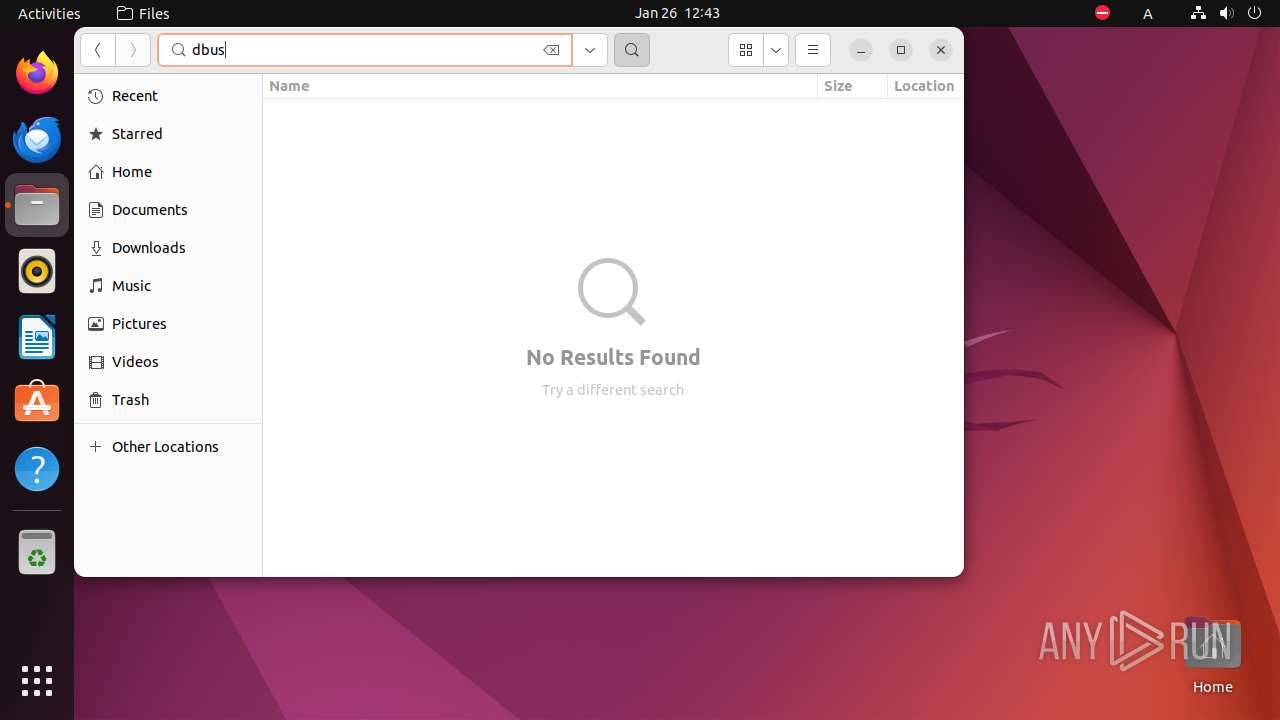
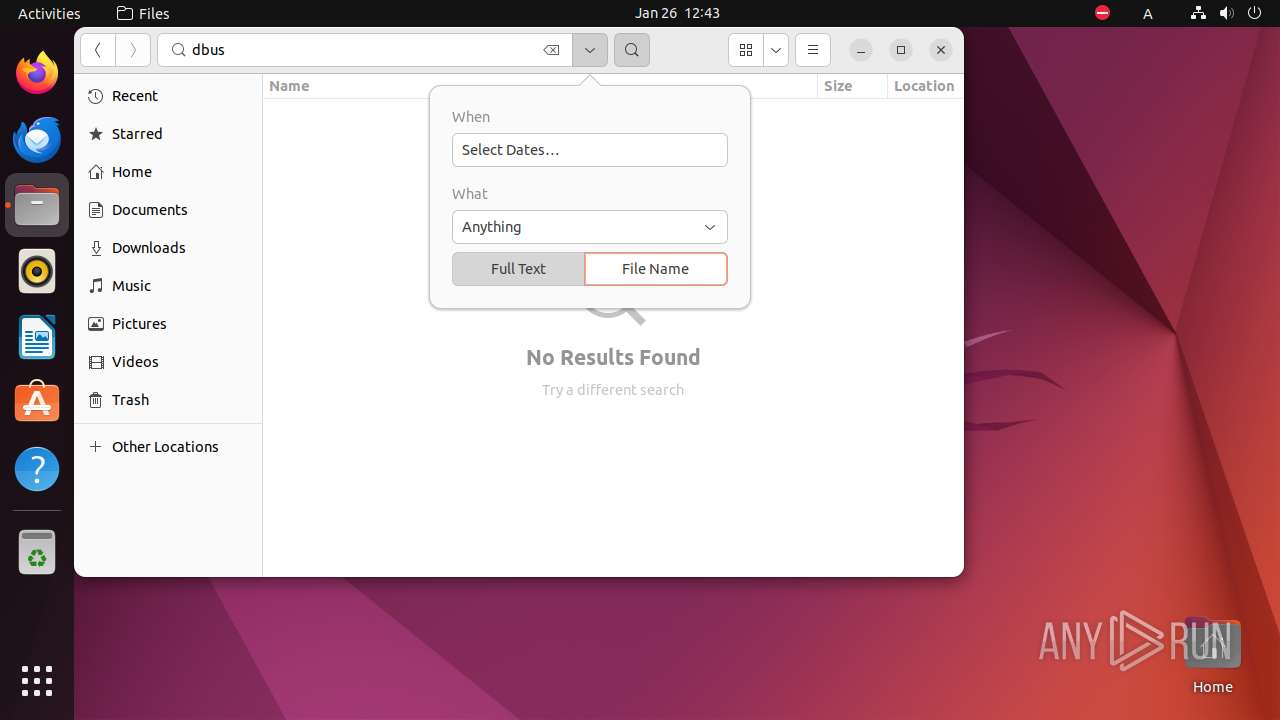
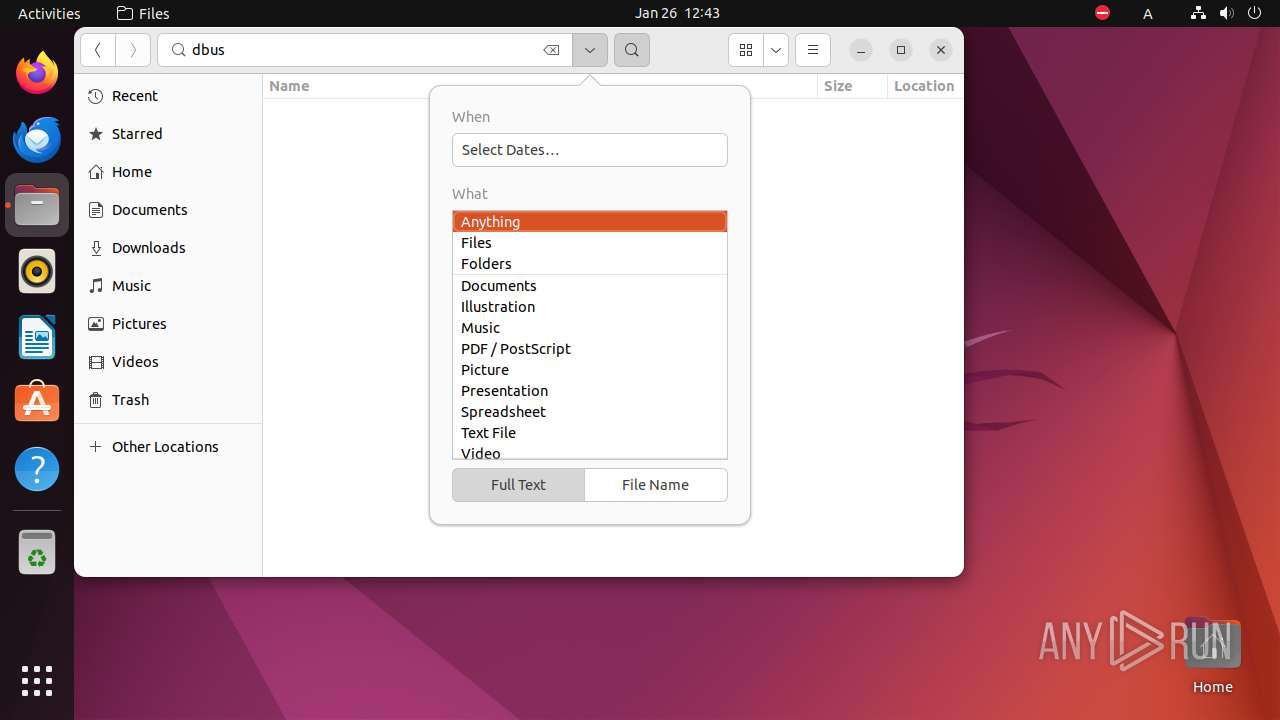
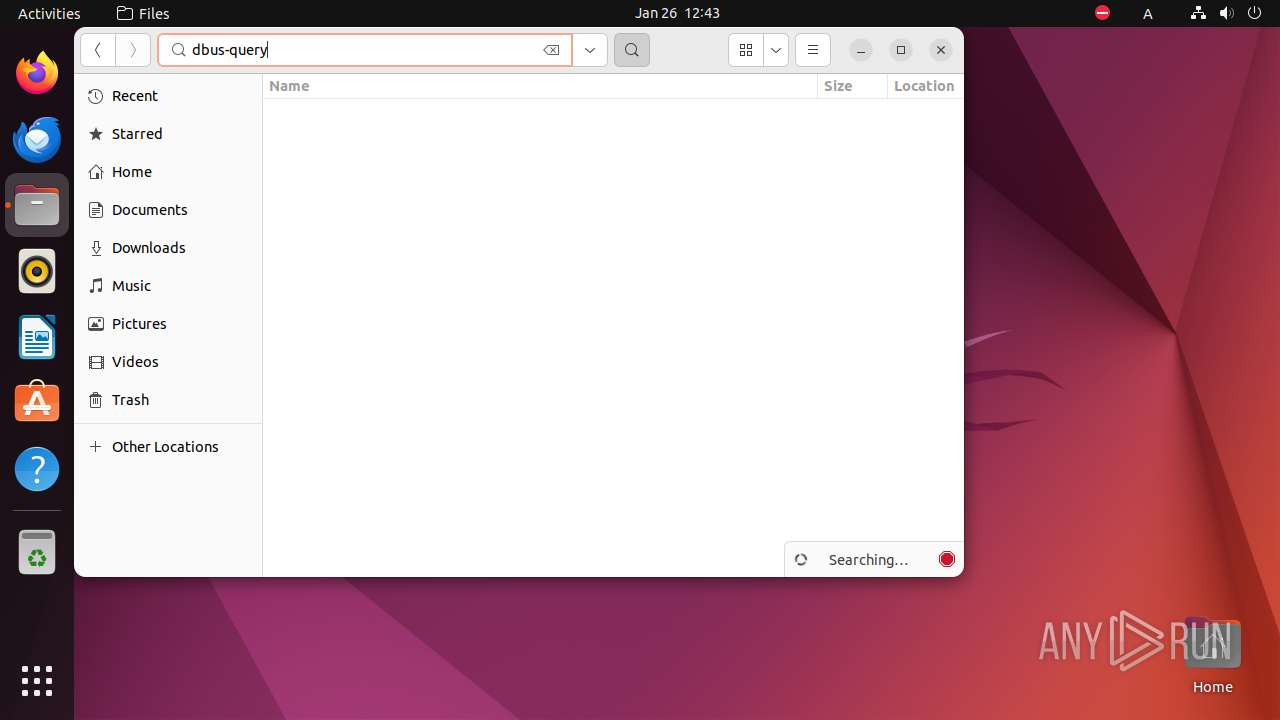
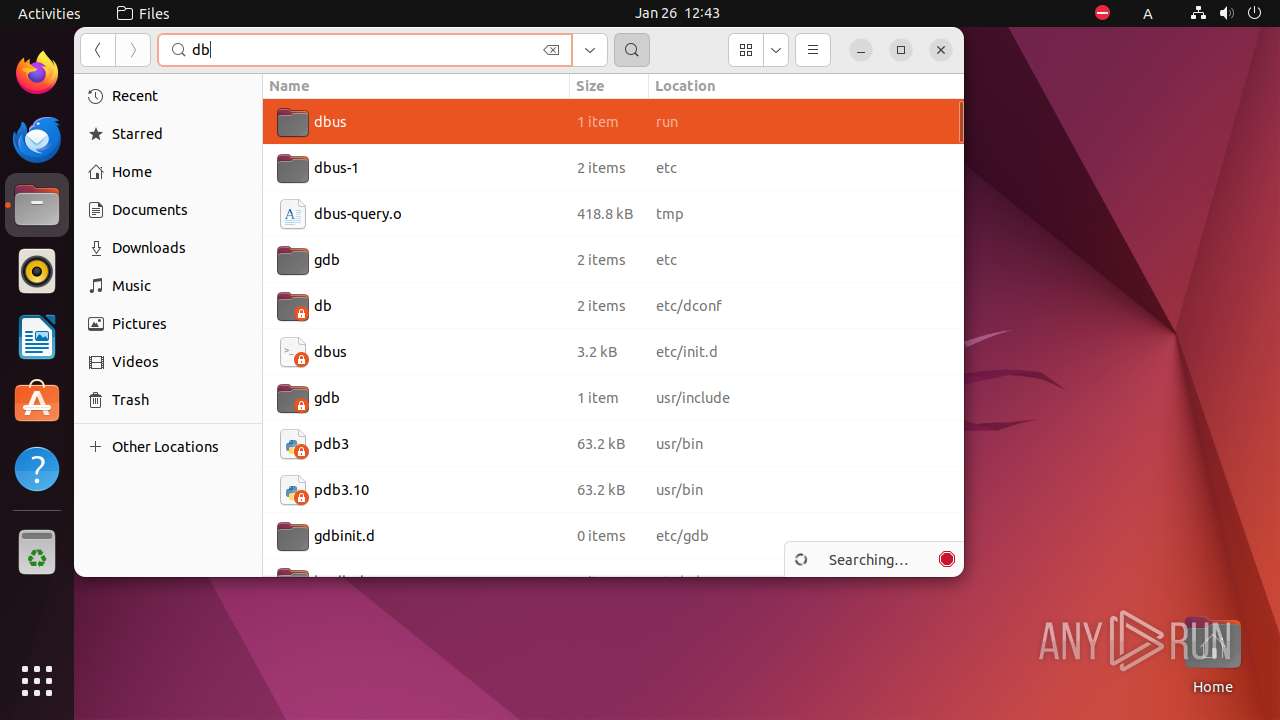
| File name: | dbus-query |
| Full analysis: | https://app.any.run/tasks/8d19a106-606b-4779-a96b-5e93411b3fb5 |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2024, 12:40:15 |
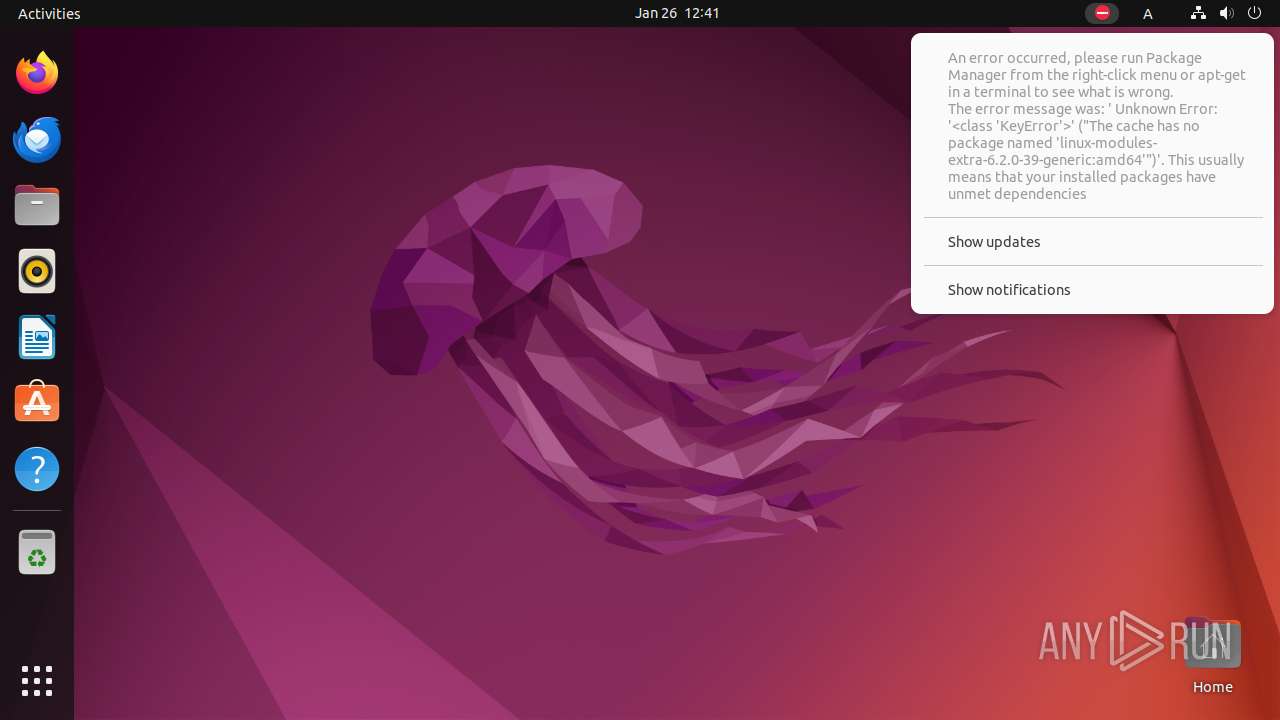
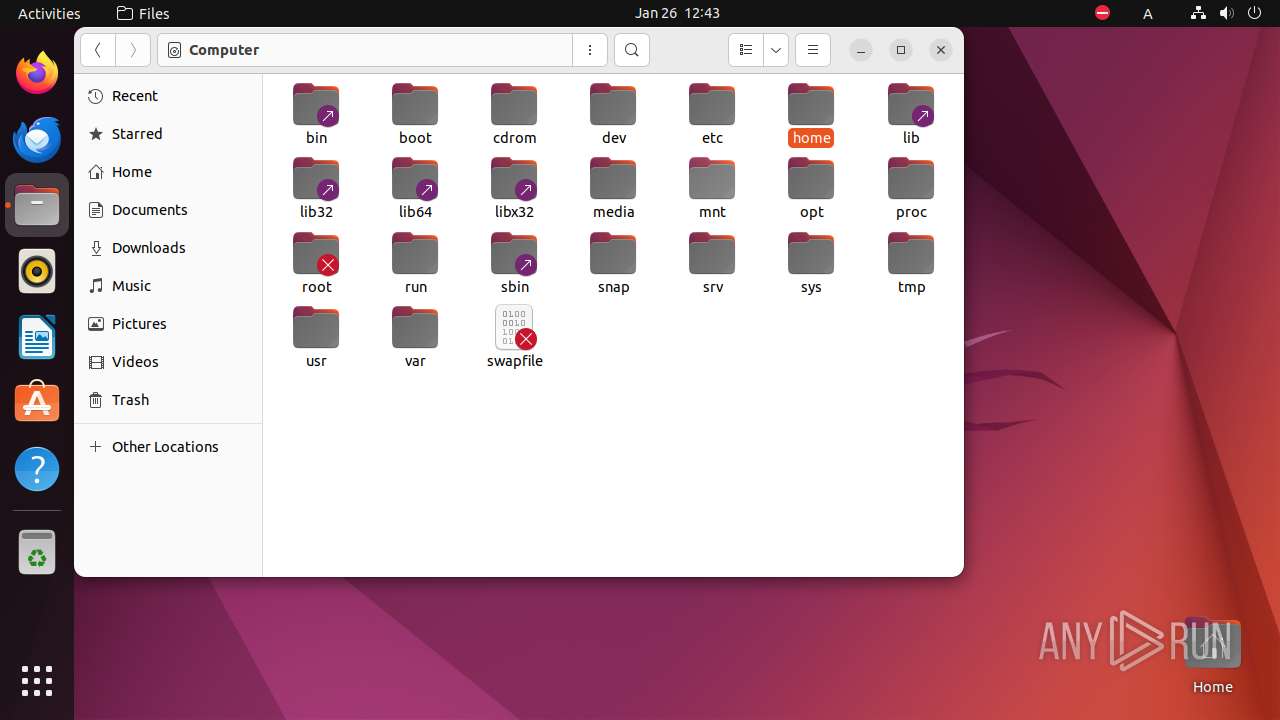
| OS: | Ubuntu 22.04.2 |
| MIME: | application/x-executable |
| File info: | ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, no section header |
| MD5: | 2F21EFACB63472121E60BFB9F17D0DDC |
| SHA1: | 5067DDFDBC98A32AE4EB6989AD092E75FB56385A |
| SHA256: | BACBE2A793D8DDCA0A195B67DEF527E66D280A13A8D4DF90B507546B76E87D29 |
| SSDEEP: | 12288:qYpnE+v01WviTMa2F5r6yHCSIIcbxHXnSDsw0bxaXFn11DUrq:qY5E+c1WviTMa2zrLHCSbcbdXSDsw0bE |
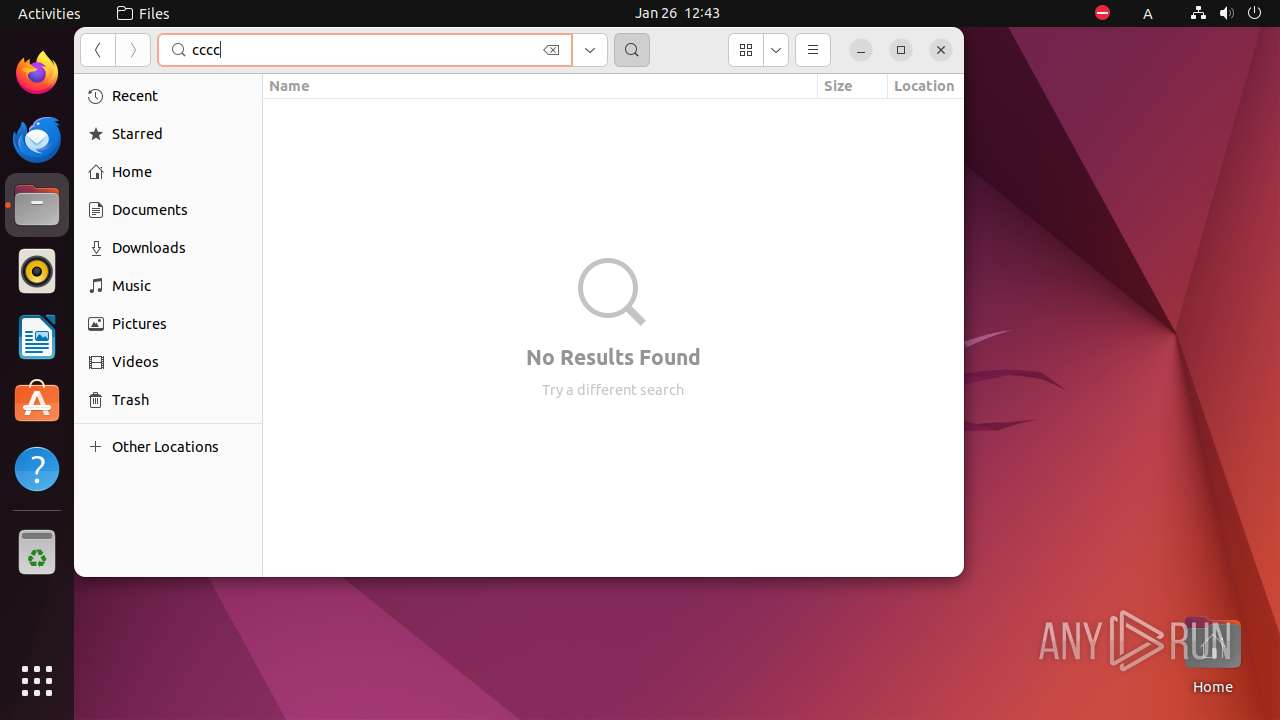
MALICIOUS
No malicious indicators.SUSPICIOUS
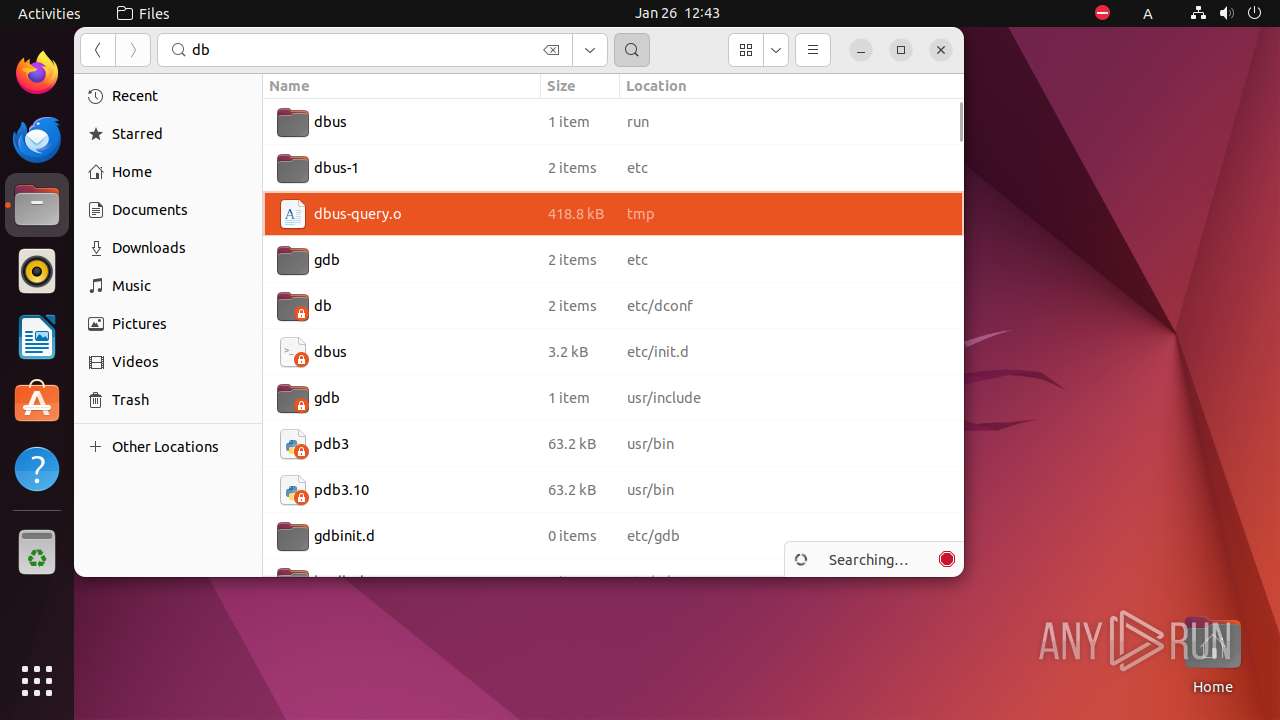
Changes file or directory permissions
- sh (PID: 6853)
Reads passwd file
- chown (PID: 6855)
- dbus-query.o (PID: 6858)
- nautilus (PID: 6890)
Executes commands using command-line interpreter
- bash (PID: 6860)
Checks system locale (may determine the language used by the system)
- dbus-query.o (PID: 6858)
Modifies file or directory owner
- sudo (PID: 6854)
INFO
Checks timezone
- sudo (PID: 6854)
- sudo (PID: 6857)
- nautilus (PID: 6890)
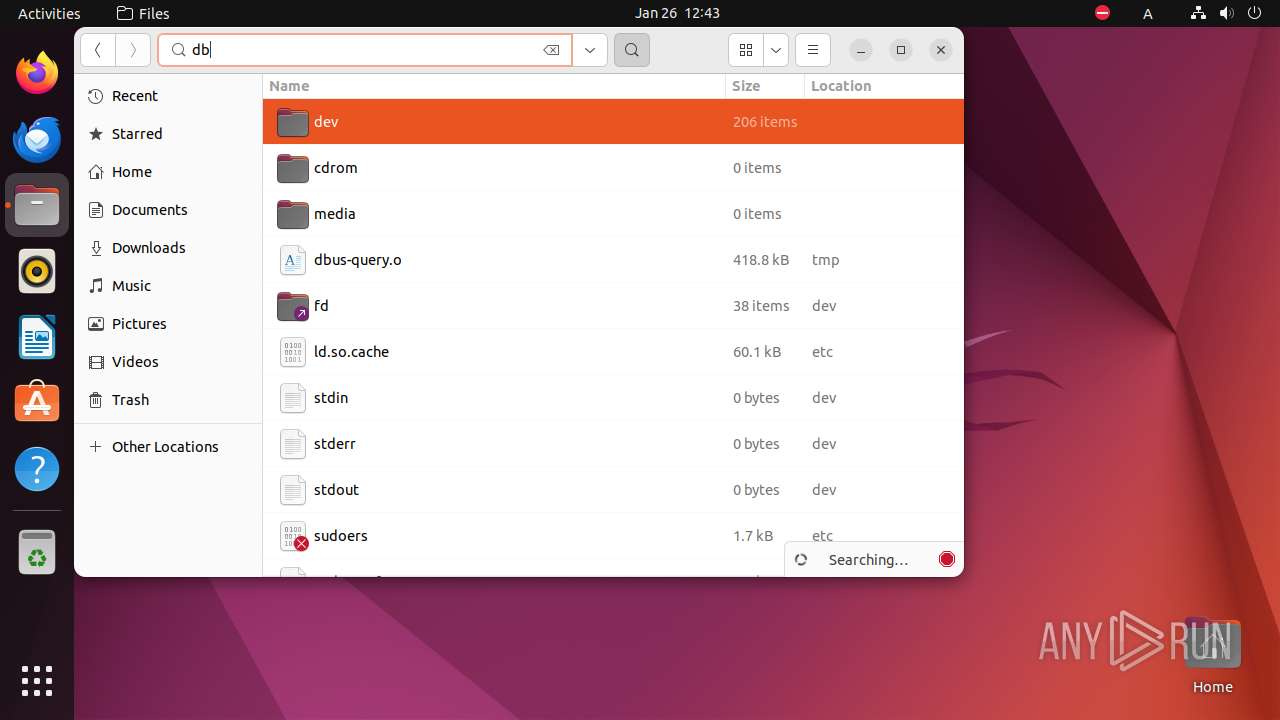
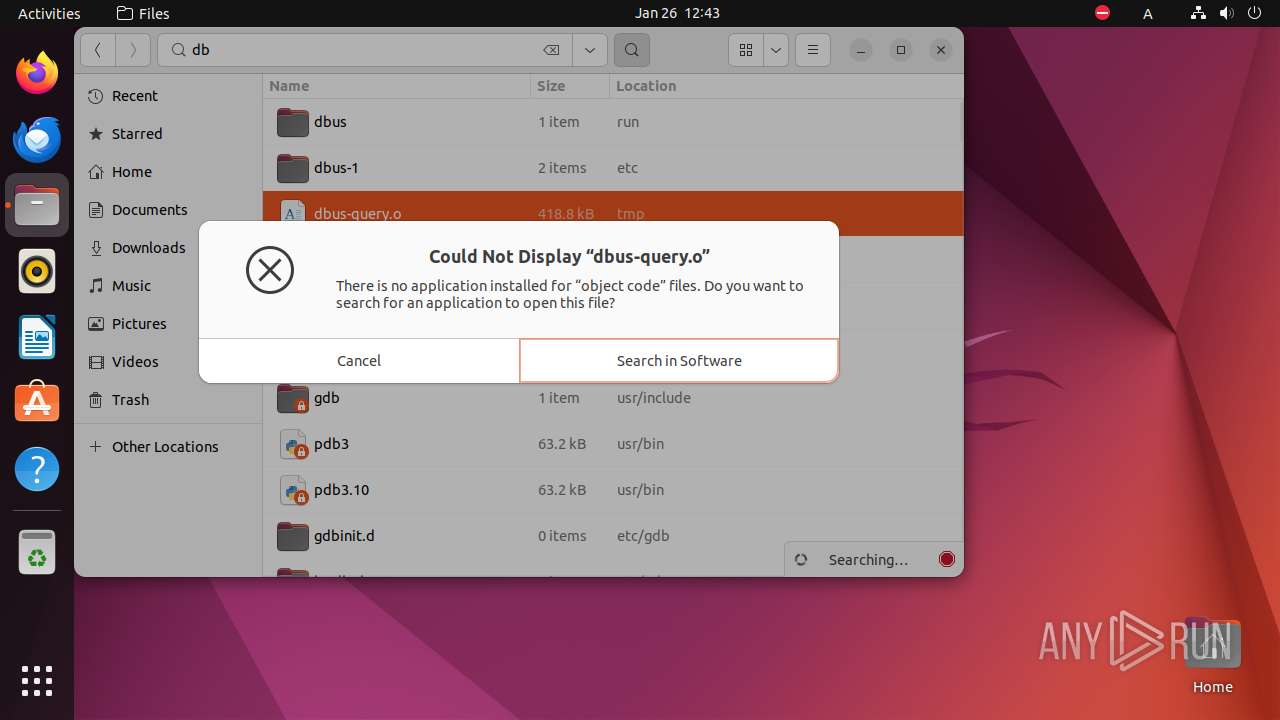
Creates file in the temporary folder
- gdk-pixbuf-thumbnailer (PID: 6926)
- bwrap (PID: 6923)
- nautilus (PID: 6890)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Executable file |
| CPUType: | AMD x86-64 |
Total processes
234
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 6853 | /bin/sh -c "sudo chown user \"/tmp/dbus-query\.o\" && chmod +x \"/tmp/dbus-query\.o\" && DISPLAY=:0 sudo -i \"/tmp/dbus-query\.o\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
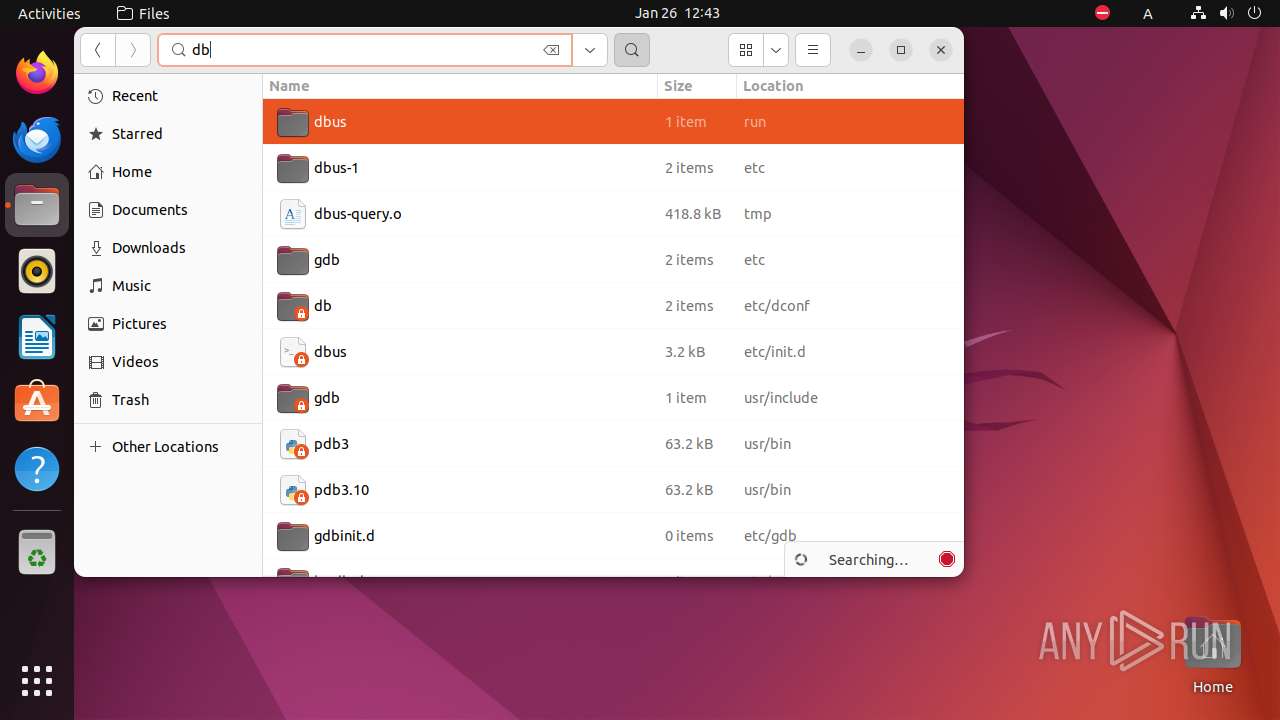
| 6854 | sudo chown user /tmp/dbus-query.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6855 | chown user /tmp/dbus-query.o | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6856 | chmod +x /tmp/dbus-query.o | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6857 | sudo -i /tmp/dbus-query.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6858 | /tmp/dbus-query.o | /tmp/dbus-query.o | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6859 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | dbus-query.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6860 | -bash --login -c \/tmp\/dbus-query\.o | /usr/bin/bash | — | dbus-query.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6861 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/sh | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 6862 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
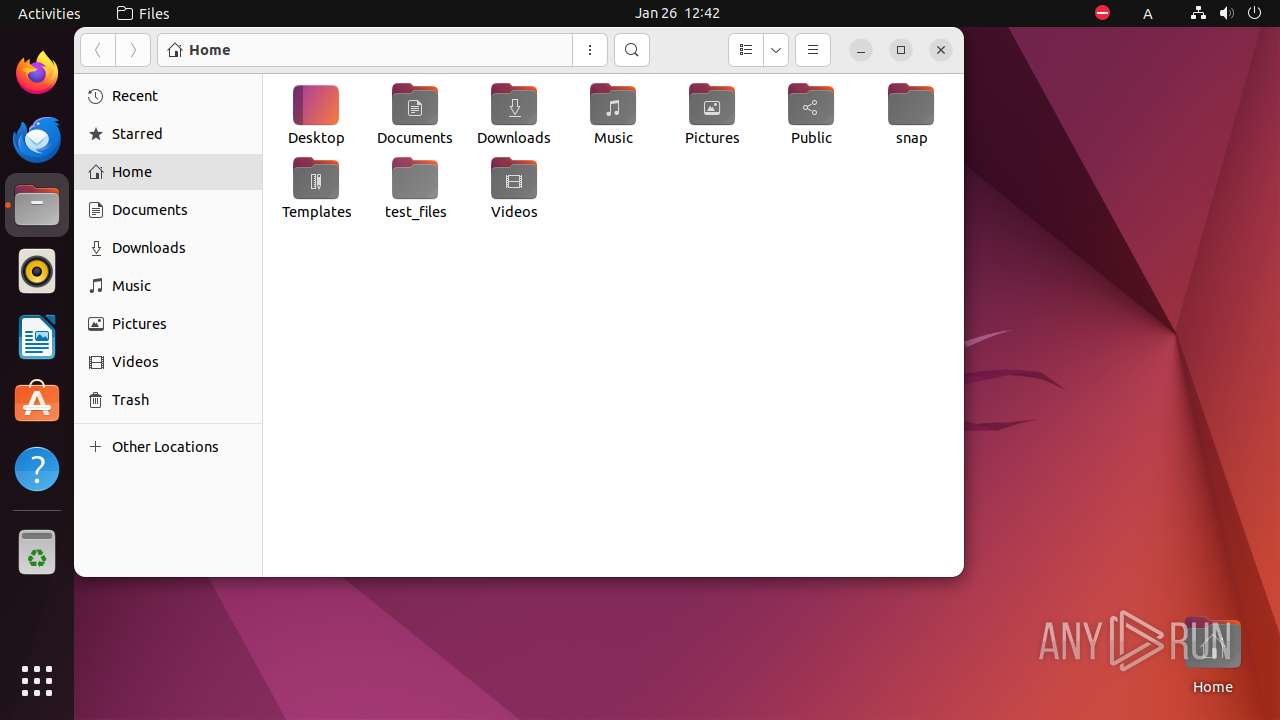
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6890 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-wal | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /home/user/.local/share/nautilus/tags/.meta.isrunning | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /home/user/.config/nautilus/search-metadata.OIMBI2 | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /dconf/user | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /tmp/flatpak-seccomp-4V70H2 | — | |
MD5:— | SHA256:— | |||
| 6890 | nautilus | /home/user/.config/nautilus/search-metadata.C8K1H2 | — | |
MD5:— | SHA256:— | |||
| 6923 | bwrap | /newroot/etc/ld.so.cache | — | |
MD5:— | SHA256:— | |||
| 6923 | bwrap | /null | — | |
MD5:— | SHA256:— | |||
| 6923 | bwrap | /zero | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
6
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.snapcraft.io |
| unknown |
212.100.168.192.in-addr.arpa |
| unknown |
connectivity-check.ubuntu.com |
| unknown |