| File name: | redirect2.txt |
| Full analysis: | https://app.any.run/tasks/b4995443-9d36-4df4-942d-4db7fafe873b |
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2025, 13:38:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | BE2D0339F48716164D7C79679AA9BD0C |
| SHA1: | 7311702E4716F82A5A232809885A60254D9005E8 |
| SHA256: | BAB2A162EACE4C6BE3639388A933E1F62054341B159A67123402DD0EB5FAD73F |
| SSDEEP: | 192:F6W74zmJQfwAuYmeZHFqkKNBD57Gyo/AbAYAaZZpsUsgsxp:F6W74sYmWHBW5kUBDZZ+Jdxp |
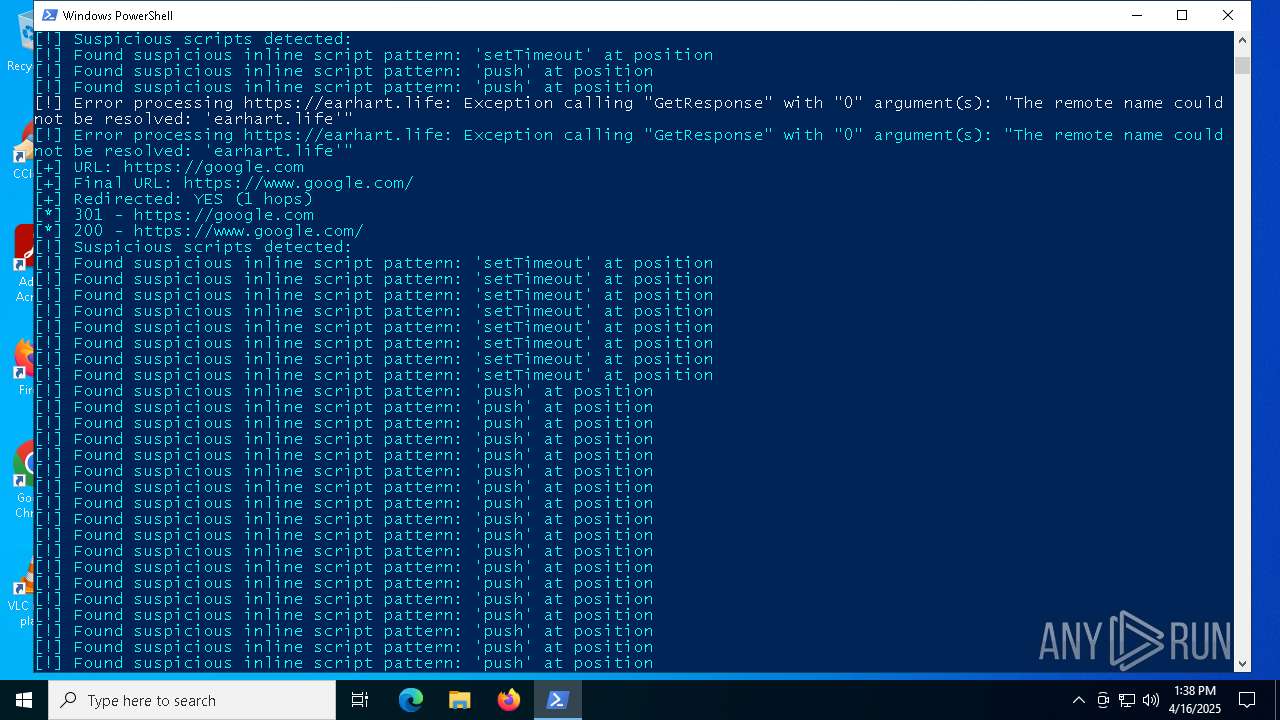
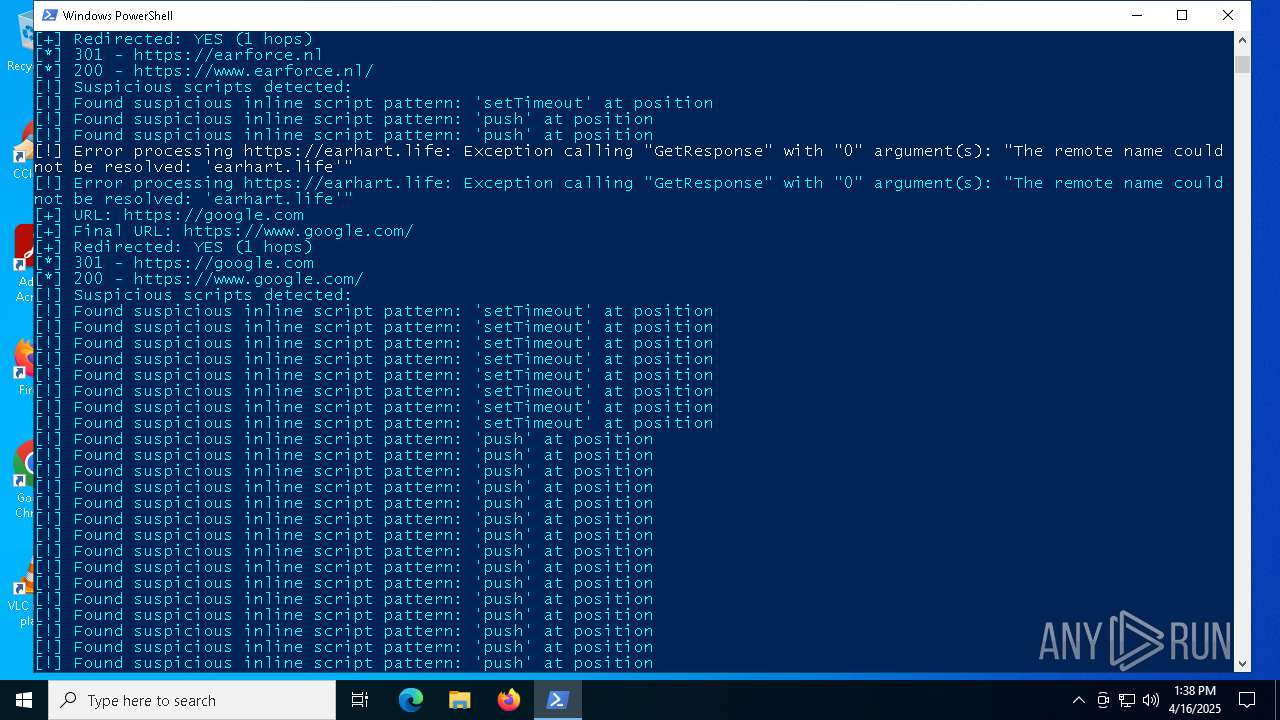
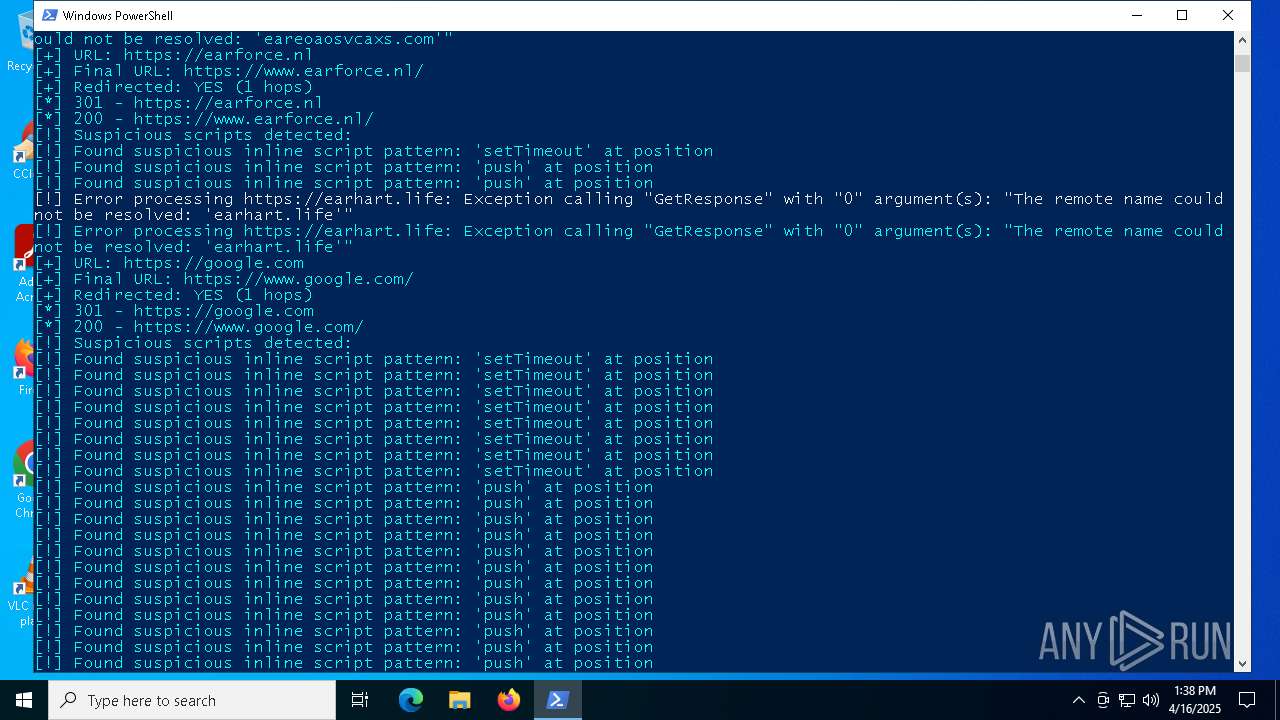
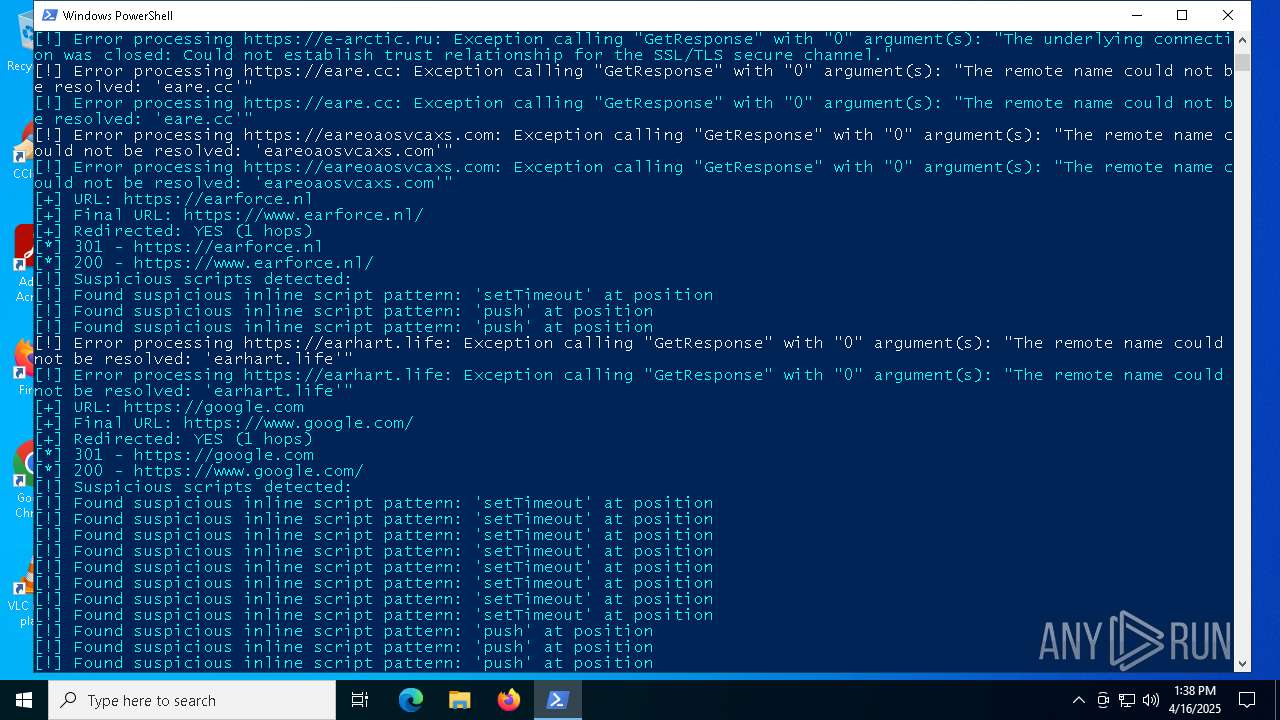
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 6048)
Connects to the CnC server
- powershell.exe (PID: 6048)
SUSPICIOUS
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 6048)
INFO
Disables trace logs
- powershell.exe (PID: 6048)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 6048)
Checks proxy server information
- powershell.exe (PID: 6048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\redirect2.txt.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6184 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 444
Read events
5 444
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jehrdzuo.fl0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bc7c.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_p1mlmhtt.n4f.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\KXK4XZMB3NYPIN3XEU5D.temp | binary | |
MD5:218C28EE8AF5FC0BF0D4131A76EF26D6 | SHA256:7E4CB7345C477E0FBCBBF31ECAB3AB2E4EAF8675F48E24DBD2256BD2544DD7D6 | |||
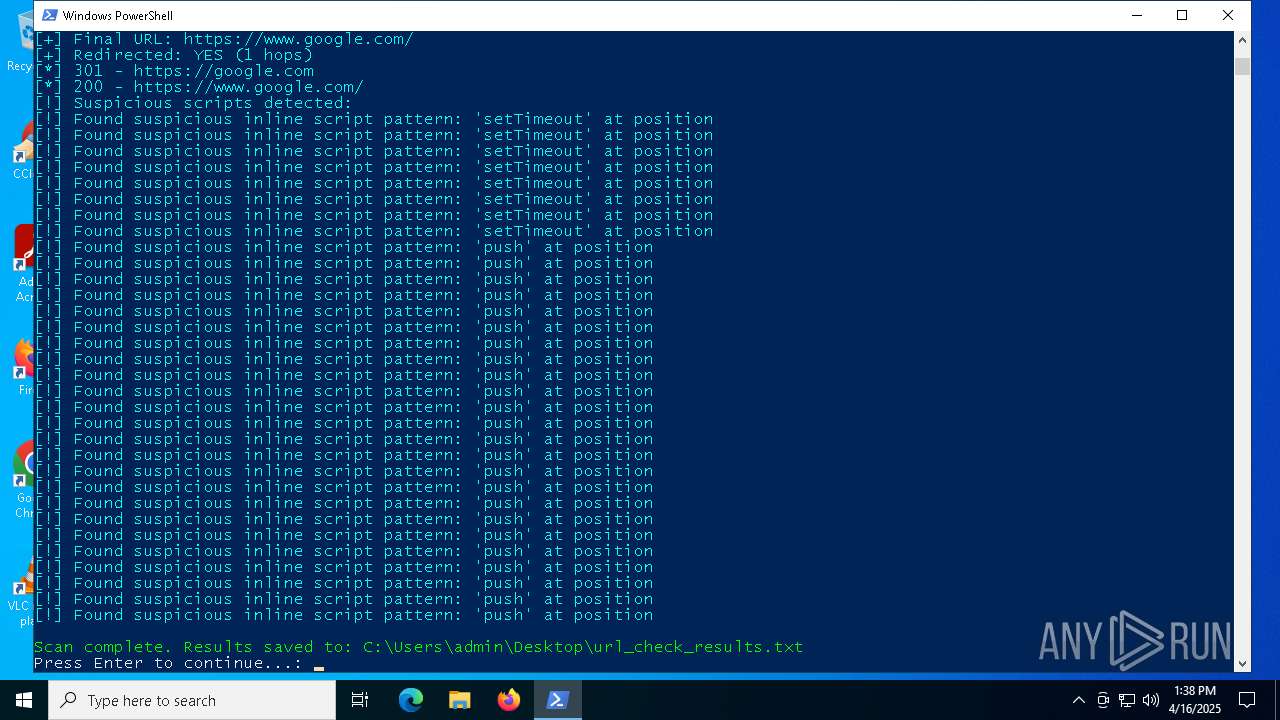
| 6048 | powershell.exe | C:\Users\admin\Desktop\url_check_results.txt | binary | |
MD5:BD73AA59484DEB36377739C197B43C37 | SHA256:A60B90226566DE43FD9950CA915D11EF2C73534DA75BDAFABE5FBF69B0C956E4 | |||
| 6048 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:218C28EE8AF5FC0BF0D4131A76EF26D6 | SHA256:7E4CB7345C477E0FBCBBF31ECAB3AB2E4EAF8675F48E24DBD2256BD2544DD7D6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
28
DNS requests
27
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6640 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
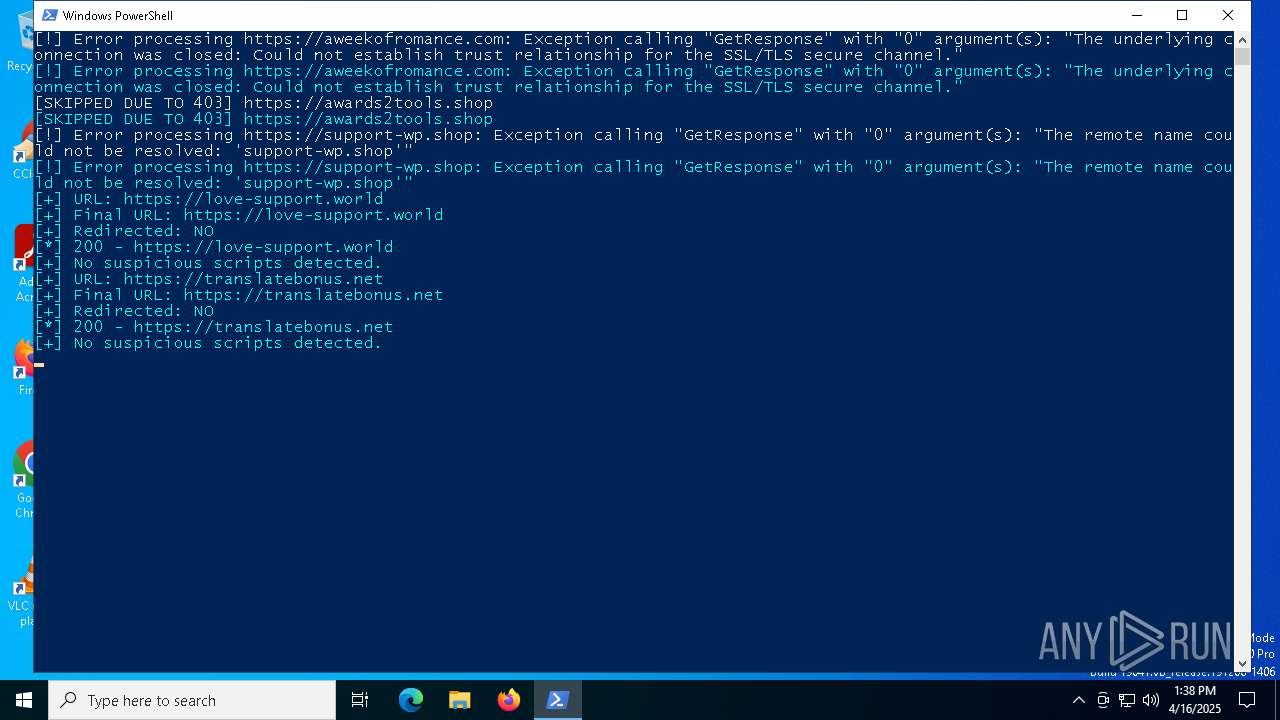
6048 | powershell.exe | 82.115.223.60:443 | aweekofromance.com | Partner LLC | RU | malicious |
6048 | powershell.exe | 15.197.130.221:443 | awards2tools.shop | AMAZON-02 | US | malicious |
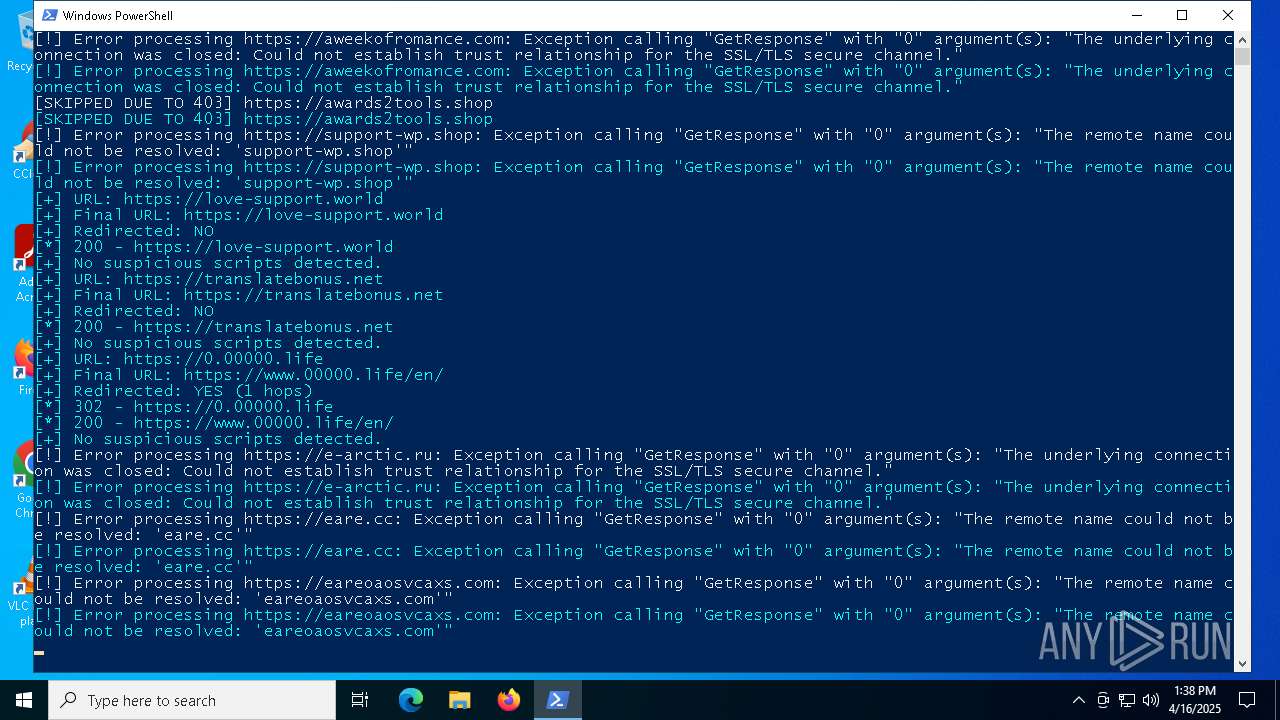
6048 | powershell.exe | 172.67.197.99:443 | 0.00000.life | CLOUDFLARENET | US | unknown |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
6048 | powershell.exe | 31.31.205.163:443 | e-arctic.ru | Domain names registrar REG.RU, Ltd | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
aweekofromance.com |
| malicious |
awards2tools.shop |
| malicious |
support-wp.shop |
| malicious |
love-support.world |
| malicious |
translatebonus.net |
| malicious |
0.00000.life |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Suspected Malicious domain by CrossDomain (love-support .world) |
6048 | powershell.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 4 |
6048 | powershell.exe | Misc Attack | ET Threatview.io High Confidence Cobalt Strike C2 IP group 5 |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |