| File name: | Clean201903211242_xp_compress.exe |
| Full analysis: | https://app.any.run/tasks/30afde07-5367-463f-a185-7c53191792bd |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2019, 14:48:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 1133537AF207AC1925C3E2B26C6D75B1 |
| SHA1: | AAC7BD49CDAB50F6C206C9736614D39180535931 |
| SHA256: | BAAF3D2485FF9FF393BD67DD3CE6E029D5F9F3580BF8379BBF8780C4283AE34C |
| SSDEEP: | 1536:WdzJWWPAXPd8d3yQlUUsWG9hmDg4xDm8gy86AvxH17JiJl00gD28biVi4nKtw:Wdt3P2m3yQlU2l0qDdGdZH2l0hlbeiYp |
MALICIOUS
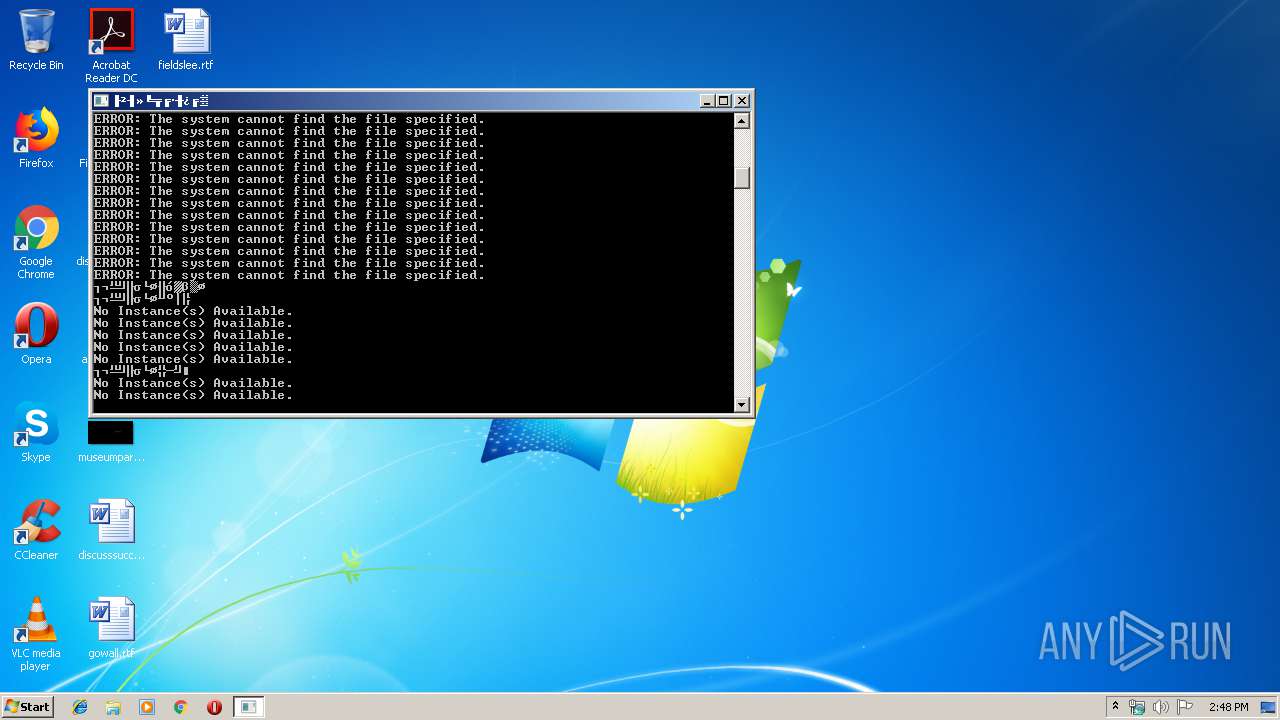
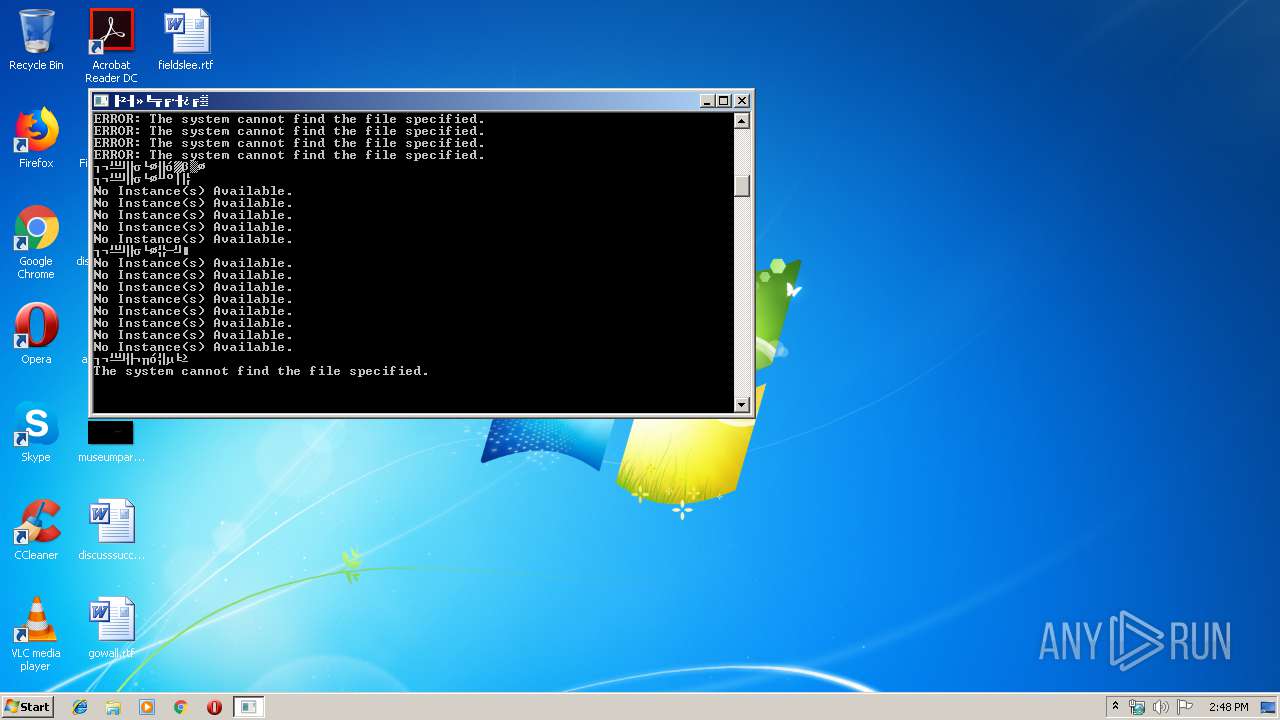
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 2208)
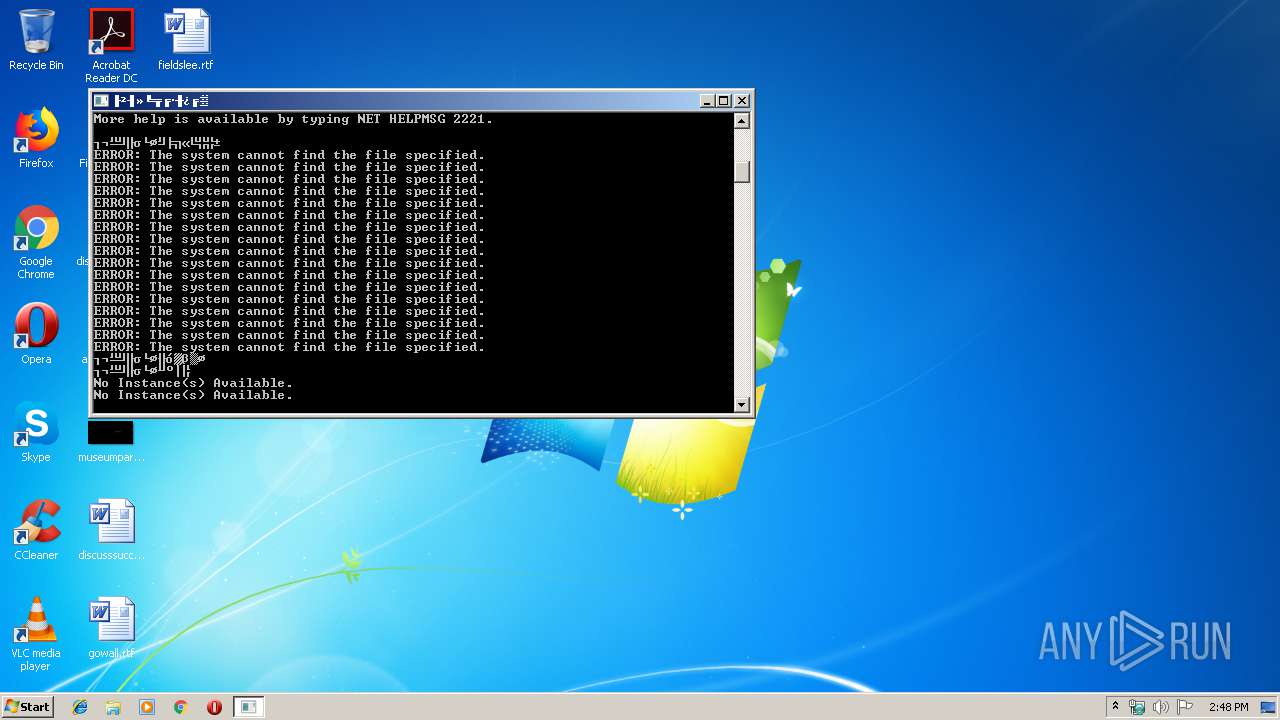
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3816)
- schtasks.exe (PID: 2648)
- schtasks.exe (PID: 3588)
- schtasks.exe (PID: 3428)
- schtasks.exe (PID: 2200)
- schtasks.exe (PID: 3112)
- schtasks.exe (PID: 3908)
- schtasks.exe (PID: 2744)
- schtasks.exe (PID: 3756)
- schtasks.exe (PID: 3248)
- schtasks.exe (PID: 3612)
- schtasks.exe (PID: 2708)
- schtasks.exe (PID: 3508)
- schtasks.exe (PID: 2512)
- schtasks.exe (PID: 3396)
- schtasks.exe (PID: 2676)
- schtasks.exe (PID: 2300)
- schtasks.exe (PID: 3164)
- schtasks.exe (PID: 2460)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 2388)
- cmd.exe (PID: 3632)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 3296)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 4060)
- cmd.exe (PID: 2260)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 2864)
- cmd.exe (PID: 2412)
- cmd.exe (PID: 3236)
- cmd.exe (PID: 1672)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 3128)
- cmd.exe (PID: 4052)
- cmd.exe (PID: 3660)
- cmd.exe (PID: 3664)
- cmd.exe (PID: 2924)
- cmd.exe (PID: 3772)
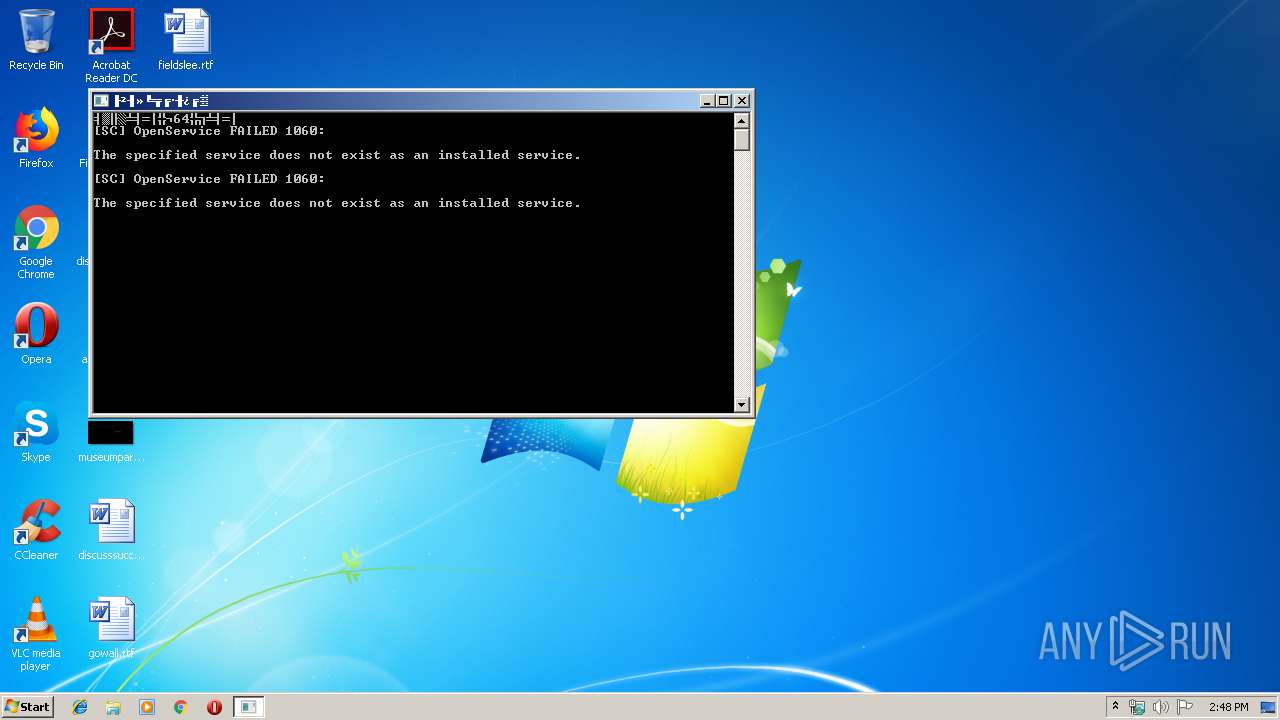
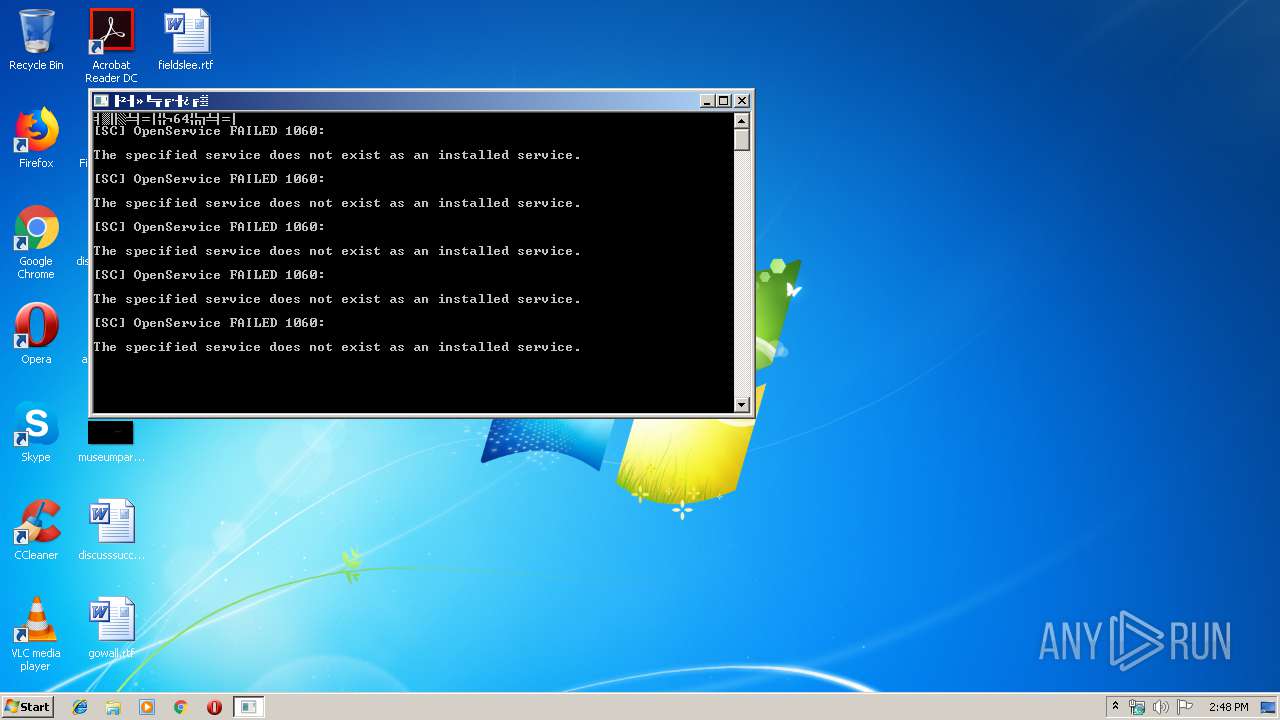
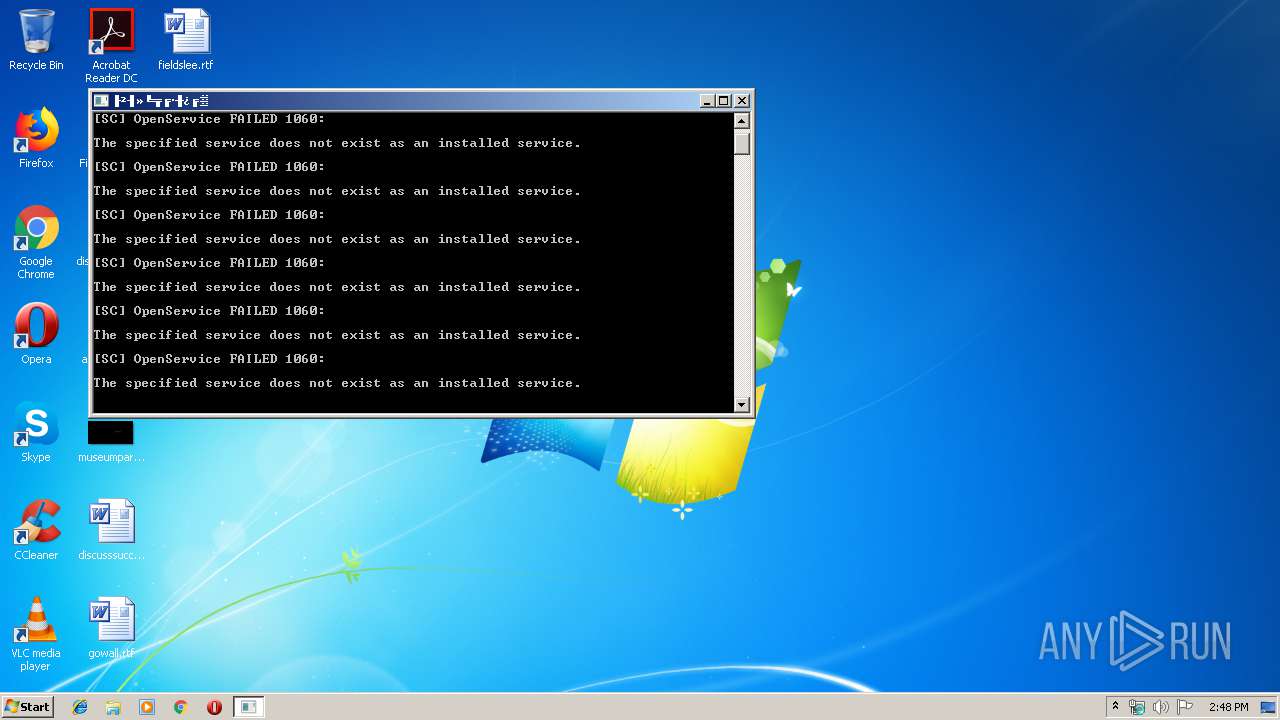
SUSPICIOUS
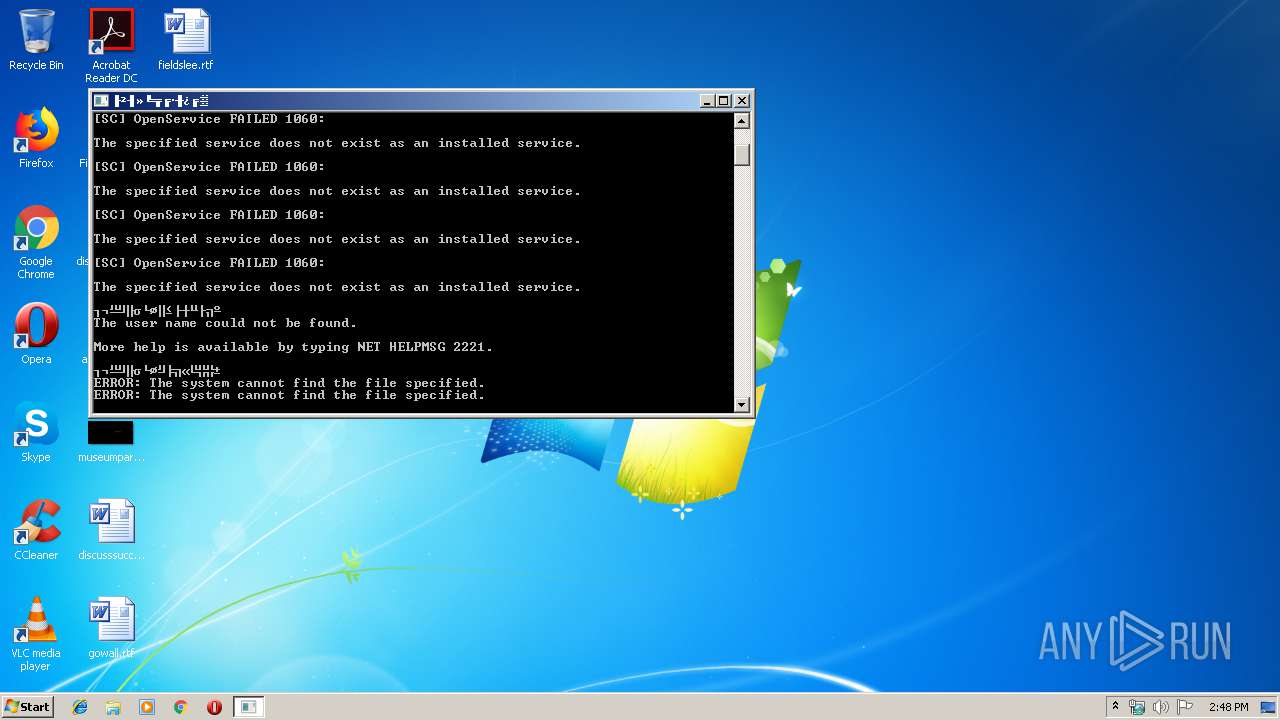
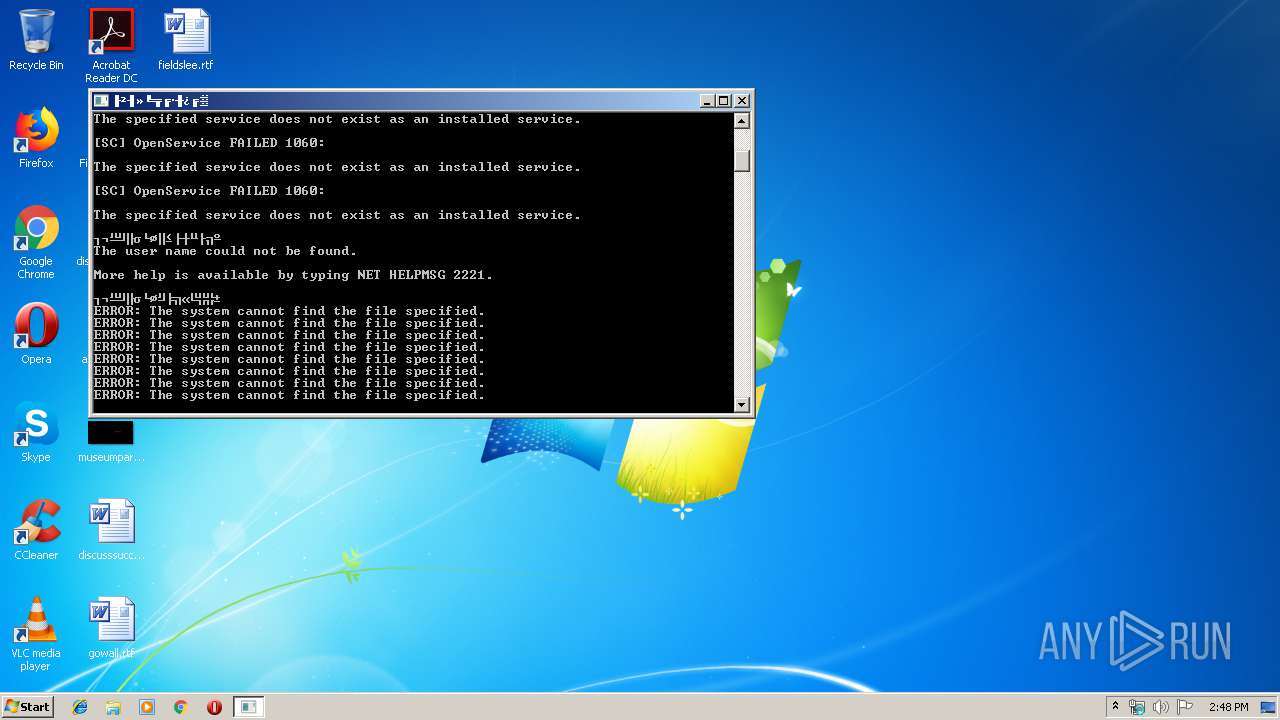
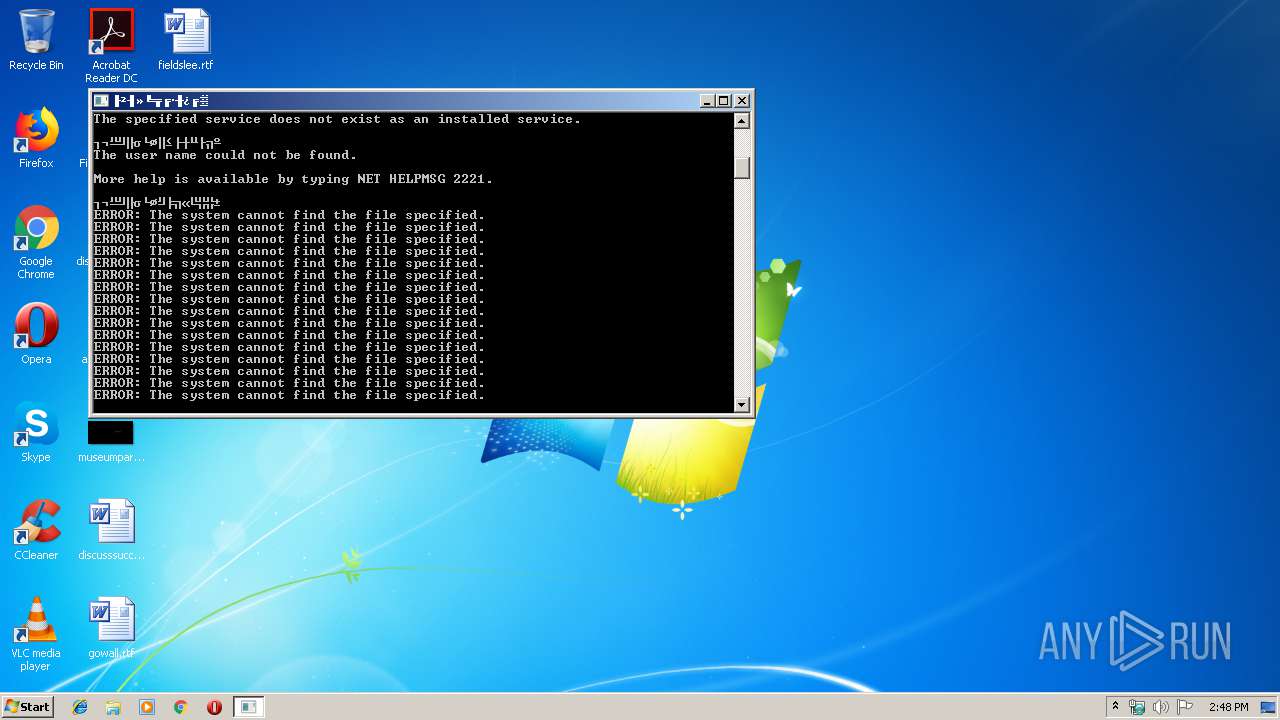
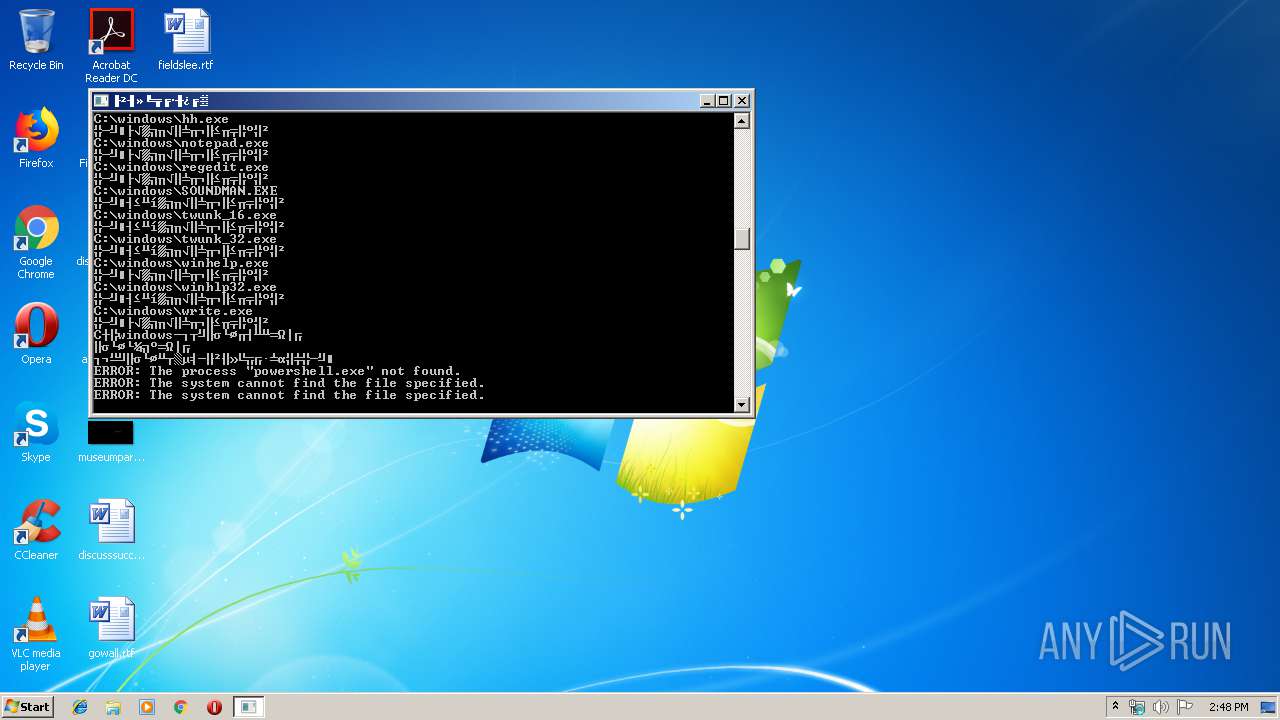
Starts SC.EXE for service management
- cmd.exe (PID: 3748)
- cmd.exe (PID: 2764)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 3232)
- cmd.exe (PID: 3212)
- cmd.exe (PID: 2236)
- cmd.exe (PID: 3752)
Starts CMD.EXE for commands execution
- Clean201903211242_xp_compress.exe (PID: 3472)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3048)
- cmd.exe (PID: 1512)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 3416)
- cmd.exe (PID: 2648)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE Yoda's Crypter (63.7) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.7) |
| .exe | | | Win32 Executable (generic) (10.8) |
| .exe | | | Generic Win/DOS Executable (4.8) |
| .exe | | | DOS Executable Generic (4.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:21 05:41:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5.12 |
| CodeSize: | - |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 21-Mar-2019 04:41:23 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 21-Mar-2019 04:41:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.UPX1 | 0x00034000 | 0x0001834A | 0x00014E77 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.98962 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
kernel32.dll |
Total processes
127
Monitored processes
93
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | C:\Windows\system32\net1 user k8h3d /del | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1512 | C:\Windows\system32\cmd.exe /c taskkill /f /im powershell.exe | C:\Windows\system32\cmd.exe | — | Clean201903211242_xp_compress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1520 | wmic process where "name='svchost.exe' and ExecutablePath='C:\\Windows\\temp\\svchost.exe'" call Terminate | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1672 | C:\Windows\system32\cmd.exe /c schtasks /delete /tn "WebServers" /f | C:\Windows\system32\cmd.exe | — | Clean201903211242_xp_compress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | wmic datafile where "drive = 'c:' and Path = '\\windows\\SysWOW64\\drivers\\' and FileName = 'svchost' and Extension = 'exe'" call delete | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2196 | C:\Windows\system32\cmd.exe /c wmic datafile where "drive = 'c:' and Path = '\\windows\\SysWOW64\\' and FileName = 'wmiex' and Extension = 'exe'" call delete | C:\Windows\system32\cmd.exe | — | Clean201903211242_xp_compress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2200 | schtasks /End /tn "Autocheck" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | C:\Windows\system32\cmd.exe /c net user k8h3d /del | C:\Windows\system32\cmd.exe | — | Clean201903211242_xp_compress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2212 | taskkill /f /im powershell.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2220 | C:\Windows\system32\cmd.exe /c sc stop Ddriver | C:\Windows\system32\cmd.exe | — | Clean201903211242_xp_compress.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
628
Read events
528
Write events
100
Delete events
0
Modification events
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (3532) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report