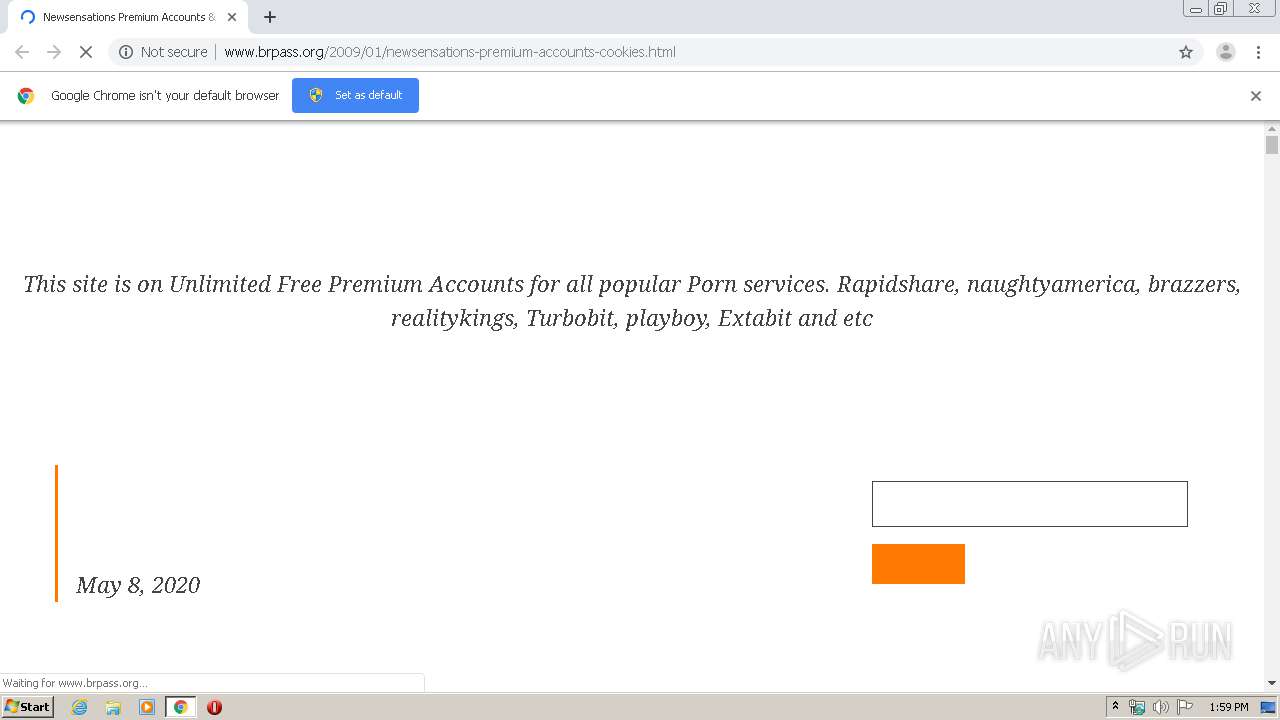
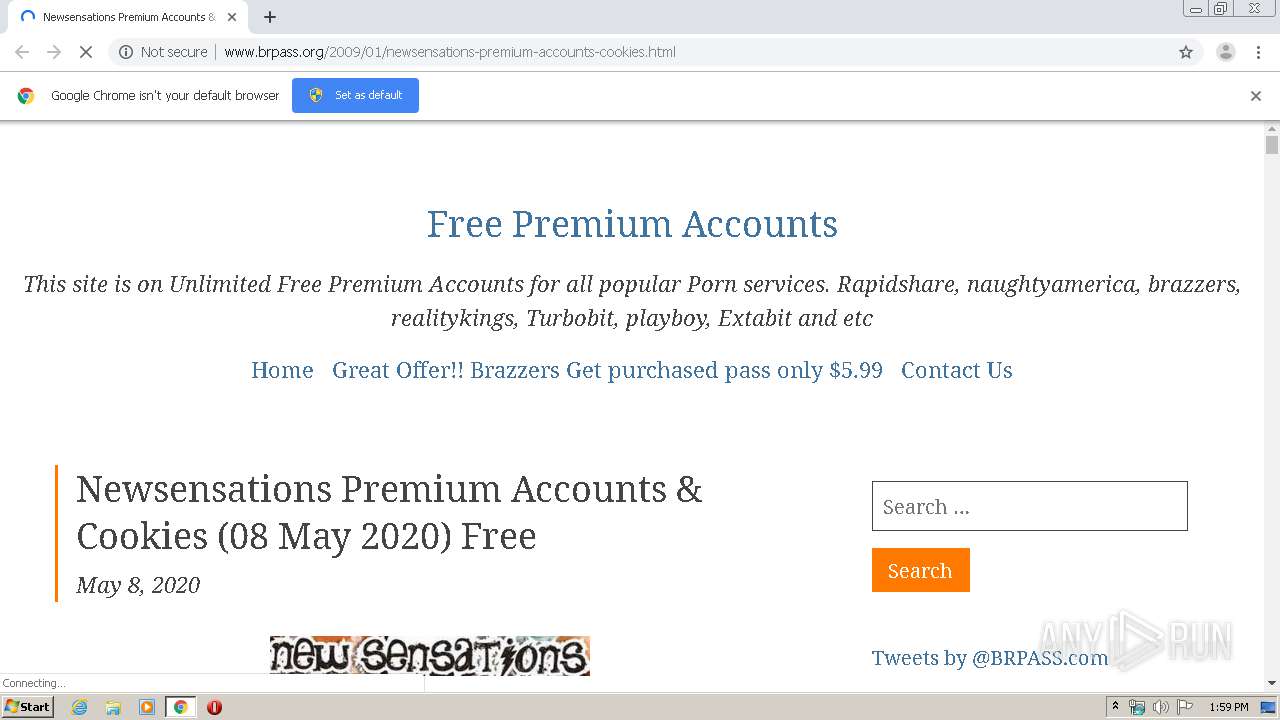
| URL: | http://www.brpass.org/2009/01/newsensations-premium-accounts-cookies.html |
| Full analysis: | https://app.any.run/tasks/99212bd7-64bc-4997-8b9d-9fcc0160f660 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2020, 12:58:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 03B93679573A18A3B6E81662A86B99AE |
| SHA1: | 435087D8EA9F5CDD771B364D2779F10A96920CDB |
| SHA256: | BA6688C0066761CBDA6010360636532F4EF3AD1CE3982F588F83D7EF3E0DF317 |
| SSDEEP: | 3:N1KJS43VUMJXVUVlAiERMKpI5R/9GRjzLD0n:Cc4lbZSlZBKpIz9GRrQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1412)
INFO
Dropped object may contain TOR URL's
- chrome.exe (PID: 1412)
Reads the hosts file
- chrome.exe (PID: 1412)
- chrome.exe (PID: 3000)
Application launched itself
- chrome.exe (PID: 1412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
47
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15898450332739366609 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3516 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4185495249302008159 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3800 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1250570513792134650 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7007245613739827983 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 740 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10433342801902161916 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15114403596475662027 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3068 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8800902454645614173 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.brpass.org/2009/01/newsensations-premium-accounts-cookies.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15498186352960867033 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,17689000770166808011,13942274540139673873,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4999087093527635785 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
623
Read events
517
Write events
101
Delete events
5
Modification events
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1412-13233589148486375 |
Value: 259 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1412) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
137
Text files
207
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EB7FA9C-584.pma | — | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2f1f5d65-a518-41be-94a7-1da60b986cfb.tmp | — | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa873f6.TMP | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa873d7.TMP | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa87454.TMP | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa87609.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
125
DNS requests
87
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3000 | chrome.exe | GET | — | 139.99.8.234:80 | http://www.brpass.org/wp-content/uploads/2014/06/newsensations_com_Premium_Accounts_Free.jpg | SG | — | — | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/themes/rindby/css/rindby.css | SG | text | 5.12 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/2009/01/newsensations-premium-accounts-cookies.html | SG | html | 9.89 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/uploads/WSwRbZwrbtZT/zJWrIlmGXzFc.js?ver=2.2.3 | SG | text | 6.06 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/uploads/WSwRbZwrbtZT/oynAoSTXZyhz.css?ver=2.2.3 | SG | text | 1010 b | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/themes/rindby/assets/fonts/notoserif-italic-latin-subset.woff2 | SG | woff2 | 33.3 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 151.139.128.10:80 | http://cdn.popcash.net/pop.js | US | text | 35.8 Kb | whitelisted |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/themes/rindby/assets/fonts/notoserif-regular-latin-subset.woff2 | SG | woff2 | 31.9 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-content/themes/rindby/assets/fonts/notoserif-bold-latin-subset.woff2 | SG | woff2 | 32.9 Kb | suspicious |
3000 | chrome.exe | GET | 200 | 139.99.8.234:80 | http://www.brpass.org/wp-includes/css/dist/block-library/style.min.css?ver=5.2.6 | SG | text | 4.65 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 139.99.8.234:80 | www.brpass.org | OVH SAS | SG | suspicious |
3000 | chrome.exe | 172.217.22.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 151.139.128.10:80 | cdn.popcash.net | Highwinds Network Group, Inc. | US | malicious |
3000 | chrome.exe | 216.58.212.129:80 | 3.bp.blogspot.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 104.20.82.199:443 | cdn.adf.ly | Cloudflare Inc | US | unknown |
3000 | chrome.exe | 35.190.90.202:443 | steadfastsystem.com | Google Inc. | US | unknown |
3000 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
3000 | chrome.exe | 192.229.233.25:80 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3000 | chrome.exe | 185.60.216.19:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.brpass.org |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
3.bp.blogspot.com |
| whitelisted |
s.w.org |
| whitelisted |
cdn.adf.ly |
| whitelisted |
cdn.popcash.net |
| whitelisted |
sh.st |
| unknown |
twitter.com |
| whitelisted |
whareotiv.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
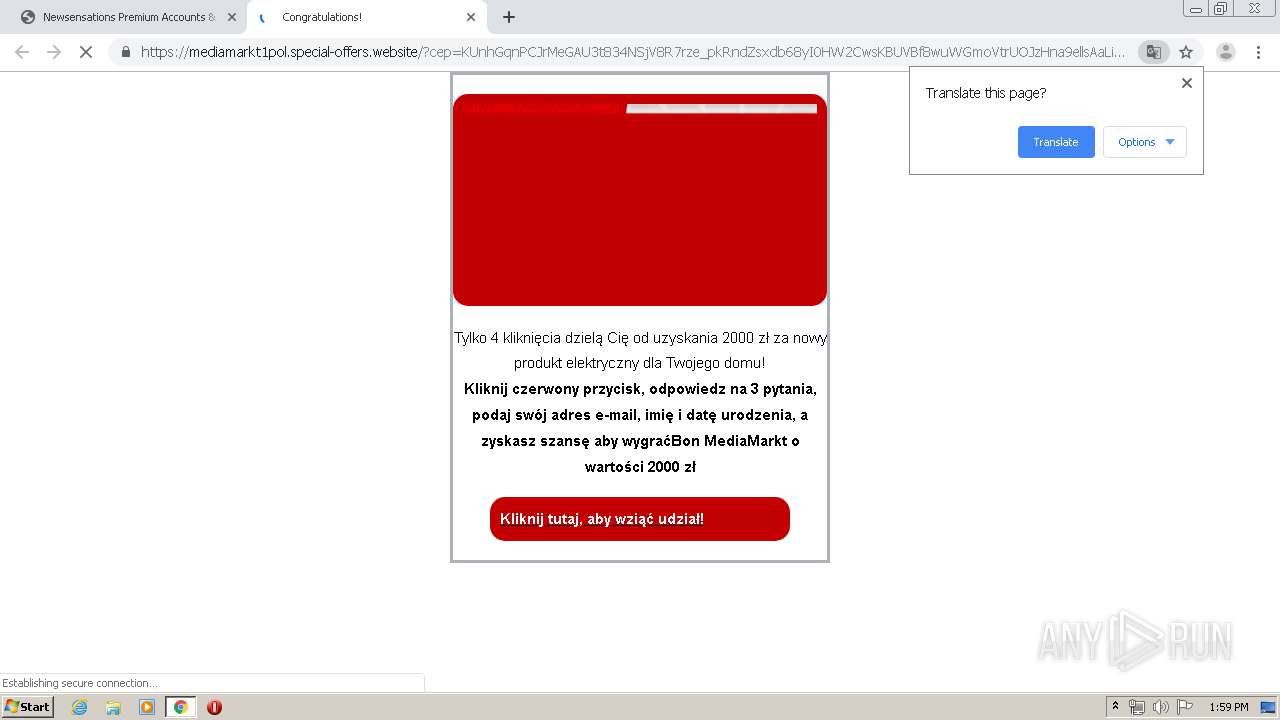
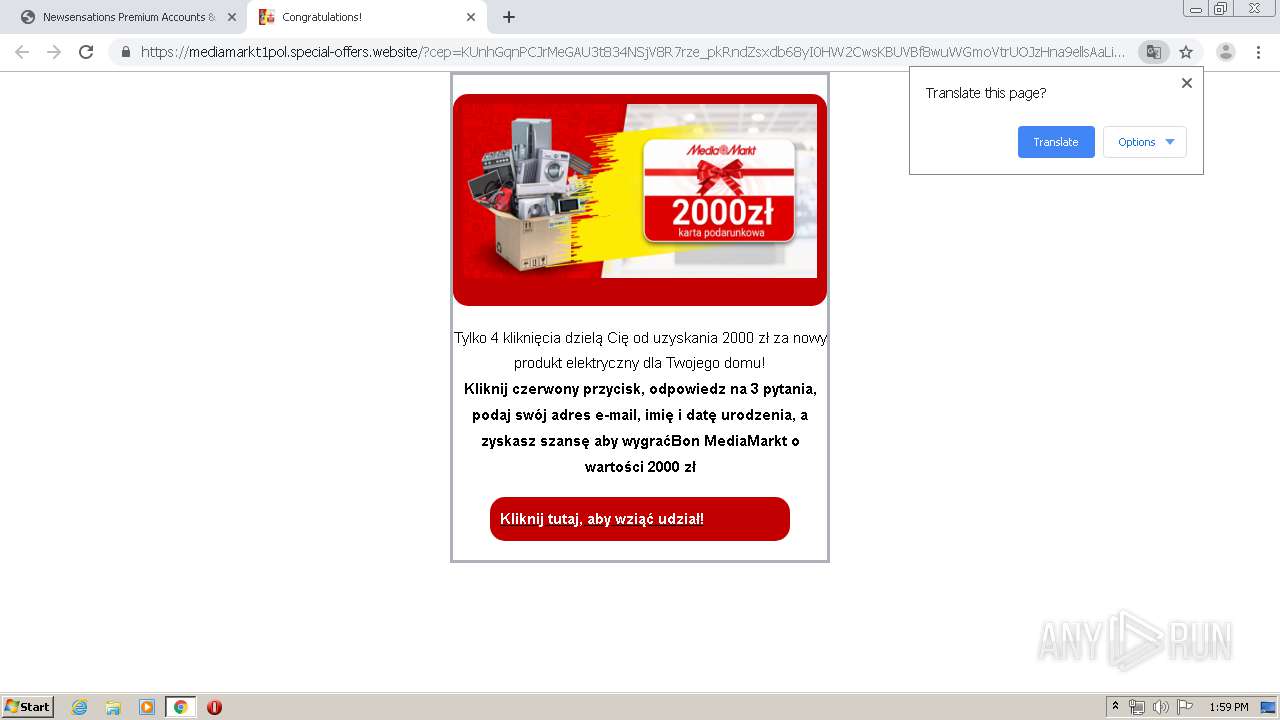
3000 | chrome.exe | Potential Corporate Privacy Violation | ET INFO Suspicious Darkwave Popads Pop Under Redirect |
3000 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3000 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3000 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
3000 | chrome.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.icu) |