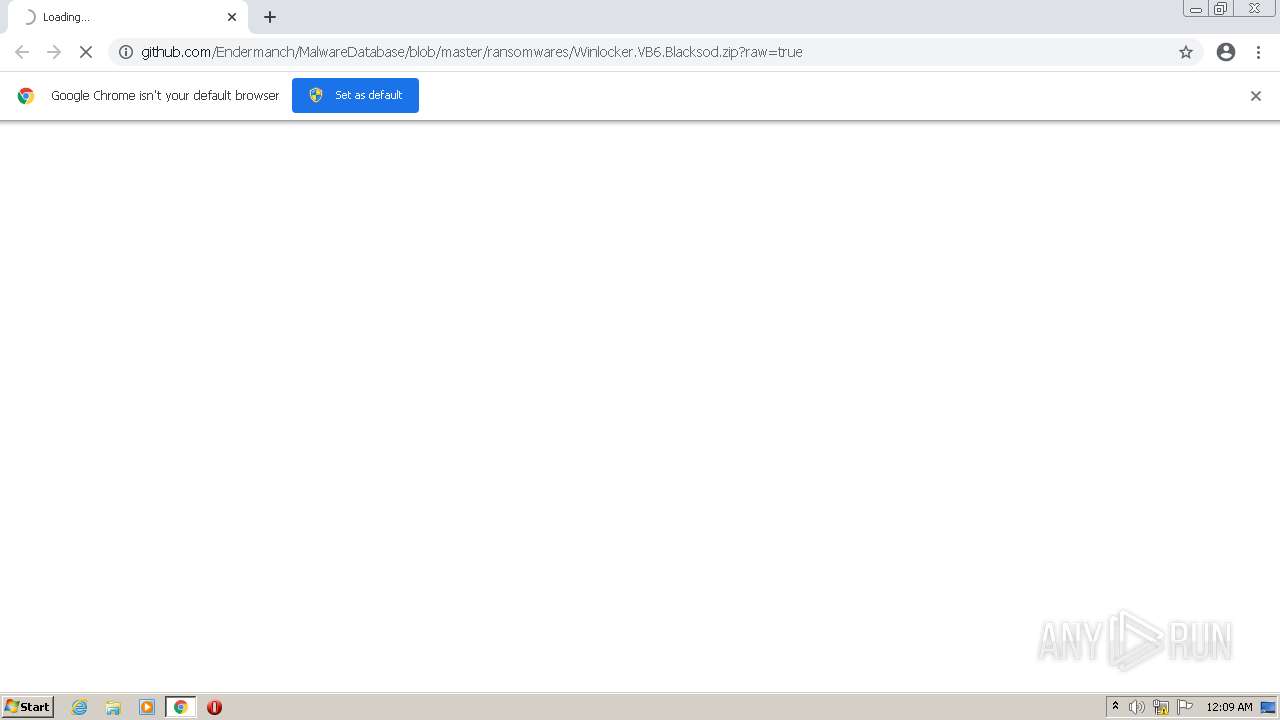
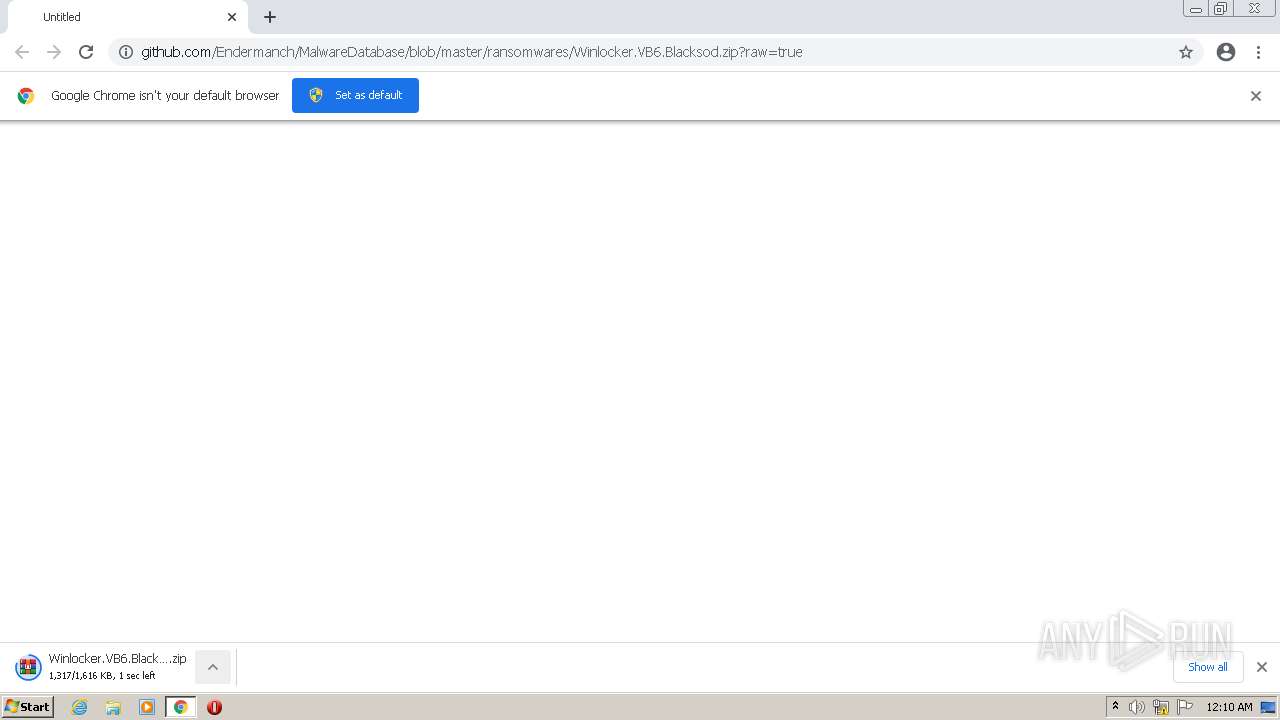
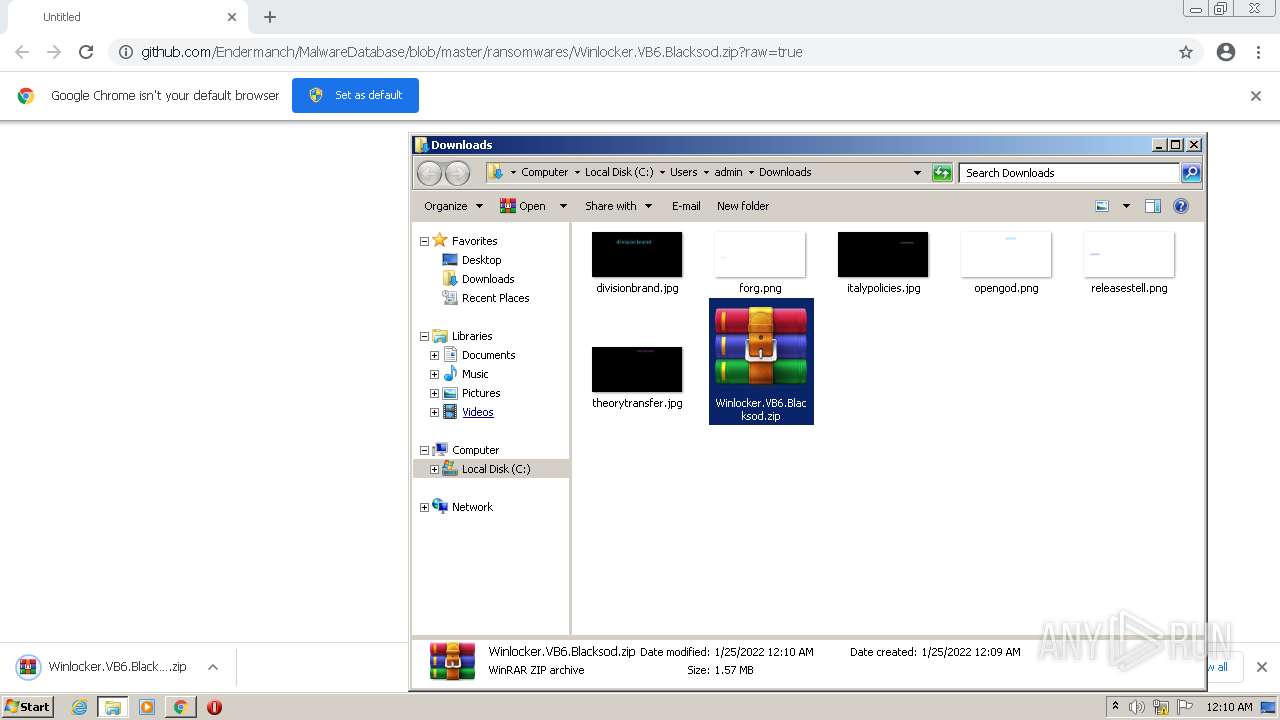
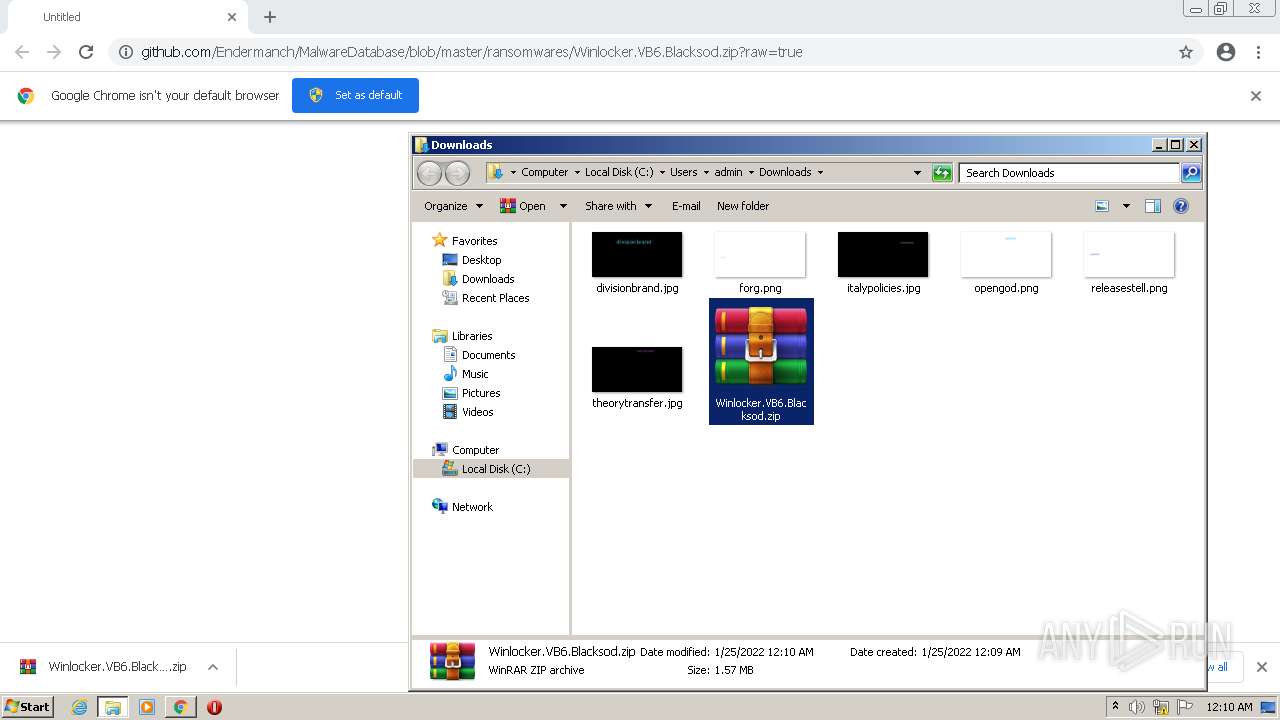
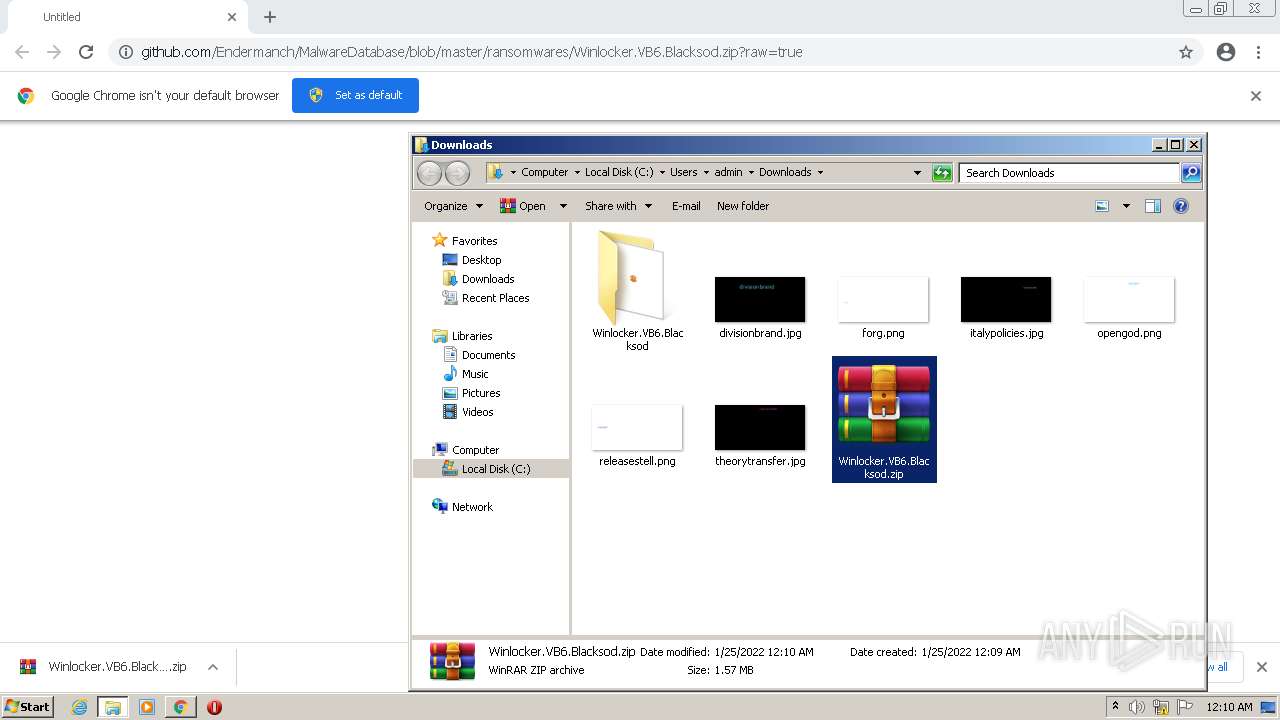
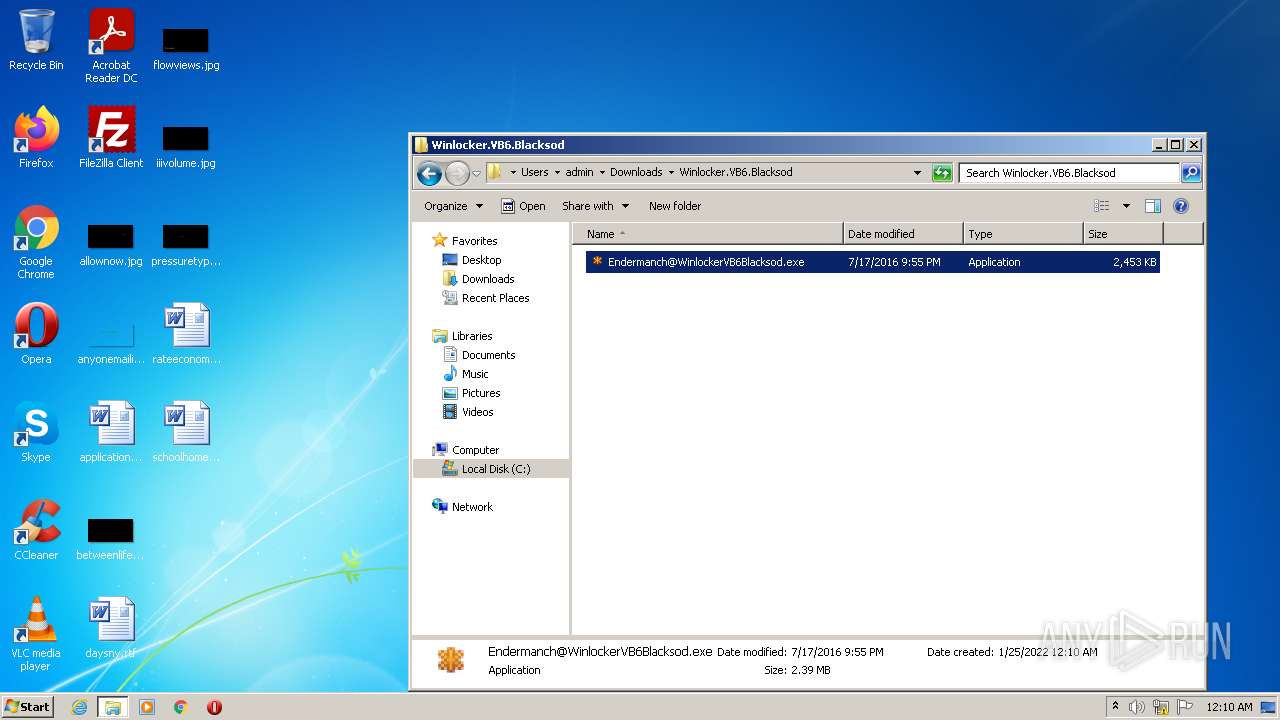
| URL: | https://github.com/Endermanch/MalwareDatabase/blob/master/ransomwares/Winlocker.VB6.Blacksod.zip?raw=true |
| Full analysis: | https://app.any.run/tasks/1e3b7814-76e7-45a4-90e8-60eb073d7134 |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2022, 00:09:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A0956DBF10D6E93C02980A8EDA3582CC |
| SHA1: | 118E807D30840D389C7841611EA175021DCB3396 |
| SHA256: | BA60DDFE4E9C8BDB9A0F0A92657F889A202B73D52CBCF02FDF0B40BEC55C85D1 |
| SSDEEP: | 3:N8tEdegLaKoEJ3PqkzEHcEie+myMoZYuMiEj:2ufLtfnz+cEizmfoZOj |
MALICIOUS
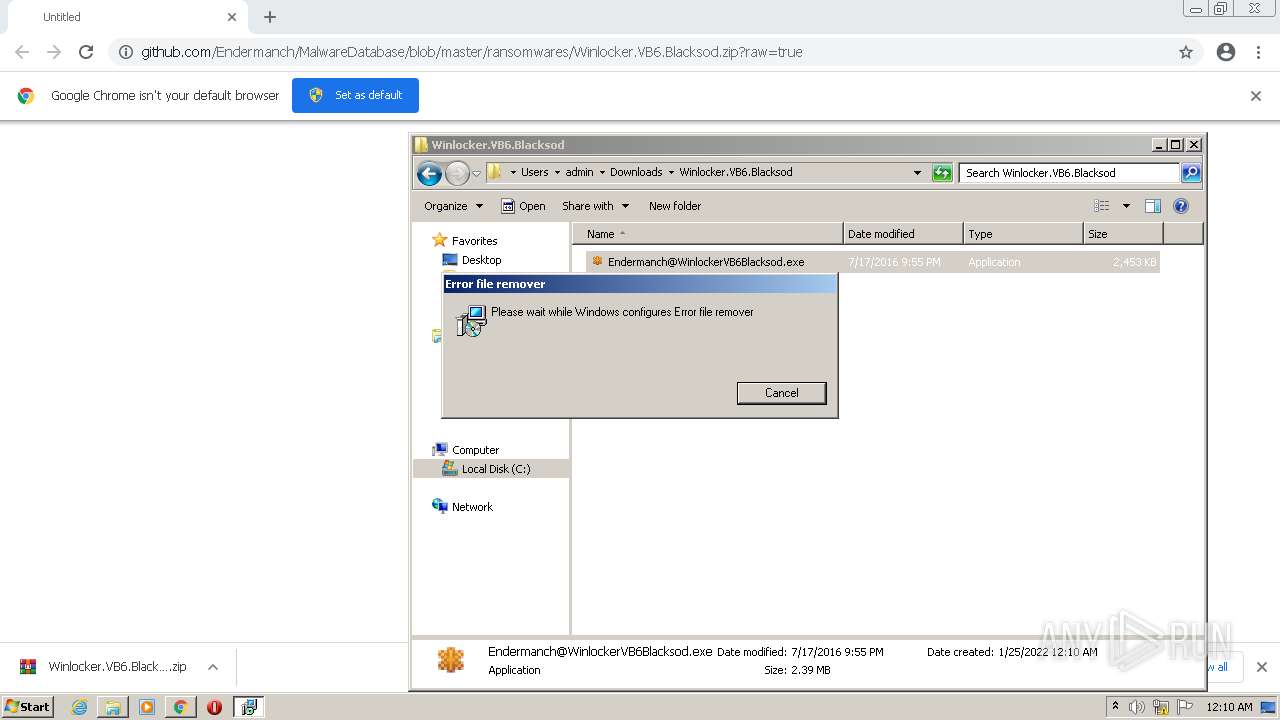
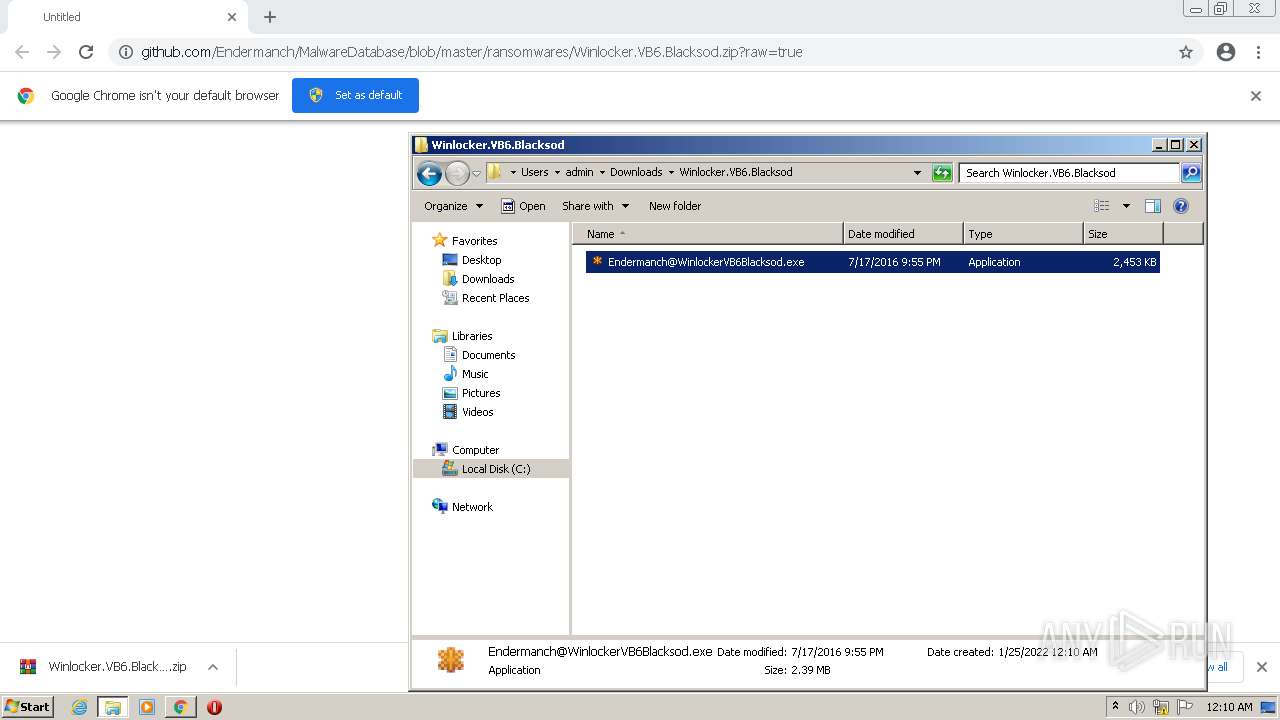
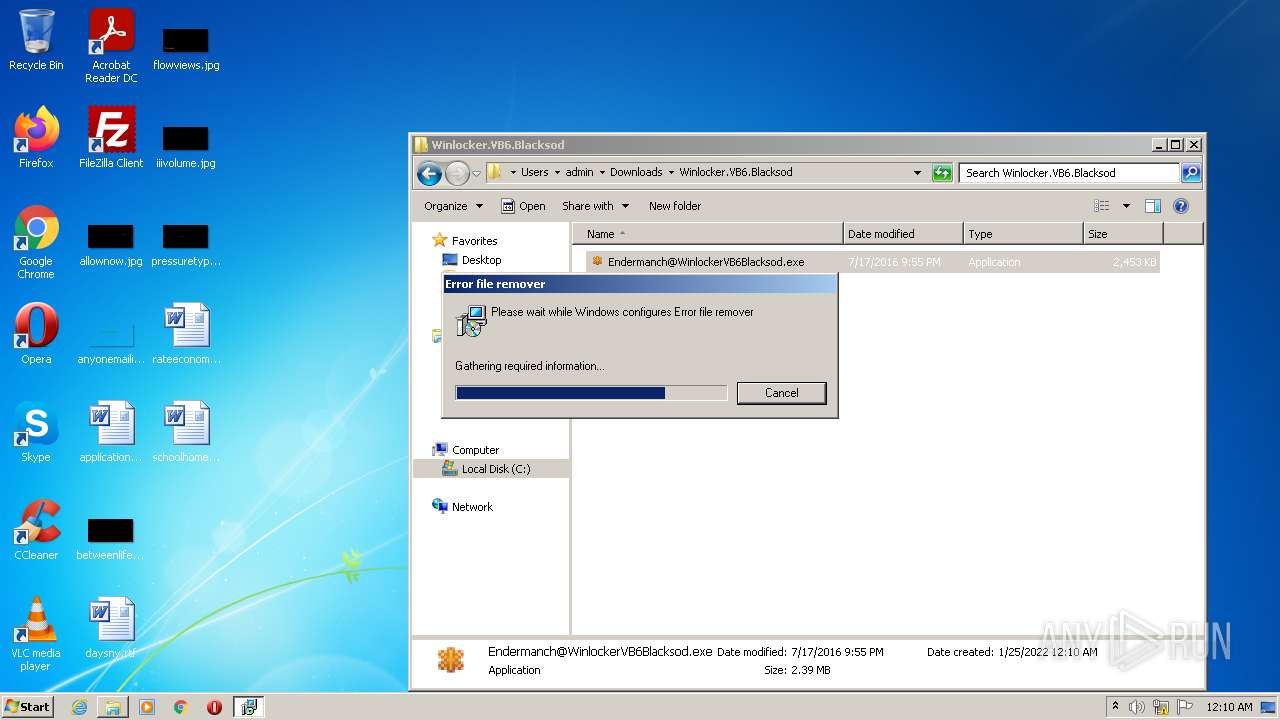
Application was dropped or rewritten from another process
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Drops executable file immediately after starts
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Loads dropped or rewritten executable
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- MsiExec.exe (PID: 3000)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
- MsiExec.exe (PID: 2200)
- MsiExec.exe (PID: 2324)
Changes the login/logoff helper path in the registry
- msiexec.exe (PID: 1076)
Loads the Task Scheduler DLL interface
- MsiExec.exe (PID: 3000)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- MsiExec.exe (PID: 596)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Connects to CnC server
- MsiExec.exe (PID: 2200)
- MsiExec.exe (PID: 2324)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3004)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3004)
- msiexec.exe (PID: 1076)
Reads the computer name
- WinRAR.exe (PID: 3004)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3004)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- msiexec.exe (PID: 1076)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Reads Environment values
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- MsiExec.exe (PID: 2324)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
- MsiExec.exe (PID: 2200)
Creates files in the user directory
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Executed as Windows Service
- msiexec.exe (PID: 1076)
Starts Microsoft Installer
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Reads Windows owner or organization settings
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- msiexec.exe (PID: 3648)
- msiexec.exe (PID: 1076)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
- msiexec.exe (PID: 2608)
Reads the Windows organization settings
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- msiexec.exe (PID: 3648)
- msiexec.exe (PID: 1076)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
- msiexec.exe (PID: 2608)
Application launched itself
- msiexec.exe (PID: 1076)
Creates files in the program directory
- msiexec.exe (PID: 1076)
Creates a directory in Program Files
- msiexec.exe (PID: 1076)
Creates files in the Windows directory
- MsiExec.exe (PID: 3000)
INFO
Checks supported languages
- chrome.exe (PID: 2172)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 752)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 2600)
- chrome.exe (PID: 1112)
- chrome.exe (PID: 2896)
- msiexec.exe (PID: 1076)
- msiexec.exe (PID: 3648)
- MsiExec.exe (PID: 2324)
- MsiExec.exe (PID: 3000)
- chrome.exe (PID: 1908)
- chrome.exe (PID: 4068)
- msiexec.exe (PID: 2608)
- MsiExec.exe (PID: 2200)
- MsiExec.exe (PID: 596)
- chrome.exe (PID: 2492)
Application launched itself
- chrome.exe (PID: 2172)
Reads the computer name
- chrome.exe (PID: 2172)
- chrome.exe (PID: 2052)
- chrome.exe (PID: 1908)
- chrome.exe (PID: 4068)
- chrome.exe (PID: 752)
- msiexec.exe (PID: 1076)
- msiexec.exe (PID: 3648)
- MsiExec.exe (PID: 2324)
- MsiExec.exe (PID: 3000)
- chrome.exe (PID: 1112)
- msiexec.exe (PID: 2608)
- MsiExec.exe (PID: 2200)
- MsiExec.exe (PID: 596)
Reads the hosts file
- chrome.exe (PID: 2172)
- chrome.exe (PID: 752)
Reads settings of System Certificates
- chrome.exe (PID: 752)
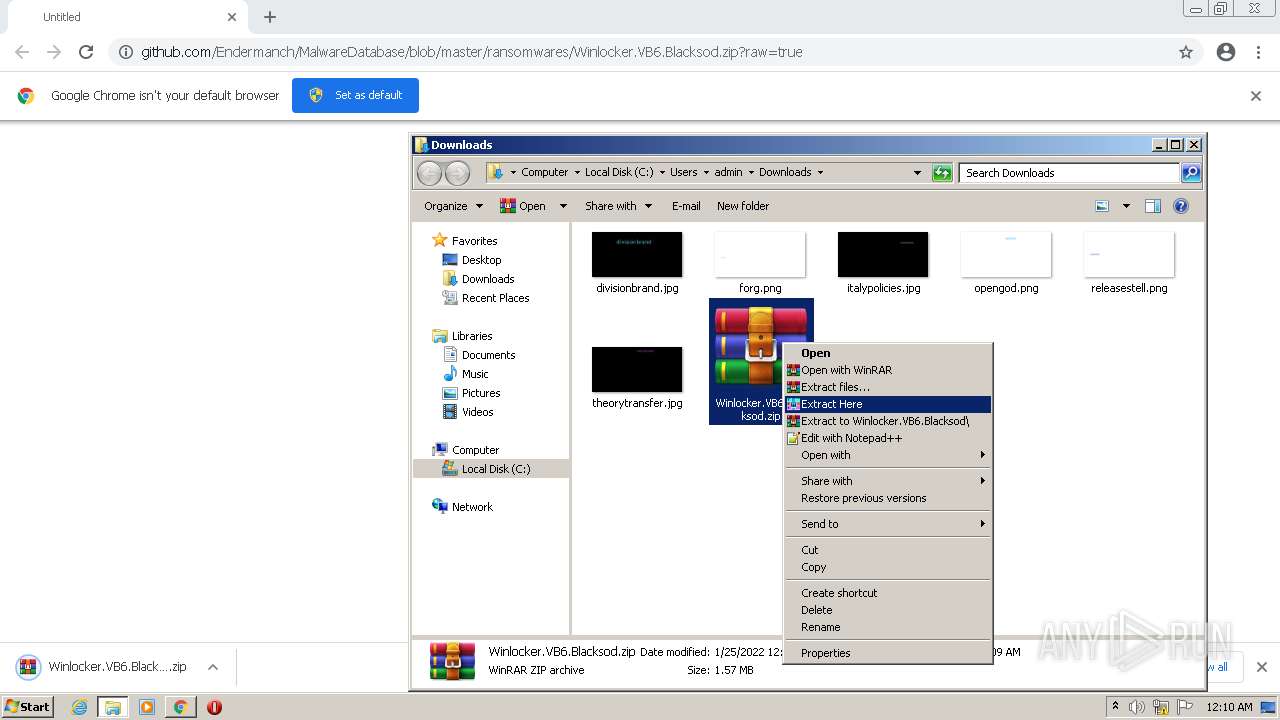
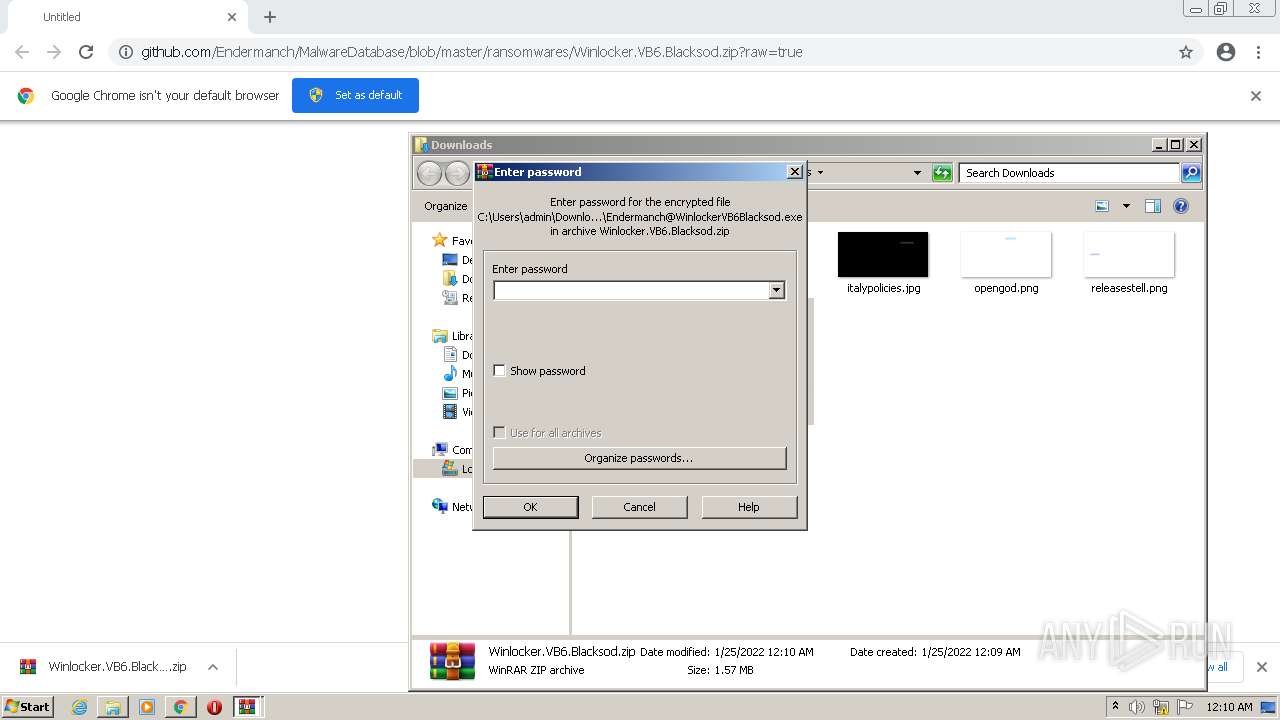
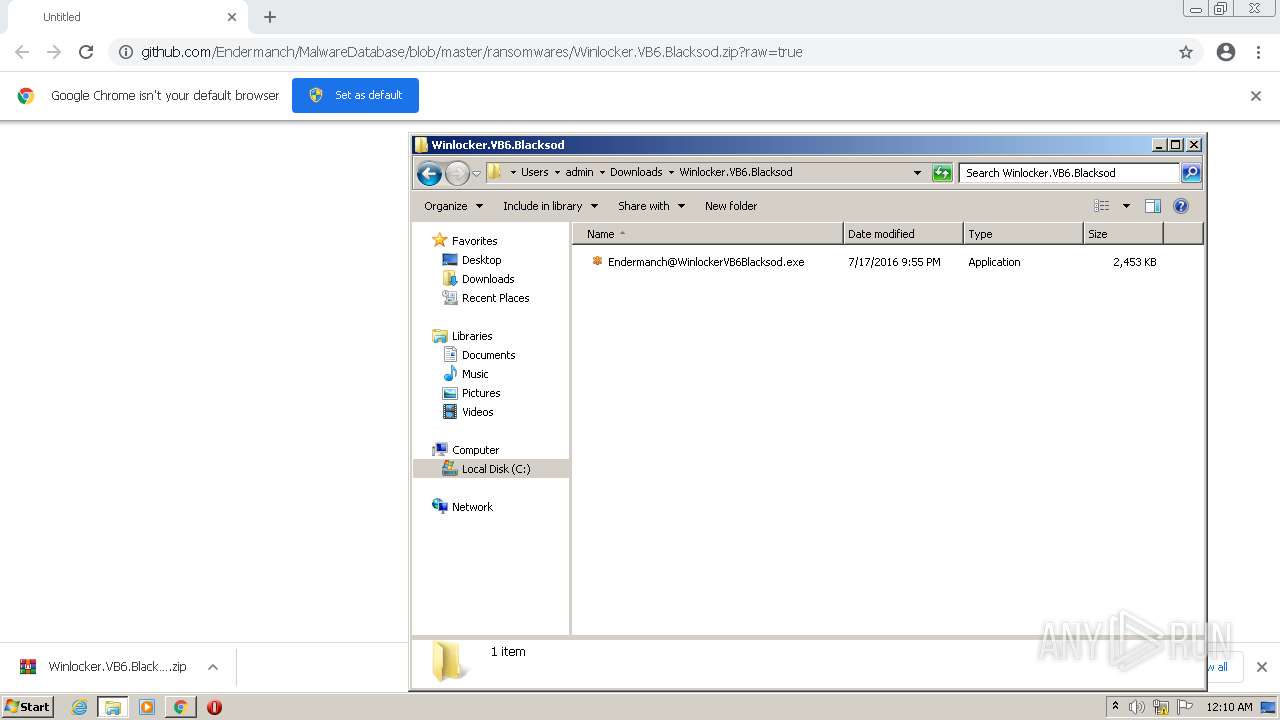
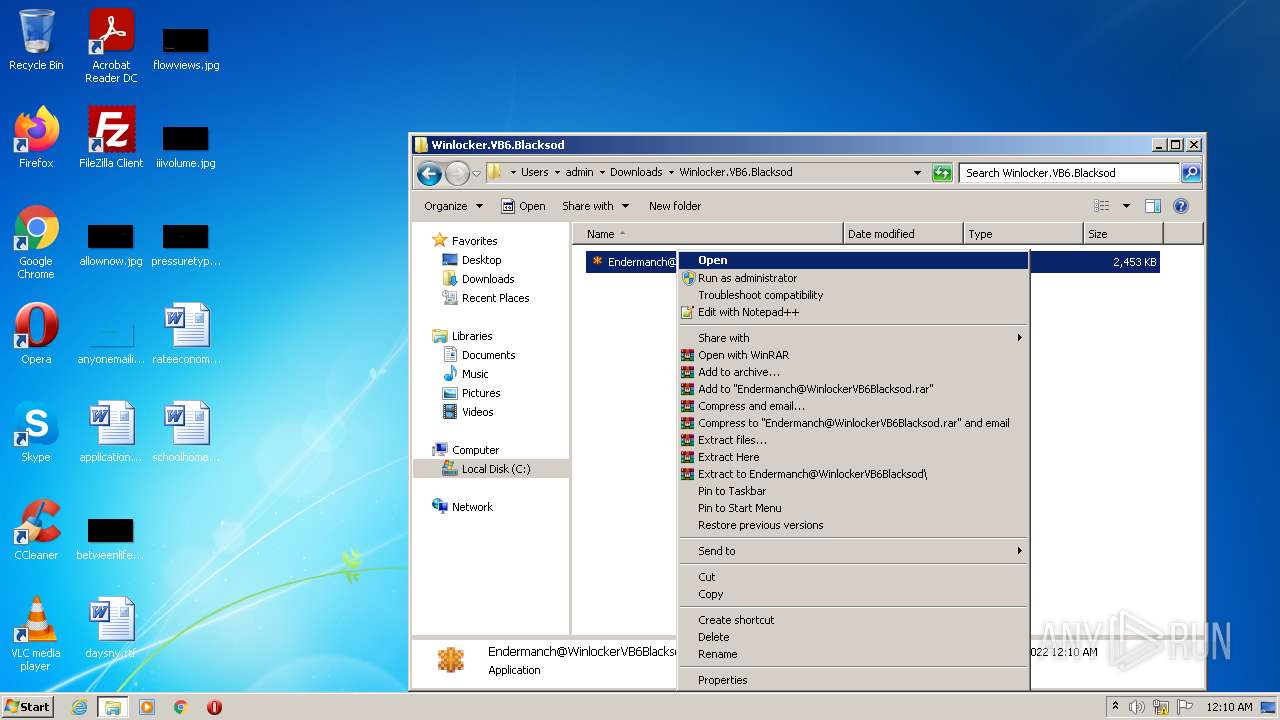
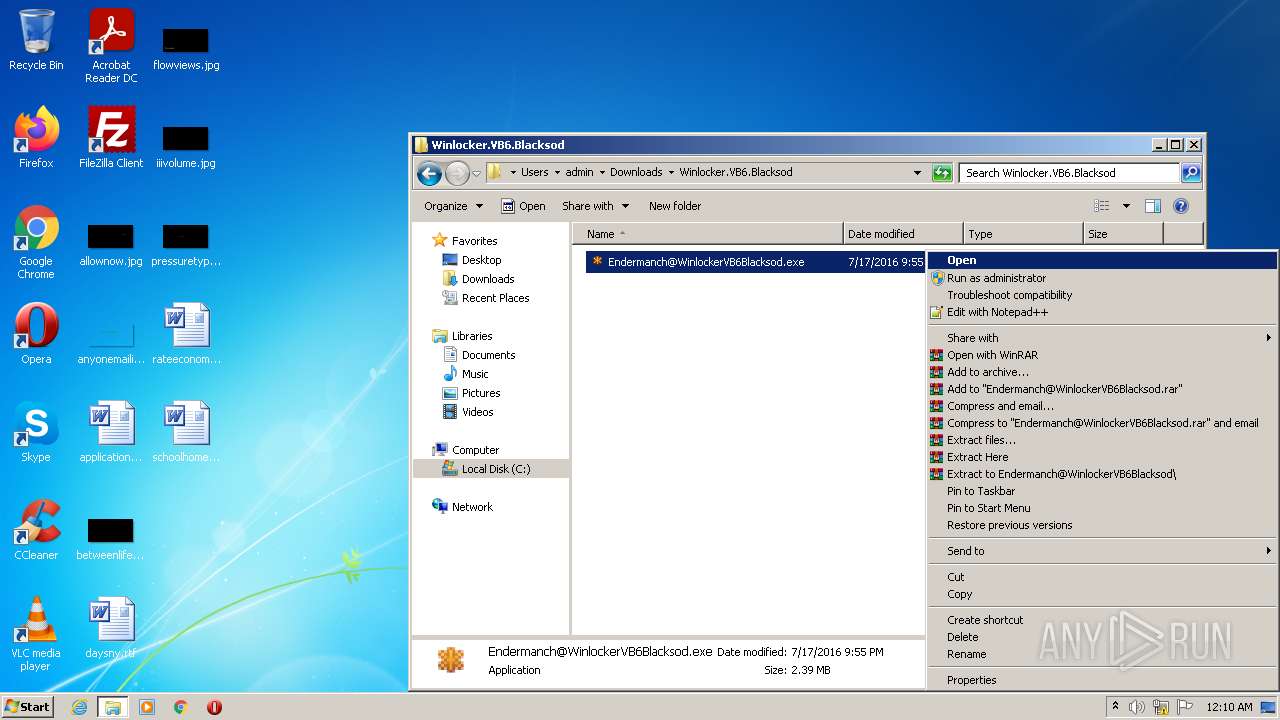
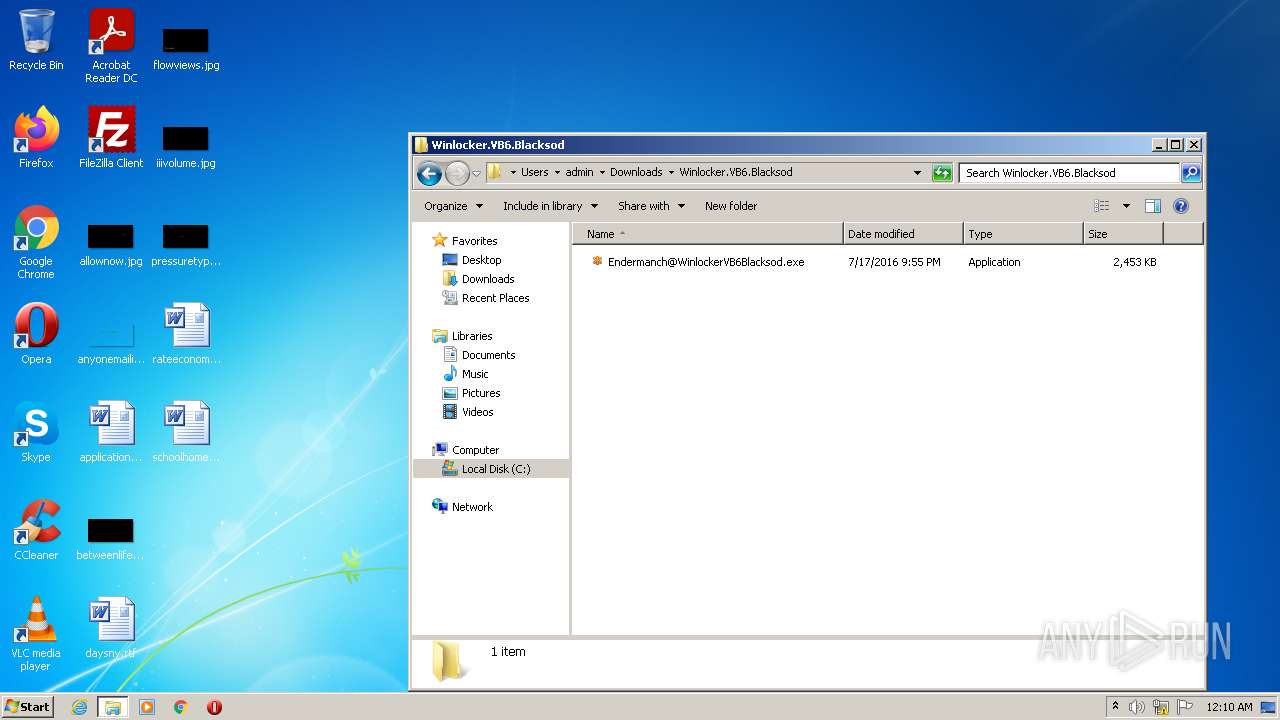
Manual execution by user
- WinRAR.exe (PID: 3004)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 3812)
- Endermanch@WinlockerVB6Blacksod.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
21
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 596 | C:\Windows\system32\MsiExec.exe -Embedding DF2EBAA44771D0A3C29FD485AB632798 E Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1000,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1232 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2192 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1000,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3268 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8965102213299568019,9844806936835758437,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2156 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://github.com/Endermanch/MalwareDatabase/blob/master/ransomwares/Winlocker.VB6.Blacksod.zip?raw=true" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2200 | C:\Windows\system32\MsiExec.exe -Embedding A1A881CEA5ADB2295FF10EC47131548E | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | C:\Windows\system32\MsiExec.exe -Embedding DD52C0274253471BB756C1C14EC40524 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
13 955
Read events
13 734
Write events
196
Delete events
25
Modification events
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
34
Suspicious files
43
Text files
88
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF3FCF-87C.pma | — | |
MD5:— | SHA256:— | |||
| 3532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF113267.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF11315e.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2172 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF1137a7.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
13
DNS requests
7
Threats
64
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2200 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
2324 | MsiExec.exe | POST | 402 | 3.209.18.1:80 | http://collect.installeranalytics.com/ | US | text | 2 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
752 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
752 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
752 | chrome.exe | 216.58.212.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
752 | chrome.exe | 140.82.121.3:443 | github.com | — | US | suspicious |
2324 | MsiExec.exe | 3.209.18.1:80 | collect.installeranalytics.com | — | US | malicious |
2200 | MsiExec.exe | 3.209.18.1:80 | collect.installeranalytics.com | — | US | malicious |
752 | chrome.exe | 185.199.108.133:443 | raw.githubusercontent.com | GitHub, Inc. | NL | malicious |
752 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
github.com |
| malicious |
accounts.google.com |
| shared |
raw.githubusercontent.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
collect.installeranalytics.com |
| malicious |
Threats
64 ETPRO signatures available at the full report