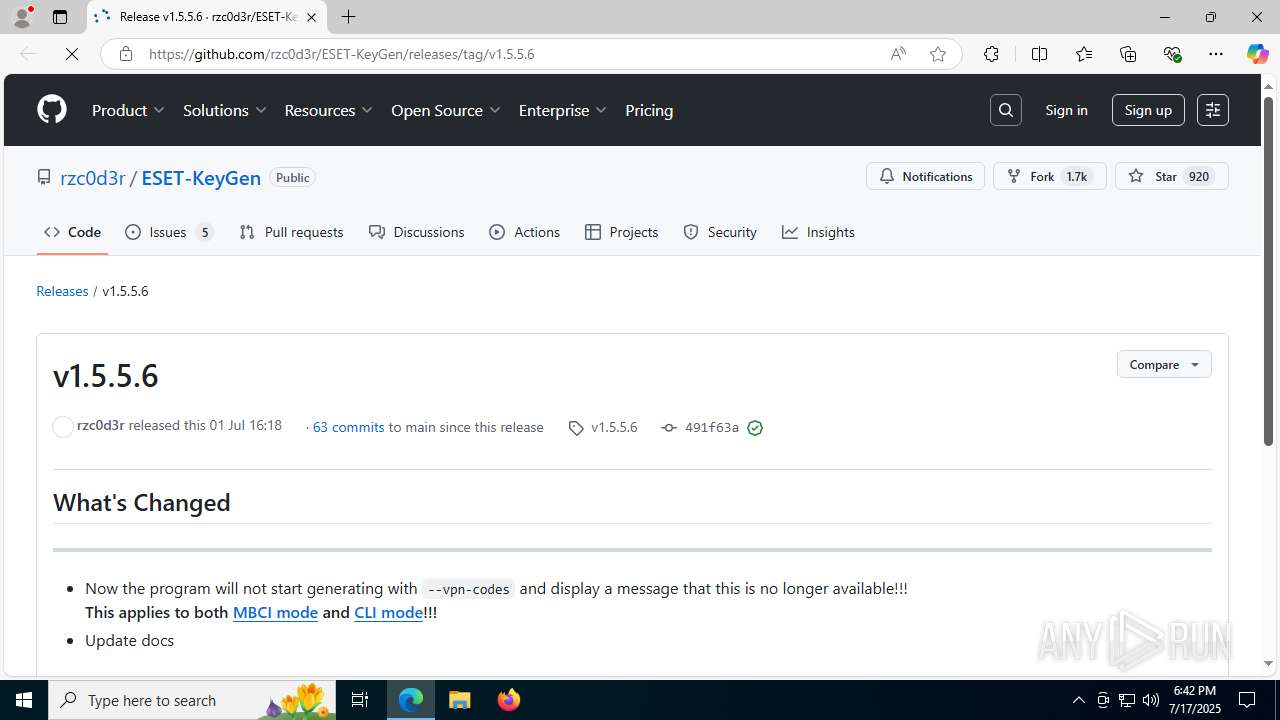
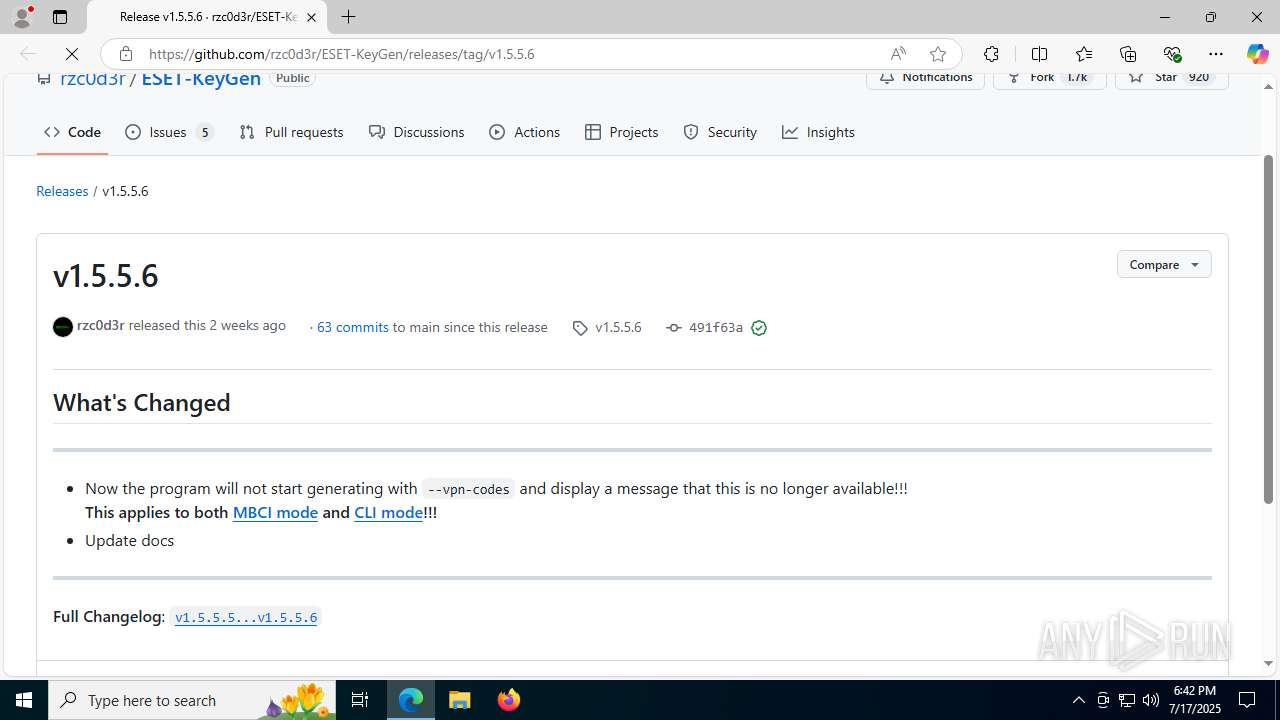
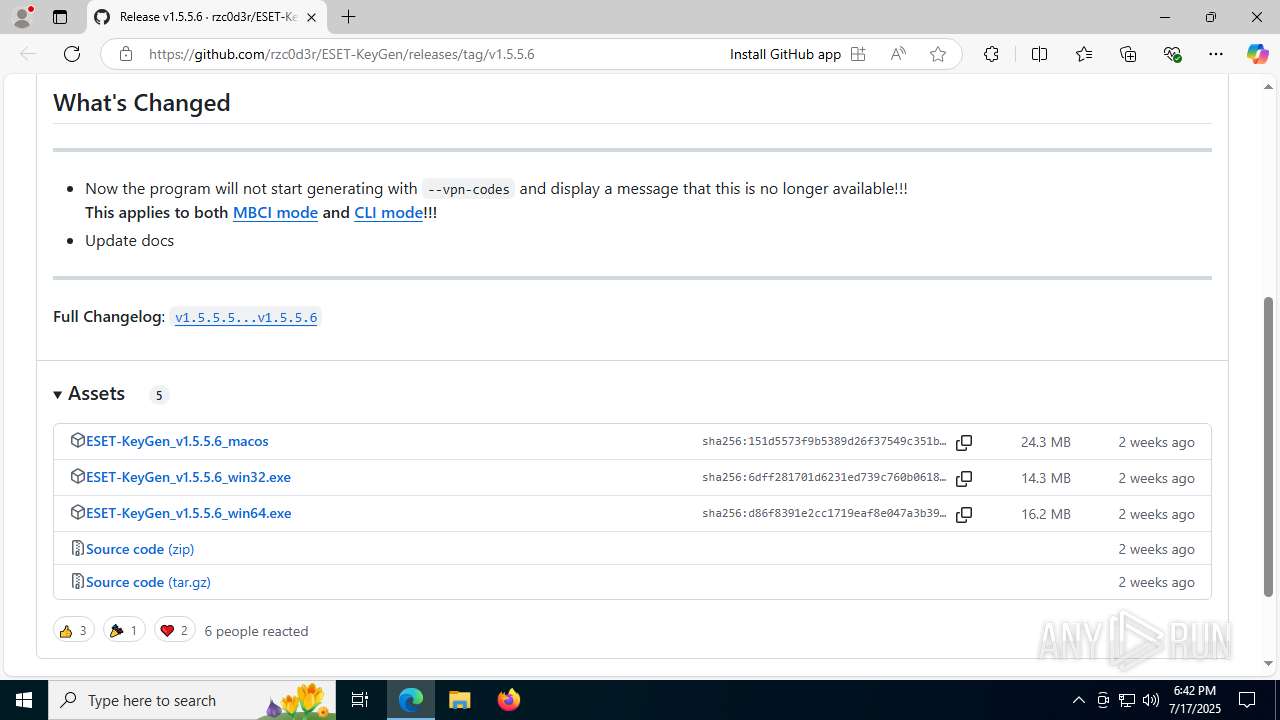
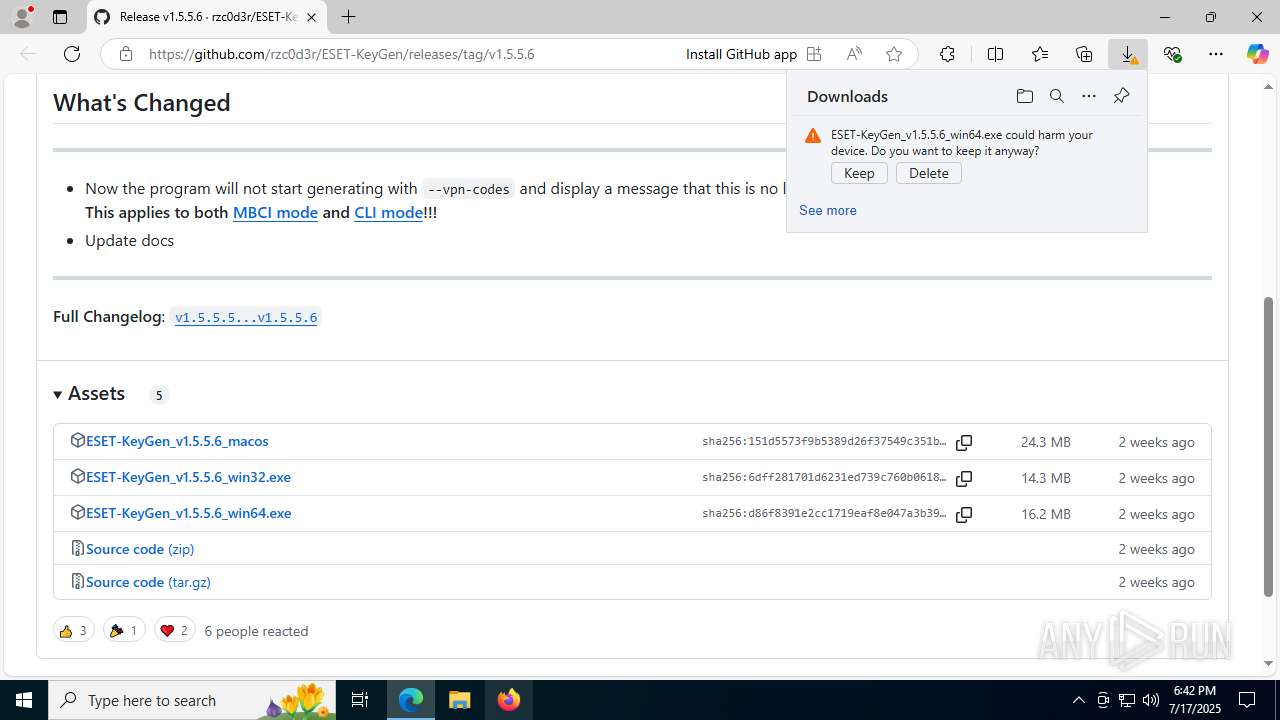
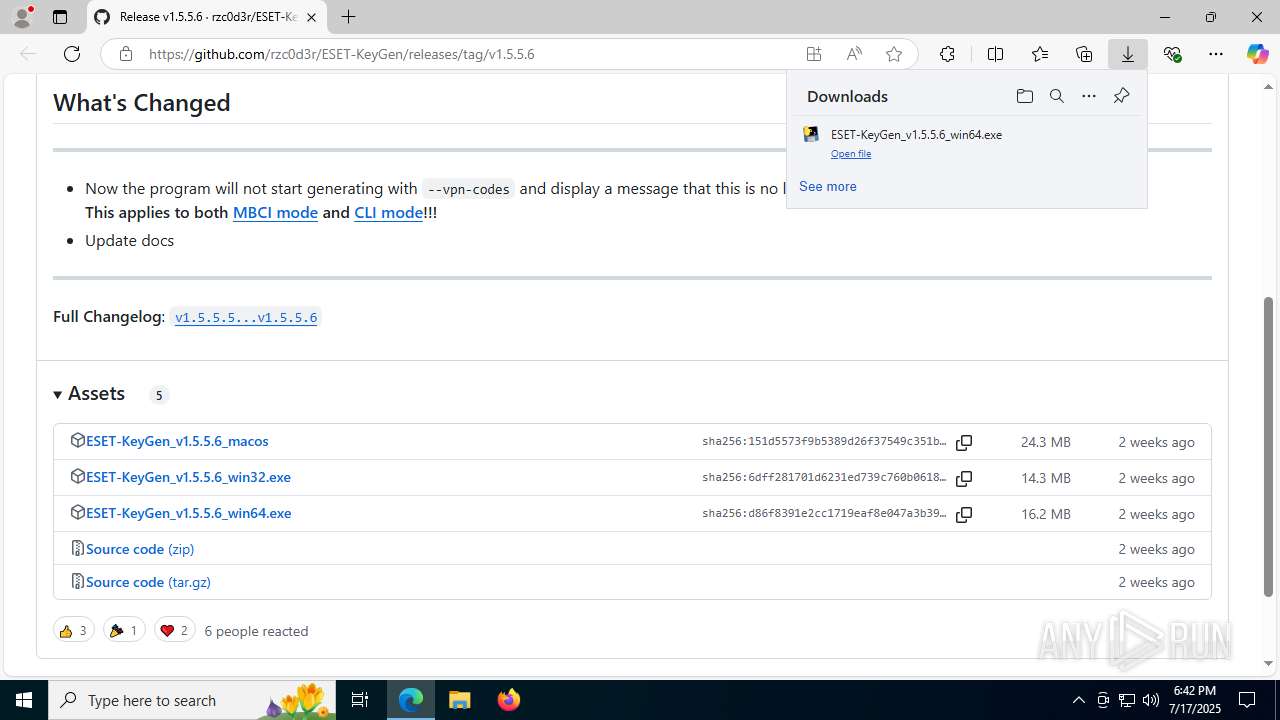
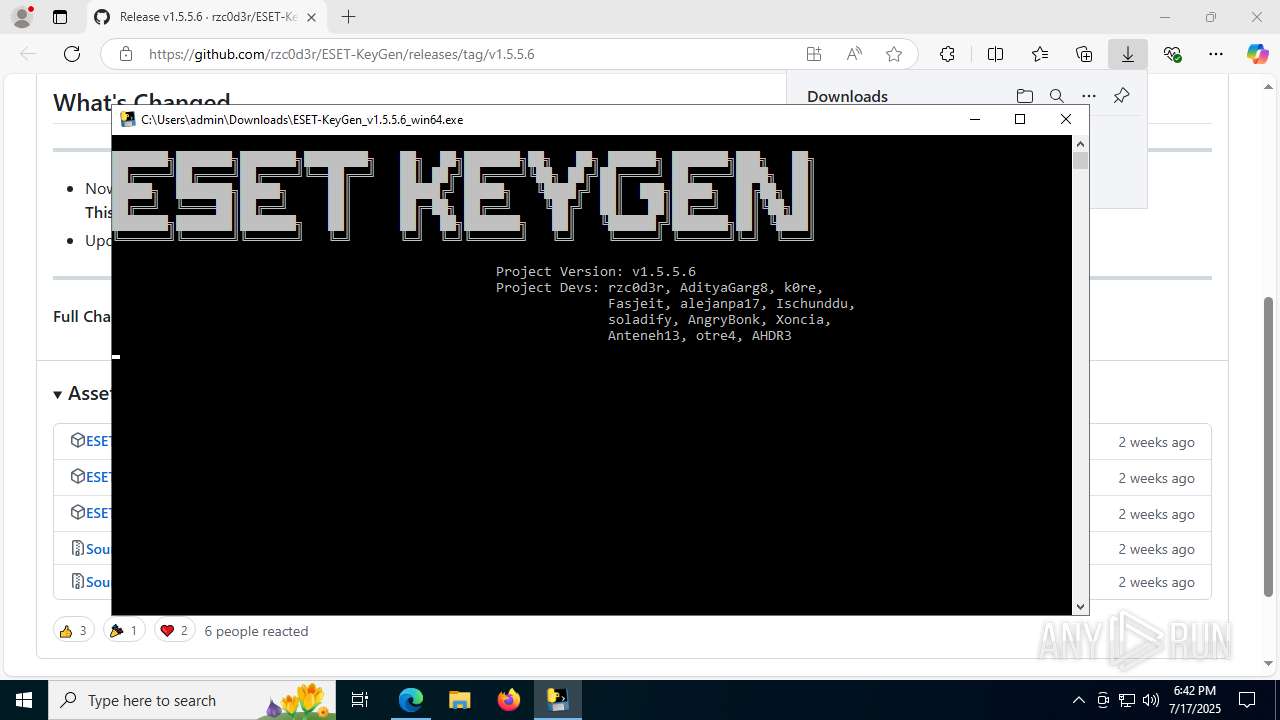
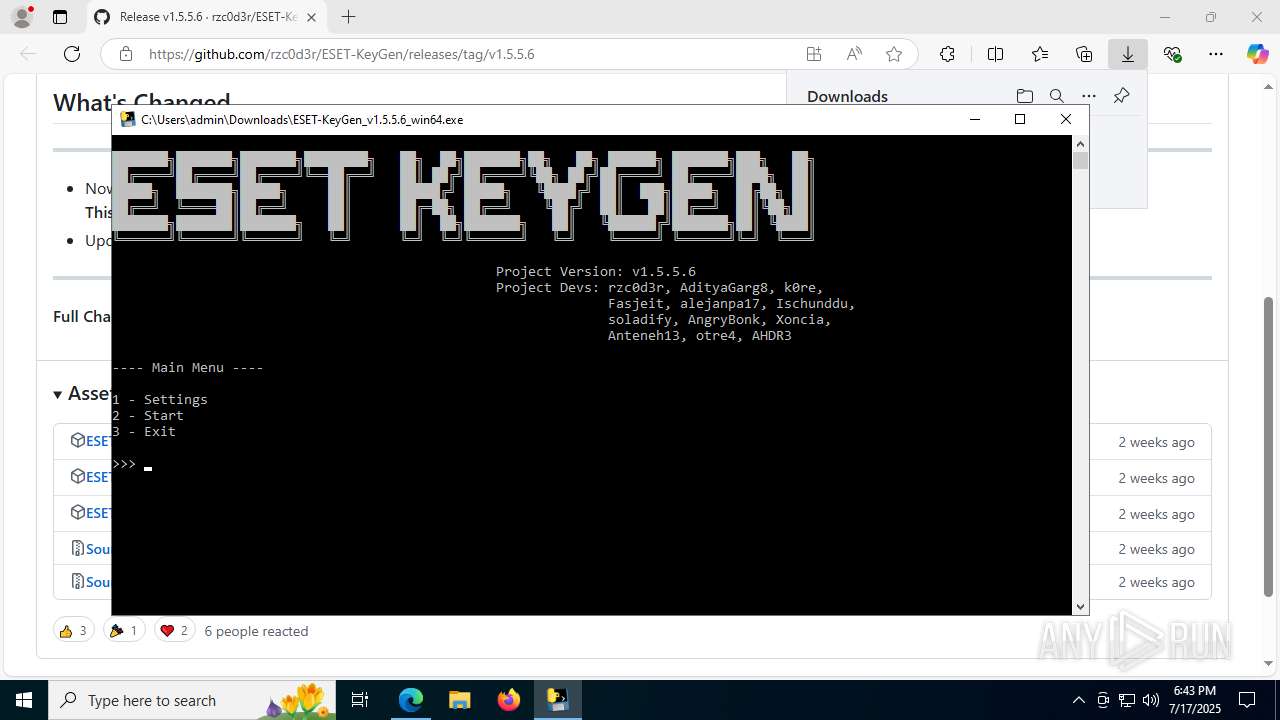
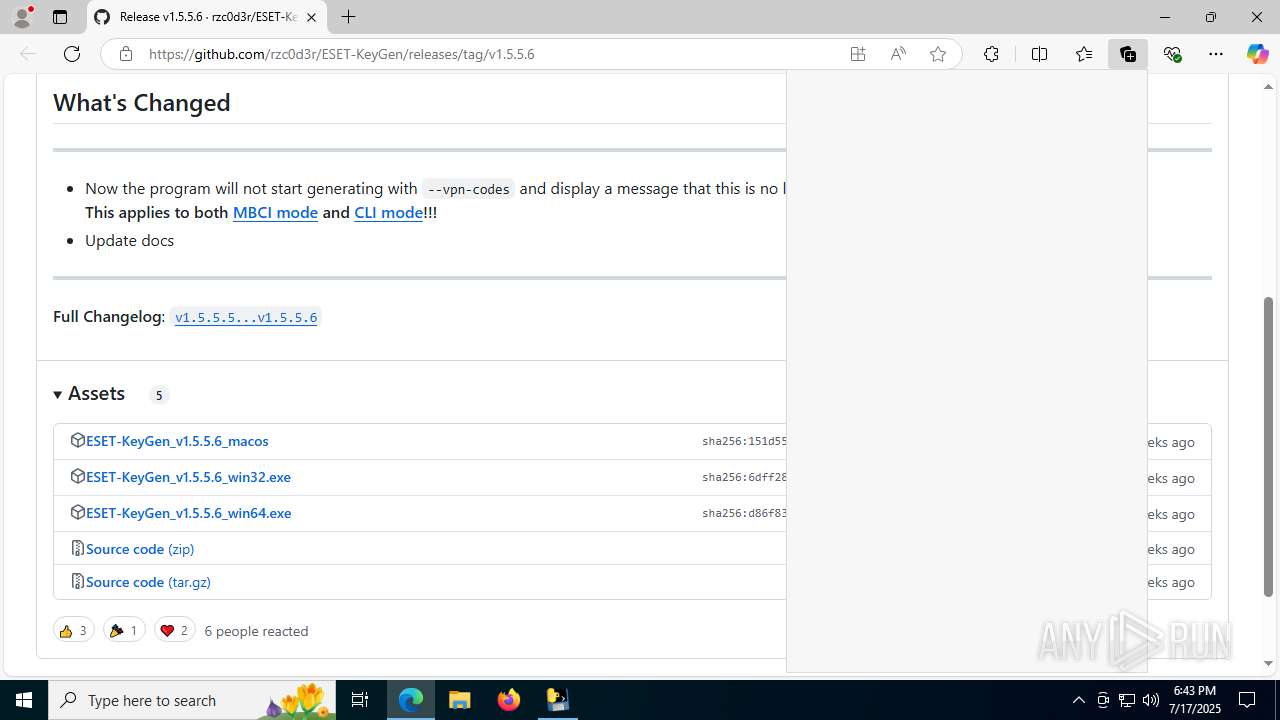
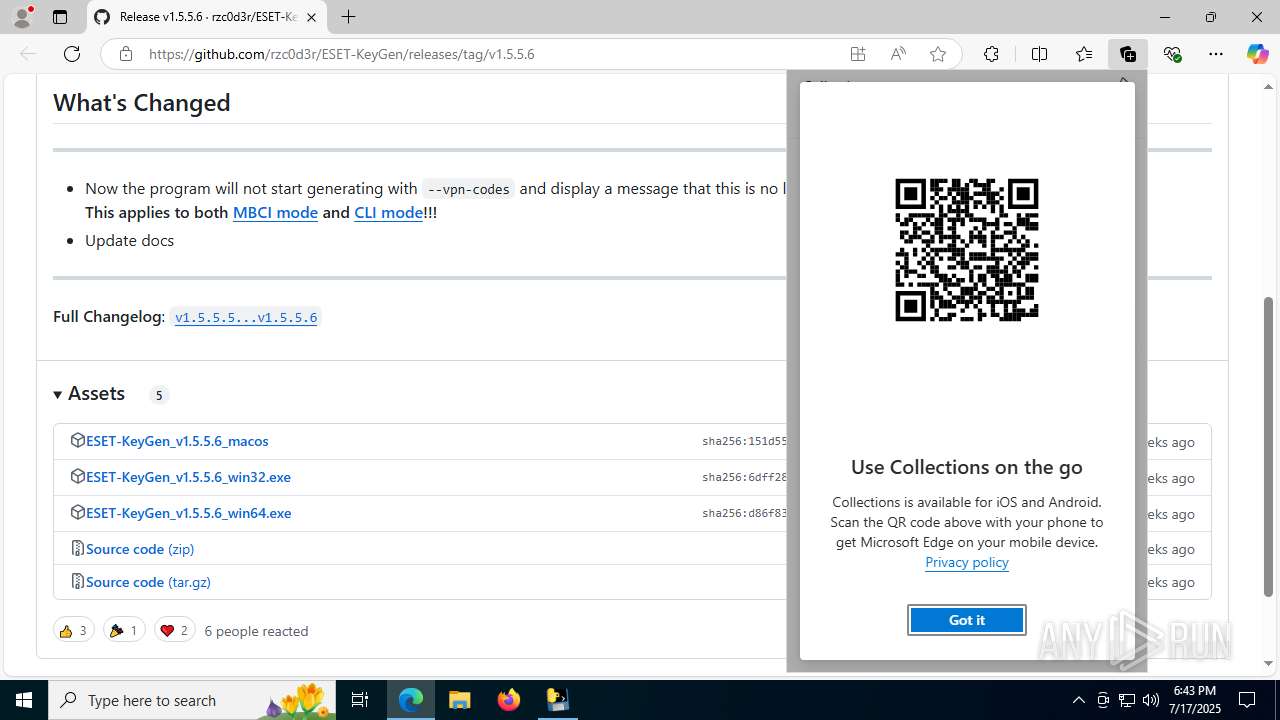
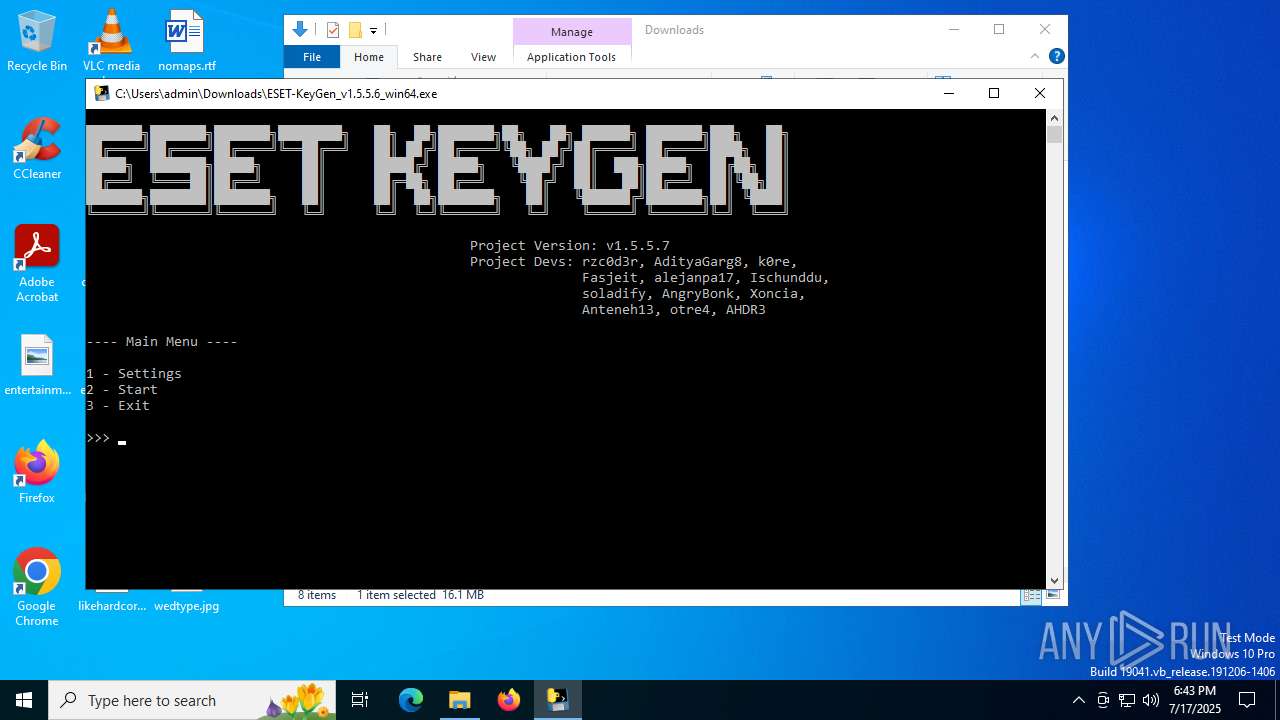
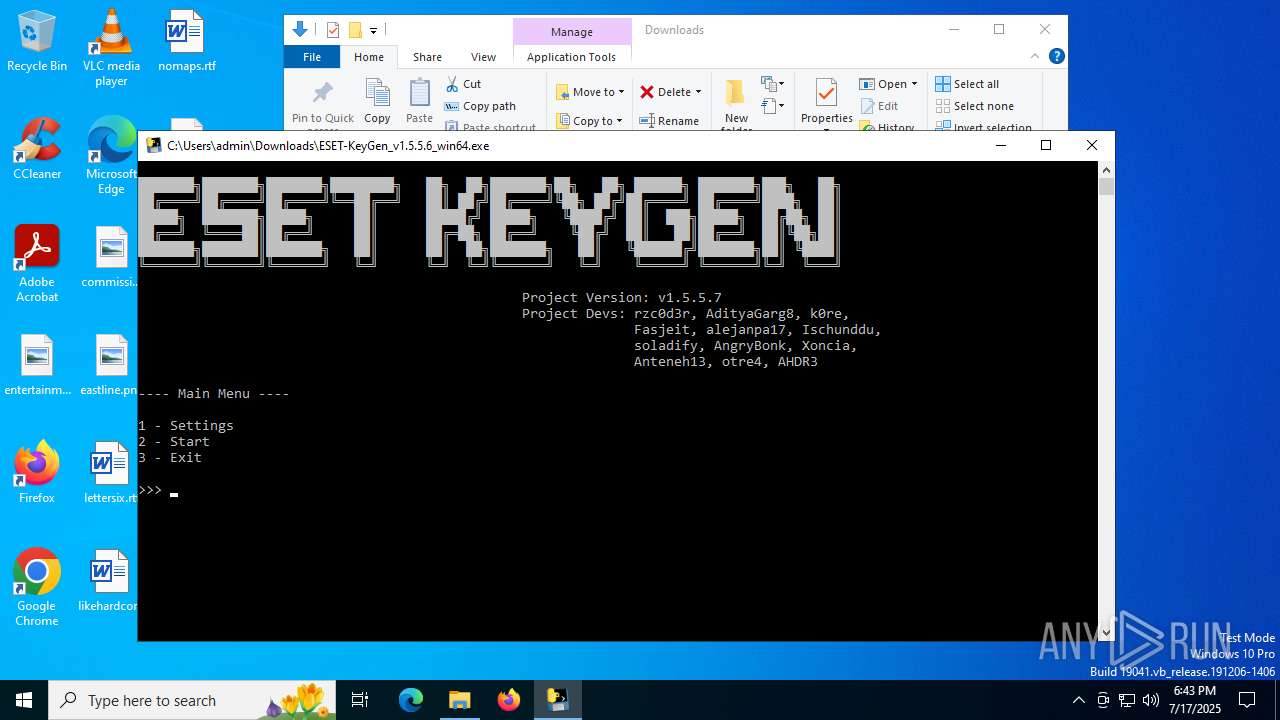
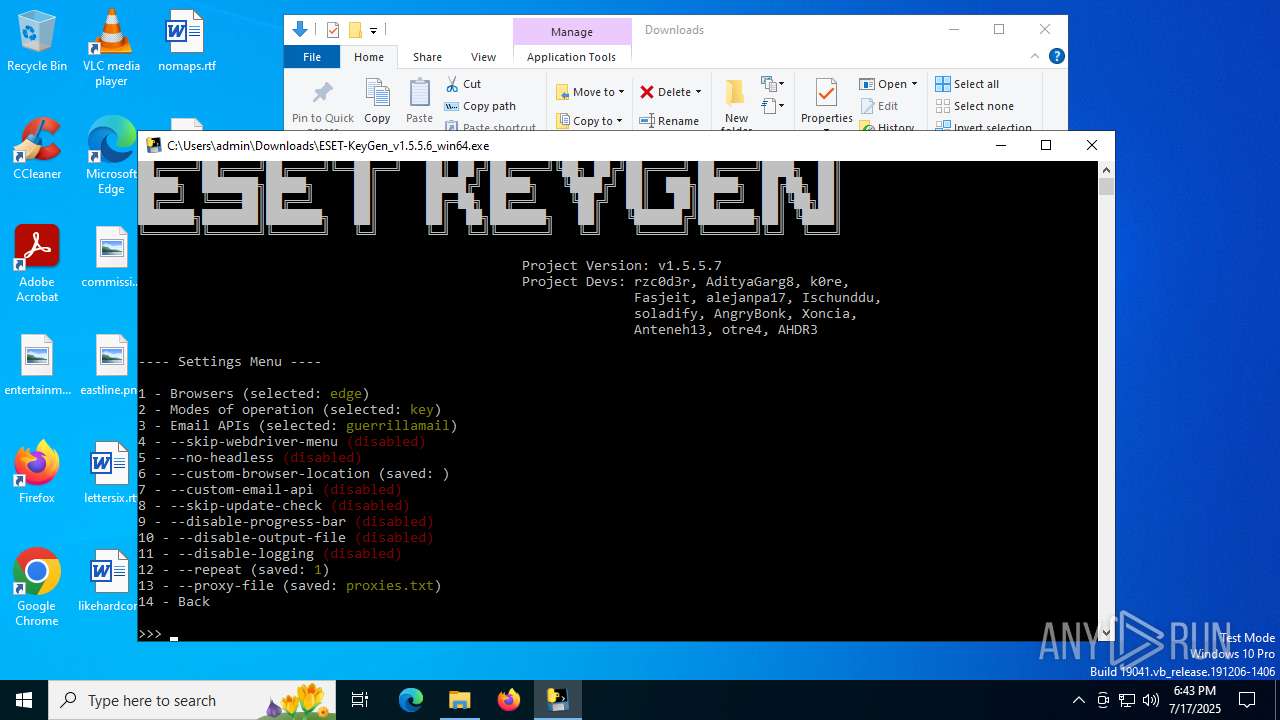
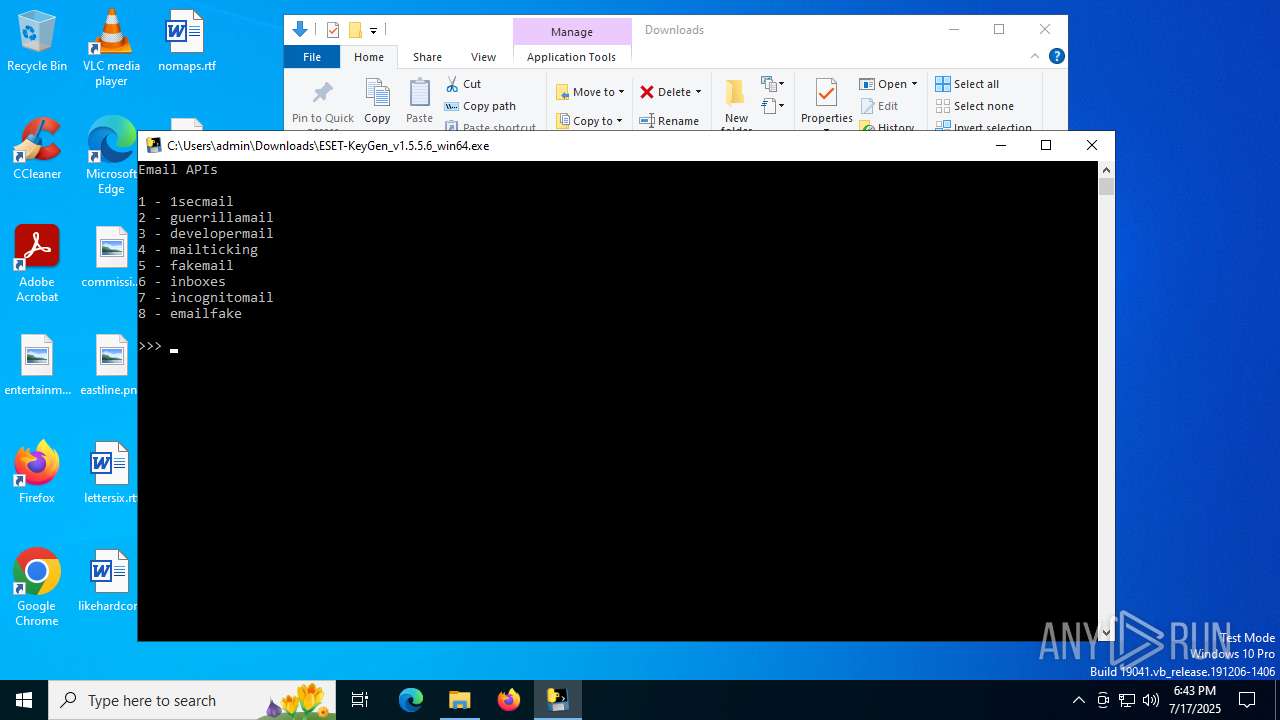
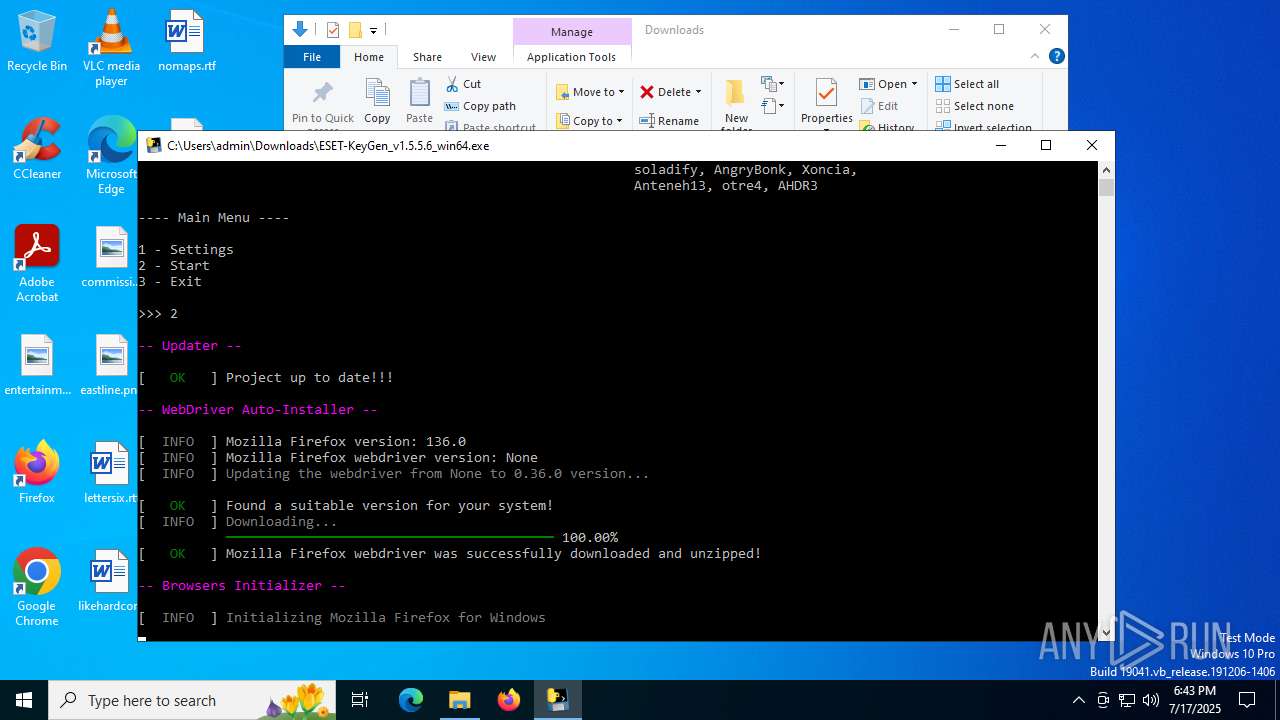
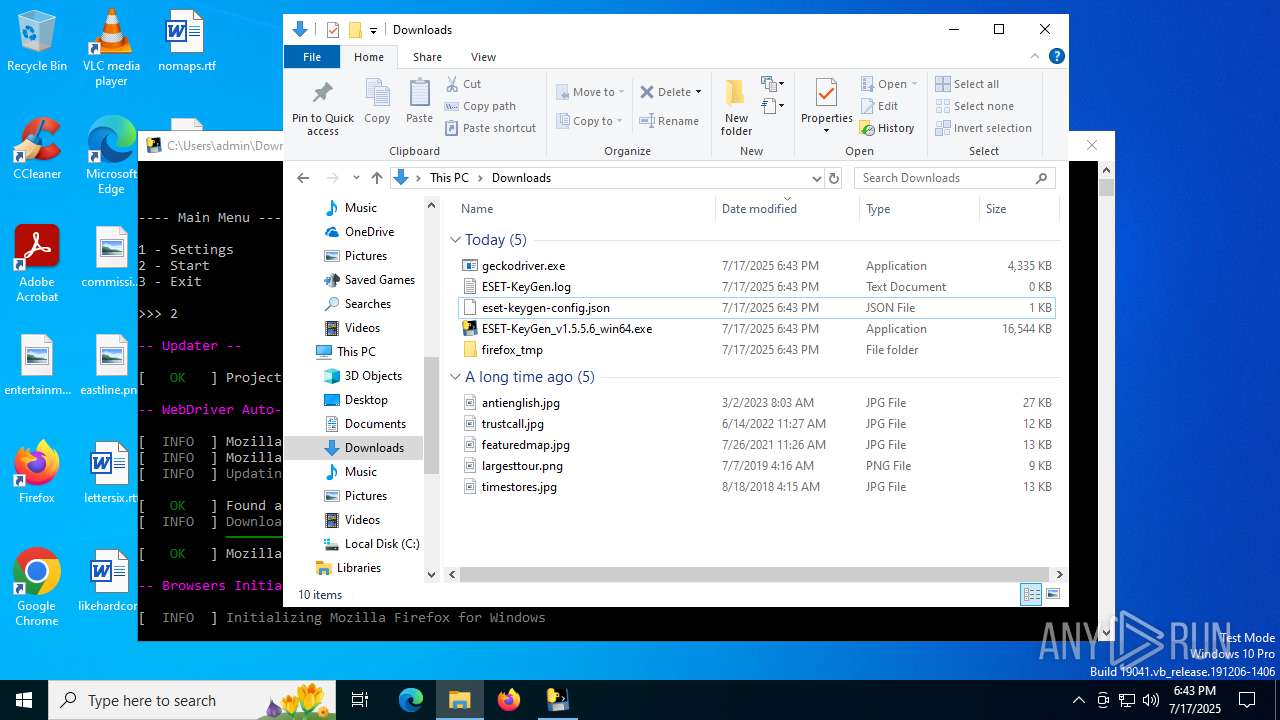
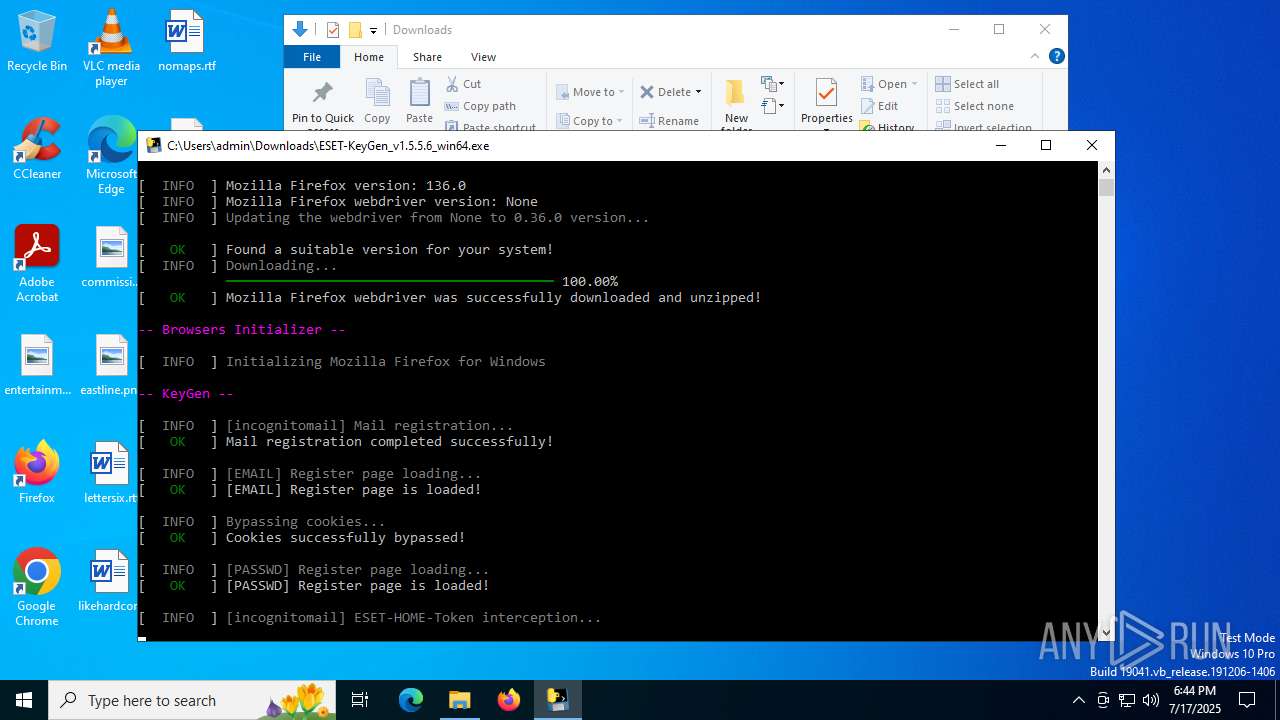
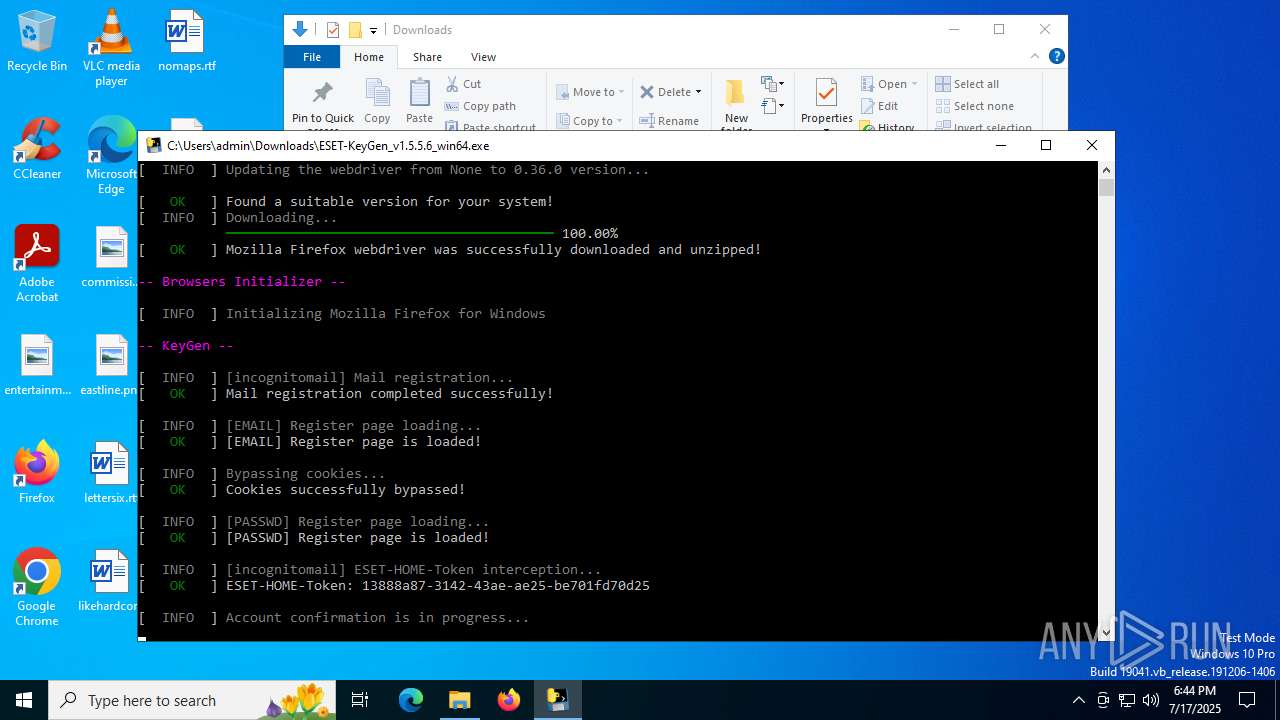
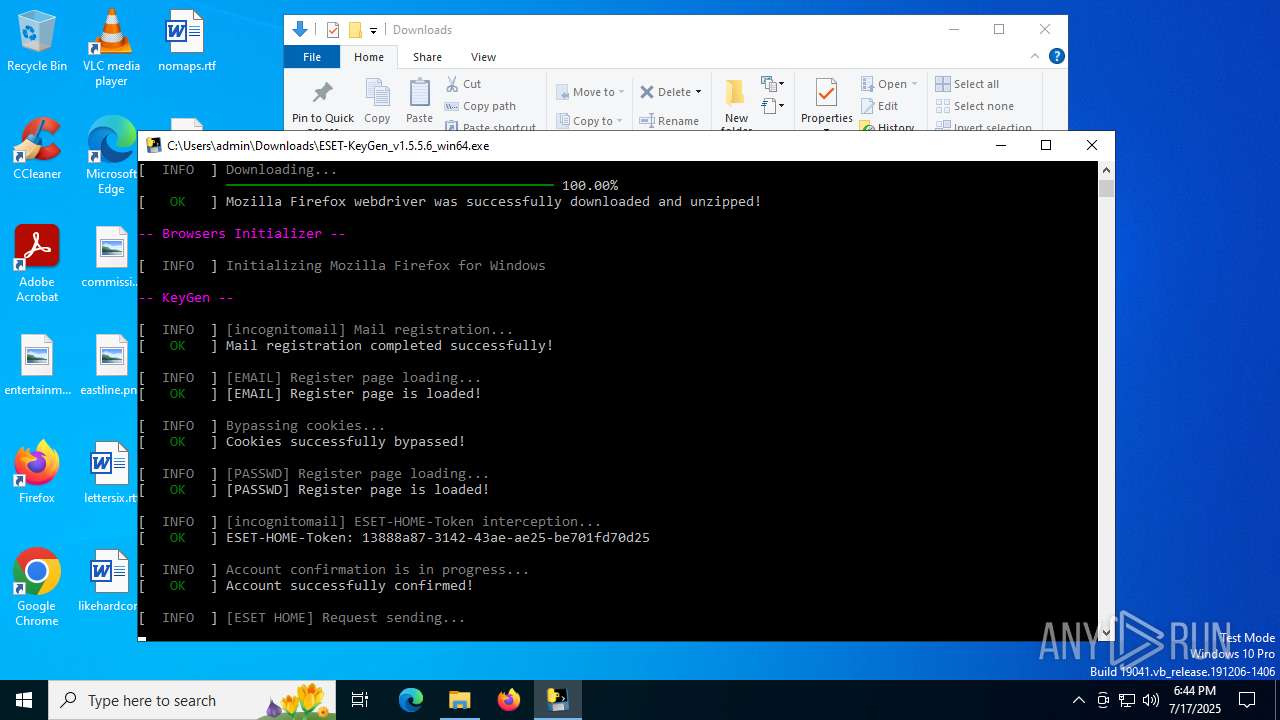
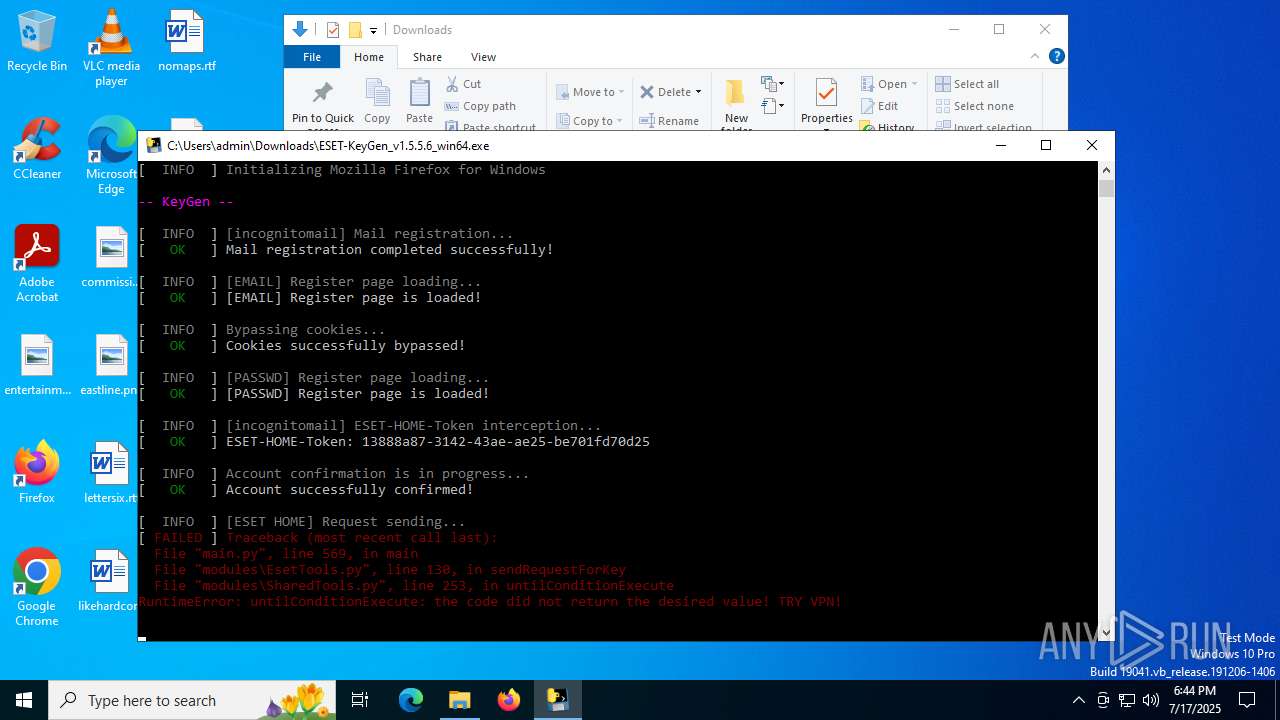
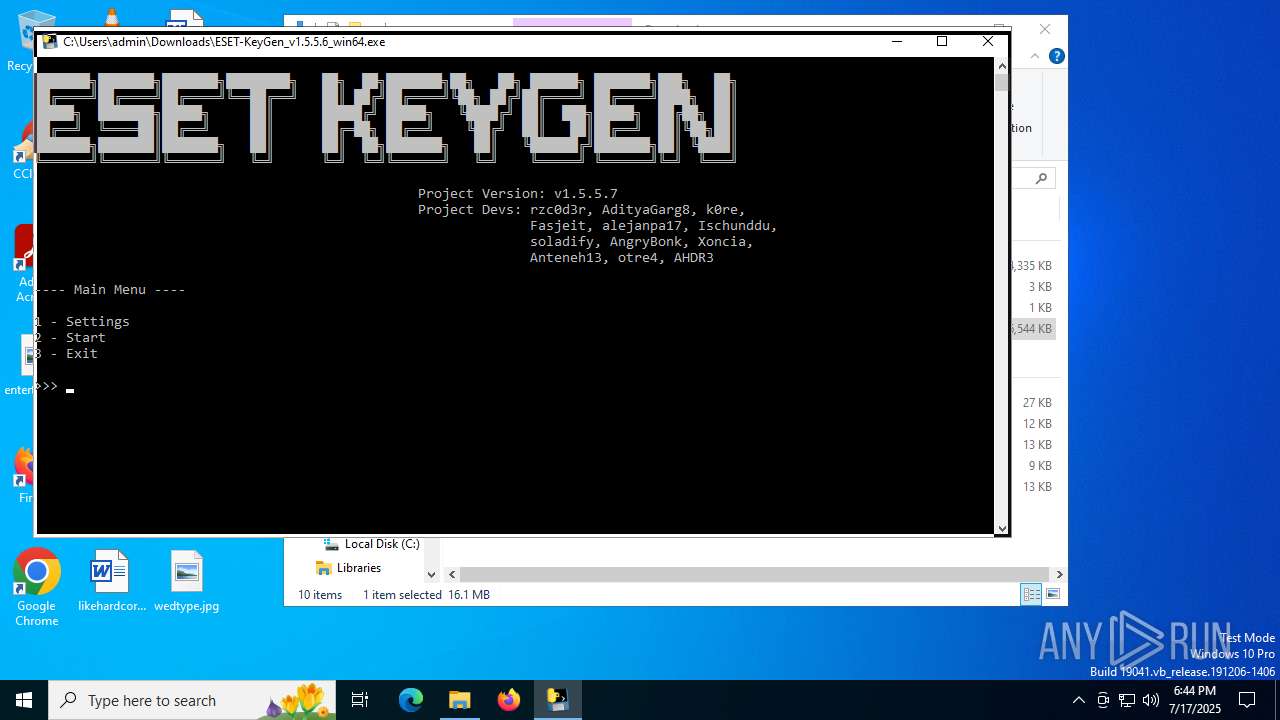
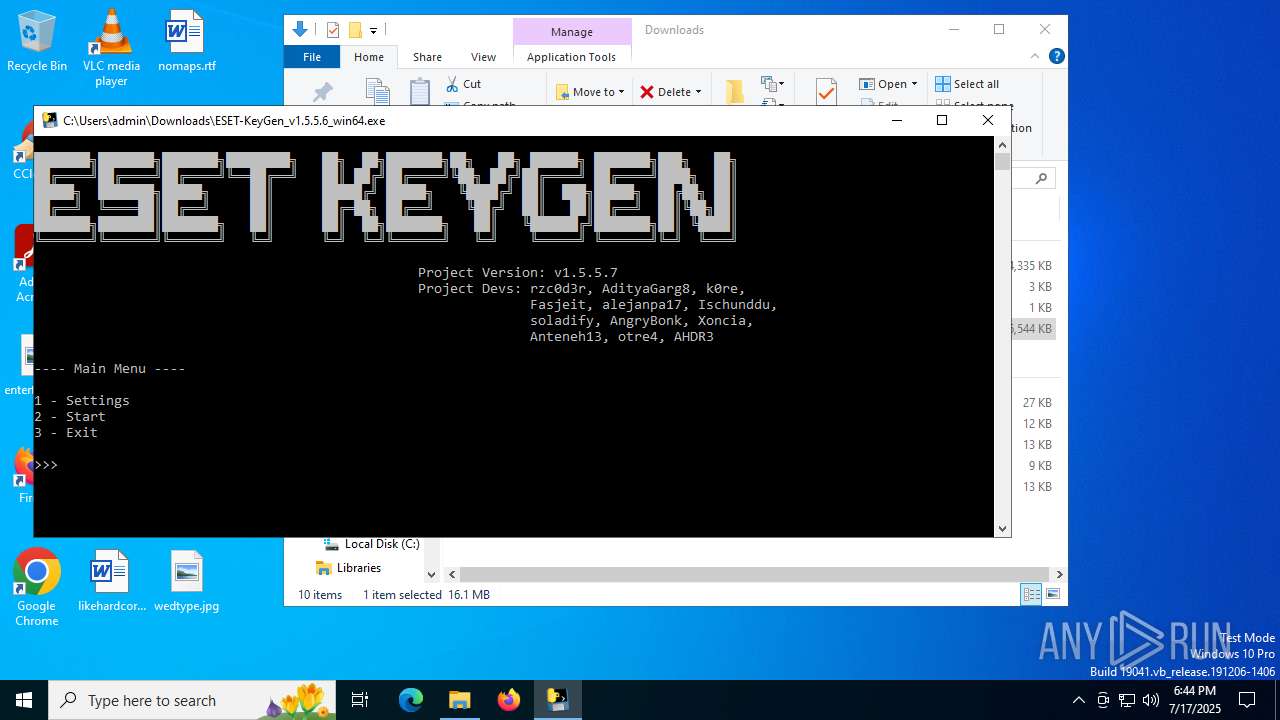
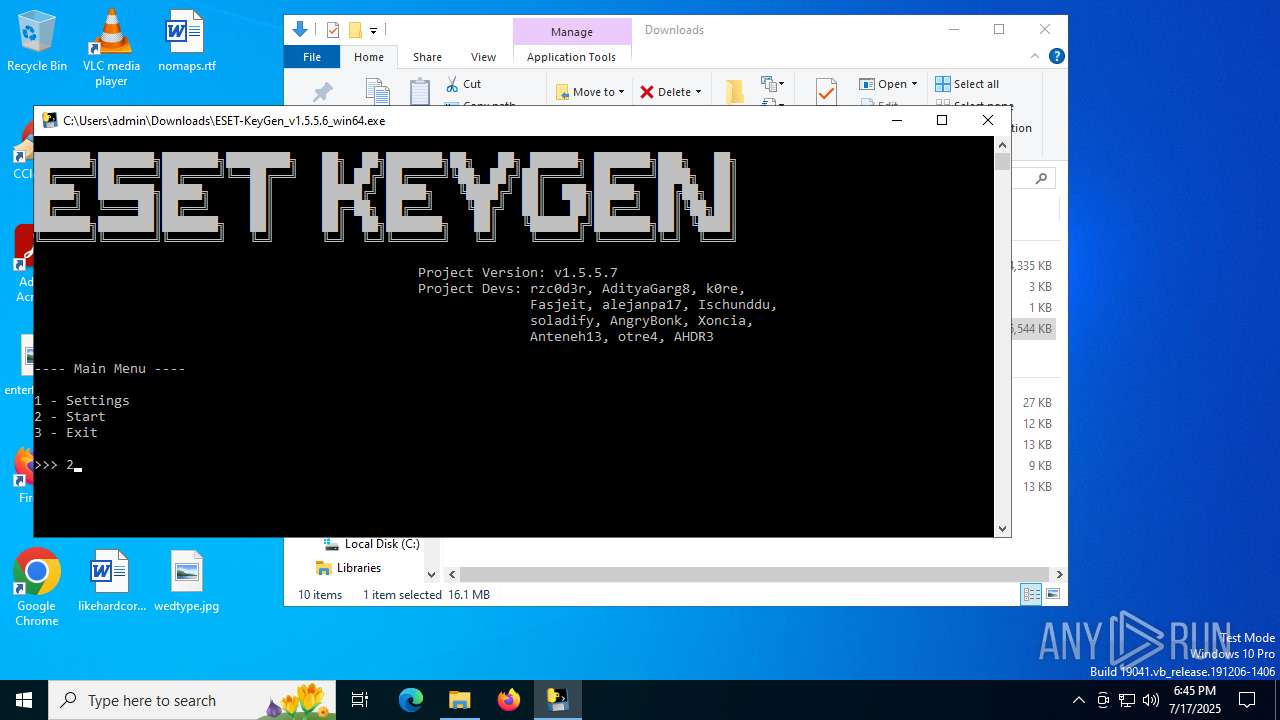
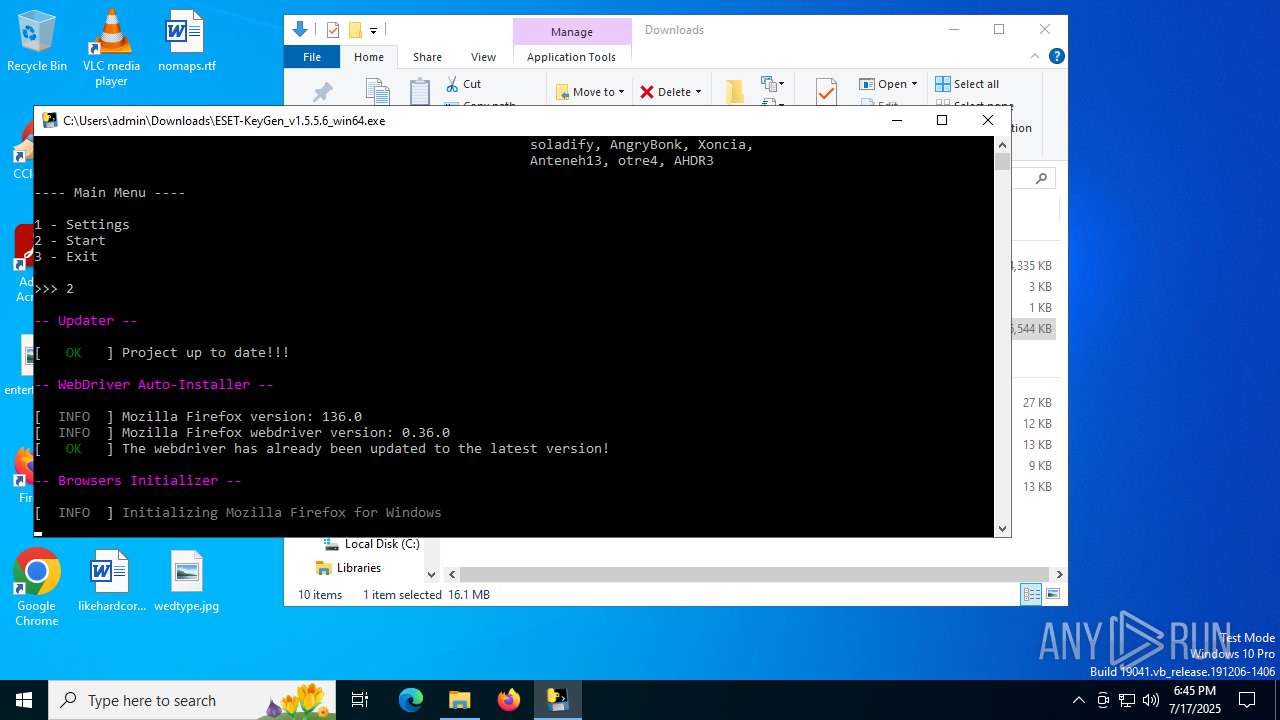
| URL: | https://github.com/rzc0d3r/ESET-KeyGen/releases/tag/v1.5.5.6 |
| Full analysis: | https://app.any.run/tasks/fbc9298b-b80d-40fb-94bc-029831d539eb |
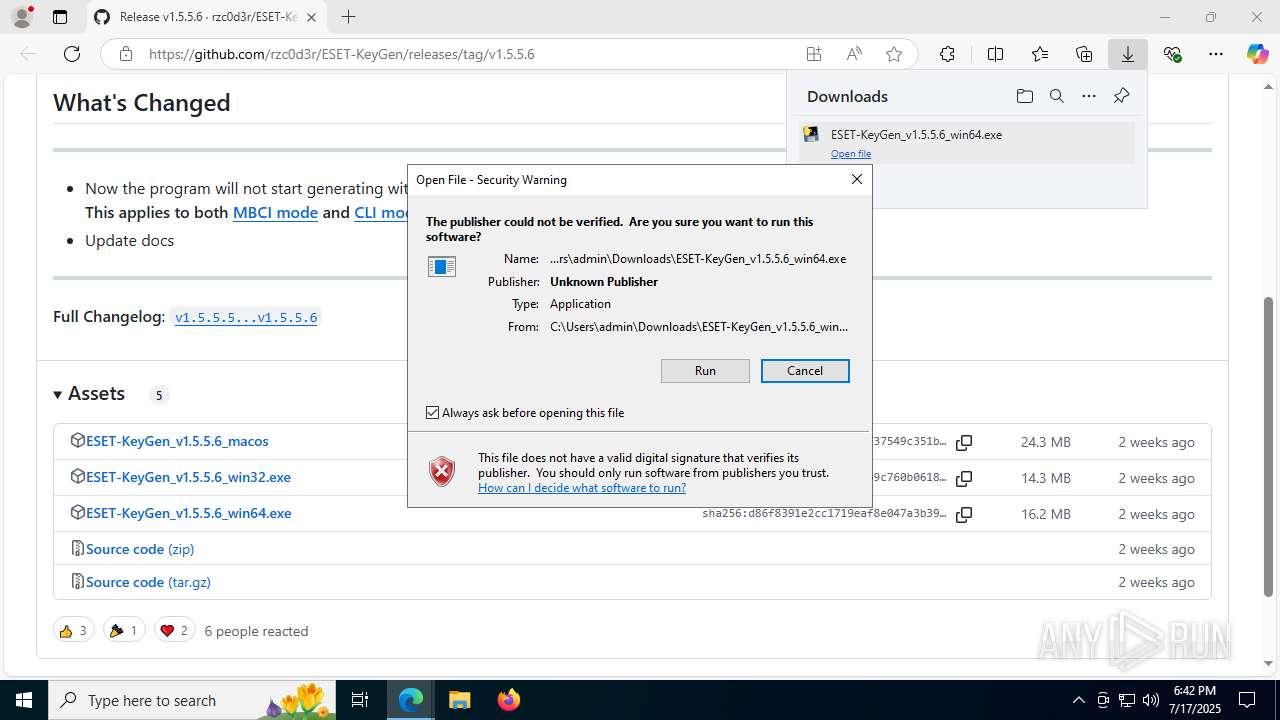
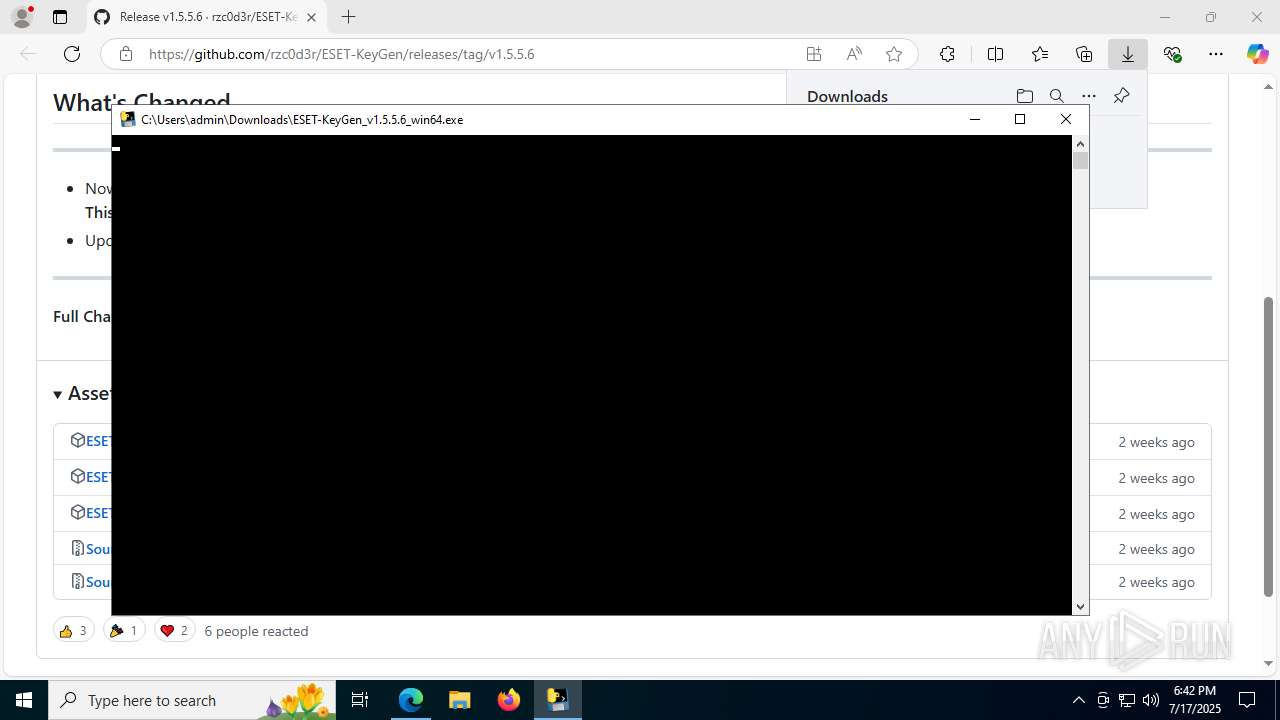
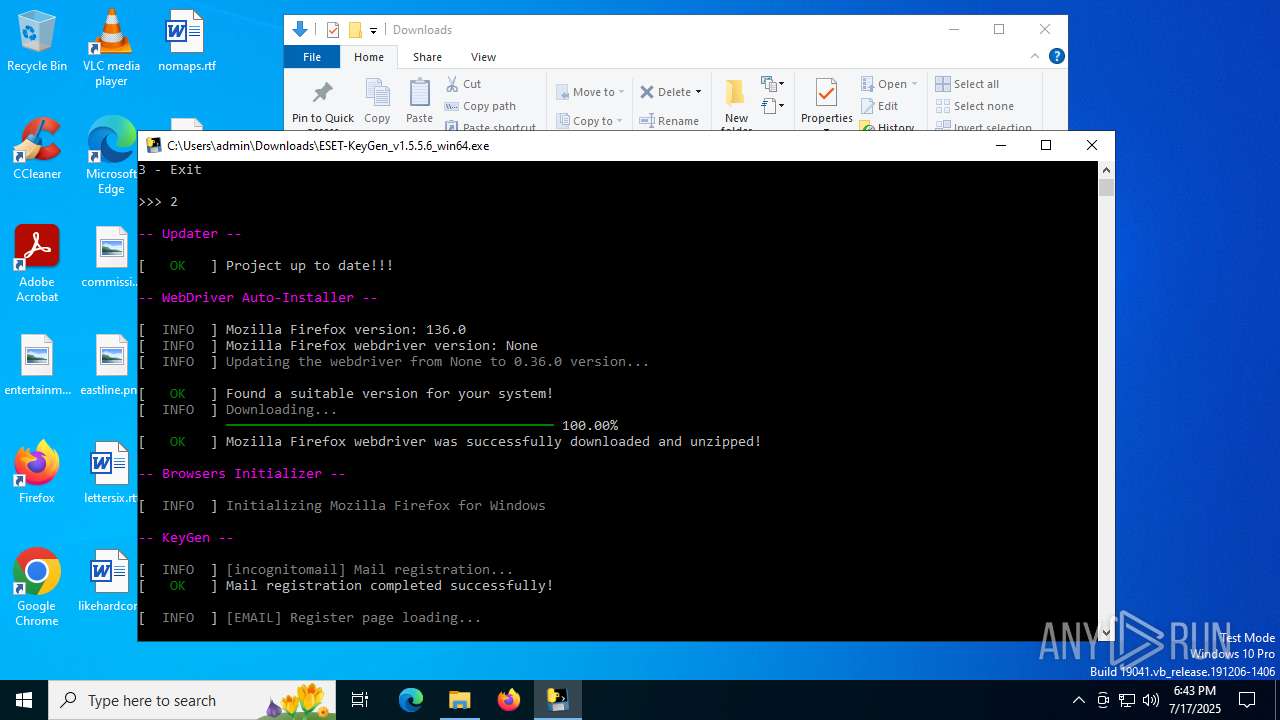
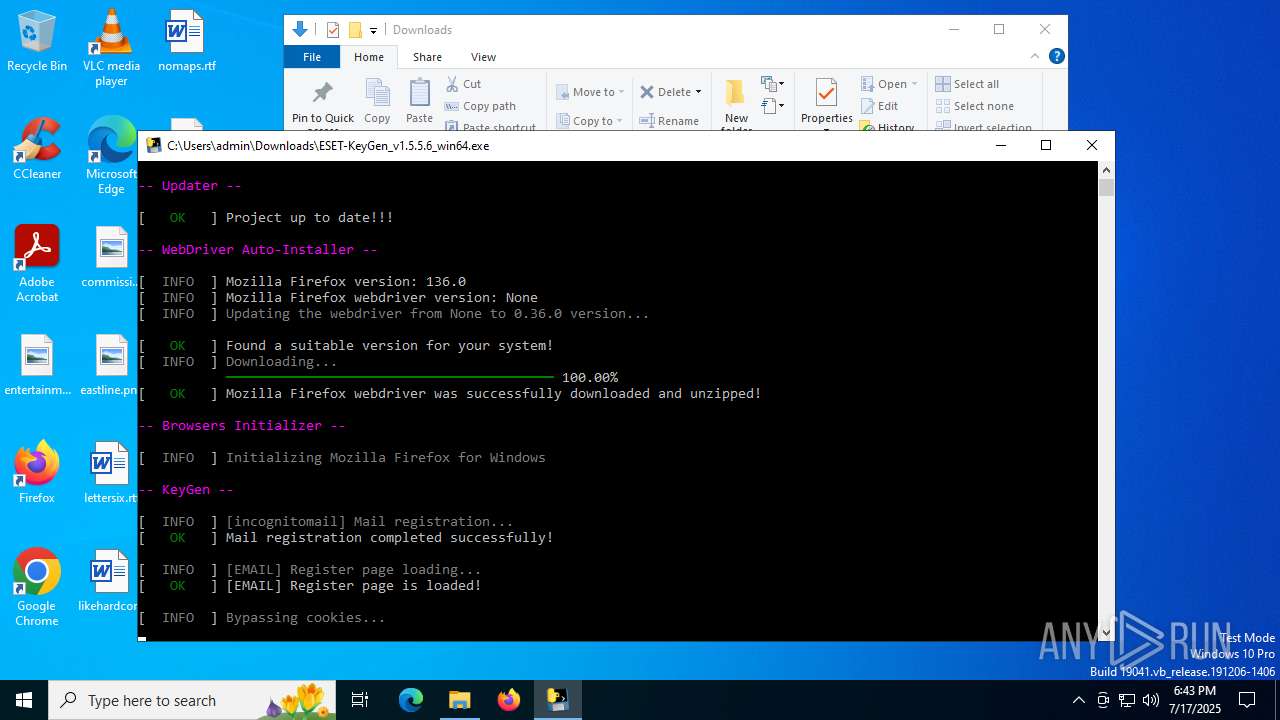
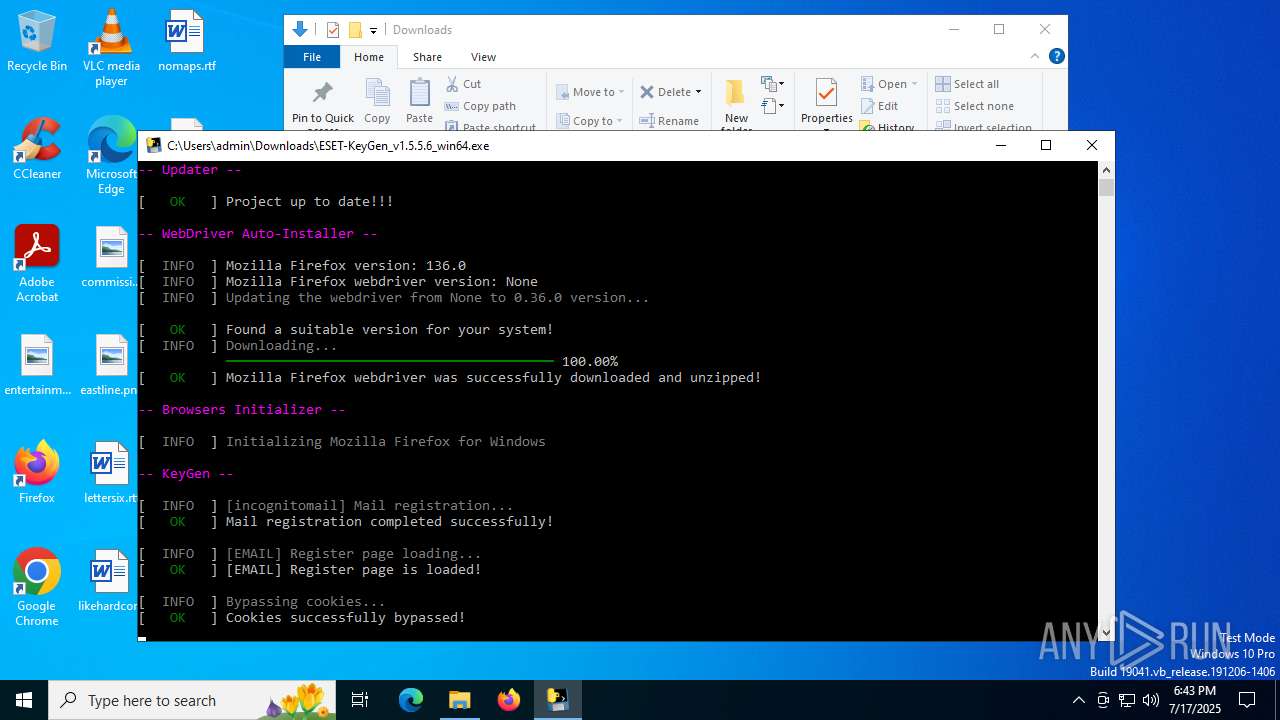
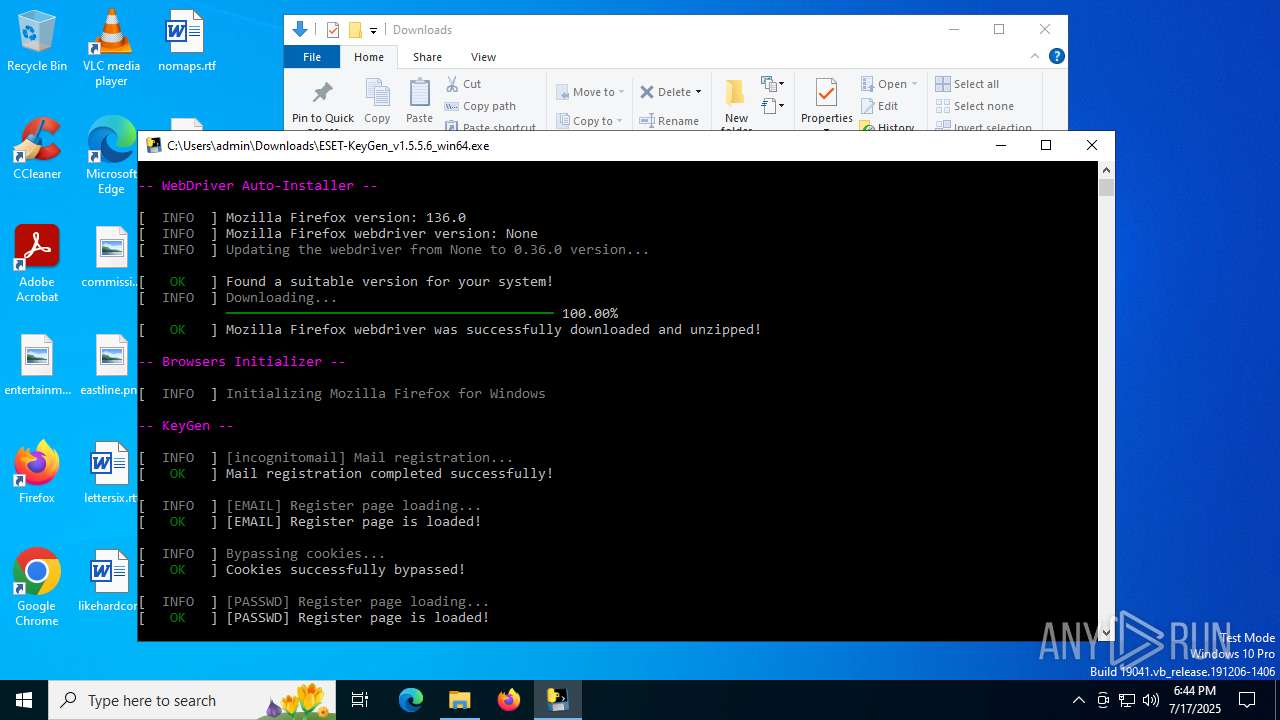
