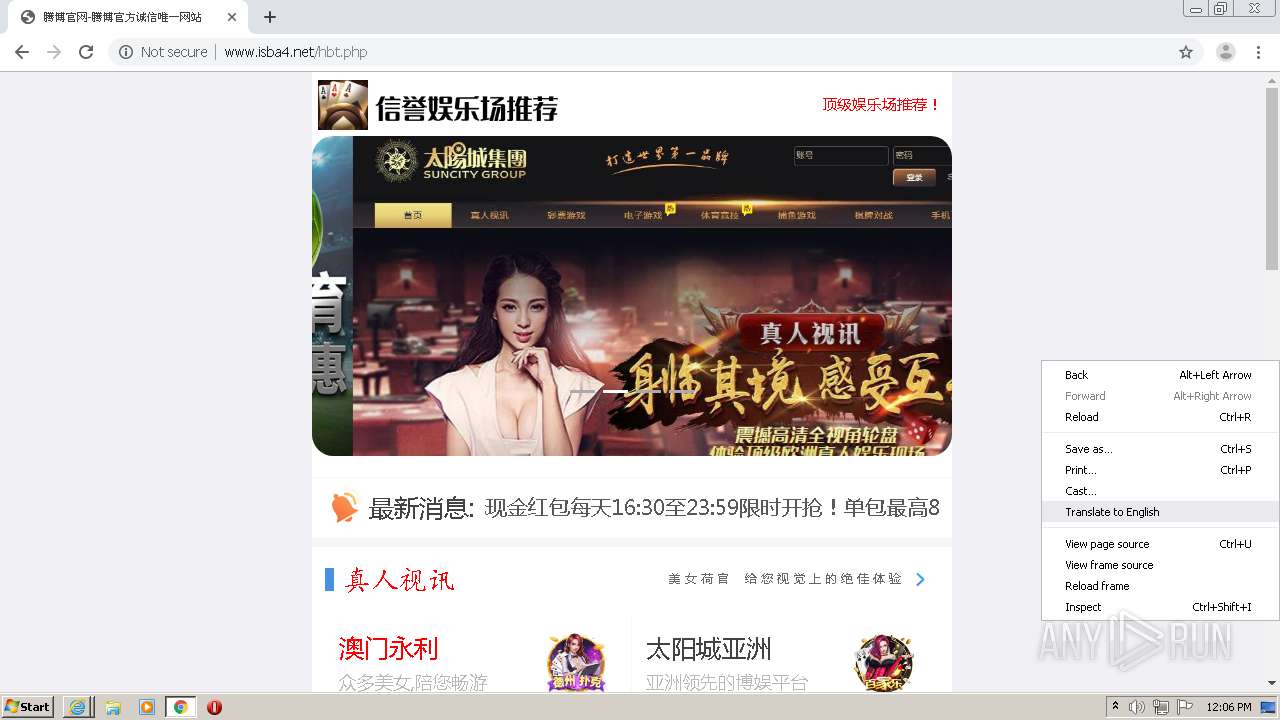
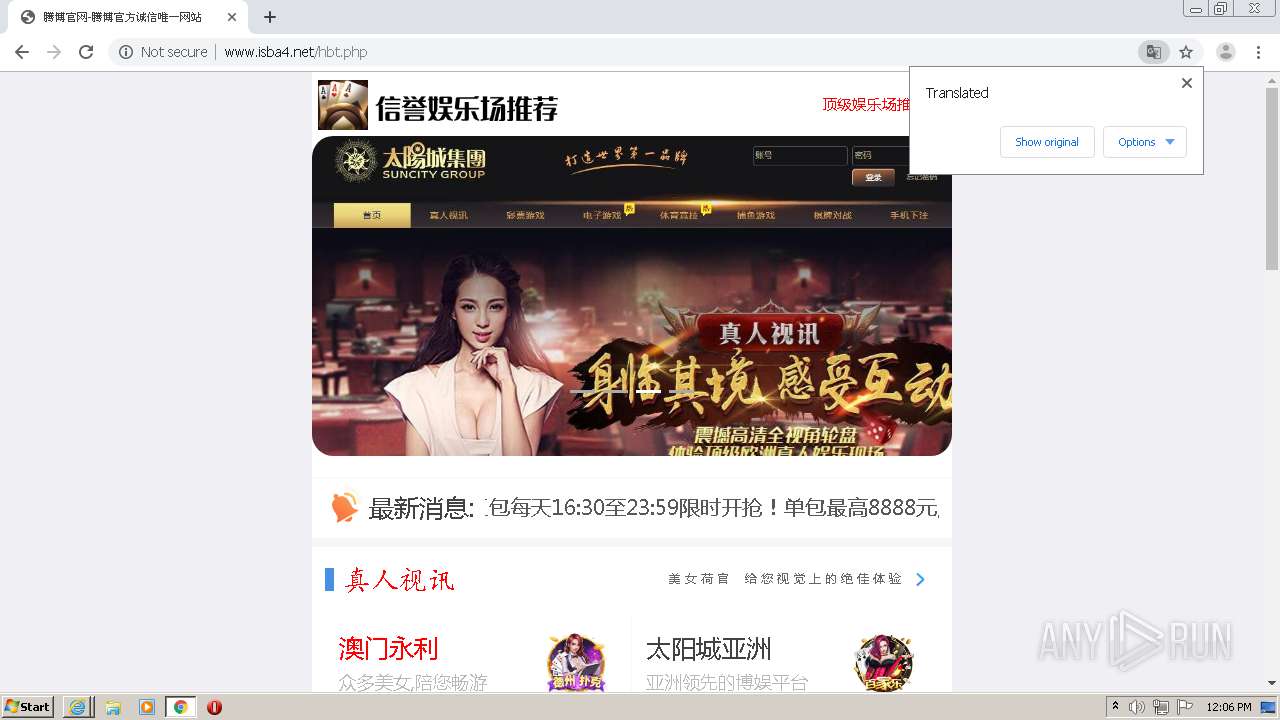
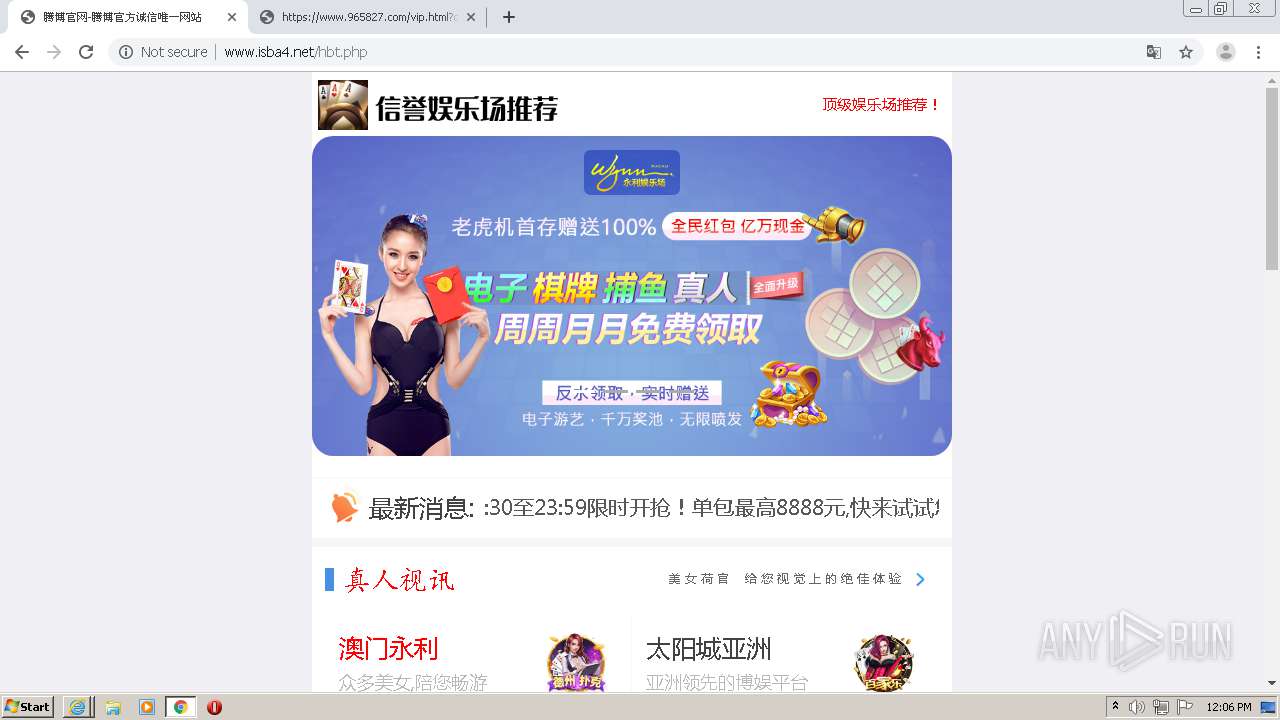
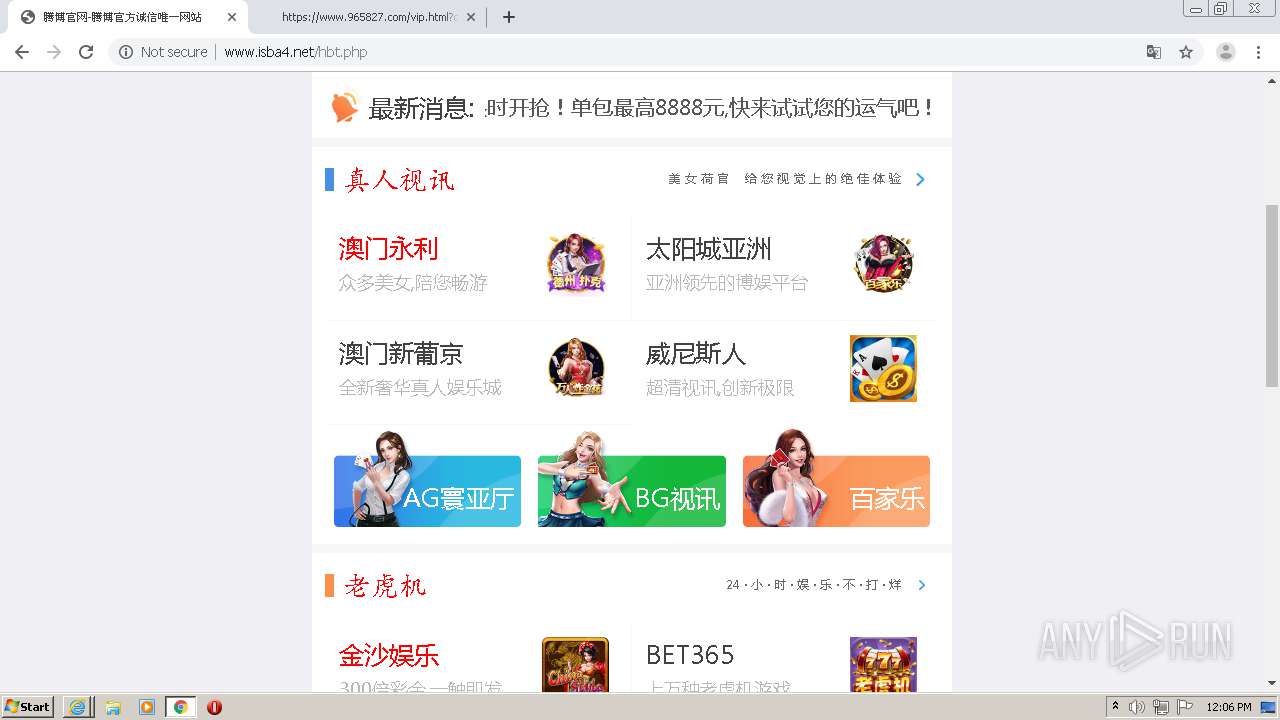
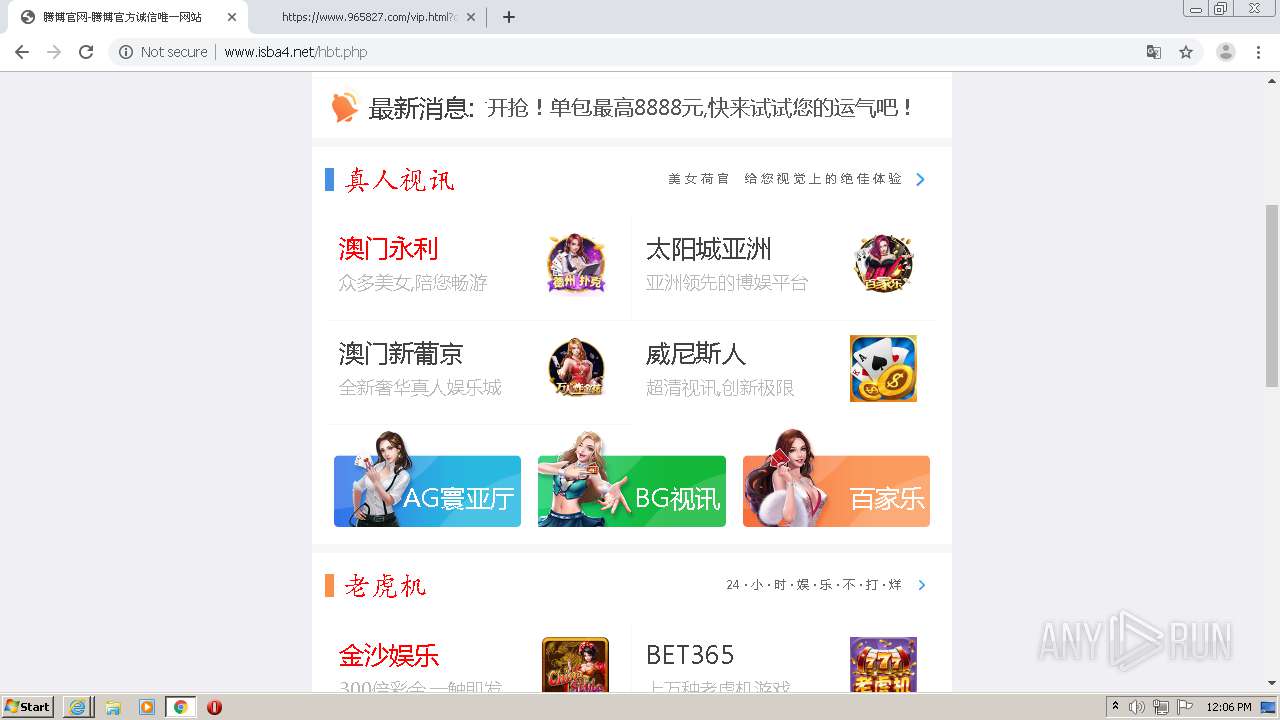
| URL: | http://www.isba4.net/hbt.php |
| Full analysis: | https://app.any.run/tasks/73f6be63-d87a-49c9-b313-ca4f1db91e69 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 11:05:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5A1541F8C9AFB7E1045D03B46F06C9B3 |
| SHA1: | 6C7C6F2AA7F4220B07A074423FEF421BAD6A8042 |
| SHA256: | BA63AA1513409A2FC2589CAE9EB7F2A1081AA9F629B7014F80D31E79BE23580C |
| SSDEEP: | 3:N1KJS42HRLV:Cc4+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3716)
Changes internet zones settings
- iexplore.exe (PID: 3848)
Application launched itself
- iexplore.exe (PID: 3848)
- chrome.exe (PID: 3608)
Reads internet explorer settings
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3716)
Manual execution by user
- chrome.exe (PID: 3608)
Reads the hosts file
- chrome.exe (PID: 3608)
- chrome.exe (PID: 3232)
Reads settings of System Certificates
- chrome.exe (PID: 3232)
- iexplore.exe (PID: 3716)
- iexplore.exe (PID: 3848)
Creates files in the user directory
- iexplore.exe (PID: 3940)
- iexplore.exe (PID: 3716)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3848)
Changes settings of System certificates
- iexplore.exe (PID: 3848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2776 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=287698102582368761 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2624819310024481152 --mojo-platform-channel-handle=3604 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16669577663028097055 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8208525178067092413 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4104272472173081897 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f0da9d0,0x6f0da9e0,0x6f0da9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8675060465493813480 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3500 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=333039475297946608 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,7416824622839742010,13677897791733730200,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3818072758706898713 --mojo-platform-channel-handle=3316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 004
Read events
783
Write events
214
Delete events
7
Modification events
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2831842604 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30840601 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
117
Text files
289
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabDF54.tmp | — | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarDF55.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F746681-E18.pma | — | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\jquery.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\tj[1].js | html | |
MD5:— | SHA256:— | |||
| 3940 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BD5208ADDEC1165FD57AF2BF2F455EAA_122109DC1B817B623370C1AE58AD2245 | binary | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bfea4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
57
TCP/UDP connections
163
DNS requests
85
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3940 | iexplore.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=20869605&rt=1601463930285&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599(www.isba4.net)%25E5%25BF%2583%25E5%2585%25A8%25E6%2584%258F%25E6%2589%2593%25E9%2580%25A0&ing=1&ekc=&sid=1601463930285&tt=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591-%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&kw=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591%25E8%25AF%259A%25E4%25BF%25A1%25E4%25BF%25A1%25E6%259C%25AC%252C%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&cu=http%253A%252F%252Fwww.isba4.net%252Fhbt.php&pu= | CN | — | — | whitelisted |
3940 | iexplore.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=20731219&rt=1601463930582&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599(www.isba4.net)%25E5%25BF%2583%25E5%2585%25A8%25E6%2584%258F%25E6%2589%2593%25E9%2580%25A0&ing=2&ekc=&sid=1601463930582&tt=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591-%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&kw=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591%25E8%25AF%259A%25E4%25BF%25A1%25E4%25BF%25A1%25E6%259C%25AC%252C%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&cu=http%253A%252F%252Fwww.isba4.net%252Fhbt.php&pu= | CN | — | — | whitelisted |
3940 | iexplore.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=20188551&rt=1601463930879&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599(www.isba4.net)%25E5%25BF%2583%25E5%2585%25A8%25E6%2584%258F%25E6%2589%2593%25E9%2580%25A0&ing=3&ekc=&sid=1601463930879&tt=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591-%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&kw=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591%25E8%25AF%259A%25E4%25BF%25A1%25E4%25BF%25A1%25E6%259C%25AC%252C%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&cu=http%253A%252F%252Fwww.isba4.net%252Fhbt.php&pu= | CN | — | — | whitelisted |
3232 | chrome.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=20869605&rt=1601463949377&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599(www.isba4.net)%25E5%25BF%2583%25E5%2585%25A8%25E6%2584%258F%25E6%2589%2593%25E9%2580%25A0&ing=1&ekc=&sid=1601463949377&tt=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591-%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&kw=%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E7%25BD%2591%25E8%25AF%259A%25E4%25BF%25A1%25E4%25BF%25A1%25E6%259C%25AC%252C%25E8%2585%25BE%25E5%258D%259A%25E5%25AE%2598%25E6%2596%25B9%25E8%25AF%259A%25E4%25BF%25A1%25E5%2594%25AF%25E4%25B8%2580%25E7%25BD%2591%25E7%25AB%2599&cu=http%253A%252F%252Fwww.isba4.net%252Fhbt.php&pu= | CN | — | — | whitelisted |
3232 | chrome.exe | GET | 200 | 104.165.77.18:80 | http://www.isba4.net/jquery.min.js | US | text | 599 b | suspicious |
3940 | iexplore.exe | GET | 200 | 104.165.77.18:80 | http://www.isba4.net/hbt.php | US | html | 448 b | suspicious |
3940 | iexplore.exe | GET | 200 | 95.101.72.191:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMdayjw3Lc41Ws87pvgVc5tug%3D%3D | unknown | der | 527 b | whitelisted |
3940 | iexplore.exe | GET | 200 | 104.165.77.18:80 | http://www.isba4.net/jquery.min.js | US | text | 599 b | suspicious |
3940 | iexplore.exe | GET | 200 | 104.165.77.18:80 | http://www.isba4.net/tj.js | US | html | 253 b | suspicious |
3848 | iexplore.exe | GET | 200 | 104.165.77.18:80 | http://www.isba4.net/hbt.php | US | html | 448 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3940 | iexplore.exe | 104.165.77.18:80 | www.isba4.net | EGIHosting | US | suspicious |
3940 | iexplore.exe | 122.228.91.91:443 | js.users.51.la | CHINANET Sichuan province Chengdu MAN network | CN | unknown |
3940 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
3940 | iexplore.exe | 183.131.207.66:80 | ia.51.la | DaLi | CN | malicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 122.10.48.116:443 | 2019chonga.com | DXTL Tseung Kwan O Service | HK | unknown |
3940 | iexplore.exe | 95.101.72.191:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
3232 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
3232 | chrome.exe | 216.58.208.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.isba4.net |
| suspicious |
js.users.51.la |
| whitelisted |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
ia.51.la |
| whitelisted |
2019chonga.com |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
www.2019chonga.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3232 | chrome.exe | Potentially Bad Traffic | ET INFO JJEncode Encoded Script |