| File name: | ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387 |
| Full analysis: | https://app.any.run/tasks/e97416d5-93f9-4c94-a1b4-a010f9734103 |
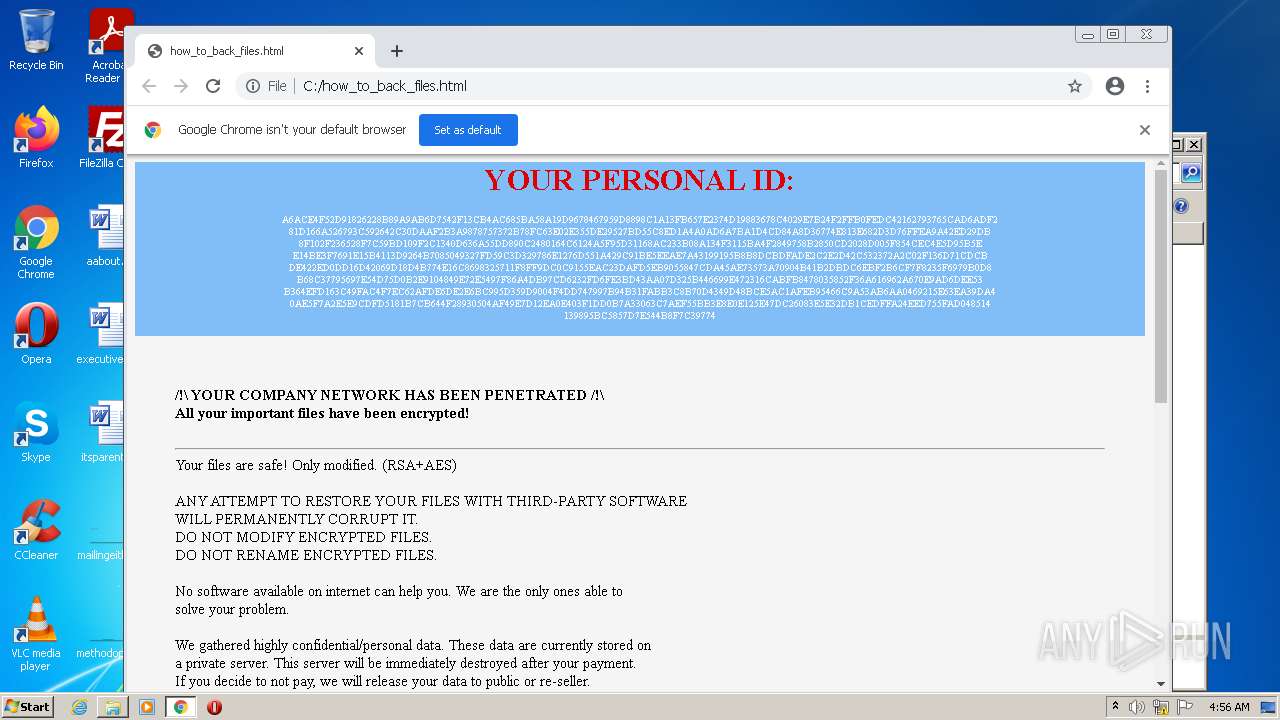
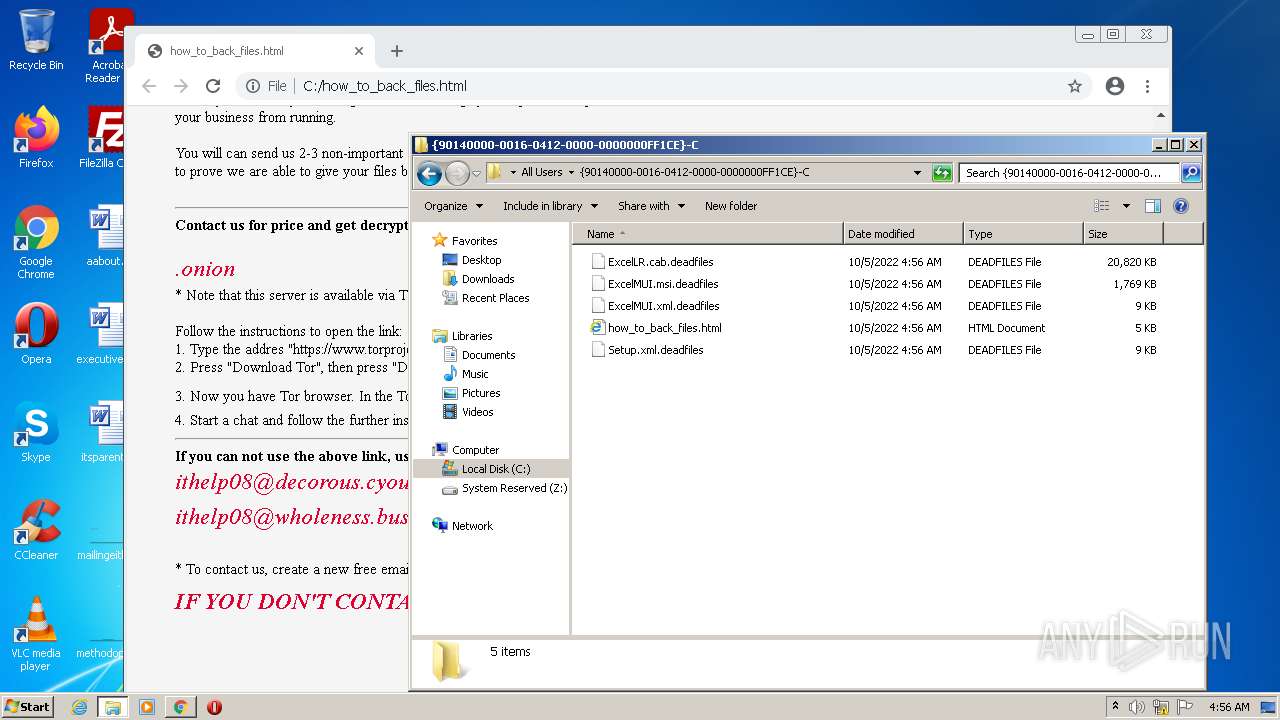
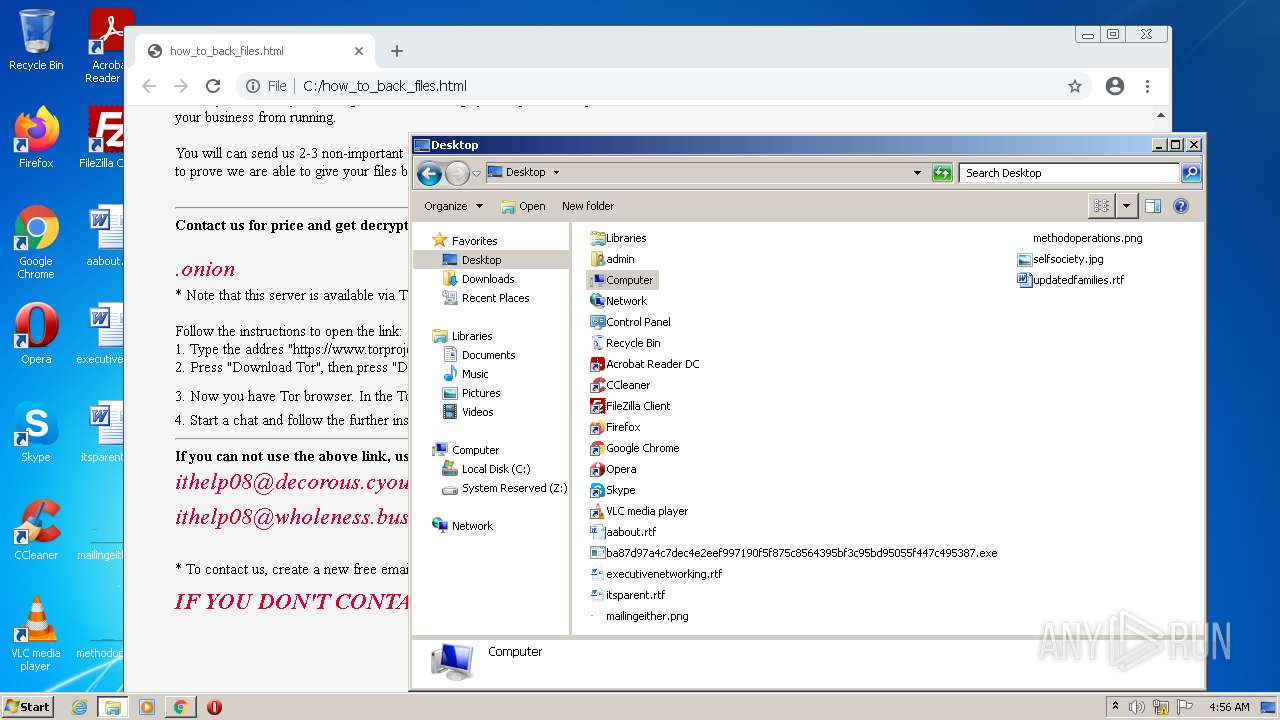
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 03:55:57 |
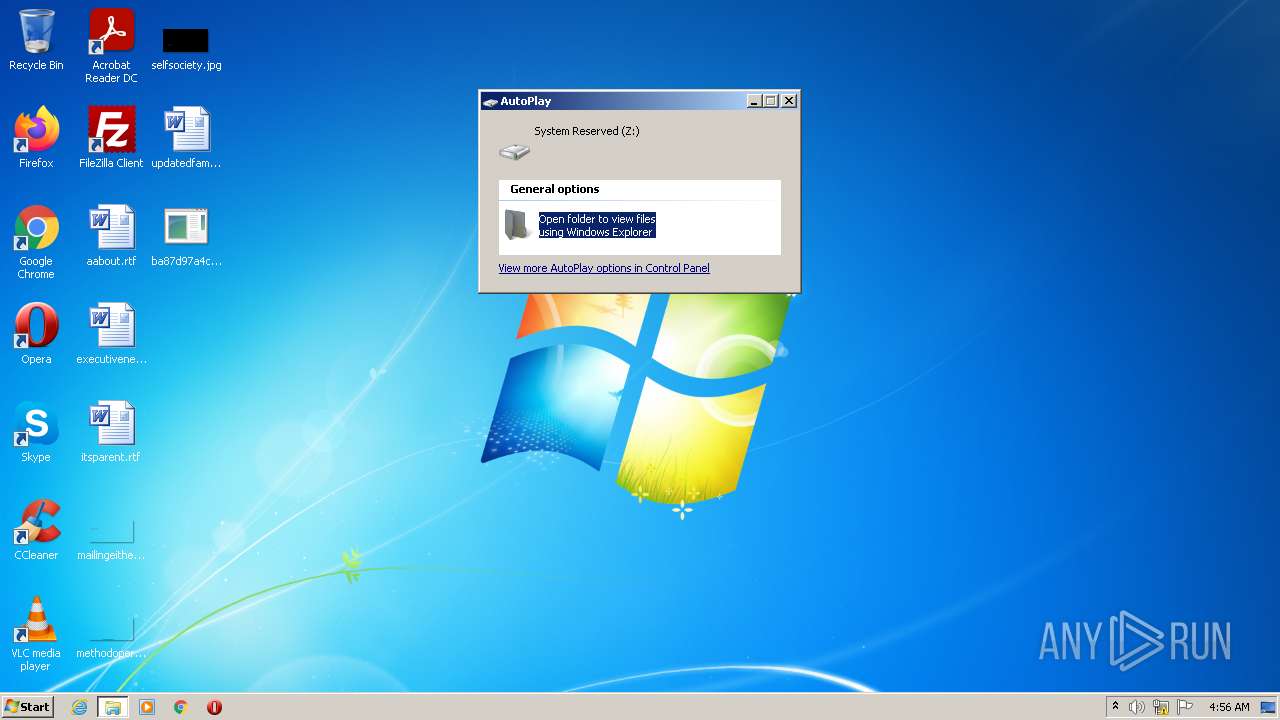
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CFA482B23FA7A59641A6B816D56A3C58 |
| SHA1: | 0CD9753113E29FD460DCDCFFB21F364B3C5A14AA |
| SHA256: | BA87D97A4C7DEC4E2EEF997190F5F875C8564395BF3C95BD95055F447C495387 |
| SSDEEP: | 12288:dQA0FfTcwpBuV2UxqDmuiLZeUaoFi2XZWfGe615HhAZV8DhKD/KeX:Tuf4wTuV2Ux3uIZeUBi2Te6HWMKrKe |
MALICIOUS
UAC/LUA settings modification
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Known privilege escalation attack
- DllHost.exe (PID: 4072)
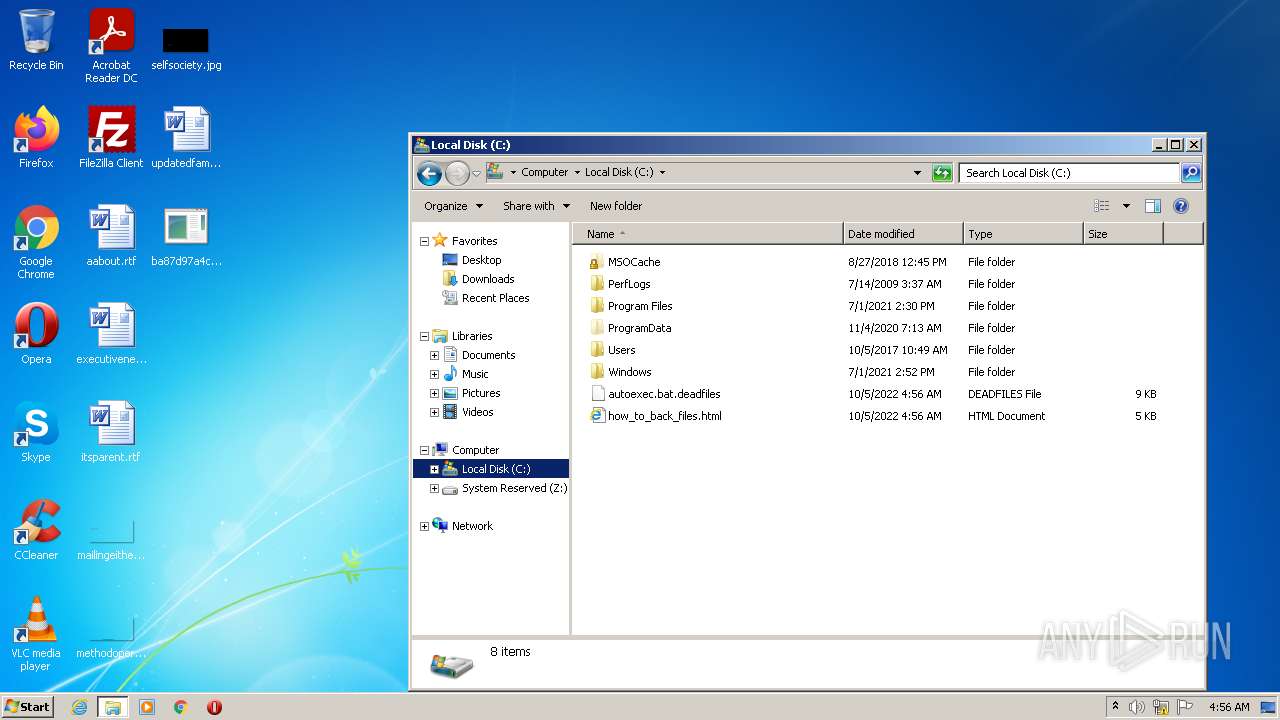
Deletes shadow copies
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Loads the Task Scheduler COM API
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Starts BCDEDIT.EXE to disable recovery
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 4072)
Checks supported languages
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 684)
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
- svhost.exe (PID: 3380)
Executed as Windows Service
- vssvc.exe (PID: 2896)
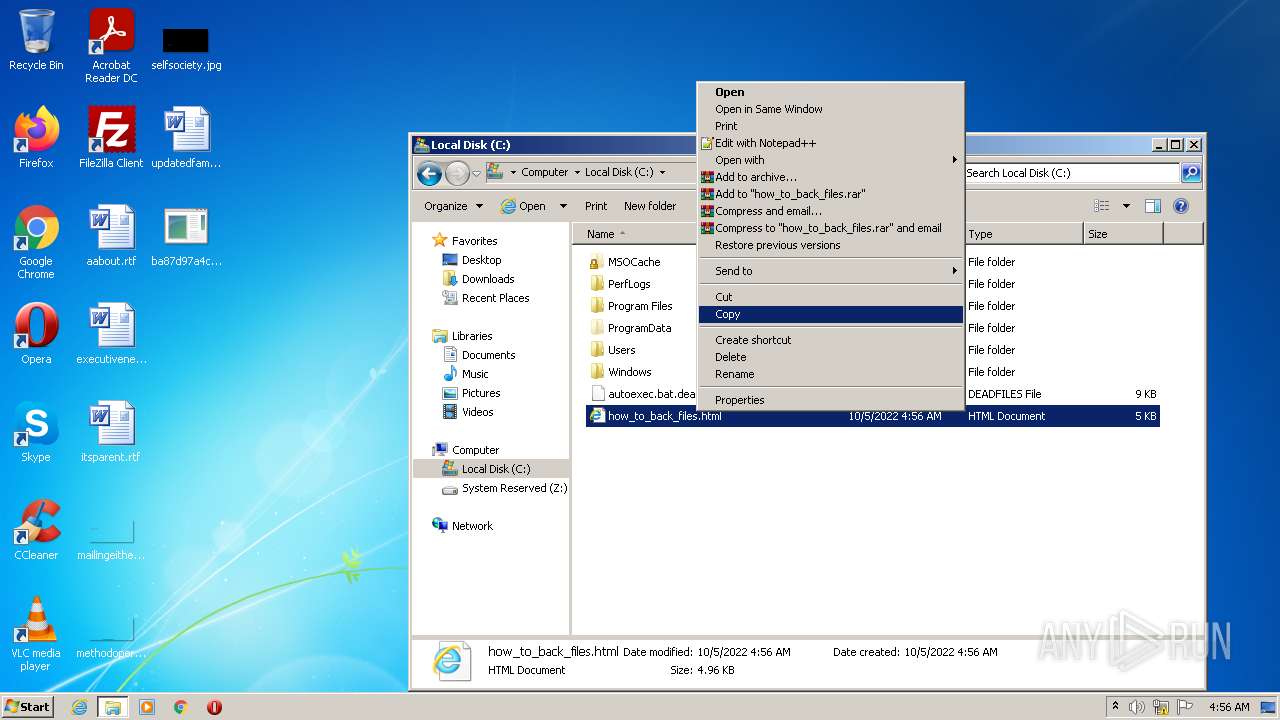
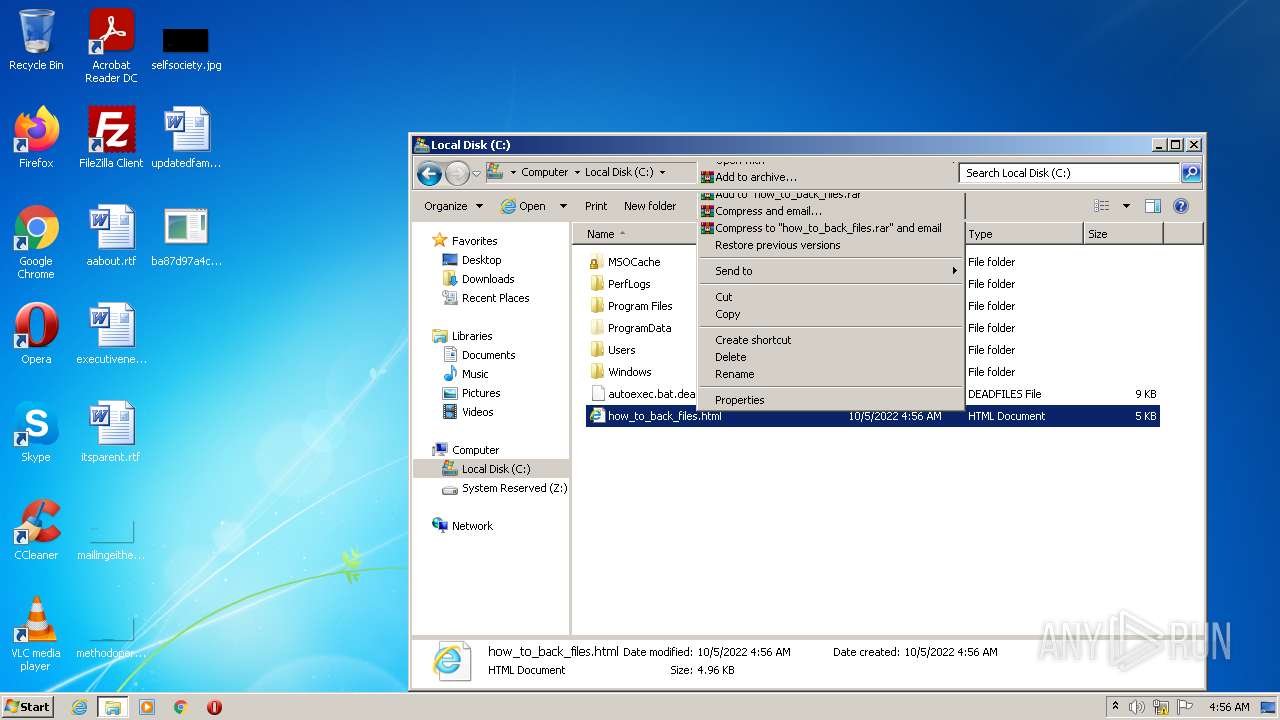
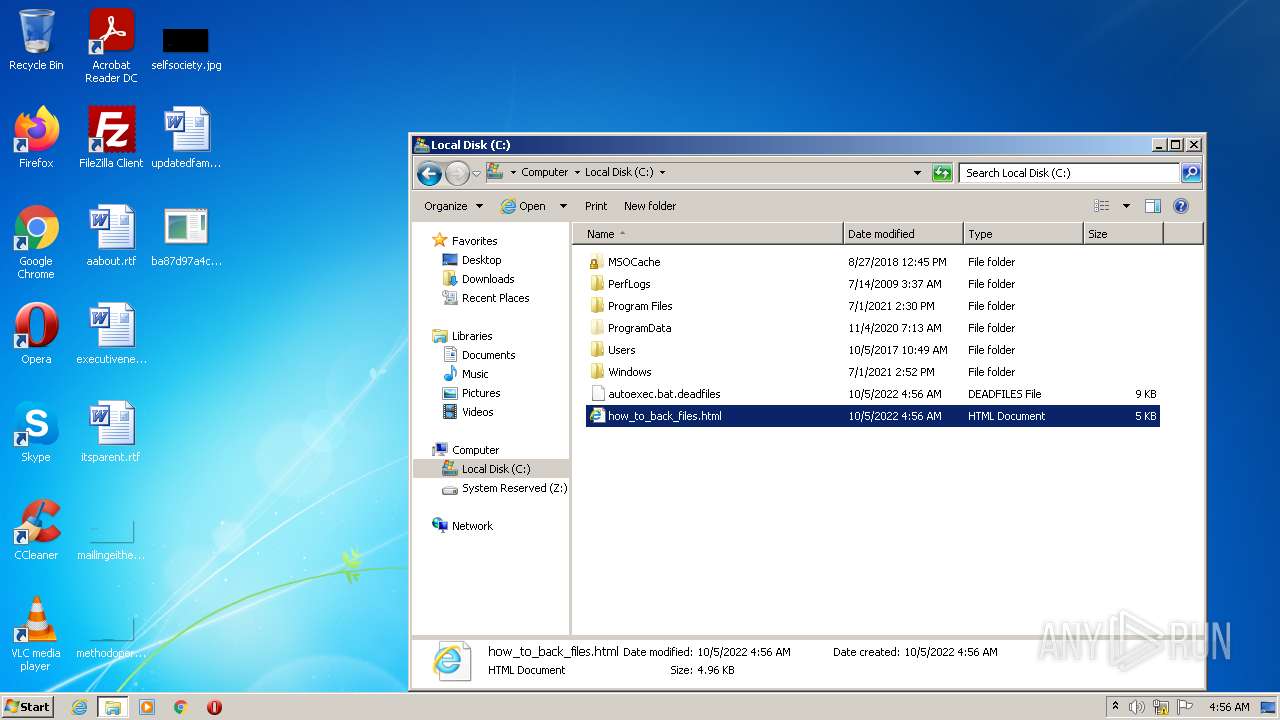
Creates files in the user directory
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Reads the computer name
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 684)
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Creates files in the Windows directory
- wbadmin.exe (PID: 3880)
- wbadmin.exe (PID: 2316)
- wbadmin.exe (PID: 1532)
- wbadmin.exe (PID: 2448)
- wbadmin.exe (PID: 3820)
- wbadmin.exe (PID: 2620)
Removes files from Windows directory
- wbadmin.exe (PID: 2448)
- wbadmin.exe (PID: 3820)
- wbadmin.exe (PID: 2620)
Writes to a desktop.ini file (may be used to cloak folders)
- ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe (PID: 1784)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3760)
Executed via Task Scheduler
- svhost.exe (PID: 3380)
INFO
Reads the computer name
- DllHost.exe (PID: 4072)
- vssadmin.exe (PID: 2436)
- vssvc.exe (PID: 2896)
- wbadmin.exe (PID: 2316)
- wbadmin.exe (PID: 3880)
- wbadmin.exe (PID: 1532)
- wmic.exe (PID: 3956)
- wbadmin.exe (PID: 2448)
- vssadmin.exe (PID: 2564)
- wmic.exe (PID: 1252)
- vssadmin.exe (PID: 4004)
- wbadmin.exe (PID: 3820)
- wbadmin.exe (PID: 2620)
- wmic.exe (PID: 760)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 1944)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 2032)
Checks supported languages
- DllHost.exe (PID: 4072)
- vssadmin.exe (PID: 2436)
- bcdedit.exe (PID: 2348)
- bcdedit.exe (PID: 3604)
- wmic.exe (PID: 3956)
- vssadmin.exe (PID: 2564)
- bcdedit.exe (PID: 3036)
- wbadmin.exe (PID: 1532)
- vssvc.exe (PID: 2896)
- wbadmin.exe (PID: 2448)
- wbadmin.exe (PID: 2316)
- wbadmin.exe (PID: 3880)
- wmic.exe (PID: 1252)
- vssadmin.exe (PID: 4004)
- bcdedit.exe (PID: 2940)
- bcdedit.exe (PID: 3536)
- bcdedit.exe (PID: 888)
- wbadmin.exe (PID: 3820)
- wbadmin.exe (PID: 2620)
- chrome.exe (PID: 3760)
- wmic.exe (PID: 760)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 1744)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3832)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 1944)
- chrome.exe (PID: 2460)
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3528)
- chrome.exe (PID: 3764)
- chrome.exe (PID: 2032)
- chrome.exe (PID: 3900)
- chrome.exe (PID: 3496)
- chrome.exe (PID: 1112)
Manual execution by user
- chrome.exe (PID: 3760)
Application launched itself
- chrome.exe (PID: 3760)
Reads the hosts file
- chrome.exe (PID: 3760)
- chrome.exe (PID: 1744)
Reads settings of System Certificates
- chrome.exe (PID: 1744)
Reads the date of Windows installation
- chrome.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2019-Oct-31 06:08:40 |
| Detected languages: |
|
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 272 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2019-Oct-31 06:08:40 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 469942 | 470016 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54453 |
.rdata | 475136 | 175538 | 175616 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.69449 |
.data | 651264 | 19304 | 14848 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.77903 |
.rsrc | 671744 | 480 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.70824 |
.reloc | 675840 | 23164 | 23552 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56882 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
CRYPT32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
NETAPI32.dll |
OLEAUT32.dll |
RstrtMgr.DLL |
SHELL32.dll |
WS2_32.dll |
Total processes
99
Monitored processes
40
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Users\admin\Desktop\ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe" | C:\Users\admin\Desktop\ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 760 | wmic.exe SHADOWCOPY /nointeractive | C:\Windows\System32\Wbem\wmic.exe | — | ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 44124 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,2616629767361109863,14462432438756204733,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1252 | wmic.exe SHADOWCOPY /nointeractive | C:\Windows\System32\Wbem\wmic.exe | — | ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 44124 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | wbadmin DELETE SYSTEMSTATEBACKUP | C:\Windows\system32\wbadmin.exe | — | ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 4294967293 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1024,2616629767361109863,14462432438756204733,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1320 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1784 | "C:\Users\admin\Desktop\ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe" | C:\Users\admin\Desktop\ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | — | DllHost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1024,2616629767361109863,14462432438756204733,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1024,2616629767361109863,14462432438756204733,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
25 729
Read events
18 735
Write events
3 561
Delete events
3 433
Modification events
| (PID) Process: | (4072) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4072) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4072) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4072) DllHost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1784) ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (1784) ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (1784) ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | Key: | HKEY_CURRENT_USER\Software\MDSLK |
| Operation: | write | Name: | Self |
Value: ba87d97a4c7dec4e2eef997190f5f875c8564395bf3c95bd95055f447c495387.exe | |||
| (PID) Process: | (2348) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
| (PID) Process: | (3604) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\250000e0 |
| Operation: | write | Name: | Element |
Value: 0100000000000000 | |||
| (PID) Process: | (2940) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
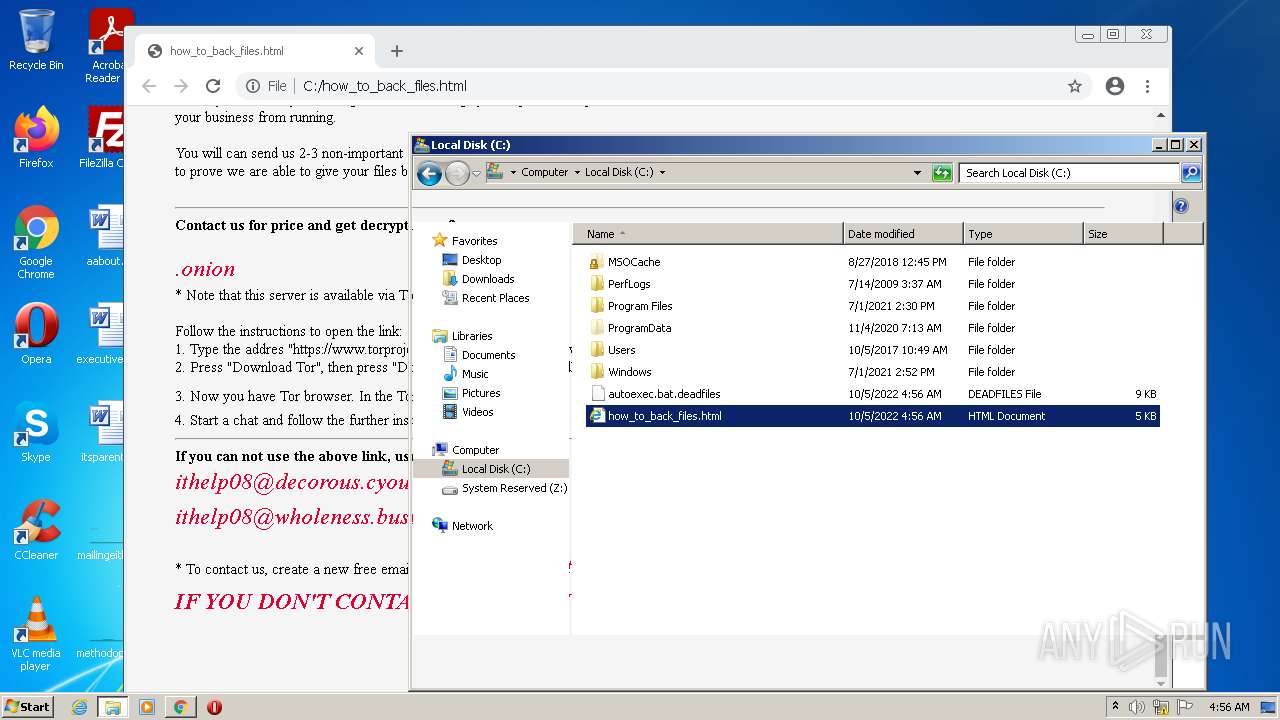
Executable files
1
Suspicious files
944
Text files
250
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.1.etl | etl | |
MD5:— | SHA256:— | |||
| 2316 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.2.etl | etl | |
MD5:— | SHA256:— | |||
| 2316 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.1.etl | etl | |
MD5:— | SHA256:— | |||
| 1532 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.3.etl | etl | |
MD5:— | SHA256:— | |||
| 2448 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.3.etl | etl | |
MD5:— | SHA256:— | |||
| 2448 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.1.etl | etl | |
MD5:— | SHA256:— | |||
| 2448 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.2.etl | etl | |
MD5:— | SHA256:— | |||
| 3820 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.2.etl | etl | |
MD5:— | SHA256:— | |||
| 2620 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.3.etl | etl | |
MD5:— | SHA256:— | |||
| 3820 | wbadmin.exe | C:\Windows\Logs\WindowsBackup\Wbadmin.1.etl | etl | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
20
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 7.06 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 178 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 19.9 Kb | whitelisted |
1744 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.6 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.2:139 | — | — | — | whitelisted |
1744 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 216.58.212.141:443 | accounts.google.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.185.225:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 172.217.169.163:443 | update.googleapis.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
924 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.187.142:443 | clients1.google.com | GOOGLE | US | whitelisted |
1744 | chrome.exe | 142.250.187.131:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |