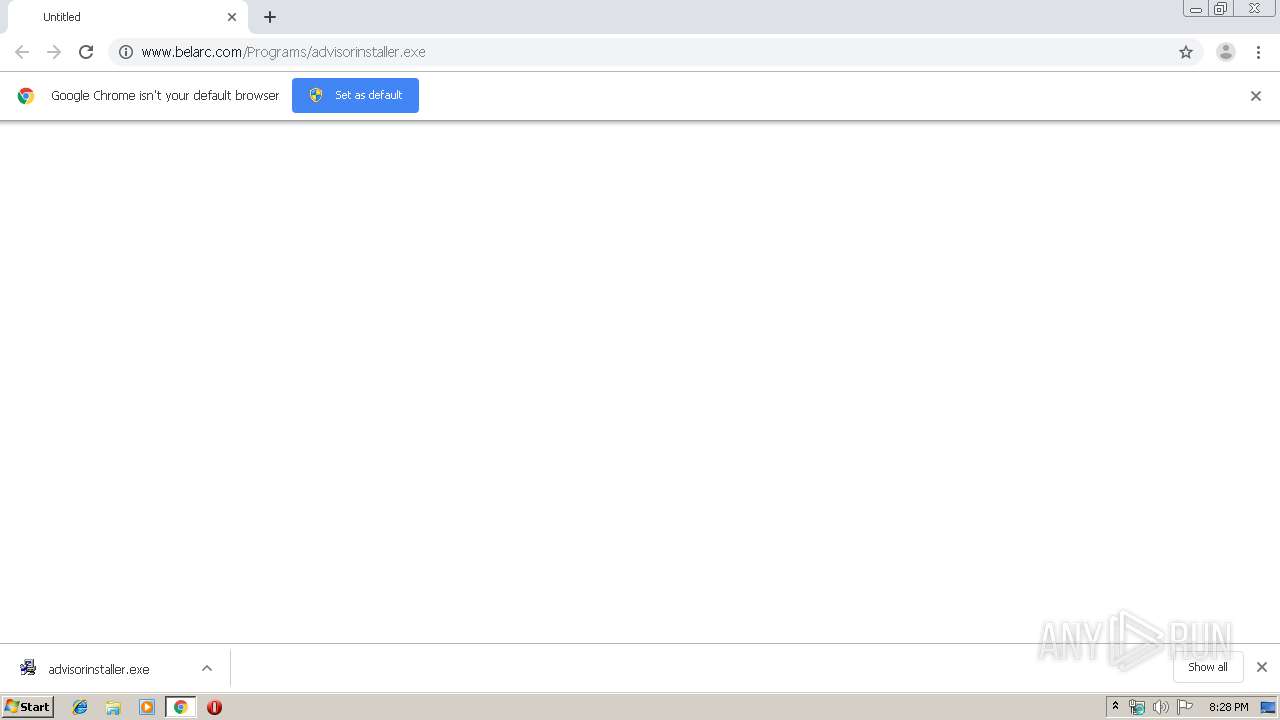
| URL: | http://www.belarc.com/Programs/advisorinstaller.exe |
| Full analysis: | https://app.any.run/tasks/e2d67c48-6af9-499a-9c1f-3fffa960388e |
| Verdict: | Malicious activity |
| Analysis date: | September 24, 2019, 19:28:14 |
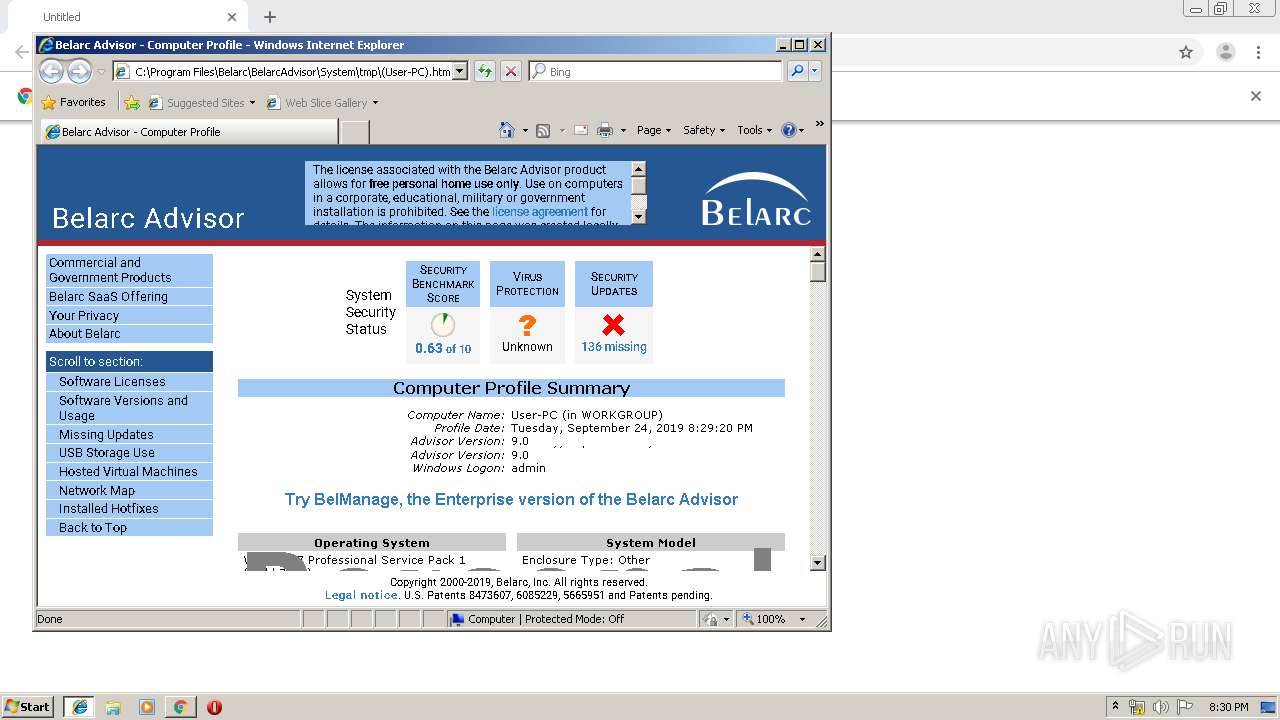
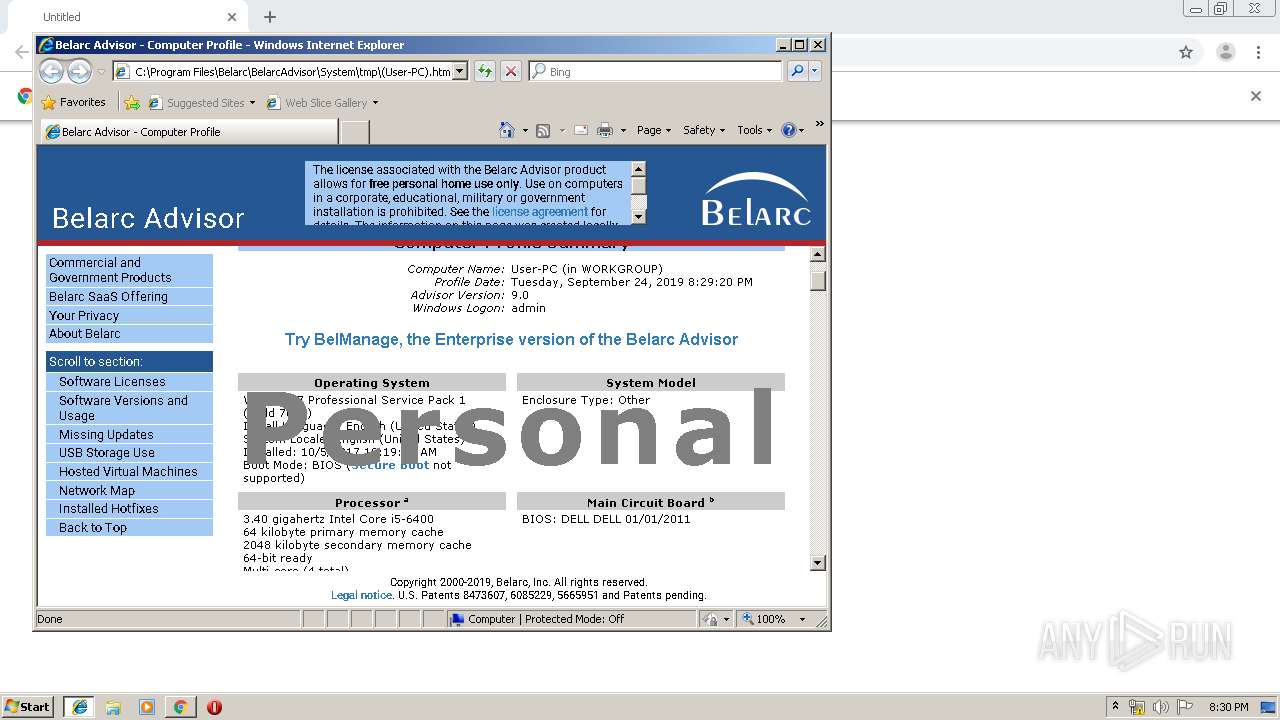
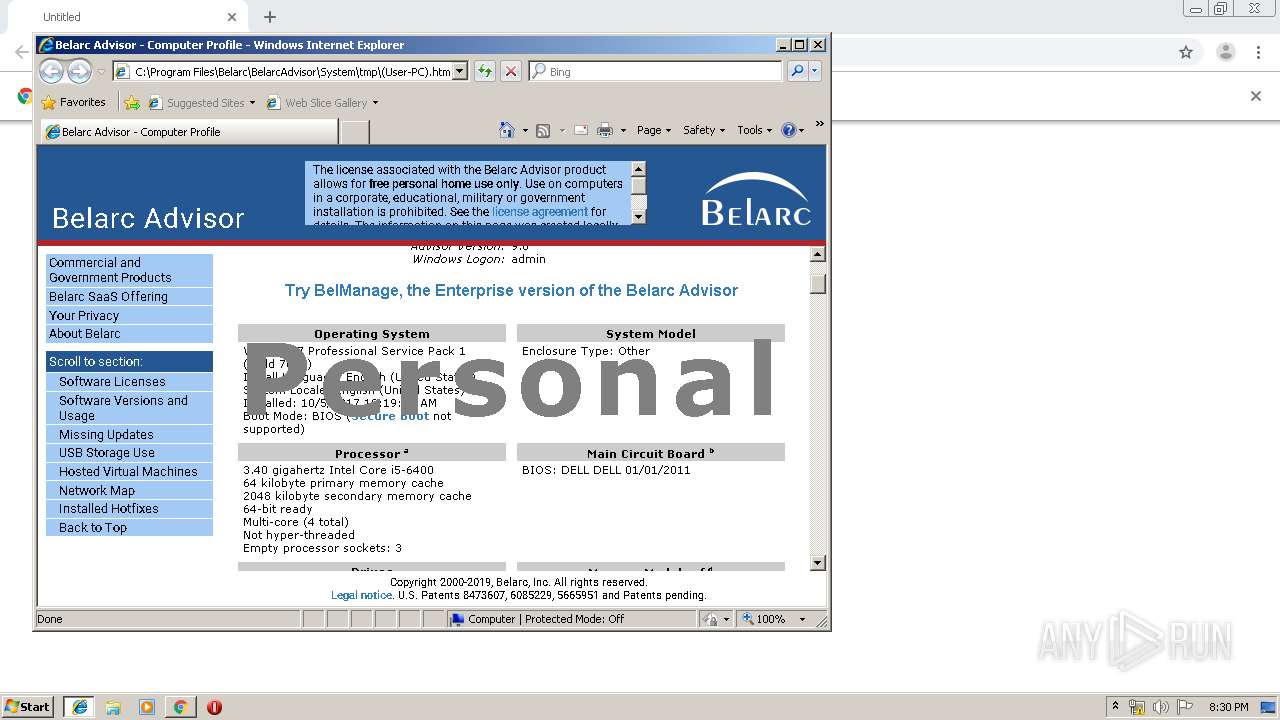
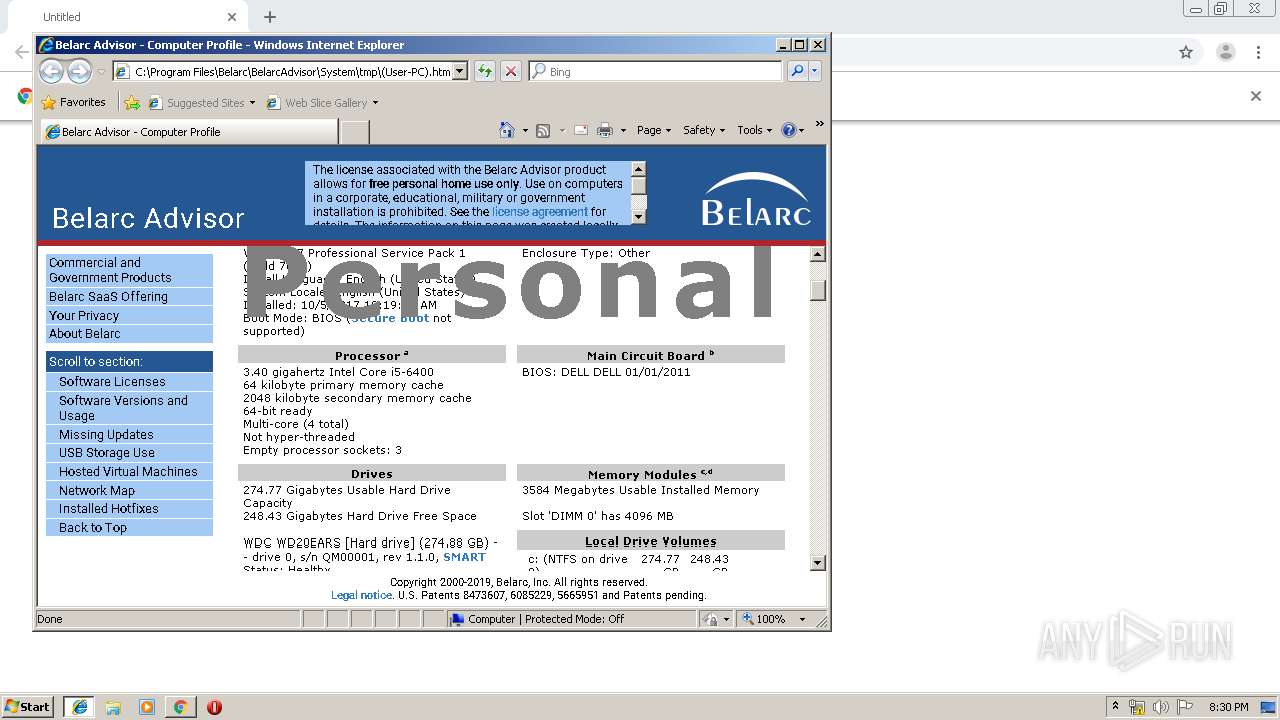
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D5E22A4FD12E8412791901F70C86BE6 |
| SHA1: | 2D6700B2758AAF147F6906375634E313BAA7FD3D |
| SHA256: | B9EAD373A7B35E81C8888E65173B8667D9DFF85708D8F4CB50CA4CC7BBFCCA49 |
| SSDEEP: | 3:N1KJS4gKX6ICXErKEW2LVOXLNn:Cc4gJwfWsVOXLN |
MALICIOUS
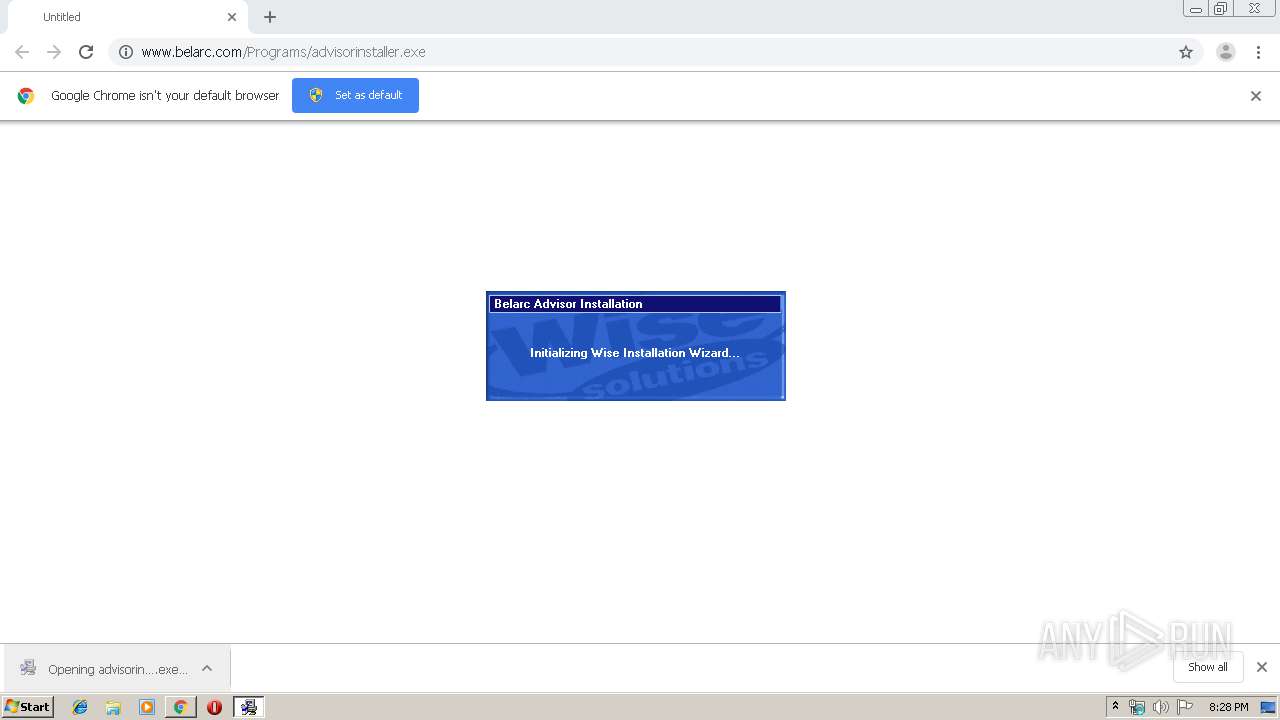
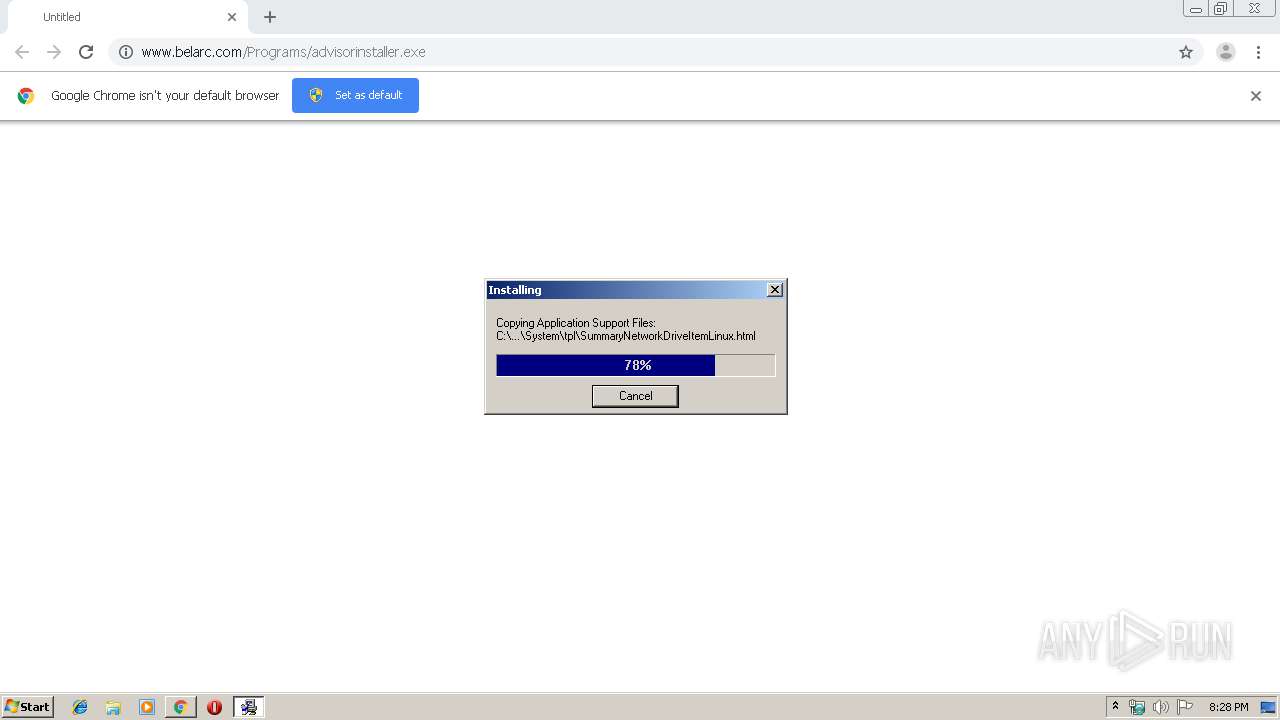
Application was dropped or rewritten from another process
- advisorinstaller.exe (PID: 3676)
- advisorinstaller.exe (PID: 3388)
- GLJ307E.tmp (PID: 2580)
- BELARC~1.EXE (PID: 3388)
Loads dropped or rewritten executable
- BELARC~1.EXE (PID: 3388)
- GLJ307E.tmp (PID: 2580)
- advisorinstaller.exe (PID: 3676)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2972)
- chrome.exe (PID: 2292)
- advisorinstaller.exe (PID: 3676)
Creates files in the user directory
- advisorinstaller.exe (PID: 3676)
- powershell.exe (PID: 3084)
Removes files from Windows directory
- advisorinstaller.exe (PID: 3676)
Modifies the open verb of a shell class
- advisorinstaller.exe (PID: 3676)
Creates files in the Windows directory
- advisorinstaller.exe (PID: 3676)
Creates a software uninstall entry
- advisorinstaller.exe (PID: 3676)
Starts application with an unusual extension
- advisorinstaller.exe (PID: 3676)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2972)
Low-level read access rights to disk partition
- BELARC~1.EXE (PID: 3388)
Creates files in the program directory
- advisorinstaller.exe (PID: 3676)
- BELARC~1.EXE (PID: 3388)
Searches for installed software
- BELARC~1.EXE (PID: 3388)
- powershell.exe (PID: 3084)
Executes PowerShell scripts
- BELARC~1.EXE (PID: 3388)
Creates COM task schedule object
- GLJ307E.tmp (PID: 2580)
INFO
Reads the hosts file
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2972)
Reads Internet Cache Settings
- chrome.exe (PID: 2972)
- iexplore.exe (PID: 1880)
- iexplore.exe (PID: 1928)
Application launched itself
- chrome.exe (PID: 2972)
- iexplore.exe (PID: 2704)
Manual execution by user
- iexplore.exe (PID: 2704)
Reads internet explorer settings
- iexplore.exe (PID: 1880)
Changes internet zones settings
- iexplore.exe (PID: 2704)
Reads settings of System Certificates
- iexplore.exe (PID: 1880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
30
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4251370417344172038 --mojo-platform-channel-handle=572 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2704 CREDAT:14337 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2704 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=436240853162099002 --mojo-platform-channel-handle=912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12996225754895539820 --mojo-platform-channel-handle=936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8050316114929800990 --mojo-platform-channel-handle=1612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11614683169154847606 --mojo-platform-channel-handle=1072 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2316 | /analyze /db "c:\users\admin\appdata\local\temp\secedit.sdb" /cfg "c:\users\admin\appdata\local\temp\secedit1.inf" /log "c:\users\admin\appdata\local\temp\secedit1.txt" /verbose | c:\windows\system32\secedit.exe | — | BELARC~1.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Security Configuration Editor Command Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13973098931295875705 --mojo-platform-channel-handle=4220 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,7060222992418260547,6861175517869654462,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=546681337623981373 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 095
Read events
2 562
Write events
528
Delete events
5
Modification events
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2764) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2972-13213826911547250 |
Value: 259 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
42
Text files
416
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e700ca0e-4b0c-41ee-a59f-1bb1b6220c60.tmp | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFf07b7.TMP | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
28
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2292 | chrome.exe | GET | 200 | 13.224.197.19:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2292 | chrome.exe | GET | 302 | 34.203.76.210:80 | http://www.belarc.com/Programs/advisorinstaller.exe | US | html | 241 b | unknown |
2292 | chrome.exe | GET | 200 | 173.194.160.74:80 | http://r5---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.83&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1569353422&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2704 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2292 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2292 | chrome.exe | GET | 200 | 2.20.188.116:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2292 | chrome.exe | 2.20.188.116:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2292 | chrome.exe | 34.203.76.210:80 | www.belarc.com | Amazon.com, Inc. | US | unknown |
2292 | chrome.exe | 172.217.18.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2292 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2292 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2292 | chrome.exe | 52.45.109.81:80 | www.belarc.com | Amazon.com, Inc. | US | unknown |
2292 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2704 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2292 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2292 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.belarc.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
downloads.belarc.com |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |