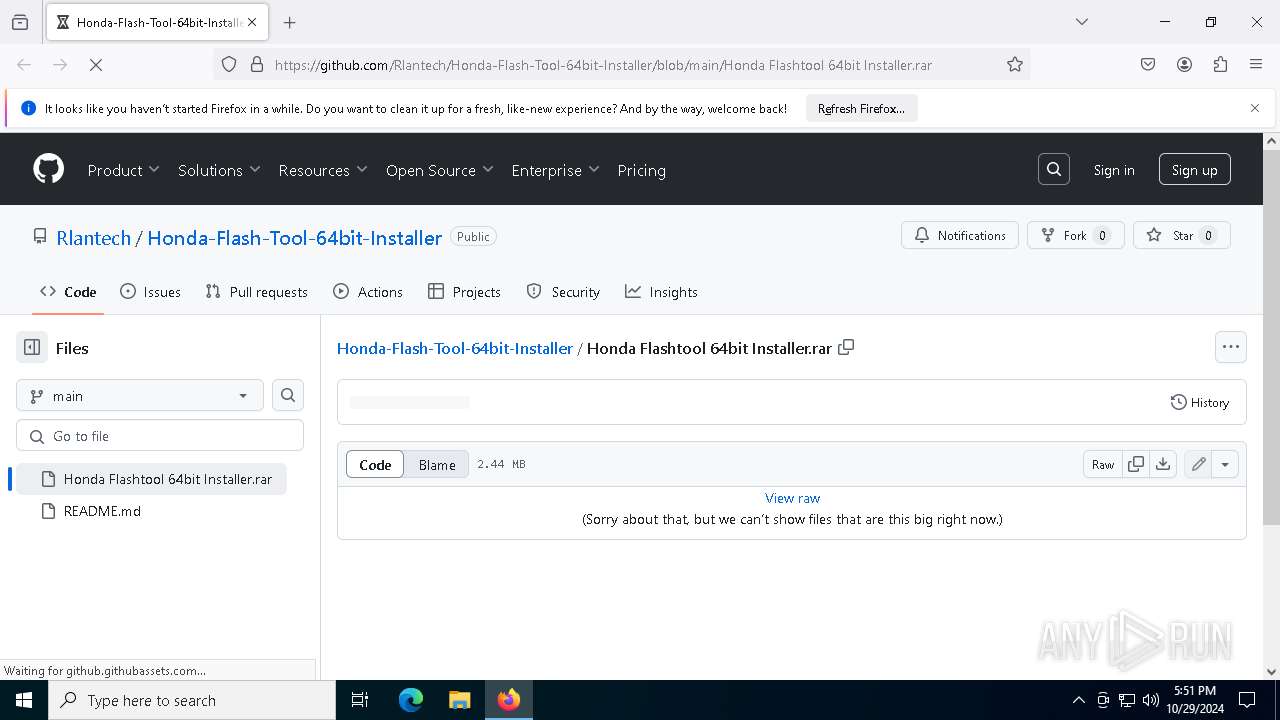
| URL: | https://github.com/Rlantech/Honda-Flash-Tool-64bit-Installer/blob/main/Honda%20Flashtool%2064bit%20Installer.rar |
| Full analysis: | https://app.any.run/tasks/8b9cd9d6-bc63-4e70-af5e-ef0fd80a870c |
| Verdict: | Malicious activity |
| Analysis date: | October 29, 2024, 17:50:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E460E3FBC87DE932BA8A650A9E51C13E |
| SHA1: | 50FE83706932B2F95EAE9797CB61EE64EB34B029 |
| SHA256: | BA2DEE71A875F37E186F6F4C9DC9BD63B0FCA03CFEEC56D46A319C9B44D26C98 |
| SSDEEP: | 3:N8tEdpi+tUDyMxdsiigXKHJMERmwRHVXLO:2uEdsiTXTs7VXLO |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- firefox.exe (PID: 4548)
- firefox.exe (PID: 612)
Executable content was dropped or overwritten
- firefox.exe (PID: 612)
- WinRAR.exe (PID: 1204)
Manual execution by a user
- WinRAR.exe (PID: 1204)
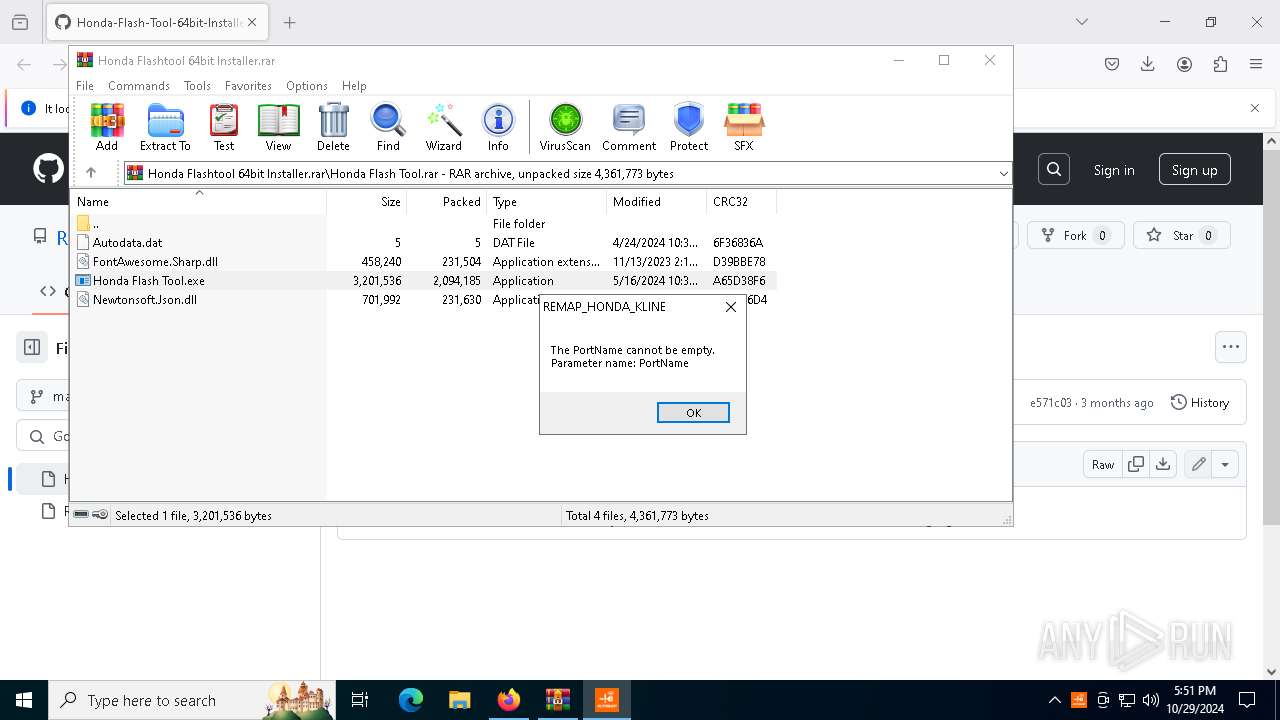
VMProtect protector has been detected
- Honda Flash Tool.exe (PID: 4228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 612 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/Rlantech/Honda-Flash-Tool-64bit-Installer/blob/main/Honda%20Flashtool%2064bit%20Installer.rar | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
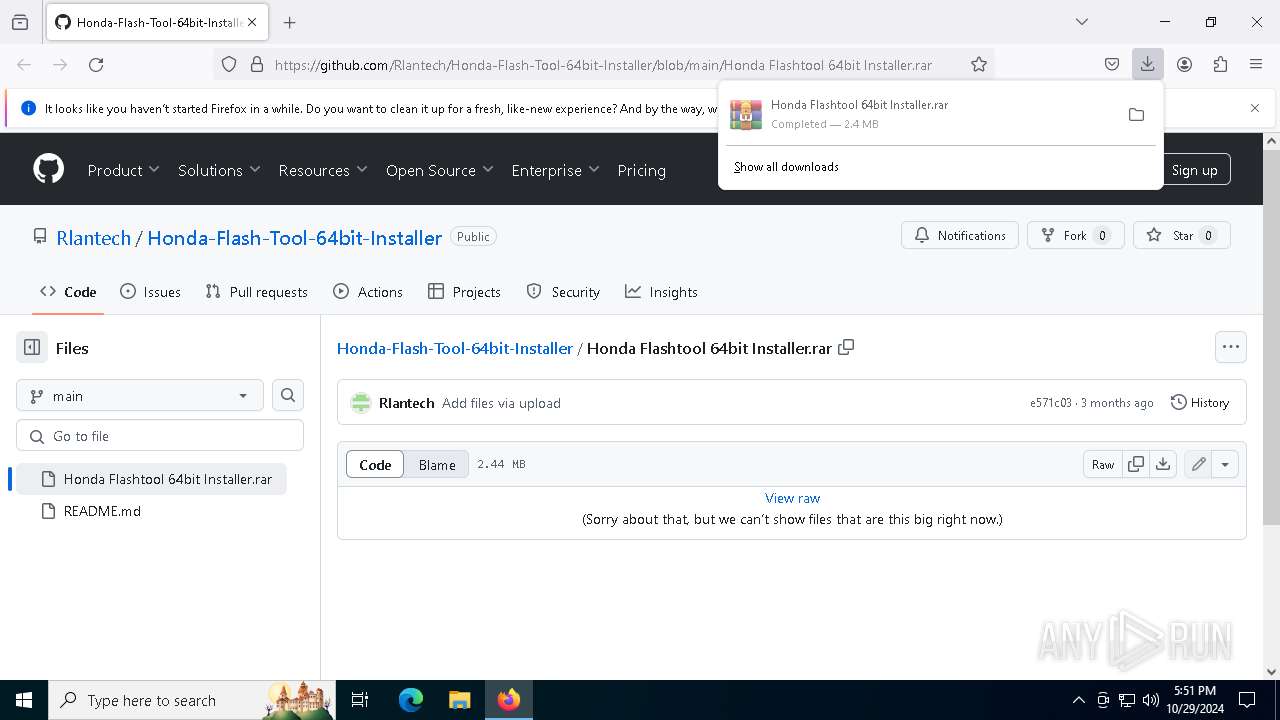
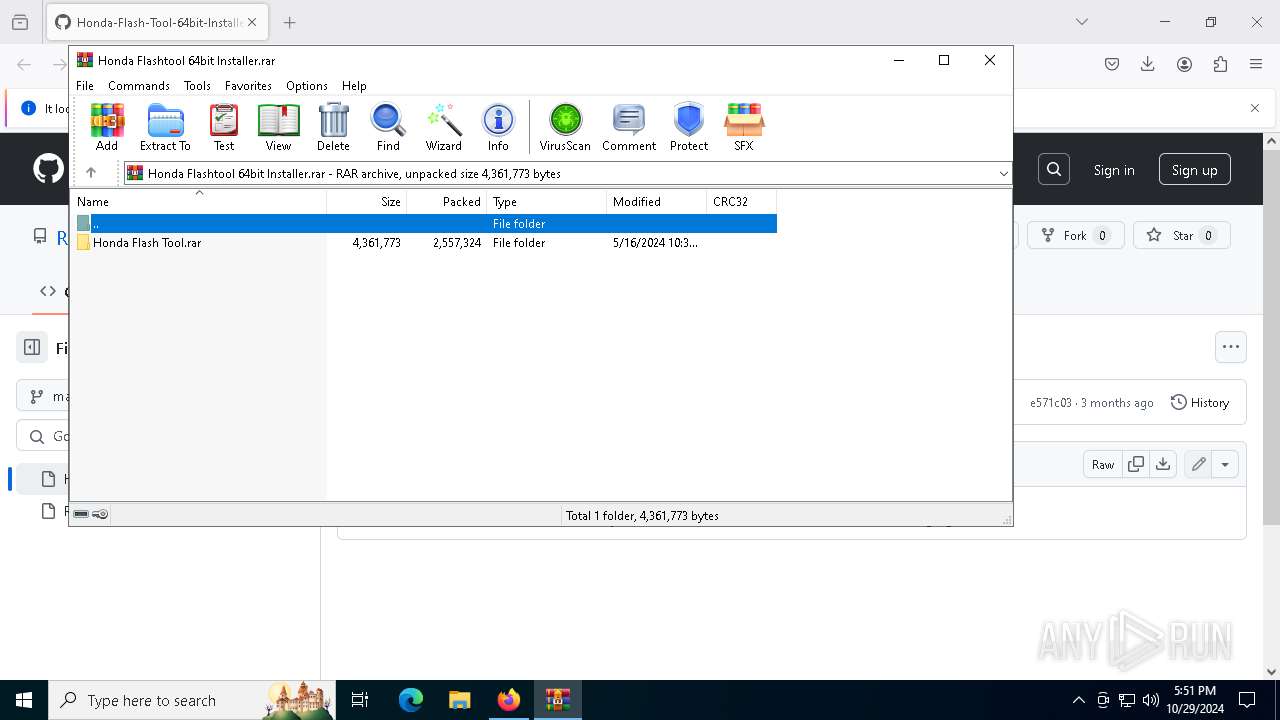
| 1204 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Honda Flashtool 64bit Installer.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 | |||||||||||||||
| 1732 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4468 -childID 2 -isForBrowser -prefsHandle 4460 -prefMapHandle 4456 -prefsLen 36339 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {2f950a28-e1b0-486f-8907-201c028d89be} 612 "\\.\pipe\gecko-crash-server-pipe.612" 1d967db7d90 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
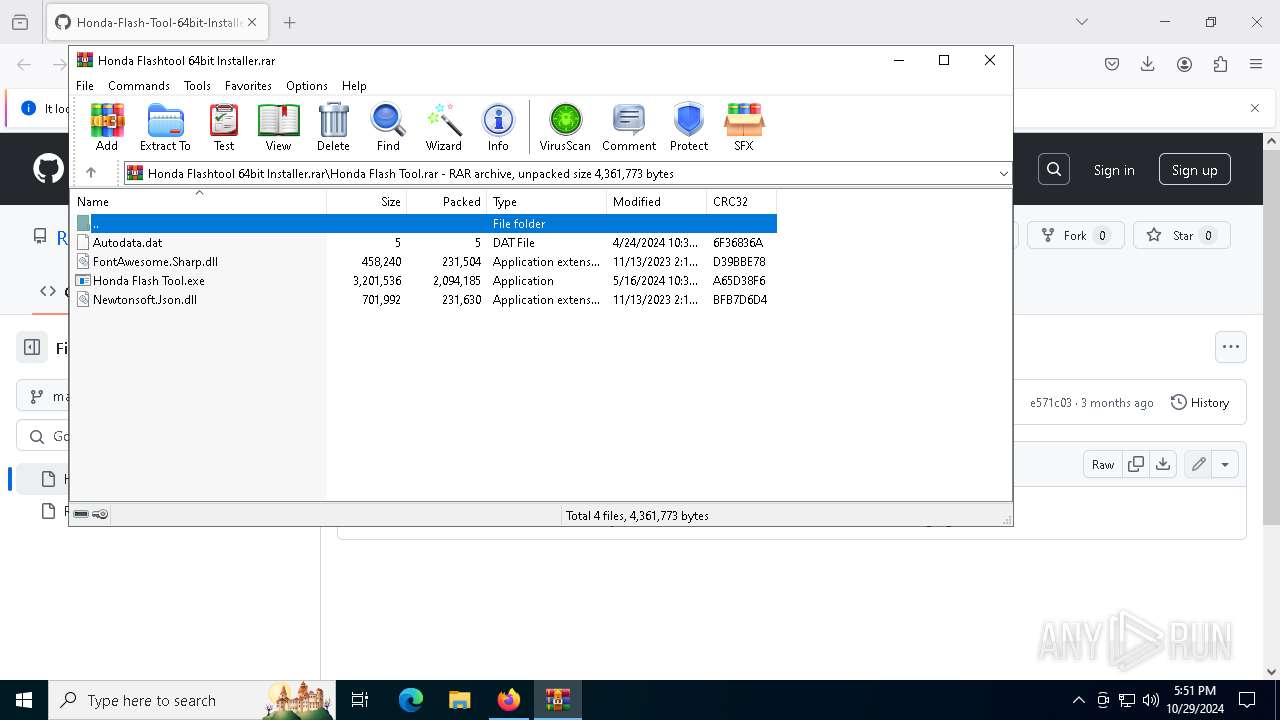
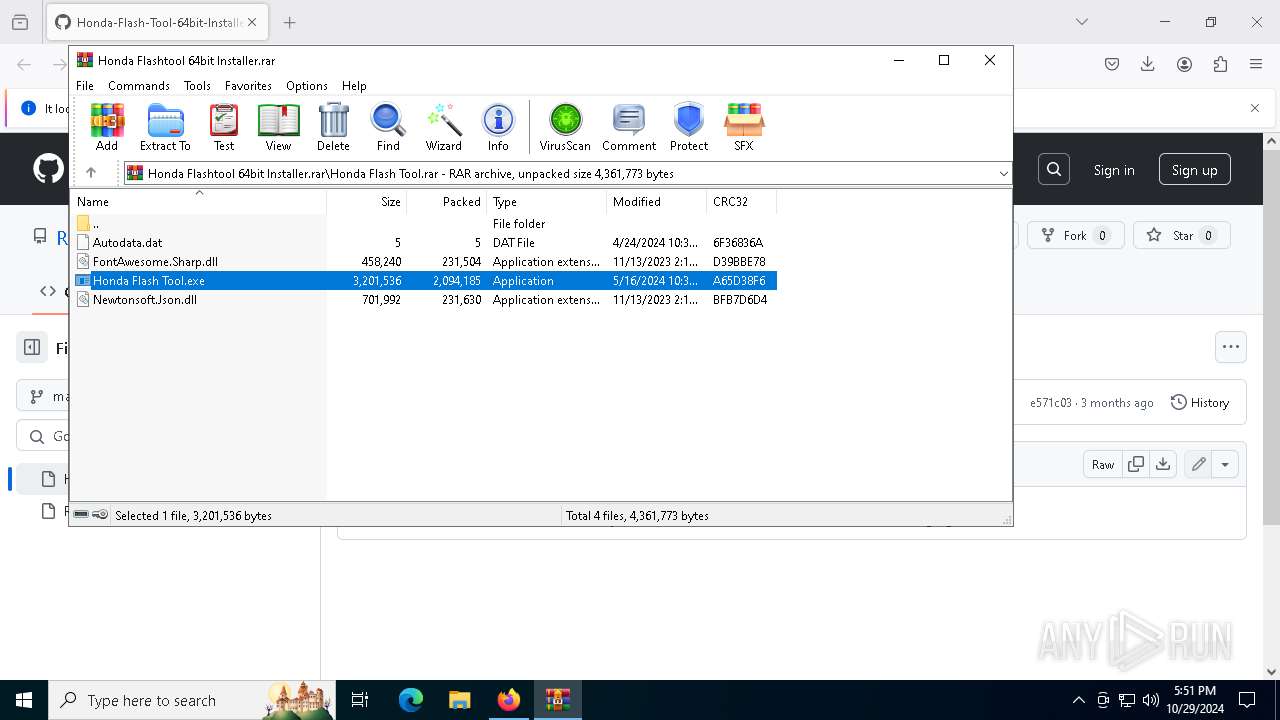
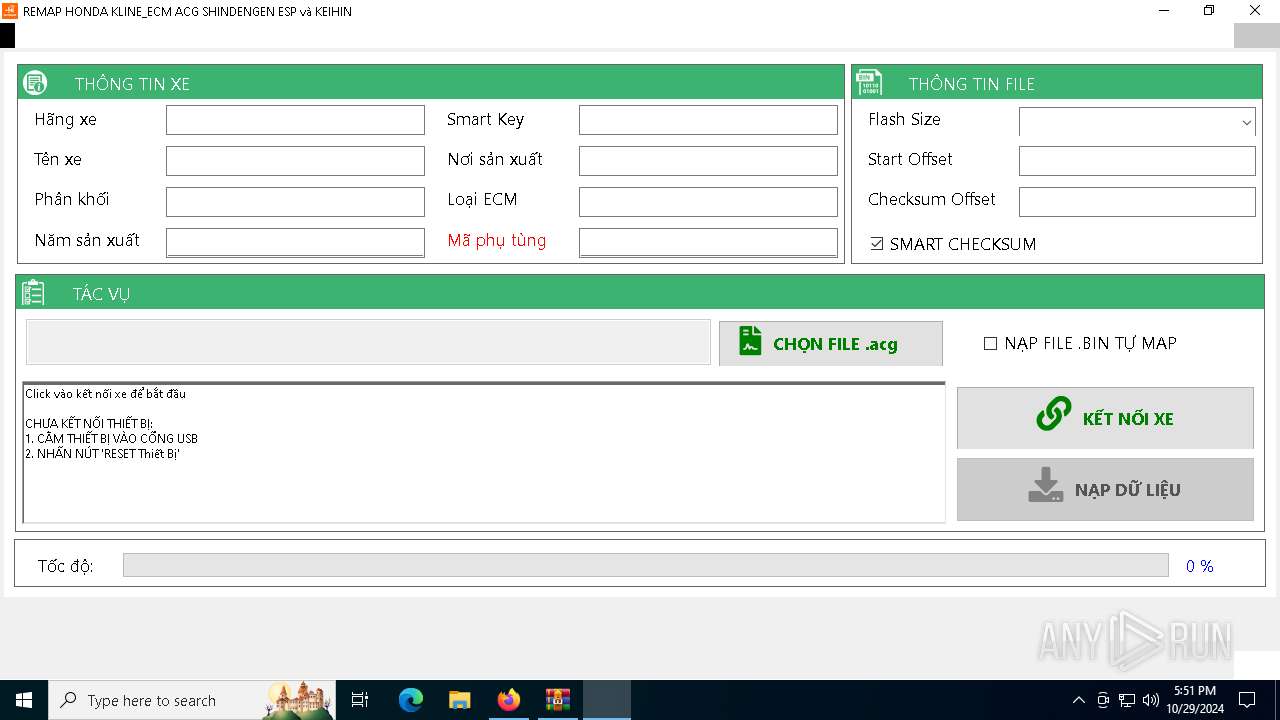
| 4228 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1204.8640\Honda Flash Tool.rar\Honda Flash Tool.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1204.8640\Honda Flash Tool.rar\Honda Flash Tool.exe | WinRAR.exe | ||||||||||||
User: admin Company: AUTOSHOP VIETNAM Integrity Level: HIGH Description: REMAP & DIAGNOSTIC HONDA Version: 6.8.1.0 | |||||||||||||||
| 4232 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1204.8640\Honda Flash Tool.rar\Honda Flash Tool.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1204.8640\Honda Flash Tool.rar\Honda Flash Tool.exe | — | WinRAR.exe | |||||||||||
User: admin Company: AUTOSHOP VIETNAM Integrity Level: MEDIUM Description: REMAP & DIAGNOSTIC HONDA Exit code: 3221226540 Version: 6.8.1.0 | |||||||||||||||
| 4548 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/Rlantech/Honda-Flash-Tool-64bit-Installer/blob/main/Honda%20Flashtool%2064bit%20Installer.rar" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 4584 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 1 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 5848 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 5940 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2192 -parentBuildID 20240213221259 -prefsHandle 2184 -prefMapHandle 2172 -prefsLen 30705 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {a40f36fd-402a-4ec9-8185-6b784bb68828} 612 "\\.\pipe\gecko-crash-server-pipe.612" 1d955182310 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 6216 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2880 -childID 1 -isForBrowser -prefsHandle 2736 -prefMapHandle 2820 -prefsLen 26798 -prefMapSize 244343 -jsInitHandle 1288 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {66e77e49-81c3-47b6-b9f5-3bc45710717c} 612 "\\.\pipe\gecko-crash-server-pipe.612" 1d966d86150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
11 577
Read events
11 576
Write events
1
Delete events
0
Modification events
| (PID) Process: | (612) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
Executable files
10
Suspicious files
268
Text files
199
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 612 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:C09FF302D57C404B61E6A89B0B9F36E7 | SHA256:6A5B4F82595799346D0E501FE6CC8629E0FD6ED27B74D0E6CB5073DDB2E3C40B | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | dbf | |
MD5:F759EB25271E6A6F0A3500520813E5FE | SHA256:015E515D432DD64FDC9502ABE9C723EEF544E7AF11C36BDFE8B38412597CA1EC | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:158D3F69D8E0433C6B9ECDE87FA4C723 | SHA256:6E8BCE86CE896E2C916DA893198908D66157C5E8F07C0BB07270D5EC59FEE37D | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:3AD7AA1AC92323459BF103D2FE6C1AD3 | SHA256:2F607625BDCD86E2C74DFD380F7F5845119963B20383C9002C3A455B1B8A6B1E | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 612 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:081E853FC984F0A46DA6F39B318B48C3 | SHA256:028A72A3B47994BCBE861663CD1C6120D5F52F2C511E3EA2451254998A54A6EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
37
TCP/UDP connections
113
DNS requests
148
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 216.58.212.131:80 | http://o.pki.goog/s/wr3/yvU | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.48:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.48:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.48:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 140.82.121.3:443 | github.com | GITHUB | US | shared |
— | — | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
— | — | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
— | — | 104.18.38.233:80 | ocsp.sectigo.com | CLOUDFLARENET | — | whitelisted |
— | — | 216.58.212.131:80 | o.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | A Network Trojan was detected | ET HUNTING Terse Unencrypted Request for Google - Likely Connectivity Check |