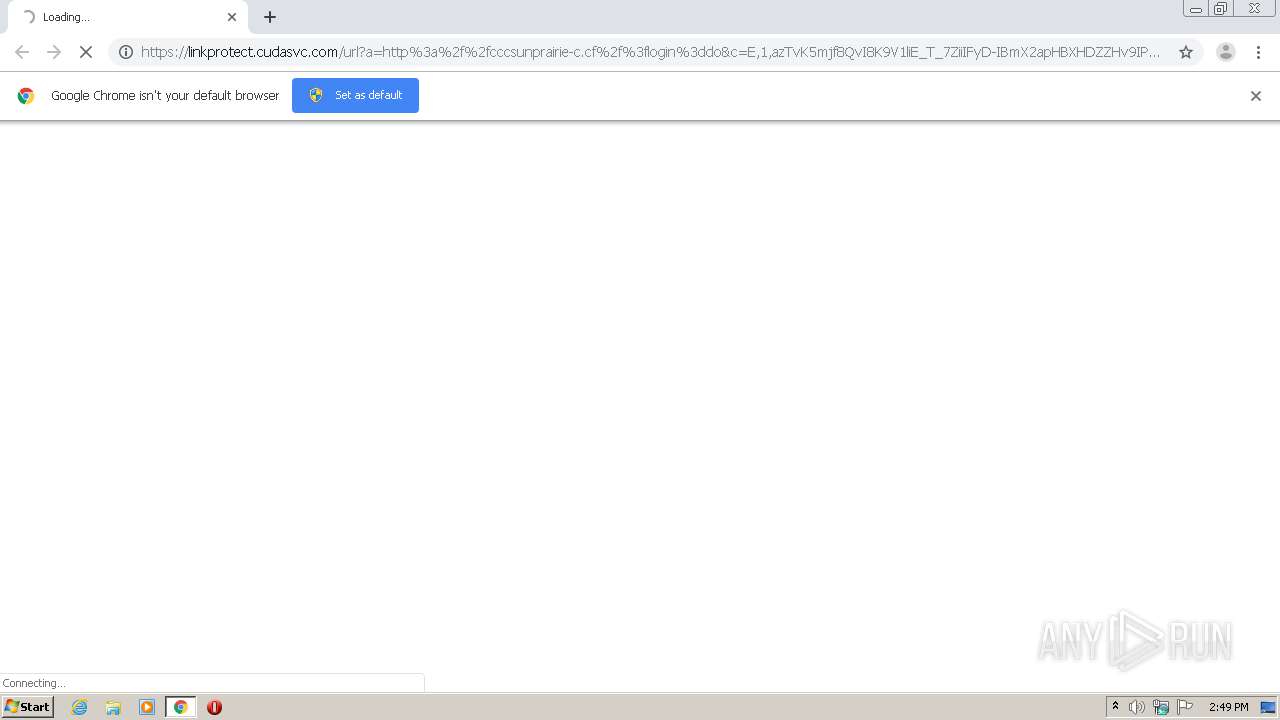
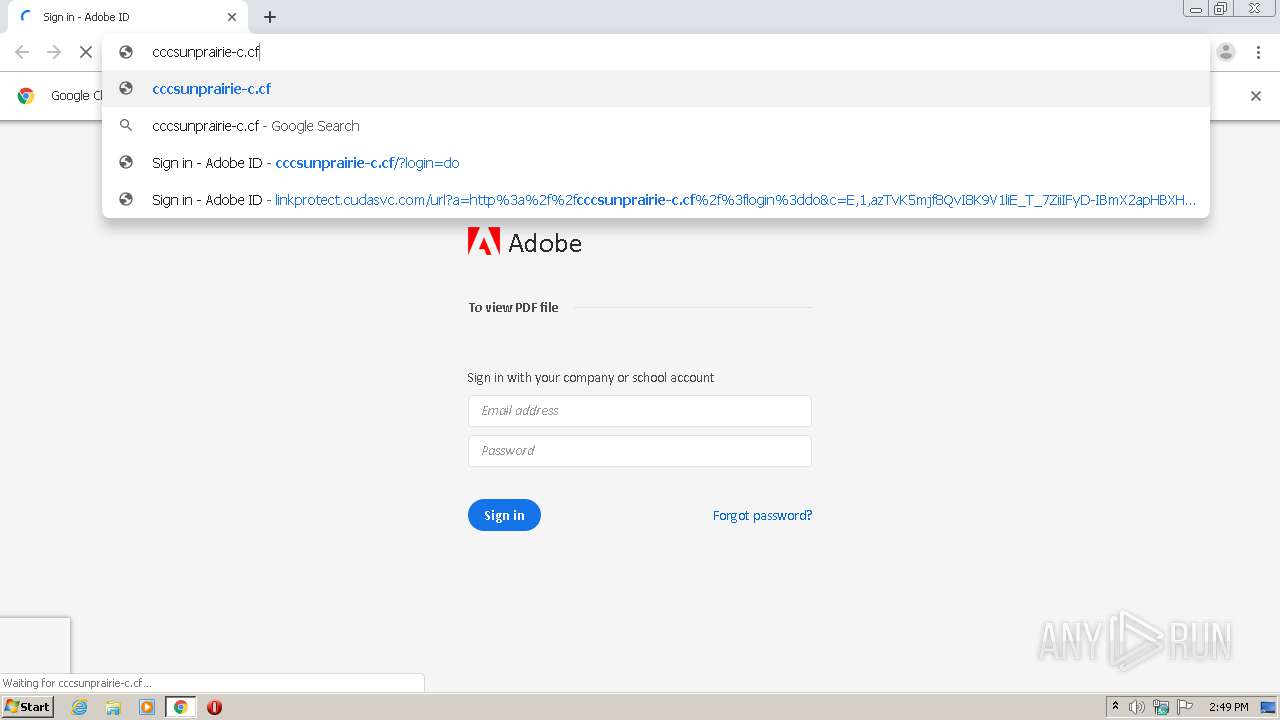
| URL: | https://linkprotect.cudasvc.com/url?a=http%3a%2f%2fcccsunprairie-c.cf%2f%3flogin%3ddo&c=E,1,azTvK5mjf8QvI8K9V1liE_T_7ZiiIFyD-IBmX2apHBXHDZZHv9IPhk1Hj41HNgMHmA2bn6wVX_p36wvUbObkMiuyWF9GWD9gz4SdQrnW8wZErI6NtyOlwhM,&typo=1 |
| Full analysis: | https://app.any.run/tasks/c9d37c57-481b-44cd-a0dc-765cf964c61f |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2021, 13:48:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 78CED2691789A465A3503B05F1BDE3A1 |
| SHA1: | E5EE78761CB52AC03C223C1F38AB5C5A31C24A80 |
| SHA256: | BAD24AC6EE3B4995F129B2D04FB9BC411EFCAE311E8779698490F46C1AB626EA |
| SSDEEP: | 6:2MBtsuTTwiqVsCraM01EBQFL8K6w+hAh8TVh5:2MnLHCraO2YweYCL5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1408)
INFO
Application launched itself
- chrome.exe (PID: 1408)
Reads the hosts file
- chrome.exe (PID: 1408)
- chrome.exe (PID: 3764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13032676527189331826 --mojo-platform-channel-handle=3188 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9770410772720050657 --mojo-platform-channel-handle=3180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://linkprotect.cudasvc.com/url?a=http%3a%2f%2fcccsunprairie-c.cf%2f%3flogin%3ddo&c=E,1,azTvK5mjf8QvI8K9V1liE_T_7ZiiIFyD-IBmX2apHBXHDZZHv9IPhk1Hj41HNgMHmA2bn6wVX_p36wvUbObkMiuyWF9GWD9gz4SdQrnW8wZErI6NtyOlwhM,&typo=1" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16664633820273350873 --mojo-platform-channel-handle=4296 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=376 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15375297787703749196 --mojo-platform-channel-handle=2848 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16760258001791064376 --mojo-platform-channel-handle=4244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2154717919527884842 --mojo-platform-channel-handle=3196 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1052,481209219928758955,16614802400037124393,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=245190533579091008 --mojo-platform-channel-handle=4292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6bbba9d0,0x6bbba9e0,0x6bbba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
203
Read events
138
Write events
61
Delete events
4
Modification events
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1408-13263140948097250 |
Value: 259 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1408) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1408-13263140948097250 |
Value: 259 | |||
Executable files
0
Suspicious files
9
Text files
279
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-607AE754-580.pma | — | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\62db560f-a622-4f01-a5a1-f6da4d62a694.tmp | — | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF133fea.TMP | text | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1408 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13423c.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
25
DNS requests
11
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3764 | chrome.exe | GET | — | 104.168.167.45:80 | http://cccsunprairie-c.cf/img/sprite.png | US | — | — | suspicious |
3764 | chrome.exe | GET | — | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/recaptcha__en.js | US | — | — | suspicious |
3764 | chrome.exe | GET | — | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/bframe_data_002/styles__ltr.css | US | — | — | suspicious |
3764 | chrome.exe | GET | — | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/bframe_data_002/18uhqkpLX_hgNtv0GBe23umXvFqNTaL8jddrrrm0s-M.js | US | — | — | suspicious |
3764 | chrome.exe | GET | 200 | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/light.css | US | text | 54.3 Kb | suspicious |
3764 | chrome.exe | GET | 200 | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/AdobeMessagingClient.css | US | text | 44.0 Kb | suspicious |
3764 | chrome.exe | GET | 200 | 104.168.167.45:80 | http://cccsunprairie-c.cf/Sign%20in%20-%20Adobe%20ID_files/anchor_002.htm | US | html | 20.5 Kb | suspicious |
3764 | chrome.exe | GET | 404 | 104.168.167.45:80 | http://cccsunprairie-c.cf/favicon.ico | US | html | 10.1 Kb | suspicious |
3764 | chrome.exe | GET | 200 | 104.168.167.45:80 | http://cccsunprairie-c.cf/js/jquery-2.2.3.min.js | US | text | 83.6 Kb | suspicious |
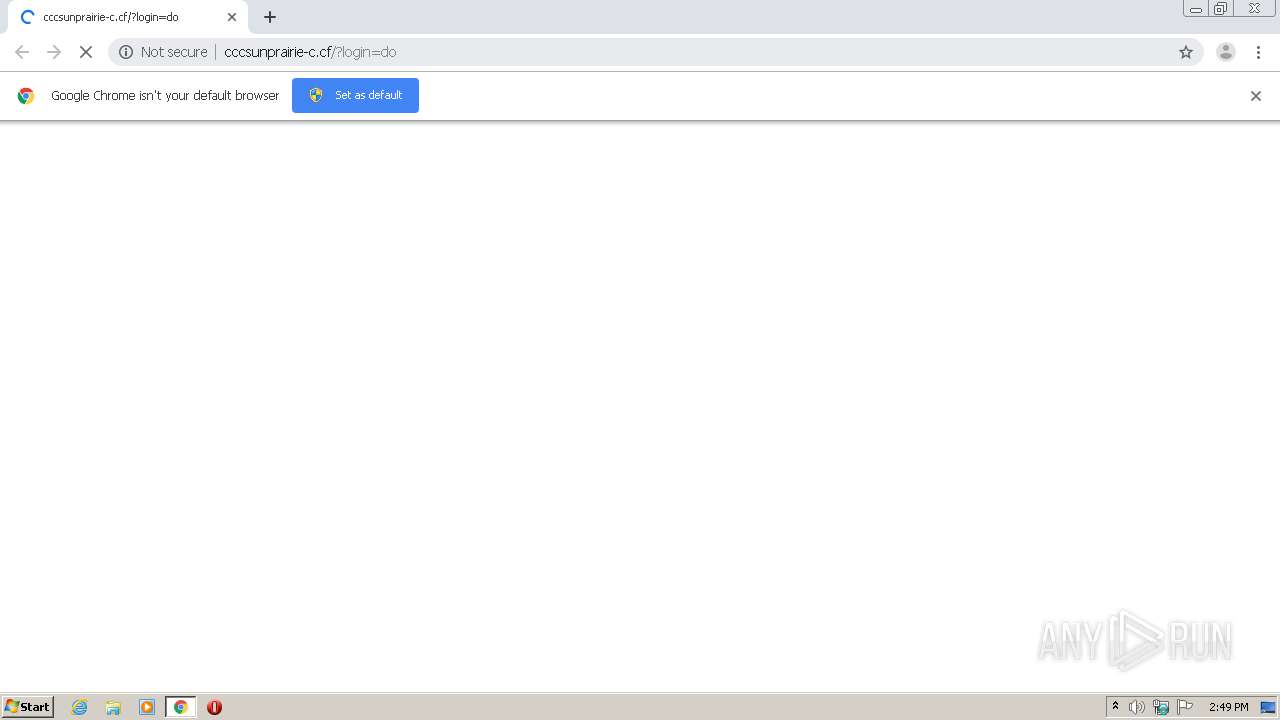
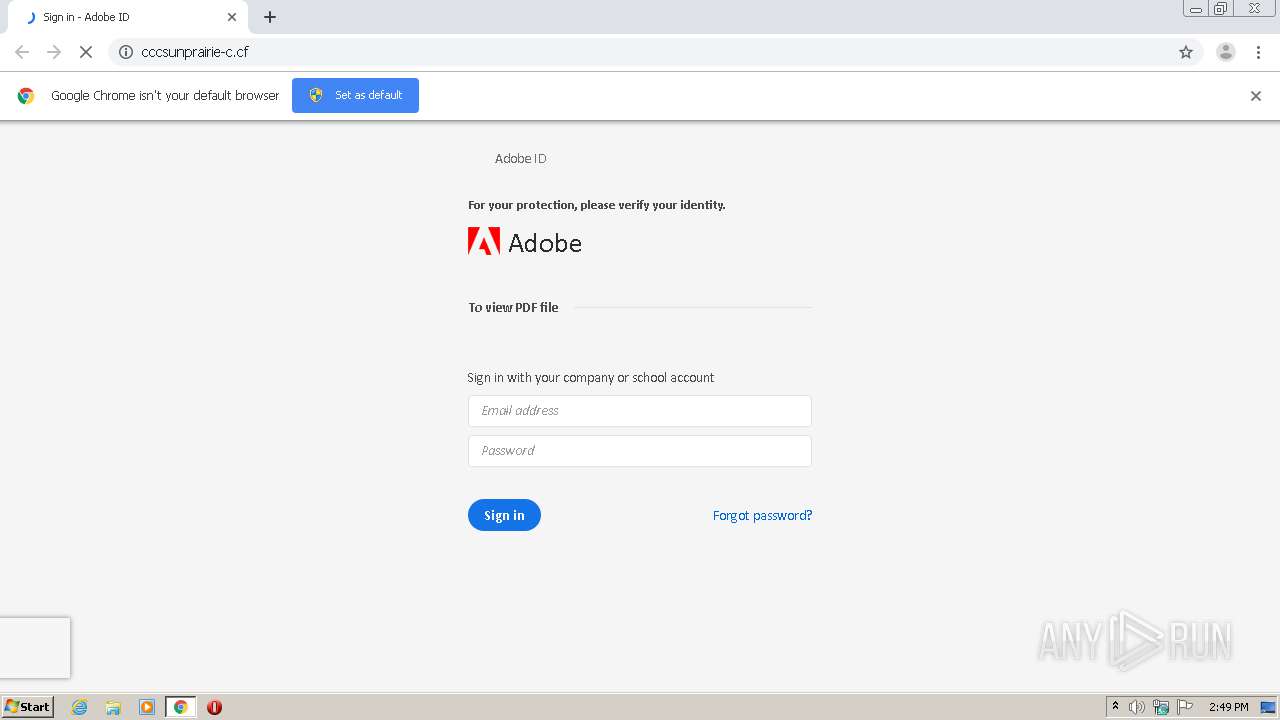
3764 | chrome.exe | GET | 200 | 104.168.167.45:80 | http://cccsunprairie-c.cf/?login=do | US | html | 27.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3764 | chrome.exe | 52.28.42.211:443 | linkprotect.cudasvc.com | Amazon.com, Inc. | DE | unknown |
3764 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 104.168.167.45:80 | cccsunprairie-c.cf | Hostwinds LLC. | US | suspicious |
3764 | chrome.exe | 142.250.34.2:80 | edgedl.gvt1.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 18.184.125.187:443 | linkprotect.cudasvc.com | — | US | unknown |
3764 | chrome.exe | 142.250.75.3:443 | clientservices.googleapis.com | Google Inc. | US | unknown |
3764 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 104.168.167.45:80 | cccsunprairie-c.cf | Hostwinds LLC. | US | suspicious |
3764 | chrome.exe | 216.58.201.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3764 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
linkprotect.cudasvc.com |
| whitelisted |
accounts.google.com |
| shared |
cccsunprairie-c.cf |
| suspicious |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
adobeid-na1.services.adobe.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
3764 | chrome.exe | A Network Trojan was detected | ET CURRENT_EVENTS Adobe Shared Document Phishing Landing Nov 19 2015 |
3764 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Adobe ID Phishing Landing - Title over non SSL |