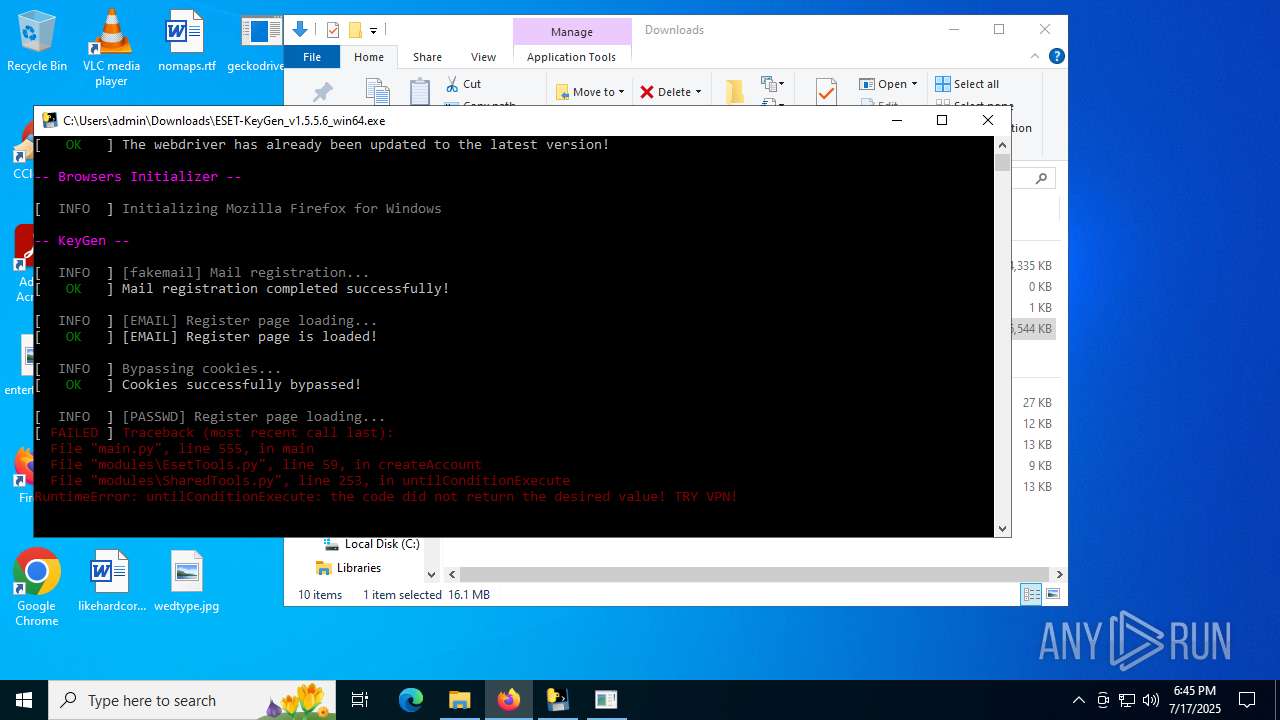
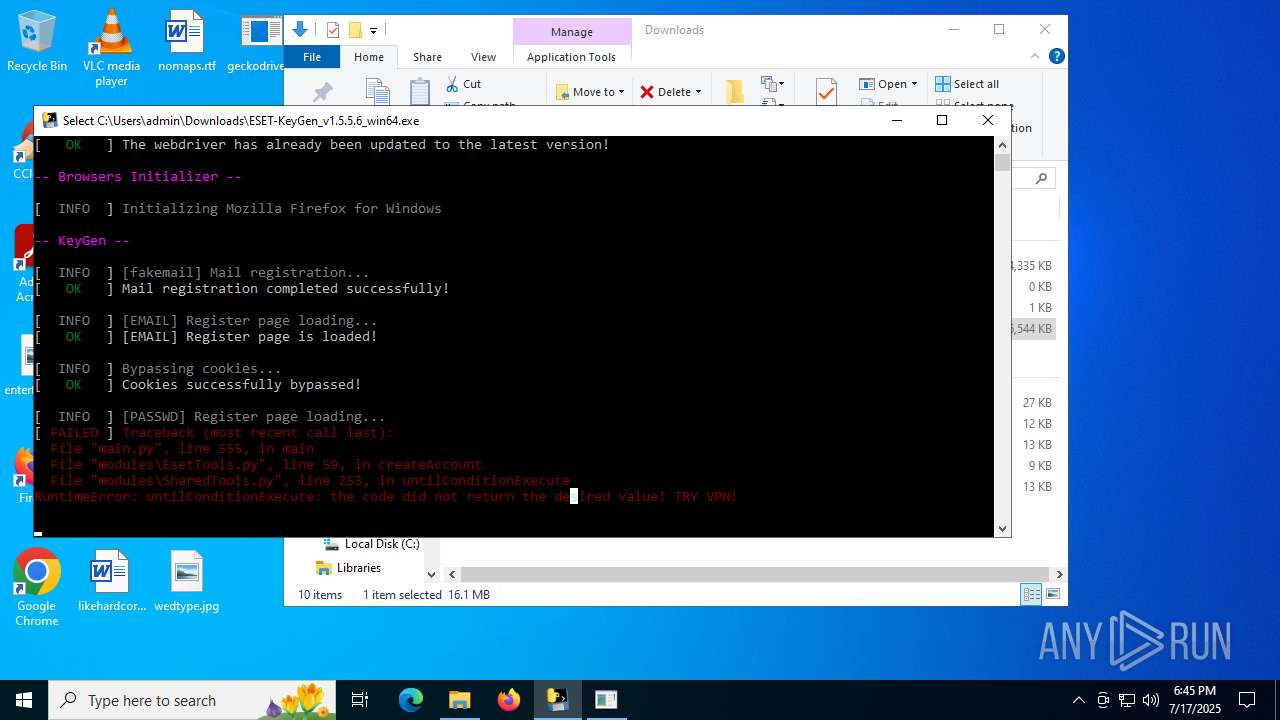
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2025, 18:42:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 62AF43950805096F2304F93F8391431B |
| SHA1: | 7E5E33306F637628FBF815EEB22C7243F7E30758 |
| SHA256: | BA8C0DD7E3535BFB094403E61923747BA9B015C72E67FEDC1A52CC3461CDE04C |
| SSDEEP: | 3:N8tEdnurQKqjLBJMqKCT:2u4rQX/MxCT |
MALICIOUS
No malicious indicators.SUSPICIOUS
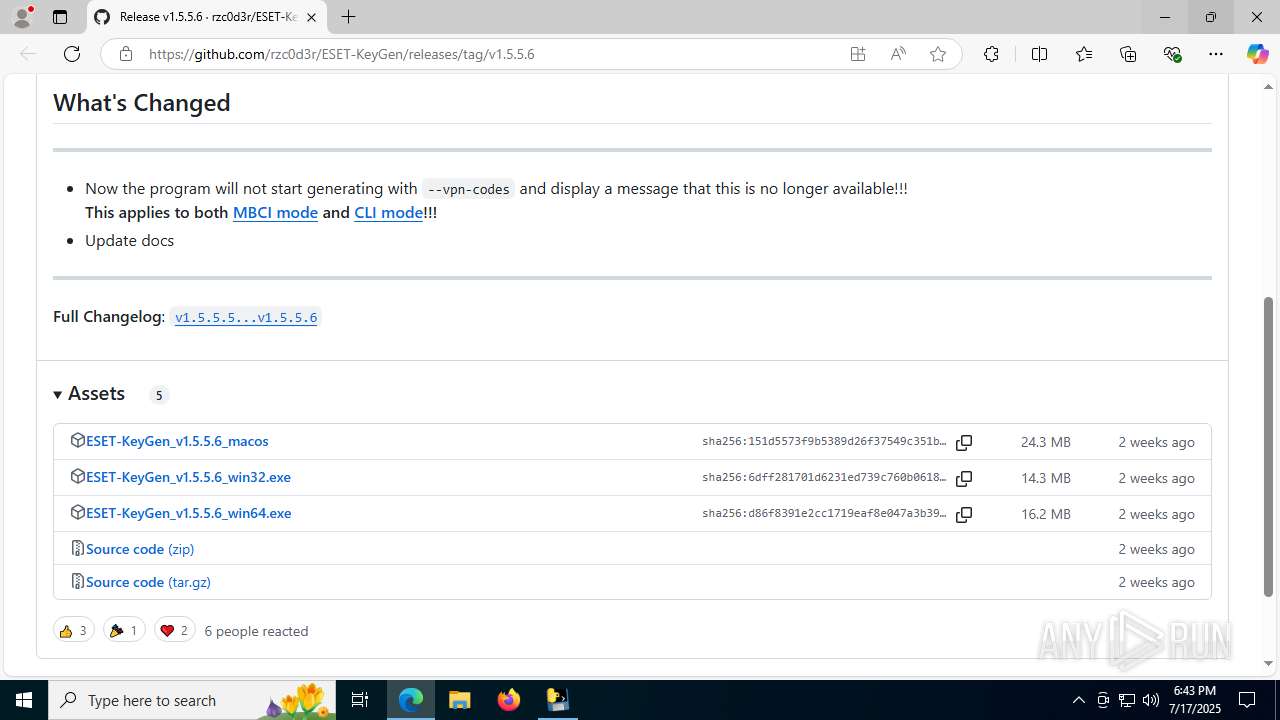
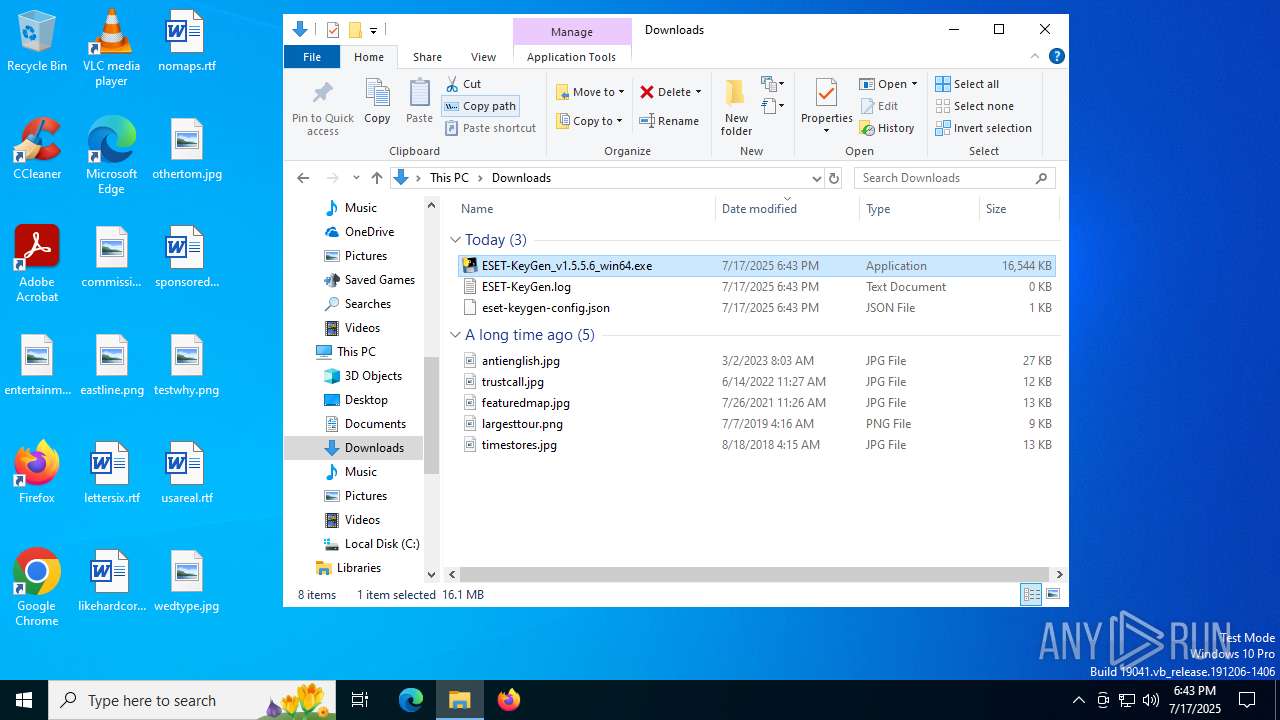
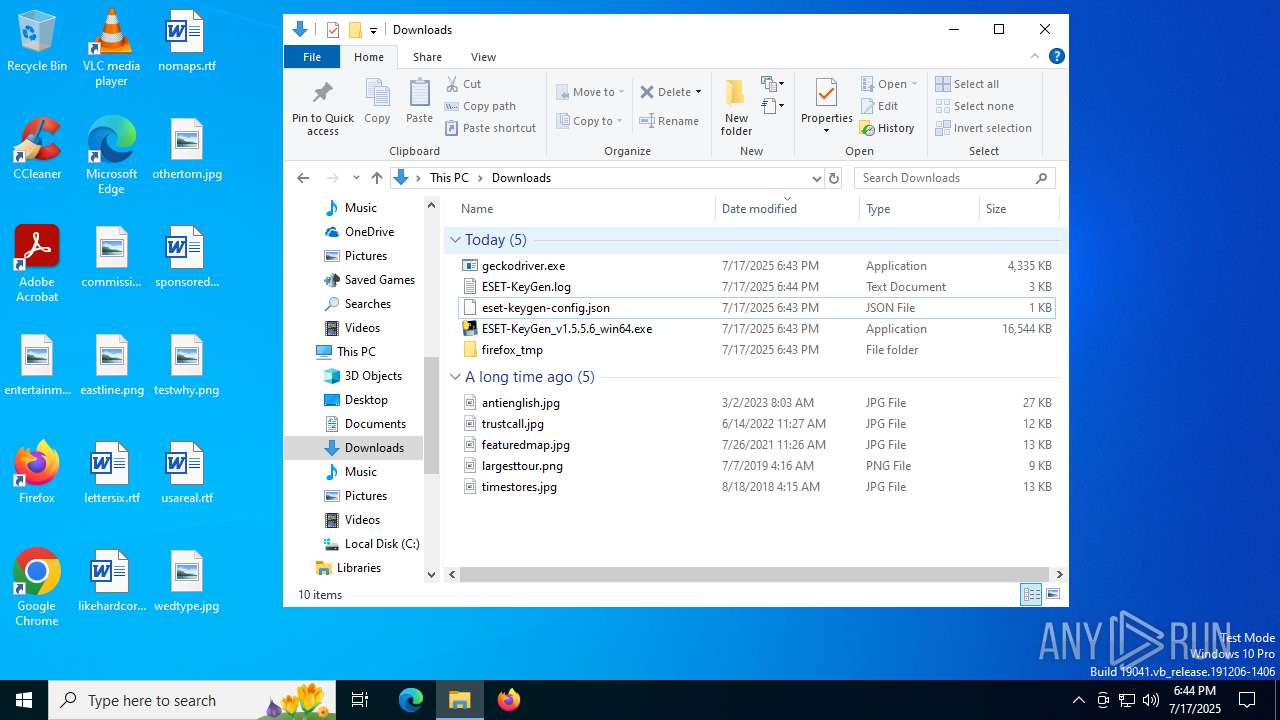
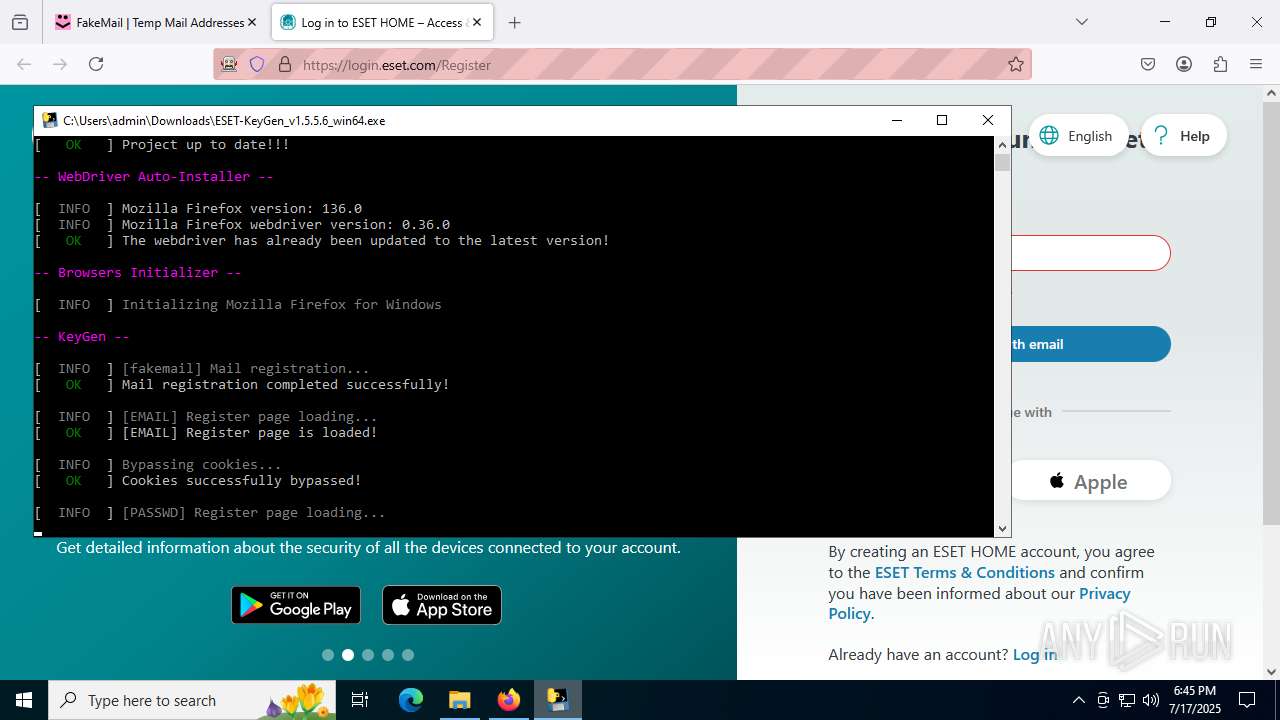
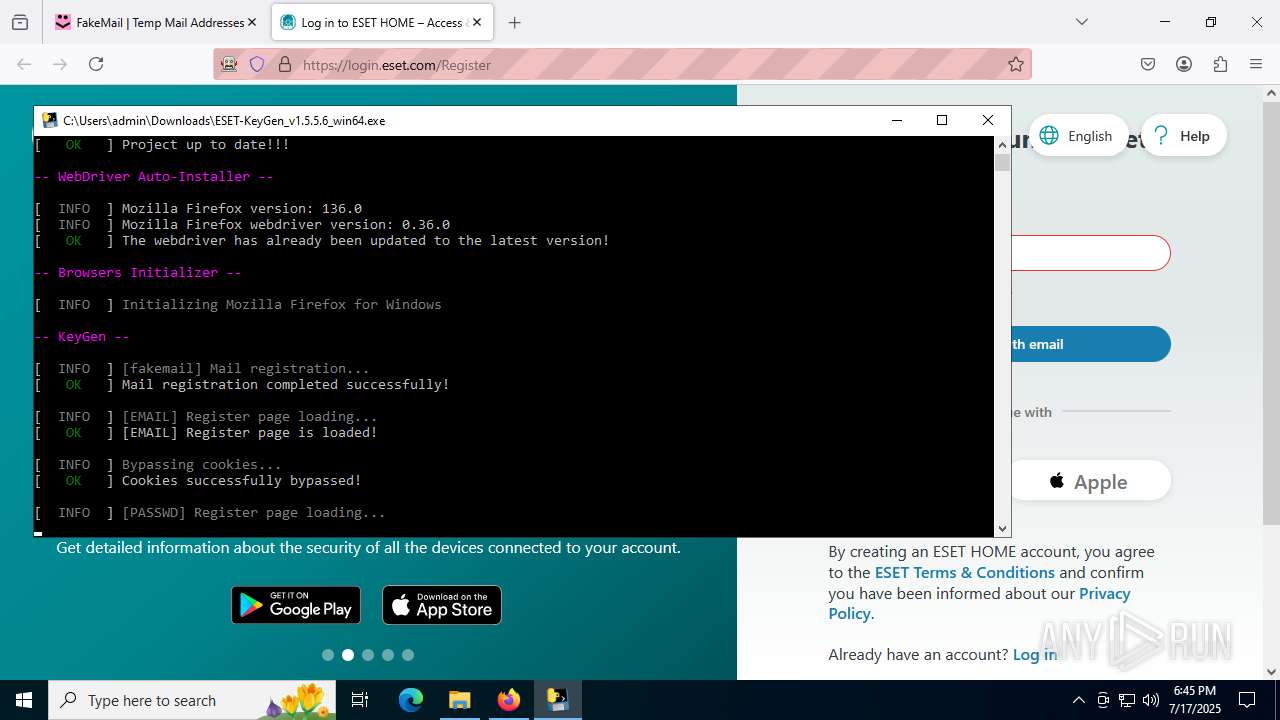
Process drops legitimate windows executable
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
Process drops python dynamic module
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
Executable content was dropped or overwritten
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
The process drops C-runtime libraries
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
Application launched itself
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
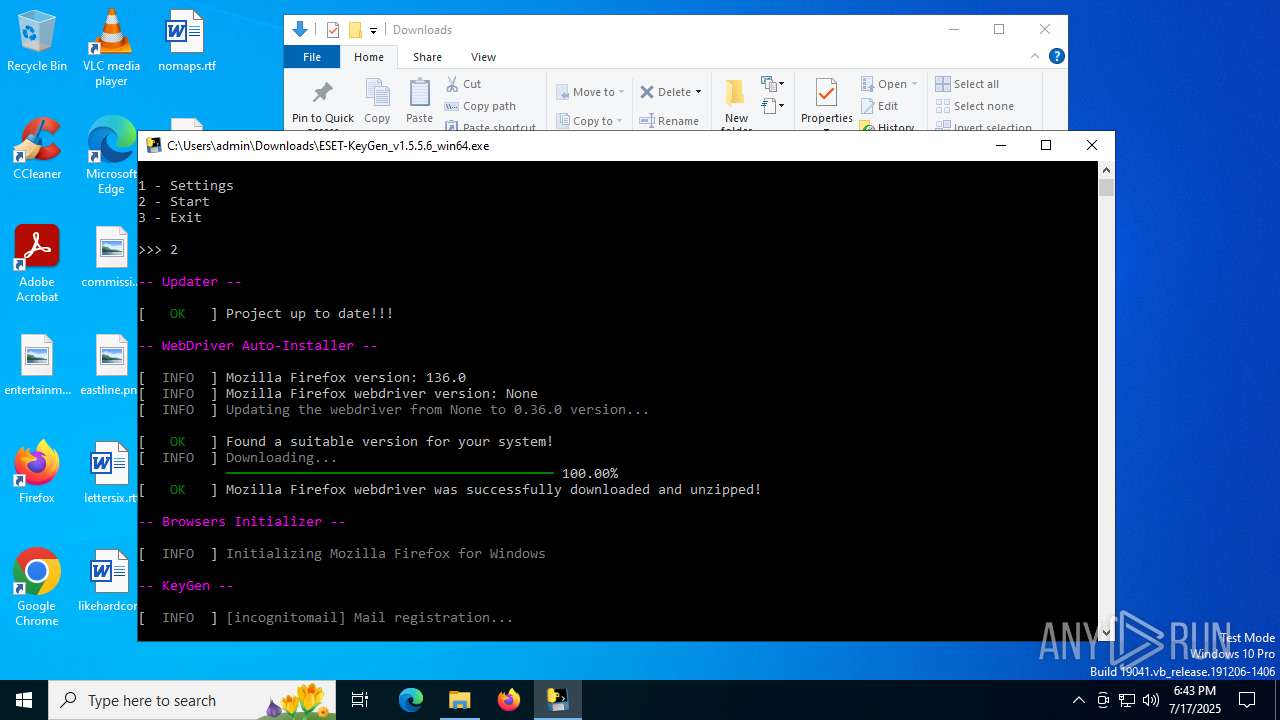
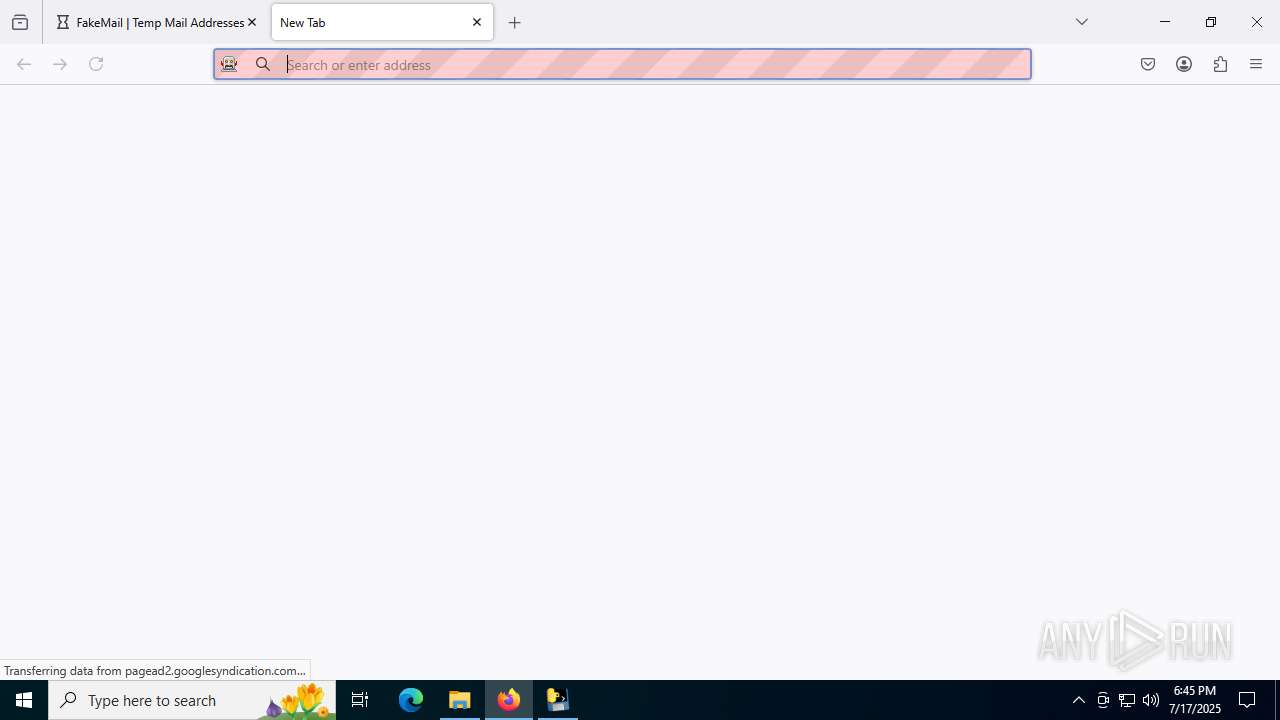
Loads Python modules
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
Starts CMD.EXE for commands execution
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4228)
Executing commands from a ".bat" file
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
INFO
Checks supported languages
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- identity_helper.exe (PID: 7844)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- curl.exe (PID: 1468)
- identity_helper.exe (PID: 7308)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
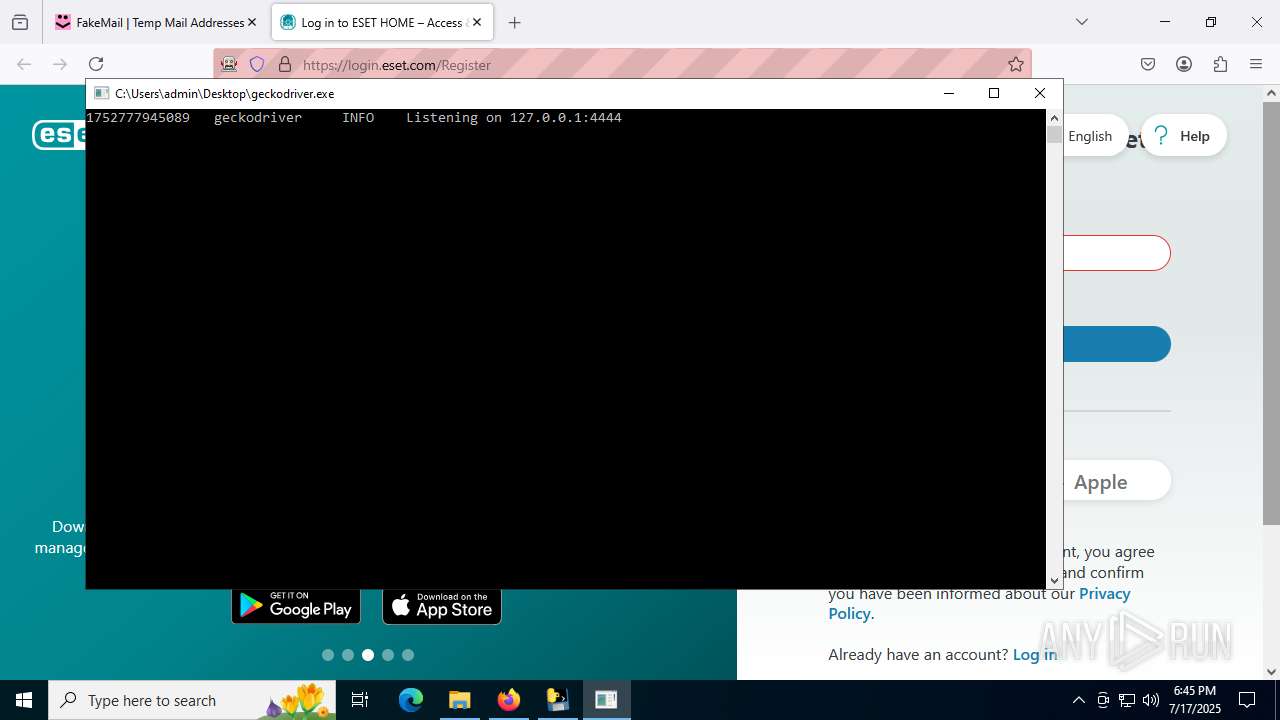
- geckodriver.exe (PID: 1128)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
- geckodriver.exe (PID: 3576)
- geckodriver.exe (PID: 7600)
- geckodriver.exe (PID: 8520)
Reads Environment values
- identity_helper.exe (PID: 7844)
- identity_helper.exe (PID: 7308)
Executable content was dropped or overwritten
- msedge.exe (PID: 5436)
- msedge.exe (PID: 3956)
Application launched itself
- msedge.exe (PID: 5436)
- msedge.exe (PID: 8128)
- firefox.exe (PID: 4232)
- firefox.exe (PID: 2228)
- firefox.exe (PID: 6892)
- firefox.exe (PID: 6212)
Reads the computer name
- identity_helper.exe (PID: 7844)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- curl.exe (PID: 1468)
- identity_helper.exe (PID: 7308)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- geckodriver.exe (PID: 1128)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
