| File name: | Kaspersky tweak v.5.0.0.0 lite final.exe |
| Full analysis: | https://app.any.run/tasks/82eb3fc7-af1e-4c15-b7e1-ae93dfcf1e22 |
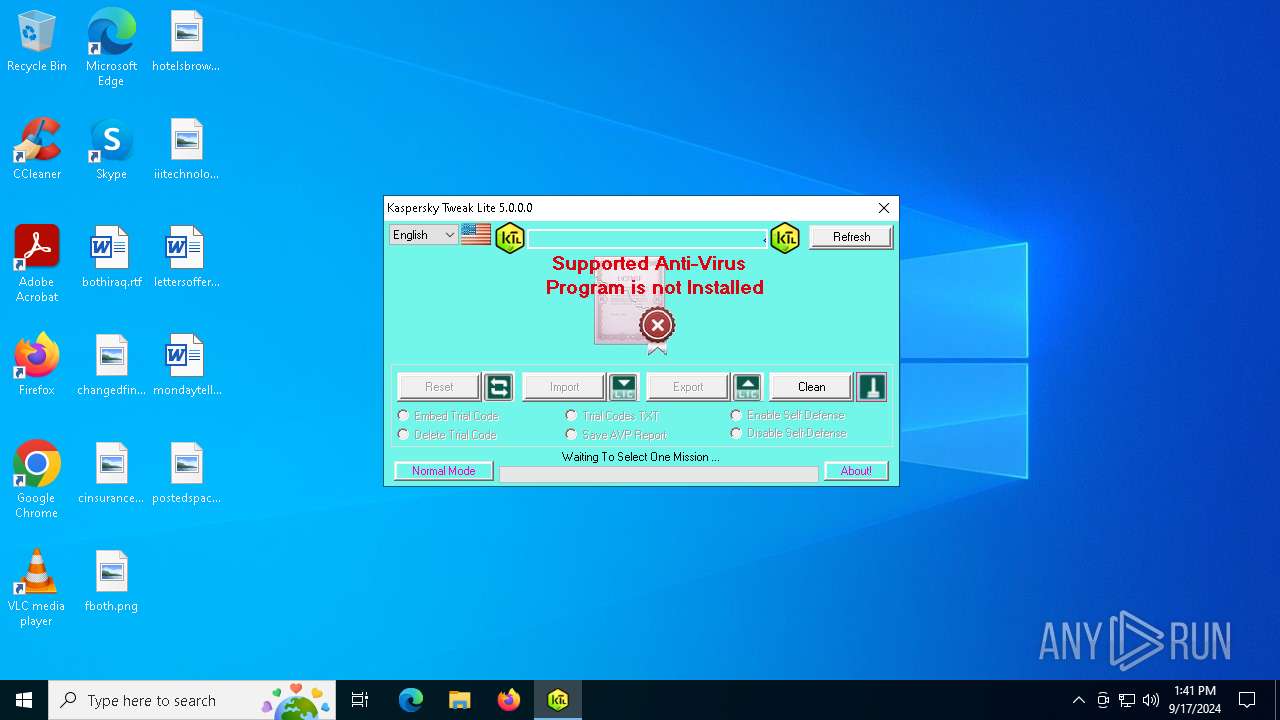
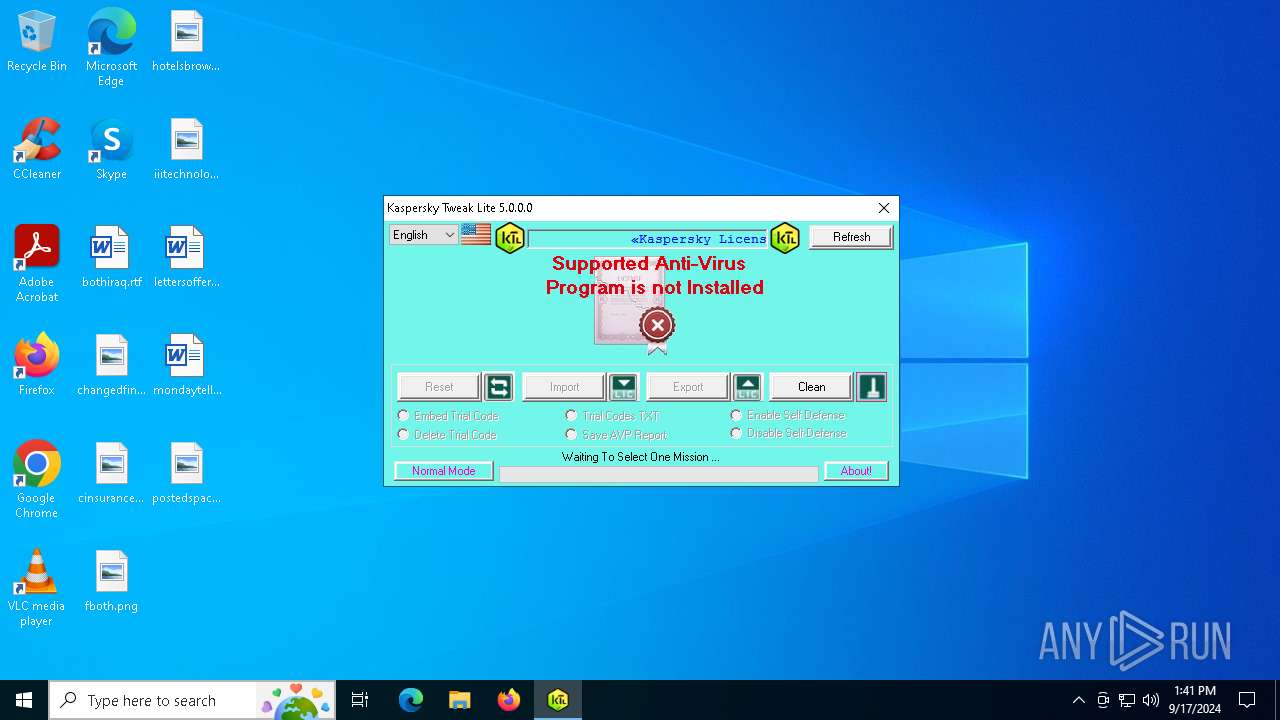
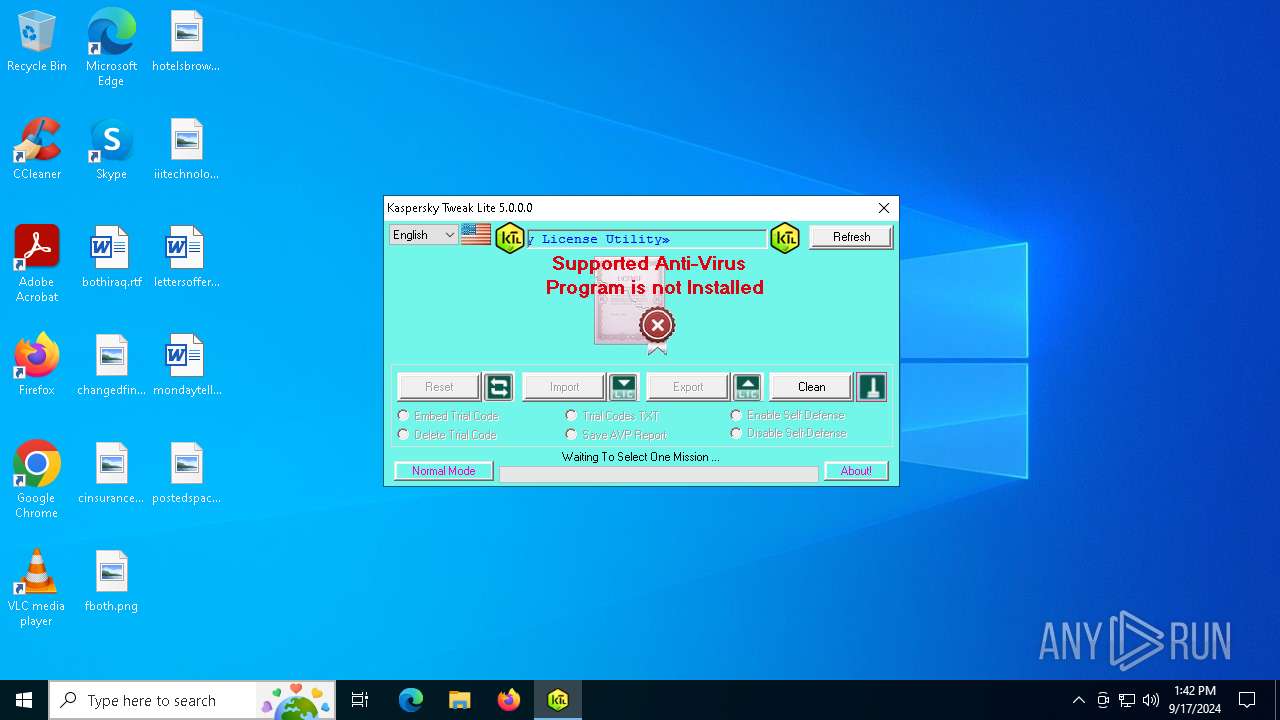
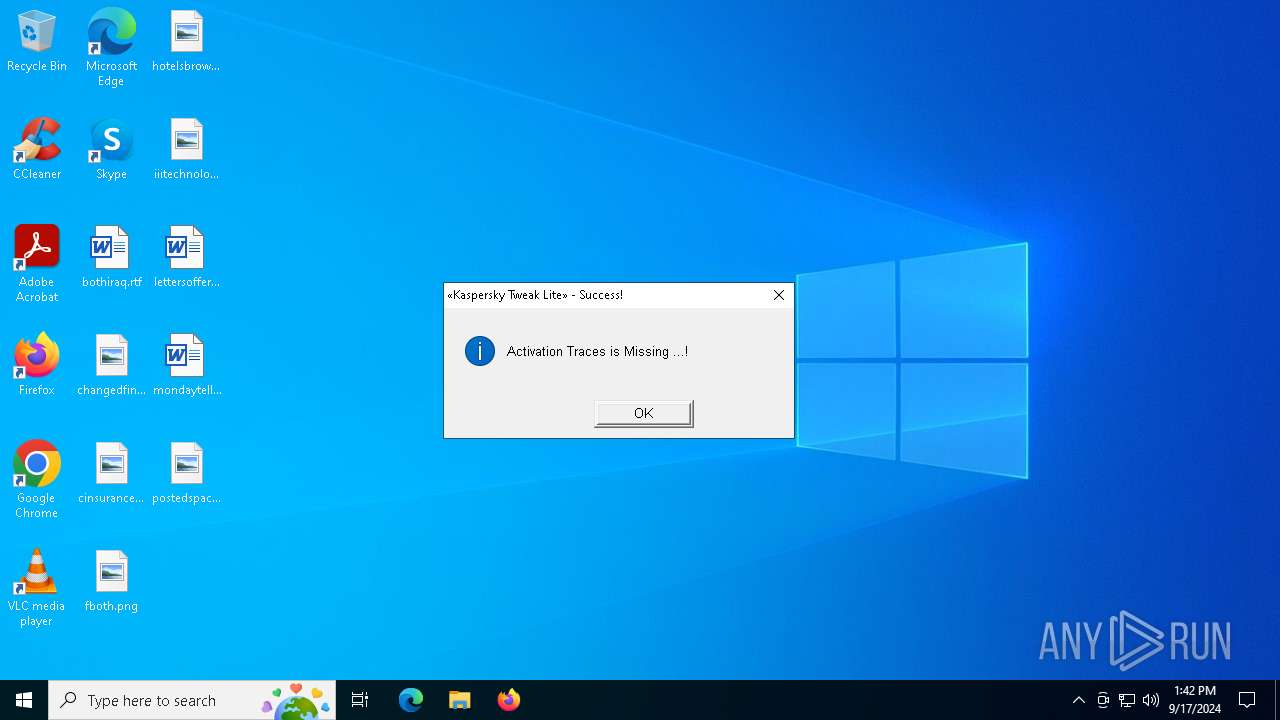
| Verdict: | Malicious activity |
| Analysis date: | September 17, 2024, 13:41:28 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | MS-DOS executable PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, MZ for MS-DOS |
| MD5: | 5EB3831974EEDC1EAE0510F81E49680E |
| SHA1: | 325C87856169171CCC96A94547D1F104879EB37E |
| SHA256: | BAC767BF1C06B9FFE76E9662E197224EBF5C17A449EB81AC0D31DA6039138EF6 |
| SSDEEP: | 49152:uAKda+xbKBV6Z0m3aXL227BRzxX2kIqRTA1zDOcx9FuS7N2Gw3xGw3SnT5gf063F:x+RK6ZF3e7LxX2kPZA1zDOUuS5jwBG1u |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- Kaspersky tweak v.5.0.0.0 lite final.exe (PID: 3864)
INFO
Mpress packer has been detected
- Kaspersky tweak v.5.0.0.0 lite final.exe (PID: 3864)
- Kaspersky tweak v.5.0.0.0 lite final.exe (PID: 7016)
The process uses AutoIt
- Kaspersky tweak v.5.0.0.0 lite final.exe (PID: 3864)
- Kaspersky tweak v.5.0.0.0 lite final.exe (PID: 7016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:06:03 14:10:47+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 633856 |
| InitializedDataSize: | 1247232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d13f8 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.0.0 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 5.0.0.0 |
| ProductVersion: | 5.0.0.0 |
| ProductName: | Kaspersky Tweak Lite |
| OriginalFileName: | KTL |
| InternalName: | KTL |
| FileDescription: | Kaspersky Tweak Lite |
| CompanyName: | TAWAB Soft 2024 |
| LegalTrademarks: | TAWAB Soft 2024 |
| LegalCopyright: | TAWAB Soft 2024 |
| Comments: | please visit : http://forum.zyzoom.net/ |
Total processes
125
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3864 | "C:\Users\admin\AppData\Local\Temp\Kaspersky tweak v.5.0.0.0 lite final.exe" | C:\Users\admin\AppData\Local\Temp\Kaspersky tweak v.5.0.0.0 lite final.exe | explorer.exe | ||||||||||||
User: admin Company: TAWAB Soft 2024 Integrity Level: HIGH Description: Kaspersky Tweak Lite Exit code: 0 Version: 5.0.0.0 Modules
| |||||||||||||||
| 5736 | "C:\Users\admin\AppData\Local\Temp\Kaspersky tweak v.5.0.0.0 lite final.exe" | C:\Users\admin\AppData\Local\Temp\Kaspersky tweak v.5.0.0.0 lite final.exe | — | explorer.exe | |||||||||||
User: admin Company: TAWAB Soft 2024 Integrity Level: MEDIUM Description: Kaspersky Tweak Lite Exit code: 3221226540 Version: 5.0.0.0 Modules
| |||||||||||||||
| 7016 | C:\Users\admin\AppData\Local\Temp\KASPER~1.EXE | C:\Users\admin\AppData\Local\Temp\Kaspersky tweak v.5.0.0.0 lite final.exe | Kaspersky tweak v.5.0.0.0 lite final.exe | ||||||||||||
User: admin Company: TAWAB Soft 2024 Integrity Level: HIGH Description: Kaspersky Tweak Lite Exit code: 0 Version: 5.0.0.0 Modules
| |||||||||||||||
Total events
1 146
Read events
1 136
Write events
6
Delete events
4
Modification events
| (PID) Process: | (3864) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3864) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3864) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3864) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (3864) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
| (PID) Process: | (7016) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7016) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7016) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7016) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (7016) Kaspersky tweak v.5.0.0.0 lite final.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
0
Suspicious files
4
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\flag_usa.jpg | image | |
MD5:37CC8C7241C52CF03BA78EAA368975C0 | SHA256:016C98C51F7326E5DCA1EF44DF06F71B21B51E49442CA1F5E751EC8ED75E7AA8 | |||
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\Nolicense.jpg | image | |
MD5:3BDC5C25DE0F1A8C29C44049AB77CB8C | SHA256:53F5FEE17915B07125DFA2E2101C41960D18DCC0C3AFCFBDFF740E8B746F9635 | |||
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\~DF0CE17FF98AC3C1B5.TMP | binary | |
MD5:159AC8986A86AA64723DF494DEC40E32 | SHA256:D3AD3B8A41F400B756123D22F179310B0C421B62C667FFCB50D7E933A008C3AE | |||
| 7016 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\DelTraces.ico | image | |
MD5:5F63D7837ACDE31C13C8D3C905BC4D6D | SHA256:7D9DC98DADA1E641ABD39459A5B735164486CA0FE93A705E5A8EBFC5E57926BF | |||
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\~DFB139A45637A1CC28.TMP | binary | |
MD5:8312A8F8E133D941792C06A7EEADD32C | SHA256:248742B0003DB1F011E6024619DD23D8FEE429B7E71075AC7A779E52B1271F1E | |||
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\licReset.ico | image | |
MD5:65E328AC8667E56B91F34411635E4F5A | SHA256:134F2698140BA21472646DBED559956BD06EB40C3363813B8696182E6F3ADEDA | |||
| 3864 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\licExpo.ico | image | |
MD5:ACB74483BF38B4497FCFD0B275FFE743 | SHA256:E09A4C4062797E06CE8DD03960A43067EEA2BEAABF70C7FFE370F6434F56D698 | |||
| 7016 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\~DF07B8C410830200A1.TMP | binary | |
MD5:9B35697FACB2E489C1A3D3895985BFED | SHA256:2F11F15C4C7CDAEF2A0FC855F6882C1F72F02C7EEDDD7064681DA323E8ACC1F4 | |||
| 7016 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\Nolicense.jpg | image | |
MD5:3BDC5C25DE0F1A8C29C44049AB77CB8C | SHA256:53F5FEE17915B07125DFA2E2101C41960D18DCC0C3AFCFBDFF740E8B746F9635 | |||
| 7016 | Kaspersky tweak v.5.0.0.0 lite final.exe | C:\Users\admin\AppData\Local\Temp\licExpo.ico | image | |
MD5:ACB74483BF38B4497FCFD0B275FFE743 | SHA256:E09A4C4062797E06CE8DD03960A43067EEA2BEAABF70C7FFE370F6434F56D698 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
28
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
752 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
752 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2968 | svchost.exe | GET | 200 | 2.16.164.106:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
1964 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4648 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6340 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 52.167.249.196:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1964 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1964 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |