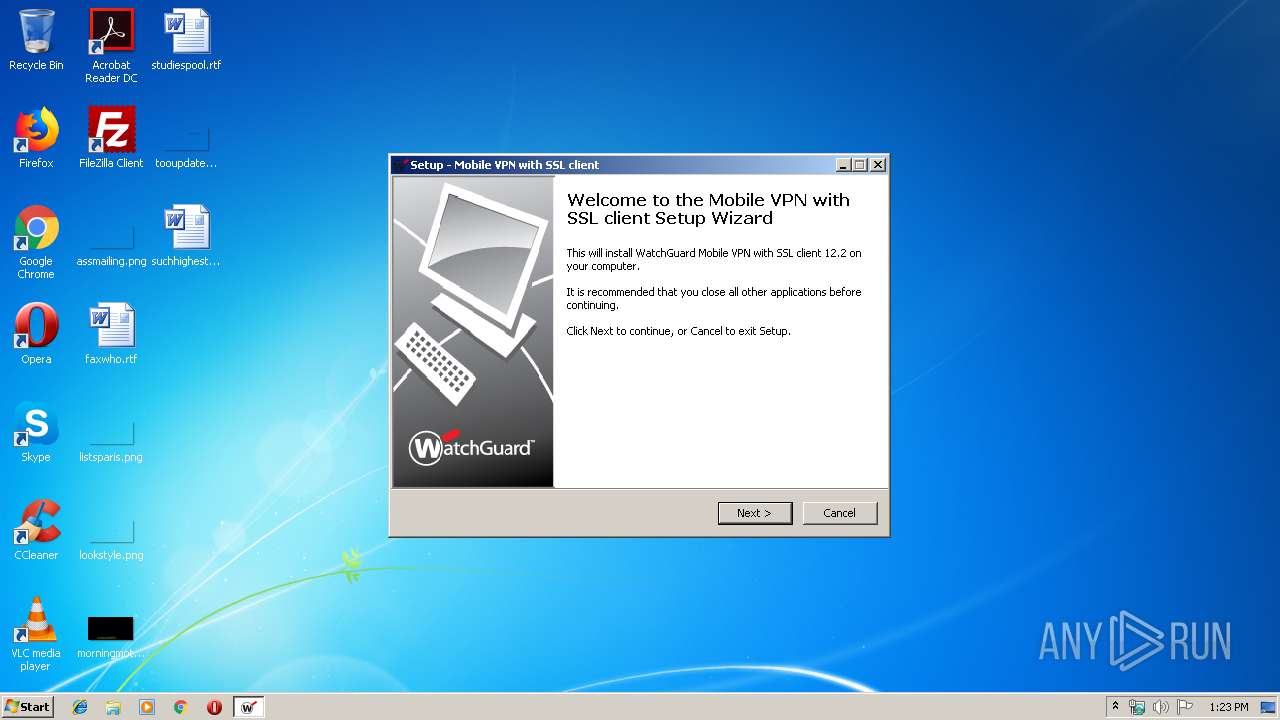
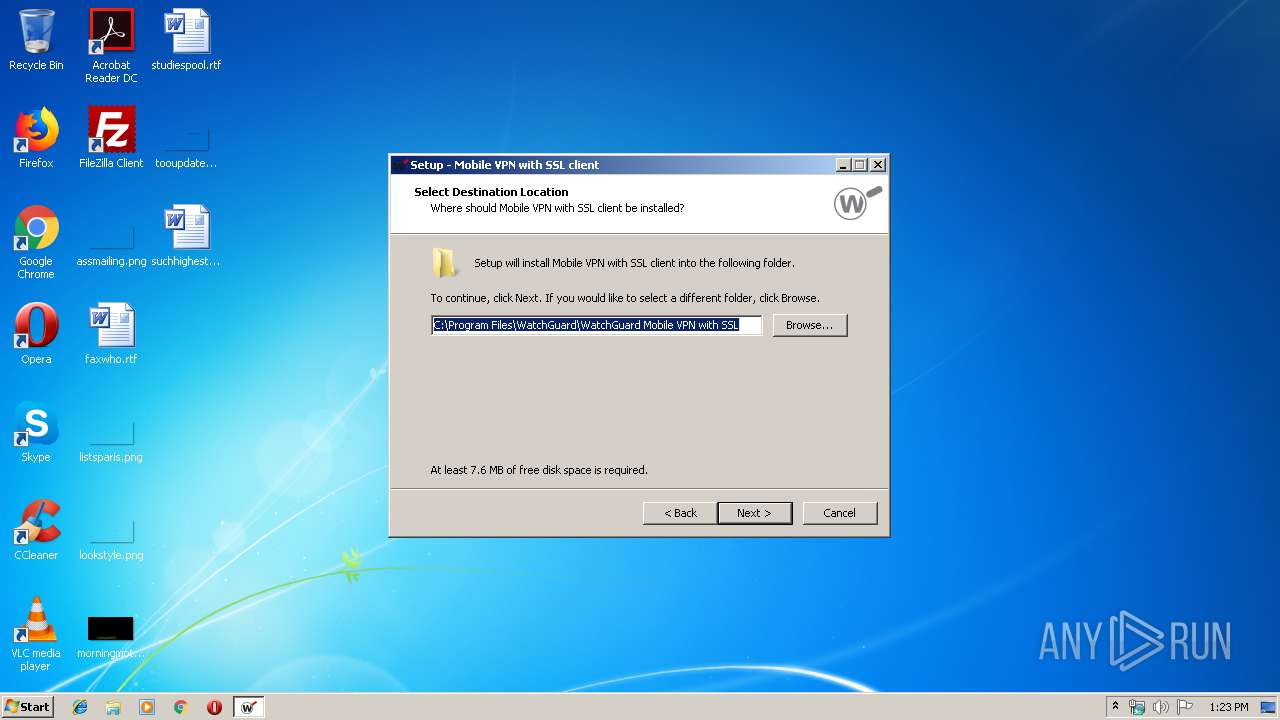
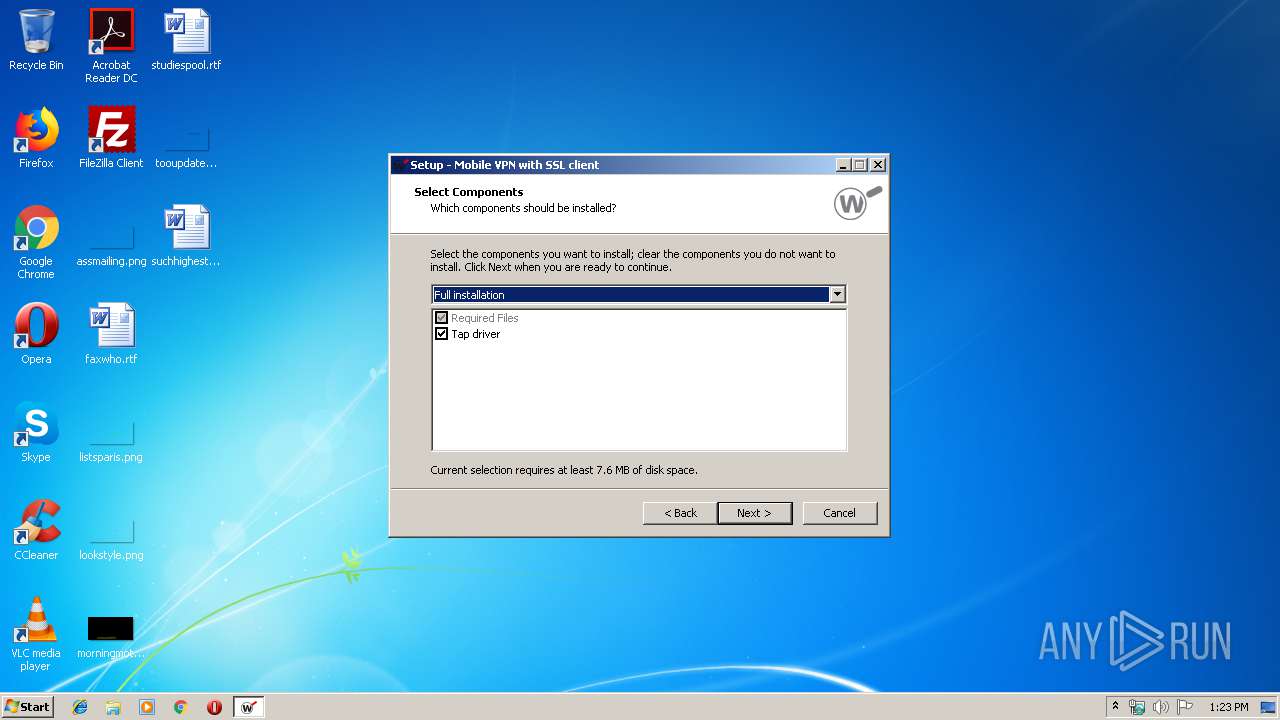
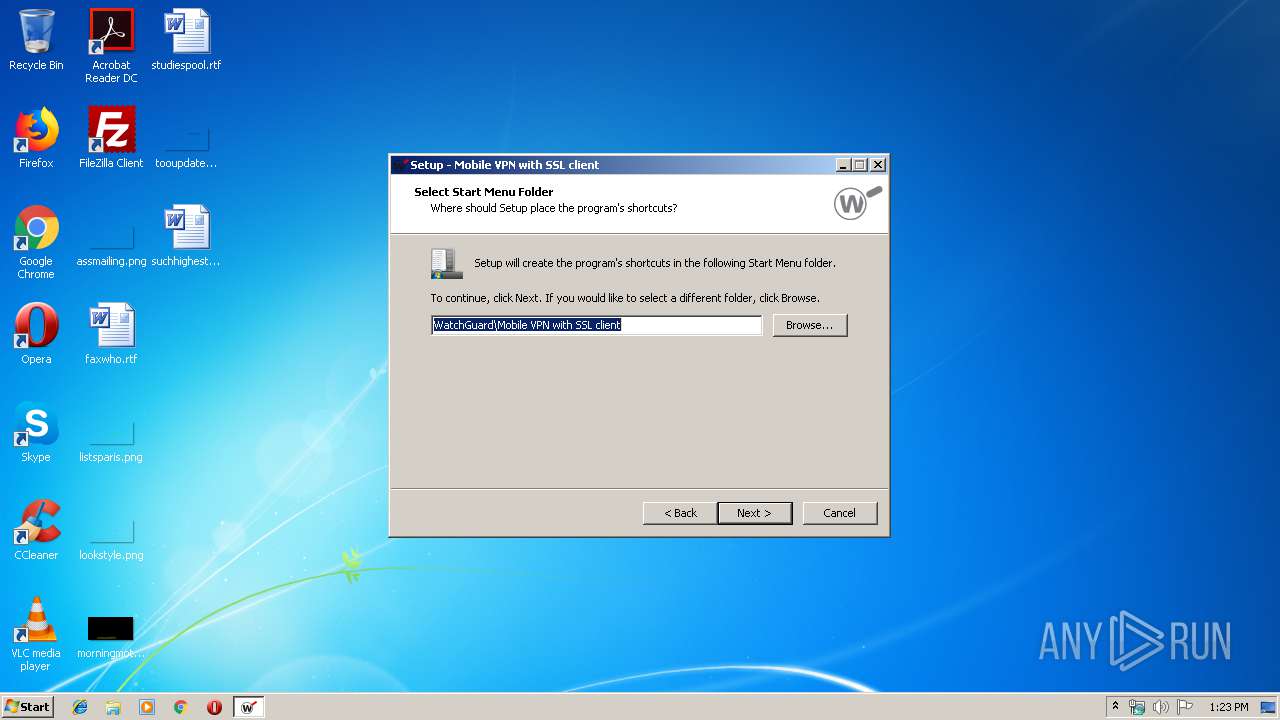
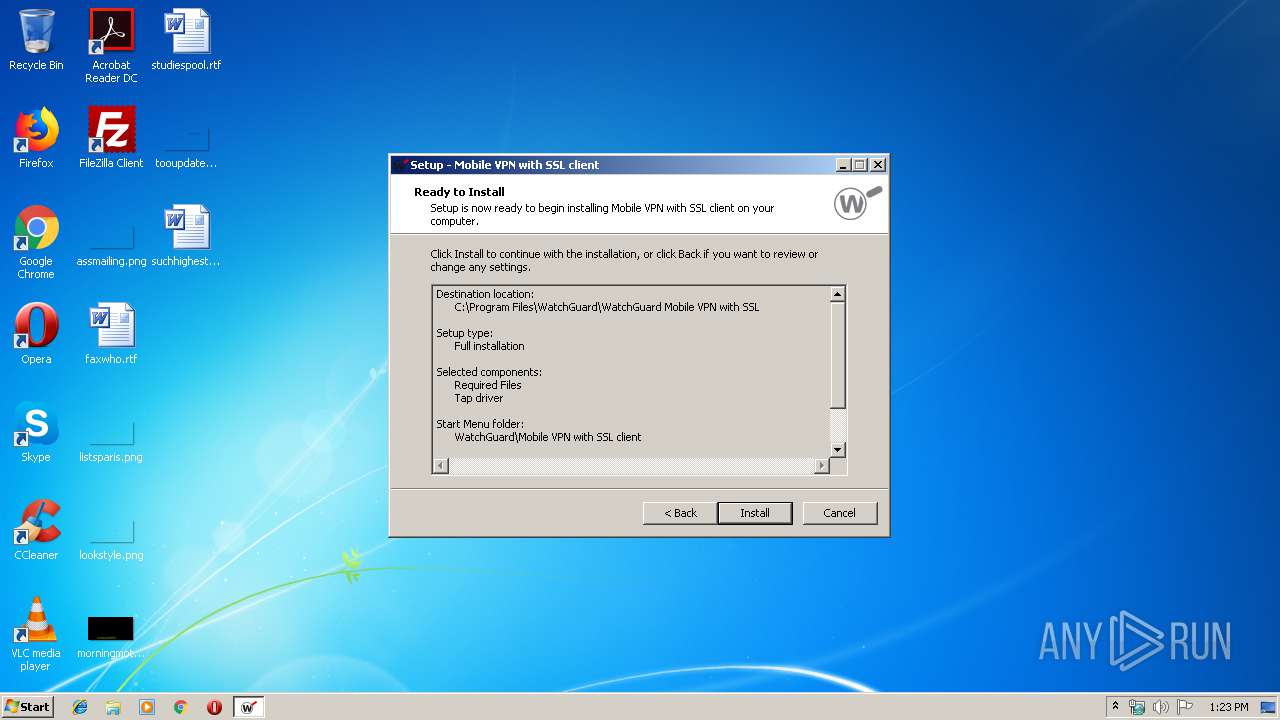
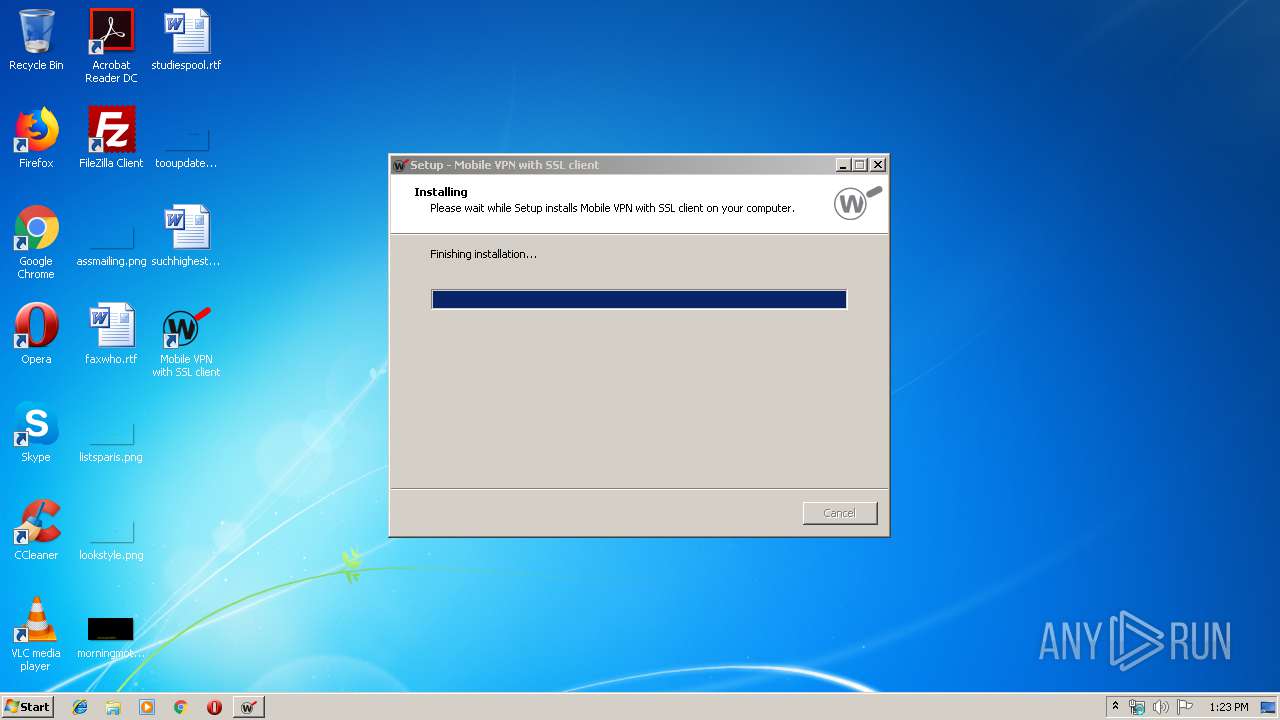
| File name: | WG-MVPN-SSL.exe |
| Full analysis: | https://app.any.run/tasks/040c4c64-1842-474e-a678-1b5e1500f80c |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2020, 13:22:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FEABD20262050F8C039287471BF7A601 |
| SHA1: | BD3EF2D563318978A2BA6A2E02B4469C25E851D9 |
| SHA256: | BAAA8511C844E99B69A7FB781A5C5B2D9FA9B75613674B9913C99BCEBEE7BDE3 |
| SSDEEP: | 49152:8qsKtWwx8n8Eq9GfbgPBwaIfGuSpnLe0iKjCdIoE4PRtBEmFk+bl/:hl4MgRqsf2waEGV1q0potNZ5 |
MALICIOUS
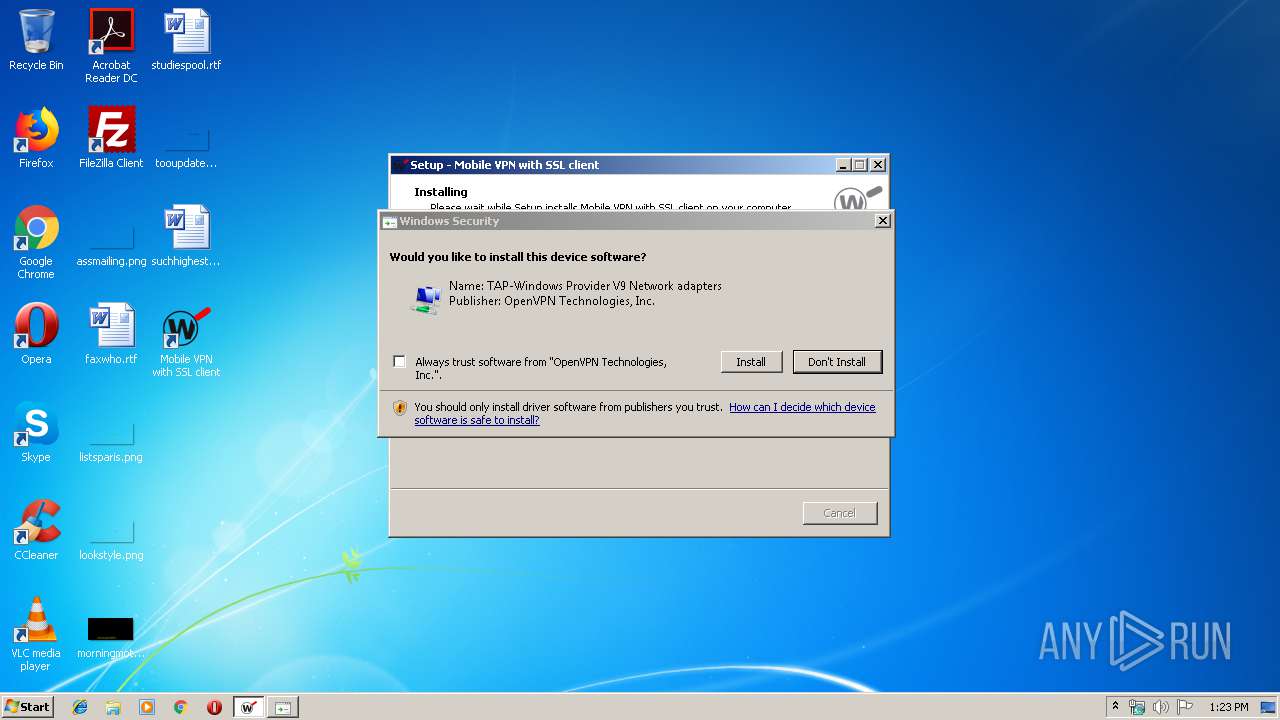
Changes settings of System certificates
- certutil.exe (PID: 2488)
- certutil.exe (PID: 1484)
- devcon.exe (PID: 1792)
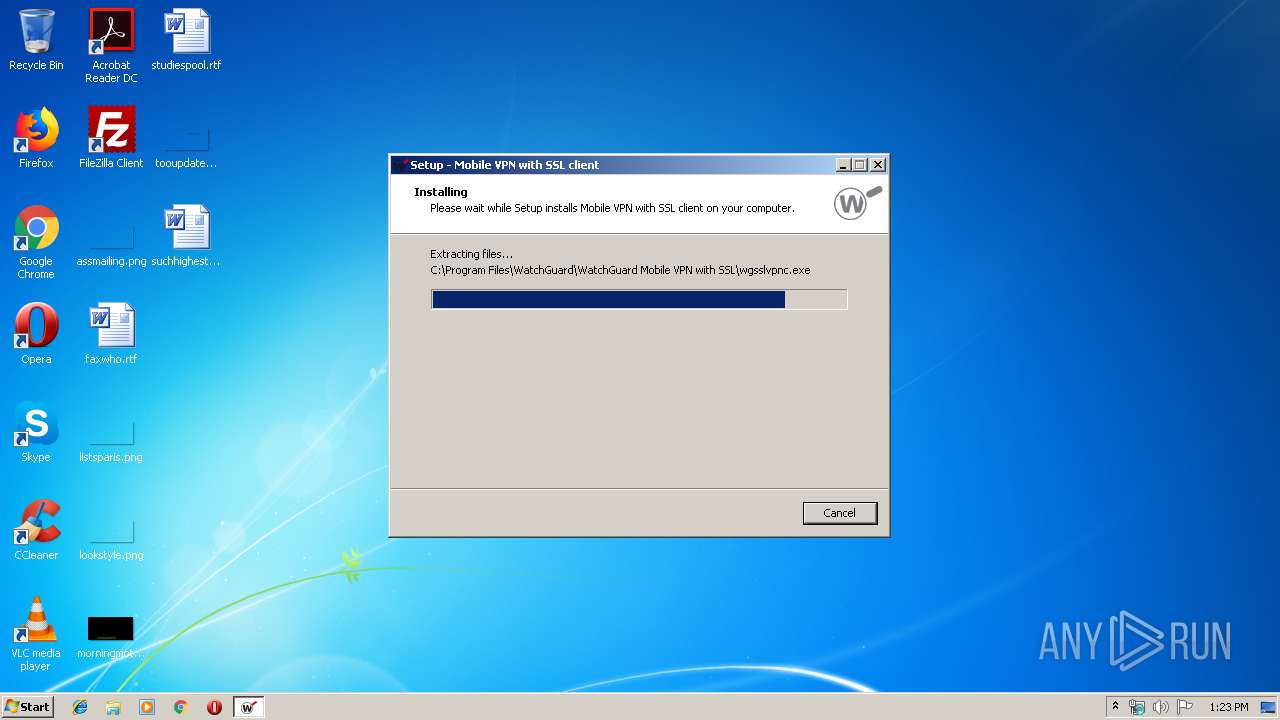
Application was dropped or rewritten from another process
- wgsslvpnc.exe (PID: 2888)
- devcon.exe (PID: 1268)
- devcon.exe (PID: 2684)
- wgsslvpnsrc.exe (PID: 4088)
- wgsslvpnsrc.exe (PID: 2552)
- devcon.exe (PID: 1792)
- wgsslvpnsrc.exe (PID: 3736)
- wgsslvpnc.exe (PID: 1908)
Loads dropped or rewritten executable
- wgsslvpnc.exe (PID: 2888)
- wgsslvpnc.exe (PID: 1908)
SUSPICIOUS
Executable content was dropped or overwritten
- WG-MVPN-SSL.exe (PID: 1796)
- WG-MVPN-SSL.exe (PID: 2468)
- WG-MVPN-SSL.tmp (PID: 3356)
- devcon.exe (PID: 1792)
- DrvInst.exe (PID: 788)
Modifies the open verb of a shell class
- WG-MVPN-SSL.tmp (PID: 3356)
Creates files in the Windows directory
- certutil.exe (PID: 2488)
- certutil.exe (PID: 1484)
- DrvInst.exe (PID: 788)
Removes files from Windows directory
- certutil.exe (PID: 2488)
- certutil.exe (PID: 1484)
- DrvInst.exe (PID: 788)
Creates files in the user directory
- wgsslvpnc.exe (PID: 2888)
Creates files in the driver directory
- DrvInst.exe (PID: 788)
Executed via COM
- DrvInst.exe (PID: 460)
- DrvInst.exe (PID: 788)
- rundll32.exe (PID: 292)
Creates files in the program directory
- devcon.exe (PID: 1792)
Executed as Windows Service
- wgsslvpnsrc.exe (PID: 3736)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 788)
INFO
Application was dropped or rewritten from another process
- WG-MVPN-SSL.tmp (PID: 3356)
- WG-MVPN-SSL.tmp (PID: 2768)
Loads dropped or rewritten executable
- WG-MVPN-SSL.tmp (PID: 3356)
Creates files in the program directory
- WG-MVPN-SSL.tmp (PID: 3356)
Creates a software uninstall entry
- WG-MVPN-SSL.tmp (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 40960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.2.0.0 |
| ProductVersionNumber: | 12.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
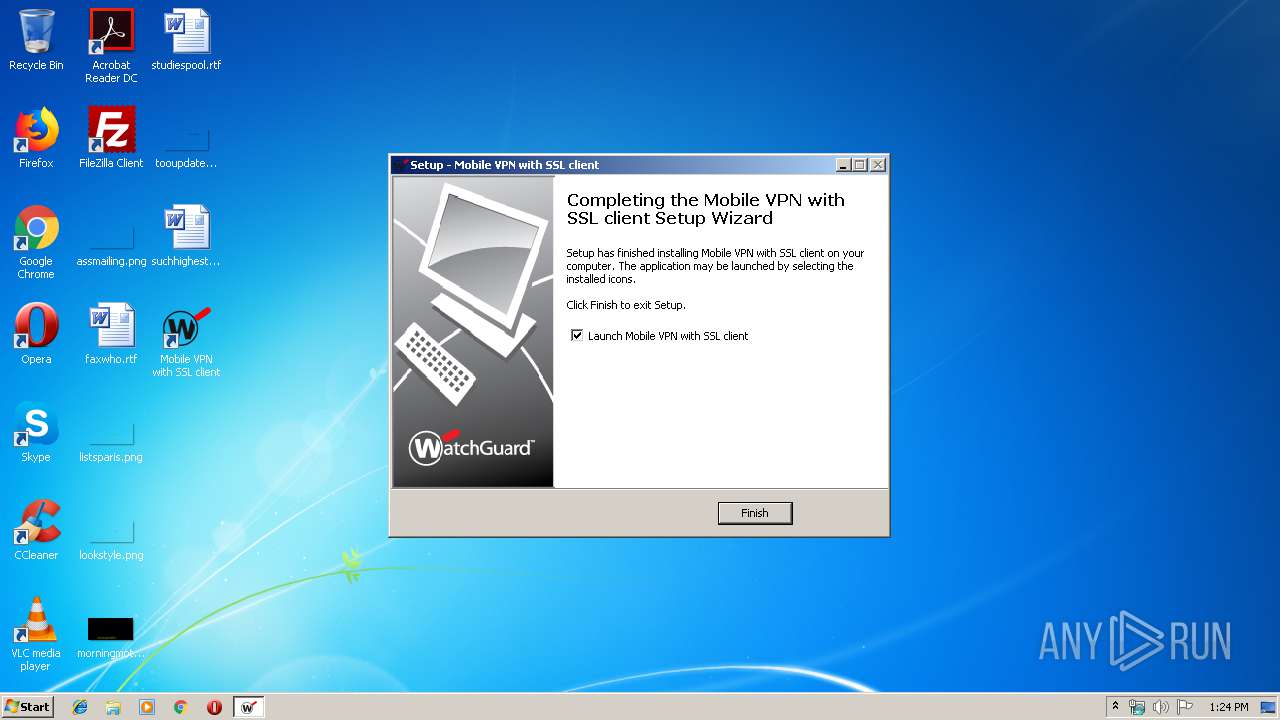
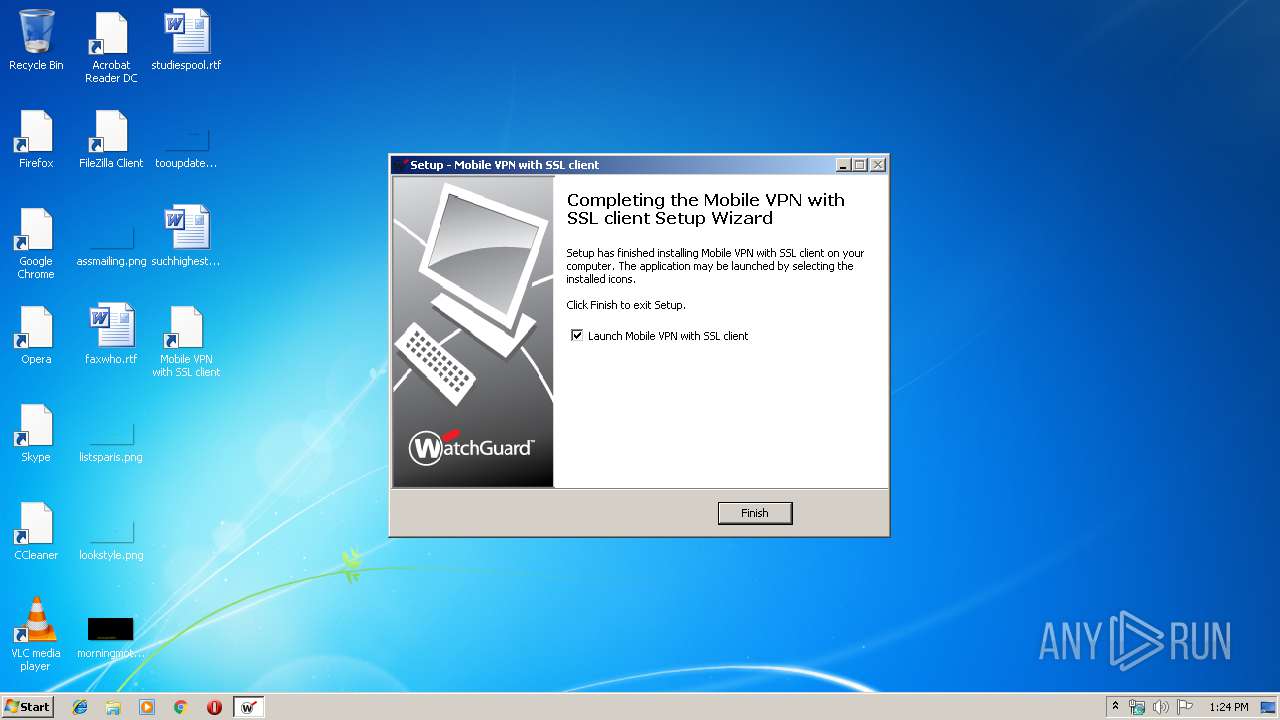
| CompanyName: | WatchGuard |
| FileDescription: | Mobile VPN with SSL client Setup |
| FileVersion: | 12.2 |
| LegalCopyright: | (c)2004-2018 WatchGuard Technologies, Inc. |
| ProductName: | Mobile VPN with SSL client |
| ProductVersion: | 12.2 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | WatchGuard |
| FileDescription: | Mobile VPN with SSL client Setup |
| FileVersion: | 12.2 |
| LegalCopyright: | (c)2004-2018 WatchGuard Technologies, Inc. |
| ProductName: | Mobile VPN with SSL client |
| ProductVersion: | 12.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009364 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.56314 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73731 |
BSS | 0x0000C000 | 0x00000E88 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B4 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x00008EC8 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.28748 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.08452 | 1444 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.84602 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.67682 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 2.12219 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.74692 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.73153 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.18351 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 1.49971 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 2.07748 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 3.01479 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
62
Monitored processes
18
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | rundll32.exe C:\Windows\system32\newdev.dll,pDiDeviceInstallNotification \\.\pipe\PNP_Device_Install_Pipe_1.{b916f2fa-ee72-4aa5-9fae-a0151e2dd7fc} "(null)" | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 460 | DrvInst.exe "3" "201" "ROOT\NET\0000" "" "" "6d14a44ff" "000003C4" "000005D0" "000005C8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 3758096921 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{1aed3c2b-e986-6ae4-3599-561c143eb15c}\oemvista.inf" "0" "6d14a44ff" "000003C4" "WinSta0\Default" "000004D0" "208" "c:\program files\watchguard\watchguard mobile vpn with ssl" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 3758096963 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1268 | "C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\devcon.exe" hwids tap0901" | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\devcon.exe | — | wgsslvpnc.exe | |||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1484 | "C:\Windows\system32\certutil.exe" -addstore "-f" "root" "C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\wgcert.cer" | C:\Windows\system32\certutil.exe | — | WG-MVPN-SSL.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\devcon.exe" install "C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\OemVista.inf" tap0901" | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\devcon.exe | wgsslvpnc.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 2 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 1796 | "C:\Users\admin\AppData\Local\Temp\WG-MVPN-SSL.exe" | C:\Users\admin\AppData\Local\Temp\WG-MVPN-SSL.exe | explorer.exe | ||||||||||||
User: admin Company: WatchGuard Integrity Level: MEDIUM Description: Mobile VPN with SSL client Setup Exit code: 0 Version: 12.2 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\wgsslvpnc.exe" | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\wgsslvpnc.exe | — | WG-MVPN-SSL.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: wgsslvpnc Module Exit code: 0 Version: 12, 2, 0, 0 Modules
| |||||||||||||||
| 2364 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{26ffe4f5-9c70-7955-33bb-0819dd537b76} Global\{496cc074-c04f-0c60-b948-2b471dafed5c} C:\Windows\System32\DriverStore\Temp\{5e4764e2-6485-6ae4-9ba5-d11cf2b25b52}\oemvista.inf C:\Windows\System32\DriverStore\Temp\{5e4764e2-6485-6ae4-9ba5-d11cf2b25b52}\tap0901.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2468 | "C:\Users\admin\AppData\Local\Temp\WG-MVPN-SSL.exe" /SPAWNWND=$D011E /NOTIFYWND=$4012C | C:\Users\admin\AppData\Local\Temp\WG-MVPN-SSL.exe | WG-MVPN-SSL.tmp | ||||||||||||
User: admin Company: WatchGuard Integrity Level: HIGH Description: Mobile VPN with SSL client Setup Exit code: 0 Version: 12.2 Modules
| |||||||||||||||
Total events
679
Read events
578
Write events
94
Delete events
7
Modification events
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 1C0D0000FA7BBA1F70CCD501 | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 894830127750D6E95DC54E541924F9FD860BA3E6065CD58E758CA443C9ED10C5 | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\devcon.exe | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 78A2225EB711C61020C36A8BCE1D6356F73A1B72CE3E3466686CA2C33A28F048 | |||
| (PID) Process: | (2488) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\TrustedPublisher\Certificates\3D0E9C9CEA6765356A7834CDEF7D4E70EC112C78 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000003D0E9C9CEA6765356A7834CDEF7D4E70EC112C782000000001000000850500003082058130820469A00302010202104D0FD6910C933CF2FEE658026CEB157B300D06092A864886F70D01010505003081B4310B300906035504061302555331173015060355040A130E566572695369676E2C20496E632E311F301D060355040B1316566572695369676E205472757374204E6574776F726B313B3039060355040B13325465726D73206F66207573652061742068747470733A2F2F7777772E766572697369676E2E636F6D2F727061202863293130312E302C06035504031325566572695369676E20436C617373203320436F6465205369676E696E672032303130204341301E170D3134303331313030303030305A170D3137303530393233353935395A3081C4310B3009060355040613025553311330110603550408130A57617368696E67746F6E3110300E0603550407130753656174746C6531263024060355040A141D5761746368477561726420546563686E6F6C6F676965732C20496E632E313E303C060355040B13354469676974616C20494420436C6173732033202D204D6963726F736F667420536F6674776172652056616C69646174696F6E207632312630240603550403141D5761746368477561726420546563686E6F6C6F676965732C20496E632E30820122300D06092A864886F70D01010105000382010F003082010A0282010100DA5CB8384FA8F7386AAB1BFF6385EA39D67CAD275838C3093AB9A194A81953DE646324E61814C7D0857D03EA7F03F6F5E778463C2AA9A815FE380568713F2CBD47E9231CF2C061EA26C155A09C76D2EF5A2A74F8E8A44B859963F467A23633822E7420BC131AC130C8C4528D818CFC0972EB5FD8AD1E2D050E5B96FB9F70A30DE2F8BA89F8A4D949143D05DCF992062721C572C077C59696F462561117F5499FC7180D533DB7BE741F02E5A91D6353B3B8C6204C302B383E548377C8A19CDA9963AC586987BD2CC1A8CF1A879D095B7F60E6FA2D2979C57B2900264F7F419EC740776D1A7278F6E313C52C3A09D1FC19F5BF2A7E6DFDE788B1DB34729CAEDFE50203010001A382017B3082017730090603551D1304023000300E0603551D0F0101FF04040302078030400603551D1F043930373035A033A031862F687474703A2F2F637363332D323031302D63726C2E766572697369676E2E636F6D2F435343332D323031302E63726C30440603551D20043D303B3039060B6086480186F84501071703302A302806082B06010505070201161C68747470733A2F2F7777772E766572697369676E2E636F6D2F72706130130603551D25040C300A06082B06010505070303307106082B0601050507010104653063302406082B060105050730018618687474703A2F2F6F6373702E766572697369676E2E636F6D303B06082B06010505073002862F687474703A2F2F637363332D323031302D6169612E766572697369676E2E636F6D2F435343332D323031302E636572301F0603551D23041830168014CF99A9EA7B26F44BC98E8FD7F00526EFE3D2A79D301106096086480186F84201010404030204103016060A2B06010401823702011B040830060101000101FF300D06092A864886F70D01010505000382010100B480FADDBDE9C6919268D5AD236823B27D2902E802B5DB2D968D0E858BB4CA455514739B449CA1E1284D97A6F2D4A94AC604FD058C6826A95C717D3097373EEB1B731E230C475832816DD1030E8D1A8BD54A069E398A0B15BCBFC5DBF28F0FB23ACDAA2DB277CE7F3CFF437CD9197220BC14F64873993221788B640E69EF9F173ED2F8ABBFC60ED97A41117B2387523B074AFF2F90AF819F5C3BA6A2FD370D1E3FCC44CFF72882704655322003CF528A8394EBC37E6F651D93792B33C9A22FD6F9BD5370EA9200477576FFF4D1519BF0DC606DAF80BB3C5C06036C1EECE8AC7CD9D148C7158ED66ABDD0F1CD76F4AFAC82E24C6806141AC2171E8240ED3D366D | |||
| (PID) Process: | (2488) certutil.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.wgssl |
| Operation: | write | Name: | |
Value: WatchGuardMobileVPNwithSSL | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WatchGuardMobileVPNwithSSL |
| Operation: | write | Name: | |
Value: WatchGuard Mobile VPN with SSL | |||
| (PID) Process: | (3356) WG-MVPN-SSL.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WatchGuardMobileVPNwithSSL\DefaultIcon |
| Operation: | write | Name: | |
Value: C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\wgsslvpnc.exe,0 | |||
Executable files
22
Suspicious files
7
Text files
156
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-08CGF.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-1KK9A.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-7JM9P.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-44G19.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-51711.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-9EHJ3.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-U14DJ.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-VM0JF.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-0VBN3.tmp | — | |
MD5:— | SHA256:— | |||
| 3356 | WG-MVPN-SSL.tmp | C:\Program Files\WatchGuard\WatchGuard Mobile VPN with SSL\is-D128E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report