| File name: | moscow.msi |
| Full analysis: | https://app.any.run/tasks/4364327f-10e5-4cc8-8400-8761e47a8239 |
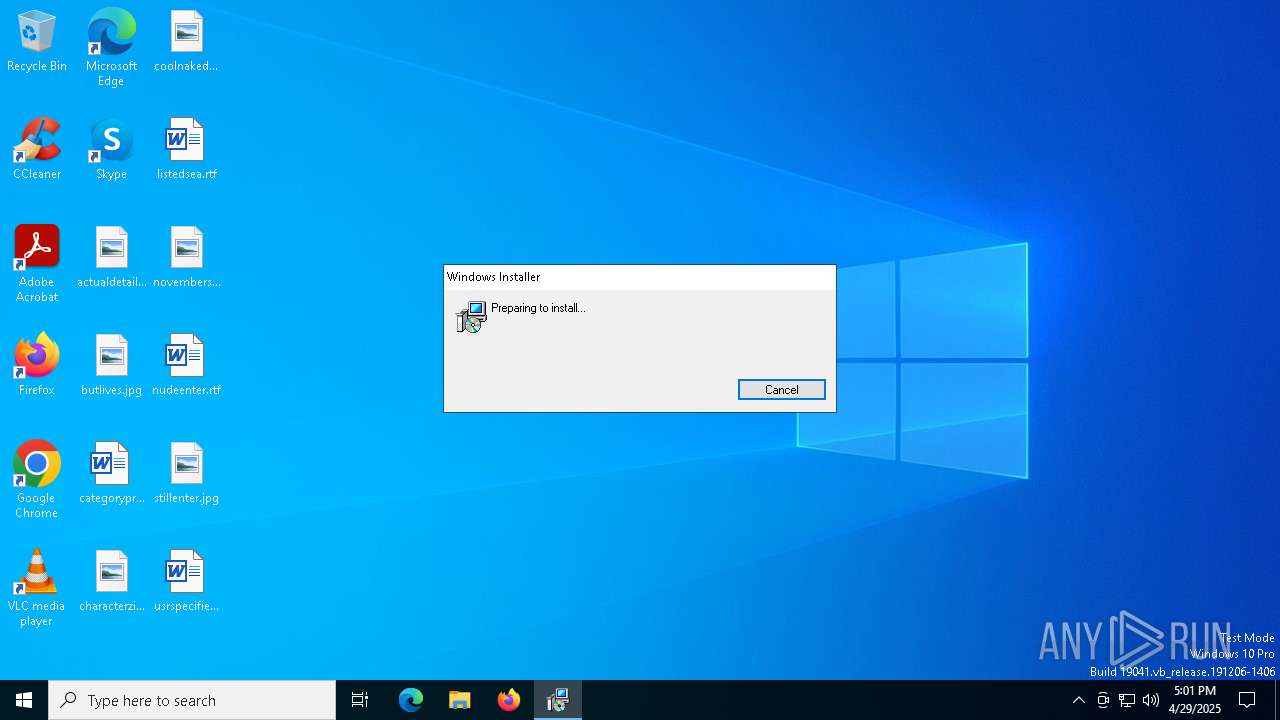
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 17:00:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Number of Characters: 0, Last Saved By: InstallShield, Number of Words: 0, Title: Installation Database, Comments: Contact: Your local administrator, Keywords: Installer,MSI,Database, Subject: Blank Project Template, Author: InstallShield, Security: 1, Number of Pages: 200, Name of Creating Application: InstallShield 2021 - Premier Edition with Virtualization Pack 27, Last Saved Time/Date: Tue Apr 29 11:30:32 2025, Create Time/Date: Tue Apr 29 11:30:32 2025, Last Printed: Tue Apr 29 11:30:32 2025, Revision Number: {5A084ED2-691D-4A04-B93C-2850E4B0C026}, Code page: 1252, Template: Intel;1033 |
| MD5: | 885FD8B5A32DD2FA8EC90922EADD4693 |
| SHA1: | 8E5A2DDA6C30D1C84AA8D0BD214F64C97917C033 |
| SHA256: | BA25A9AA28FDA73323BEB643CD4E9F638CEB6D5E1C61459E133D41763C8C57C9 |
| SSDEEP: | 98304:DzntBCaM15O+FBJV09+Z8jdOf1pwvusWI6ZD/Utk1ojWm3SRFcW0u891tI8ctDRx:/ca7hgUZuz |
MALICIOUS
GENERIC has been found (auto)
- msiexec.exe (PID: 7416)
- S-Cobalt.exe (PID: 7936)
Executing a file with an untrusted certificate
- ISBEW64.exe (PID: 7516)
- ISBEW64.exe (PID: 7556)
- ISBEW64.exe (PID: 7596)
- ISBEW64.exe (PID: 7636)
- ISBEW64.exe (PID: 7676)
- ISBEW64.exe (PID: 7724)
- ISBEW64.exe (PID: 7776)
- ISBEW64.exe (PID: 7812)
- ISBEW64.exe (PID: 7852)
- ISBEW64.exe (PID: 7896)
SUSPICIOUS
The process drops C-runtime libraries
- msiexec.exe (PID: 7416)
- S-Cobalt.exe (PID: 7936)
Process drops legitimate windows executable
- msiexec.exe (PID: 7416)
- S-Cobalt.exe (PID: 7936)
Starts itself from another location
- S-Cobalt.exe (PID: 7936)
Executable content was dropped or overwritten
- S-Cobalt.exe (PID: 7936)
- S-Cobalt.exe (PID: 7972)
Reads the date of Windows installation
- Archiveadvanced_alpha.exe (PID: 4000)
Starts CMD.EXE for commands execution
- S-Cobalt.exe (PID: 7972)
INFO
Executable content was dropped or overwritten
- msiexec.exe (PID: 7416)
- msiexec.exe (PID: 7312)
Create files in a temporary directory
- msiexec.exe (PID: 7416)
- S-Cobalt.exe (PID: 7972)
The sample compiled with english language support
- msiexec.exe (PID: 7416)
- msiexec.exe (PID: 7312)
- S-Cobalt.exe (PID: 7936)
Reads the computer name
- msiexec.exe (PID: 7416)
- msiexec.exe (PID: 7376)
- ISBEW64.exe (PID: 7516)
- ISBEW64.exe (PID: 7556)
- ISBEW64.exe (PID: 7596)
- ISBEW64.exe (PID: 7636)
- ISBEW64.exe (PID: 7724)
- ISBEW64.exe (PID: 7776)
- ISBEW64.exe (PID: 7676)
- S-Cobalt.exe (PID: 7936)
- S-Cobalt.exe (PID: 7972)
- ISBEW64.exe (PID: 7812)
- ISBEW64.exe (PID: 7852)
- ISBEW64.exe (PID: 7896)
- Archiveadvanced_alpha.exe (PID: 4000)
An automatically generated document
- msiexec.exe (PID: 7312)
Checks supported languages
- msiexec.exe (PID: 7416)
- msiexec.exe (PID: 7376)
- ISBEW64.exe (PID: 7516)
- ISBEW64.exe (PID: 7556)
- ISBEW64.exe (PID: 7596)
- ISBEW64.exe (PID: 7676)
- ISBEW64.exe (PID: 7724)
- ISBEW64.exe (PID: 7776)
- ISBEW64.exe (PID: 7812)
- ISBEW64.exe (PID: 7636)
- ISBEW64.exe (PID: 7896)
- S-Cobalt.exe (PID: 7936)
- S-Cobalt.exe (PID: 7972)
- ISBEW64.exe (PID: 7852)
- Archiveadvanced_alpha.exe (PID: 4000)
Creates files in the program directory
- S-Cobalt.exe (PID: 7936)
Reads the machine GUID from the registry
- Archiveadvanced_alpha.exe (PID: 4000)
Reads the software policy settings
- Archiveadvanced_alpha.exe (PID: 4000)
Checks proxy server information
- Archiveadvanced_alpha.exe (PID: 4000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .mst | | | Windows SDK Setup Transform Script (60.2) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Characters: | - |
|---|---|
| LastModifiedBy: | InstallShield |
| Words: | - |
| Title: | Installation Database |
| Comments: | Contact: Your local administrator |
| Keywords: | Installer,MSI,Database |
| Subject: | Blank Project Template |
| Author: | InstallShield |
| Security: | Password protected |
| Pages: | 200 |
| Software: | InstallShield? 2021 - Premier Edition with Virtualization Pack 27 |
| ModifyDate: | 2025:04:29 11:30:32 |
| CreateDate: | 2025:04:29 11:30:32 |
| LastPrinted: | 2025:04:29 11:30:32 |
| RevisionNumber: | {5A084ED2-691D-4A04-B93C-2850E4B0C026} |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;1033 |
Total processes
147
Monitored processes
20
Malicious processes
3
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4000 | C:\Users\admin\AppData\Local\Temp\Archiveadvanced_alpha.exe | C:\Users\admin\AppData\Local\Temp\Archiveadvanced_alpha.exe | S-Cobalt.exe | ||||||||||||
User: admin Company: Nenad Hrg (SoftwareOK.com) Integrity Level: MEDIUM Description: Q-Dir Version: 11,4,4,0 Modules
| |||||||||||||||
| 4120 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | S-Cobalt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7312 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\moscow.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1603 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7416 | C:\Windows\syswow64\MsiExec.exe -Embedding 45835F8A0F79D241980F0E3CFAA981EB C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7516 | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{5CFC7A71-00F1-4DE6-BF96-A8CA91160B16} | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7556 | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{9819C151-EA7F-4542-BBD8-E9EDD143F66D} | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7596 | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{7F77ED3C-2309-41A8-90EF-534A1976B796} | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7636 | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe {EFB7539B-24F3-46B6-AF6E-3B021B51EFEF}:{3A673530-DB57-4704-99CD-4A2206A3B8A0} | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISBEW64.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 029
Read events
1 029
Write events
0
Delete events
0
Modification events
Executable files
15
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1E389B03-2ACC-4A31-9641-3FF0F5031EF0}\Kres.ym | — | |
MD5:— | SHA256:— | |||
| 7936 | S-Cobalt.exe | C:\ProgramData\powerlaunch_JYv3_x86\Kres.ym | — | |
MD5:— | SHA256:— | |||
| 7972 | S-Cobalt.exe | C:\Users\admin\AppData\Local\Temp\ED0E32E.tmp | — | |
MD5:— | SHA256:— | |||
| 7312 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSID1F8.tmp | executable | |
MD5:A0E940A3D3C1523416675125E3B0C07E | SHA256:B8FA7AA425E4084EA3721780A13D11E08B8D53D1C5414B73F22FAECA1BFD314F | |||
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1E389B03-2ACC-4A31-9641-3FF0F5031EF0}\msvcp140.dll | executable | |
MD5:E9F00DD8746712610706CBEFFD8DF0BD | SHA256:4CB882621A3D1C6283570447F842801B396DB1B3DCD2E01C2F7002EFD66A0A97 | |||
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\IsConfig.ini | text | |
MD5:0190E026BF516E9A38526A5D5534E4B6 | SHA256:4B31A19BA314BCE99E0A3A84A0B77B70FFEF3C831EEAD4084ABC3A76C53C0EAB | |||
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1E389B03-2ACC-4A31-9641-3FF0F5031EF0}\vcruntime140.dll | executable | |
MD5:A554E4F1ADDC0C2C4EBB93D66B790796 | SHA256:E610CDAC0A37147919032D0D723B967276C217FF06EA402F098696AB4112512A | |||
| 7312 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDAD2.tmp | executable | |
MD5:DB1D86F58DFC8A527F80983A91B85F3A | SHA256:21B2597ACFB28052DC210EB346758BC9C2B0D871EAC342E397DFB553C52E8F28 | |||
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\setup.inx | binary | |
MD5:9FA303D3F405AAF6F96929E42FBB87F3 | SHA256:A53282ADB18F8DFAF94AE9468ACC8C37DC1711A3AFC69E942A59FF766EBA6BDC | |||
| 7416 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{AA37CC2B-96BA-49DA-8C51-0D84C946562C}\ISRT.dll | executable | |
MD5:8AF02BF8E358E11CAEC4F2E7884B43CC | SHA256:58A724D23C63387A2DDA27CCFDBC8CA87FD4DB671BEA8BB636247667F6A5A11E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5512 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
— | — | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
softserver.cfd |
| unknown |