- geckodriver.exe (PID: 7600)
- geckodriver.exe (PID: 8520)
The sample compiled with english language support
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
Create files in a temporary directory
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- geckodriver.exe (PID: 1128)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
- geckodriver.exe (PID: 7600)
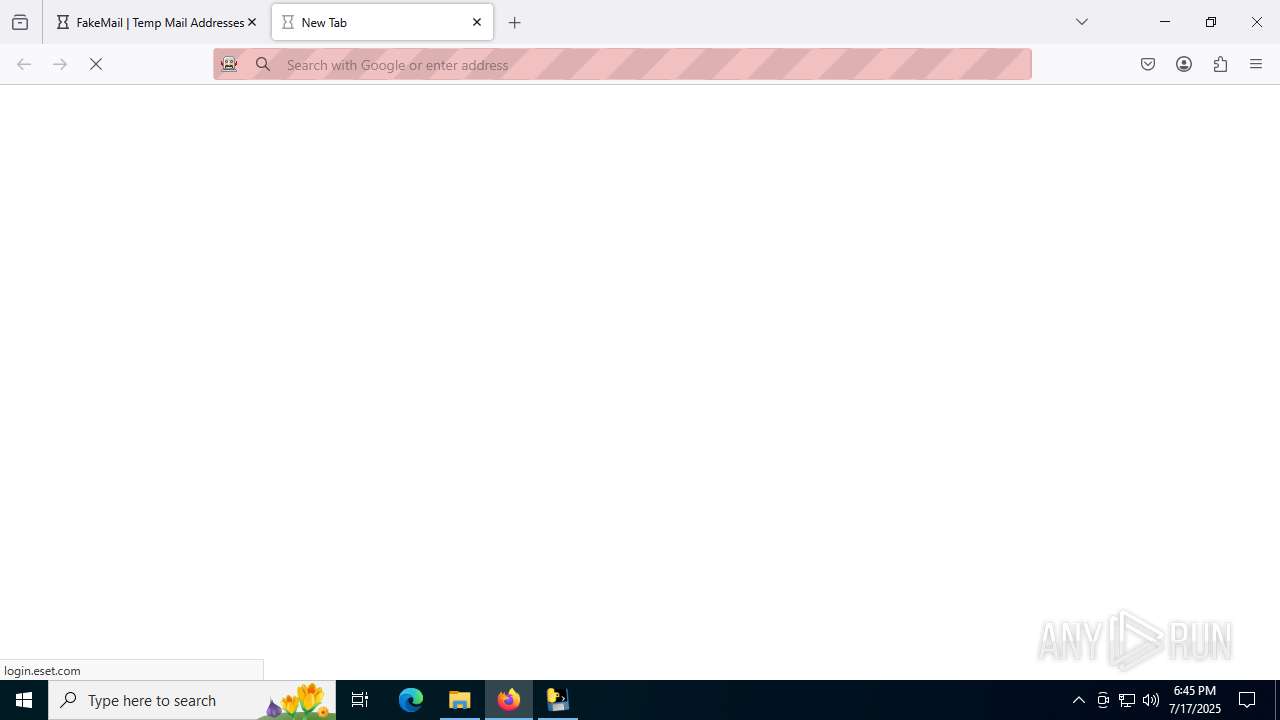
Reads the machine GUID from the registry
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
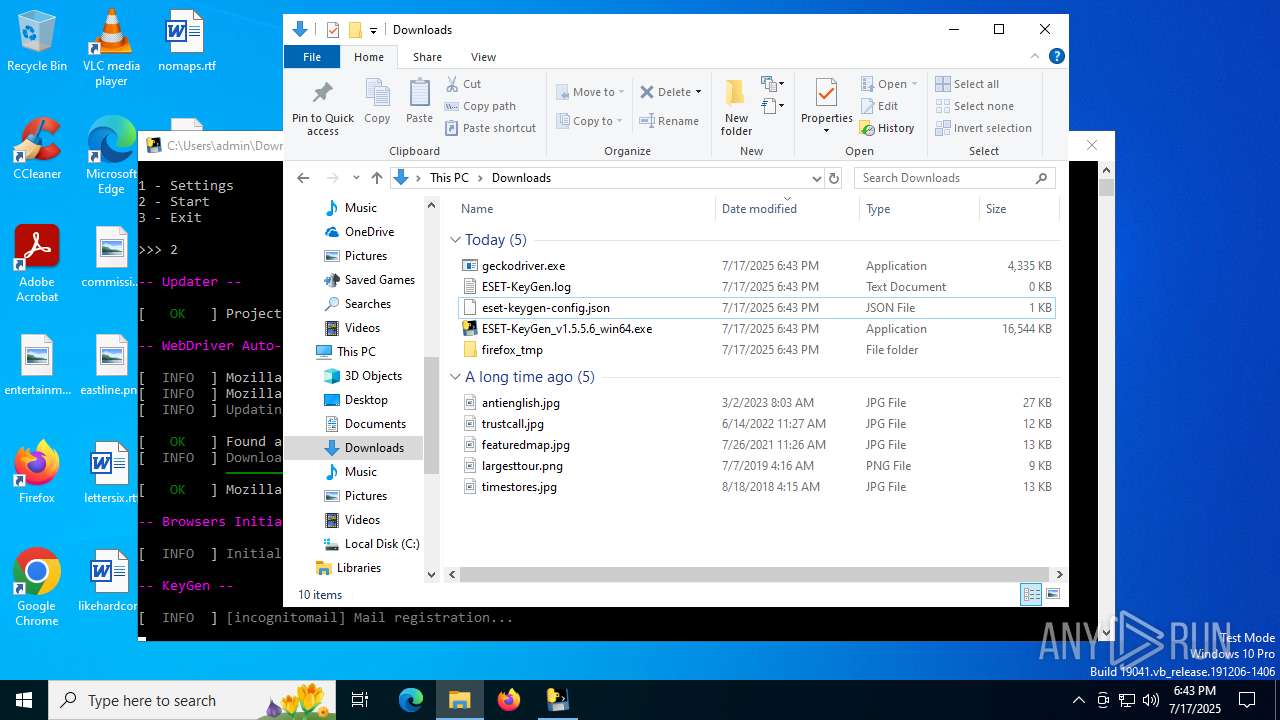
Drops encrypted JS script (Microsoft Script Encoder)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
Checks proxy server information
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- slui.exe (PID: 3852)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
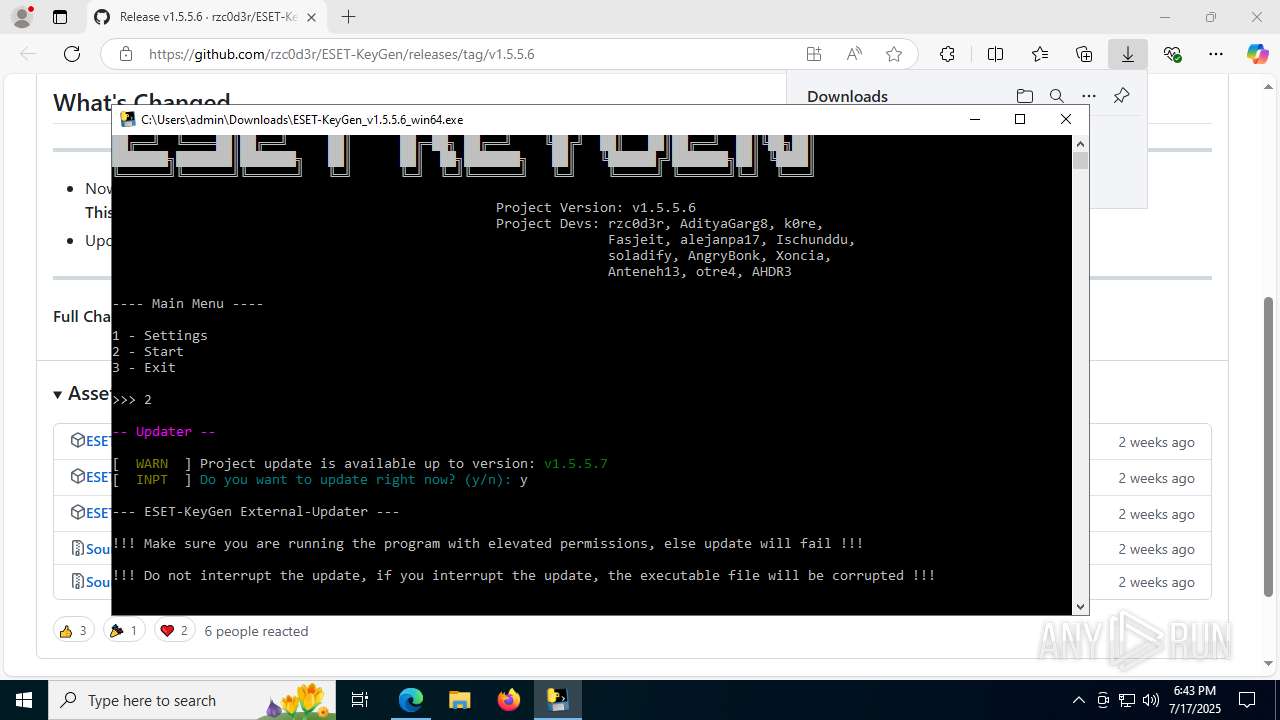
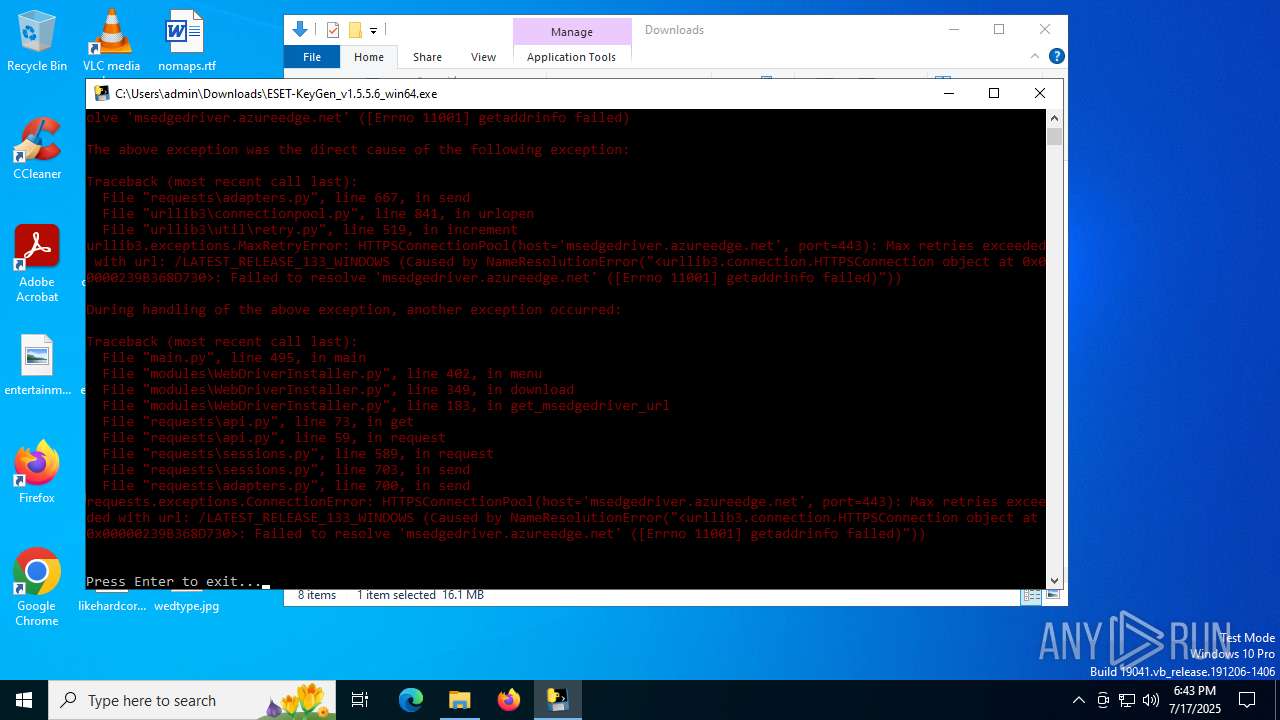
Execution of CURL command
- cmd.exe (PID: 4228)
Manual execution by a user
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8036)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2528)
- geckodriver.exe (PID: 8520)
PyInstaller has been detected (YARA)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 8188)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7792)
Checks operating system version
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 2292)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7440)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 4192)
- ESET-KeyGen_v1.5.5.6_win64.exe (PID: 7268)
Reads the software policy settings
- slui.exe (PID: 3852)
Reads Microsoft Office registry keys
- firefox.exe (PID: 4232)
- firefox.exe (PID: 6212)
Application based on Rust
- geckodriver.exe (PID: 1128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
270
Monitored processes
126
Malicious processes
5
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5096,i,17209110238581445413,8698234095428223941,262144 --variations-seed-version --mojo-platform-channel-handle=4652 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 472 | timeout 1 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -sandboxingKind 0 -prefsHandle 4488 -prefsLen 41620 -prefMapHandle 4492 -prefMapSize 269706 -ipcHandle 4416 -initialChannelId {83313972-0571-4824-87ae-e30c6014b7da} -parentPid 6212 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6212" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 6 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 136.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4448 -prefsLen 39649 -prefMapHandle 4296 -prefMapSize 269706 -jsInitHandle 4440 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 4556 -initialChannelId {4d36a924-23c4-4281-8172-85698dfe1661} -parentPid 6212 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6212" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1128 | C:\Users\admin\Downloads\geckodriver.exe --port 49816 --websocket-port 49817 | C:\Users\admin\Downloads\geckodriver.exe | — | ESET-KeyGen_v1.5.5.6_win64.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1180 | C:\WINDOWS\system32\cmd.exe /c cls | C:\Windows\System32\cmd.exe | — | ESET-KeyGen_v1.5.5.6_win64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | where curl | C:\Windows\System32\where.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Where - Lists location of files Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3516 -prefsLen 30390 -prefMapHandle 3520 -prefMapSize 269706 -jsInitHandle 3524 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3532 -initialChannelId {b9b6cca4-110c-4319-aa7d-1a072721cfe6} -parentPid 6212 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6212" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 5 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5764 -prefsLen 39916 -prefMapHandle 5912 -prefMapSize 269706 -jsInitHandle 5916 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5852 -initialChannelId {5f6ec925-9911-4eb2-adea-65504e4cec0f} -parentPid 6212 -crashReporter "\\.\pipe\gecko-crash-server-pipe.6212" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 16 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
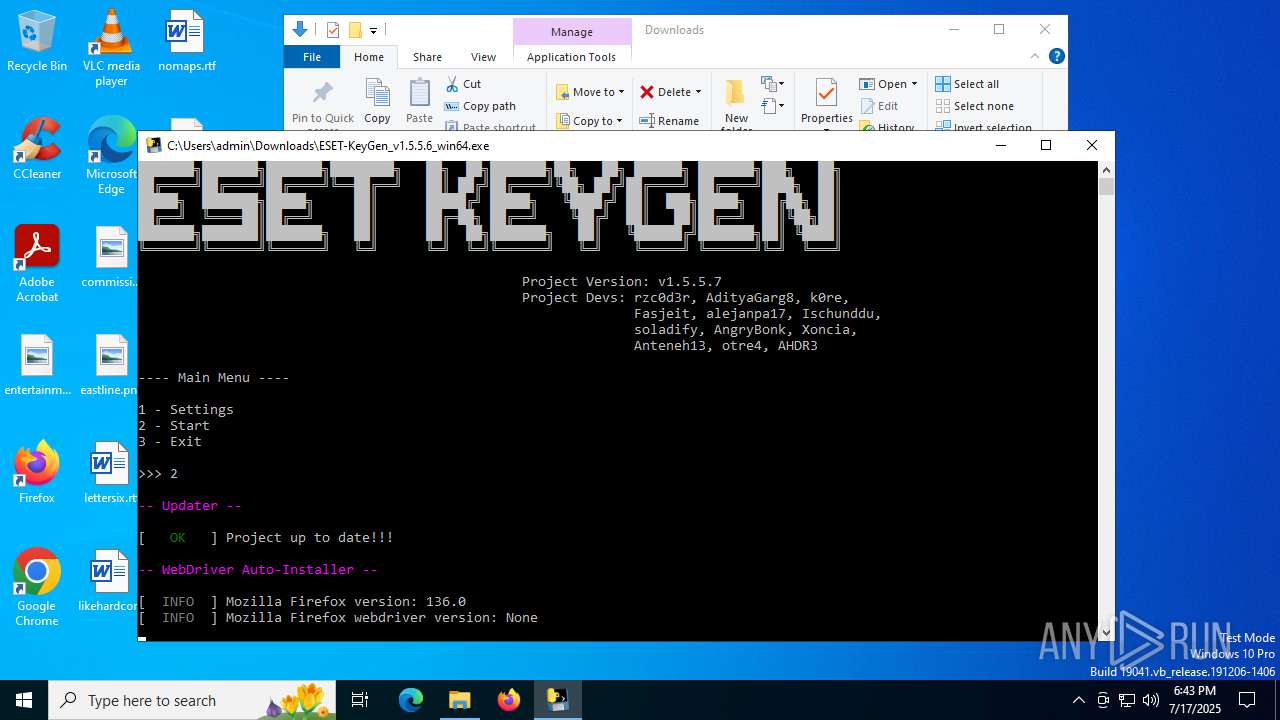
| 1468 | curl -#L https://github.com/shadowcopyrz/ESET-KGEN-COPY/releases/download/v1.5.5.7/ESET-KeyGen_v1.5.5.7_win64.exe -o C:\Users\admin\Downloads\ESET-KeyGen_v1.5.5.6_win64.exe | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
Total events
44 585
Read events
44 558
Write events
27
Delete events
0
Modification events
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 724D1EA8BA982F00 | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459544 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4655FB4C-0ACB-4D53-B209-453D2CE4BD07} | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459544 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3A70A5C1-2DAB-4C4C-9CE4-9C49678F35DD} | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459544 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FFA80FBC-3890-4D55-86D5-827B3853C8EA} | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459544 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {49B07065-86B4-4E53-8DD8-4DE1F704EE83} | |||
| (PID) Process: | (5436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459544 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F3B4A663-1FC9-47CF-B745-00CD1FB06A38} | |||
Executable files
269
Suspicious files
574
Text files
246
Unknown types
347
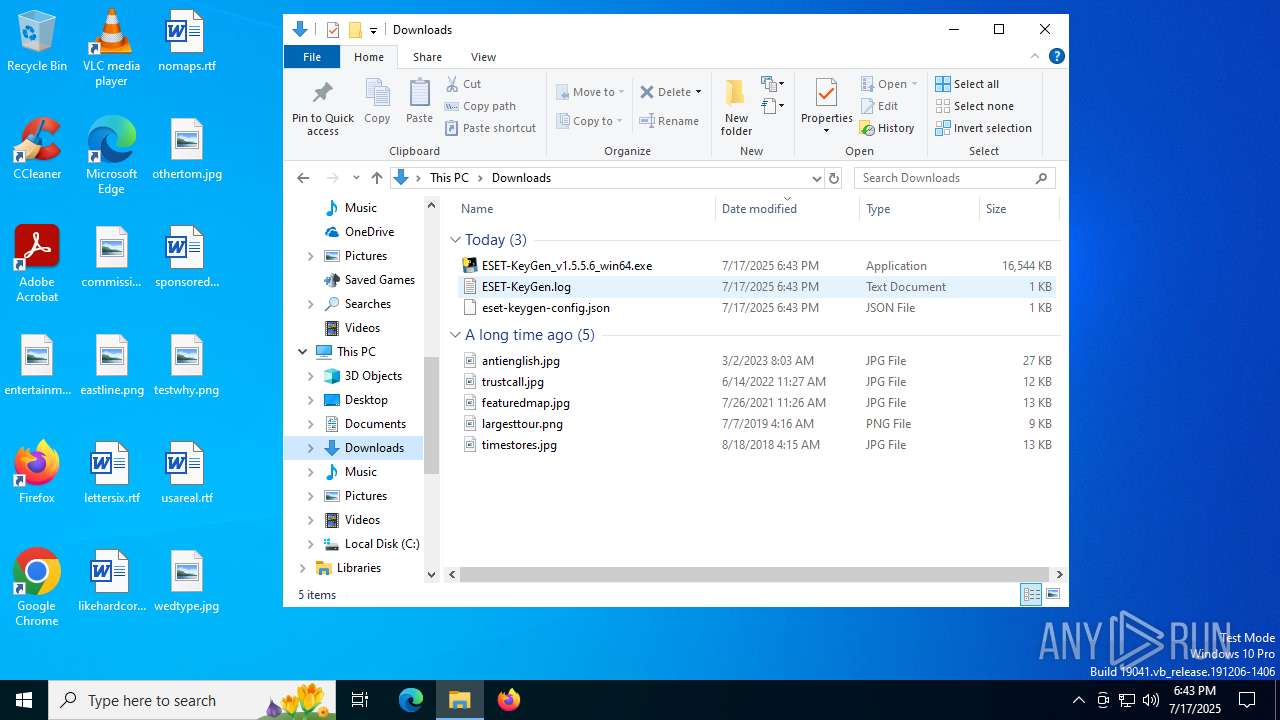
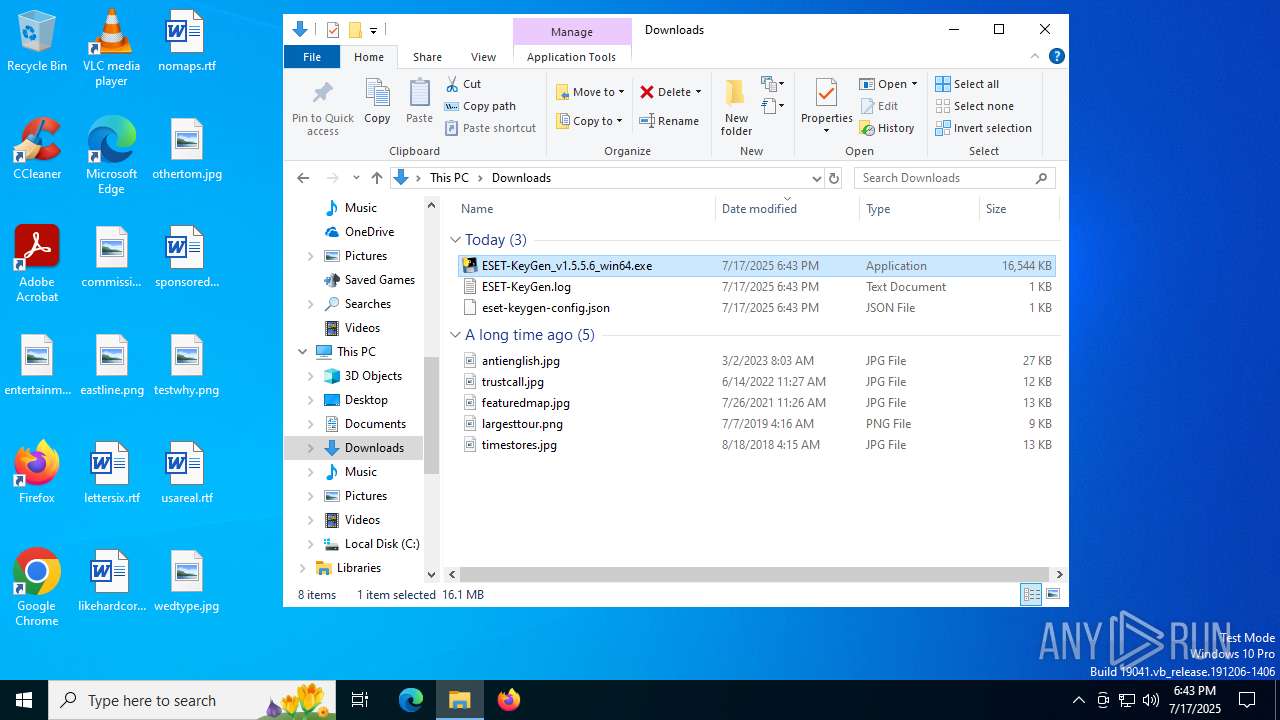
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF18d491.TMP | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF18d4a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF18d4a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF18d4a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF18d4a0.TMP | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
78
TCP/UDP connections
276
DNS requests
344
Threats
270
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3956 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:HXof-zlDdKhbliUI_dDQ1ENxCjGpe0rWgk9Fec2D9rQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4168 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
8140 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2432 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3956 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
3956 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3956 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
user-images.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4232 | firefox.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |