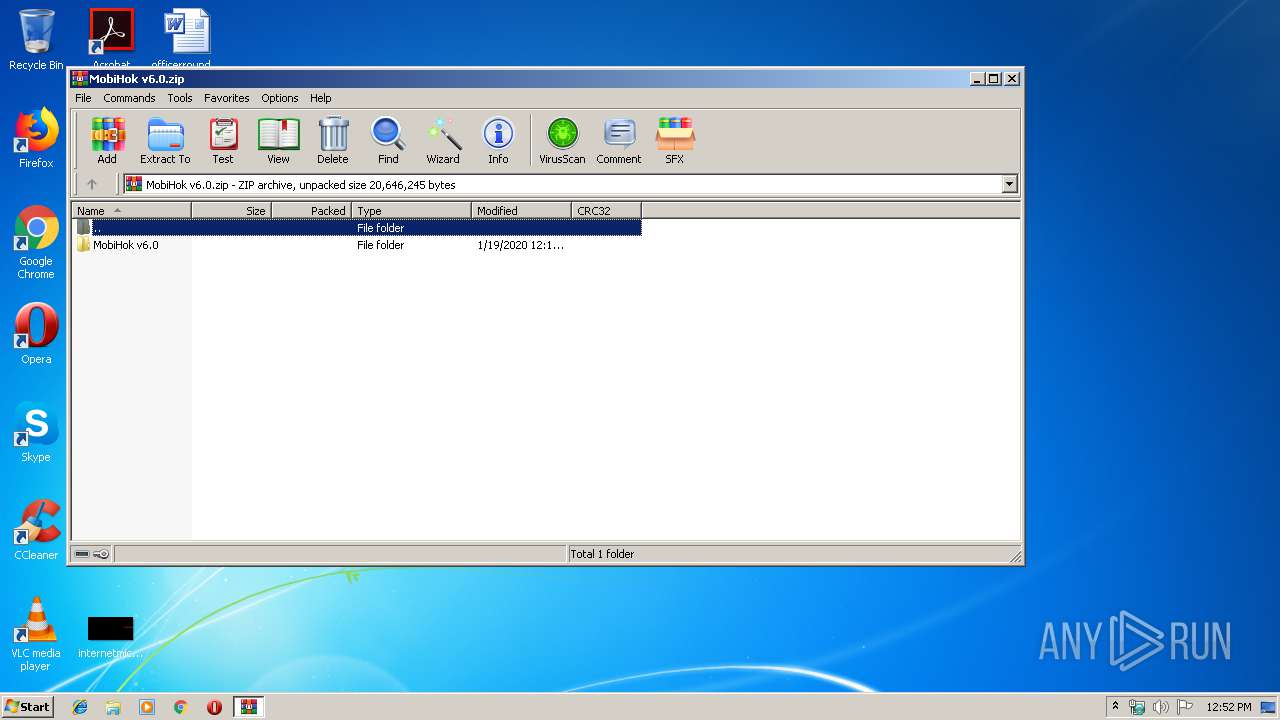
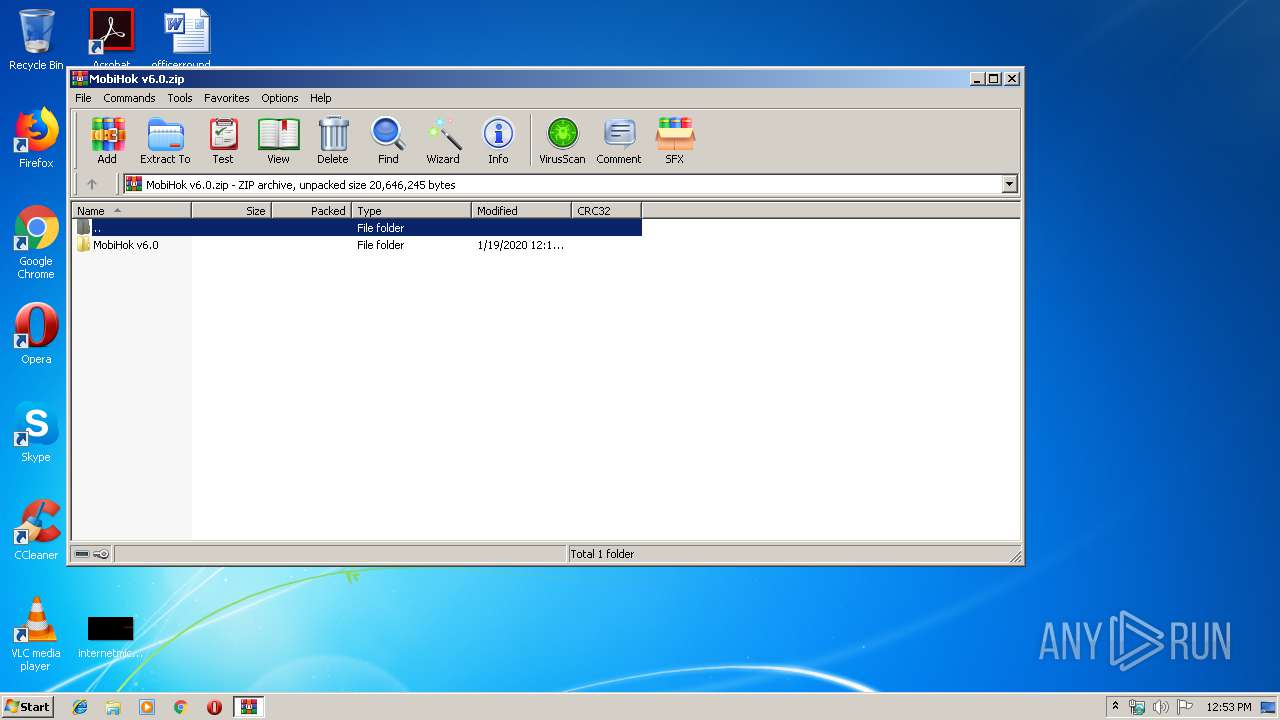
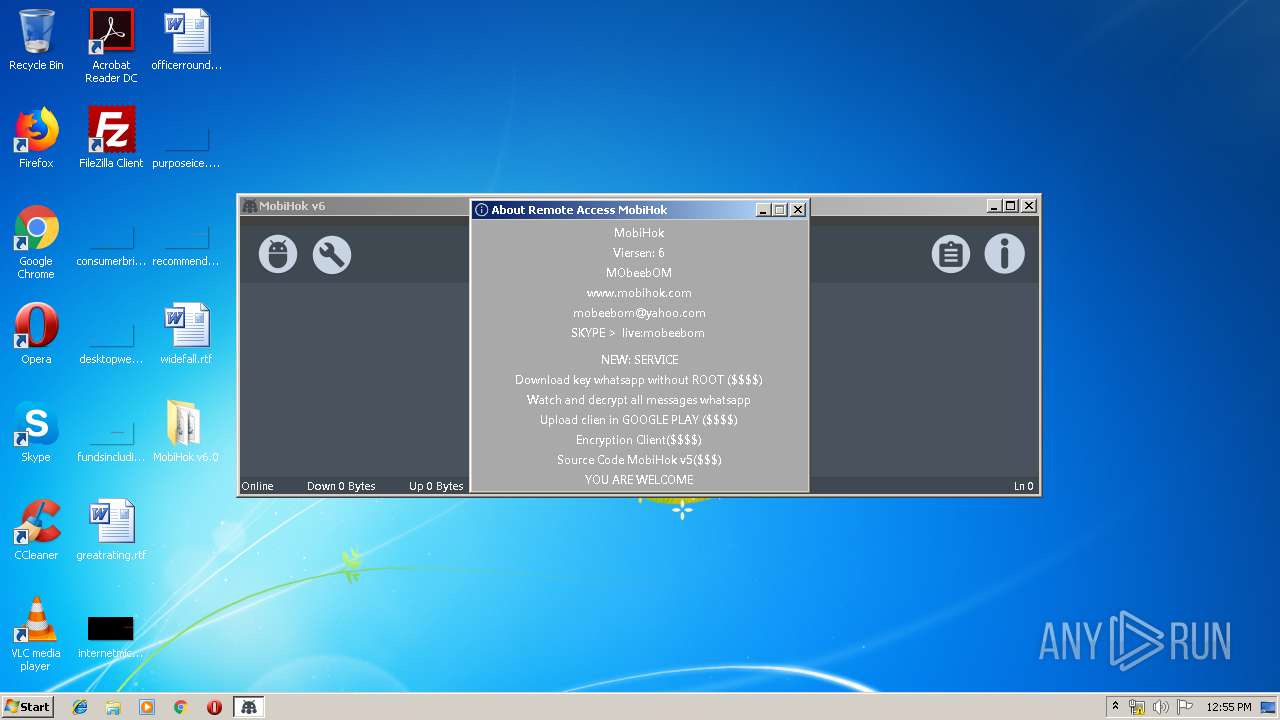
| File name: | MobiHok v6.0.zip |
| Full analysis: | https://app.any.run/tasks/93d428c9-dcf6-4642-bac3-34d989b6dcae |
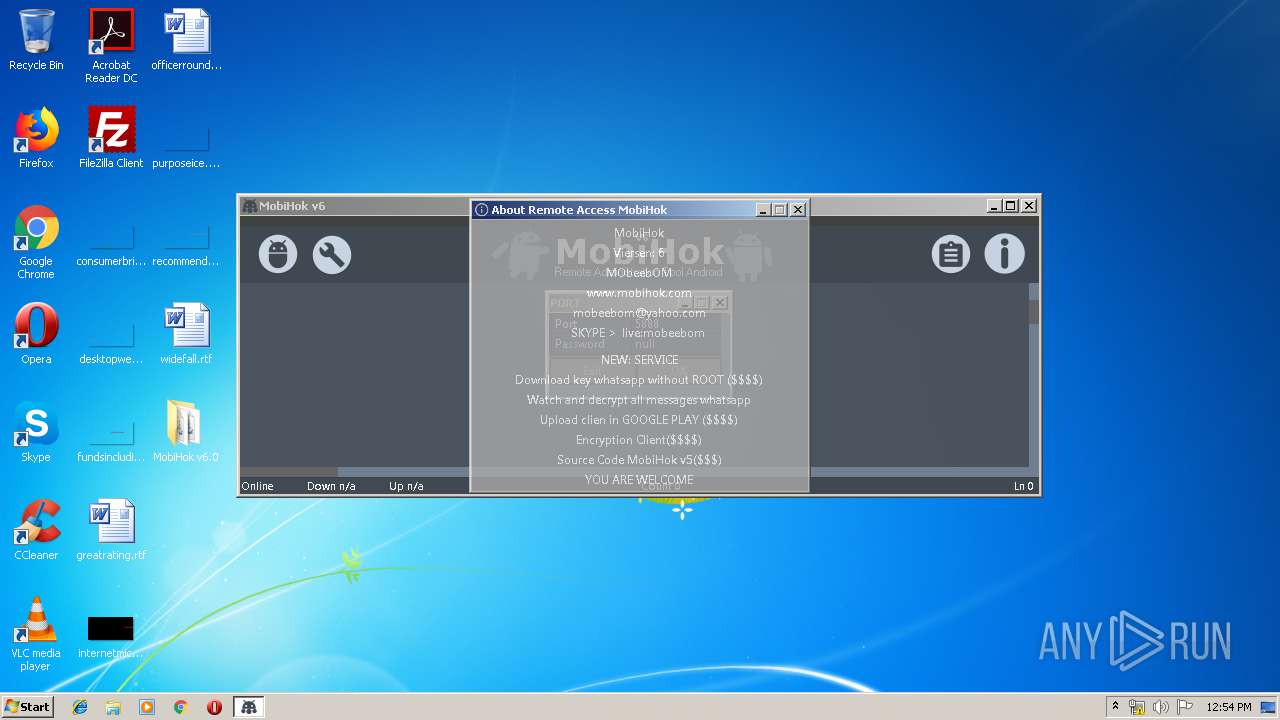
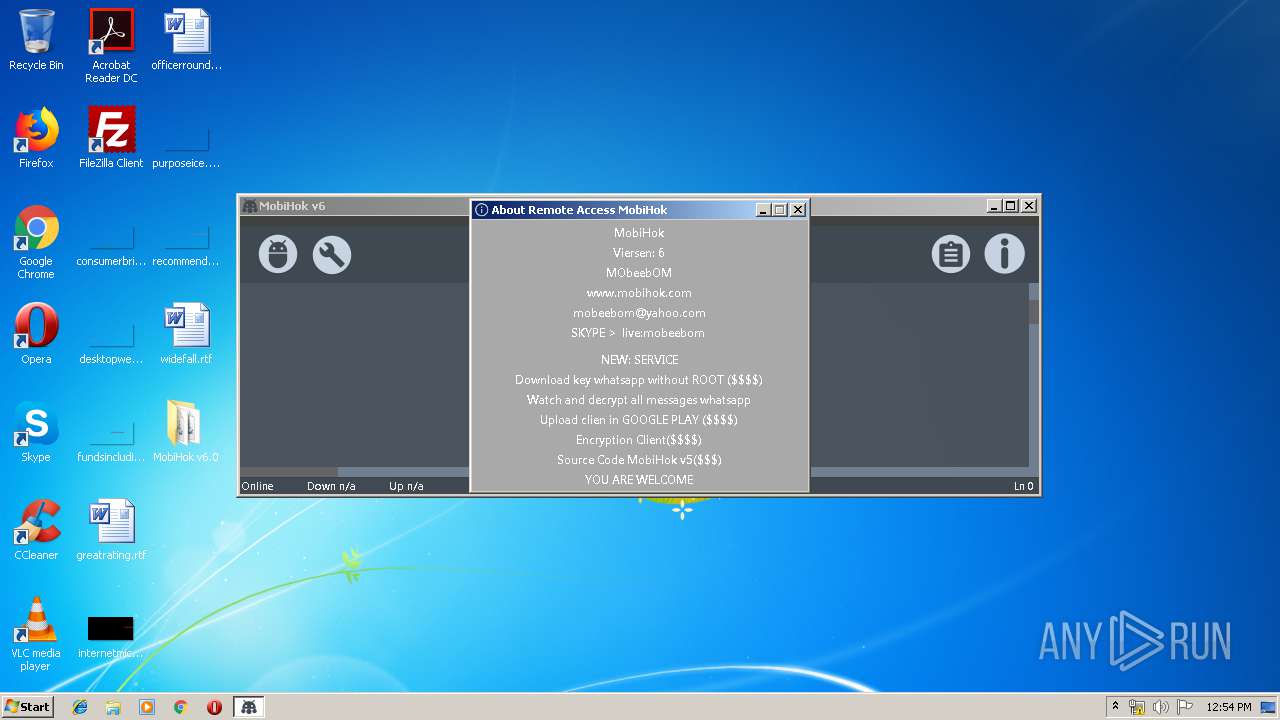
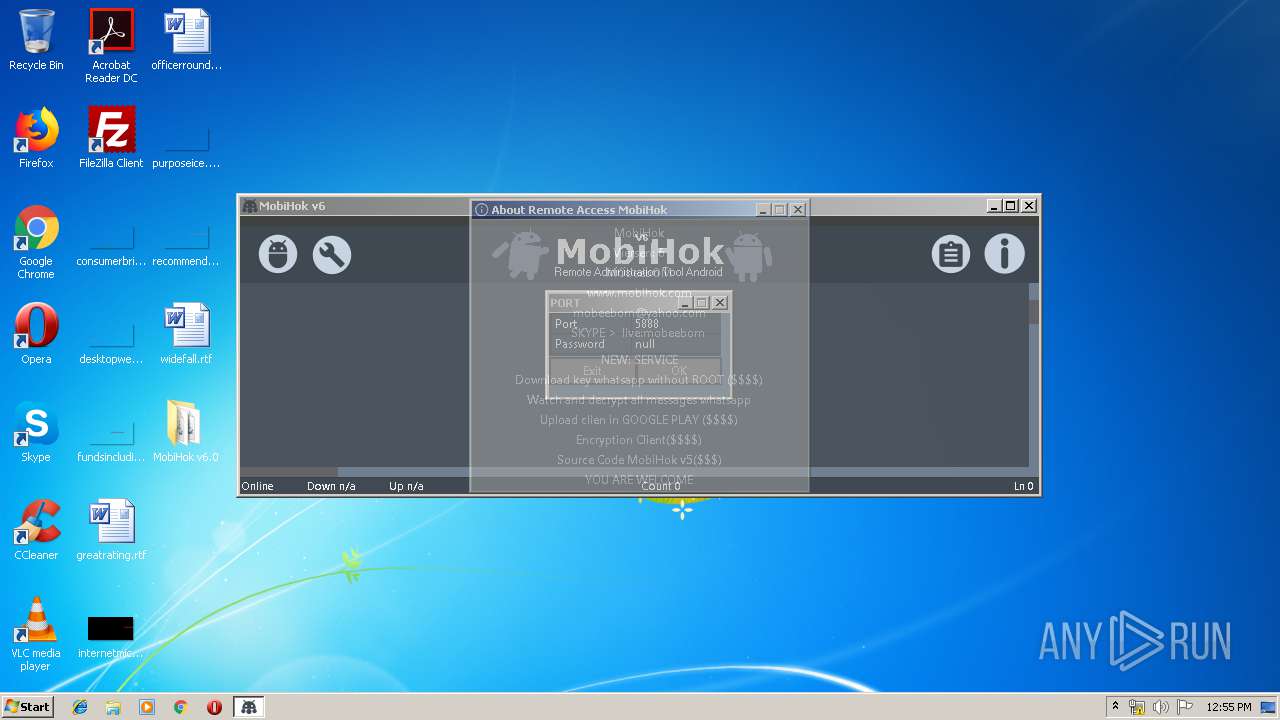
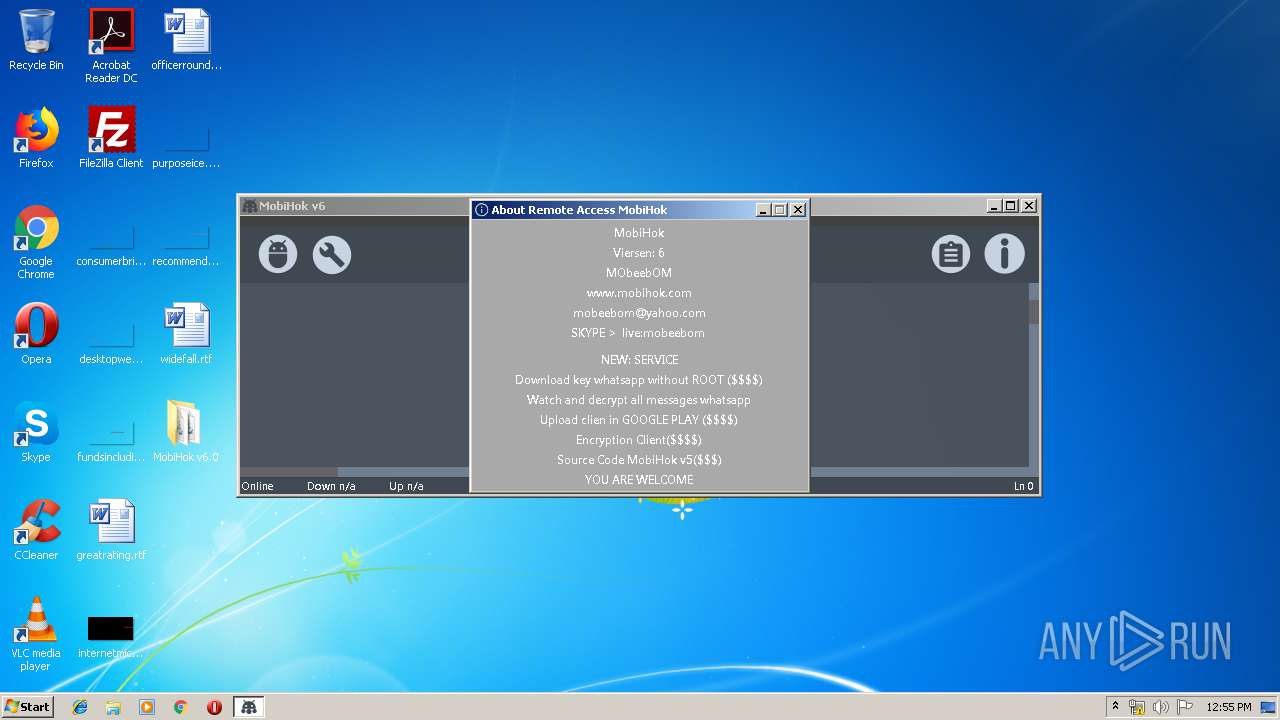
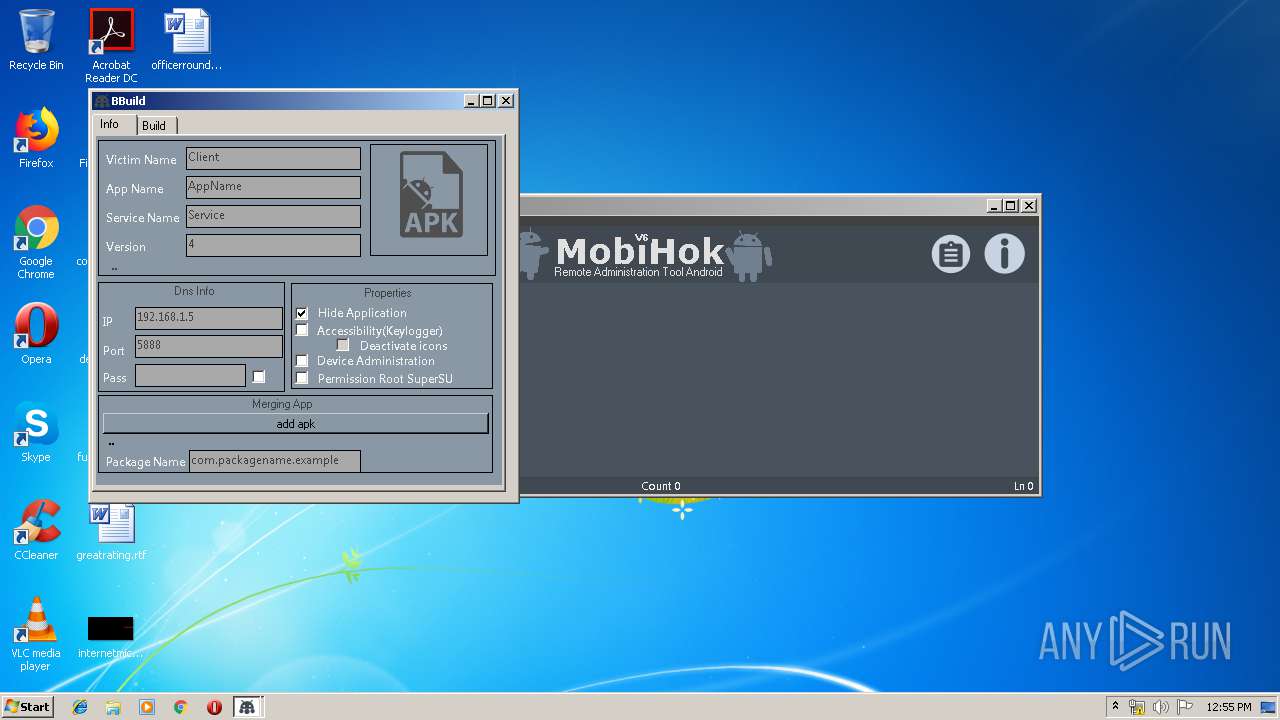
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2020, 12:52:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | FF780DE08712A715E51ABA837A0CE816 |
| SHA1: | 7741D64D968A311B6FE9B75E1CE46E4EB46F5E47 |
| SHA256: | B9CAB3F439FCDEB557F1A943FAE6153E6E4DC8FB8E8FDE76656EC899A31361EB |
| SSDEEP: | 393216:utNl23/ceHXRN7ZnWN5EY1GkqPVyvvnaUPLtC0qlLc:uc3/ceHrZWHtqPEvvnPdqm |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3388)
Application was dropped or rewritten from another process
- MobiHok.exe (PID: 1952)
- MobiHok.exe (PID: 1520)
- MobiHok.exe (PID: 3408)
- MobiHok.exe (PID: 3616)
Runs app for hidden code execution
- MobiHok.exe (PID: 3616)
SUSPICIOUS
Writes to a desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 2992)
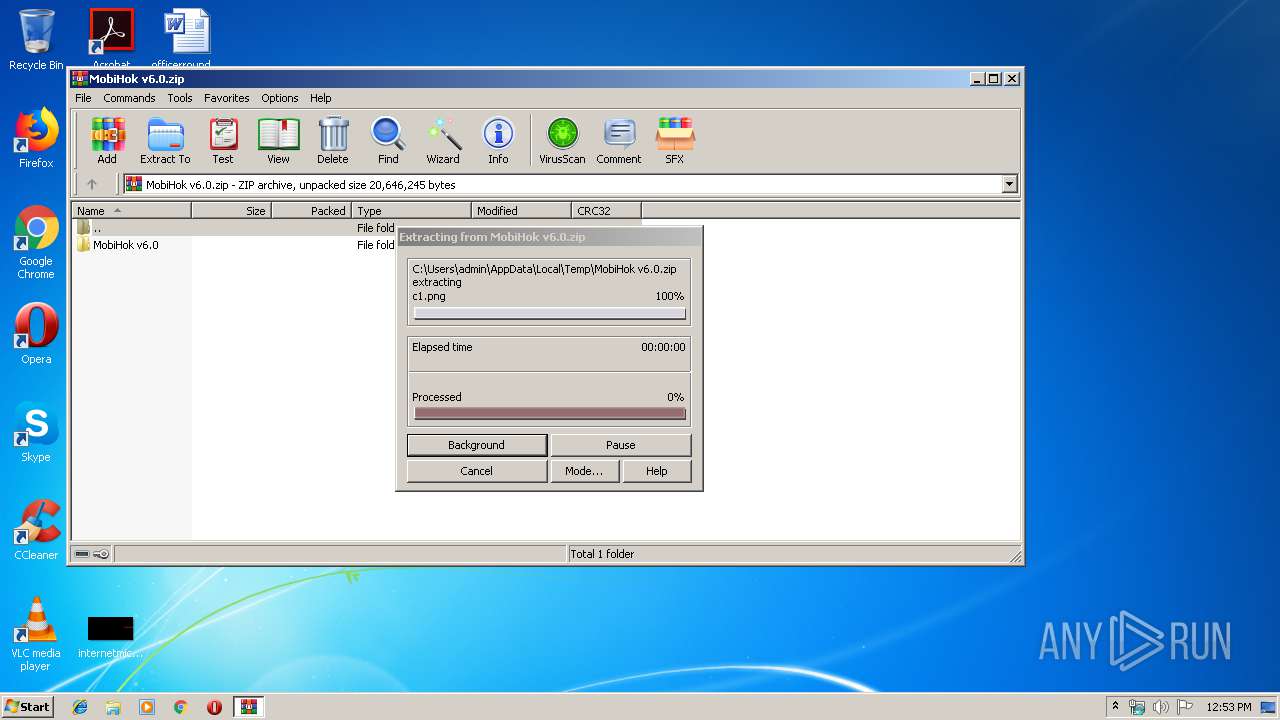
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2992)
Starts CMD.EXE for commands execution
- MobiHok.exe (PID: 3616)
INFO
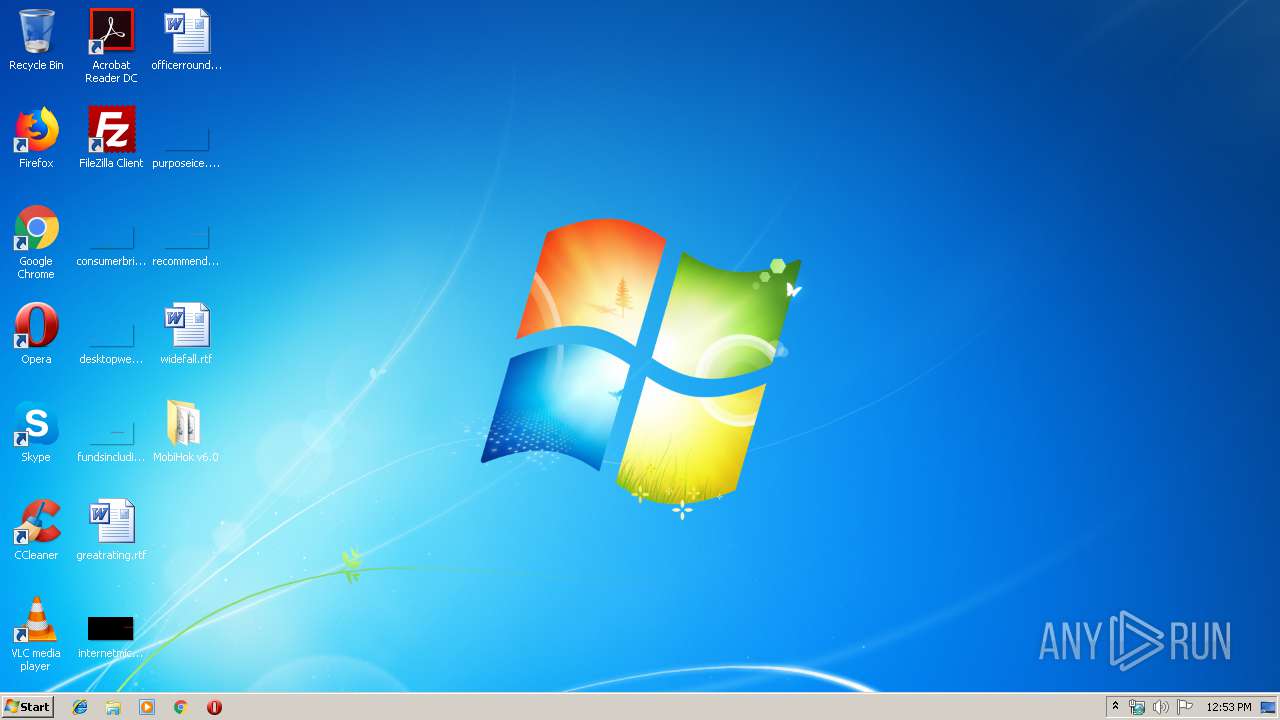
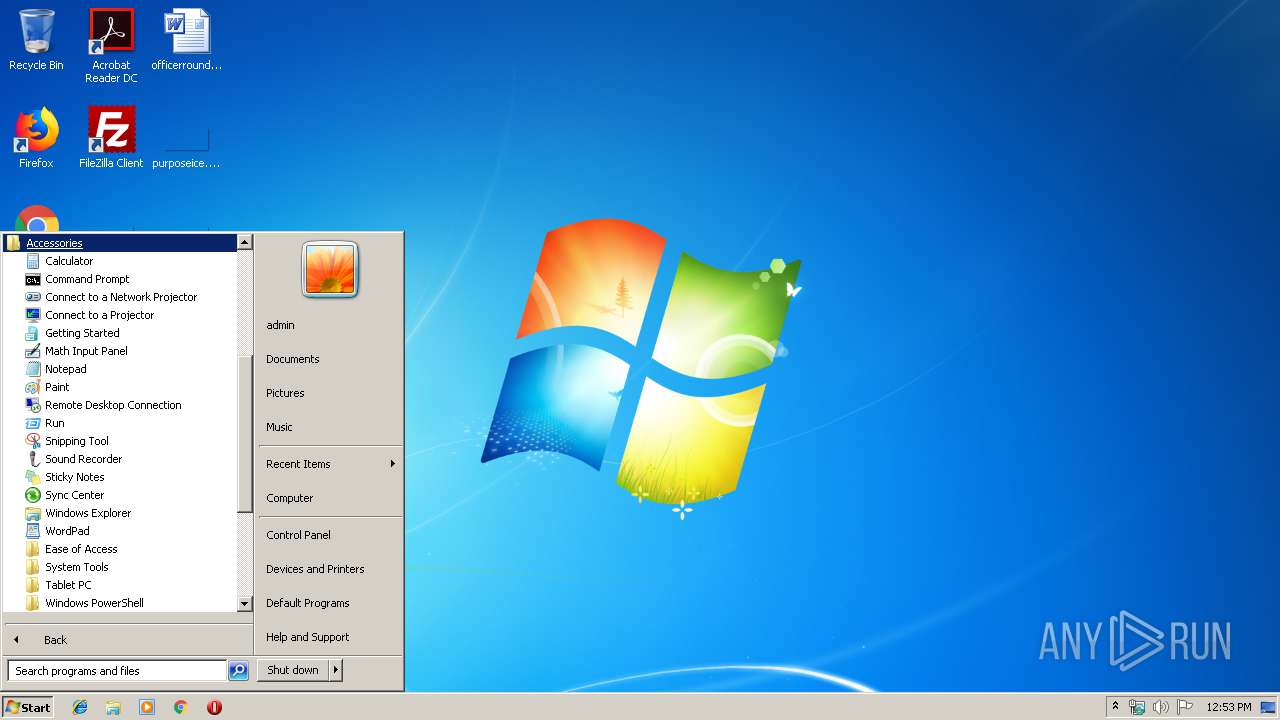
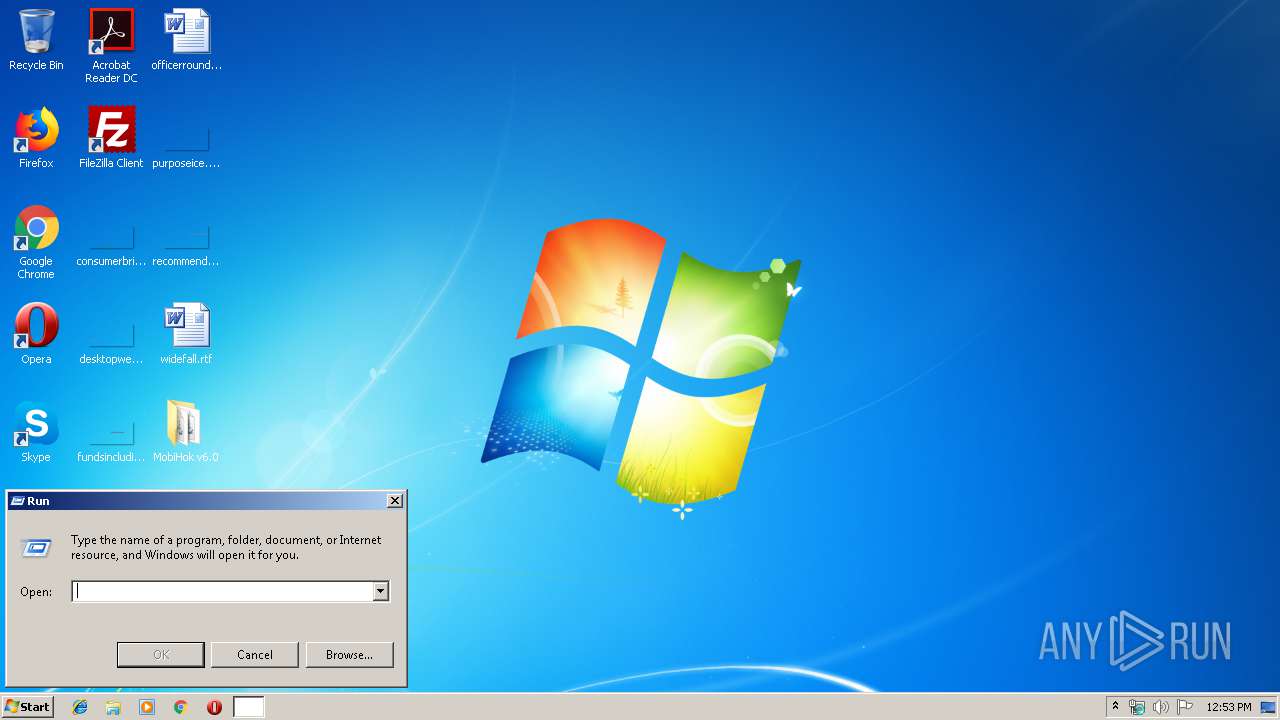
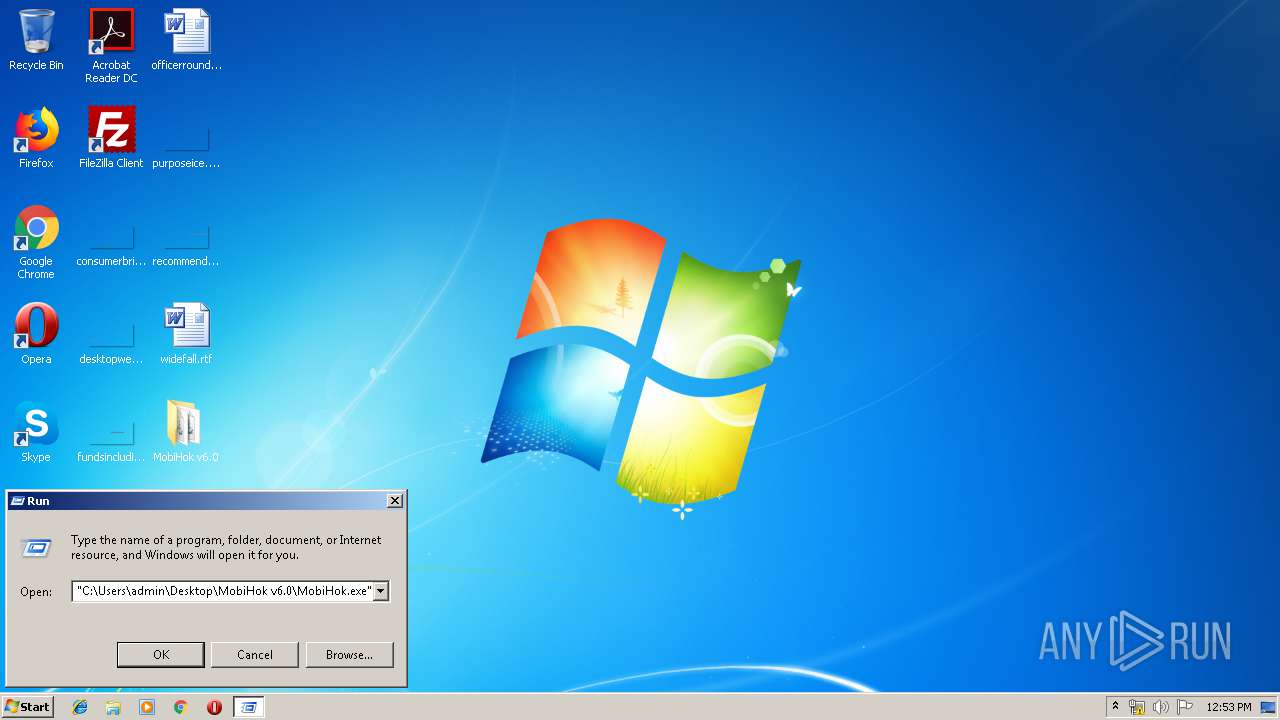
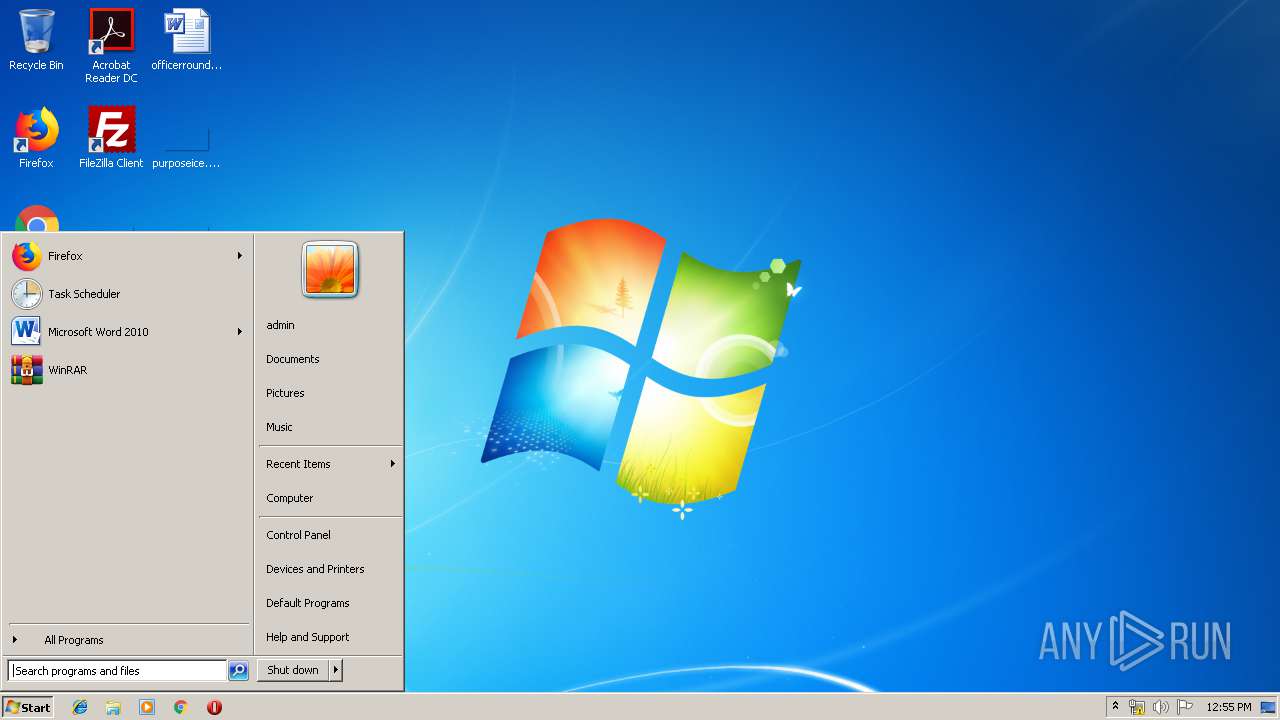
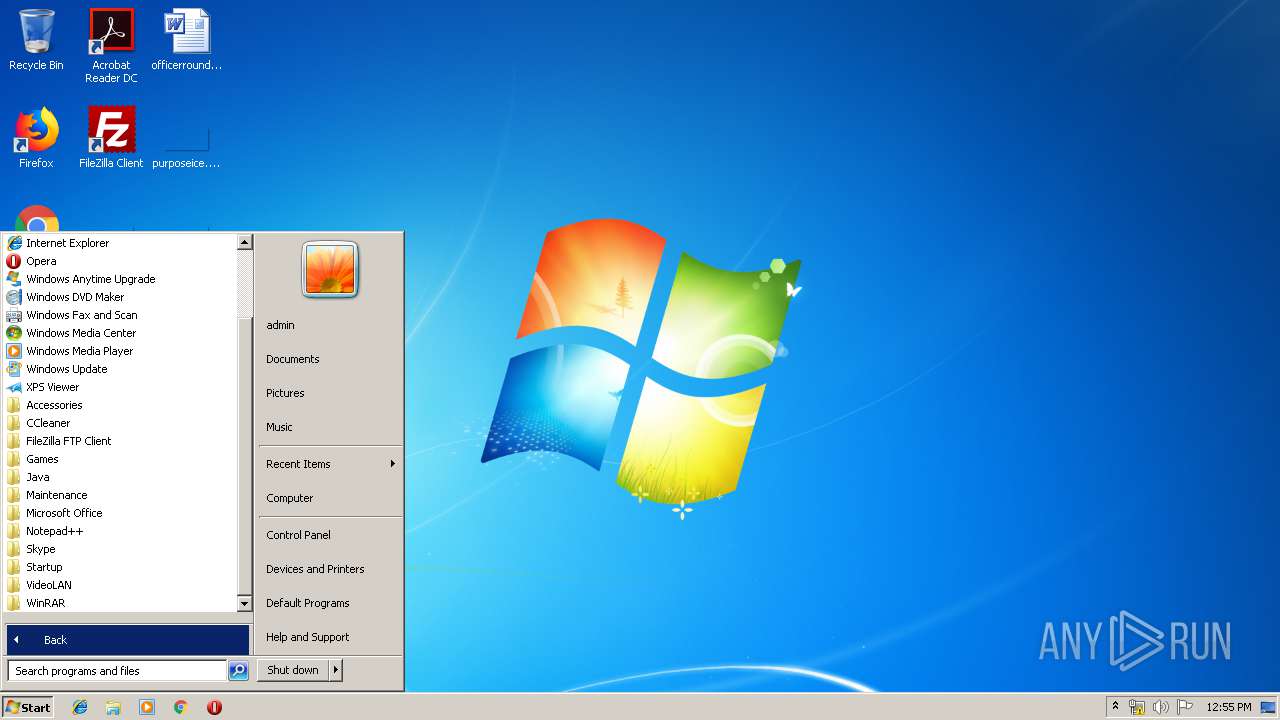
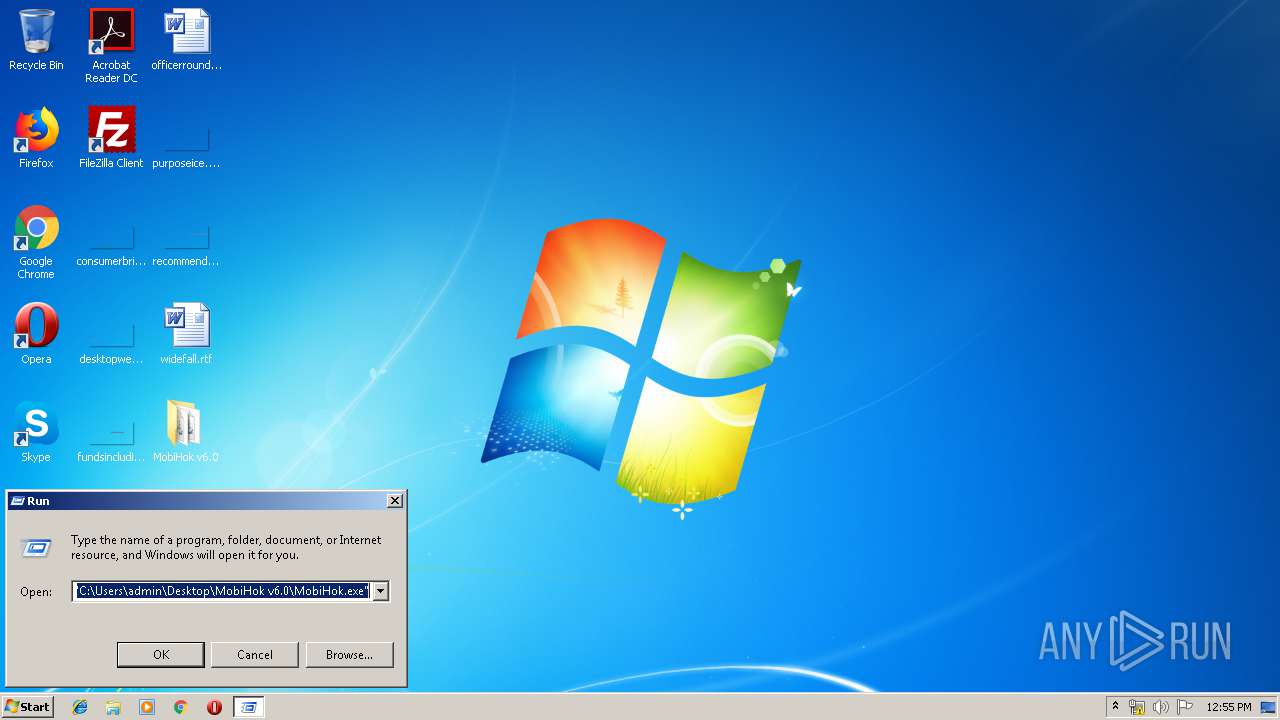
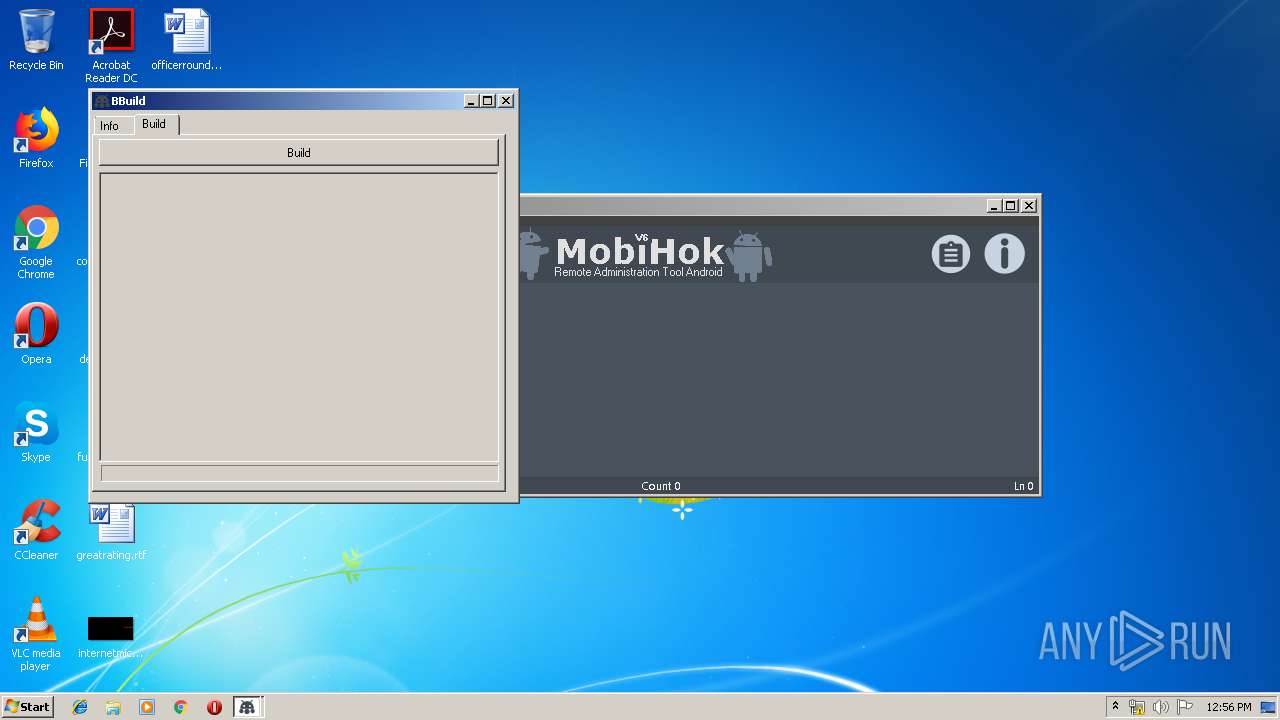
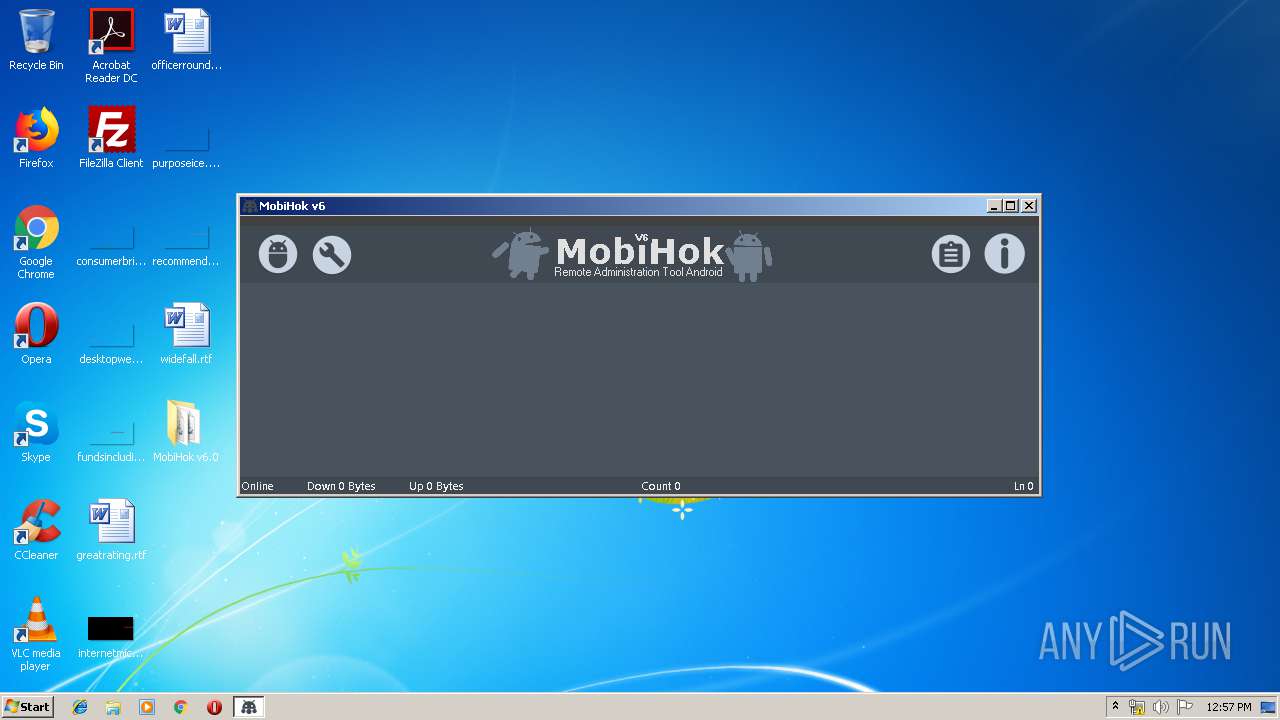
Manual execution by user
- MobiHok.exe (PID: 1520)
- MobiHok.exe (PID: 1952)
- MobiHok.exe (PID: 3408)
- MobiHok.exe (PID: 3616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | None |
| ZipModifyDate: | 2020:01:19 20:17:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | MobiHok v6.0/ |
Total processes
53
Monitored processes
9
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
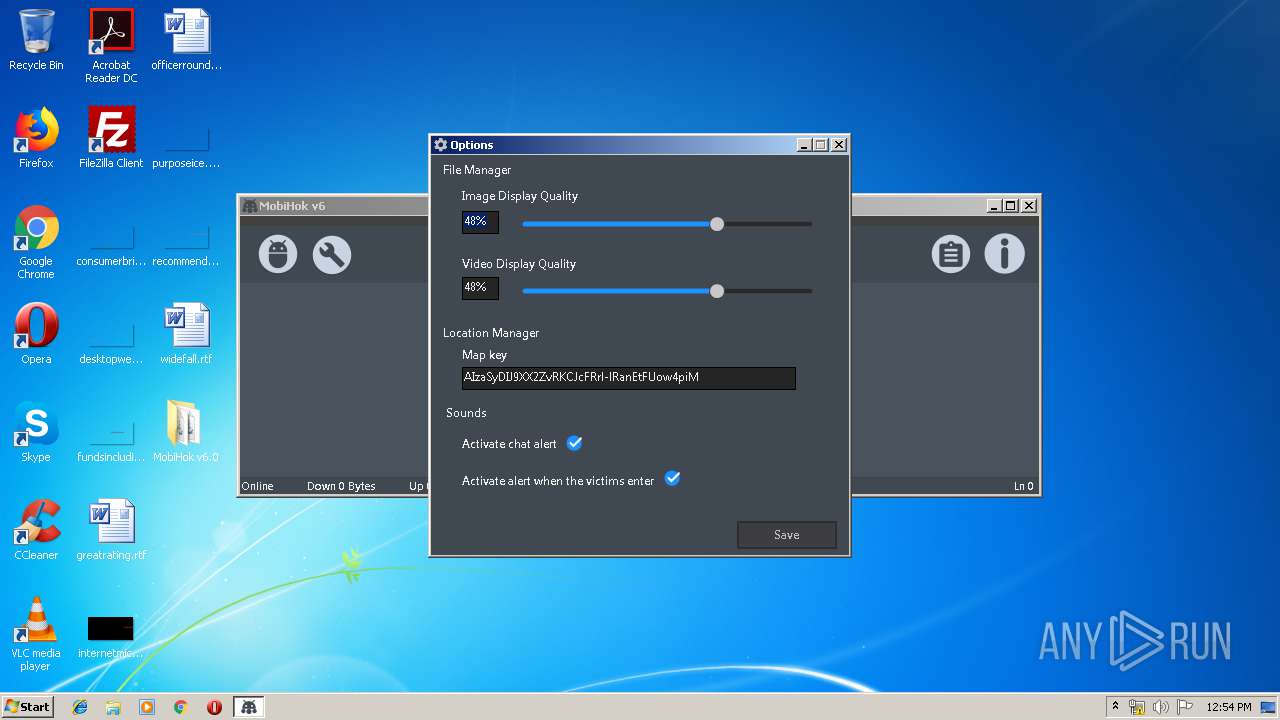
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
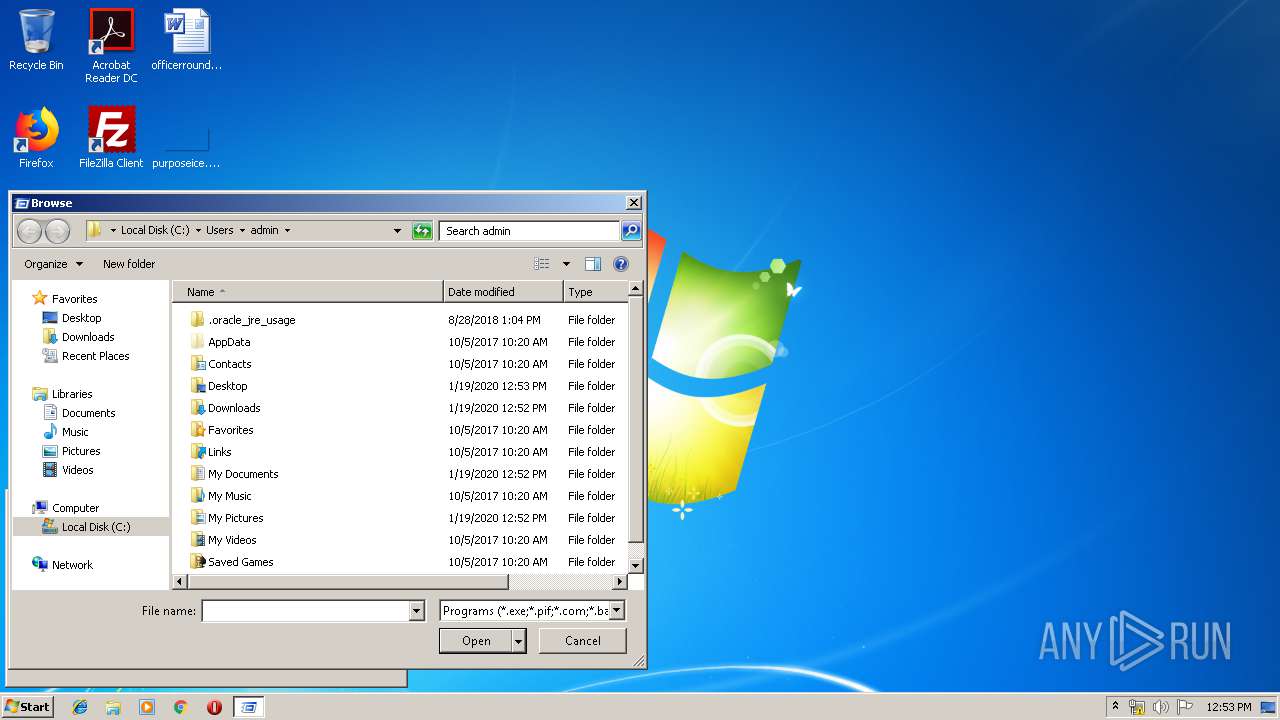
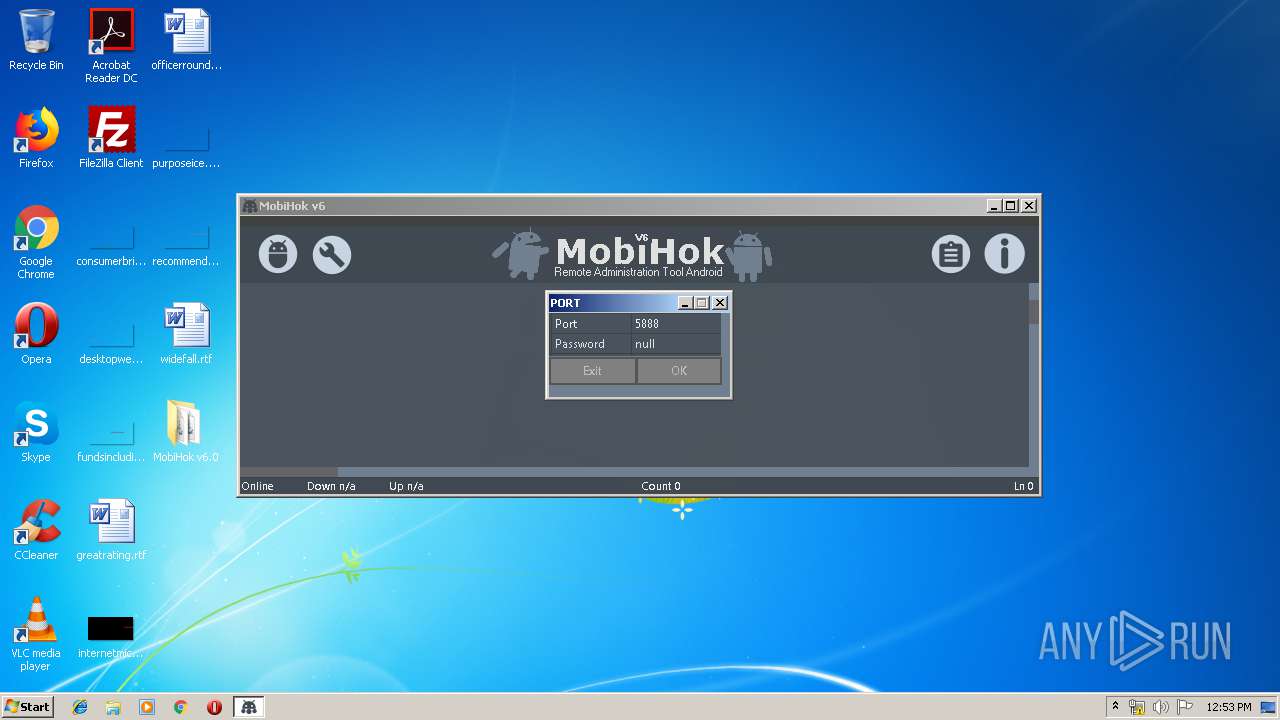
| 1520 | "C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe" | C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe | explorer.exe | ||||||||||||
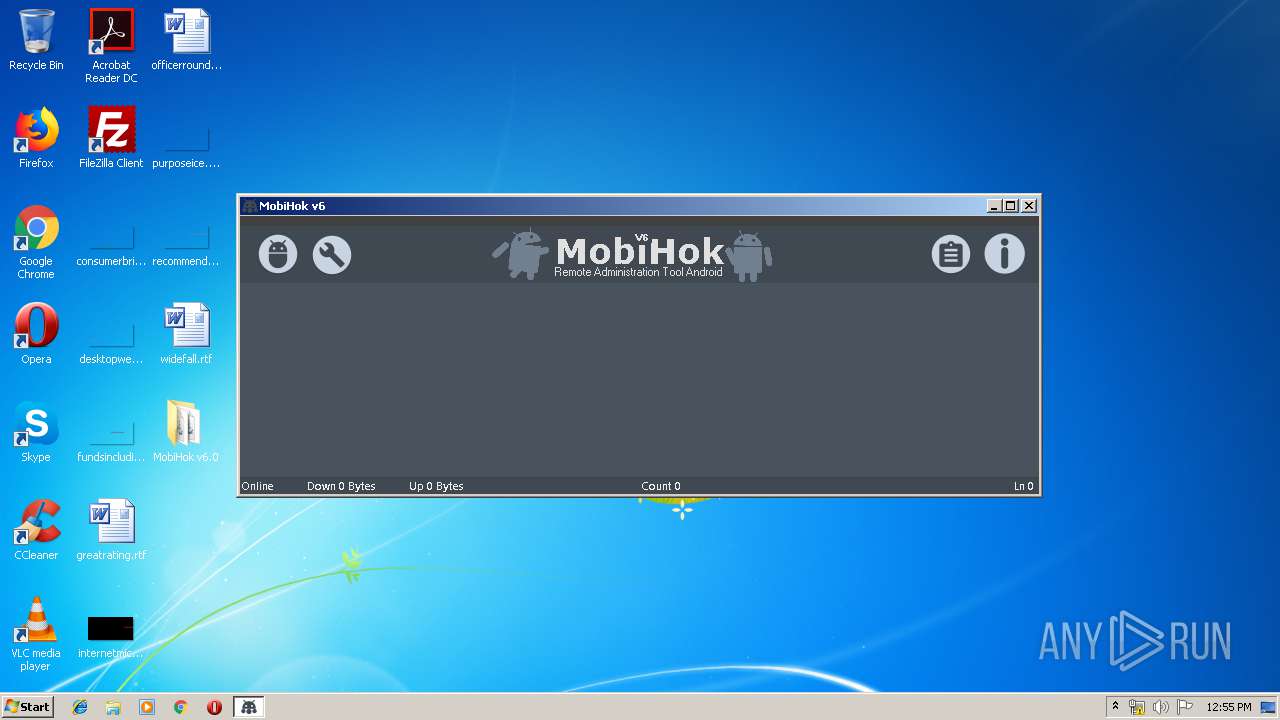
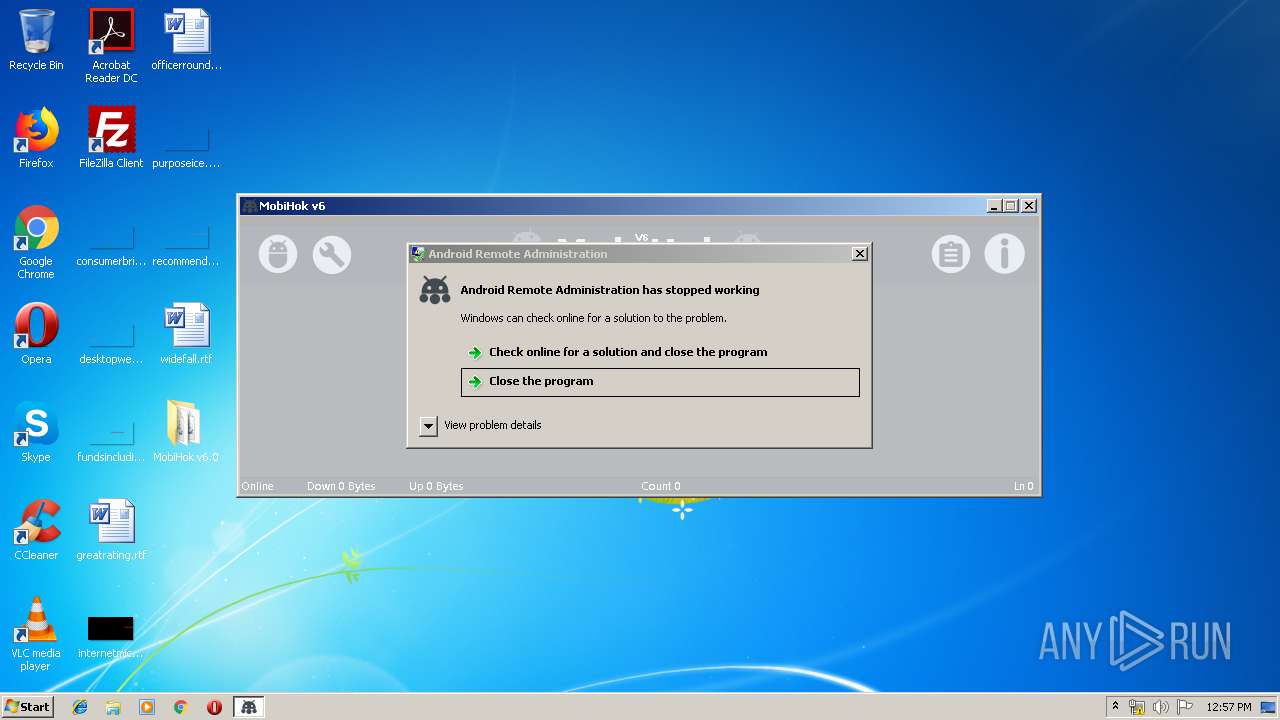
User: admin Integrity Level: HIGH Description: Android Remote Administration Exit code: 0 Version: 6.4.0.0 Modules
| |||||||||||||||
| 1952 | "C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe" | C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Android Remote Administration Exit code: 3221226540 Version: 6.4.0.0 Modules
| |||||||||||||||
| 2944 | java -jar -Duser.language=en "C:\BuildingMH\apktool\\apktool.jar" d app-release.apk | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
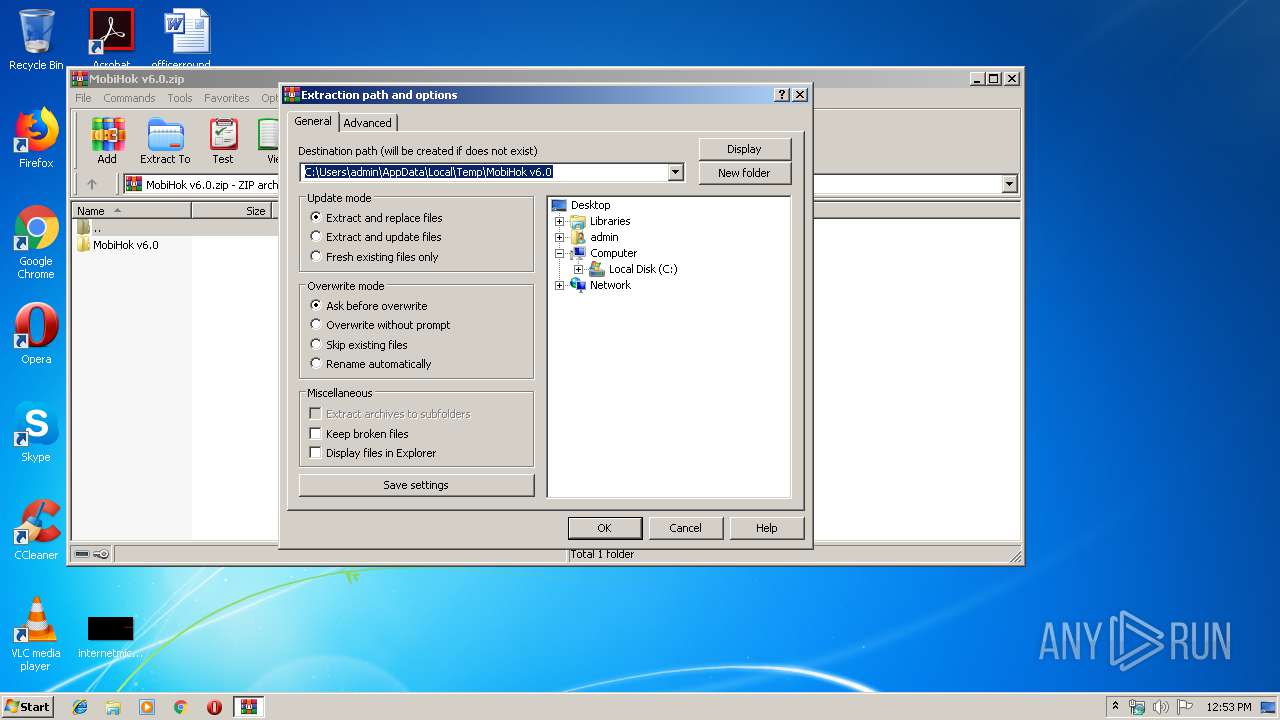
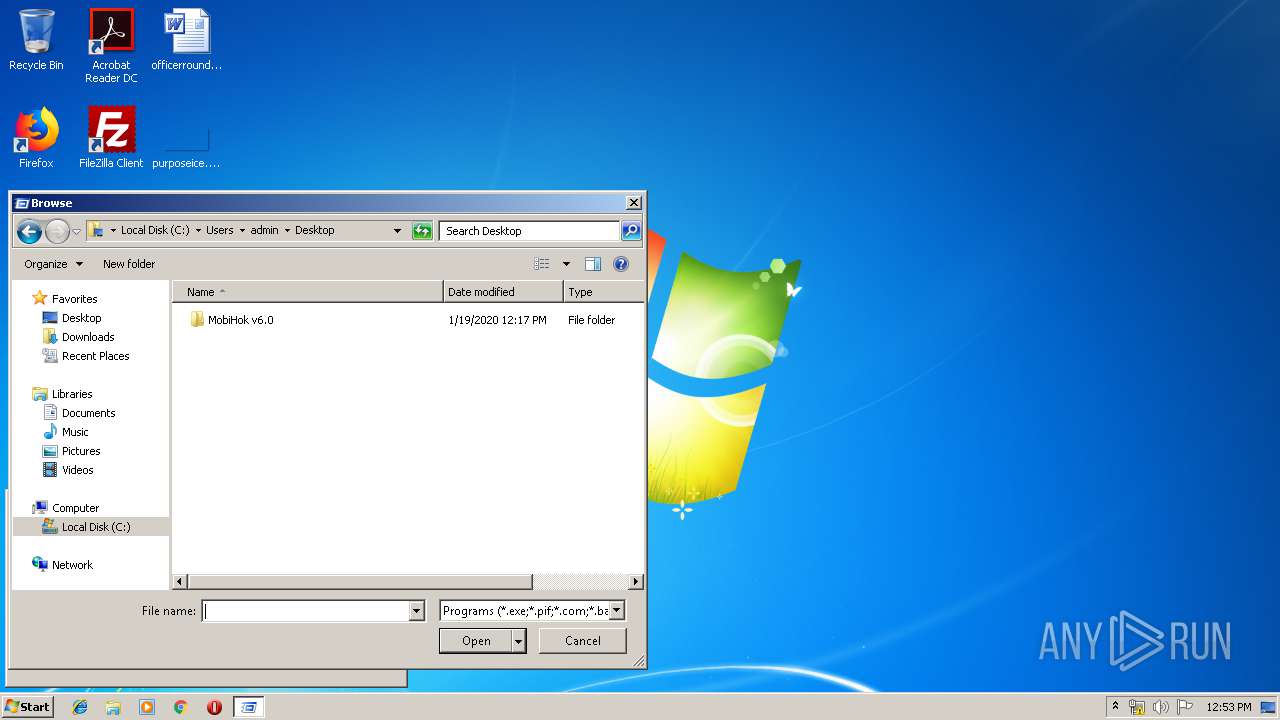
| 2992 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MobiHok v6.0.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3220 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | MobiHok.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3388 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3408 | "C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe" | C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Android Remote Administration Exit code: 3221226540 Version: 6.4.0.0 Modules
| |||||||||||||||
| 3616 | "C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe" | C:\Users\admin\Desktop\MobiHok v6.0\MobiHok.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Android Remote Administration Exit code: 3762504530 Version: 6.4.0.0 Modules
| |||||||||||||||
| 4044 | java -version | C:\ProgramData\Oracle\Java\javapath\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
1 142
Read events
1 110
Write events
32
Delete events
0
Modification events
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MobiHok v6.0.zip | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2992) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
11
Suspicious files
5
Text files
579
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Interop.WMPLib.dll | executable | |
MD5:D1F3D205C9EF2055159D42874EE171B1 | SHA256:A35140EDF2B1FFE8056D18EC8A913601285D261DE959C20B66261E8A93F89A58 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Clients\Client_000000000000000\Screenshot\myscreen_172629.png | image | |
MD5:F66A3940414B2FB8118250238C901FA4 | SHA256:4AC680A283B0A46EE1C9ABEE98D92236C3FFCEC3078B279DE602BC4BB7C61437 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Icons\AccountManager\com.android.email.png | image | |
MD5:1FC4ABE2F26276C04B55591BD0A584C3 | SHA256:6E68465A4C4E86F84517A3B230510E4D5D2F163744CD592C55DA8A89B0C866F5 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Audio\c.wav | wav | |
MD5:27096BEF1DC9B799CDA15F750F03DEBE | SHA256:59AC30EA0CC45B94A8D5DFA7A2066DEC9C9510629999326FBD95FB92E8B06AB9 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\CoreAudioApi.dll | executable | |
MD5:6A009B7C4B252788D80D4E40ADCF51CE | SHA256:DF6115987161EE1238F9564BD10C998D9016F582E5B7B9D23D21A74D6955BDD3 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Icons\AccountManager\com.facebook.messenger.png | image | |
MD5:A3E44E927AFBBCAFD1CCBA0DF328341B | SHA256:38D2CDFF888A68FA4928ADA746DB2588E76127447ACA16BEAD6E03D940D9D266 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Icons\AccountManager\com.bbm.account.png | image | |
MD5:5343892A5AEBBA75AD7485437151A5DA | SHA256:35BBB89EC6ACEEAF456C11E00FFCC8B9B08A642F22BA136B2E16AE49A2CA4767 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Audio\v.wav | wav | |
MD5:BE9D61130C128A445075763B0F2F01B8 | SHA256:C2924E0DA65984CD28DBCA3A75A606E7E3E97205D2FFED1EBC26B9C4D8C56DF5 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Icons\AccountManager\account.png | image | |
MD5:37B34268C25A9BF7EBF61DD220382F5F | SHA256:2D522164E403478E178483DFD9D1F31BA2E8E8E9056F967AA626308E39AA6BD0 | |||
| 2992 | WinRAR.exe | C:\Users\admin\Desktop\MobiHok v6.0\Resources\Audio\vv.wav | wav | |
MD5:E177531A745D763A36BEA84BF778089F | SHA256:42CB5F6E9605F429C6504430710DE0110697E1219DB28C7551E382170253ACB0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report