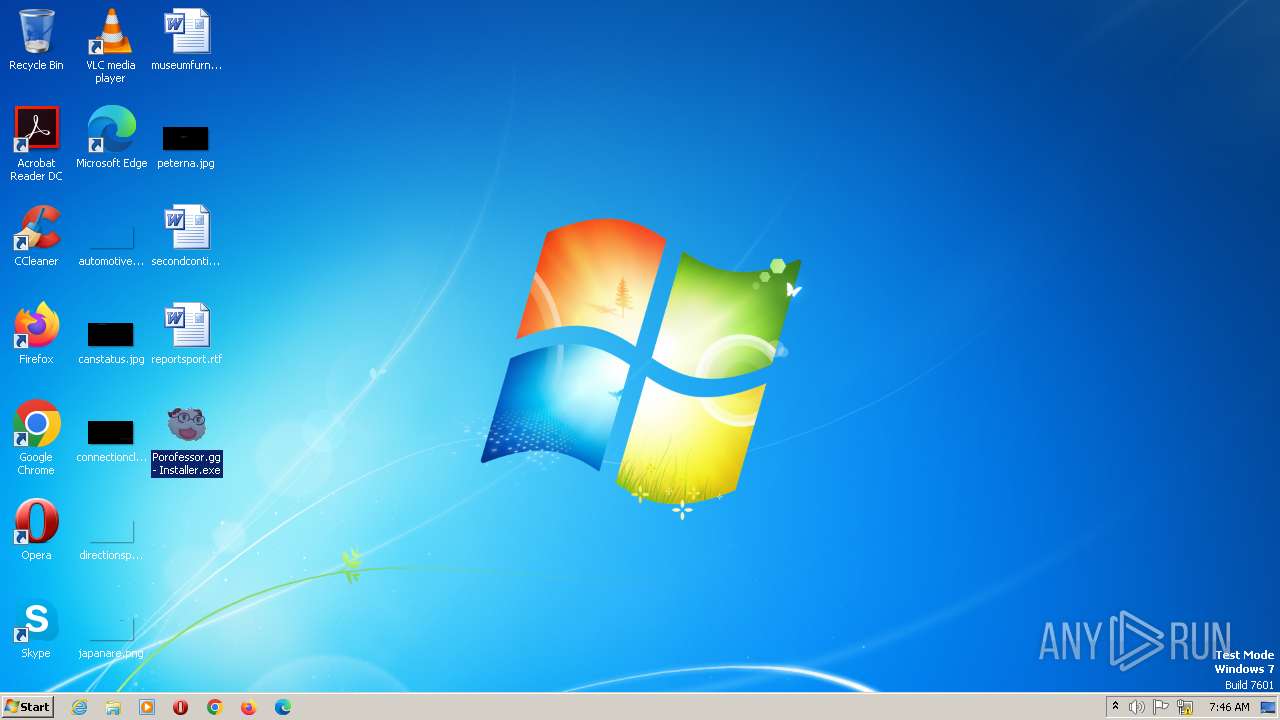
| File name: | Porofessor.gg - Installer.exe |
| Full analysis: | https://app.any.run/tasks/aec99557-fe70-4e52-80e3-6d63d4751a24 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2023, 07:45:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0C2AE78FF797A680DE2EC6390751769D |
| SHA1: | 2BAC01C43B583585A51CCB2A3B84AB7760A3117E |
| SHA256: | BA6627BA1BAAF964CE46A44B87D06A3ADB99048F9D11E1CF9829BFD33217CB91 |
| SSDEEP: | 49152:KUl37xE87vxpsrFpIvCymzTpRfGsjYkjoRUcRU:KQlPN+TIv6DfGxjCR |
MALICIOUS
Loads dropped or rewritten executable
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Setup.exe (PID: 320)
- Porofessor.gg - Installer.exe (PID: 2960)
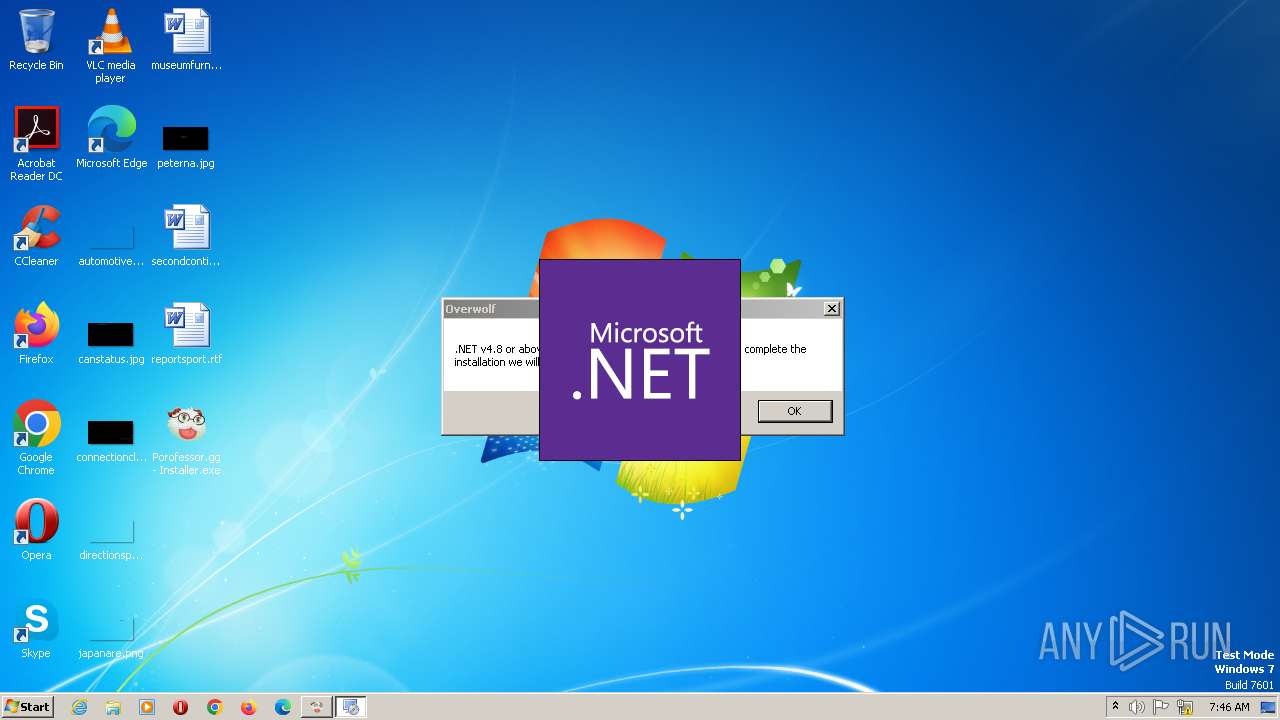
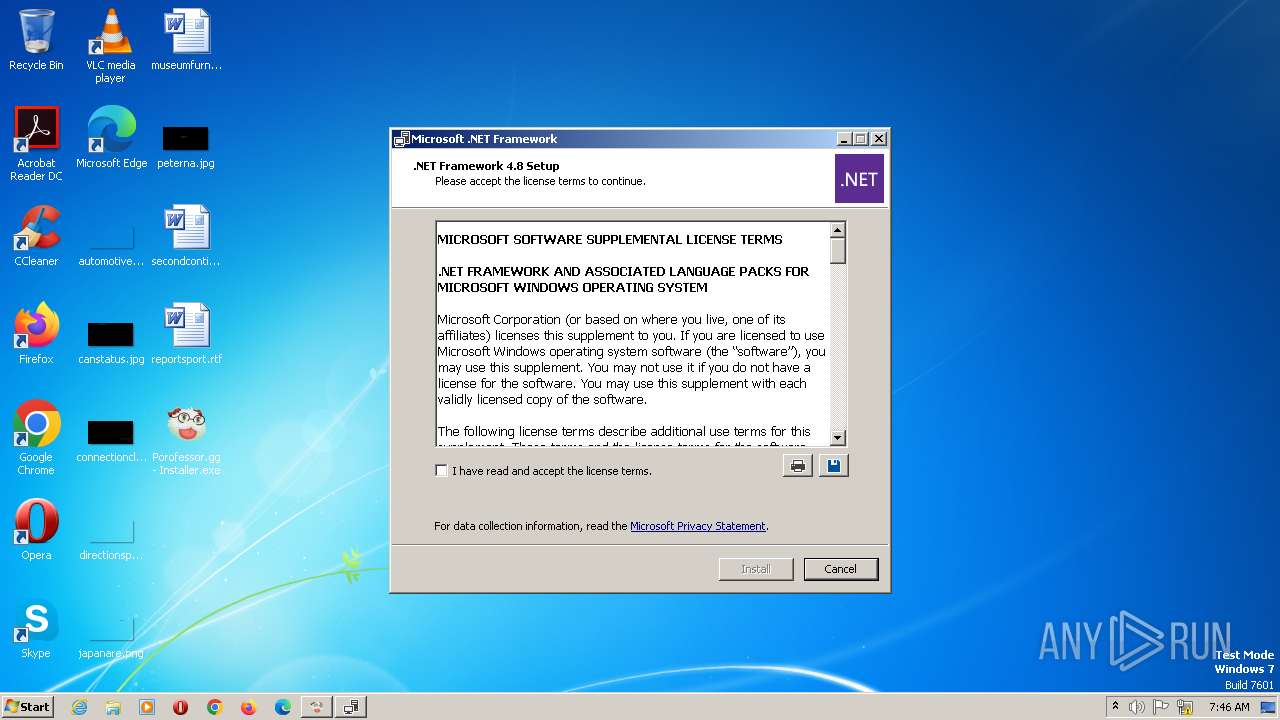
Application was dropped or rewritten from another process
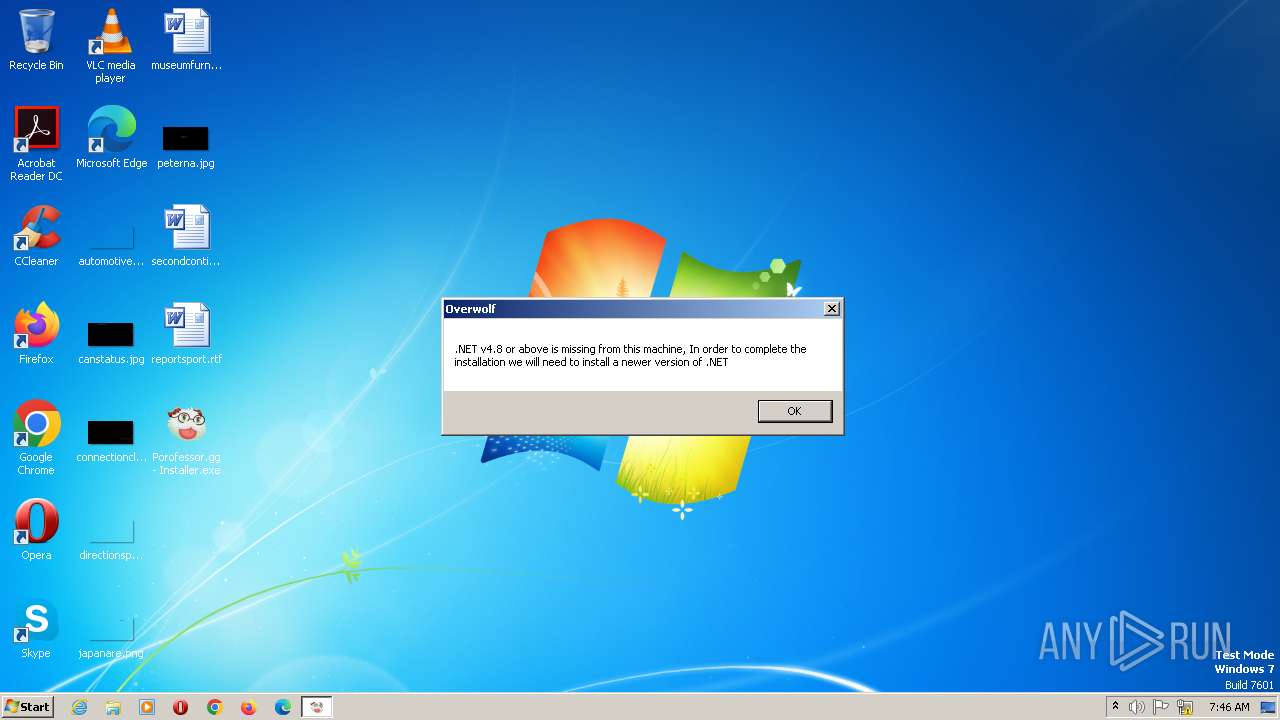
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
SUSPICIOUS
Executable content was dropped or overwritten
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
Application launched itself
- Porofessor.gg - Installer.exe (PID: 664)
The process creates files with name similar to system file names
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
Reads the Internet Settings
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
Reads settings of System Certificates
- Porofessor.gg - Installer.exe (PID: 2960)
Reads security settings of Internet Explorer
- Porofessor.gg - Installer.exe (PID: 2960)
Checks Windows Trust Settings
- Porofessor.gg - Installer.exe (PID: 2960)
INFO
Checks supported languages
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
The process checks LSA protection
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
Reads the computer name
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
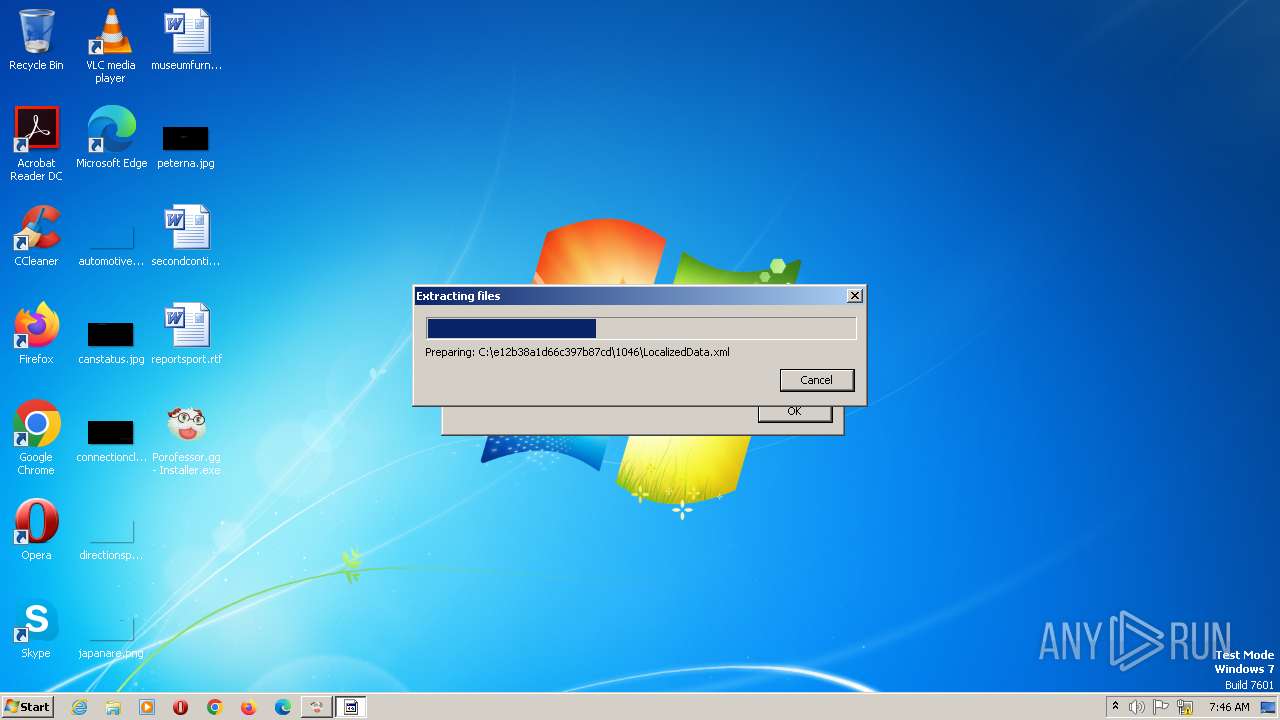
Create files in a temporary directory
- Porofessor.gg - Installer.exe (PID: 664)
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
Checks proxy server information
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
Reads the machine GUID from the registry
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- ndp48-web.exe (PID: 3036)
- Setup.exe (PID: 320)
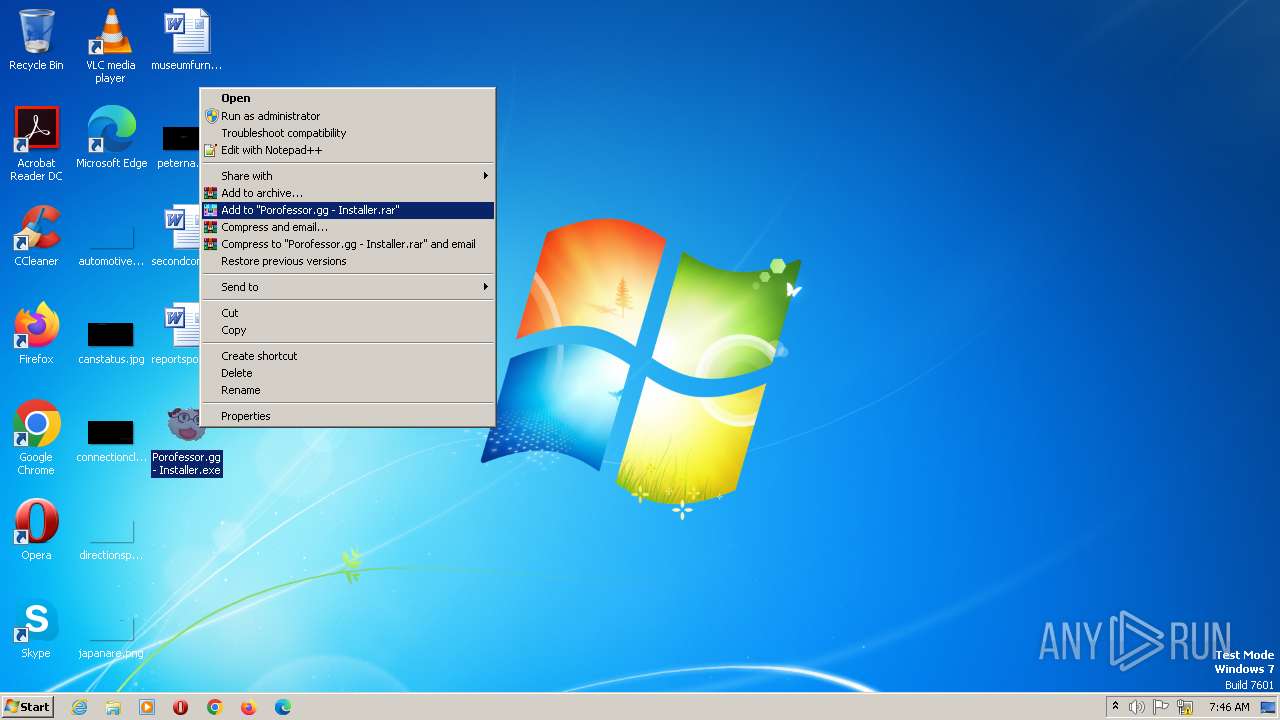
Manual execution by a user
- Porofessor.gg - Installer.exe (PID: 2960)
Creates files or folders in the user directory
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
Reads Environment values
- Porofessor.gg - Installer.exe (PID: 2396)
- Porofessor.gg - Installer.exe (PID: 2960)
- Setup.exe (PID: 320)
Reads CPU info
- Setup.exe (PID: 320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 2.225.0.2 |
|---|---|
| ProductName: | Porofessor |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| FileVersion: | 2.225.0.2 |
| FileDescription: | Porofessor |
| CompanyName: | Overwolf Ltd. |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.225.0.2 |
| FileVersionNumber: | 2.225.0.2 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x352d |
| UninitializedDataSize: | 2048 |
| InitializedDataSize: | 186880 |
| CodeSize: | 27136 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2021:09:25 21:57:46+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2021 21:57:46 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Overwolf Ltd. |
| FileDescription: | Porofessor |
| FileVersion: | 2.225.0.2 |
| LegalCopyright: | Copyright (C) 2021 Overwolf Ltd. All Rights Reserved. |
| LegalTrademarks: | - |
| ProductName: | Porofessor |
| ProductVersion: | 2.225.0.2 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Sep-2021 21:57:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006897 | 0x00006A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4584 |
.rdata | 0x00008000 | 0x000014A6 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02411 |
.data | 0x0000A000 | 0x0002B018 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15458 |
.ndata | 0x00036000 | 0x0001F000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00055000 | 0x00046620 | 0x00046800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58208 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29934 | 830 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.99306 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.17146 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.32691 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.43192 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
5
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | C:\e12b38a1d66c397b87cd\\Setup.exe /norestart /x86 /x64 /web | C:\e12b38a1d66c397b87cd\Setup.exe | — | ndp48-web.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 664 | "C:\Users\admin\Desktop\Porofessor.gg - Installer.exe" | C:\Users\admin\Desktop\Porofessor.gg - Installer.exe | explorer.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: MEDIUM Description: Porofessor Exit code: 0 Version: 2.225.0.2 Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\Desktop\Porofessor.gg - Installer.exe" /UAC:3017A /NCRC | C:\Users\admin\Desktop\Porofessor.gg - Installer.exe | Porofessor.gg - Installer.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: HIGH Description: Porofessor Exit code: 0 Version: 2.225.0.2 Modules
| |||||||||||||||
| 2960 | "C:\Users\admin\Desktop\Porofessor.gg - Installer.exe" | C:\Users\admin\Desktop\Porofessor.gg - Installer.exe | explorer.exe | ||||||||||||
User: admin Company: Overwolf Ltd. Integrity Level: HIGH Description: Porofessor Exit code: 0 Version: 2.225.0.2 Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Local\Temp\nst9EC.tmp\ndp48-web.exe" /norestart | C:\Users\admin\AppData\Local\Temp\nst9EC.tmp\ndp48-web.exe | Porofessor.gg - Installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Setup Exit code: 0 Version: 4.8.04115.00 Modules
| |||||||||||||||
Total events
2 217
Read events
2 186
Write events
31
Delete events
0
Modification events
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000096000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2396) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2960) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2960) Porofessor.gg - Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000097000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
79
Suspicious files
51
Text files
251
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\log4net.dll | executable | |
MD5:F15C8A9E2876568B3910189B2D493706 | SHA256:AE9C8073C3357C490F5D1C64101362918357C568F6B9380A60B09A4A4C1FF309 | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\System.dll | executable | |
MD5:7399323923E3946FE9140132AC388132 | SHA256:5A1C20A3E2E2EB182976977669F2C5D9F3104477E98F74D69D2434E79B92FDC3 | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\uac.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\DotNetZip.dll | executable | |
MD5:190E712F2E3B065BA3D5F63CB9B7725E | SHA256:6C512D9943A225D686B26FC832589E4C8BEF7C4DD0A8BDFD557D5D27FE5BBA0F | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\OWInstaller.exe | executable | |
MD5:BE911333A79A500745DDEA328B0DC241 | SHA256:B82DAF8066C12933C8CC6E651A23E6CCA29D7DD8FB77B86AF9A7F6EBEBD7C455 | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\Microsoft.Win32.TaskScheduler.dll | executable | |
MD5:2C2649A25231C63ECBE3A6211559DD10 | SHA256:E9610ACFD892A37D2B0BE32BAAC8DDD4C50F5BF55E2A3A8AB97B07E6735F969B | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\CommandLine.dll | executable | |
MD5:064D615E82FB1762CF530787AD3E66F6 | SHA256:01289017A6F057925189E4A1B1D4D5B5929188E2A64CF27A8CBAF25339DEF75B | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\UserInfo.dll | executable | |
MD5:9301577FF4D229347FE33259B43EF3B2 | SHA256:090C4BC8DC534E97B3877BD5115EB58B3E181495F29F231479F540BAB5C01EDC | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\SharpRaven.dll | executable | |
MD5:1B35C00148BFB50C60707D5FFA647638 | SHA256:4858FB3BDFE6EC2F6A7A15C0C62D595DDA56988B50F9A703B284FF660DFA256F | |||
| 664 | Porofessor.gg - Installer.exe | C:\Users\admin\AppData\Local\Temp\nsrD242.tmp\nsis7z.dll | executable | |
MD5:C2FF16FA8503AA6CEBE37B1F16F9AD74 | SHA256:76CA8B22934AC8FE7F492BF0A2F4B1FEE5147A649C1706DA44BA3E0BE6D4A751 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
5
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2396 | Porofessor.gg - Installer.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?Name=installer_uac_action&Value=1&&Extra=%5b%7b%22Name%22%3a%22installer_version%22%2c%22Value%22%3a%222.225.0.2%22%7d%5d | US | text | 2 b | malicious |
2960 | Porofessor.gg - Installer.exe | GET | 200 | 69.16.175.42:80 | http://analyticsnew.overwolf.com/analytics/Counter?Name=installer_uac_action&Value=1&&Extra=%5b%7b%22Name%22%3a%22installer_version%22%2c%22Value%22%3a%222.225.0.2%22%7d%5d | US | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
328 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2396 | Porofessor.gg - Installer.exe | 69.16.175.42:80 | analyticsnew.overwolf.com | STACKPATH-CDN | US | malicious |
2960 | Porofessor.gg - Installer.exe | 69.16.175.42:80 | analyticsnew.overwolf.com | STACKPATH-CDN | US | malicious |
2960 | Porofessor.gg - Installer.exe | 68.232.34.200:443 | download.visualstudio.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
analyticsnew.overwolf.com |
| malicious |
download.visualstudio.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2960 | Porofessor.gg - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2396 | Porofessor.gg - Installer.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |