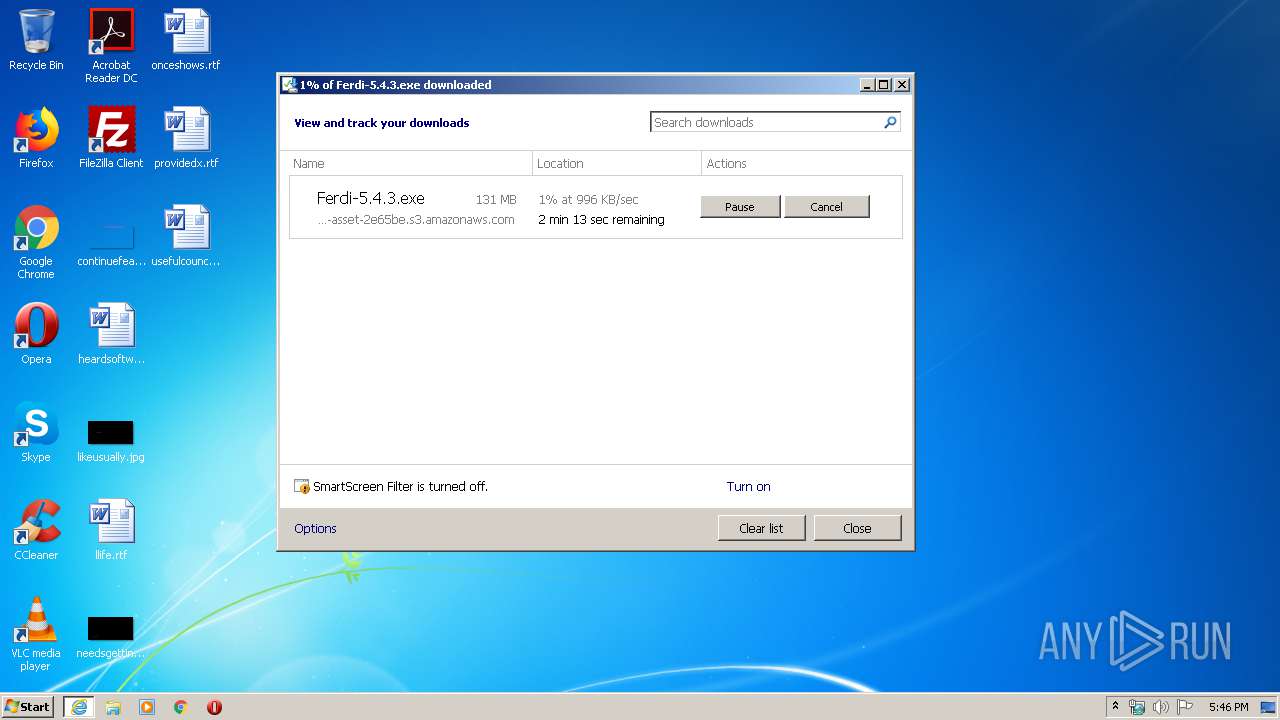
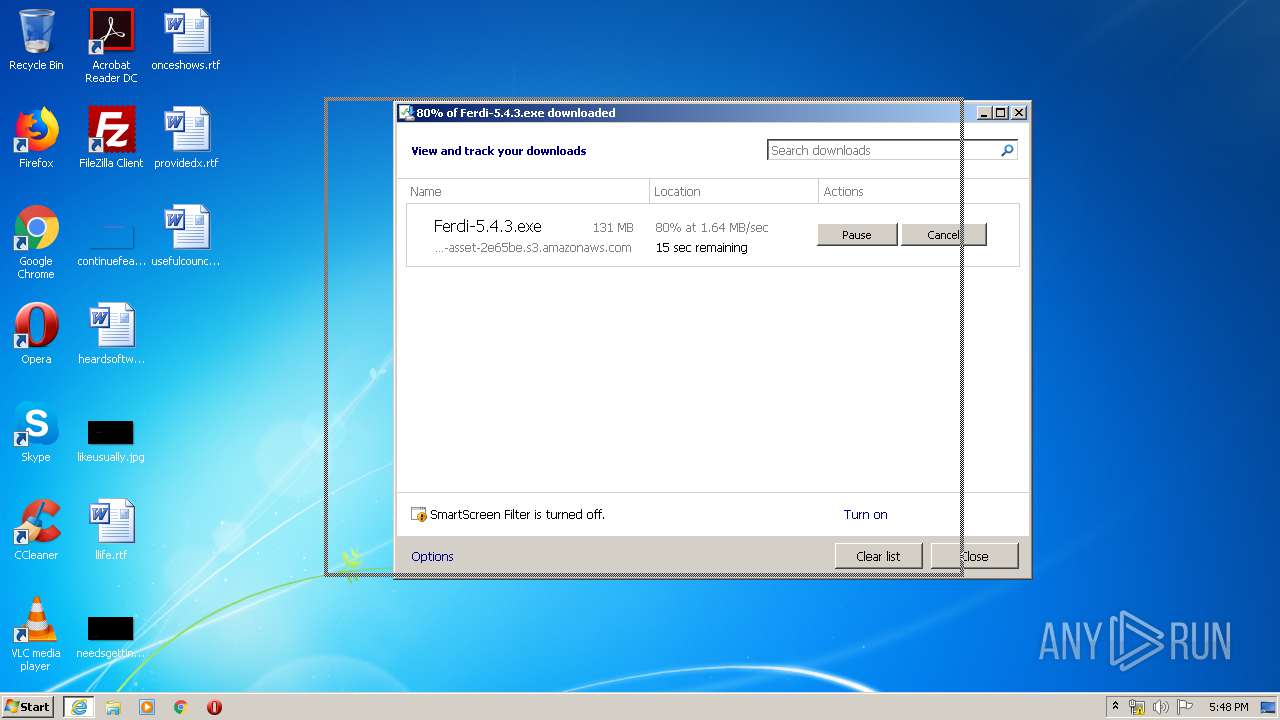
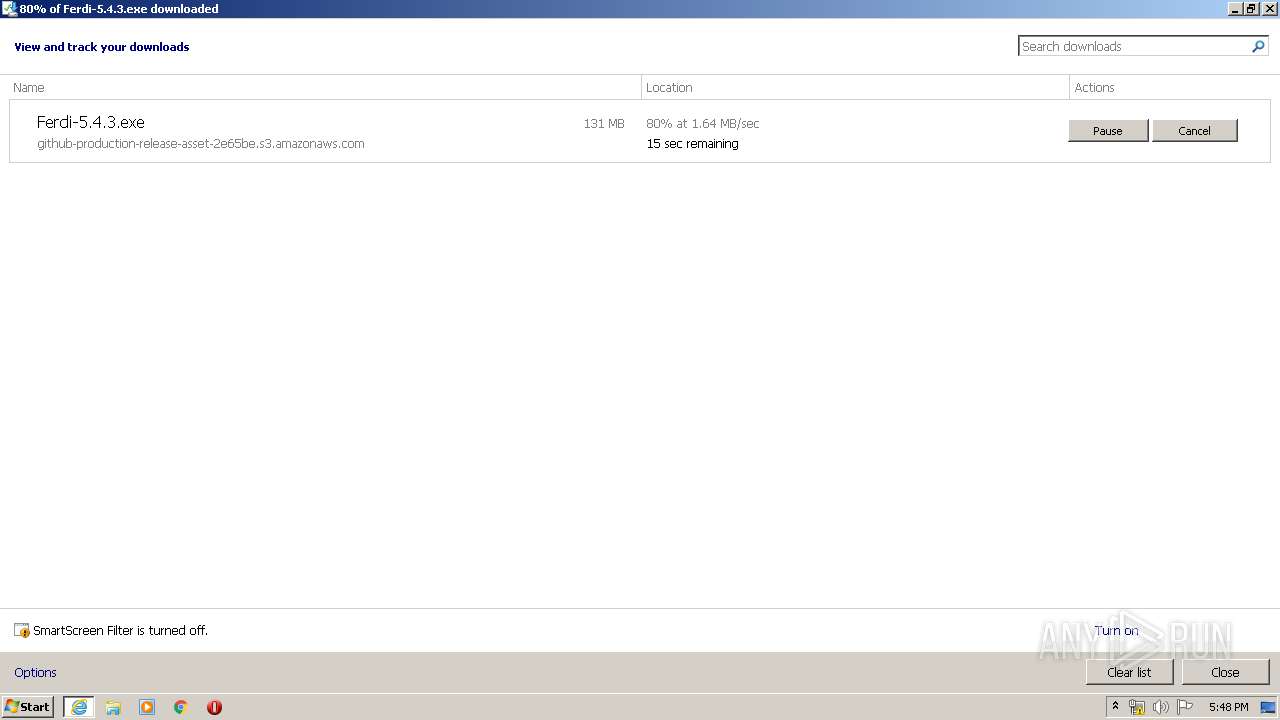
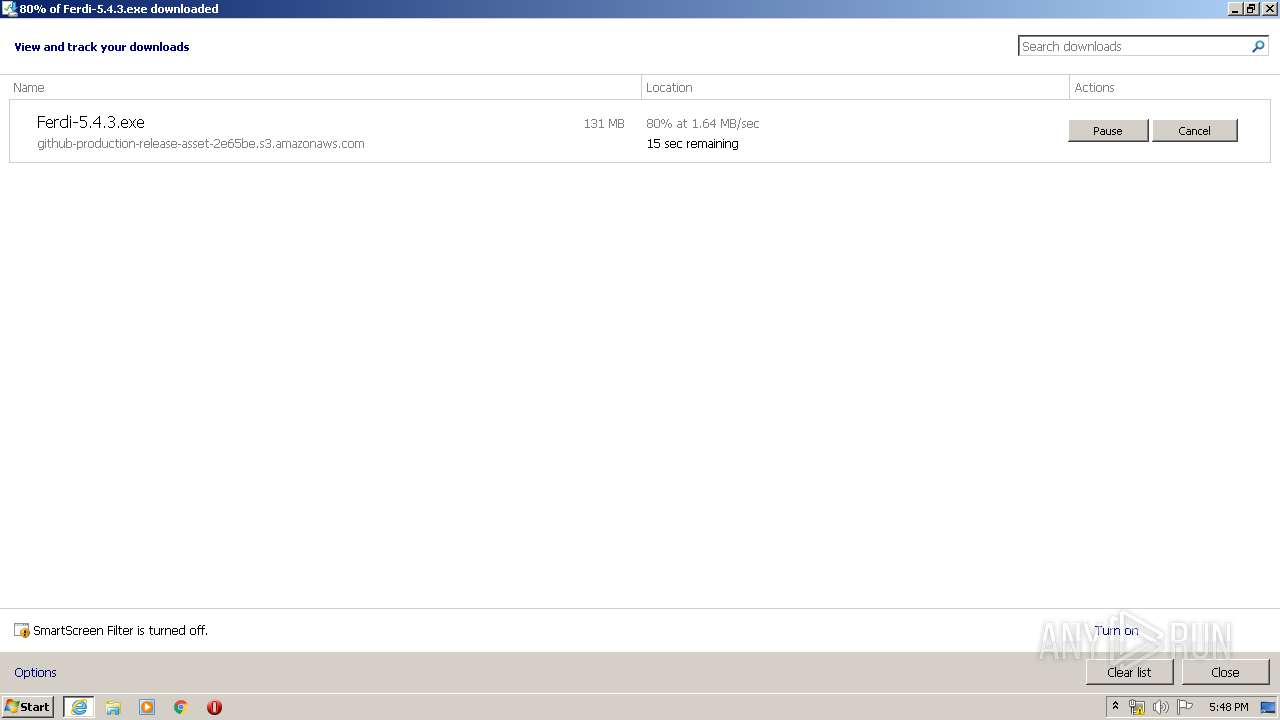
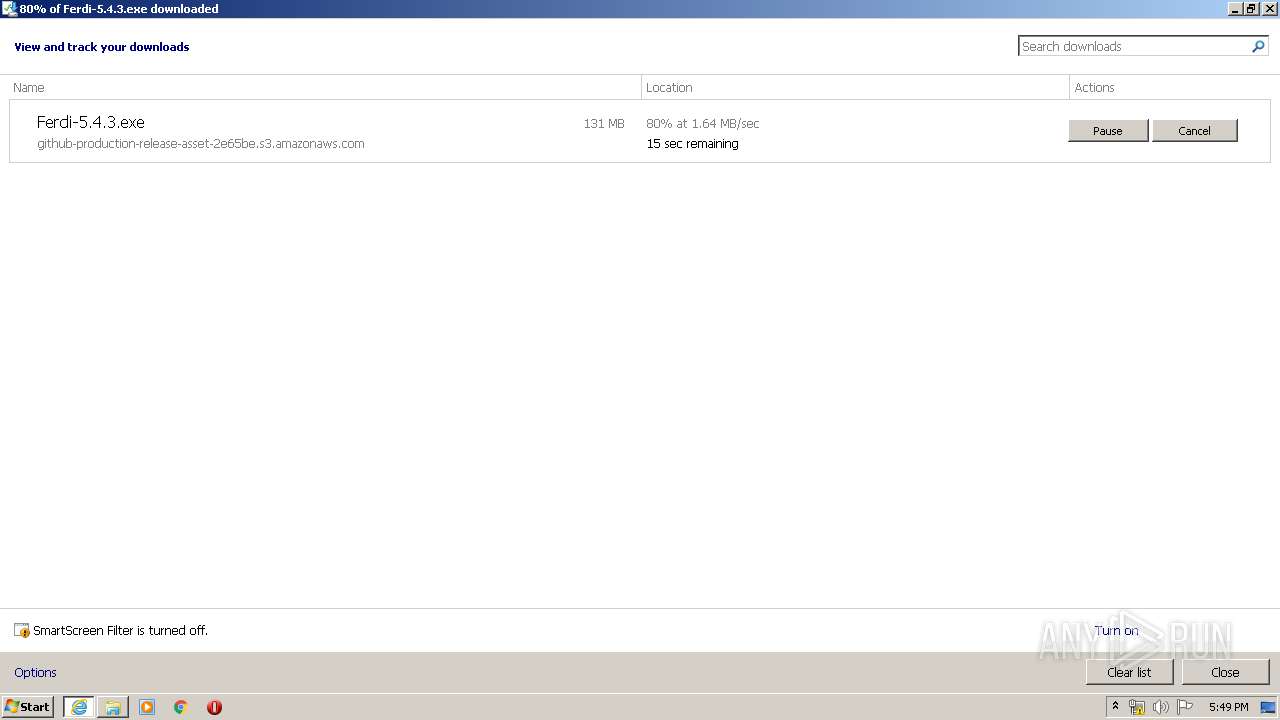
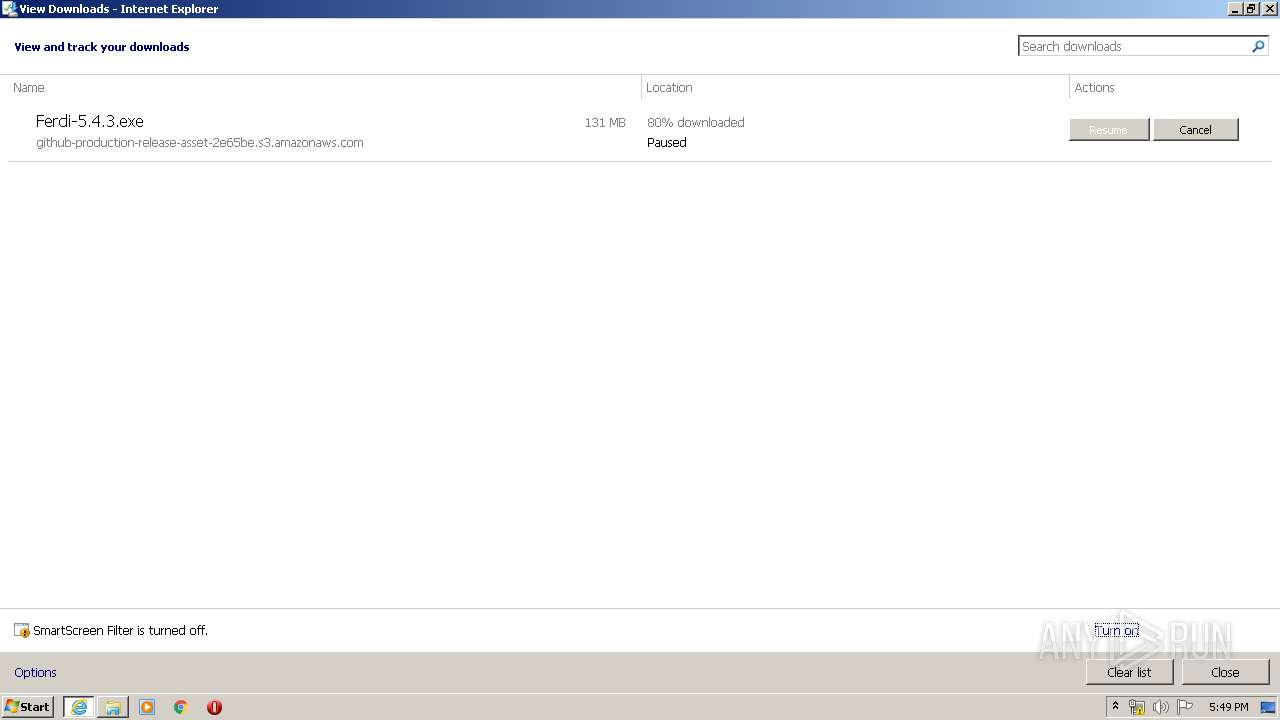
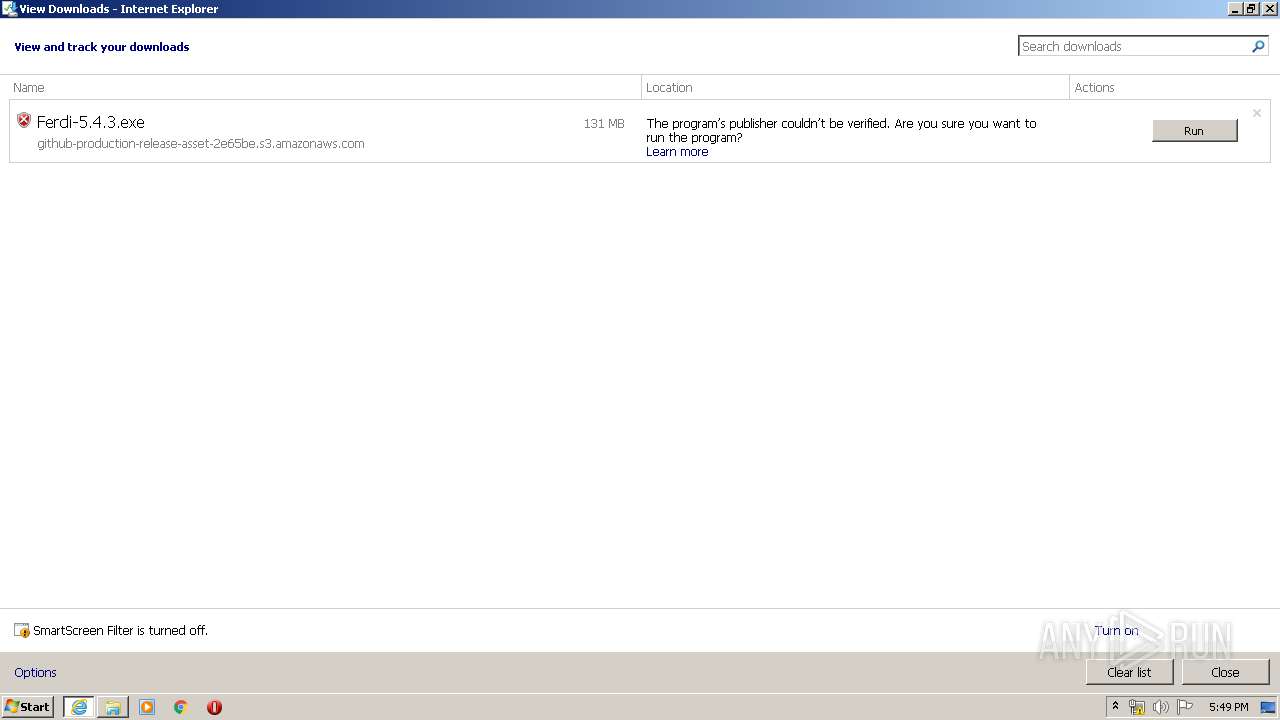
| URL: | https://github.com/getferdi/ferdi/releases/download/v5.4.3/Ferdi-5.4.3.exe |
| Full analysis: | https://app.any.run/tasks/f65d2185-d7b1-47d0-8dc2-4044d4692f1e |
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2020, 16:45:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C556E57FD3B00CDD278F3DF66D525A06 |
| SHA1: | 55FD08F943C041D210806717D74D28A8CC396D08 |
| SHA256: | BA4365E50CE95C46EF4BE035B5165AFF05DEFFB8375B329C9D838080F408DD0A |
| SSDEEP: | 3:N8tEdyARcXBLDAqKXAr2kC6RDkLN:2uk0cRv0YA |
MALICIOUS
Loads dropped or rewritten executable
- Ferdi-5.4.3.exe (PID: 1836)
- Ferdi.exe (PID: 2068)
- Ferdi.exe (PID: 3488)
- Ferdi.exe (PID: 2948)
- Ferdi.exe (PID: 2340)
- Ferdi.exe (PID: 3120)
- Ferdi.exe (PID: 1756)
- Ferdi.exe (PID: 3512)
- Ferdi.exe (PID: 2308)
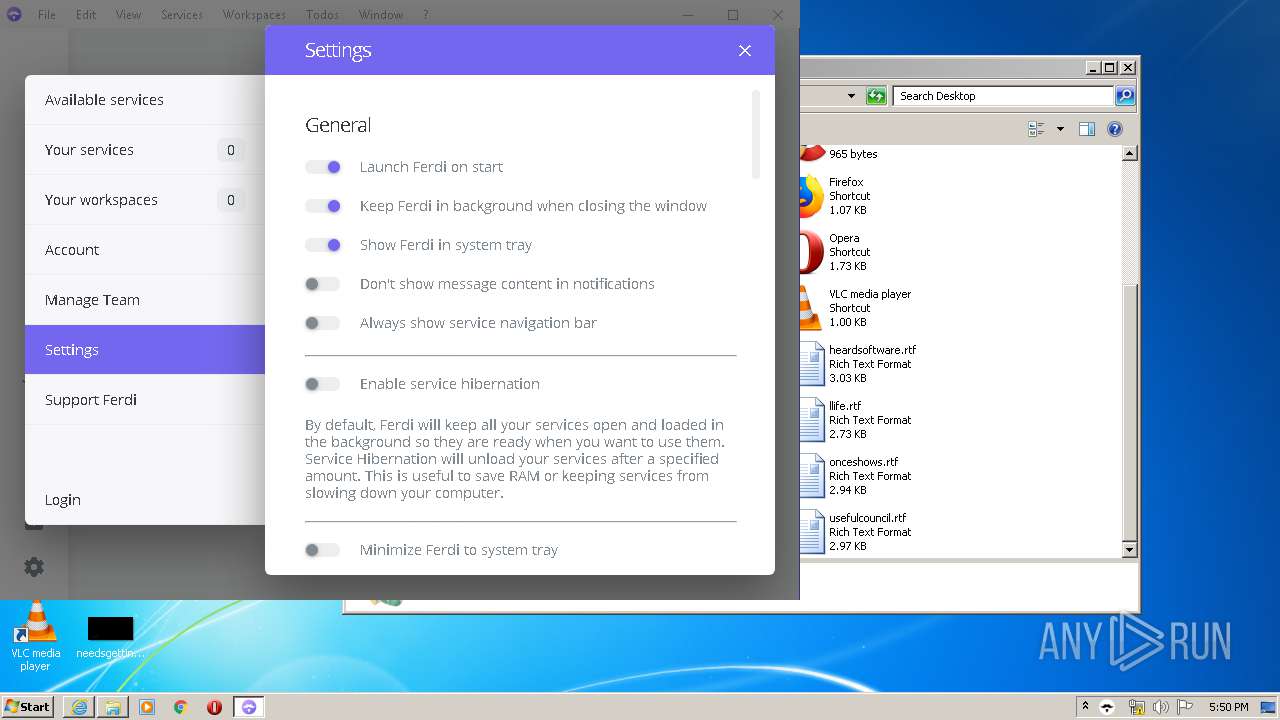
Changes the autorun value in the registry
- reg.exe (PID: 3808)
SUSPICIOUS
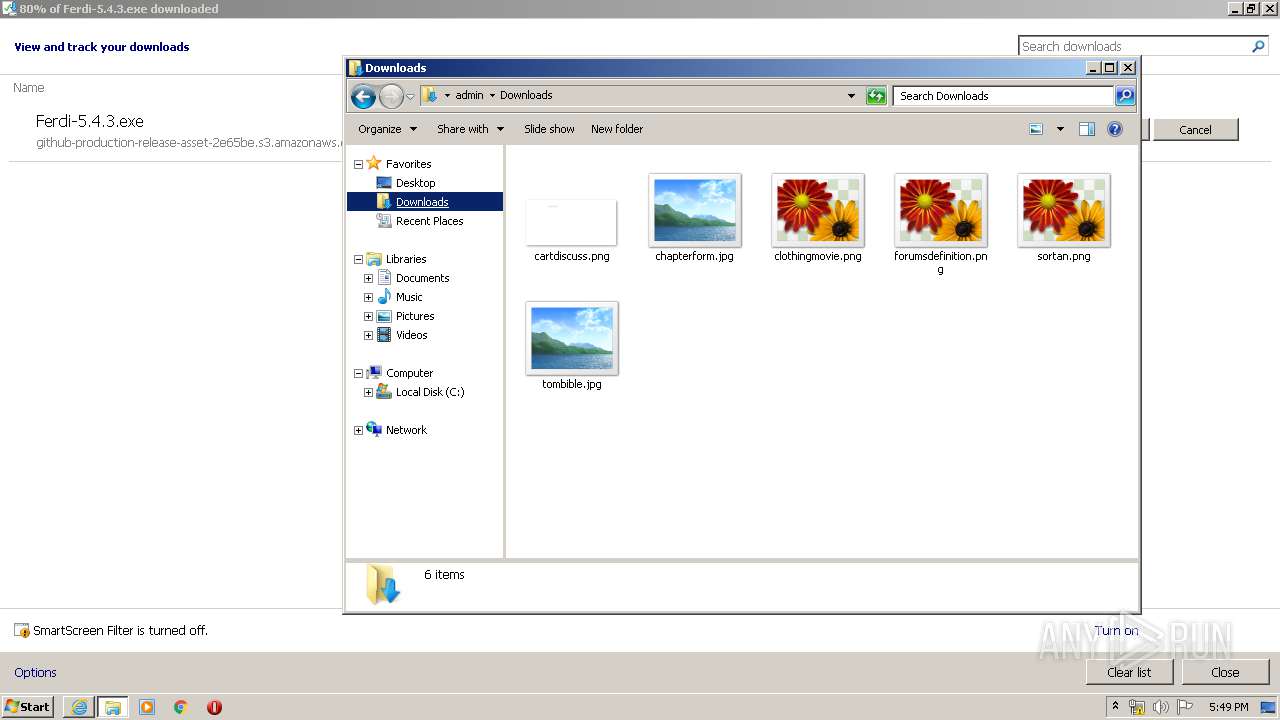
Creates files in the user directory
- Ferdi.exe (PID: 2068)
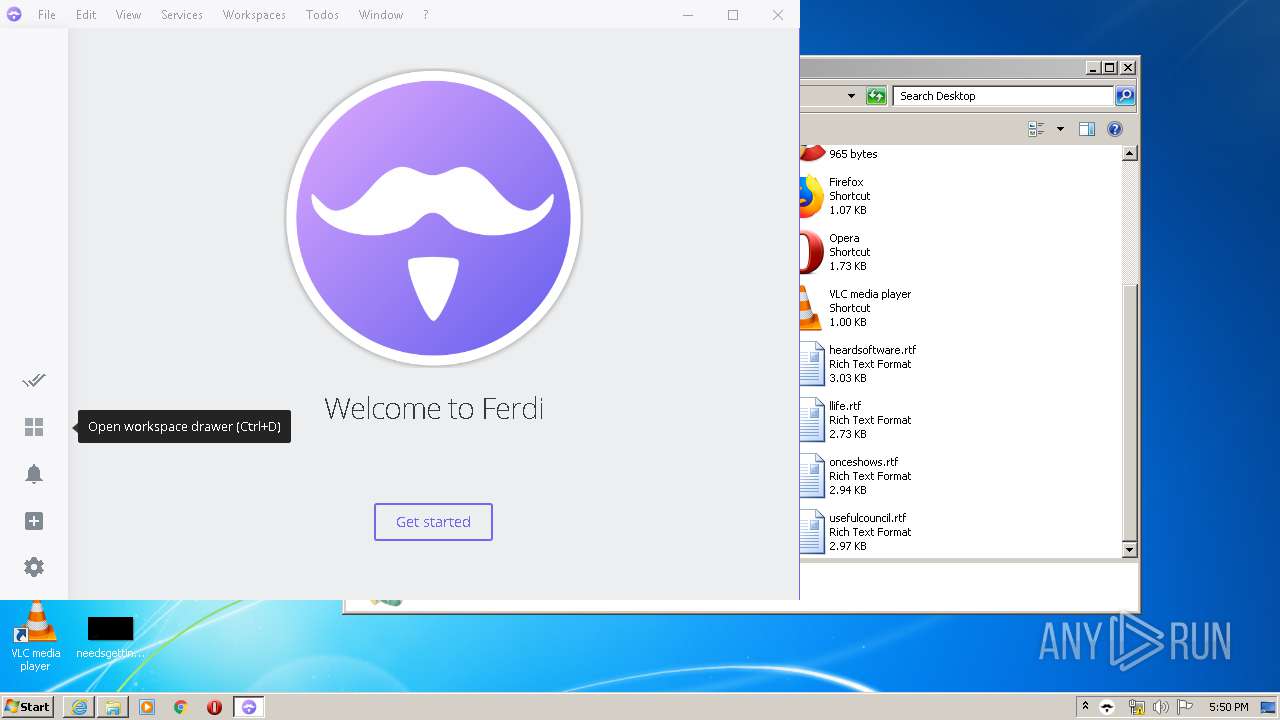
Modifies the open verb of a shell class
- Ferdi.exe (PID: 2068)
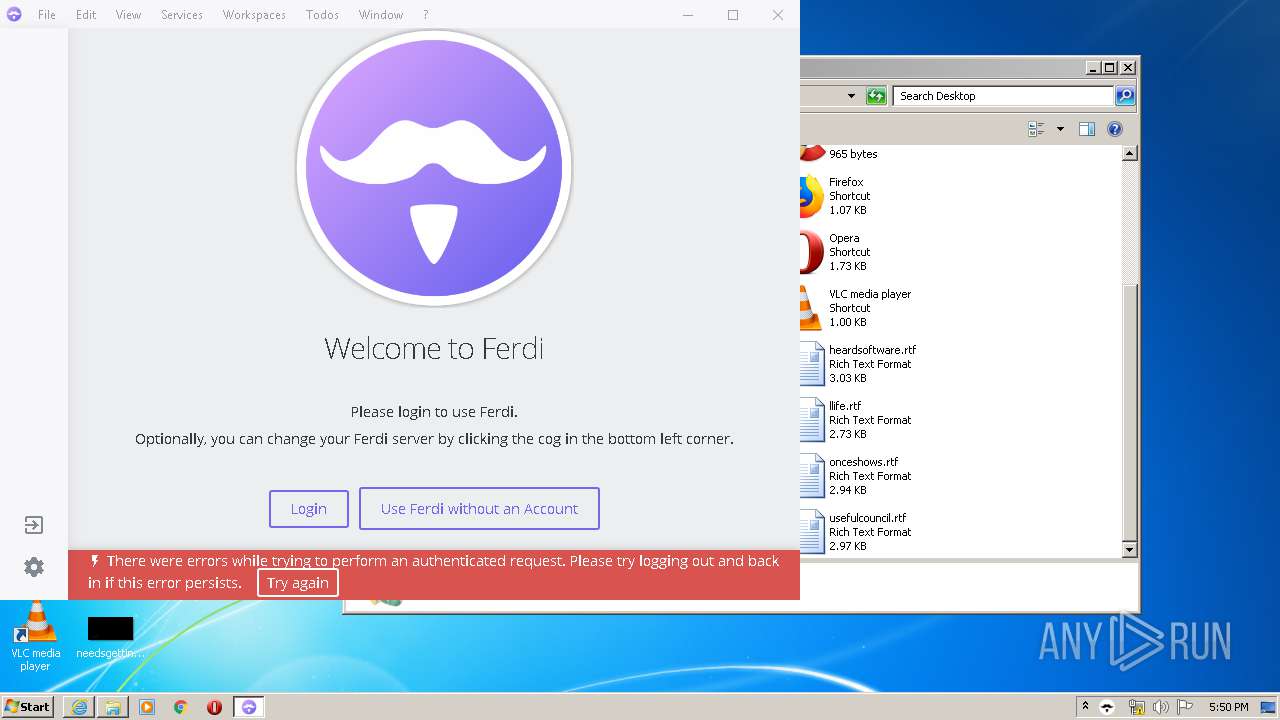
Application launched itself
- Ferdi.exe (PID: 2068)
Executable content was dropped or overwritten
- Ferdi-5.4.3.exe (PID: 1836)
- Ferdi.exe (PID: 2068)
- Ferdi.exe (PID: 2340)
Uses REG.EXE to modify Windows registry
- Ferdi.exe (PID: 2340)
INFO
Application launched itself
- iexplore.exe (PID: 3568)
Reads Internet Cache Settings
- iexplore.exe (PID: 3568)
- iexplore.exe (PID: 580)
Changes internet zones settings
- iexplore.exe (PID: 3568)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3568)
Creates files in the user directory
- iexplore.exe (PID: 580)
- iexplore.exe (PID: 3568)
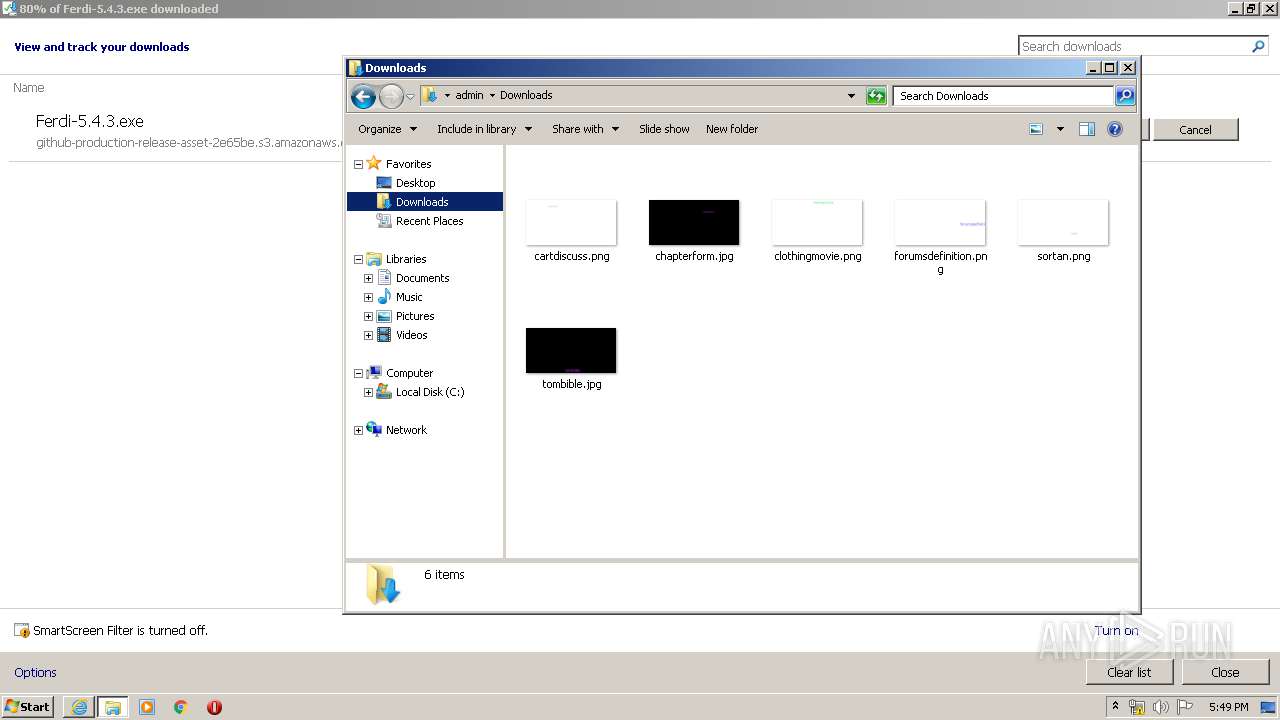
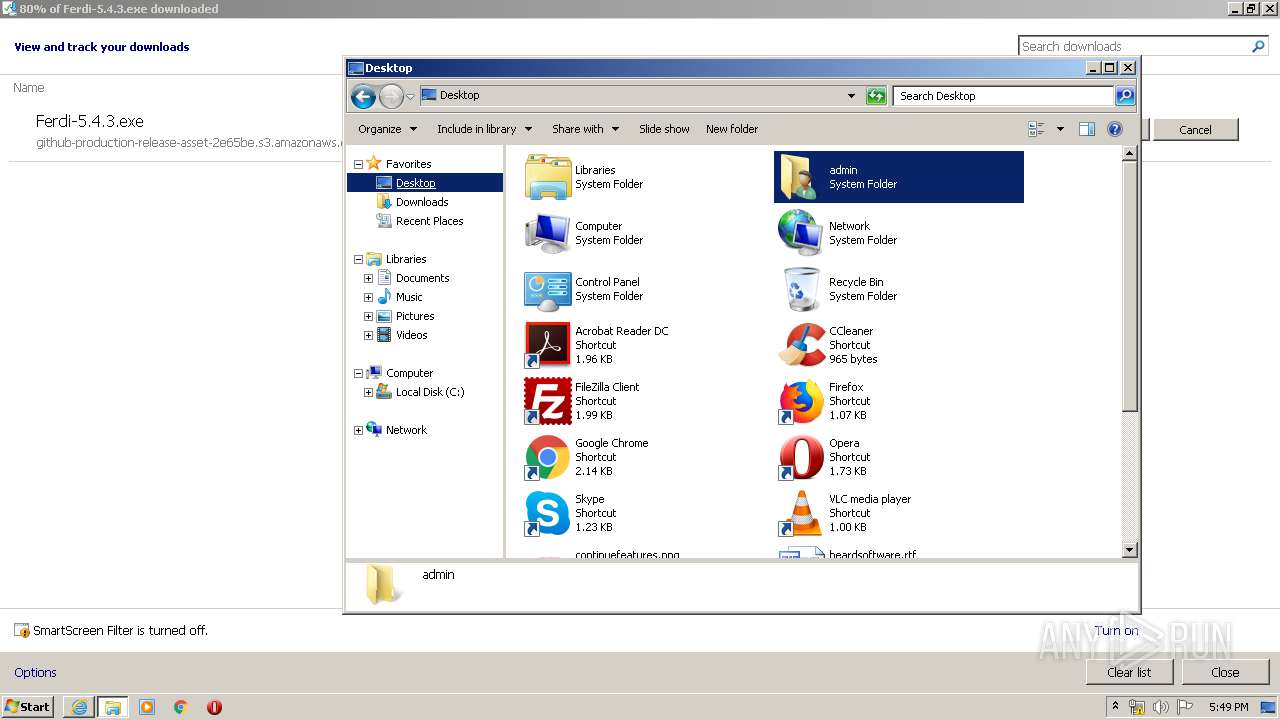
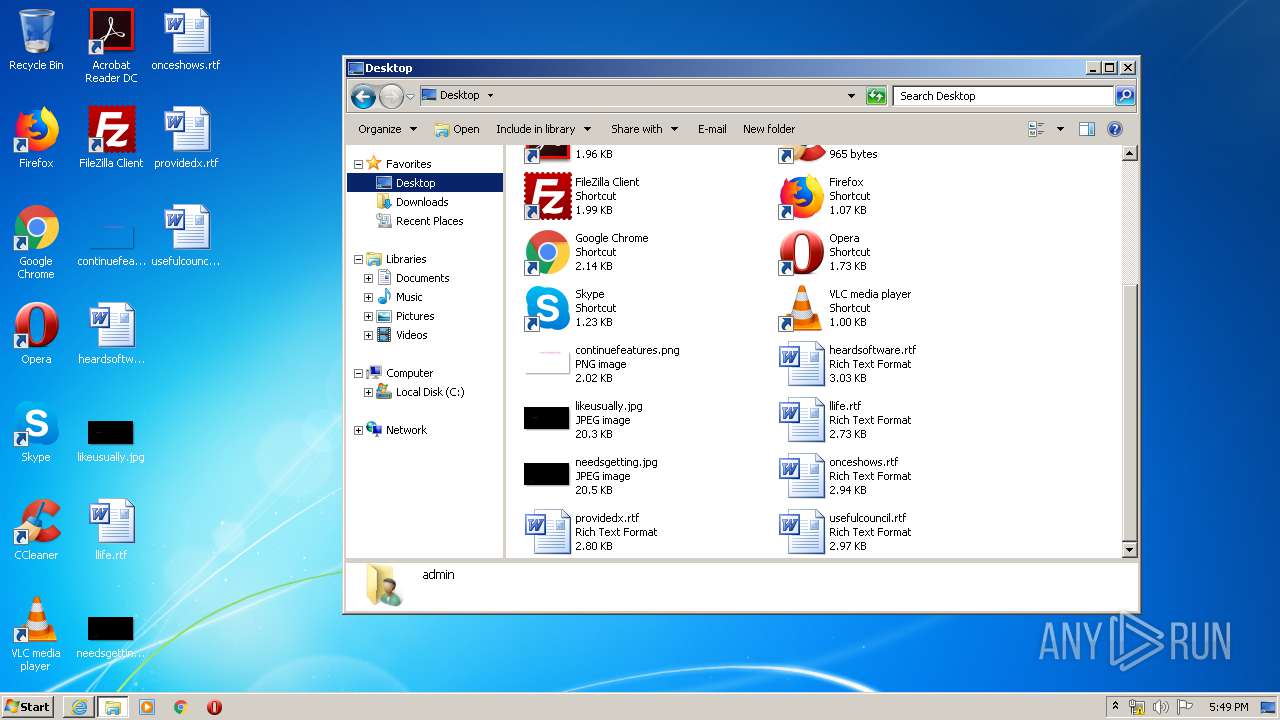
Manual execution by user
- explorer.exe (PID: 2872)
Reads the hosts file
- Ferdi.exe (PID: 2068)
- Ferdi.exe (PID: 3120)
Reads settings of System Certificates
- iexplore.exe (PID: 580)
- iexplore.exe (PID: 3568)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3568)
Changes settings of System certificates
- iexplore.exe (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
14
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | C:\Windows\system32\reg.exe QUERY HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v Ferdi | C:\Windows\system32\reg.exe | — | Ferdi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3568 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1756 | "C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe" --type=gpu-process --field-trial-handle=1084,9573011722389434417,1185983376300687113,131072 --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --service-request-channel-token=11537352761536434904 --mojo-platform-channel-handle=1108 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | — | Ferdi.exe | |||||||||||
User: admin Company: Amine Mouafik Integrity Level: LOW Description: Ferdi Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
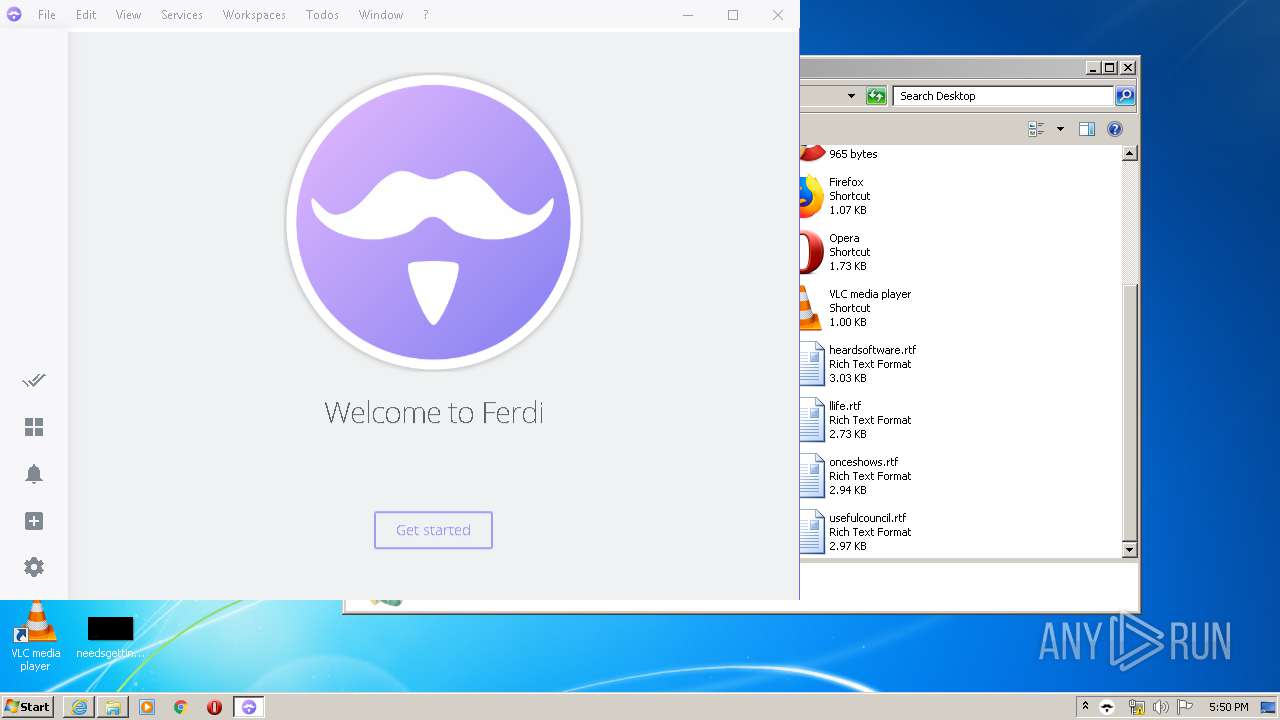
| 1836 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Ferdi-5.4.3.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Ferdi-5.4.3.exe | iexplore.exe | ||||||||||||
User: admin Company: Amine Mouafik Integrity Level: MEDIUM Description: Messaging app for WhatsApp, Slack, Telegram, HipChat, Hangouts and many many more. Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
| 2068 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | Ferdi-5.4.3.exe | ||||||||||||
User: admin Company: Amine Mouafik Integrity Level: MEDIUM Description: Ferdi Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
| 2308 | "C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe" --type=renderer --field-trial-handle=1084,9573011722389434417,1185983376300687113,131072 --disable-features=SpareRendererForSitePerProcess --disable-gpu-compositing --lang=en-US --app-user-model-id=com.kytwb.ferdi --app-path="C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\resources\app.asar\features\todos\preload.js" --background-color=#fff --guest-instance-id=3 --enable-blink-features --disable-blink-features --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=735512269456570174 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2164 /prefetch:1 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | — | Ferdi.exe | |||||||||||
User: admin Company: Amine Mouafik Integrity Level: MEDIUM Description: Ferdi Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe" --type=renderer --field-trial-handle=1084,9573011722389434417,1185983376300687113,131072 --disable-features=SpareRendererForSitePerProcess --lang=en-US --app-user-model-id=com.kytwb.ferdi --app-path="C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\resources\app.asar" --node-integration --webview-tag --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\resources\app.asar\sentry.js" --background-color=#7367F0 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=455743706864619721 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1712 /prefetch:1 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | Ferdi.exe | ||||||||||||
User: admin Company: Amine Mouafik Integrity Level: MEDIUM Description: Ferdi Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
| 2872 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe" --type=gpu-process --field-trial-handle=1084,9573011722389434417,1185983376300687113,131072 --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3378973736605790212 --mojo-platform-channel-handle=1108 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | — | Ferdi.exe | |||||||||||
User: admin Company: Amine Mouafik Integrity Level: LOW Description: Ferdi Exit code: 4 Version: 5.4.3.1002 Modules
| |||||||||||||||
| 3120 | "C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe" --type=utility --field-trial-handle=1084,9573011722389434417,1185983376300687113,131072 --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --service-request-channel-token=10216275539560907241 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Users\admin\AppData\Local\Temp\1X4hyf0HizxPyJsprw3CBf7uwGY\Ferdi.exe | Ferdi.exe | ||||||||||||
User: admin Company: Amine Mouafik Integrity Level: MEDIUM Description: Ferdi Exit code: 0 Version: 5.4.3.1002 Modules
| |||||||||||||||
Total events
9 373
Read events
1 891
Write events
4 999
Delete events
2 483
Modification events
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1656897990 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30808060 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3568) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
22
Suspicious files
135
Text files
158
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF4E7.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF4E8.tmp | — | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\86FAP2B5.txt | — | |
MD5:— | SHA256:— | |||
| 580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Ferdi-5.4.3[1].exe | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab349B.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar349C.tmp | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5EEJNDKY.txt | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5V5DZYFV.txt | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver34FB.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
37
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
580 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAGC%2BAmOouYmuRo7J4Qfua8%3D | US | der | 1.47 Kb | whitelisted |
580 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 564 b | whitelisted |
3568 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
3568 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3568 | iexplore.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
580 | iexplore.exe | 140.82.118.4:443 | github.com | — | US | malicious |
580 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3568 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3568 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3568 | iexplore.exe | 72.21.91.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1052 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 140.82.118.6:443 | api.github.com | — | US | suspicious |
3120 | Ferdi.exe | 104.31.80.187:443 | api.getferdi.com | Cloudflare Inc | US | shared |
3120 | Ferdi.exe | 52.216.144.227:443 | github-production-release-asset-2e65be.s3.amazonaws.com | Amazon.com, Inc. | US | unknown |
3120 | Ferdi.exe | 140.82.118.4:443 | github.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
github-production-release-asset-2e65be.s3.amazonaws.com |
| shared |
crl4.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |