| File name: | margintp1.exe |
| Full analysis: | https://app.any.run/tasks/4d5c49ef-94ac-4714-bd38-4641ab683f9f |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 13:29:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4CA462E9FDB89EF30C36AD4BF68D596E |
| SHA1: | 25CB36A84ED102E5B219C6F8CE33AA5733C34A73 |
| SHA256: | BABB7CA5D32DD5A32D030CC7281AA3639D579916707E35D4FEBF1BE73D2D1DC1 |
| SSDEEP: | 98304:+6Zq7OhsuNpo5DBGQEJ399c8Urtc2LNPQYBRfFTwN:+2+V+fP8cePQ6pFTE |
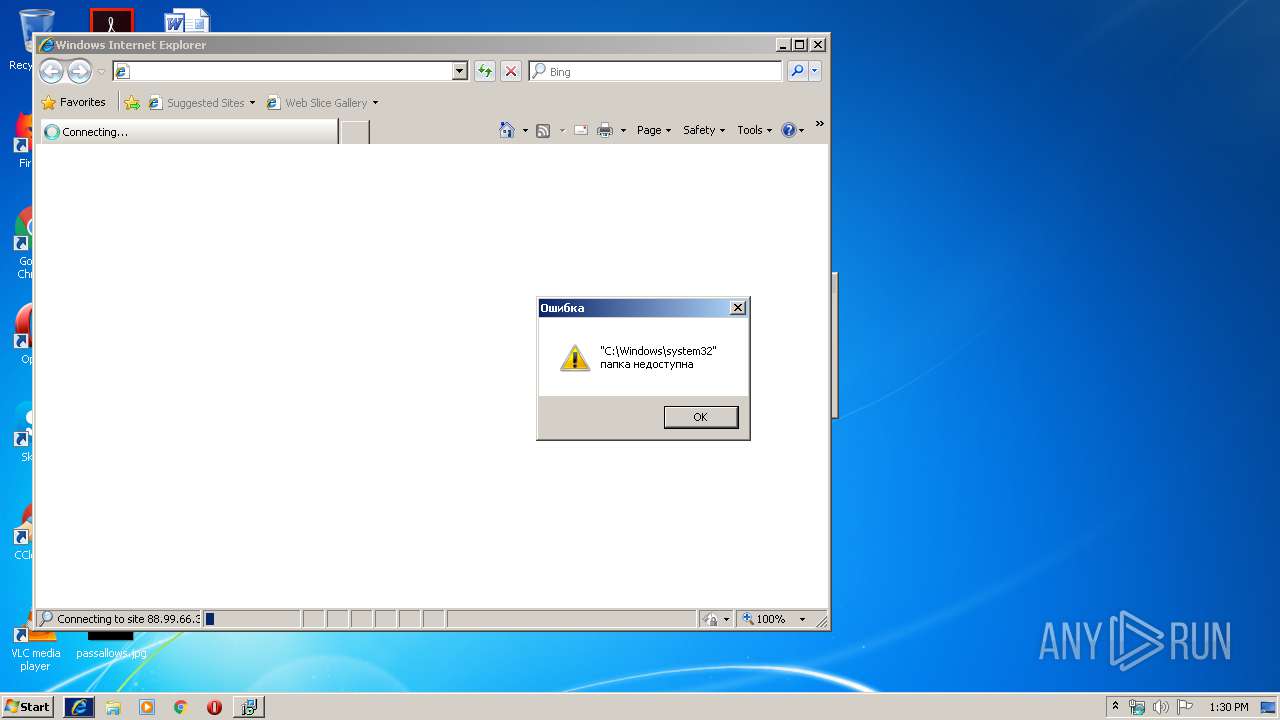
MALICIOUS
Loads the Task Scheduler DLL interface
- margintp1.exe (PID: 2840)
Loads dropped or rewritten executable
- margintp1.exe (PID: 2840)
SUSPICIOUS
Reads Environment values
- margintp1.exe (PID: 2840)
- MsiExec.exe (PID: 2384)
- MsiExec.exe (PID: 1044)
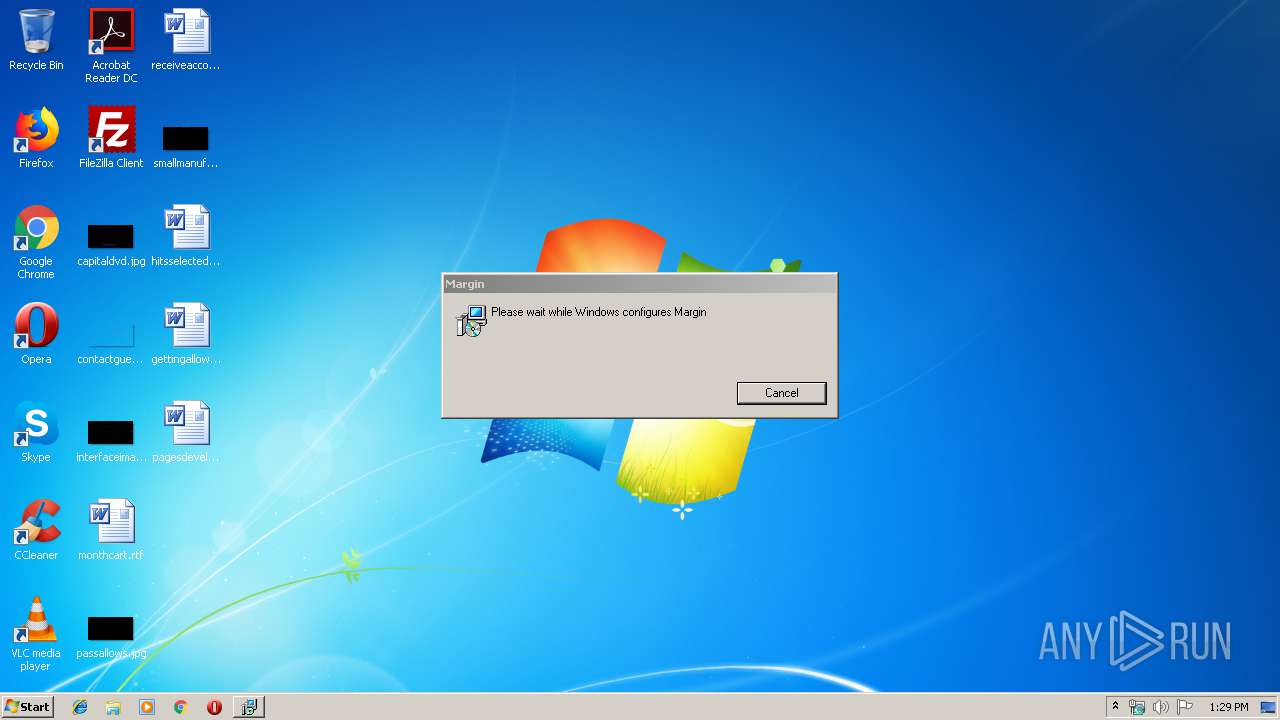
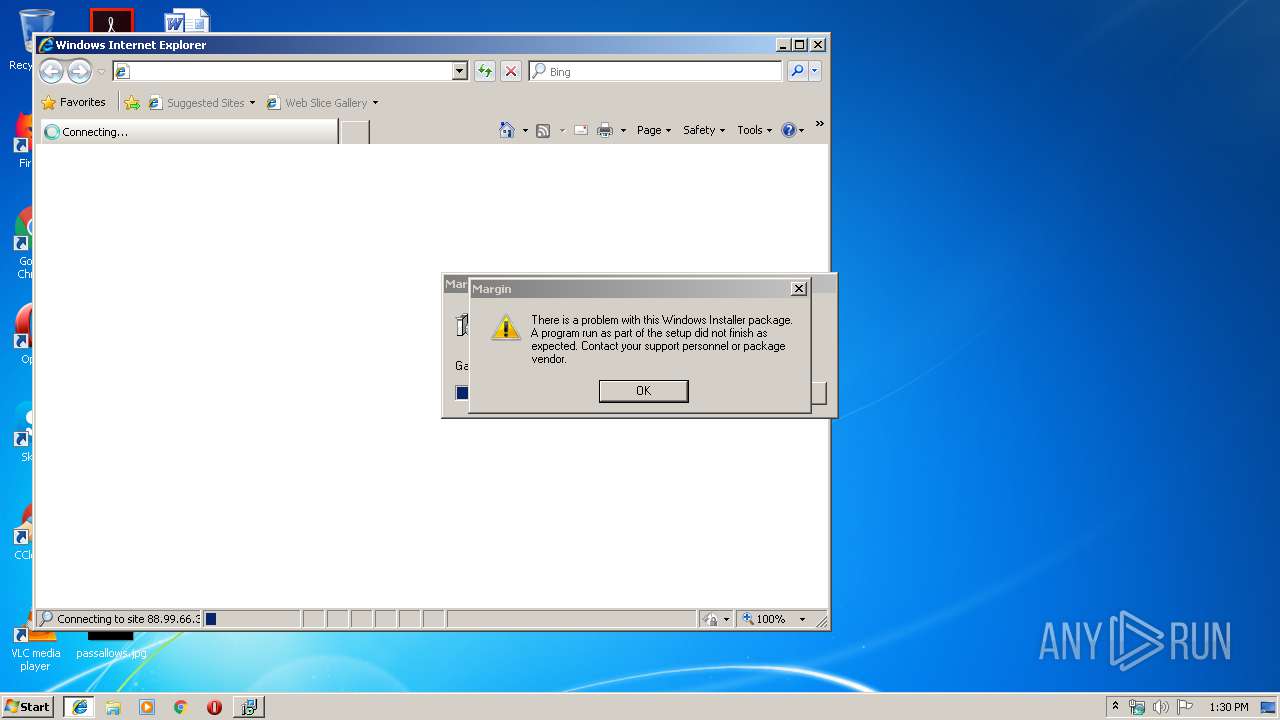
Starts Microsoft Installer
- margintp1.exe (PID: 2840)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2280)
- margintp1.exe (PID: 2840)
Executed via COM
- iexplore.exe (PID: 3740)
Creates files in the user directory
- margintp1.exe (PID: 2840)
Executed as Windows Service
- vssvc.exe (PID: 3396)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 3396)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 1044)
- MsiExec.exe (PID: 2384)
Searches for installed software
- msiexec.exe (PID: 2280)
Changes internet zones settings
- iexplore.exe (PID: 3740)
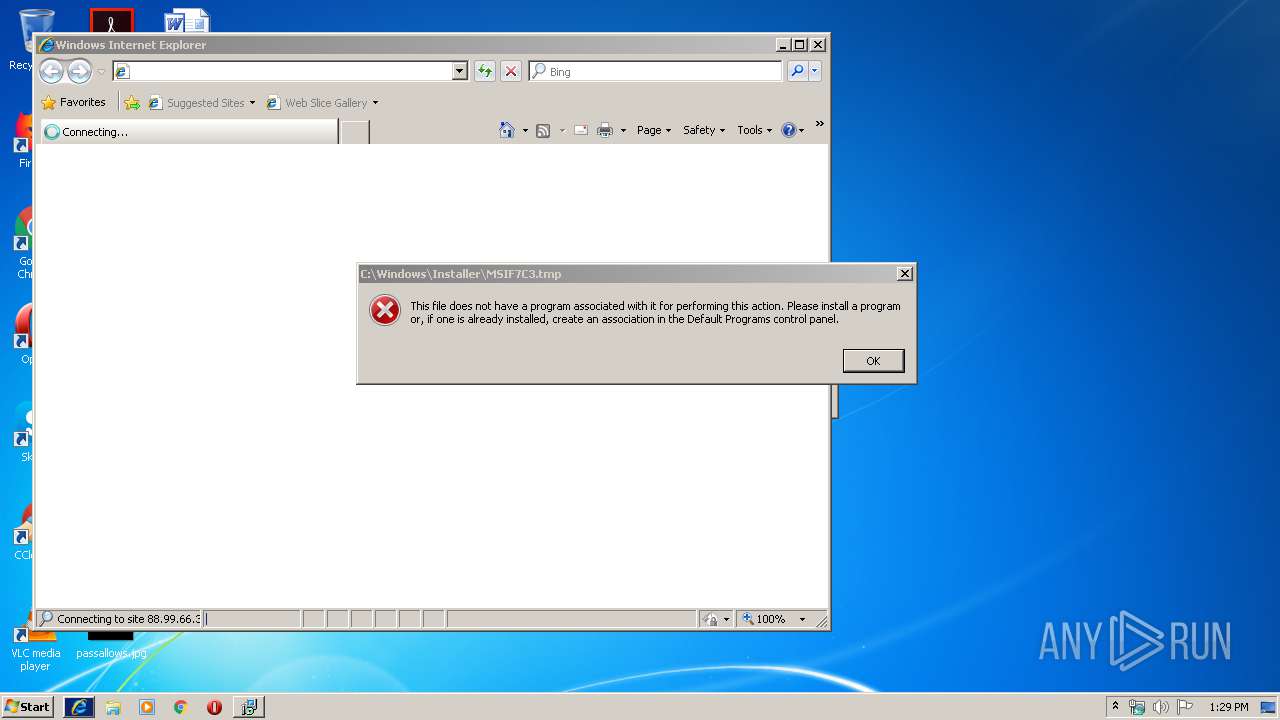
Application was dropped or rewritten from another process
- MSIF7C3.tmp (PID: 272)
- MSIF15A.tmp (PID: 3968)
Starts application with an unusual extension
- msiexec.exe (PID: 2280)
Application launched itself
- msiexec.exe (PID: 2280)
Reads internet explorer settings
- iexplore.exe (PID: 2196)
Reads Internet Cache Settings
- iexplore.exe (PID: 2196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:11:13 09:49:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.23 |
| CodeSize: | 1501184 |
| InitializedDataSize: | 599552 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11af1c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.7.13.0 |
| ProductVersionNumber: | 7.7.13.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Margin Trade |
| FileDescription: | Margin Installer |
| FileVersion: | 7.7.13 |
| InternalName: | margintp1 |
| LegalCopyright: | Copyright (C) 2019 Margin Trade |
| OriginalFileName: | margintp1.exe |
| ProductName: | Margin |
| ProductVersion: | 7.7.13 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Nov-2019 08:49:41 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Margin Trade |
| FileDescription: | Margin Installer |
| FileVersion: | 7.7.13 |
| InternalName: | margintp1 |
| LegalCopyright: | Copyright (C) 2019 Margin Trade |
| OriginalFileName: | margintp1.exe |
| ProductName: | Margin |
| ProductVersion: | 7.7.13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 13-Nov-2019 08:49:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0016E7EF | 0x0016E800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45011 |
.rdata | 0x00170000 | 0x0005E7BC | 0x0005E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.60173 |
.data | 0x001CF000 | 0x000070F8 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.05657 |
.rsrc | 0x001D7000 | 0x000152B8 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.36148 |
.reloc | 0x001ED000 | 0x0001952C | 0x00019600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55919 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.221 | 1915 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.1591 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.46873 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.54157 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.01317 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.35254 | 1888 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.35766 | 820 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
46
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\Installer\MSIF7C3.tmp" -p123 -s1 | C:\Windows\Installer\MSIF7C3.tmp | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1044 | C:\Windows\system32\MsiExec.exe -Embedding A0E1F459DD38C0DFCF0ED9FCDB515424 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3740 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2384 | C:\Windows\system32\MsiExec.exe -Embedding 49F18E5229436EBFE024DB56D93CDDB6 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\Margin Trade\Margin 7.7.13\install\27C4E79\margintp1.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\margintp1.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1575635198 " AI_EUIMSI="" | C:\Windows\system32\msiexec.exe | — | margintp1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Users\admin\AppData\Local\Temp\margintp1.exe" | C:\Users\admin\AppData\Local\Temp\margintp1.exe | explorer.exe | ||||||||||||
User: admin Company: Margin Trade Integrity Level: MEDIUM Description: Margin Installer Exit code: 1603 Version: 7.7.13 Modules
| |||||||||||||||
| 3396 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3740 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
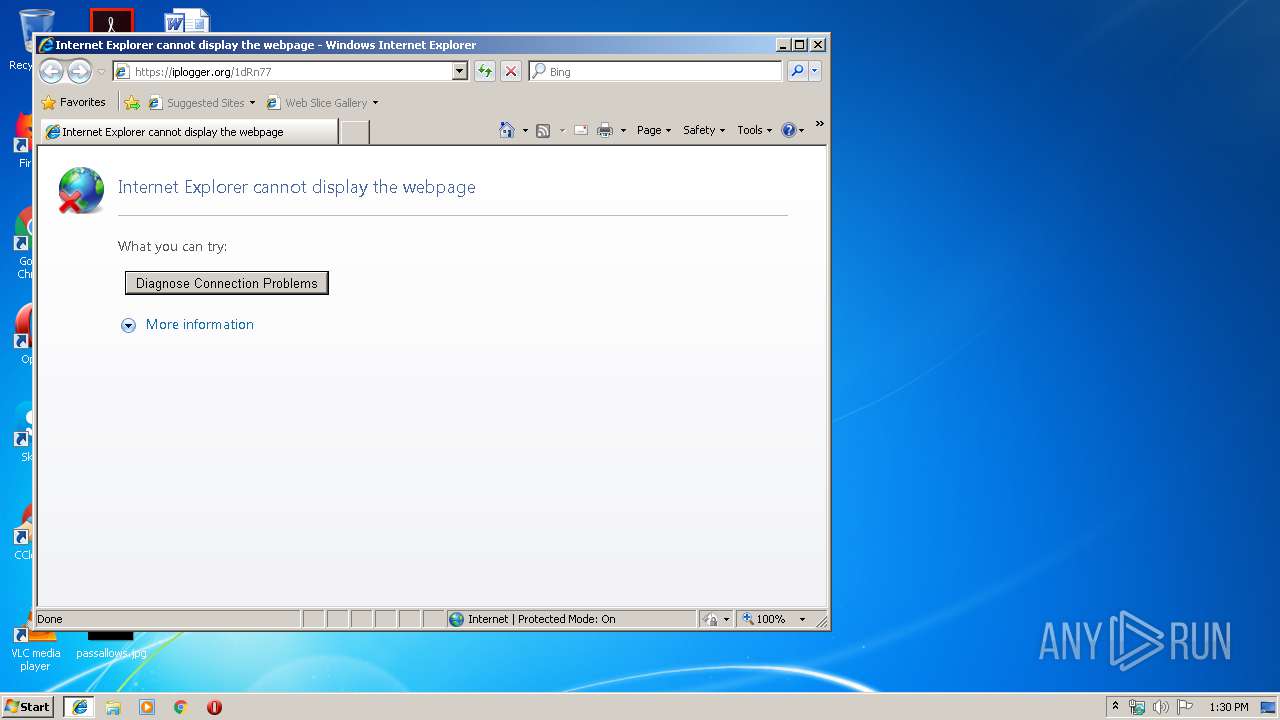
| 3968 | "C:\Windows\Installer\MSIF15A.tmp" https://iplogger.org/1dRn77 | C:\Windows\Installer\MSIF15A.tmp | msiexec.exe | ||||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 0 Version: 16.5.0.0 Modules
| |||||||||||||||
Total events
1 539
Read events
1 341
Write events
193
Delete events
5
Modification events
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000C44A213639ACD501E8080000580A0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000C44A213639ACD501E8080000580A0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 33 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000004966D3639ACD501E8080000580A0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2280) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005EF86F3639ACD501E8080000980A0000E8030000010000000000000000000000BD49508A3E2B7144A535CEEFE406977E0000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E2CF873639ACD501440D0000C00A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E2CF873639ACD501440D00003C0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E2CF873639ACD501440D00001C0C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000E2CF873639ACD501440D0000300F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3396) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000004A59913639ACD501440D00001C0C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
9
Suspicious files
4
Text files
73
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | margintp1.exe | C:\Users\admin\AppData\Local\Temp\MSIAF37.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIED49.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIED5A.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIED7A.tmp | — | |
MD5:— | SHA256:— | |||
| 3396 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIEFEC.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIEFED.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIF0AA.tmp | — | |
MD5:— | SHA256:— | |||
| 2280 | msiexec.exe | C:\Windows\Installer\MSIF0F9.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3740 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3740 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2196 | iexplore.exe | 88.99.66.31:443 | iplogger.org | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
iplogger.org |
| shared |
dns.msftncsi.com |
| shared |
Threats
1 ETPRO signatures available at the full report
Process | Message |
|---|---|
margintp1.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\margintp1.exe] CPU: __isa_available = 5
|
margintp1.exe | [AVX_CRT_Fix][\\?\C:\Users\admin\AppData\Roaming\Margin Trade\Margin 7.7.13\install\decoder.dll] CPU: __isa_available = 5
|
margintp1.exe | [AVX_CRT_Fix][\\?\C:\Users\admin\AppData\Roaming\Margin Trade\Margin 7.7.13\install\decoder.dll] CPU: __isa_available = 5
|
margintp1.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\INAAF17.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIAF37.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIAFE4.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIEBF1.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIED49.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIED5A.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIED7A.tmp] CPU: __isa_available = 5
|