| URL: | https://r.search.yahoo.com/cbclk2/dWU9MjRGQUY0Q0E0RUFGNDBGMCZ1dD0xNTQ2OTc3ODk2MDAwJnVvPTc2MjA5OTk4MTg0NTk5Jmx0PTImZXM9Y1NFbTNLOEdQUy5kdS5KeiZqZT1hYjgyY2M1ZS0xMzgwLTExZTktOWQ3MC0wMDhjZmE1YjU2NWMtMmFlY2I4MWI4NzAwJnVpPTE0NC45LjU2LjEzMSZqdD0xNTQ2OTc3ODk2NTcyJnBwPXMz/RV=2/RE=1547006696/RO=10/RU=https%3a%2f%2fwww.bing.com%2faclick%3fld%3dd3jfwz4HIdW7qdwRmzZmc3HDVUCUxfJBDBM-vuSTs0Y_aalglWtC0hZGBi0maHfQf3Iz6VVvc1RPDrtPrLE6AigFeCJgeY4x8IbppV6gVGn8HsrhKIV5TrUYrF_4vMMHe-sWHx0QI0zznmdvL9EQQFvEOw2h-CTSGLv-ouDToJcl7a9QV4%26u%3dhttp%253a%252f%252fspecialsweetrecipes.com%252f%26rlid%3d7571c41093831969fcae982591eb7c73/RK=2/RS=74nxAxE29wYlv2n86JutM2hoRNY-;_ylt=AwrJ7F1oAjVcIeEAr7VXNyoA;_ylu=X3oDMTE5NjUxdmRjBGNvbG8DYmYxBHBvcwMzBHZ0aWQDQjU4NTlfMQRzZWMDb3YtYm90dG9t;_ylc=X3IDMgRydAMx?p=food+network |
| Full analysis: | https://app.any.run/tasks/a810a0eb-0a87-4d1c-951f-f33162928ac4 |
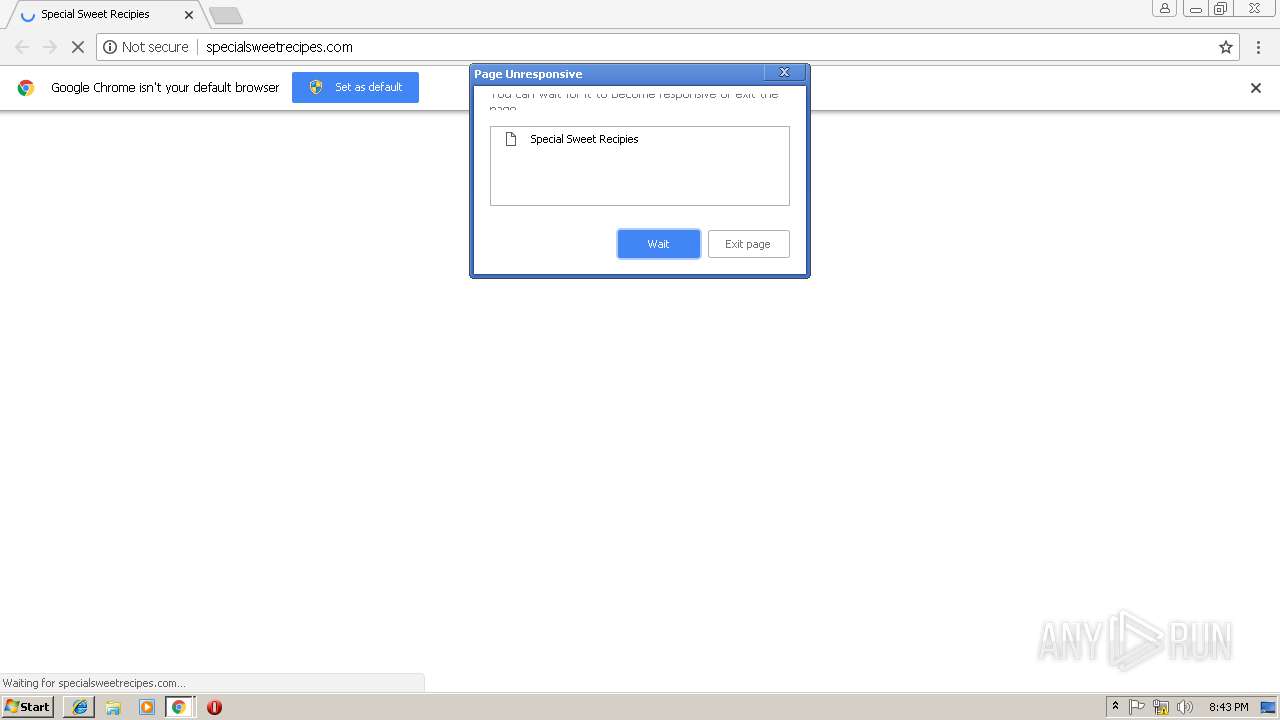
| Verdict: | No threats detected |
| Analysis date: | January 08, 2019, 20:41:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 390ACA80D13FB2FB21586EF7600D7991 |
| SHA1: | 9FF9A0FFE8ABA9E7D048C00FF9B71887FC2E310D |
| SHA256: | BAC8C2727E2A441932A1E973FFDF73BA08760ED27F2680C2A7829DDC71D59273 |
| SSDEEP: | 24:2ix5nhl7AObGEIx0p98n+25ManOljTmWCy:v7FBIx0p9OIljTH/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
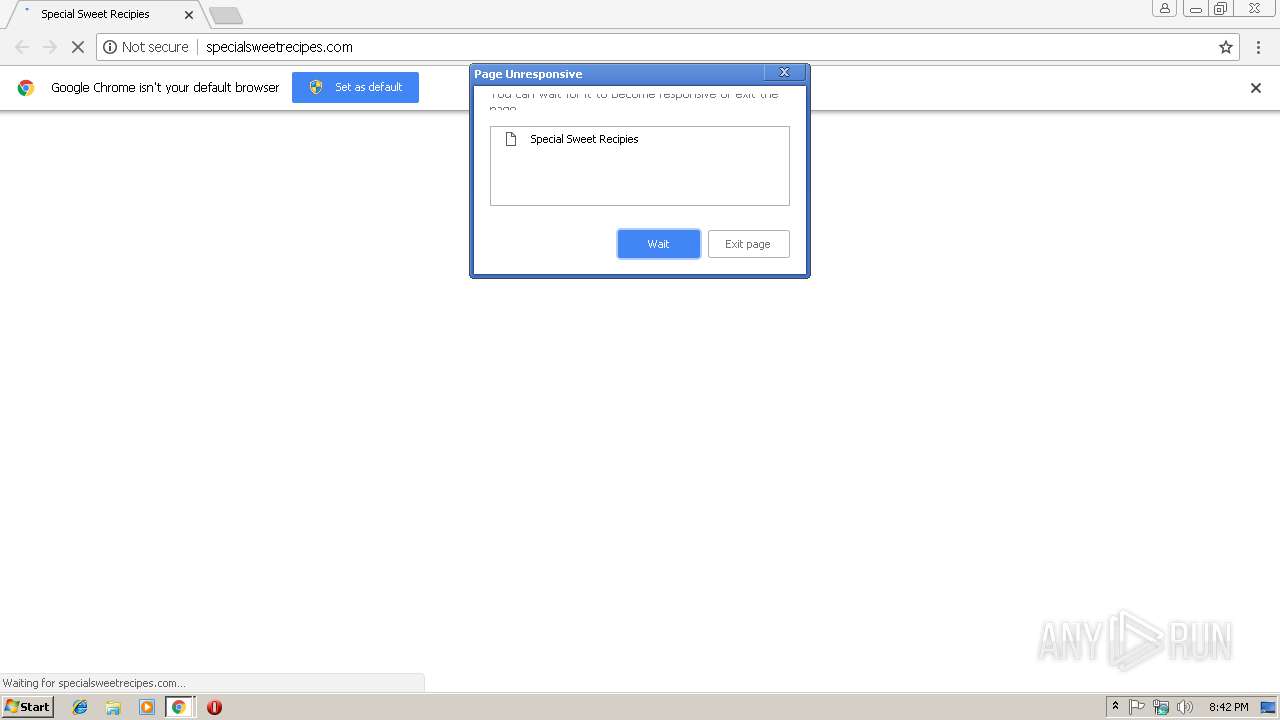
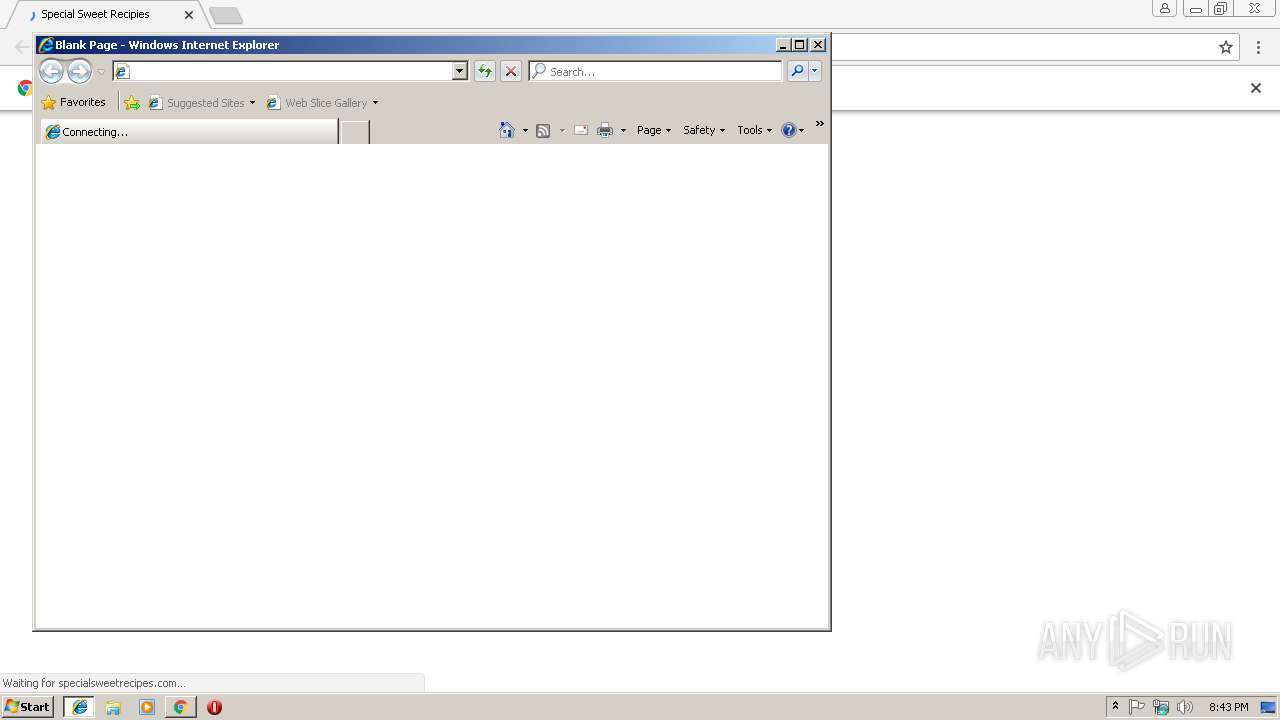
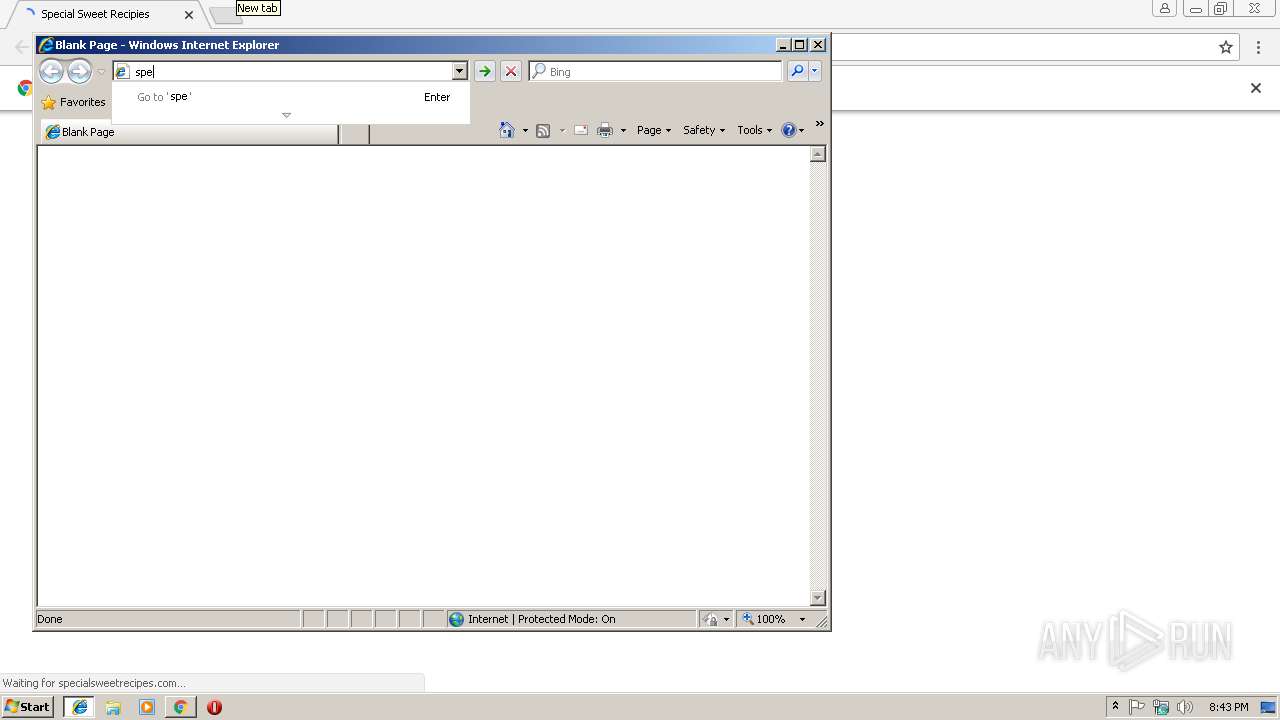
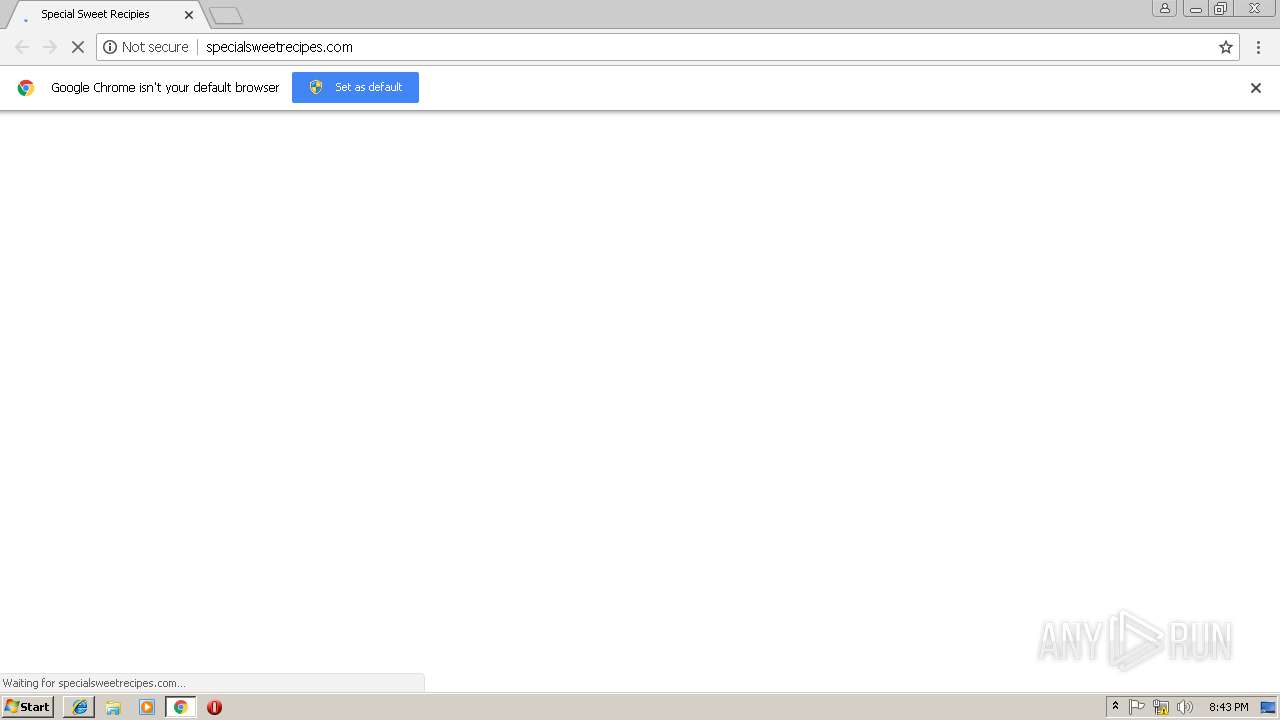
Application launched itself
- iexplore.exe (PID: 2892)
- chrome.exe (PID: 2968)
Reads settings of System Certificates
- chrome.exe (PID: 2968)
Reads Internet Cache Settings
- iexplore.exe (PID: 2316)
Changes internet zones settings
- iexplore.exe (PID: 2892)
Reads internet explorer settings
- iexplore.exe (PID: 2316)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=33FF2C0AC3CCF2B4F5A9F9DE1C426F58 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2892 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9FA4BEFECCF0649080EA9ECA35DF4D97 --renderer-client-id=4 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 2 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2892 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2AD0EF92353C9C78131F1C879FDC3C29 --mojo-platform-channel-handle=608 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2972 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://r.search.yahoo.com/cbclk2/dWU9MjRGQUY0Q0E0RUFGNDBGMCZ1dD0xNTQ2OTc3ODk2MDAwJnVvPTc2MjA5OTk4MTg0NTk5Jmx0PTImZXM9Y1NFbTNLOEdQUy5kdS5KeiZqZT1hYjgyY2M1ZS0xMzgwLTExZTktOWQ3MC0wMDhjZmE1YjU2NWMtMmFlY2I4MWI4NzAwJnVpPTE0NC45LjU2LjEzMSZqdD0xNTQ2OTc3ODk2NTcyJnBwPXMz/RV=2/RE=1547006696/RO=10/RU=https%3a%2f%2fwww.bing.com%2faclick%3fld%3dd3jfwz4HIdW7qdwRmzZmc3HDVUCUxfJBDBM-vuSTs0Y_aalglWtC0hZGBi0maHfQf3Iz6VVvc1RPDrtPrLE6AigFeCJgeY4x8IbppV6gVGn8HsrhKIV5TrUYrF_4vMMHe-sWHx0QI0zznmdvL9EQQFvEOw2h-CTSGLv-ouDToJcl7a9QV4%26u%3dhttp%253a%252f%252fspecialsweetrecipes.com%252f%26rlid%3d7571c41093831969fcae982591eb7c73/RK=2/RS=74nxAxE29wYlv2n86JutM2hoRNY-;_ylt=AwrJ7F1oAjVcIeEAr7VXNyoA;_ylu=X3oDMTE5NjUxdmRjBGNvbG8DYmYxBHBvcwMzBHZ0aWQDQjU4NTlfMQRzZWMDb3YtYm90dG9t;_ylc=X3IDMgRydAMx?p=food+network | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=686A482BB8A185FD0234E4E491AACAB1 --mojo-platform-channel-handle=2332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --service-pipe-token=8FC767577AF1E7C24CB24E9688133455 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8FC767577AF1E7C24CB24E9688133455 --renderer-client-id=3 --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,1112433181398300262,13346142530850764726,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=AD3D7AF5BD644689441E929F2F6C356A --mojo-platform-channel-handle=3716 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
921
Read events
810
Write events
108
Delete events
3
Modification events
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2944) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2968-13191453738170125 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2968-13191453738170125 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
35
Text files
116
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\74802bb0-60c3-48cc-b75f-0942b928756a.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\887550d0-366d-42c9-a0ee-78ce189e87c6.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:1AA66EFDB743FB0A8DCC1CD79B0B6542 | SHA256:28D56532CCED7375A2A1C7731E57C1A1C2EC1AC9827F3E5BEEE7F8069A5F87DD | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:C10EBD4DB49249EFC8D112B2920D5F73 | SHA256:90A1B994CAFE902F22A88A22C0B6CC9CB5B974BF20F8964406DD7D6C9B8867D1 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF198d04.TMP | text | |
MD5:92BE6B127E72365885AD4C3FB6534EE2 | SHA256:54302A2573ACC775720E7DB0AD85873276713302B4F72596A8DCC44B01C70E51 | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF198d42.TMP | text | |
MD5:197882774A7ECEC9046BC48F63189B66 | SHA256:27377B0D5F989997C2C3F74ACF163EED44B60631DDAA768F6655D7BE555742B2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/admin/russia/20150902-panzanella-salad-food-lab-kenji-15-edit-1500x1125.jpg | US | image | 306 Kb | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/admin/russia/chicken-cabbage-stir-fry-recipe-800h.jpg | US | image | 191 Kb | malicious |
2968 | chrome.exe | GET | — | 107.180.51.3:80 | http://specialsweetrecipes.com/admin/russia/lemon-and-honey-roast-chicken-107554-1.jpeg | US | — | — | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/ | US | html | 8.97 Kb | malicious |
2968 | chrome.exe | GET | 200 | 104.19.197.151:80 | http://cdnjs.cloudflare.com/ajax/libs/jstimezonedetect/1.0.6/jstz.min.js | US | text | 4.01 Kb | whitelisted |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/plugin-frameworks/bootstrap.css | US | text | 21.8 Kb | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/fonts/ionicons.css | US | text | 8.65 Kb | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/common/styles.css | US | text | 10.1 Kb | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/dist/sweetalert.css | US | text | 2.34 Kb | malicious |
2968 | chrome.exe | GET | 200 | 107.180.51.3:80 | http://specialsweetrecipes.com/plugin-frameworks/jquery-3.2.1.min.js | US | text | 29.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | chrome.exe | 212.82.100.137:443 | r.search.yahoo.com | Yahoo! UK Services Limited | CH | shared |
2968 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2968 | chrome.exe | 104.19.197.151:80 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2968 | chrome.exe | 107.180.51.3:80 | specialsweetrecipes.com | GoDaddy.com, LLC | US | malicious |
2968 | chrome.exe | 216.58.206.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.18.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.18.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
r.search.yahoo.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.bing.com |
| whitelisted |
specialsweetrecipes.com |
| malicious |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |