| File name: | ba506d2acdff76109d44688dc4213d9192852f00dacf2933543c256e450f85de.msi |
| Full analysis: | https://app.any.run/tasks/aa1a8e84-551d-4084-83a1-9cfd436e5b37 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 21:25:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 15:06:51 2020, Code page: 1252, Revision Number: {9B9BDA25-DA69-4F4E-A6B1-53C3F8980848}, Number of Words: 10, Subject: Windows, Author: MYMSqZGvFr, Name of Creating Application: 432432432432 (Evaluation Installer), Template: ;1033, Comments: (Evaluation Installer), Title: Installation Database, Keywords: Installer, MSI, Database, Security: 0, Number of Pages: 200 |
| MD5: | F56286E1B544DB75D711D9AC267C4CE5 |
| SHA1: | FFB5A9650475D40076287F6D24831CE78B047B36 |
| SHA256: | BA506D2ACDFF76109D44688DC4213D9192852F00DACF2933543C256E450F85DE |
| SSDEEP: | 24576:TaSxGU0fqgQazW/G/tPABM+seD6T+QXle8AVLdPliY5Aj5:TaSw/QmW/GqMpe++QXllAVLdPliY5Al |
MALICIOUS
Drops executable file immediately after starts
- msiexec.exe (PID: 1168)
Writes to a start menu file
- MsiExec.exe (PID: 3004)
SUSPICIOUS
Executed as Windows Service
- msiexec.exe (PID: 1168)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1168)
Reads the Windows organization settings
- msiexec.exe (PID: 2828)
- msiexec.exe (PID: 1168)
Reads Windows owner or organization settings
- msiexec.exe (PID: 1168)
- msiexec.exe (PID: 2828)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 1168)
Application launched itself
- msiexec.exe (PID: 1168)
Drops a file with a compile date too recent
- msiexec.exe (PID: 1168)
Creates files in the user directory
- MsiExec.exe (PID: 3004)
Checks for external IP
- MsiExec.exe (PID: 3004)
INFO
Checks supported languages
- msiexec.exe (PID: 2828)
- msiexec.exe (PID: 1168)
- MsiExec.exe (PID: 3004)
Reads the computer name
- msiexec.exe (PID: 2828)
- msiexec.exe (PID: 1168)
- MsiExec.exe (PID: 3004)
Checks Windows Trust Settings
- MsiExec.exe (PID: 3004)
Reads settings of System Certificates
- MsiExec.exe (PID: 3004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Pages: | 200 |
|---|---|
| Security: | None |
| Keywords: | Installer, MSI, Database |
| Title: | Installation Database |
| Comments: | (Evaluation Installer) |
| Template: | ;1033 |
| Software: | 432432432432 (Evaluation Installer) |
| LastModifiedBy: | - |
| Author: | MYMSqZGvFr |
| Subject: | Windows |
| Words: | 10 |
| RevisionNumber: | {9B9BDA25-DA69-4F4E-A6B1-53C3F8980848} |
| CodePage: | Windows Latin 1 (Western European) |
| ModifyDate: | 2020:09:18 14:06:51 |
| CreateDate: | 2009:12:11 11:47:44 |
| LastPrinted: | 2009:12:11 11:47:44 |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
1
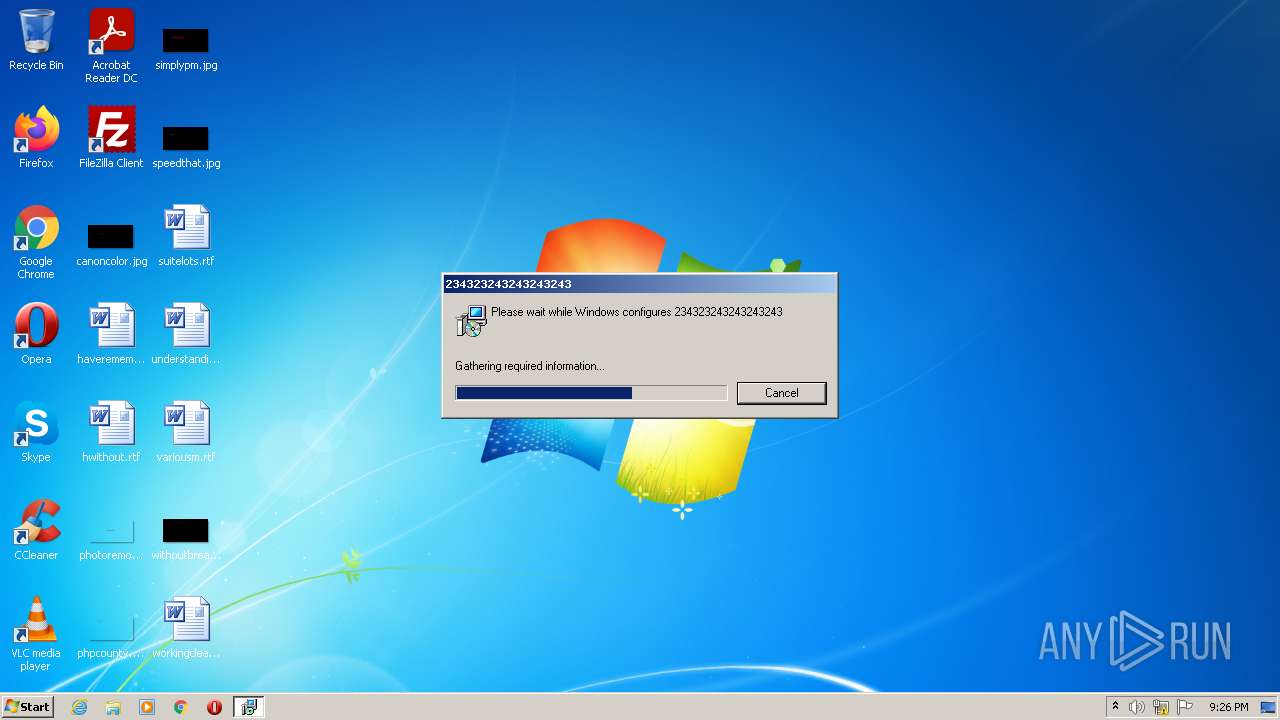
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1168 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2828 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ba506d2acdff76109d44688dc4213d9192852f00dacf2933543c256e450f85de.msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 1603 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | C:\Windows\system32\MsiExec.exe -Embedding 5E33B7A12053DFD988765259AACD006C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 826
Read events
6 783
Write events
38
Delete events
5
Modification events
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 90040000263336558D09D801 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 179C0949C27CCBF78332693F07ED13E1E3DC676925E5451DDC8E4ADE5C740C11 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1168) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\13f0fd.ipi | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3004) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
5
Suspicious files
9
Text files
5
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1168 | msiexec.exe | C:\Windows\Installer\13f0fb.msi | executable | |
MD5:— | SHA256:— | |||
| 1168 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF79BBE9EF70192AE7.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\ext\73Rl9.js | text | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\ext\a1jMB.png | image | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\ext\manifest.json | binary | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\ext\111ms.js | text | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Google Chrome.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1168 | msiexec.exe | C:\Windows\Installer\13f0fd.ipi | binary | |
MD5:— | SHA256:— | |||
| 1168 | msiexec.exe | C:\Windows\Installer\MSIF312.tmp | executable | |
MD5:— | SHA256:— | |||
| 3004 | MsiExec.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\User Pinned\TaskBar\Google Chrome.lnk | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
4
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | MsiExec.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1d4/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQDiOJGRlIYAiAoAAAABKkNX | US | der | 472 b | whitelisted |
3004 | MsiExec.exe | GET | 302 | 34.117.59.81:80 | http://myexternalip.com/raw | US | text | 50 b | shared |
3004 | MsiExec.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3004 | MsiExec.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | der | 724 b | whitelisted |
3004 | MsiExec.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?91ac130b07bb0ab3 | unknown | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | MsiExec.exe | 208.118.63.215:1433 | sql5098.site4now.net | Sharktech | US | suspicious |
3004 | MsiExec.exe | 34.117.59.81:80 | myexternalip.com | — | US | whitelisted |
3004 | MsiExec.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3004 | MsiExec.exe | 142.250.185.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3004 | MsiExec.exe | 34.117.59.81:443 | myexternalip.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sql5098.site4now.net |
| suspicious |
myexternalip.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3004 | MsiExec.exe | Potentially Bad Traffic | ET POLICY Outbound MSSQL Connection to Standard port (1433) |
3004 | MsiExec.exe | Potentially Bad Traffic | ET POLICY Outbound MSSQL Connection to Standard port (1433) |
3004 | MsiExec.exe | Potential Corporate Privacy Violation | ET POLICY External IP Check myexternalip.com |
3004 | MsiExec.exe | Potential Corporate Privacy Violation | ET POLICY IP Check Domain (myexternalip .com in TLS SNI) |
3004 | MsiExec.exe | Potentially Bad Traffic | ET POLICY Outbound MSSQL Connection to Standard port (1433) |
3004 | MsiExec.exe | Potentially Bad Traffic | ET POLICY Outbound MSSQL Connection to Standard port (1433) |
1 ETPRO signatures available at the full report