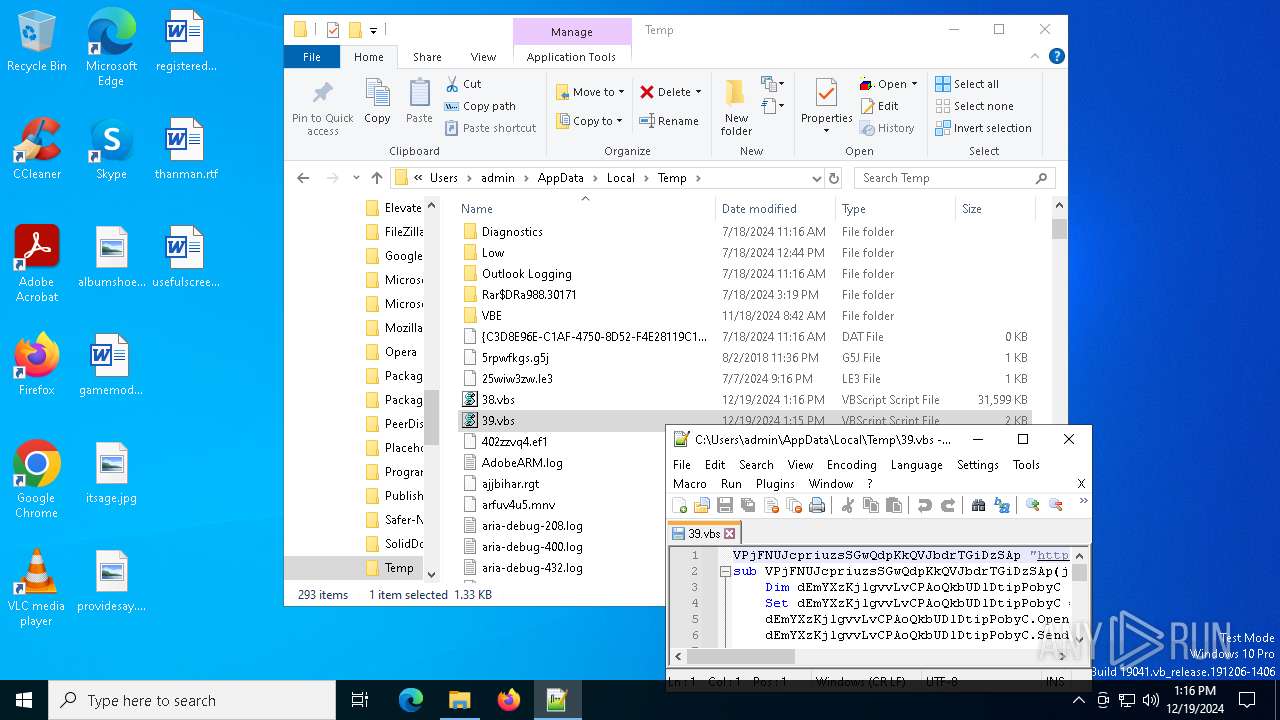
| File name: | temp.vbs |
| Full analysis: | https://app.any.run/tasks/003a6212-a720-4b9f-9c1e-be64aacdf460 |
| Verdict: | Malicious activity |
| Analysis date: | December 19, 2024, 13:15:32 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (690), with CRLF line terminators |
| MD5: | C6A3419678F5DA5320CE873ED39F9129 |
| SHA1: | 2F3A6AC89EFF5F7E5B15F987E8457A7A14605A0C |
| SHA256: | BA06A54D707D24BA9C587A7FFFD042BFA0B29A1C6E20F70A16AA30DA7982A1BC |
| SSDEEP: | 3072:y9p1ncgAzsEv+C9bPAjBTORDIwovu2dVBAwXbjoTVQ:EplcPRB9bPwBTkIwoGkVBAwXbjo5Q |
MALICIOUS
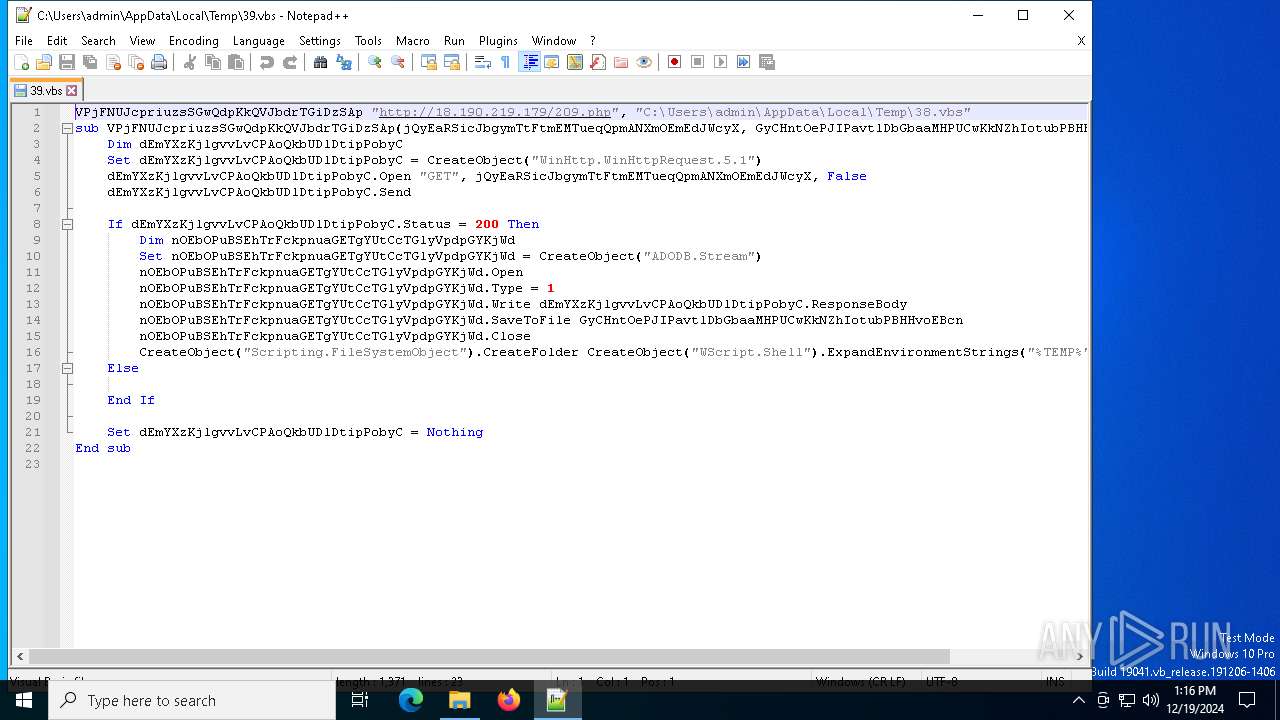
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3364)
- wscript.exe (PID: 6936)
Gets context to execute command-line operations (SCRIPT)
- wscript.exe (PID: 3364)
Access Task Scheduler's settings (SCRIPT)
- wscript.exe (PID: 3364)
Gets security context of the user (SCRIPT)
- wscript.exe (PID: 3364)
Gets or sets visibliity for the scheduled task (SCRIPT)
- wscript.exe (PID: 3364)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 3364)
Creates a new folder (SCRIPT)
- wscript.exe (PID: 6936)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 6936)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 6936)
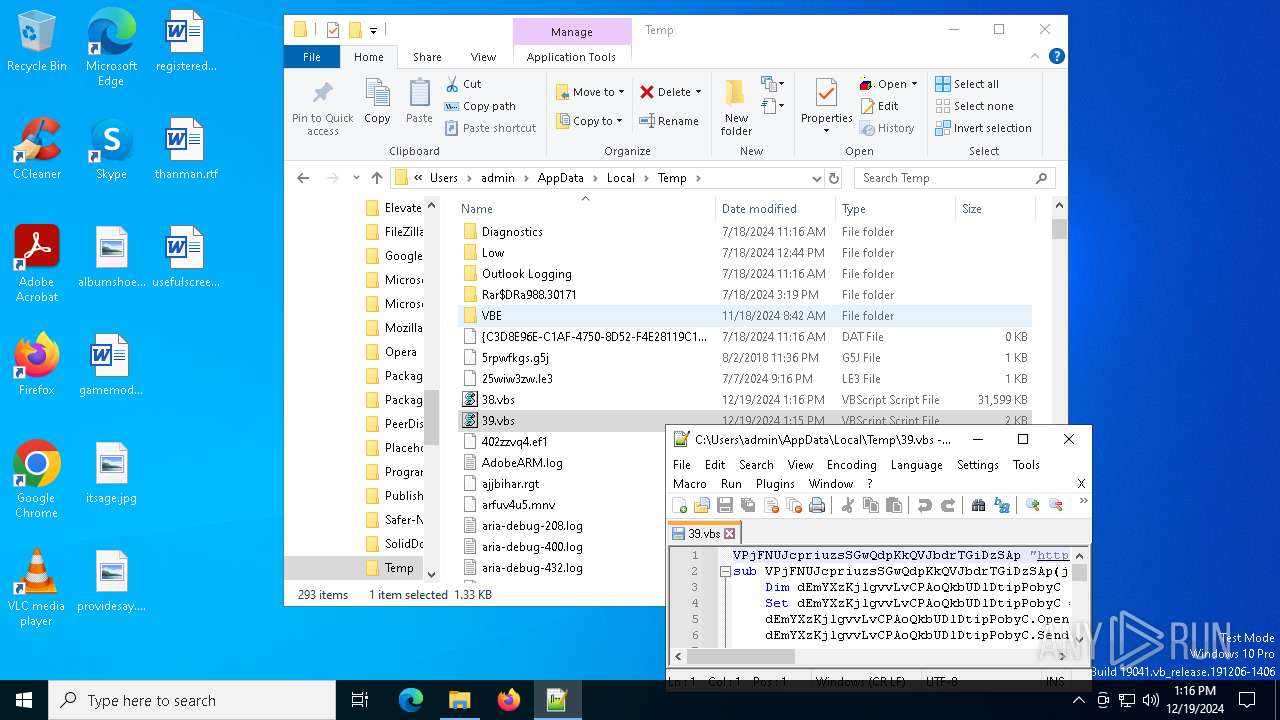
SUSPICIOUS
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 3364)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 3364)
- wscript.exe (PID: 6936)
Gets scheduled task context (SCRIPT)
- wscript.exe (PID: 3364)
Gets context to manipulate scheduled tasks (SCRIPT)
- wscript.exe (PID: 3364)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3364)
- wscript.exe (PID: 6936)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- wscript.exe (PID: 3364)
Accesses object representing scheduled task trigger (SCRIPT)
- wscript.exe (PID: 3364)
Accesses Scheduled Task settings (SCRIPT)
- wscript.exe (PID: 3364)
Gets or sets the principal for the task (SCRIPT)
- wscript.exe (PID: 3364)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3364)
- wscript.exe (PID: 6936)
- wscript.exe (PID: 2088)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 3364)
- wscript.exe (PID: 6936)
- wscript.exe (PID: 2088)
The process executes via Task Scheduler
- wscript.exe (PID: 6936)
- wscript.exe (PID: 2088)
Connects to the server without a host name
- wscript.exe (PID: 6936)
Accesses current user name via WMI (SCRIPT)
- wscript.exe (PID: 2088)
Accesses computer name via WMI (SCRIPT)
- wscript.exe (PID: 2088)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 2088)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 6936)
INFO
Manual execution by a user
- notepad++.exe (PID: 3552)
- notepad++.exe (PID: 4052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
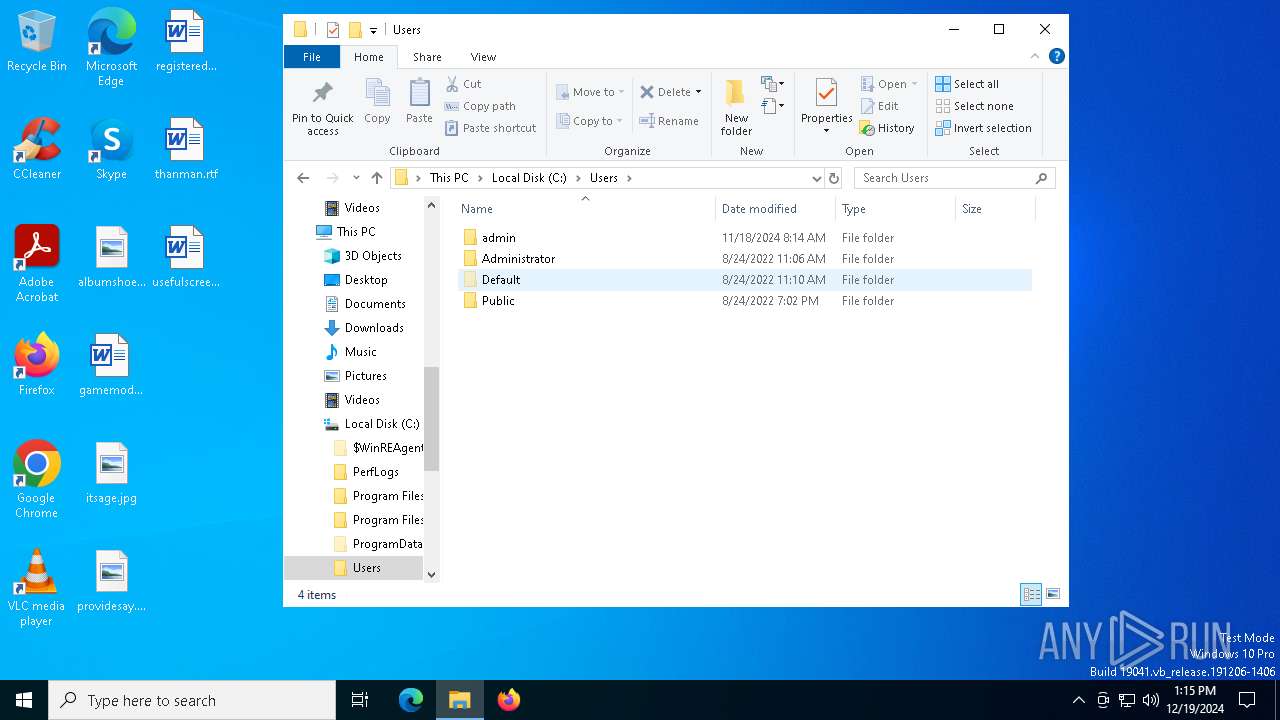
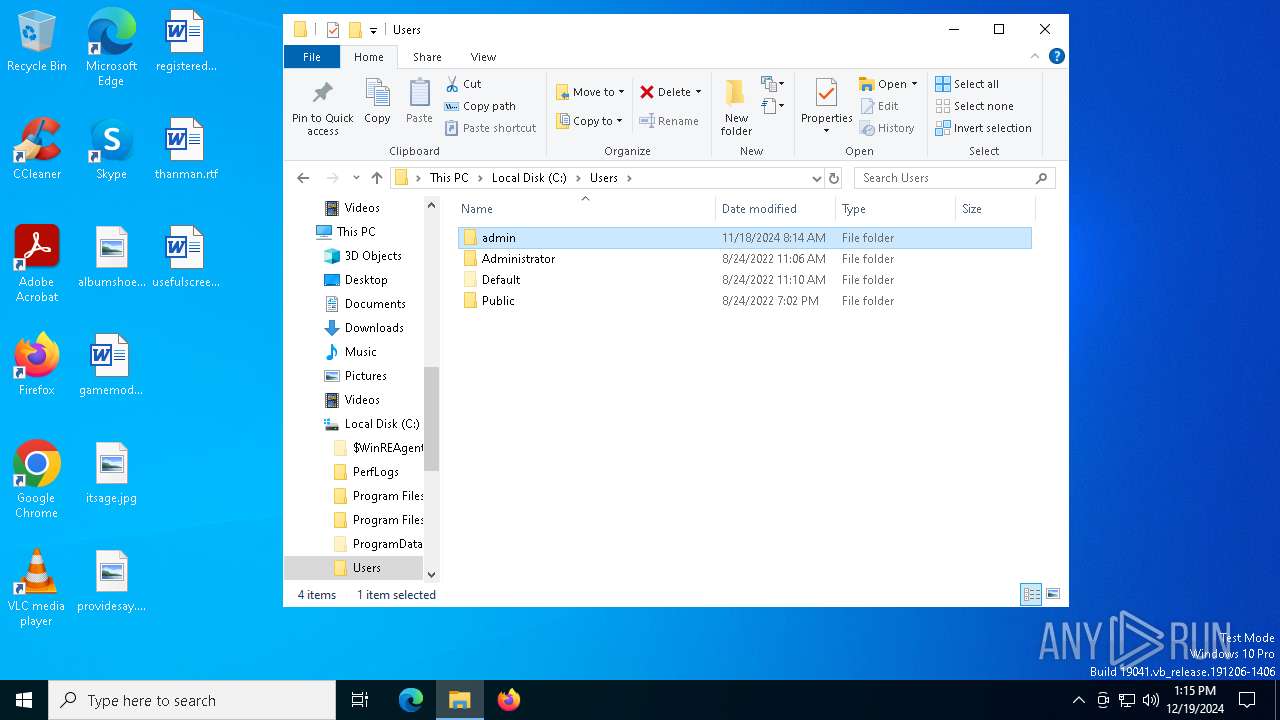
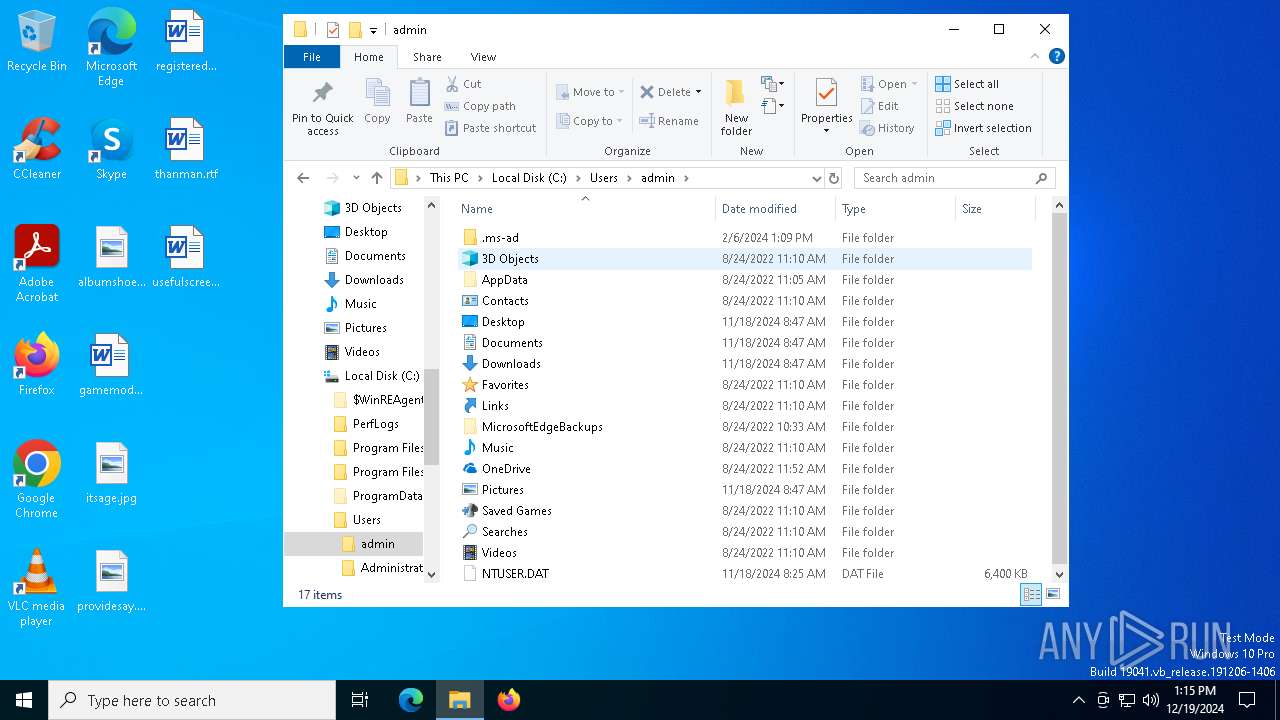
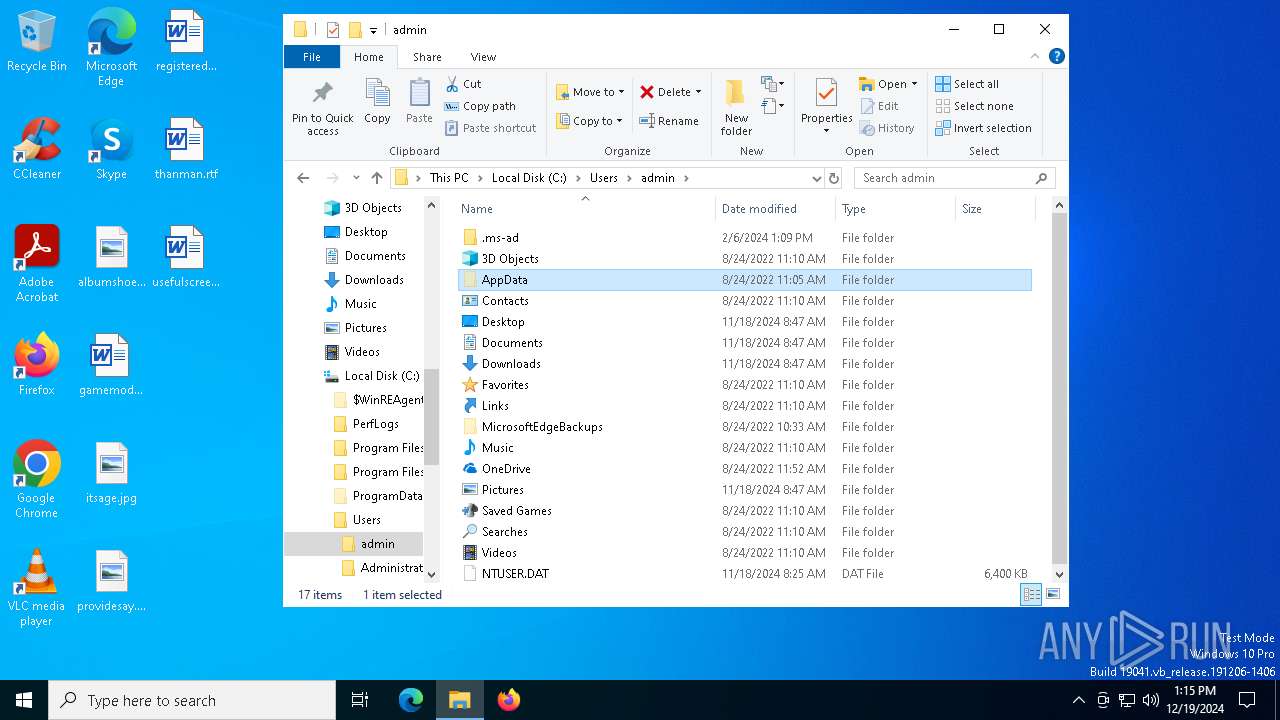
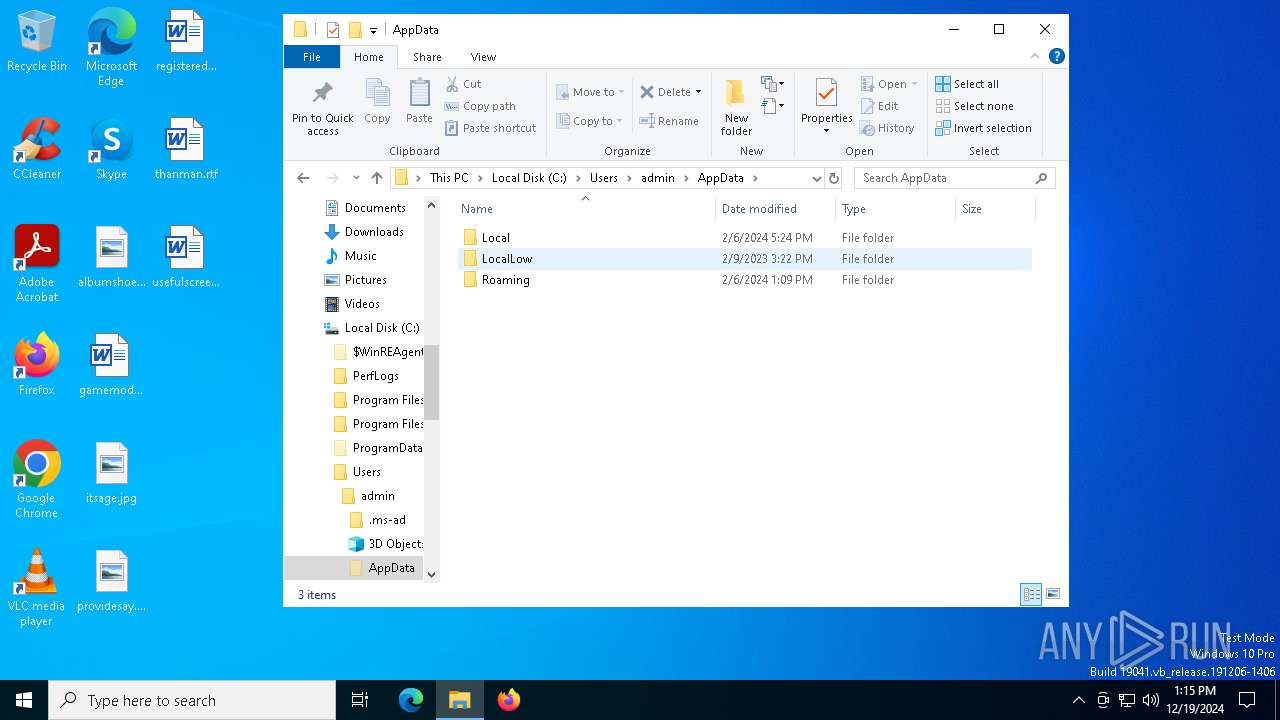
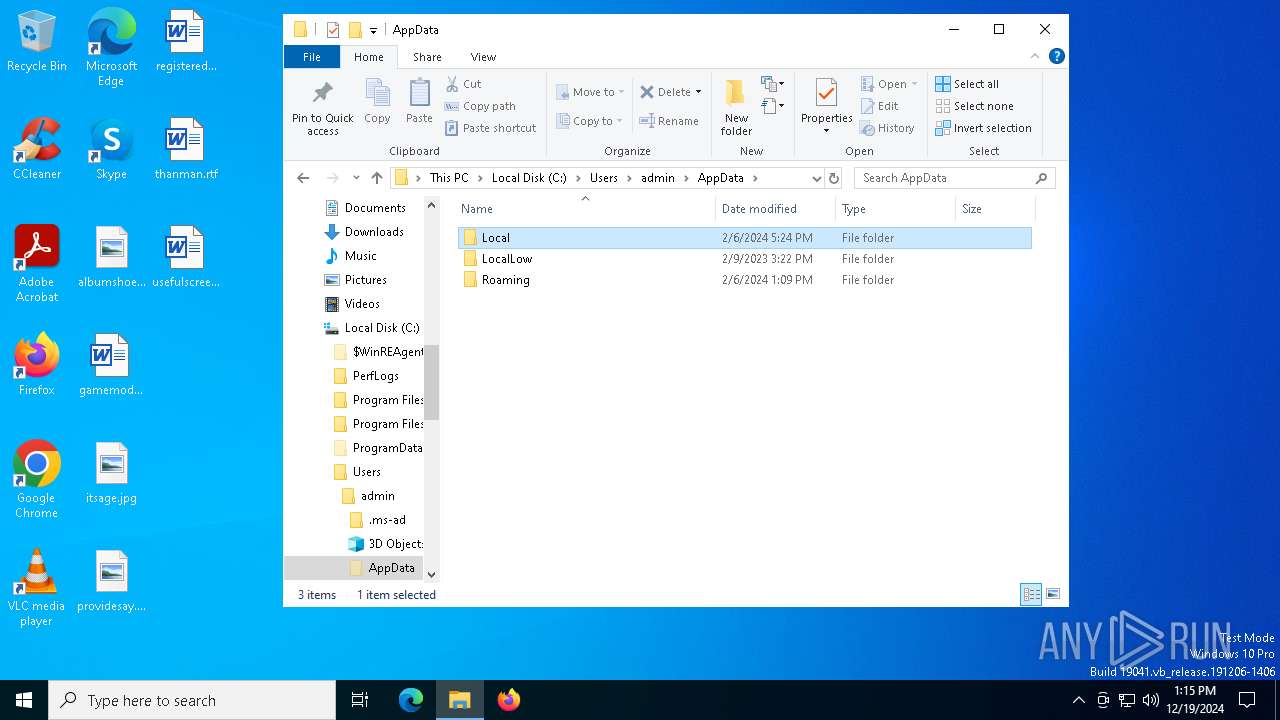
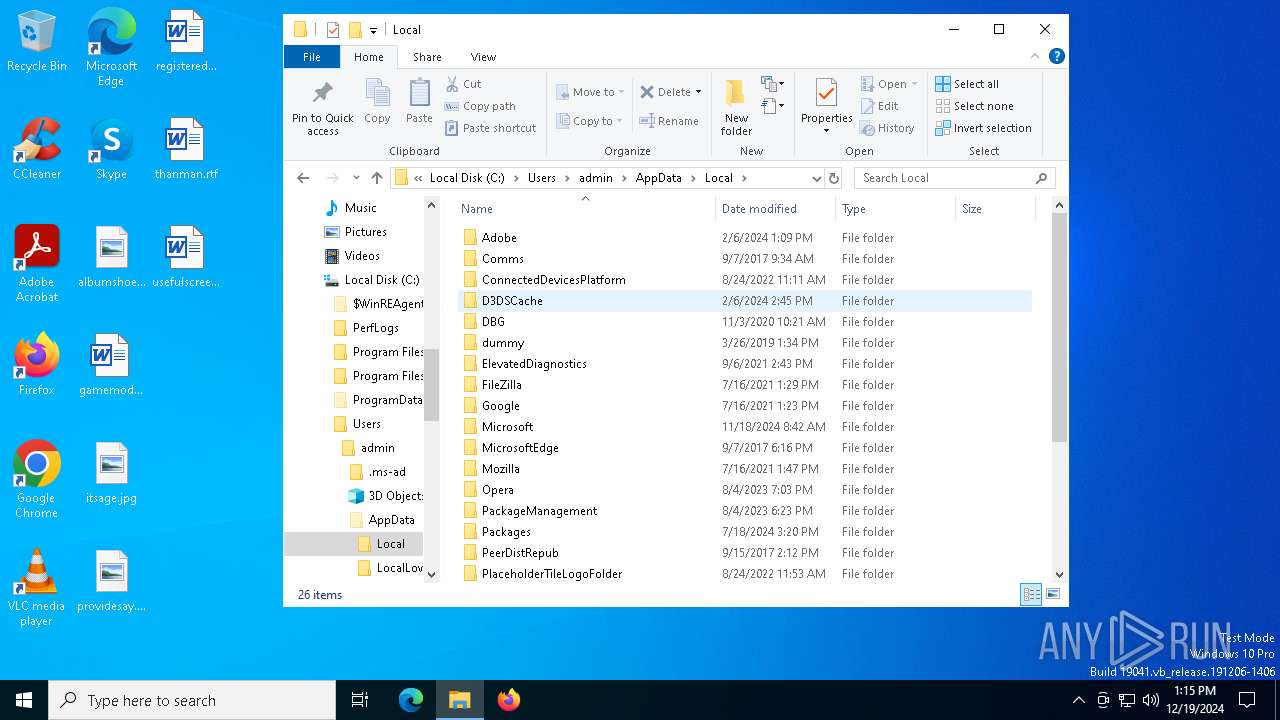
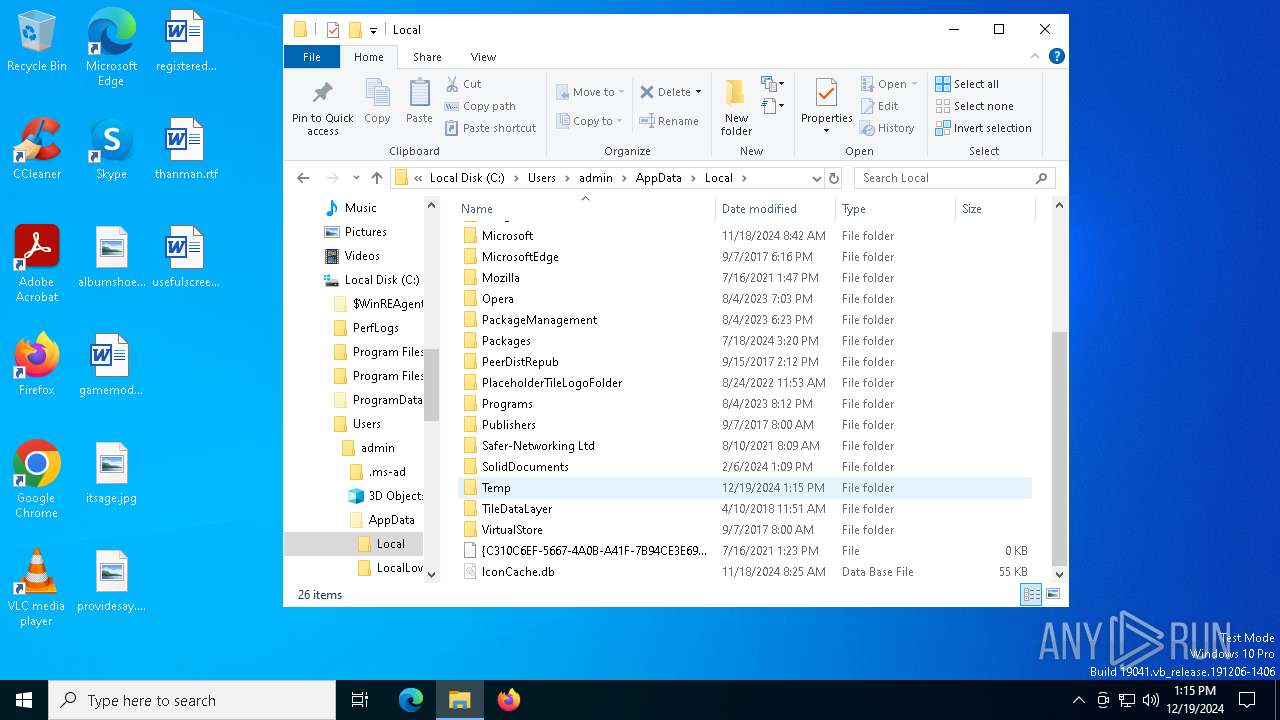
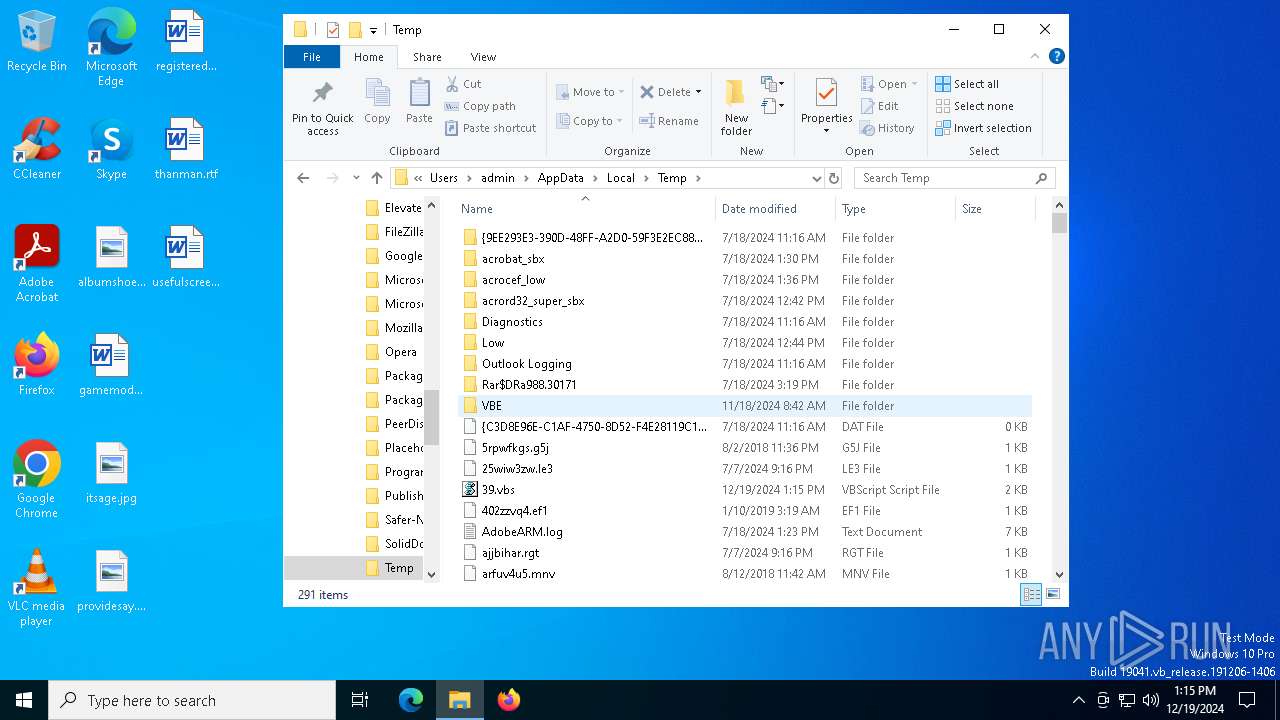
| 2088 | "wscript.exe" "C:\Users\admin\AppData\Local\Temp\38.vbs" | C:\Windows\System32\wscript.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
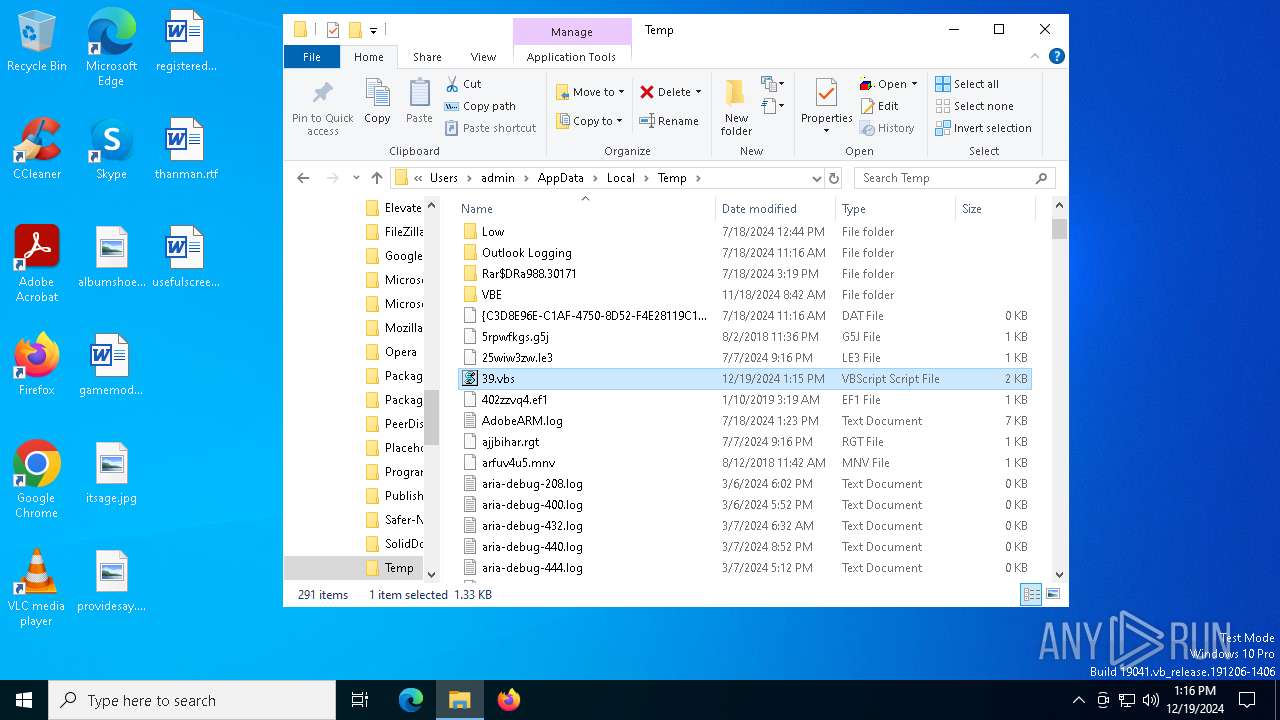
| 3364 | "C:\WINDOWS\System32\WScript.exe" C:\Users\admin\AppData\Local\Temp\temp.vbs | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3552 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\39.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\38.vbs" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 6800 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6936 | "wscript.exe" "C:\Users\admin\AppData\Local\Temp\39.vbs" | C:\Windows\System32\wscript.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
Total events
1 179
Read events
1 179
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
5
Unknown types
0
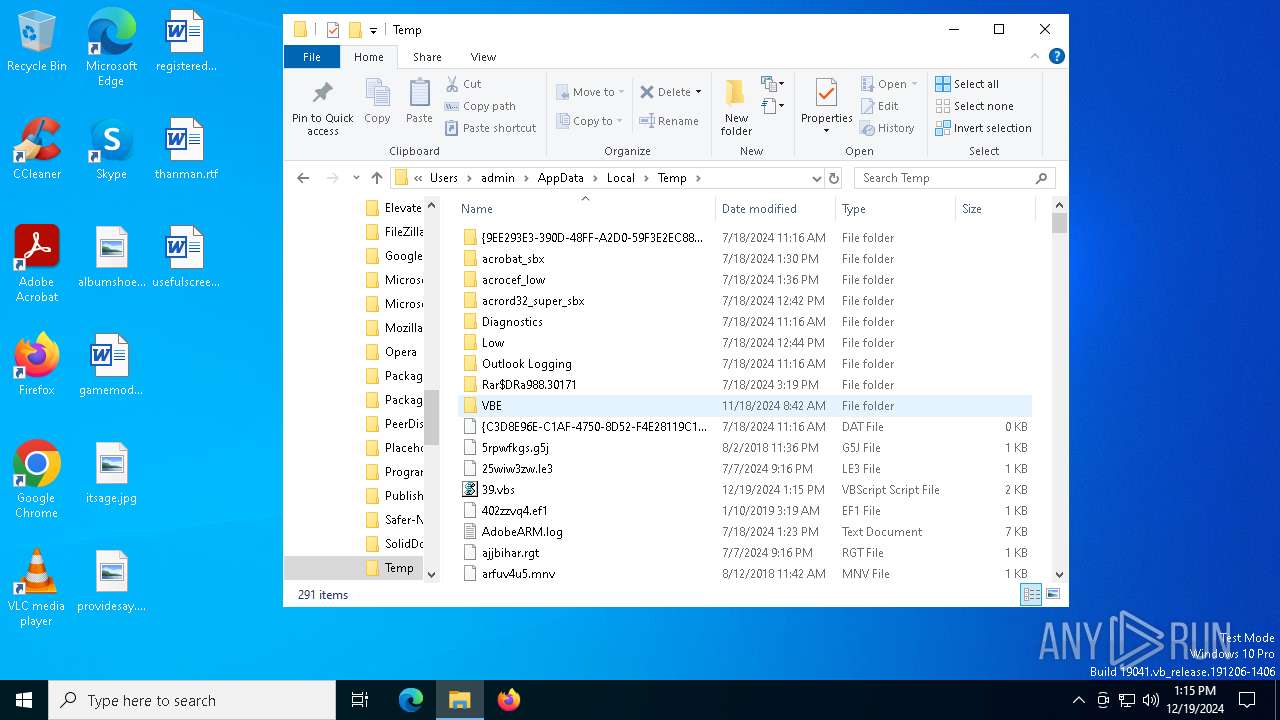
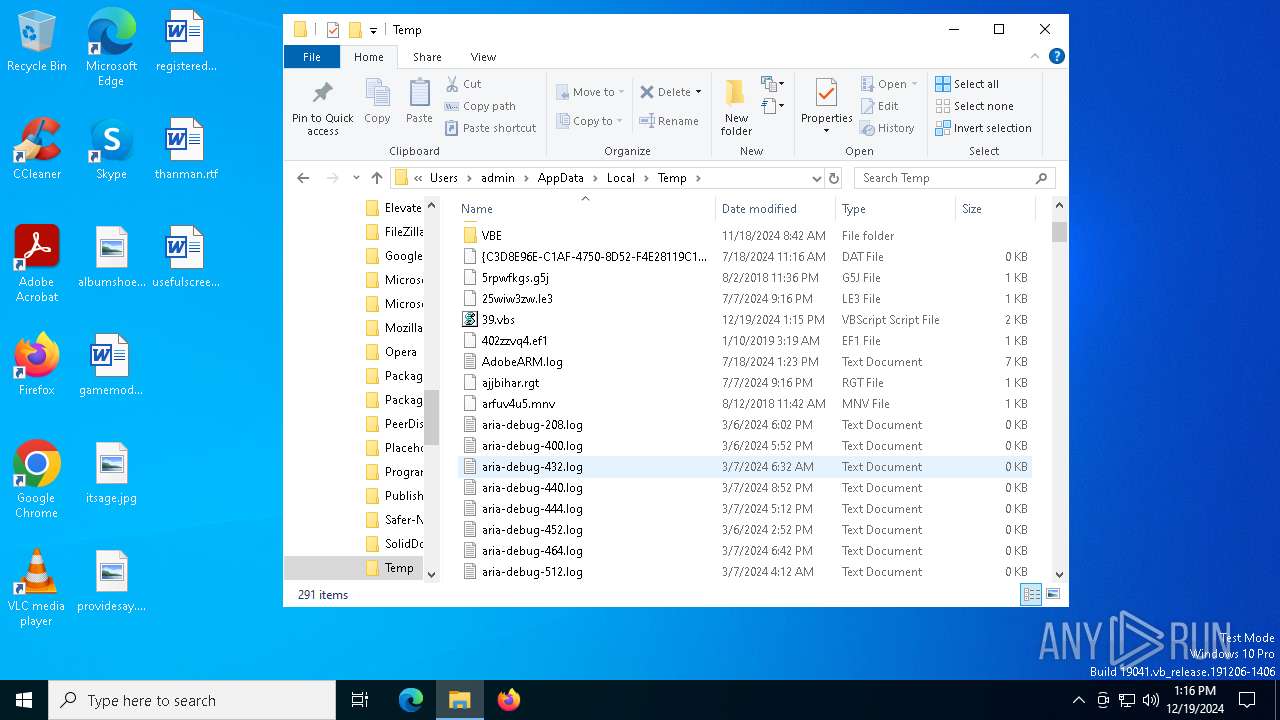
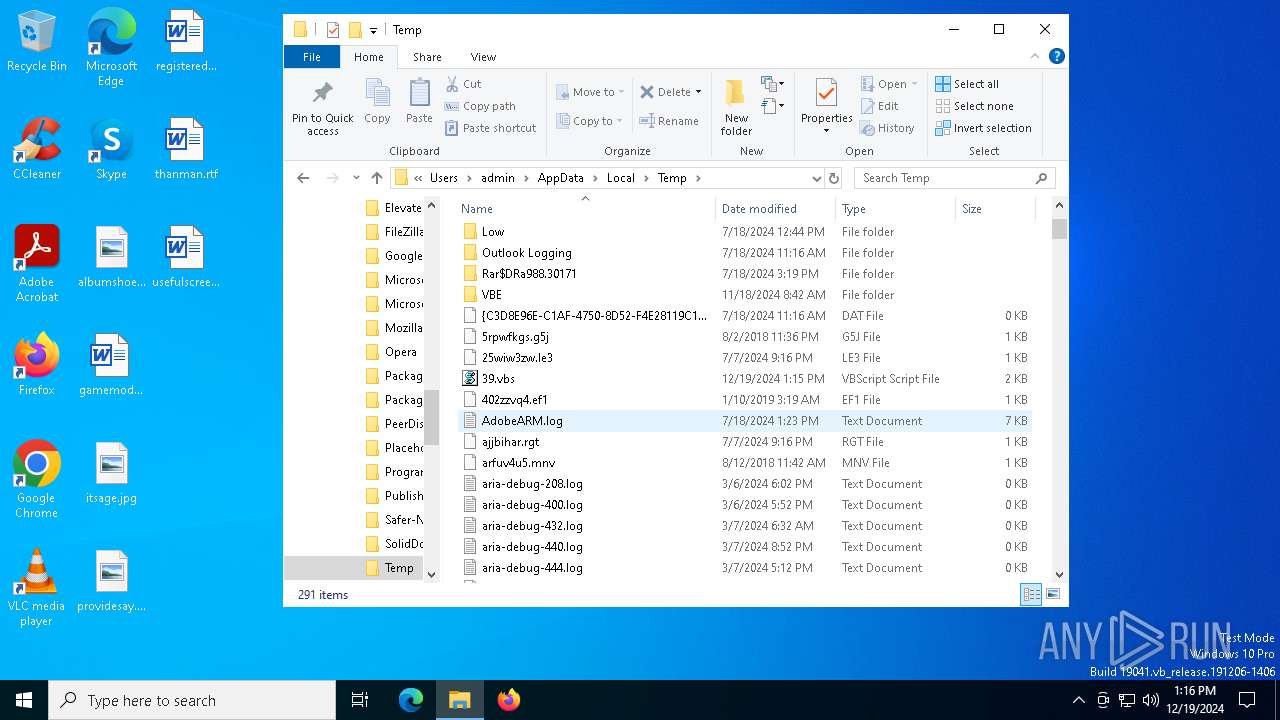
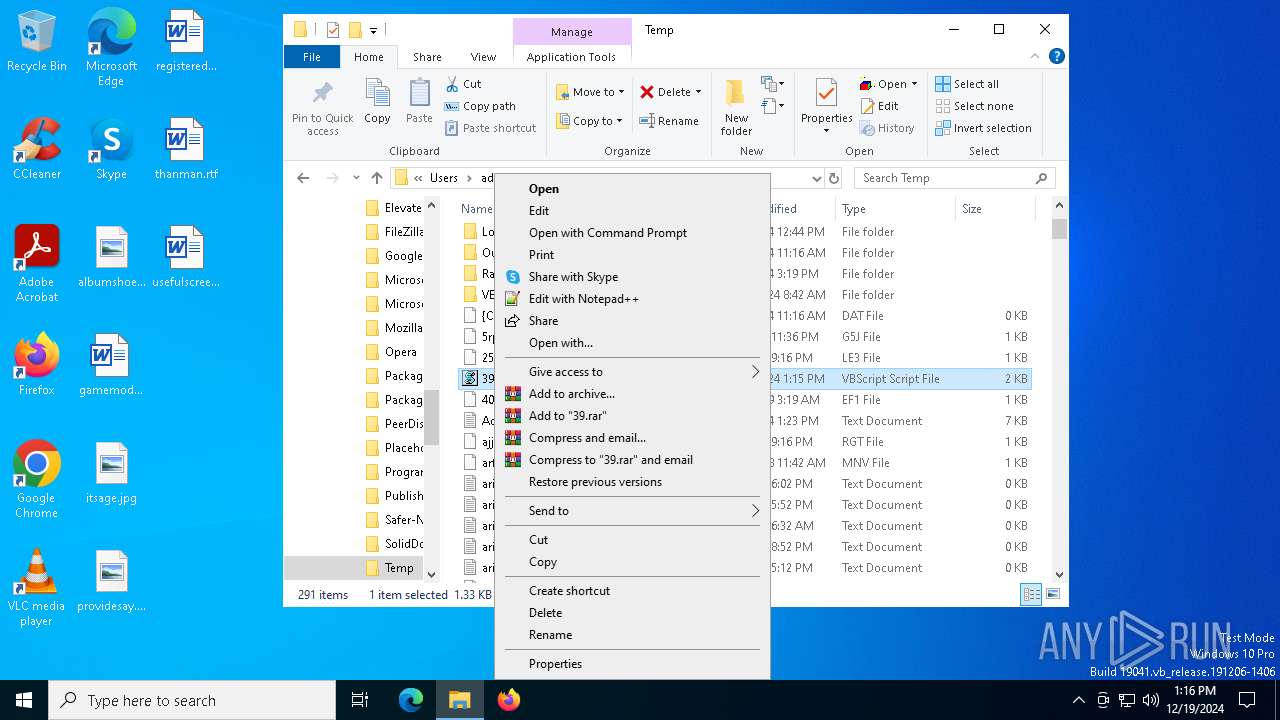
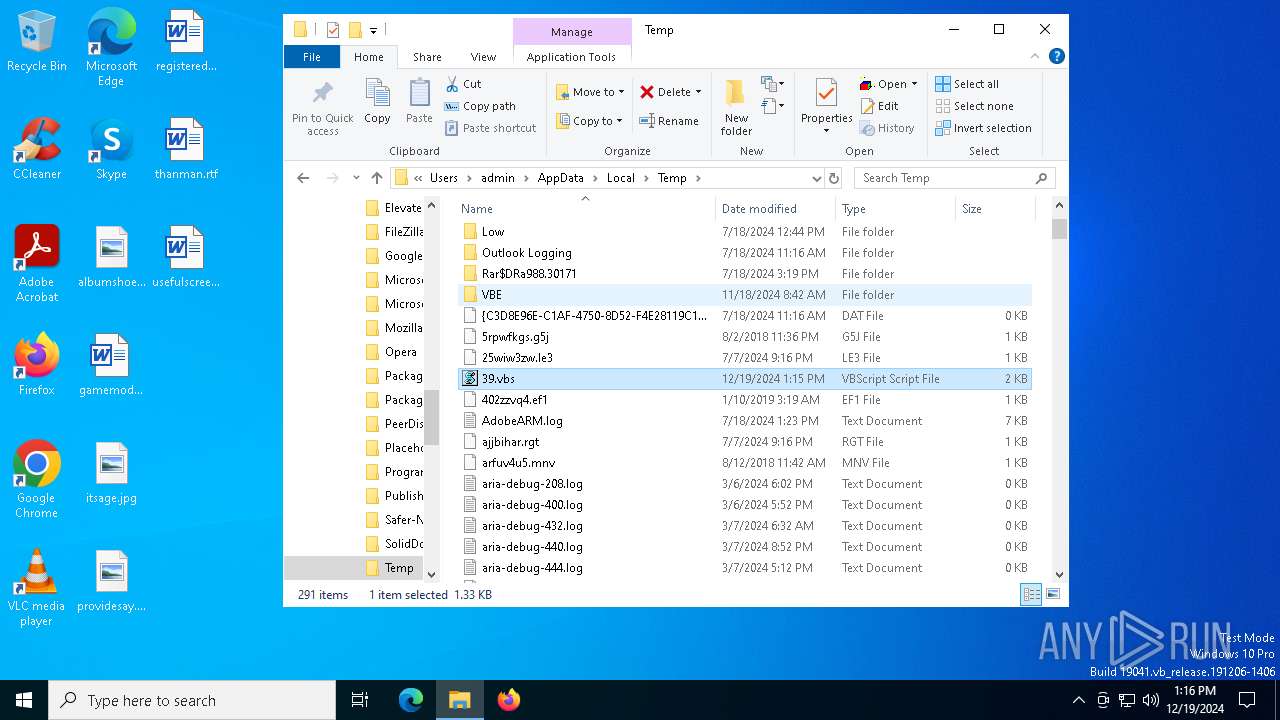
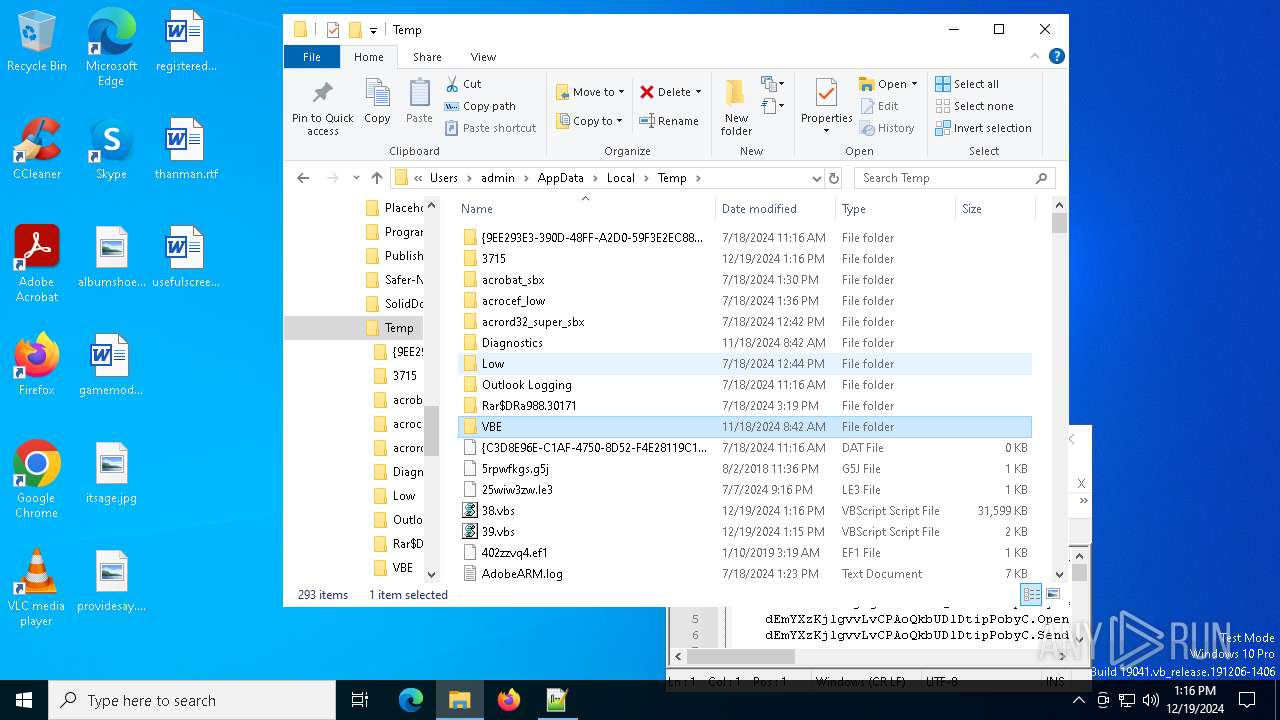
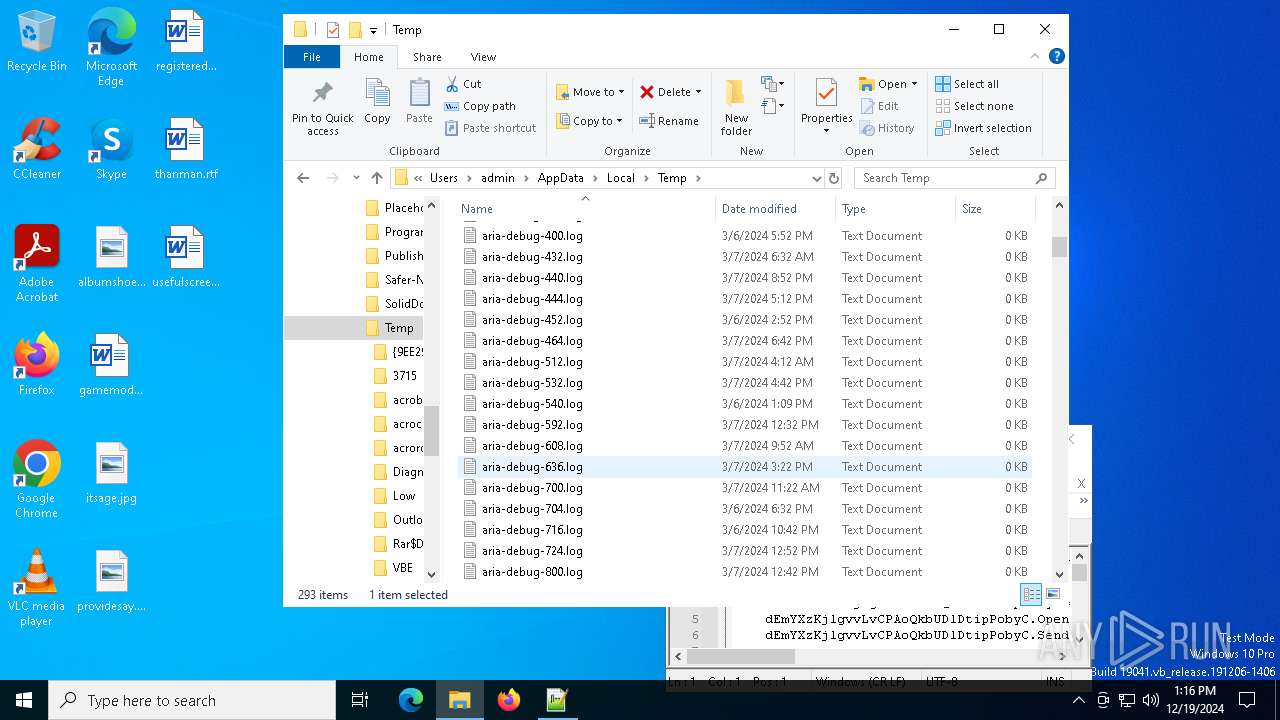
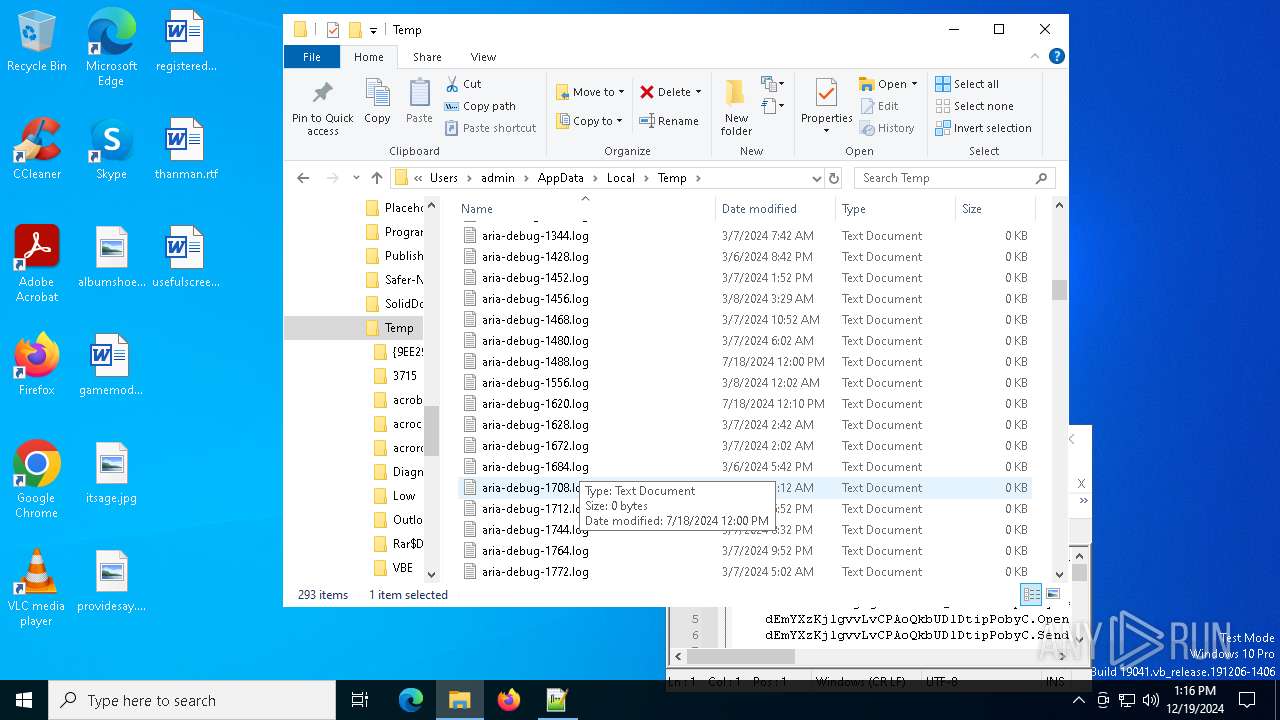
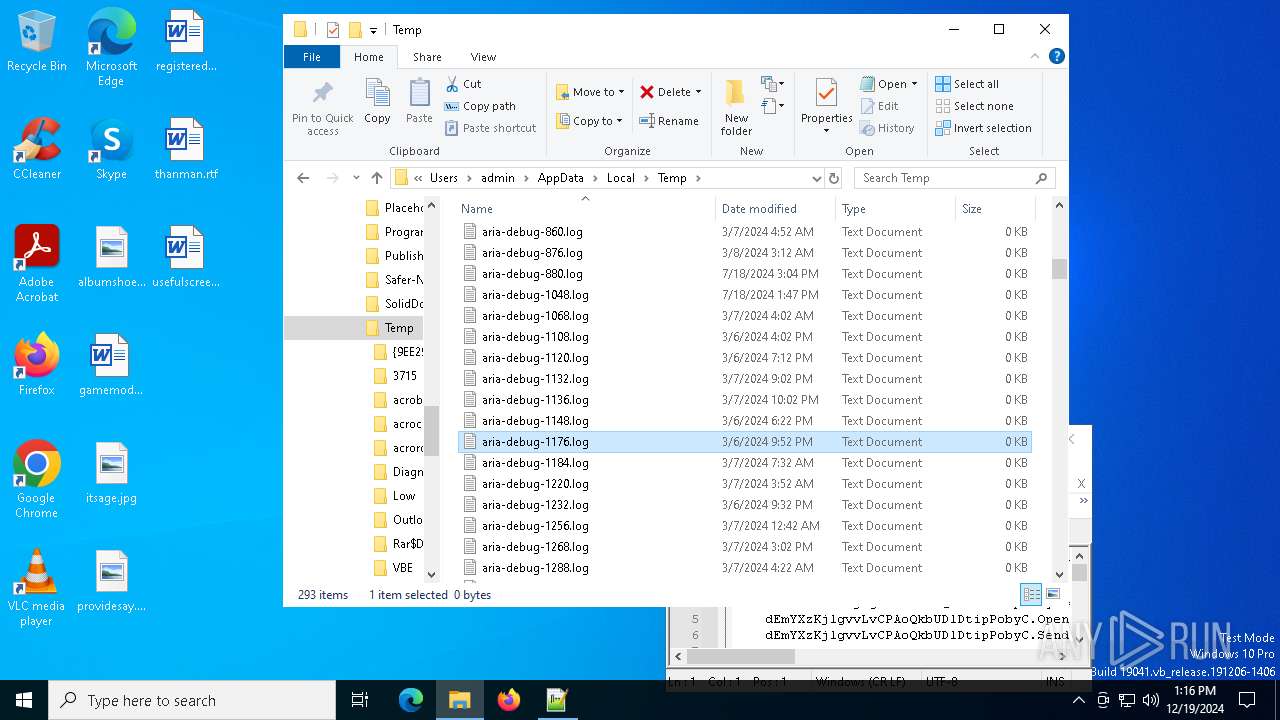
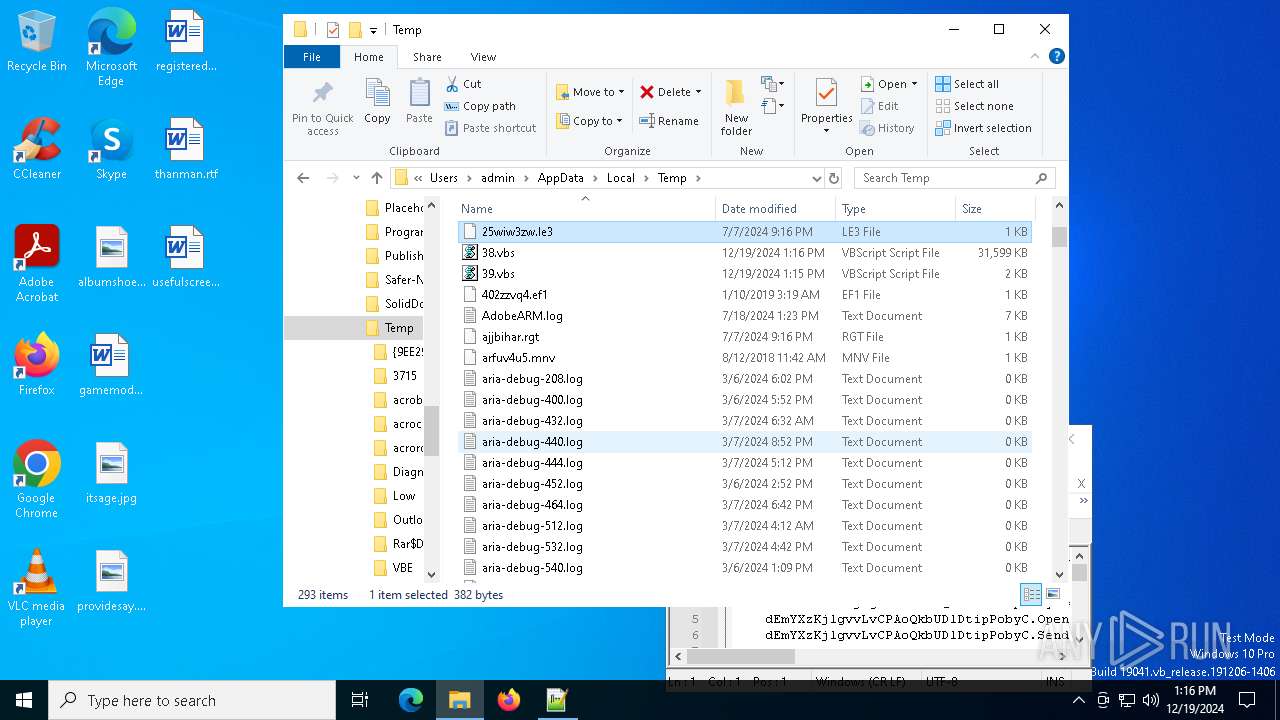
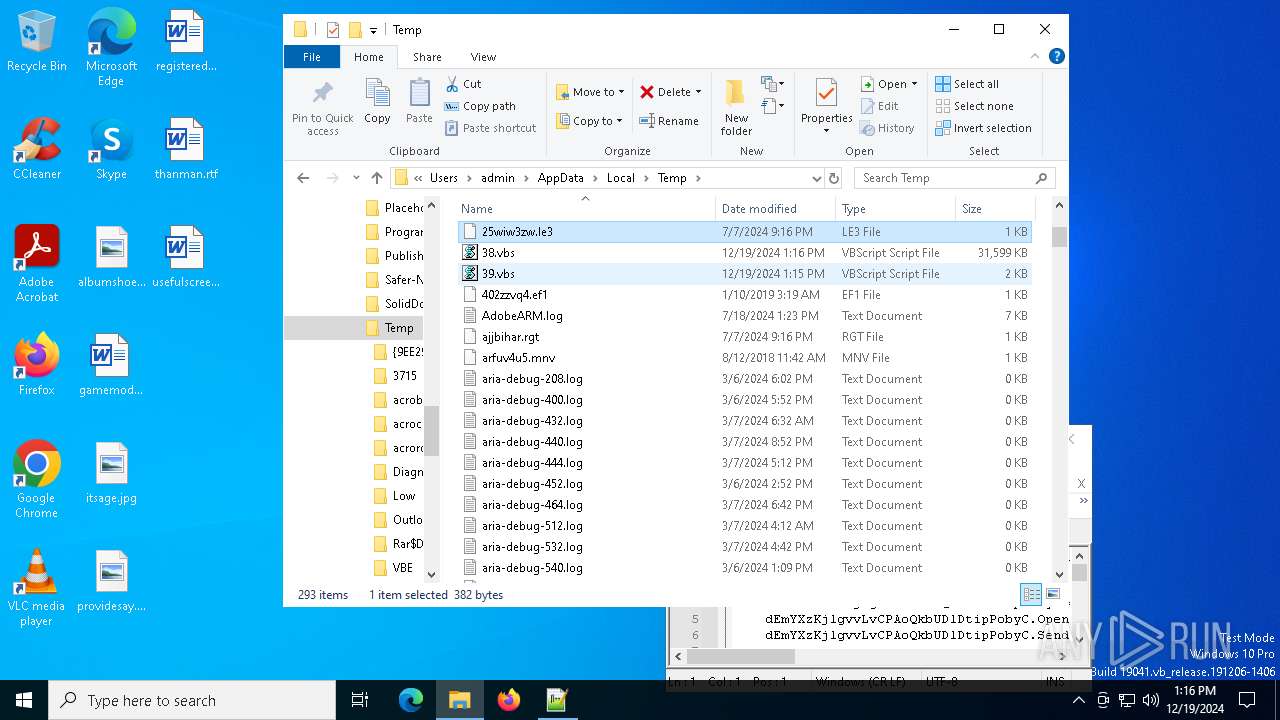
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6936 | wscript.exe | C:\Users\admin\AppData\Local\Temp\38.vbs | — | |
MD5:— | SHA256:— | |||
| 3364 | wscript.exe | C:\Users\admin\AppData\Local\Temp\39.vbs | text | |
MD5:E133BB44DC7A2F10BD7806FB877999D0 | SHA256:B341A4B4564F2C8ADDE3958EF2338D7189601F784926F83E528F4CBBDB94EED8 | |||
| 3552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\stylers.xml | xml | |
MD5:312281C4126FA897EF21A7E8CCB8D495 | SHA256:53B4BE3ED1CFD712E53542B30CFE30C5DB35CC48BE7C57727DFEC26C9E882E90 | |||
| 3552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\langs.xml | xml | |
MD5:FE22EC5755BC98988F9656F73B2E6FB8 | SHA256:F972C425CE176E960F6347F1CA2F64A8CE2B95A375C33A03E57538052BA0624D | |||
| 3552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\shortcuts.xml | text | |
MD5:F11D96162BC521F5CF49FFE6B6841C9B | SHA256:BE9AEAEAB5A2E4899BA7E582274BA592C1B9BAF688B340A754B8EF32B23CFA9C | |||
| 3552 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\plugins\config\converter.ini | text | |
MD5:F70F579156C93B097E656CABA577A5C9 | SHA256:B926498A19CA95DC28964B7336E5847107DD3C0F52C85195C135D9DD6CA402D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6936 | wscript.exe | GET | 302 | 18.190.219.179:80 | http://18.190.219.179/209.php | unknown | — | — | unknown |
2424 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7064 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7064 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2160 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.160:443 | www.bing.com | Akamai International B.V. | GB | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 184.28.89.167:443 | go.microsoft.com | AKAMAI-AS | US | whitelisted |
3976 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
againg.s3.us-east-2.amazonaws.com |
| shared |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|