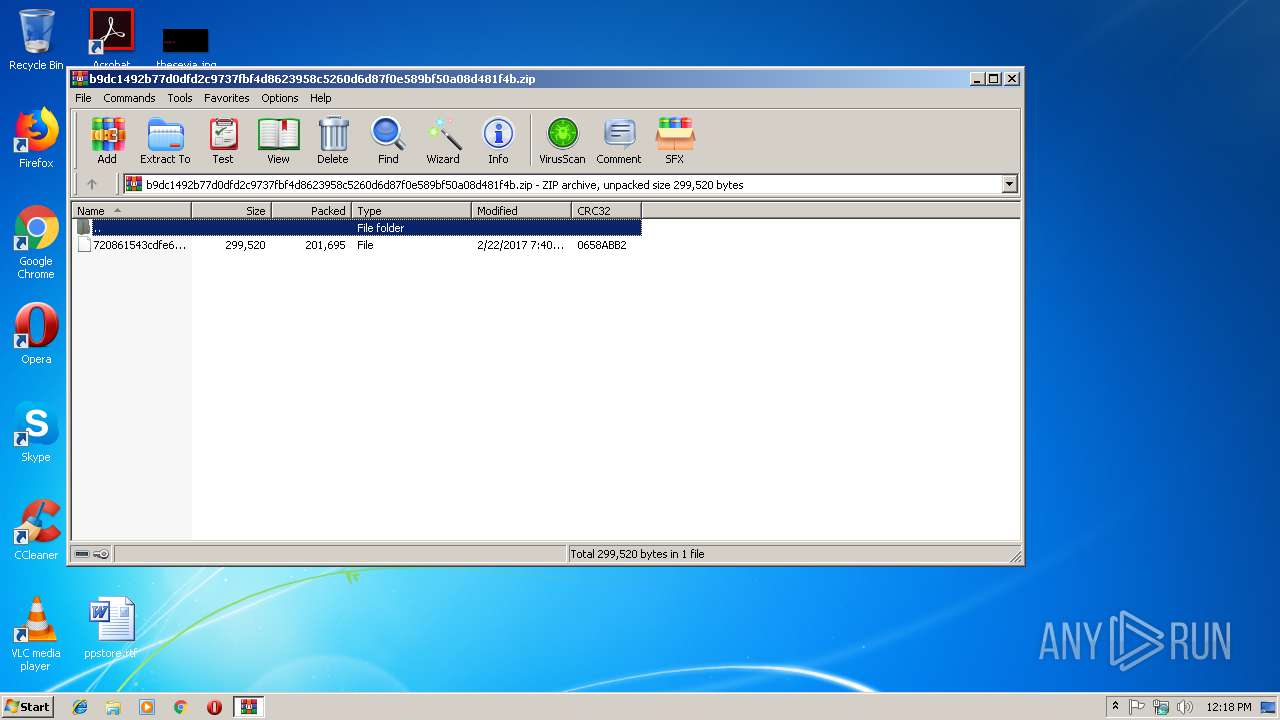
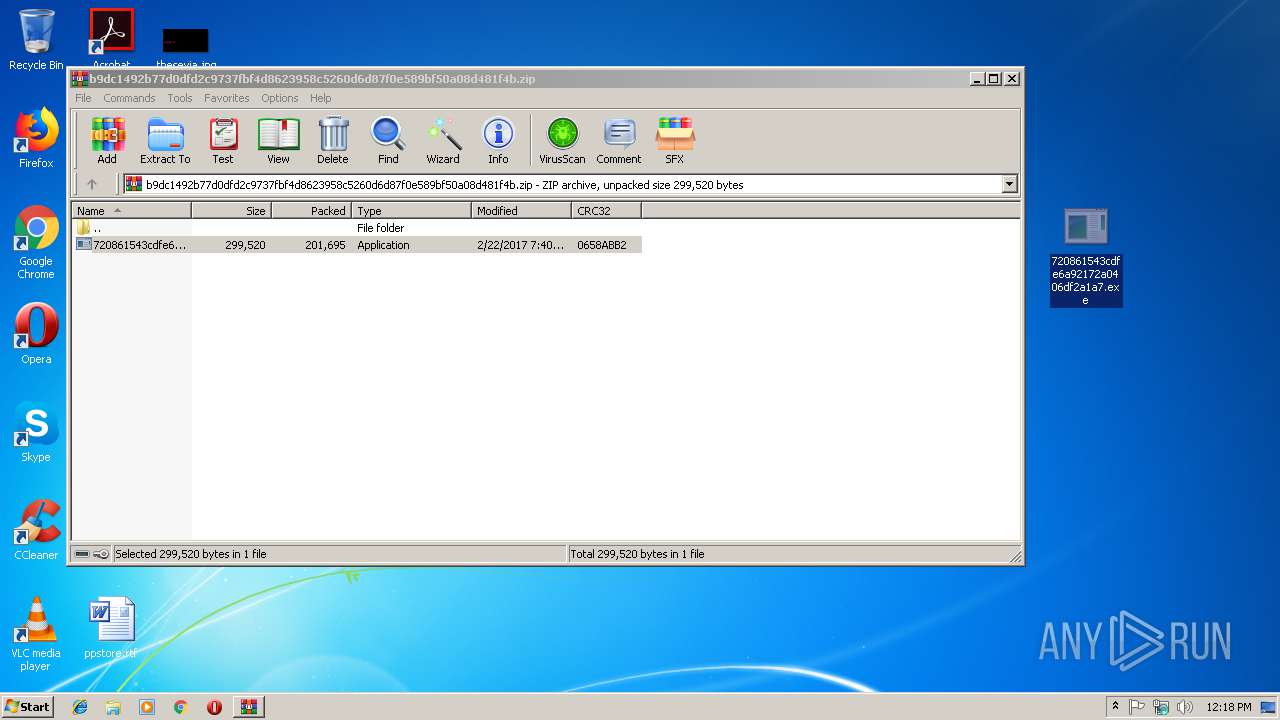
| File name: | b9dc1492b77d0dfd2c9737fbf4d8623958c5260d6d87f0e589bf50a08d481f4b |
| Full analysis: | https://app.any.run/tasks/b703e98d-d2b2-44e1-be7e-88e9d827e634 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 12:18:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5DF1759BA32BBFE625A9EB0E61CADF14 |
| SHA1: | 95661A23C15ECEBFDC46694C275B5FAB8BE2708C |
| SHA256: | B9DC1492B77D0DFD2C9737FBF4D8623958C5260D6D87F0E589BF50A08D481F4B |
| SSDEEP: | 6144:4no6lmq7n9R7c2Q1Ir+C5eYiO09HpZQ/xA5K:43lBL9+xIyCDi79J+us |
MALICIOUS
Loads the Task Scheduler COM API
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
- svchost.exe (PID: 300)
Application was dropped or rewritten from another process
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
Changes the autorun value in the registry
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
Runs injected code in another process
- svchost.exe (PID: 300)
Uses SVCHOST.EXE for hidden code execution
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
Application was injected by another process
- dwm.exe (PID: 2008)
SUSPICIOUS
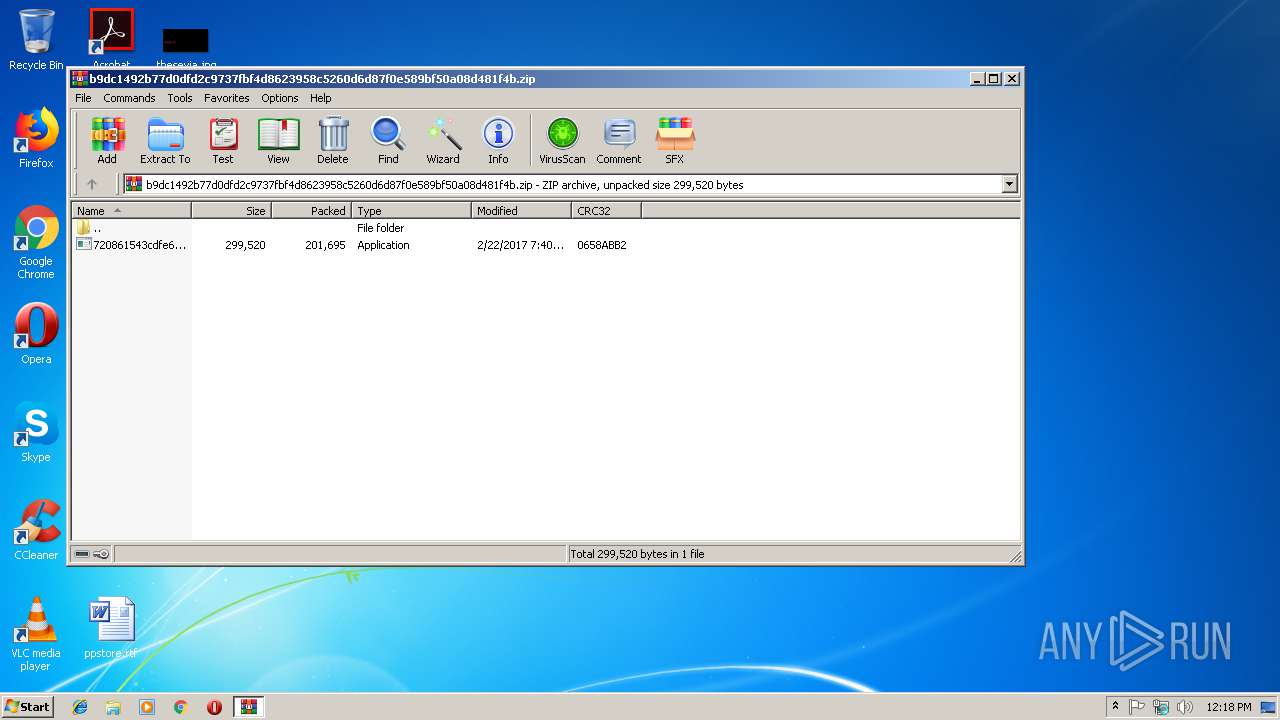
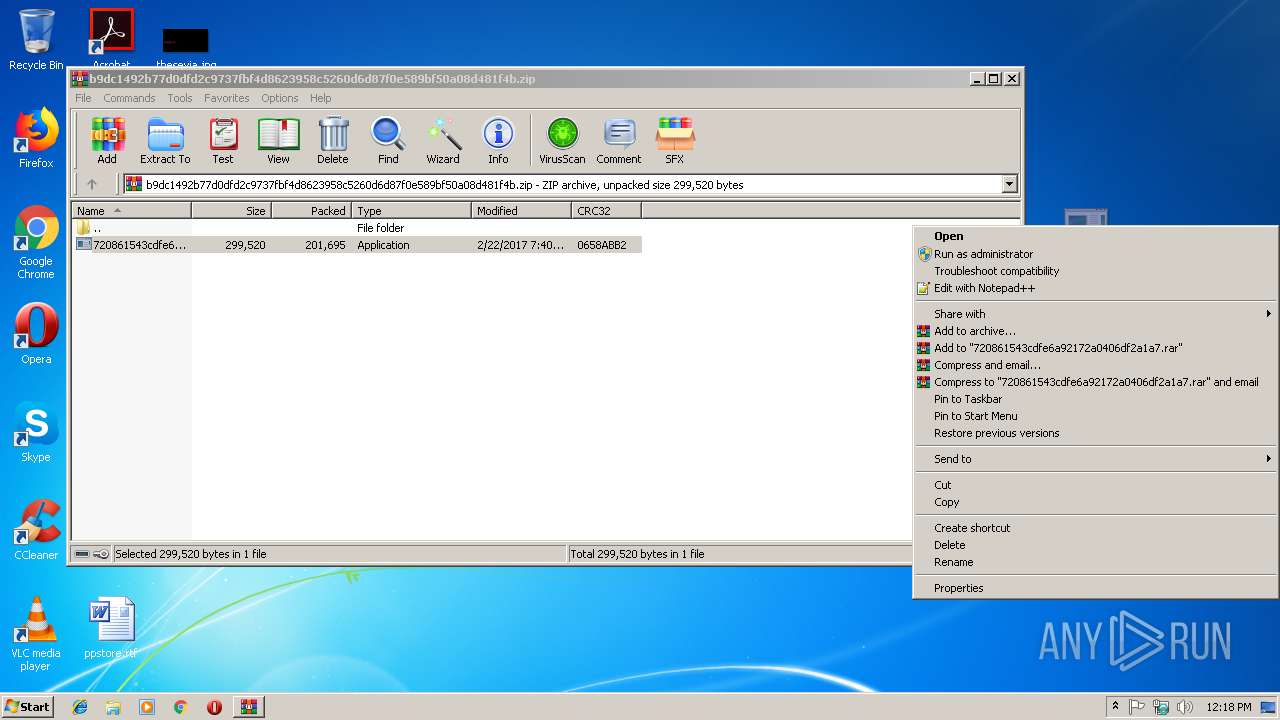
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3504)
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
Creates files in the user directory
- 720861543cdfe6a92172a0406df2a1a7.exe (PID: 3168)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:02:22 19:40:13 |
| ZipCRC: | 0x0658abb2 |
| ZipCompressedSize: | 201695 |
| ZipUncompressedSize: | 299520 |
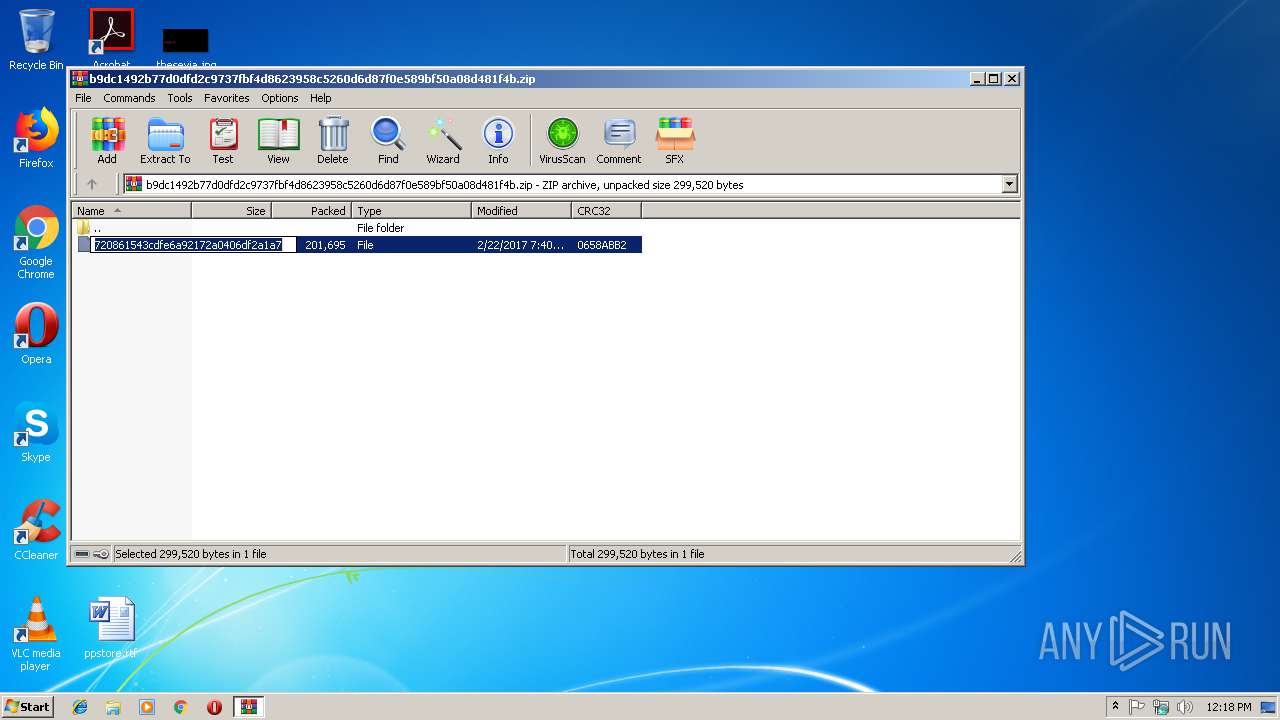
| ZipFileName: | 720861543cdfe6a92172a0406df2a1a7 |
Total processes
36
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Windows\system32\svchost.exe" | C:\Windows\system32\svchost.exe | — | 720861543cdfe6a92172a0406df2a1a7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
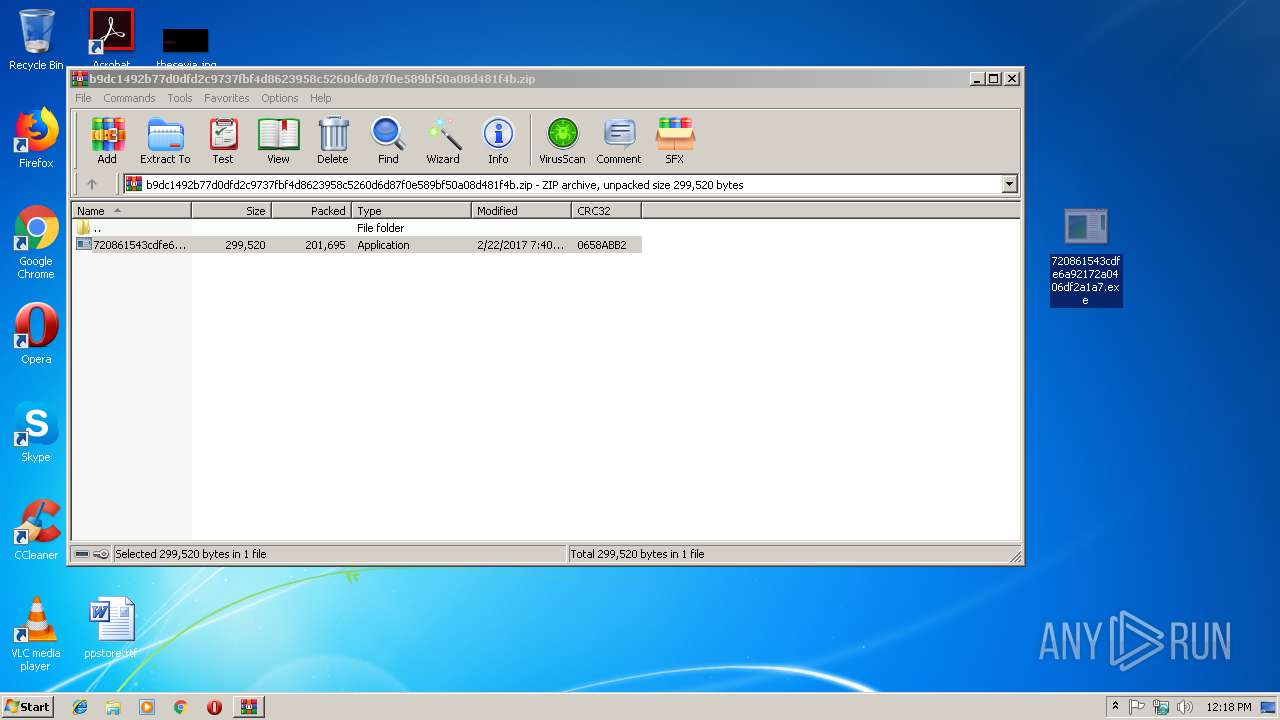
| 3168 | "C:\Users\admin\Desktop\720861543cdfe6a92172a0406df2a1a7.exe" | C:\Users\admin\Desktop\720861543cdfe6a92172a0406df2a1a7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
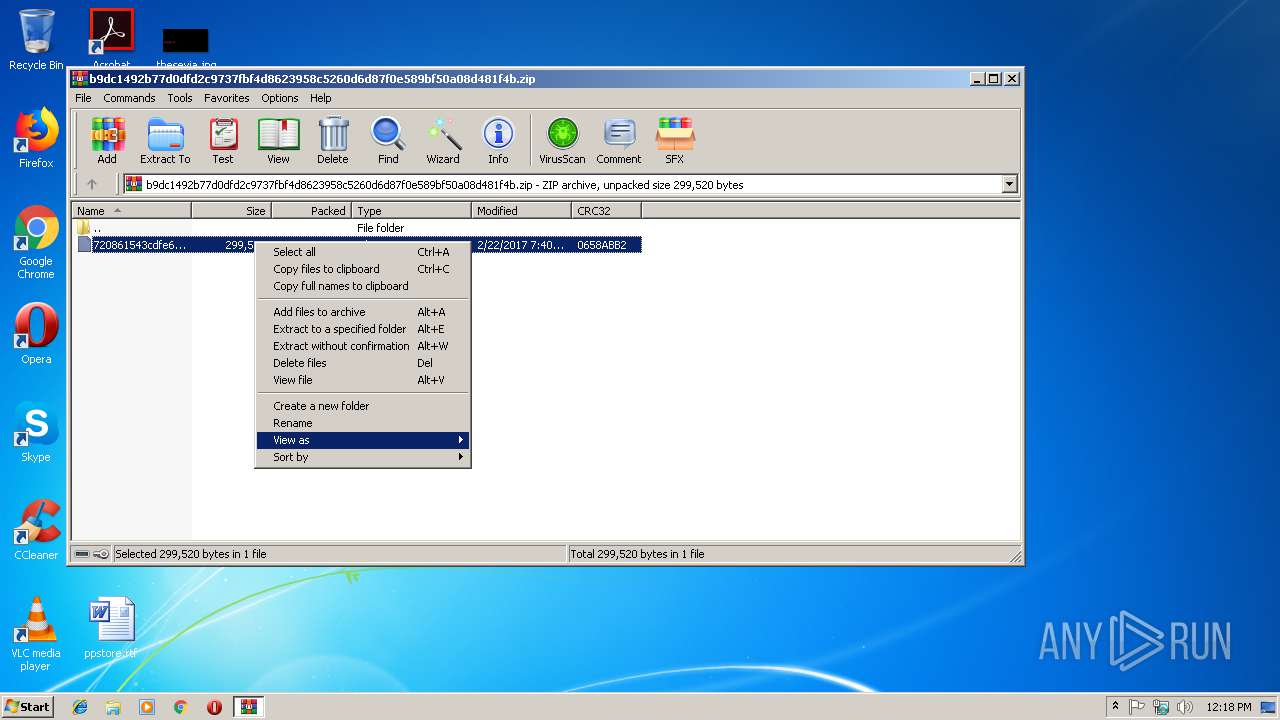
| 3504 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\b9dc1492b77d0dfd2c9737fbf4d8623958c5260d6d87f0e589bf50a08d481f4b.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
520
Read events
503
Write events
17
Delete events
0
Modification events
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\b9dc1492b77d0dfd2c9737fbf4d8623958c5260d6d87f0e589bf50a08d481f4b.zip | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3504) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\__rzi_3504.21421 | — | |
MD5:— | SHA256:— | |||
| 3504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3504.21644\720861543cdfe6a92172a0406df2a1a7.exe | executable | |
MD5:— | SHA256:— | |||
| 3168 | 720861543cdfe6a92172a0406df2a1a7.exe | C:\users\admin\appdata\roaming\{23FF9D04-F5B3-A8A2-503C-F1A9E9B71CF4}\8e404d9b.exe | executable | |
MD5:— | SHA256:— | |||
| 3504 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\b9dc1492b77d0dfd2c9737fbf4d8623958c5260d6d87f0e589bf50a08d481f4b.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report