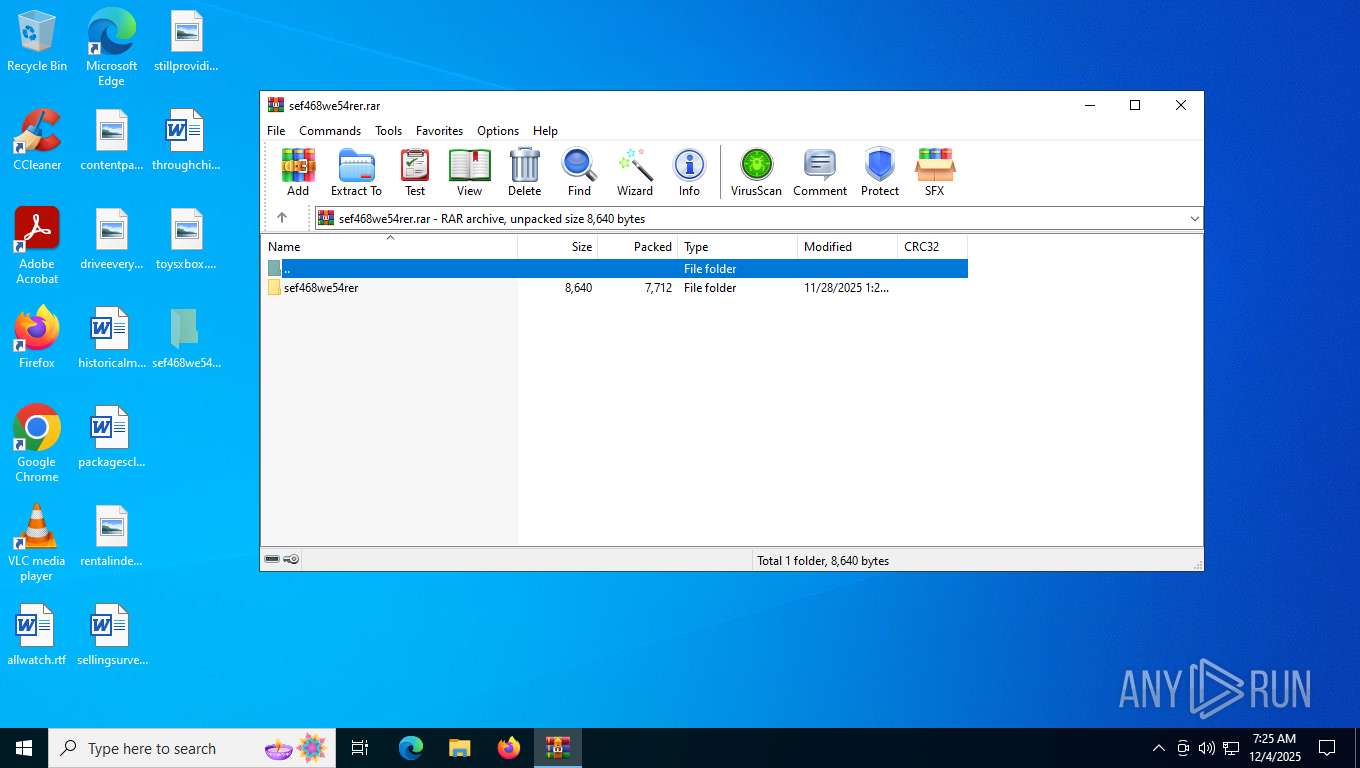
Generic archive extractor
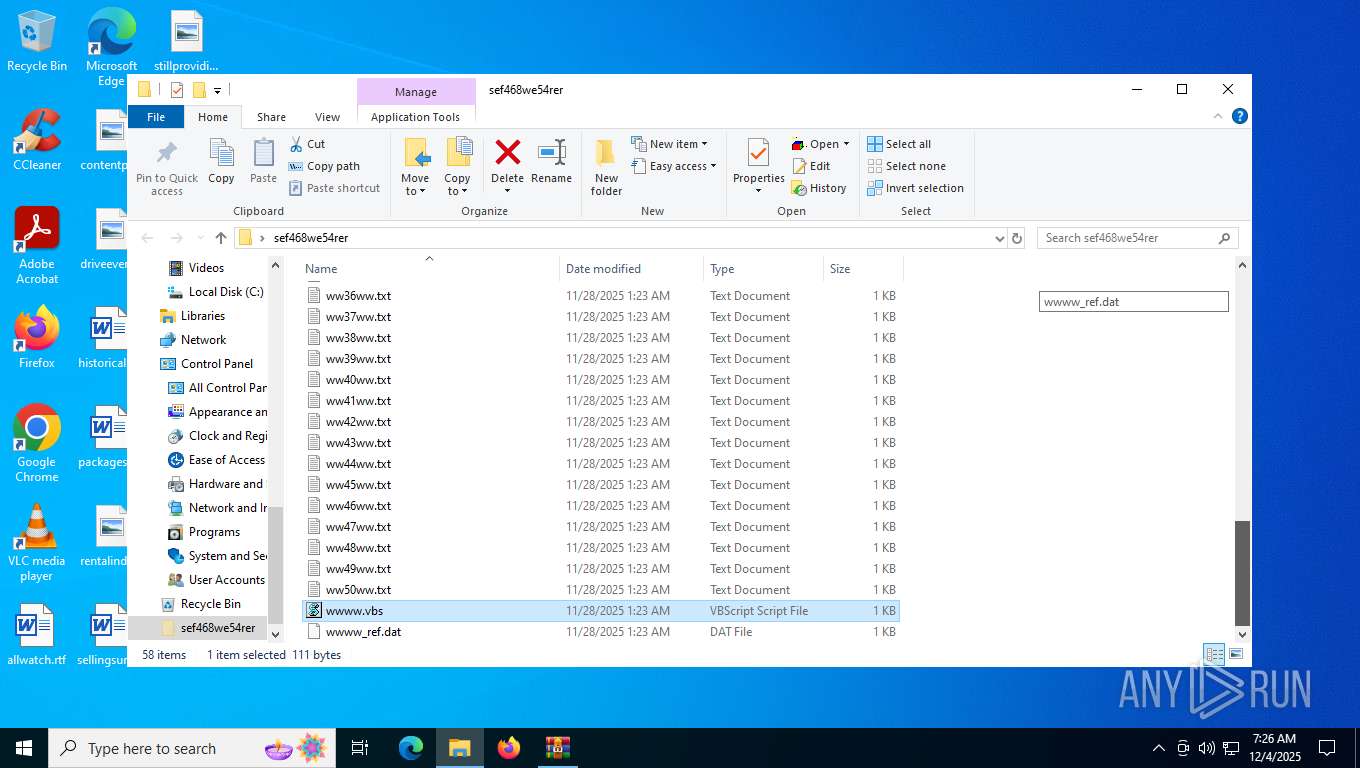
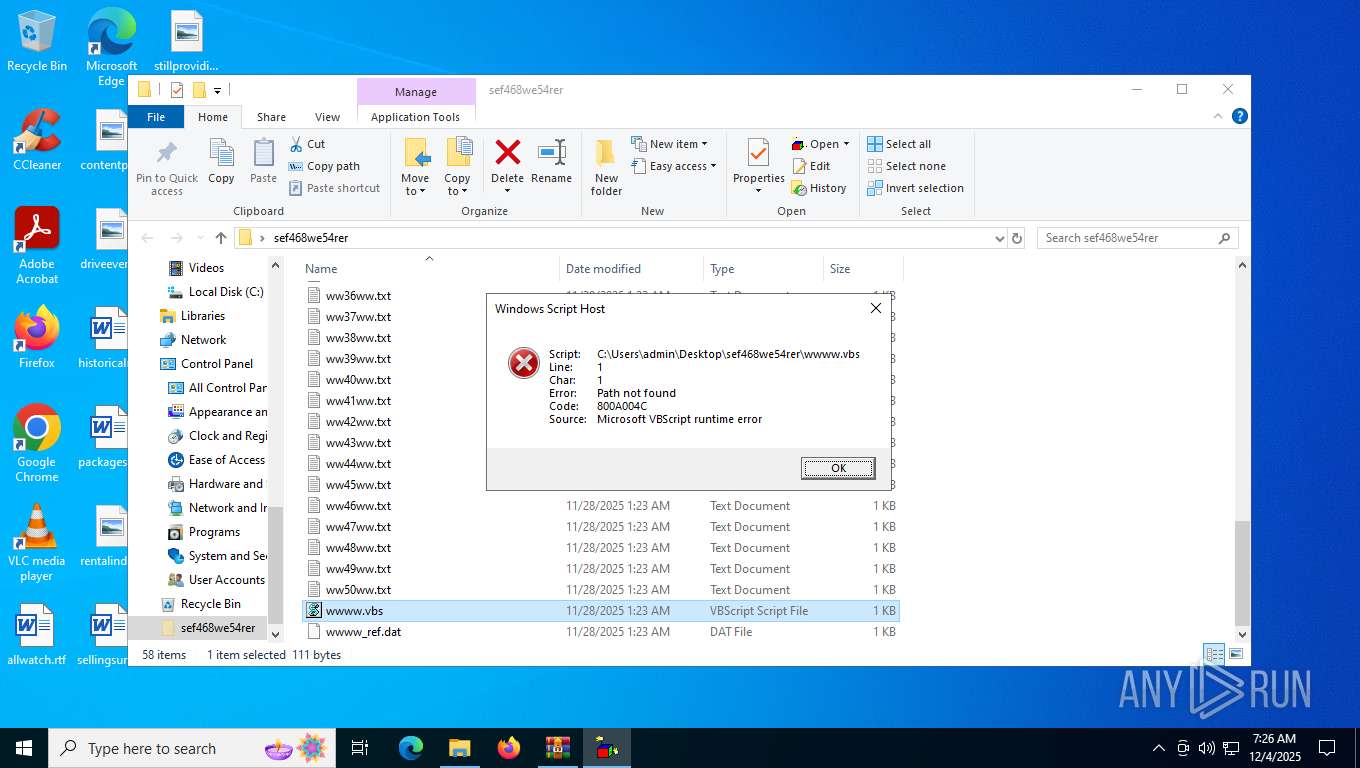
- WinRAR.exe (PID: 7356)
Opens a text file (SCRIPT)
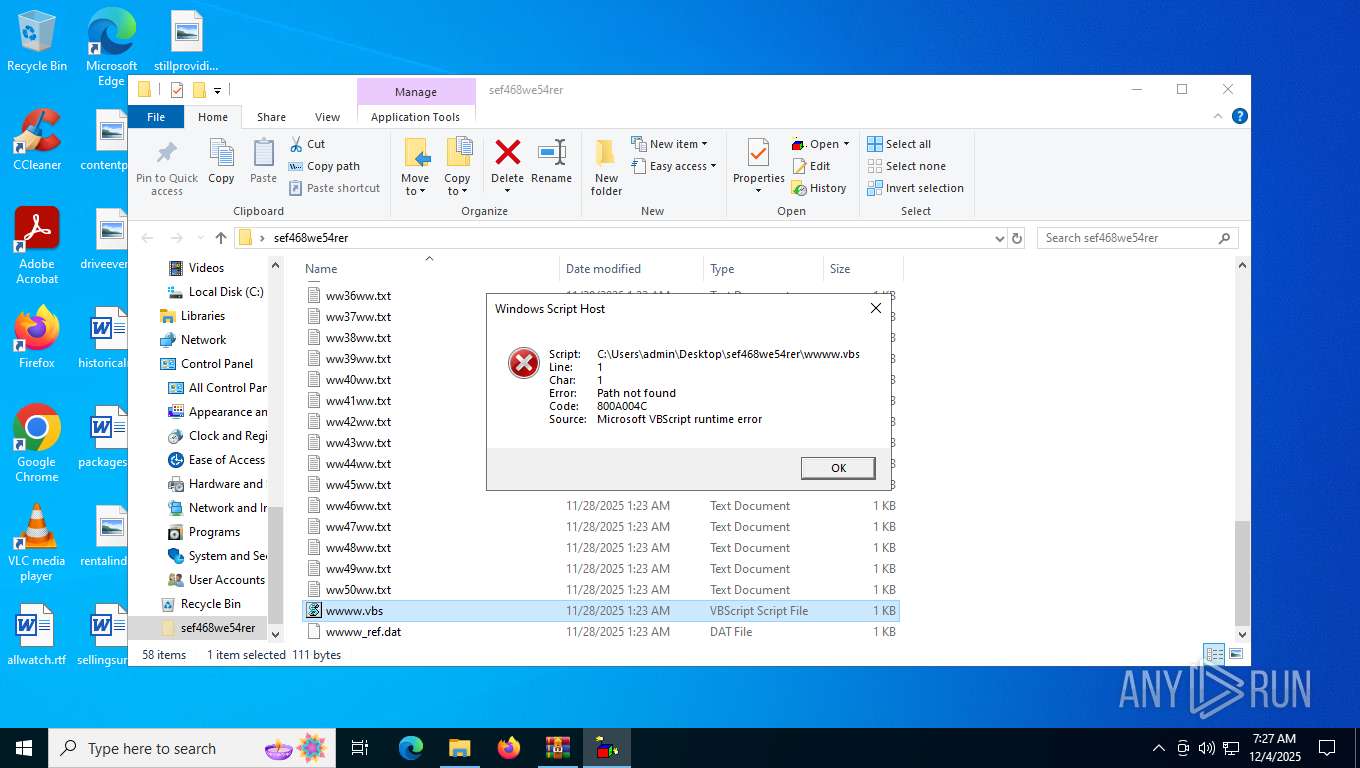
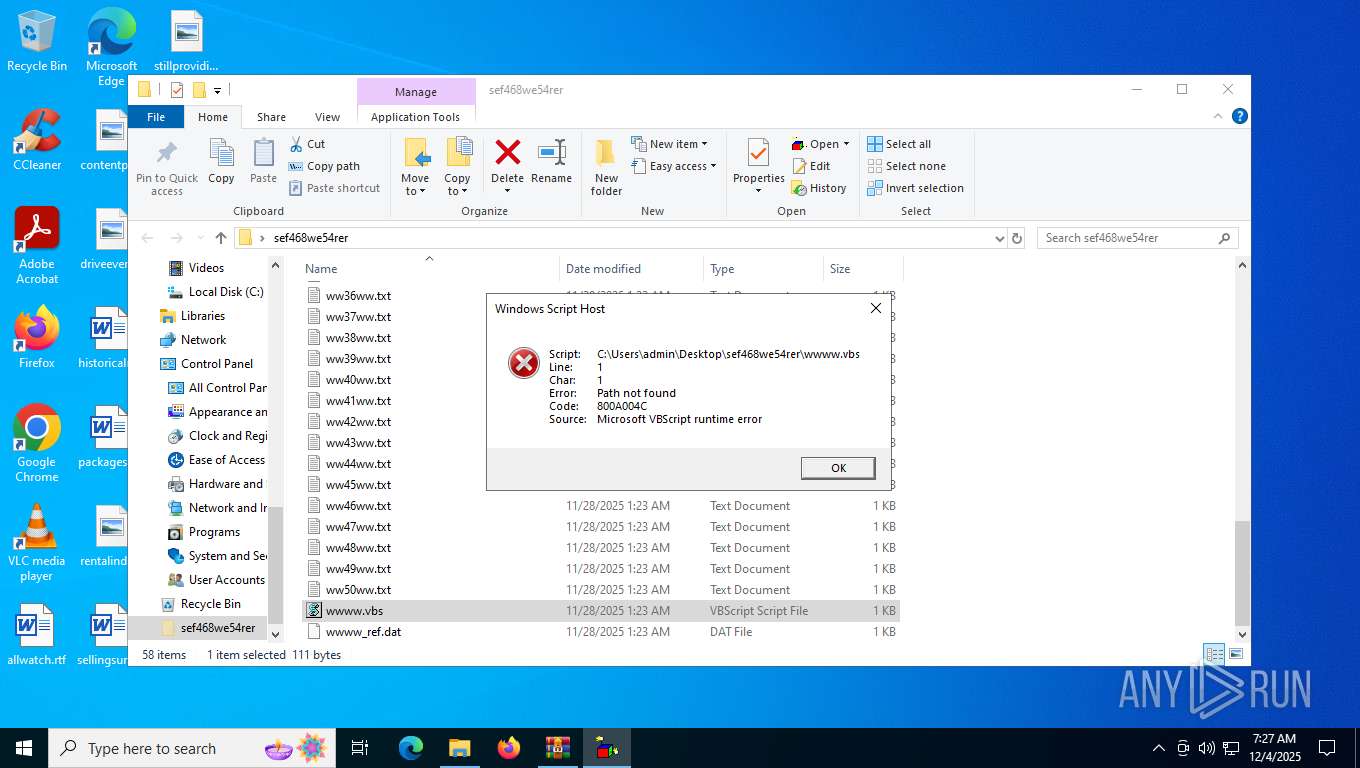
- wscript.exe (PID: 7516)
- wscript.exe (PID: 3956)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7516)
- wscript.exe (PID: 3956)
INFO
Manual execution by a user
- wscript.exe (PID: 7516)
- wscript.exe (PID: 3956)
Checks proxy server information
- slui.exe (PID: 8176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 4 |
| UncompressedSize: | 4 |
| OperatingSystem: | Win32 |
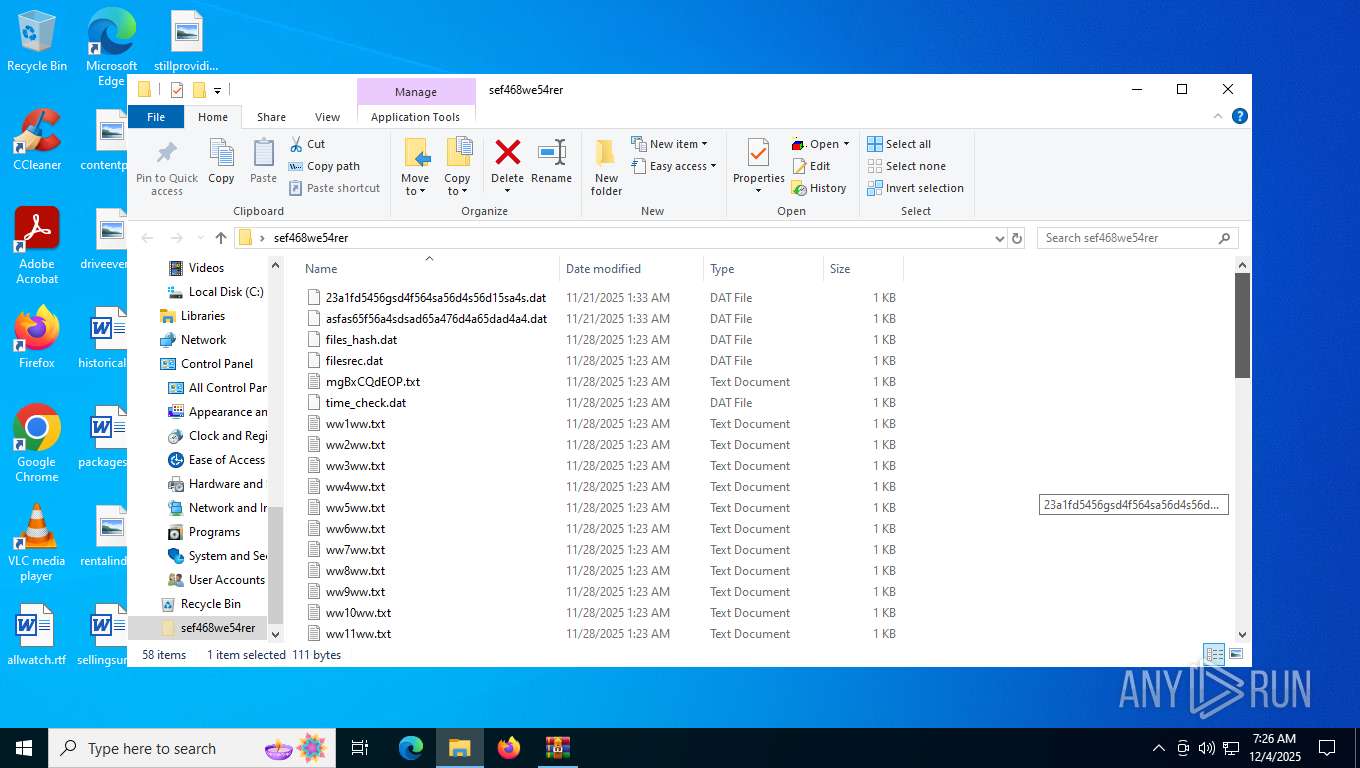
| ArchivedFileName: | sef468we54rer/23a1fd5456gsd4f564sa56d4s56d15sa4s.dat |
Total processes
151
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
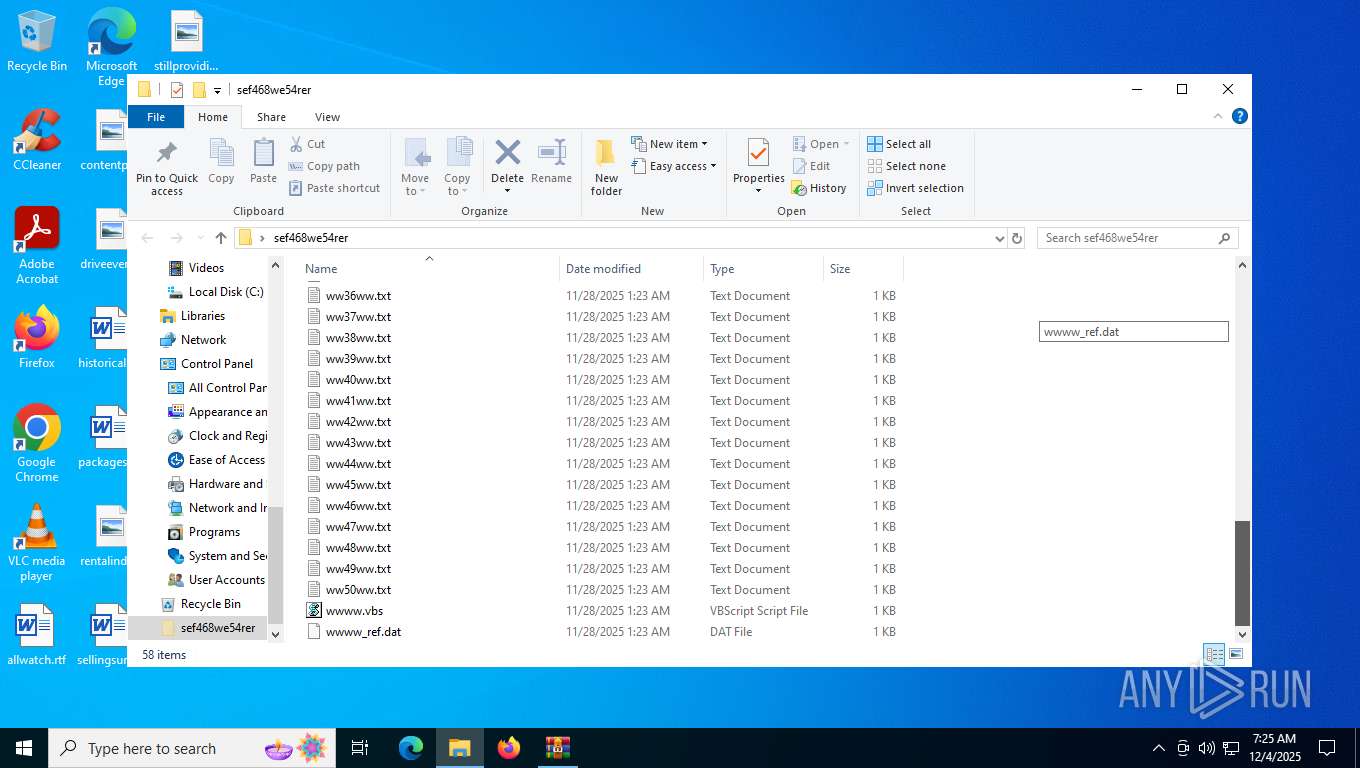
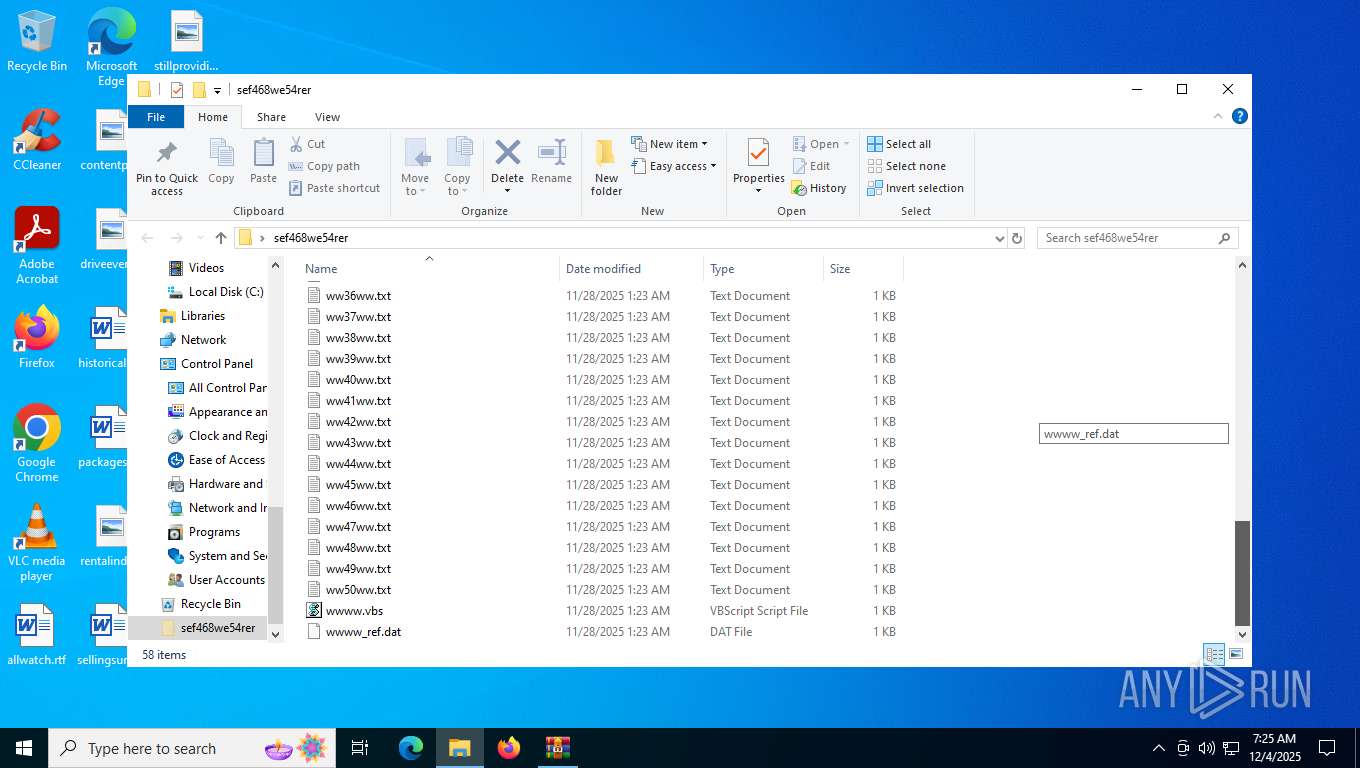
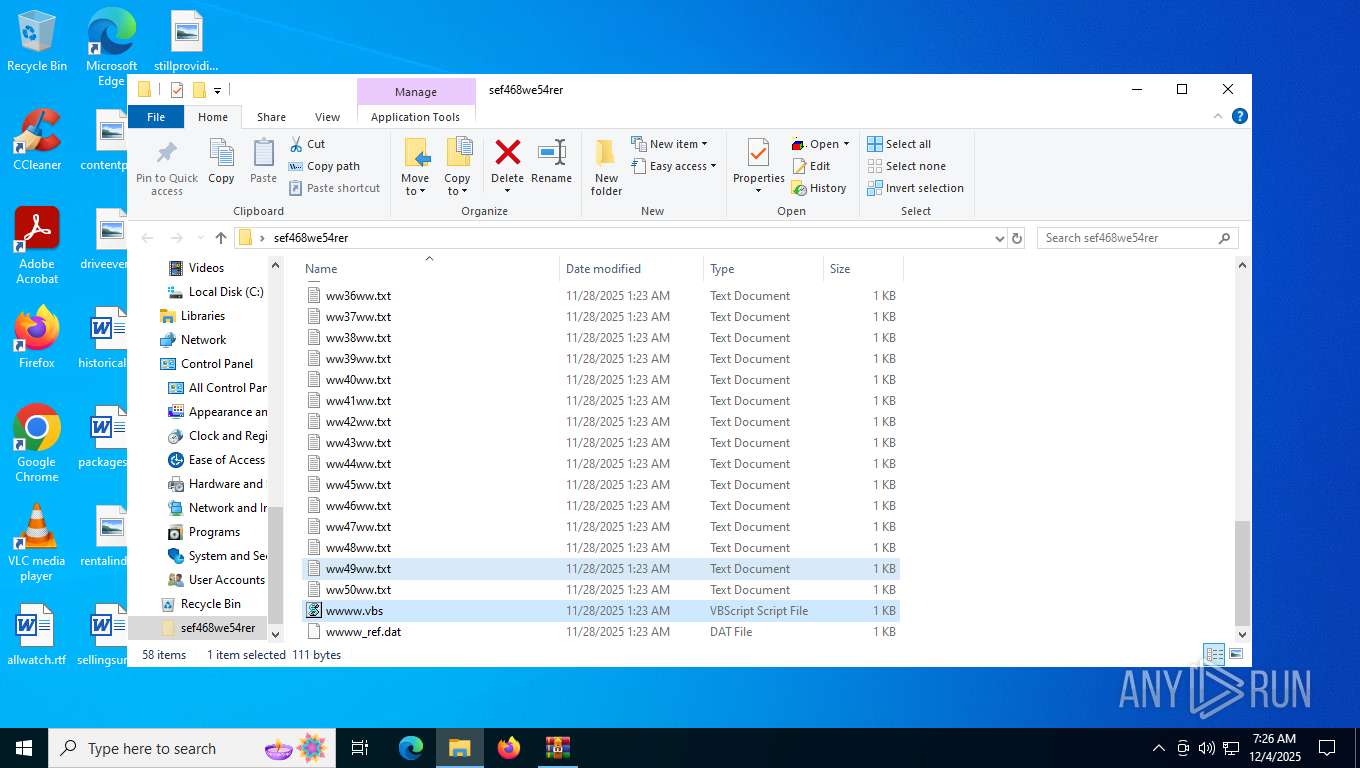
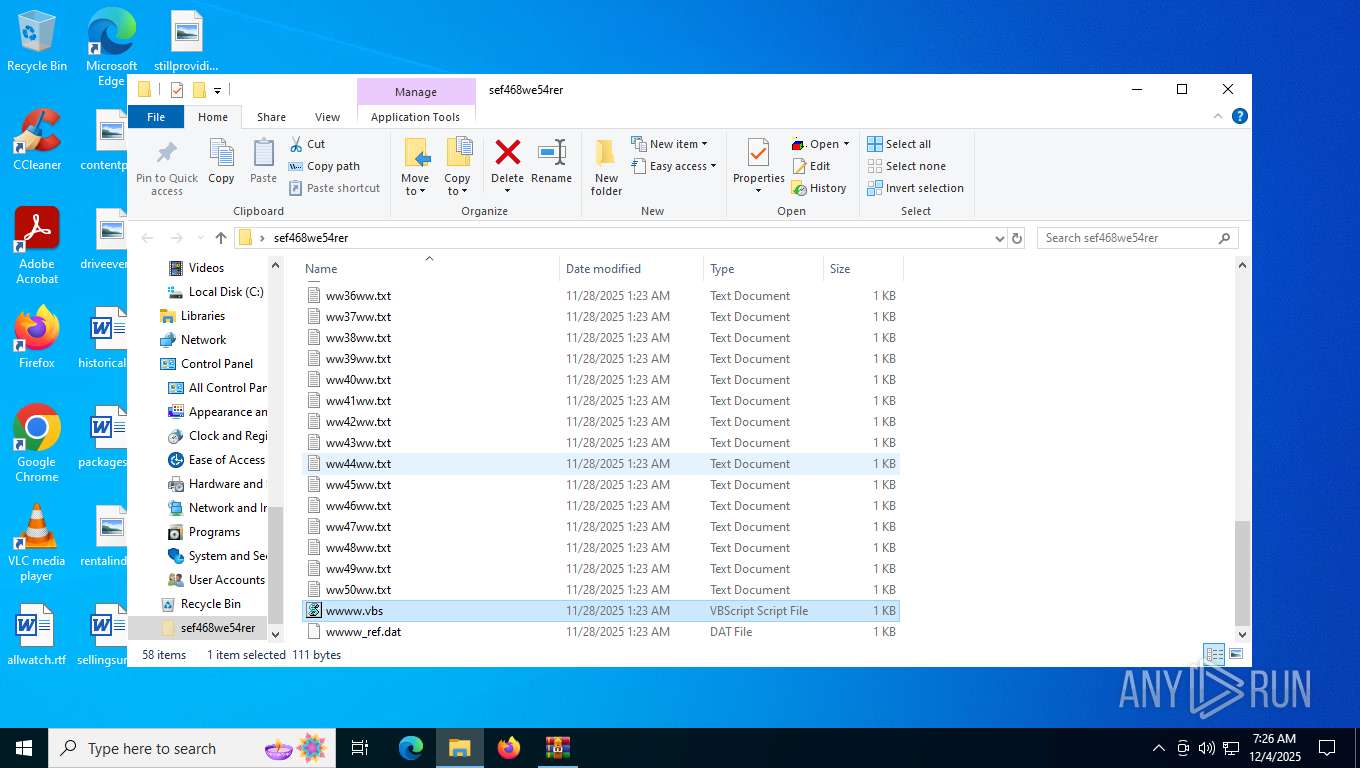
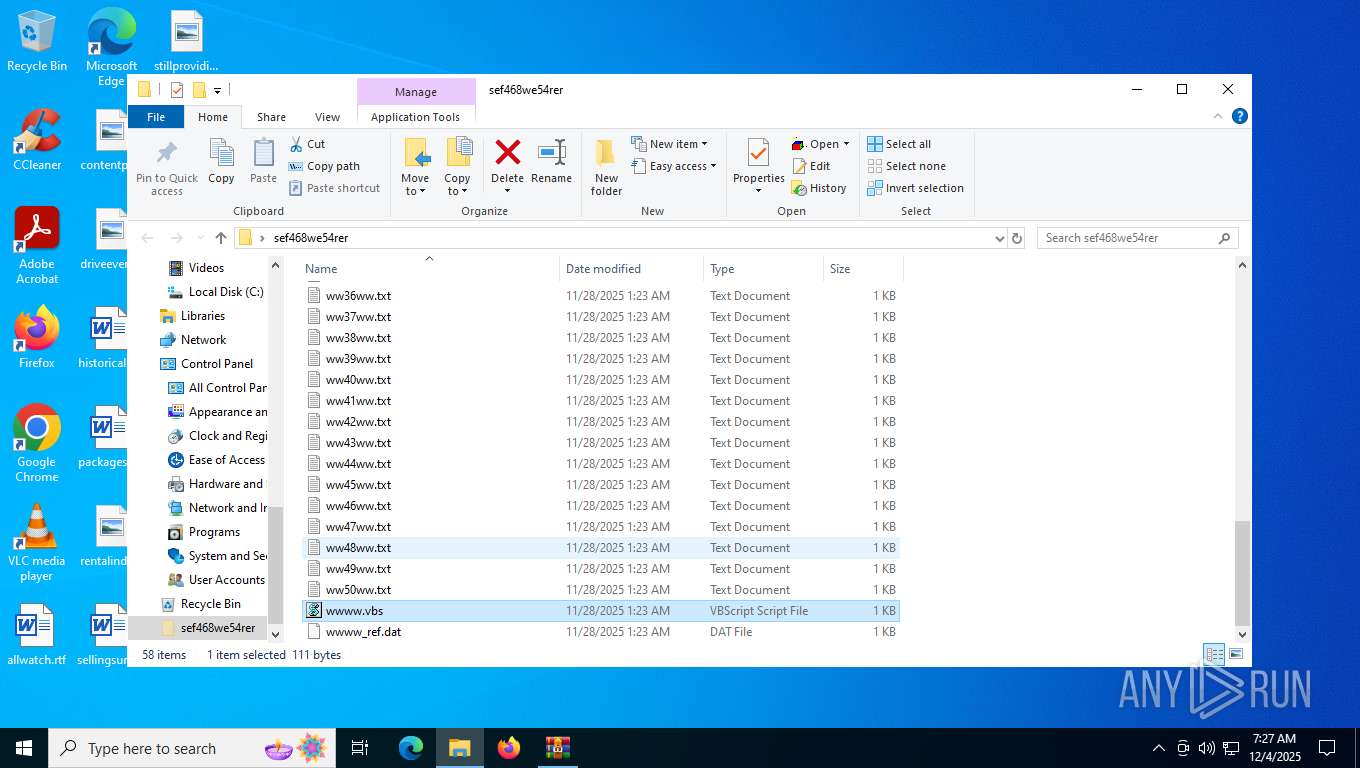
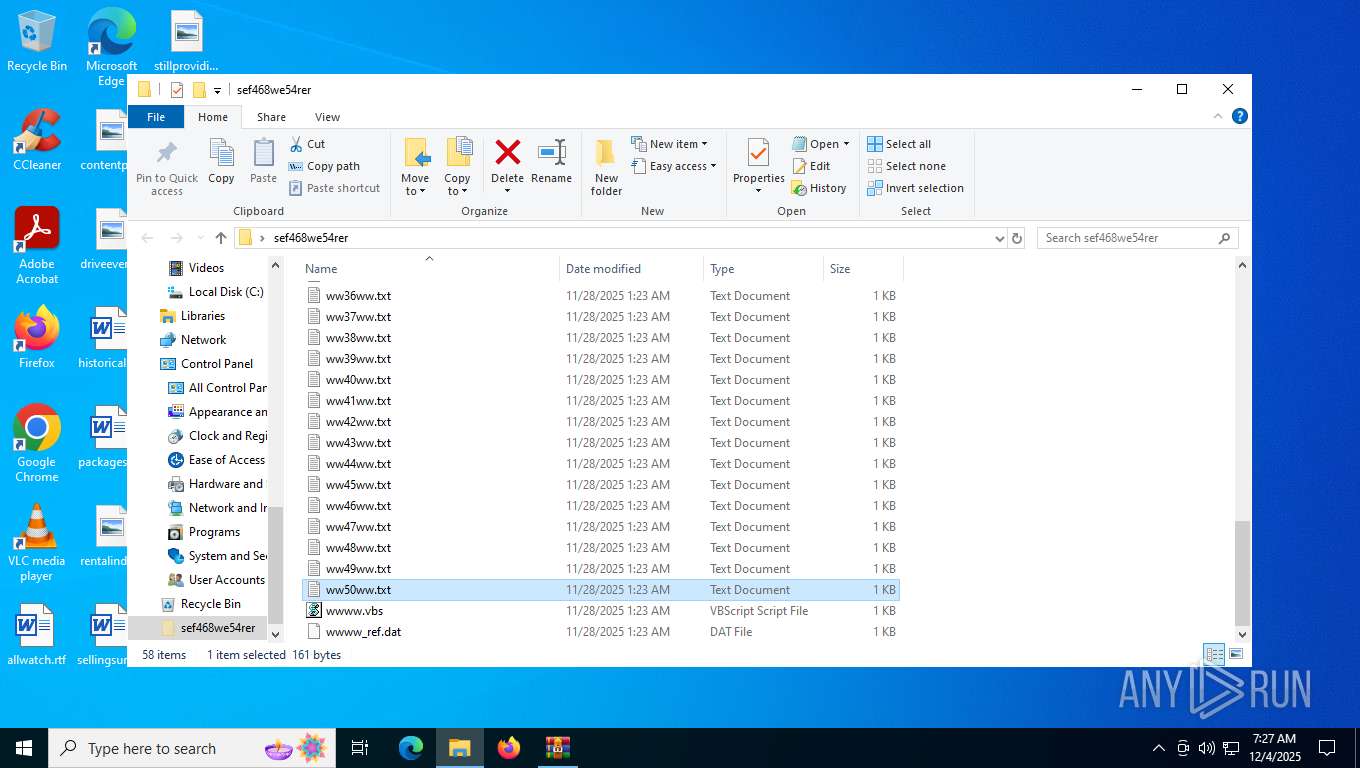
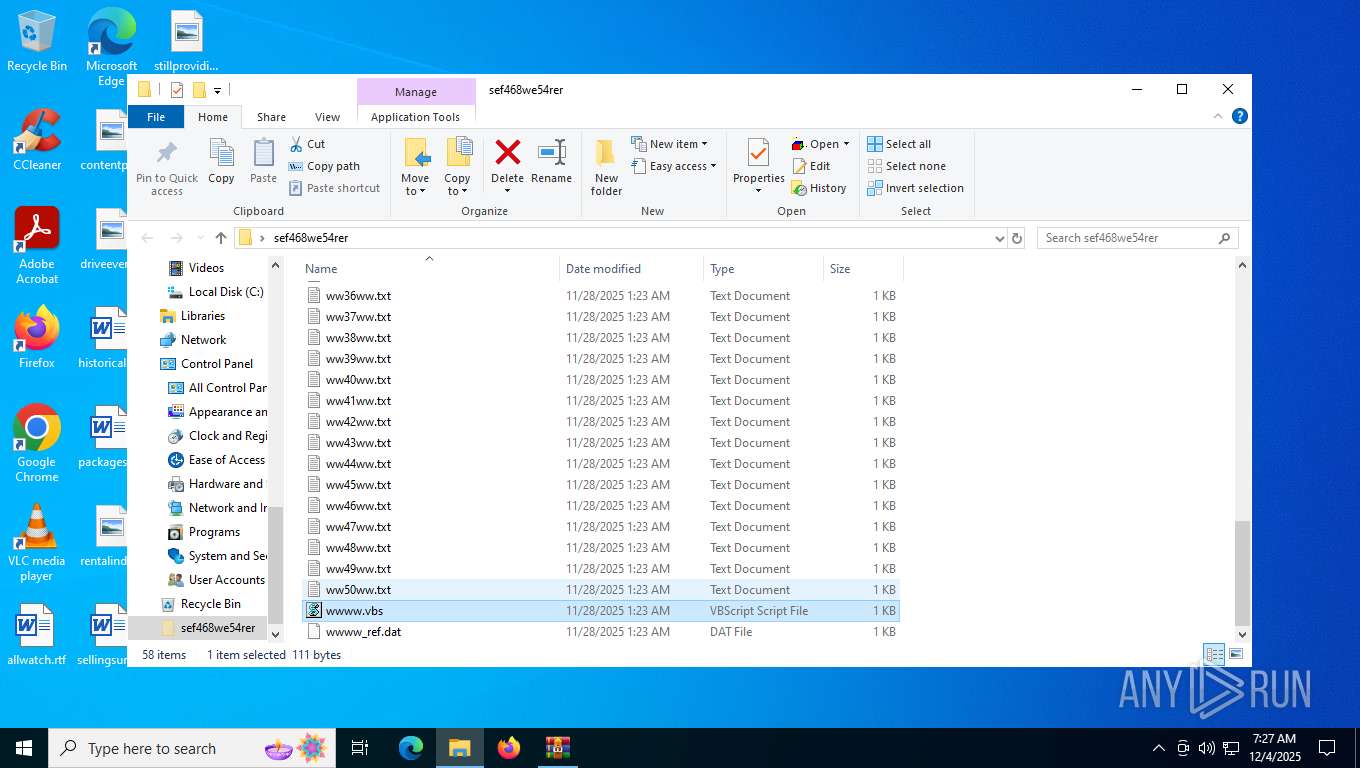
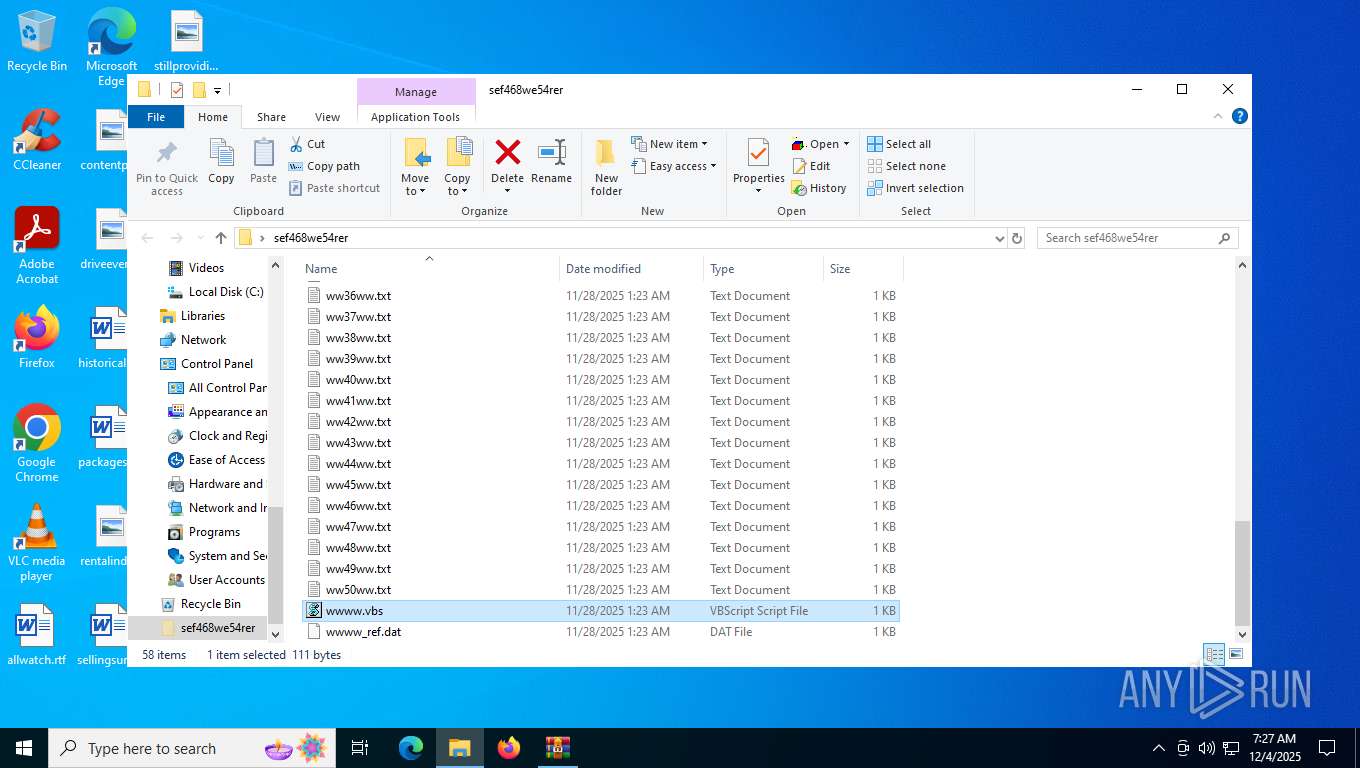
| 3956 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\sef468we54rer\wwww.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4888 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 5320 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x102c460,0x102c46c,0x102c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
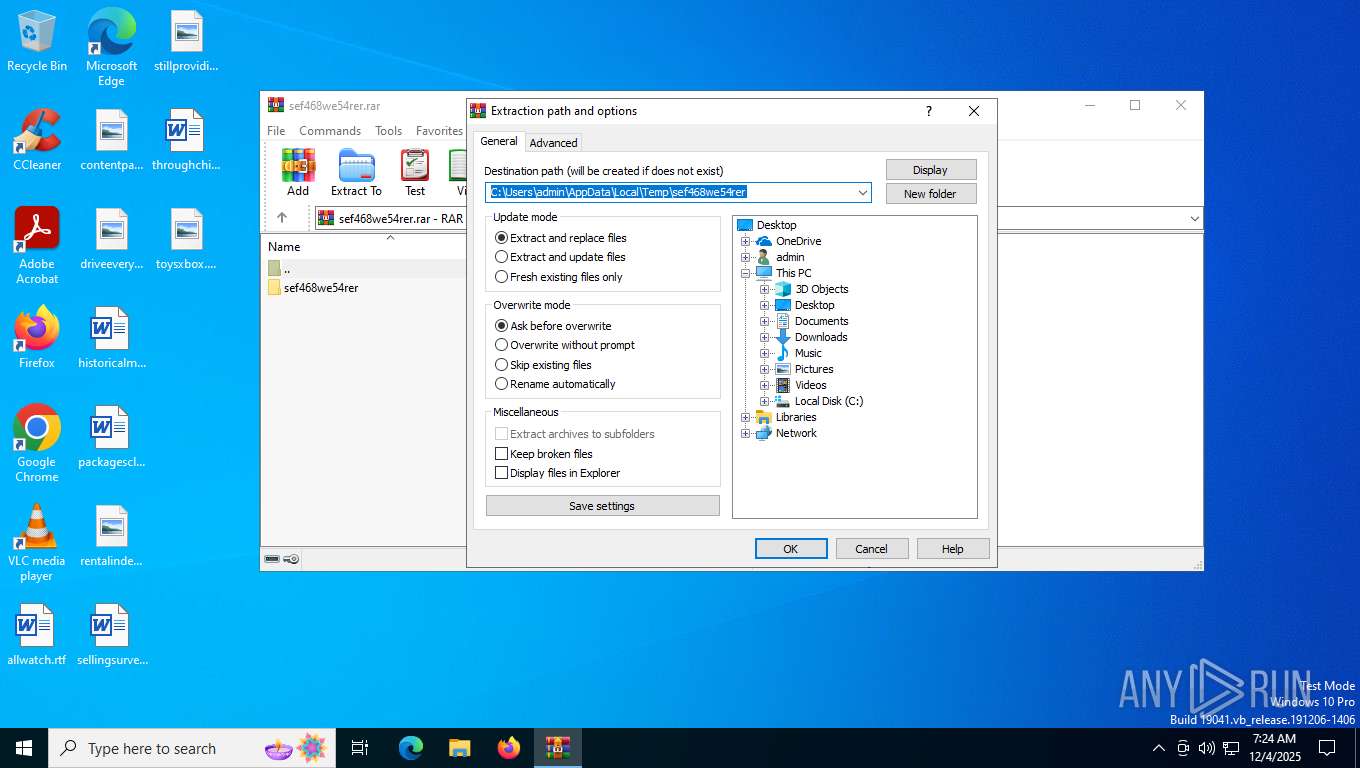
| 7356 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\sef468we54rer.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7516 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\sef468we54rer\wwww.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 8176 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 098
Read events
9 072
Write events
13
Delete events
13
Modification events
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sef468we54rer.rar | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7356) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
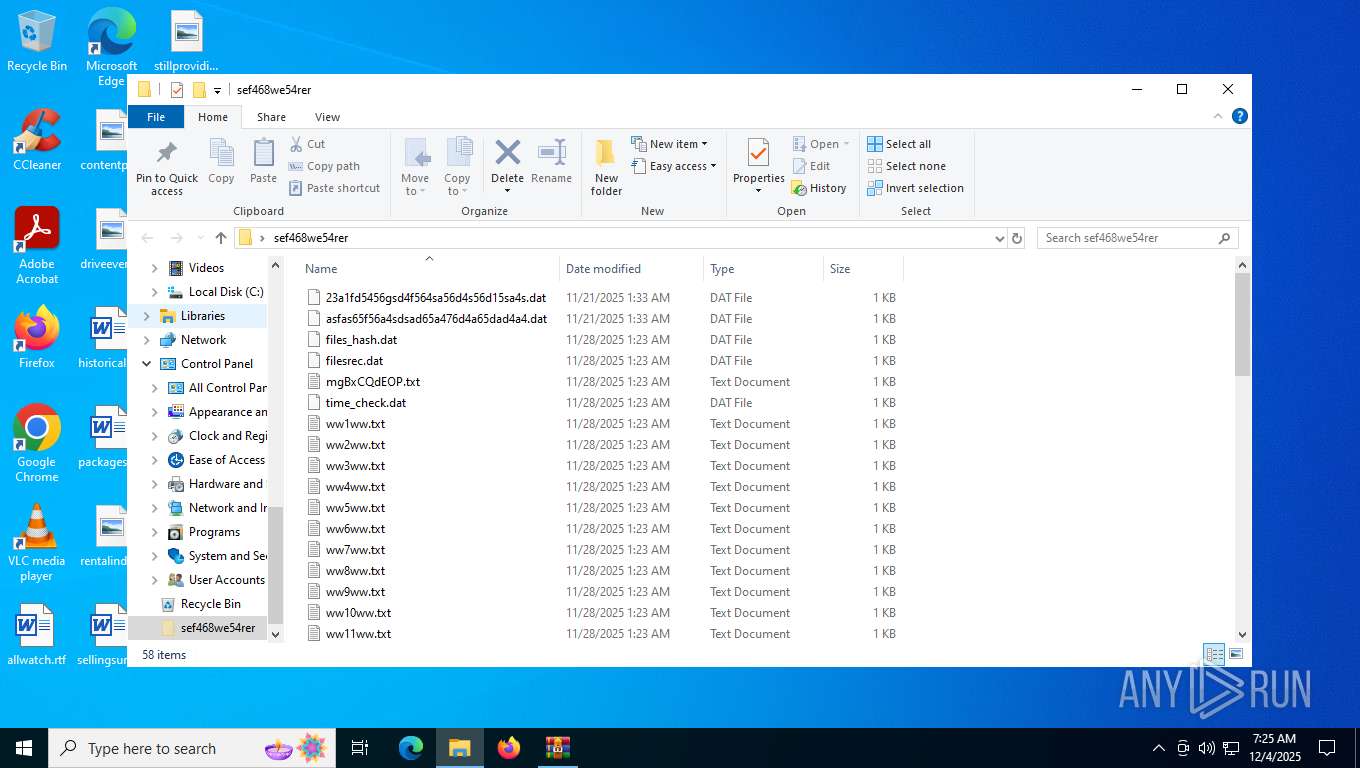
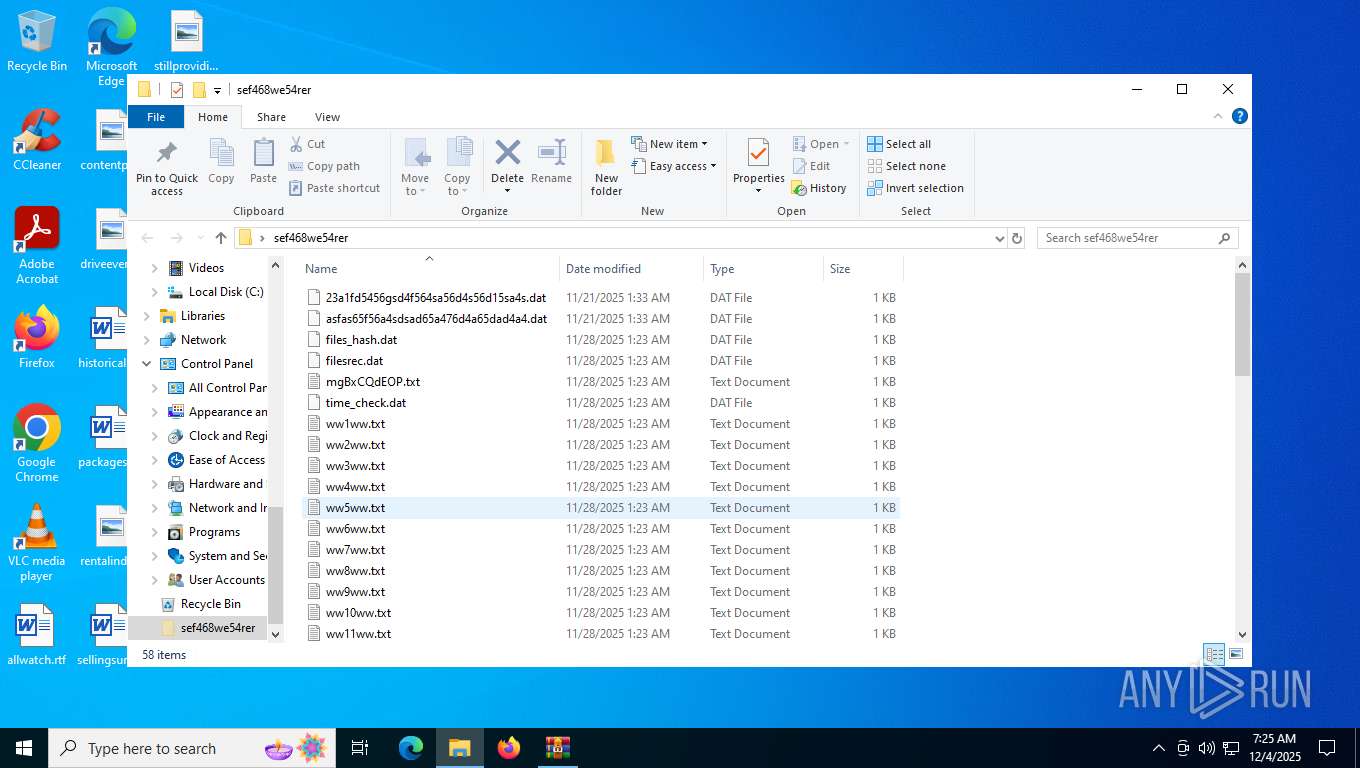
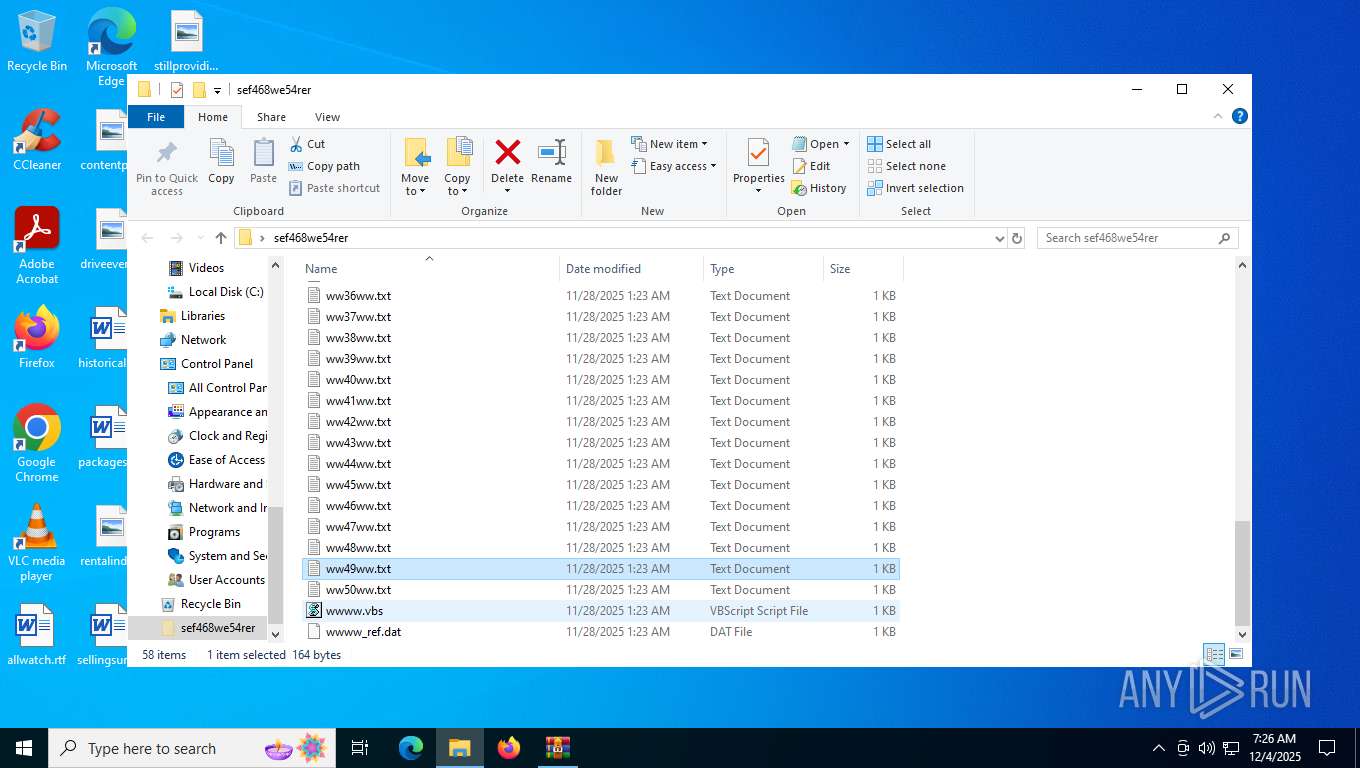
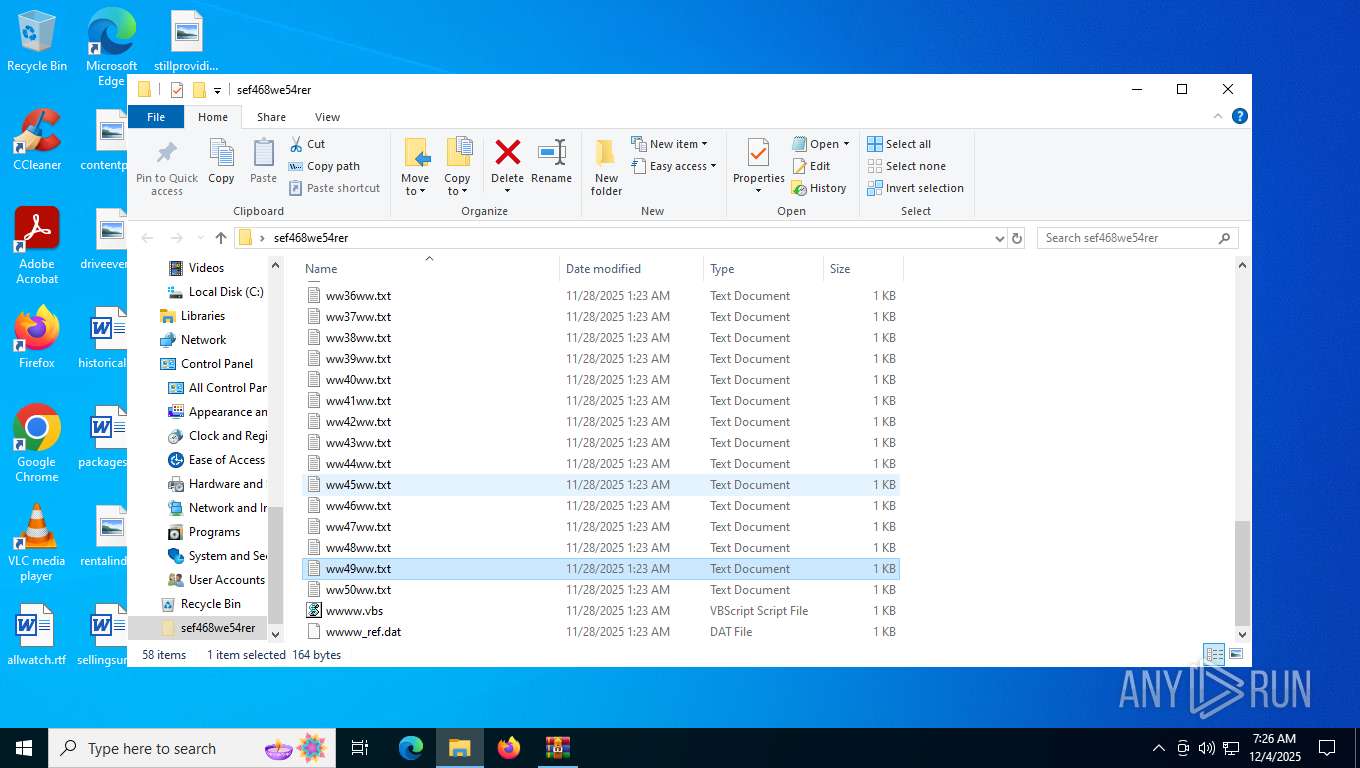
Executable files
0
Suspicious files
0
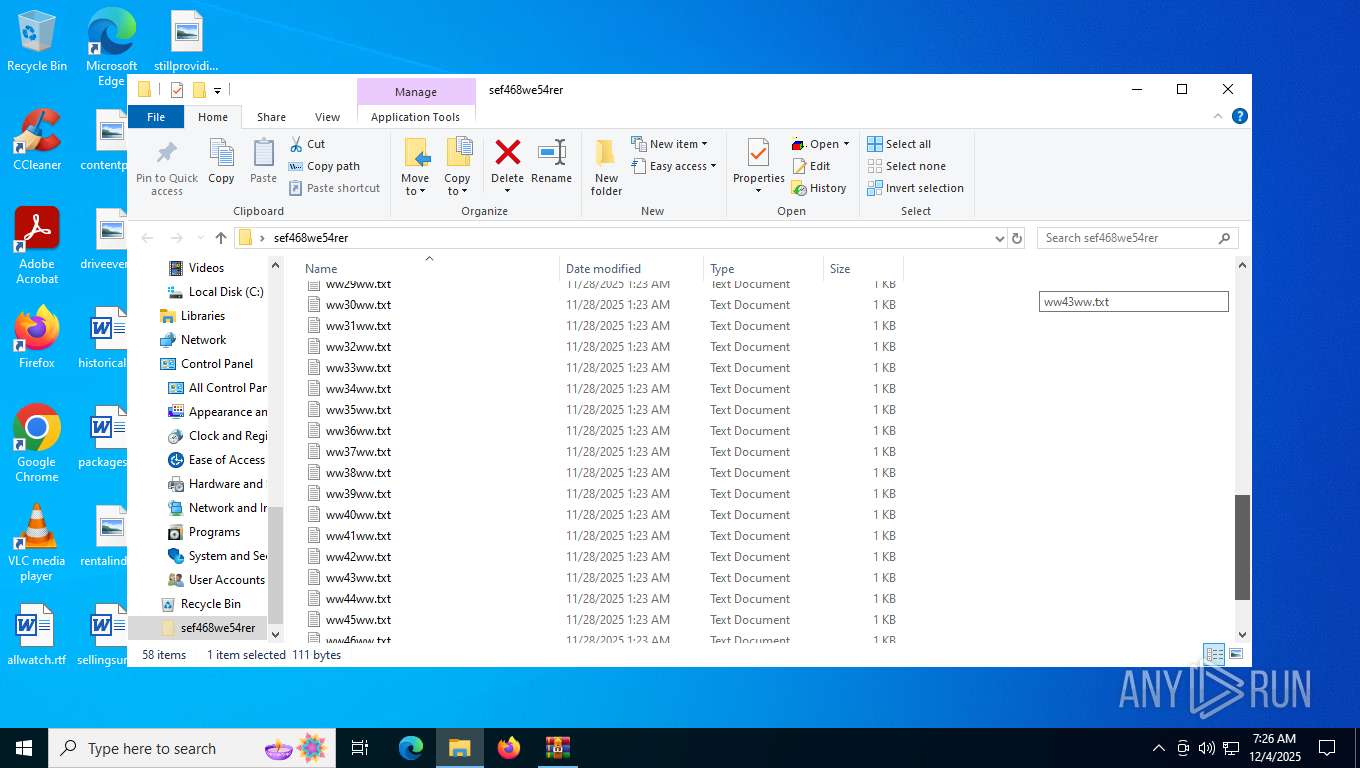
Text files
59
Unknown types
0
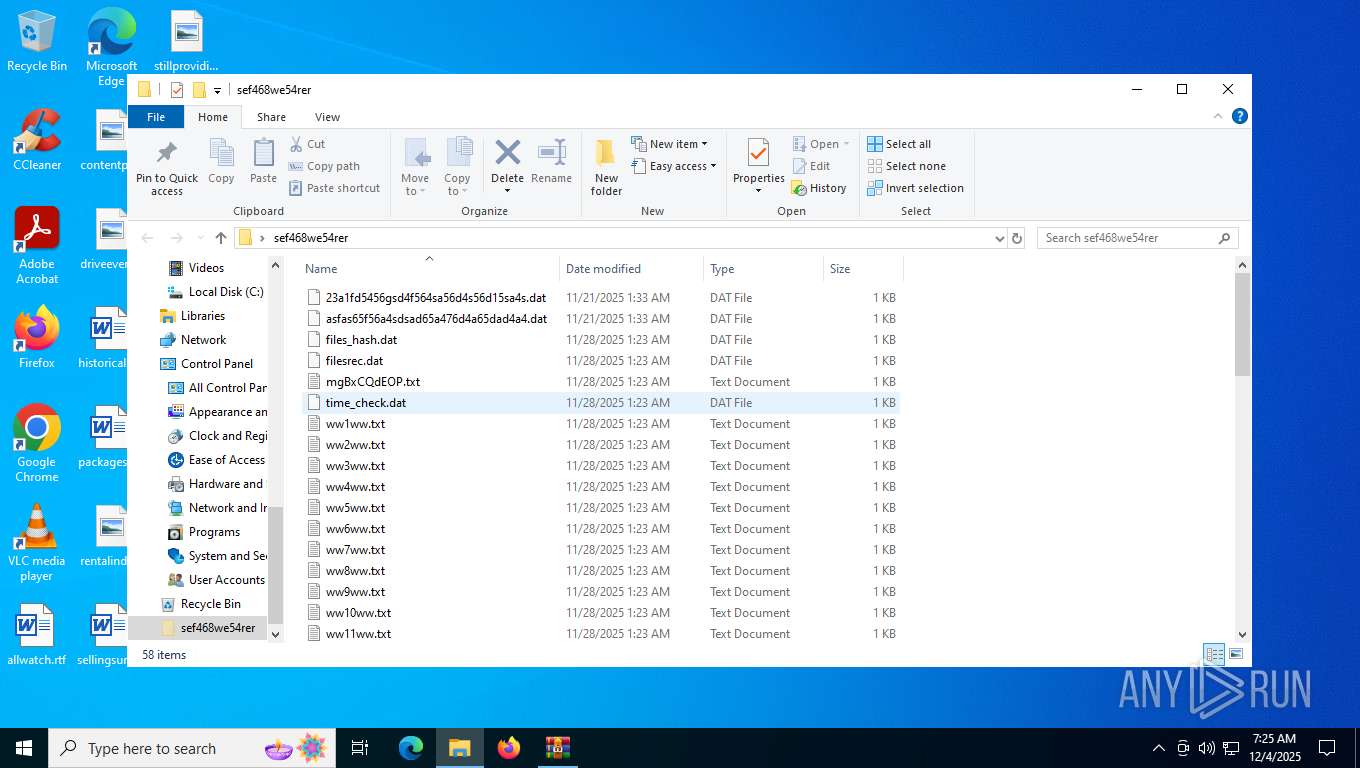
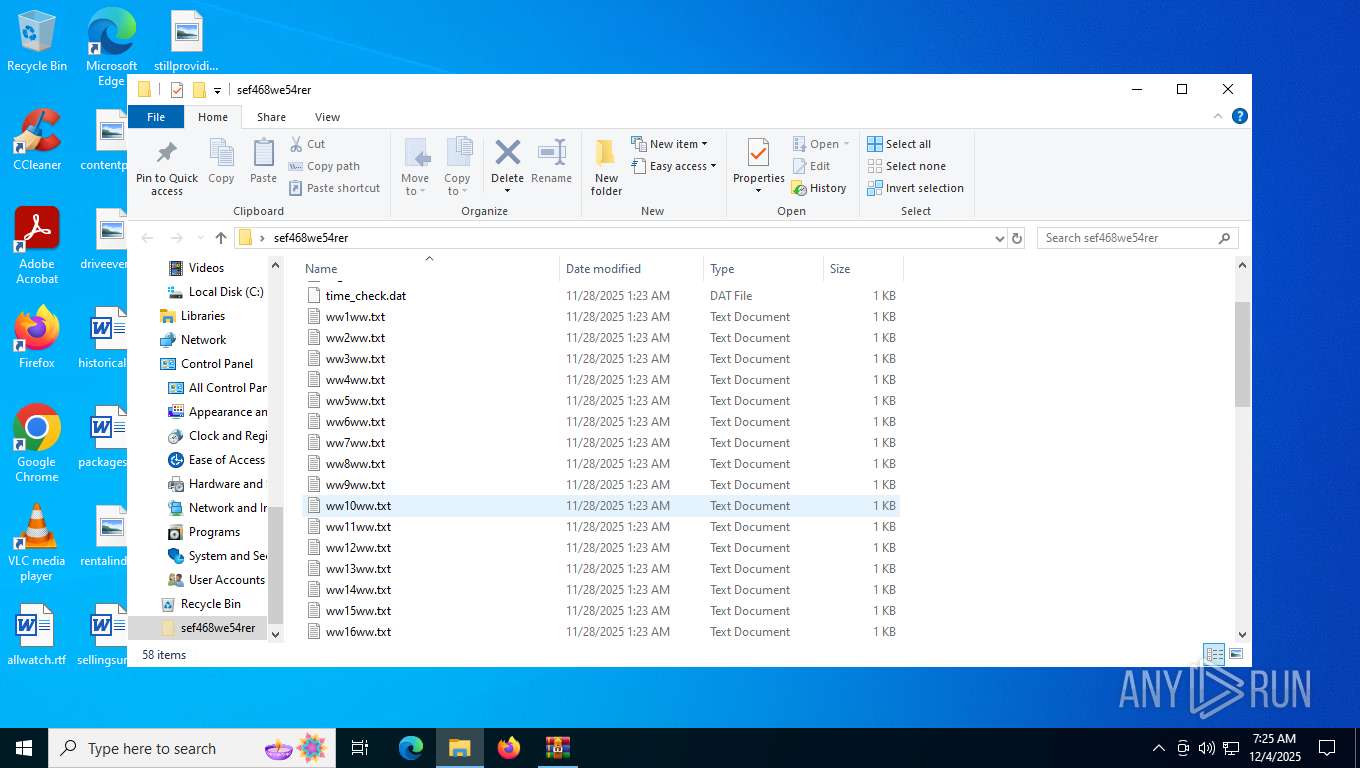
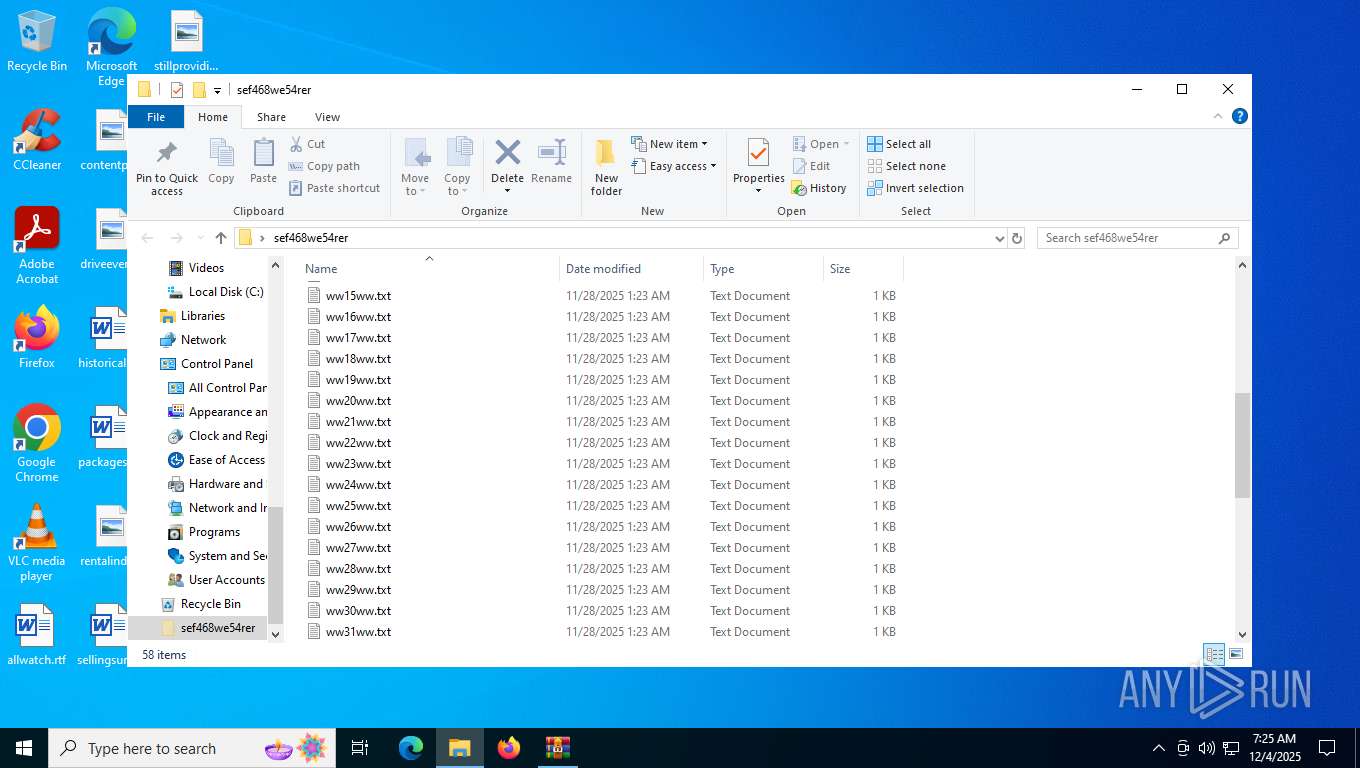
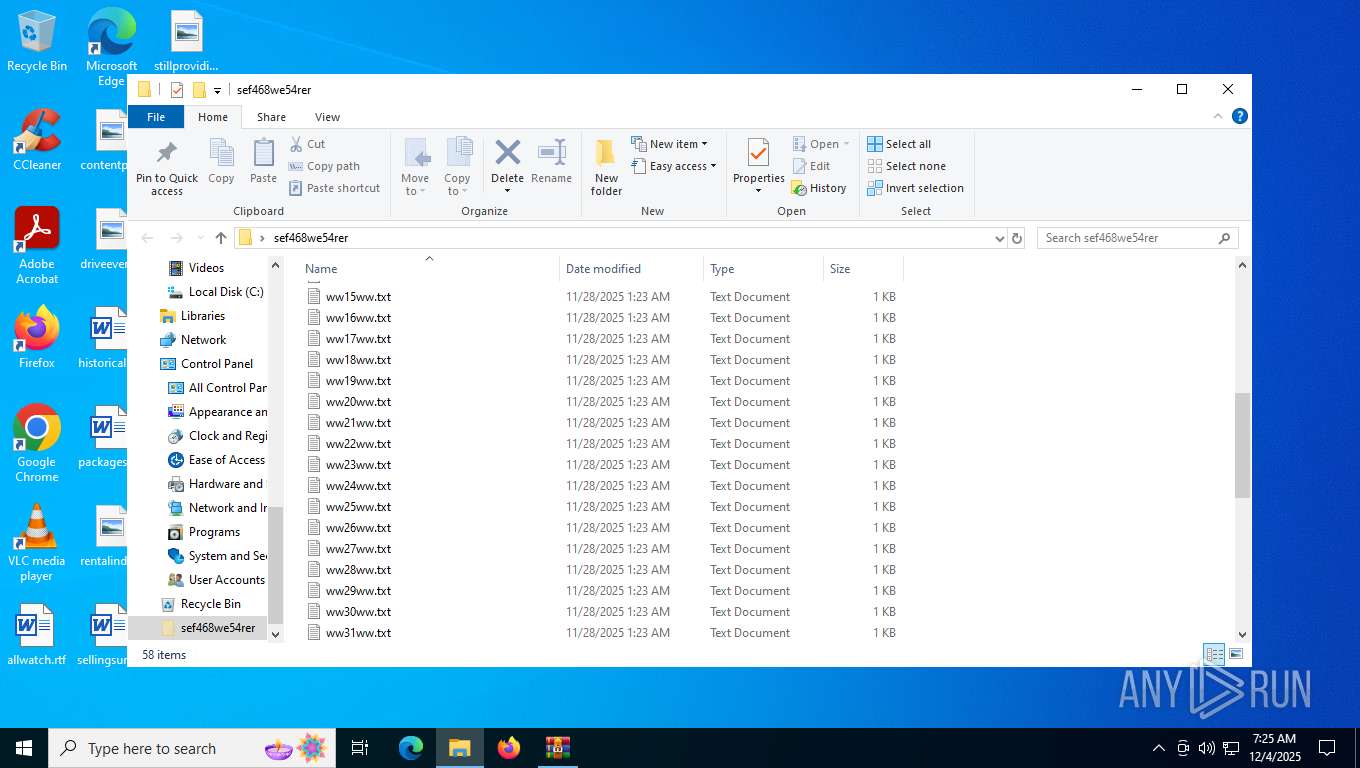
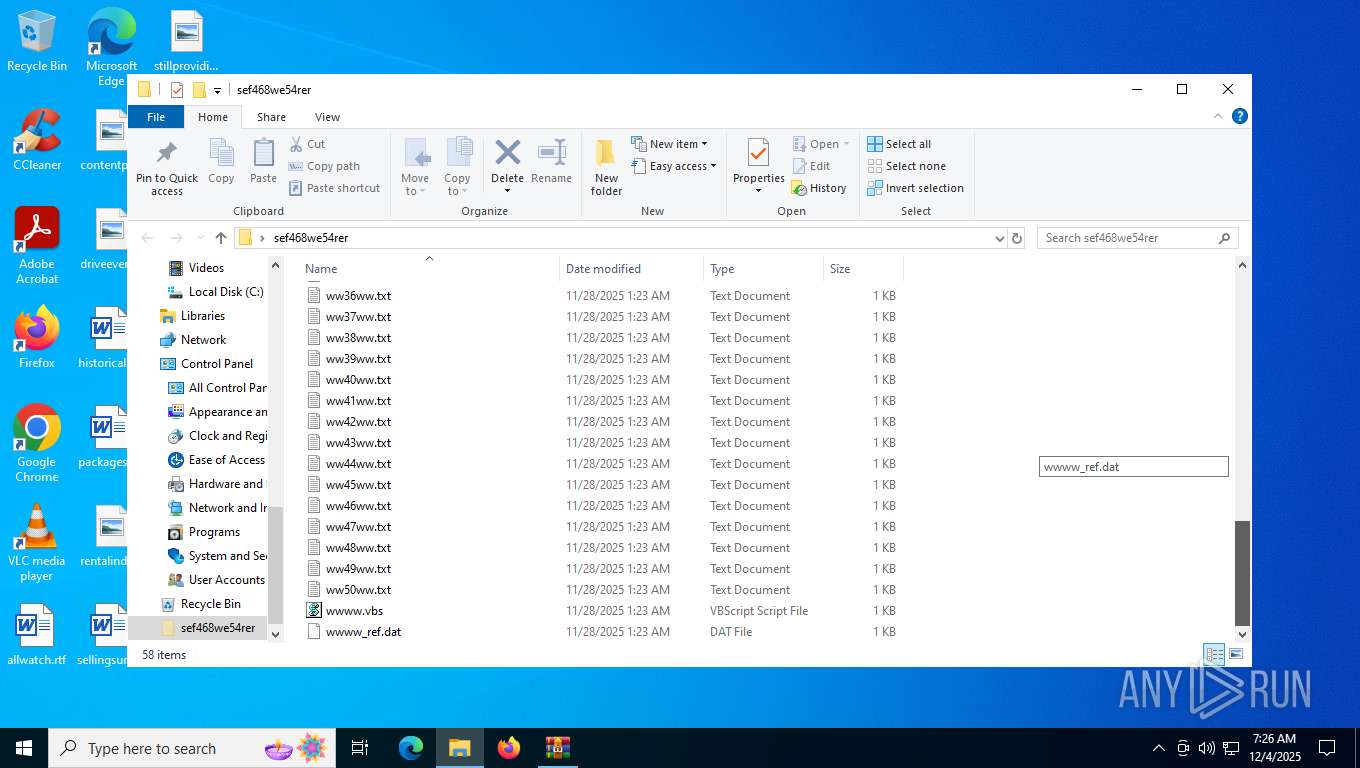
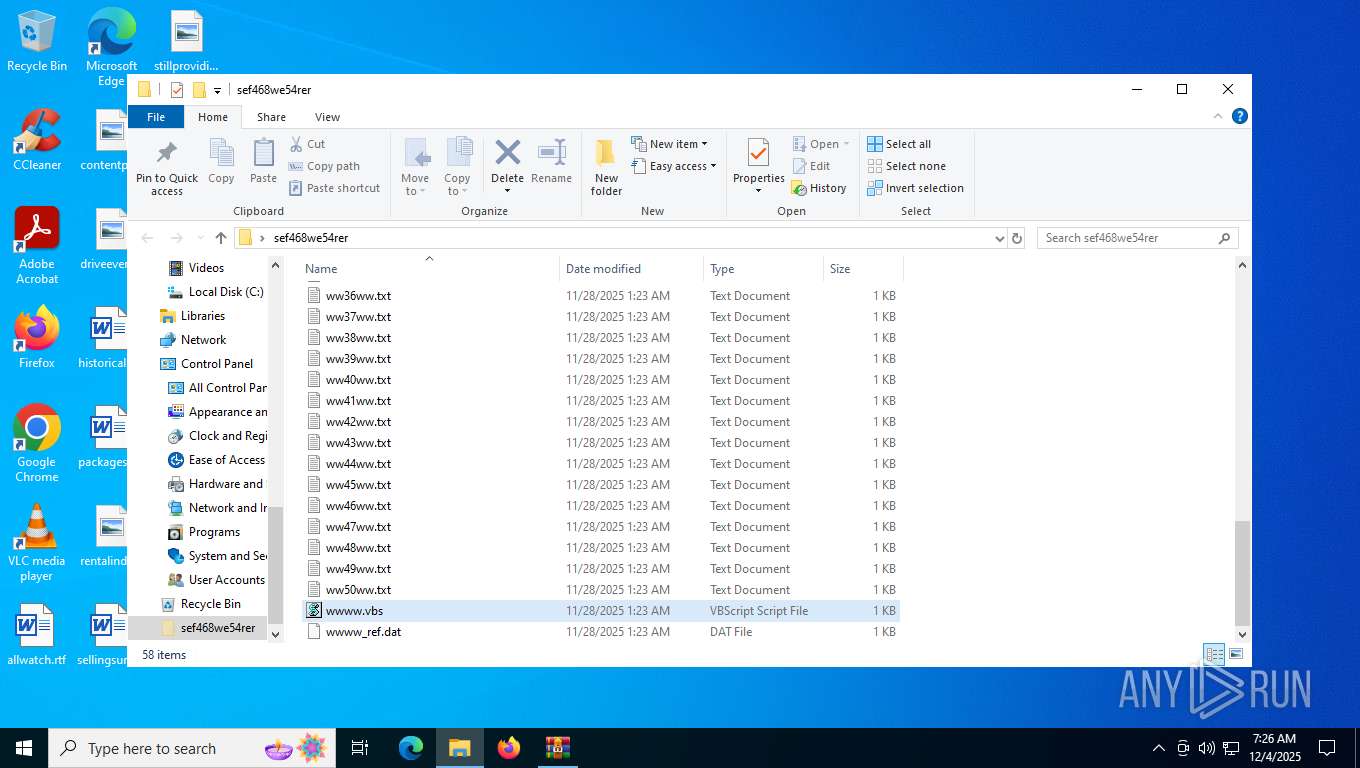
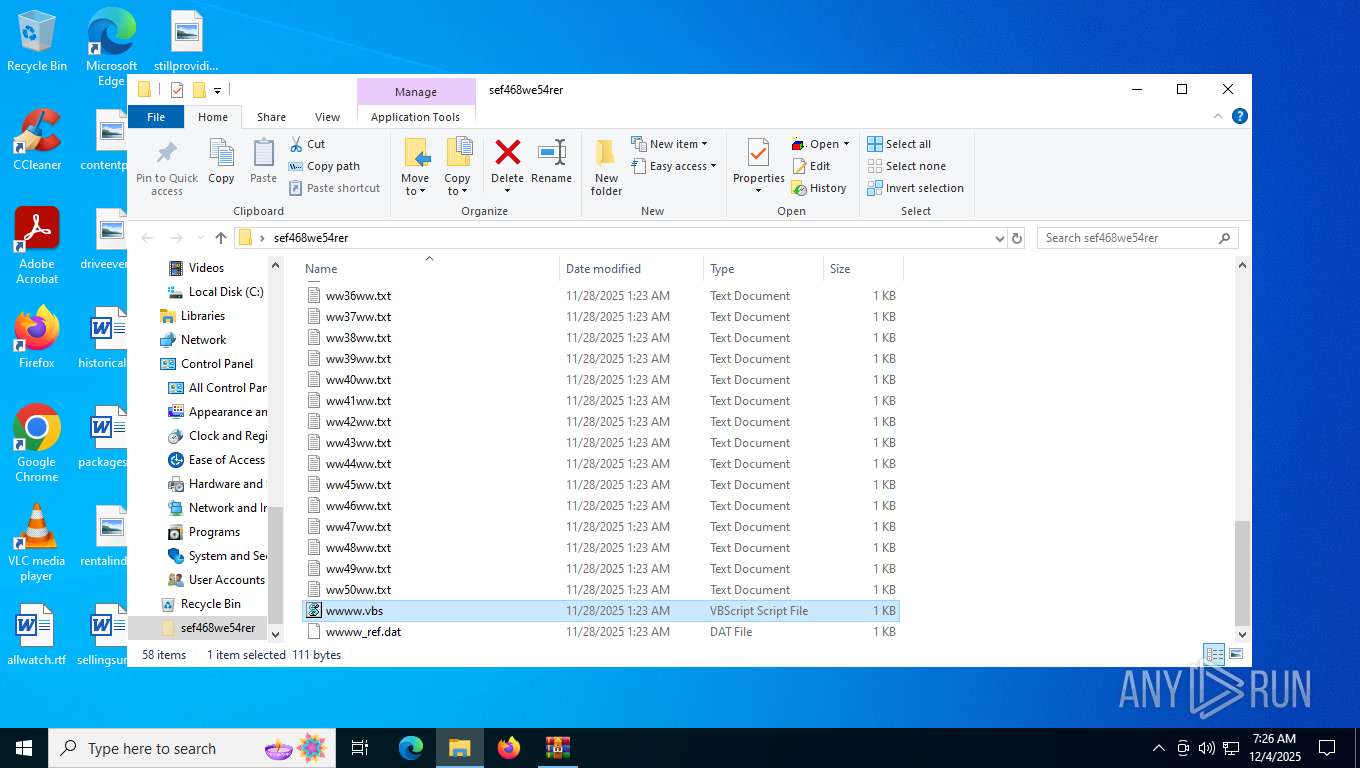
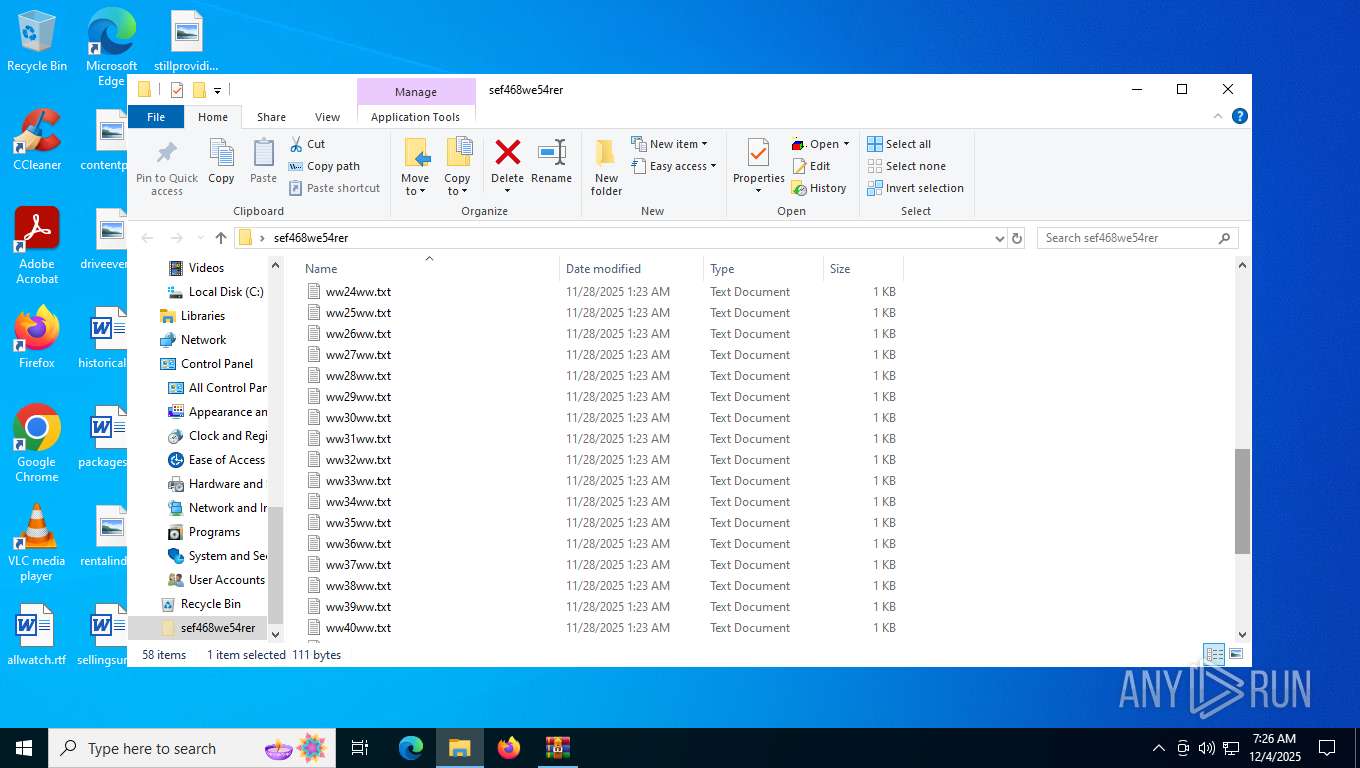
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww15ww.txt | text | |
MD5:FFF57F9593D1934D90E48803E3E506E7 | SHA256:8080BC1B9686E35BB7BC0F7A9CF70CAE685E4634386817036BDF768AE6248778 | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\23a1fd5456gsd4f564sa56d4s56d15sa4s.dat | text | |
MD5:B326B5062B2F0E69046810717534CB09 | SHA256:B5BEA41B6C623F7C09F1BF24DCAE58EBAB3C0CDD90AD966BC43A45B44867E12B | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\mgBxCQdEOP.txt | text | |
MD5:7A6D4AC8141992774FFB9B3C46DD09B3 | SHA256:BBC808884E190AFB824EA477DC3BBBA77A829EA3BD402AF3B151637364AAEB6F | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\asfas65f56a4sdsad65a476d4a65dad4a4.dat | text | |
MD5:B326B5062B2F0E69046810717534CB09 | SHA256:B5BEA41B6C623F7C09F1BF24DCAE58EBAB3C0CDD90AD966BC43A45B44867E12B | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\time_check.dat | text | |
MD5:3D37052C761747449616E3F7B5191400 | SHA256:B43B1ADE7C32DC15A668DD347C84C8E1272EF9768719EC043F423F50DBDCF795 | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww14ww.txt | text | |
MD5:3D5D7FFBEAC6E8FD3D0C018711ADC358 | SHA256:667F2EFEB806875C7A48350273859C001C315C0E6C9C3708AAFE57A3493C3396 | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww11ww.txt | text | |
MD5:5EE8810D73BA0759CB7DD138202D7CBD | SHA256:9663611D6A70B70E4BE1A05F3B6CAD7C18916425F4414AB031B20DCA273205D8 | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww12ww.txt | text | |
MD5:BA696F8998E6A05D924E542A6C8B39B4 | SHA256:EAFF78E793D26A712D52CC6D41C2445E3E0DF6D20F7EBDE756289EEFB079EDCC | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww17ww.txt | text | |
MD5:87E99FD0D01F508262EEF4387F569760 | SHA256:F496CD45AB6782634C068A2E85EDA0C87711C100D03827AAEC5A1611087B85C0 | |||
| 7356 | WinRAR.exe | C:\Users\admin\Desktop\sef468we54rer\ww13ww.txt | text | |
MD5:91387EF514F57356EA18AFB745BDC166 | SHA256:AED8D0653518B3DCE299065875EF7FD7FECCD0F3C4AFC1F2C8E4386C8C58BF01 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
26
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2408 | svchost.exe | GET | 200 | 23.55.110.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1416 | svchost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 23.55.110.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7984 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
2580 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2408 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7088 | SearchApp.exe | 2.23.227.138:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2408 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2408 | svchost.exe | 23.55.110.193:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
1416 | svchost.exe | 40.126.32.140:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1416 | svchost.exe | 172.66.2.5:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |