| File name: | ActivationATI(H).zip |
| Full analysis: | https://app.any.run/tasks/ebf7a4ad-053b-4305-8e6f-177e0fd1bcfa |
| Verdict: | Malicious activity |
| Analysis date: | June 29, 2018, 19:14:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 43662D82E1F5BC3AE02B3C363557645F |
| SHA1: | 0543AFC378F45E3348D27BB696DA52158C8986AB |
| SHA256: | B9BC6B9FFA3CF5393FB139E546B4FD52E09F1B7CF85363D7CBB624E460F4C713 |
| SSDEEP: | 98304:Sy4MBlLol1nR9aTUOi50/Yj1FoUmCKEjhA:Sy4MfexRSULWQj1yBe+ |
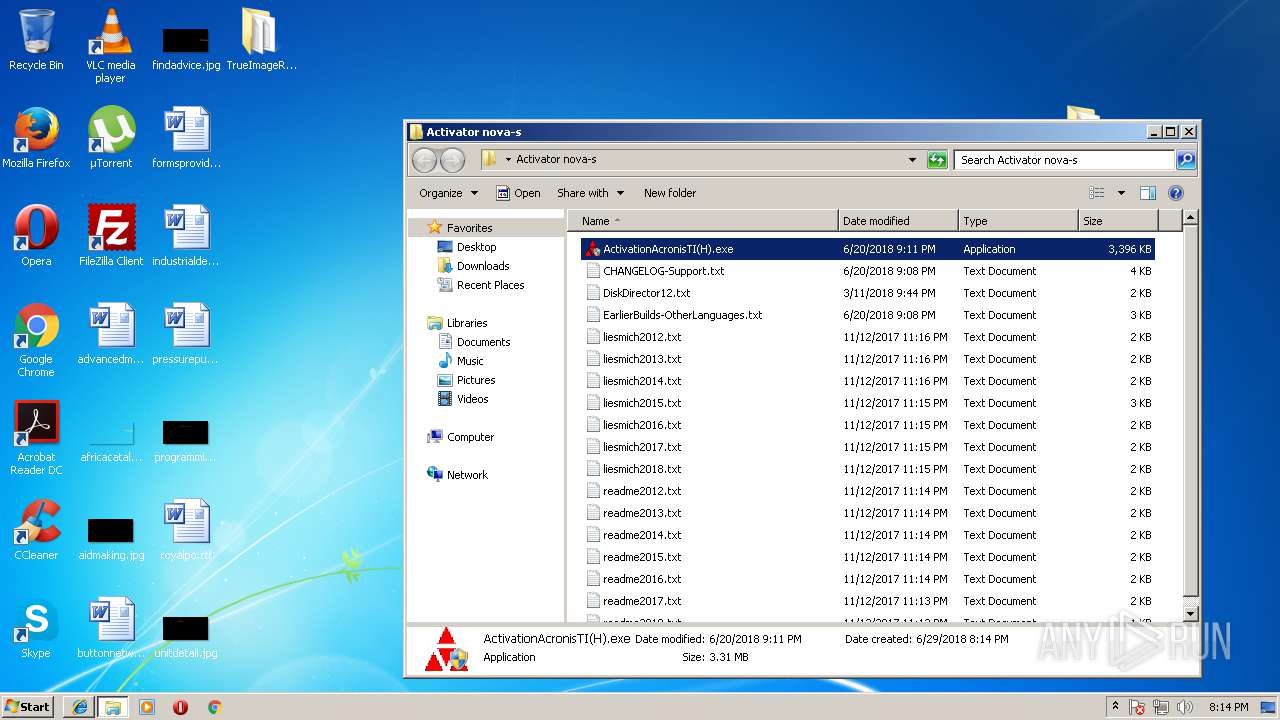
MALICIOUS
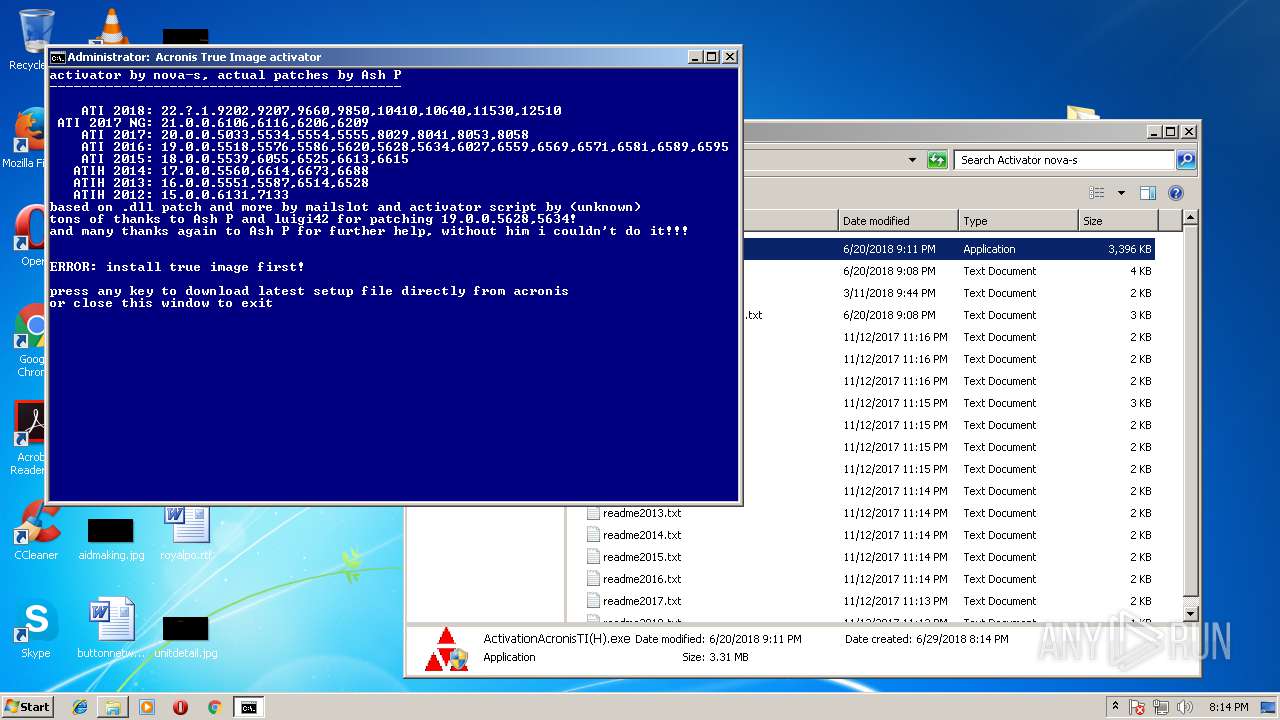
Application was dropped or rewritten from another process
- ActivationAcronisTI(H).exe (PID: 3412)
- ActivationAcronisTI(H).exe (PID: 4016)
SUSPICIOUS
Executable content was dropped or overwritten
- ActivationAcronisTI(H).exe (PID: 4016)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2028)
- cmd.exe (PID: 2736)
Checks Windows language
- reg.exe (PID: 2780)
Checks supported languages
- reg.exe (PID: 2780)
Starts CMD.EXE for commands execution
- ActivationAcronisTI(H).exe (PID: 4016)
- cmd.exe (PID: 3444)
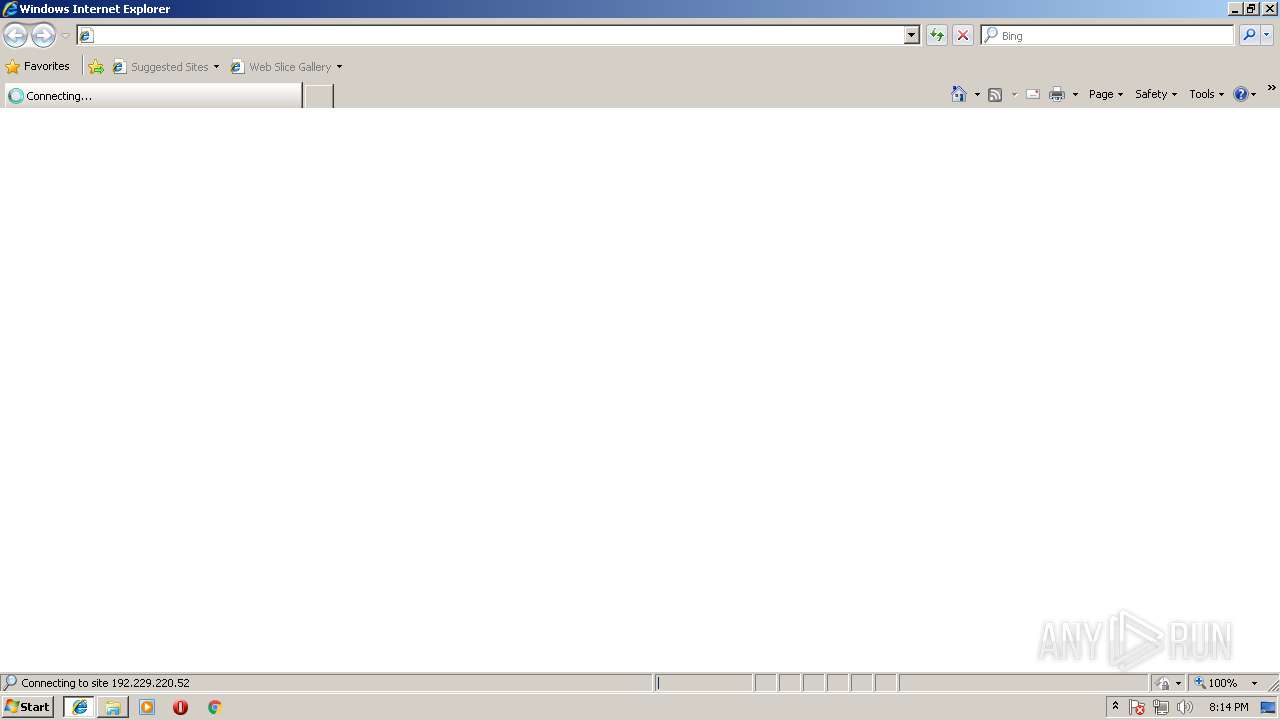
Starts Internet Explorer
- cmd.exe (PID: 3444)
INFO
Application launched itself
- iexplore.exe (PID: 3856)
Dropped object may contain URL's
- iexplore.exe (PID: 688)
- ActivationAcronisTI(H).exe (PID: 4016)
- xcopy.exe (PID: 3512)
Reads internet explorer settings
- iexplore.exe (PID: 688)
Creates files in the user directory
- iexplore.exe (PID: 688)
Changes internet zones settings
- iexplore.exe (PID: 3856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:06:20 22:11:22 |
| ZipCRC: | 0x63b058e9 |
| ZipCompressedSize: | 3433054 |
| ZipUncompressedSize: | 3477323 |
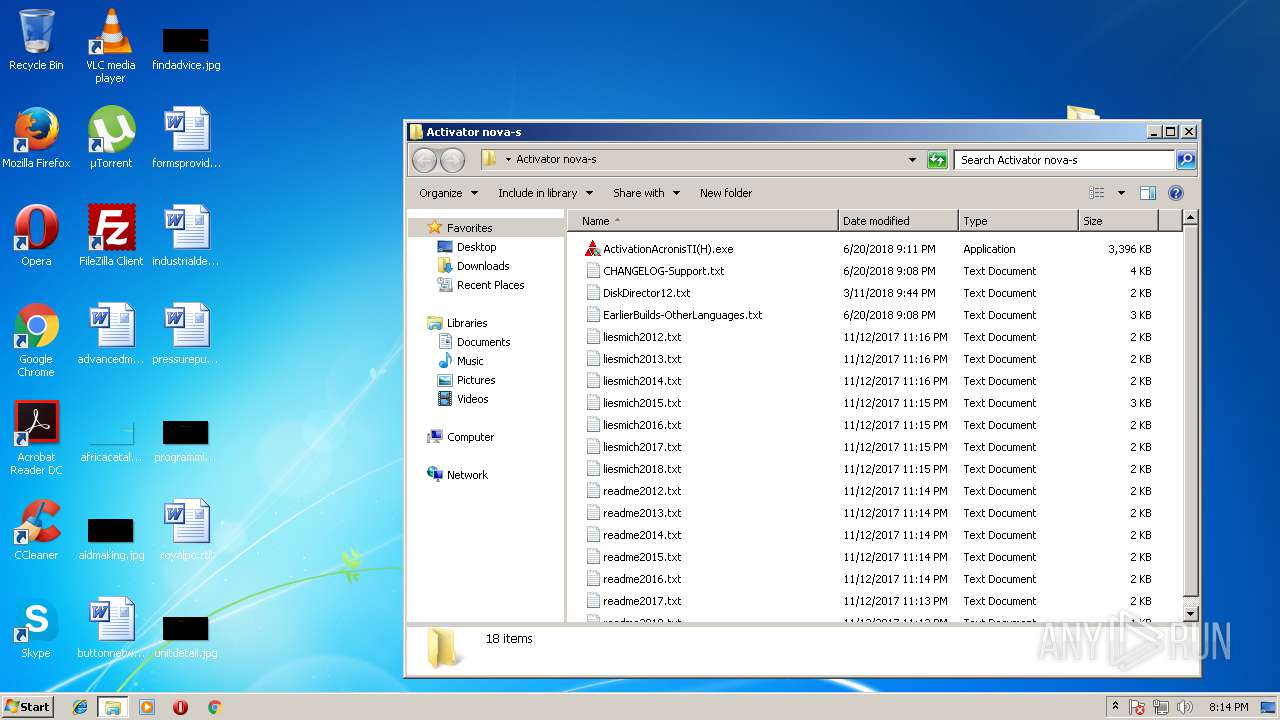
| ZipFileName: | Activator nova-s/ActivationAcronisTI(H).exe |
Total processes
52
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3856 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1596 | REG QUERY "HKLM\SOFTWARE\Acronis\TrueImageHome\Settings" /v LicenseActivatorExePath | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2028 | C:\Windows\system32\cmd.exe /c REG QUERY "HKLM\SOFTWARE\Acronis\TrueImageHome\Settings" /v LicenseActivatorExePath 2>NUL | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2168 | mode con:cols=86 lines=36 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
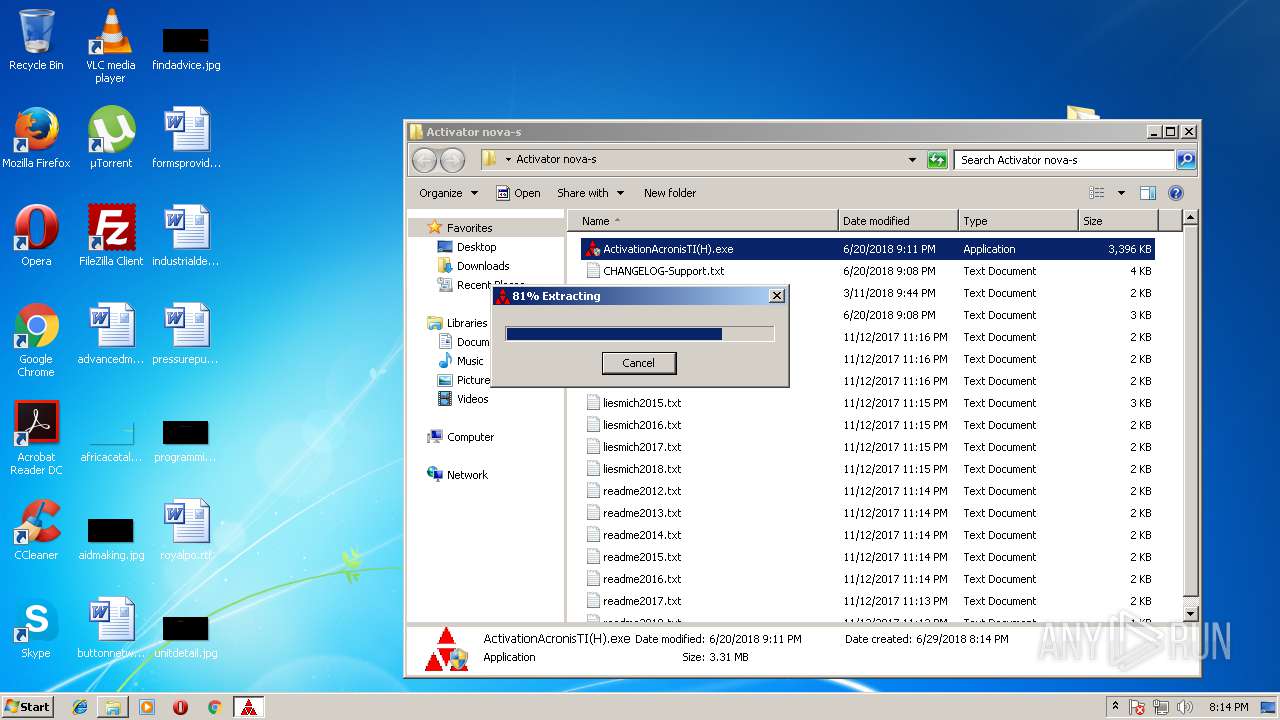
| 2188 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\ActivationATI(H).zip" | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
| 2736 | C:\Windows\system32\cmd.exe /c REG QUERY "HKLM\SYSTEM\CurrentControlSet\Control\Nls\Language" /v InstallLanguage | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2780 | REG QUERY "HKLM\SYSTEM\CurrentControlSet\Control\Nls\Language" /v InstallLanguage | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
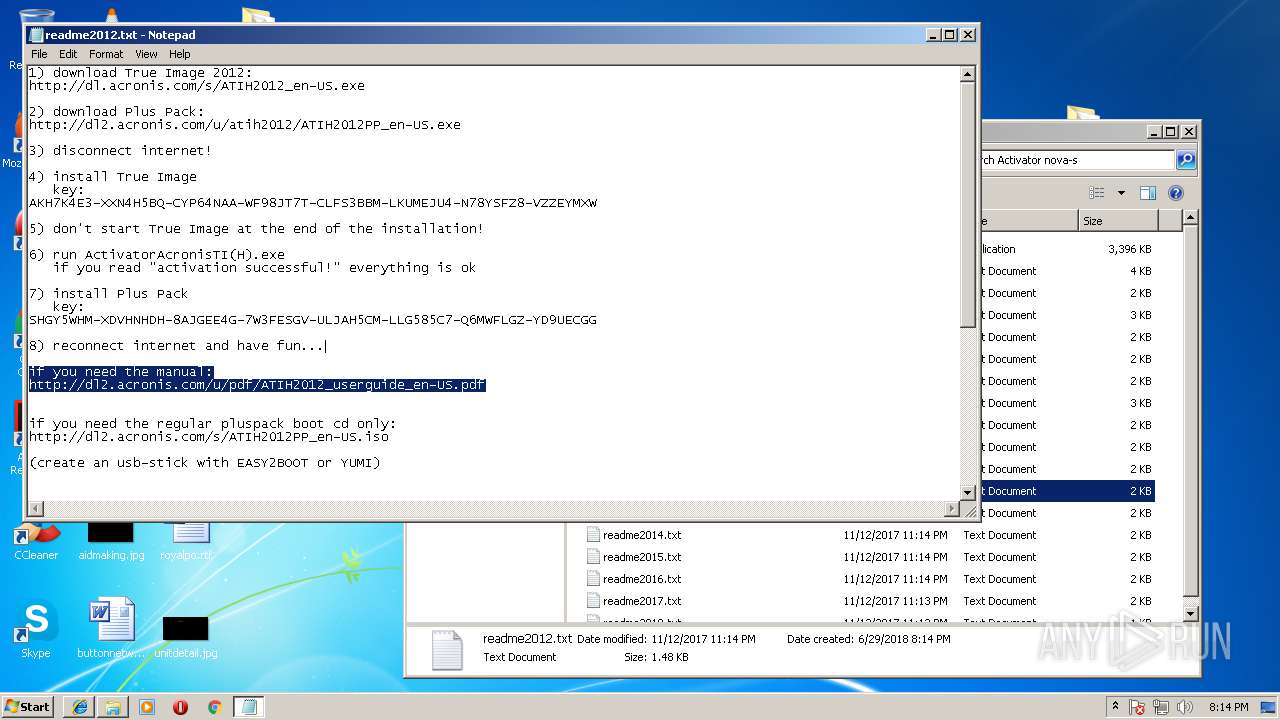
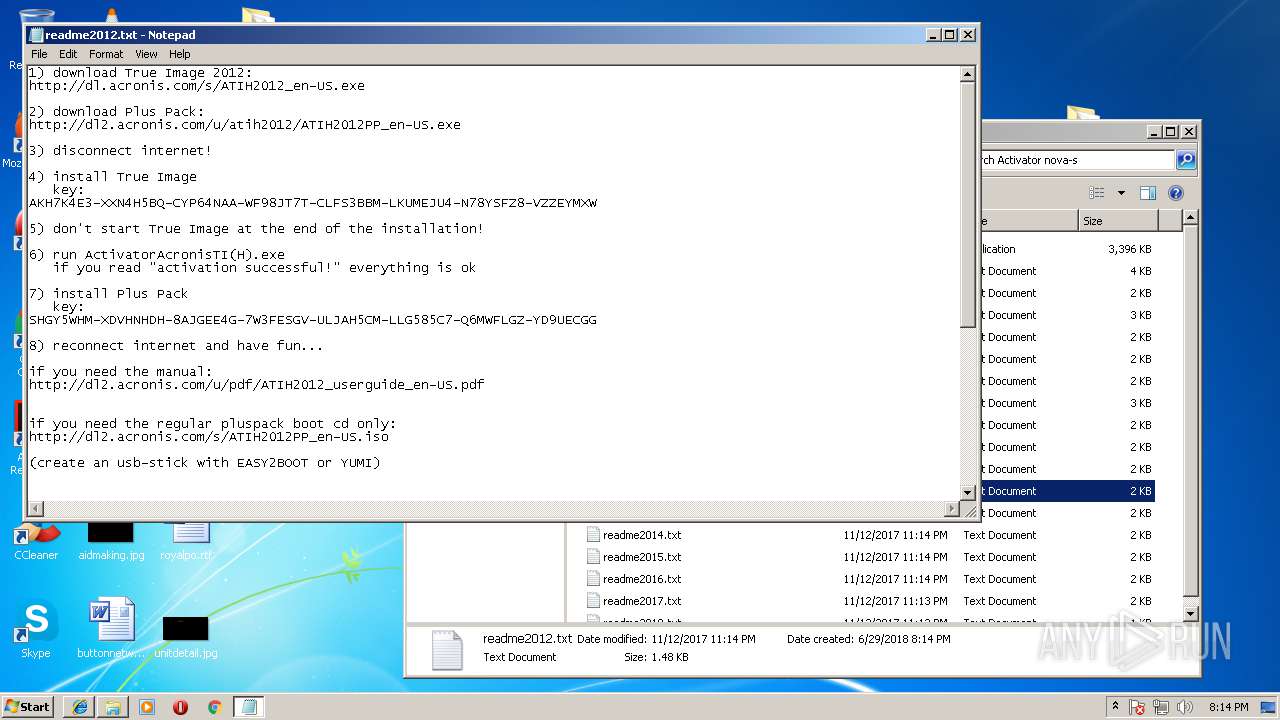
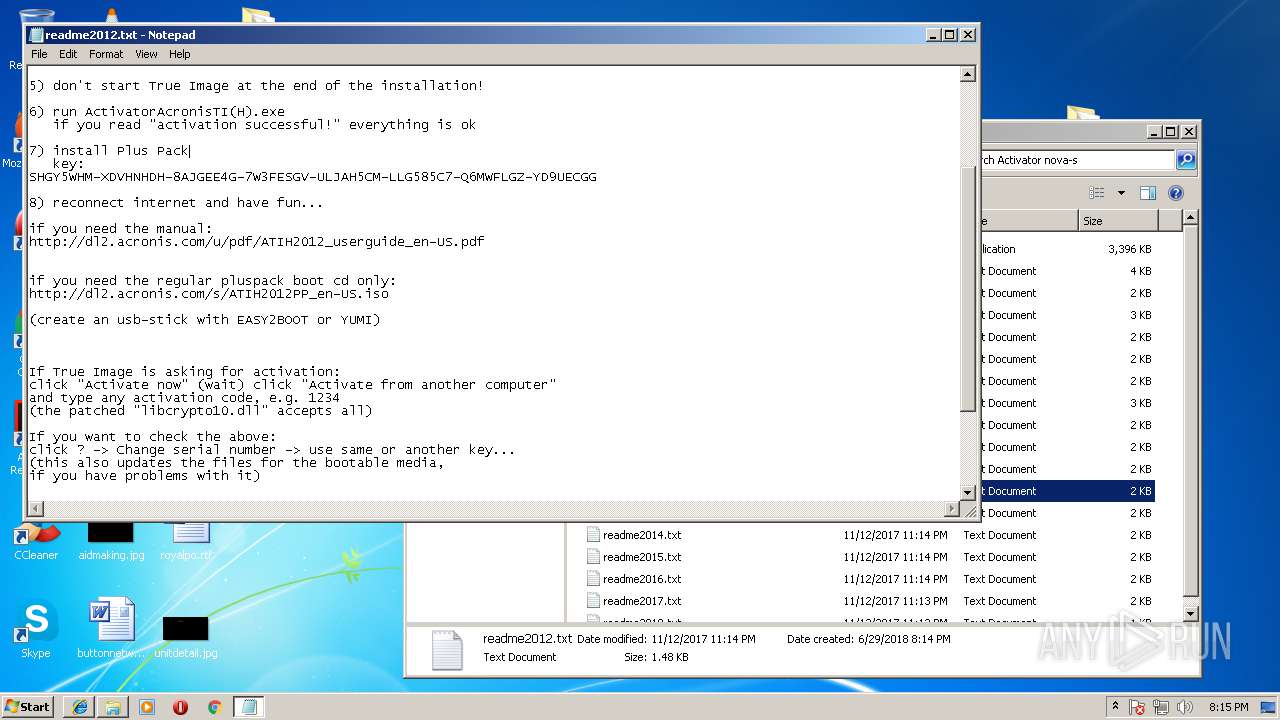
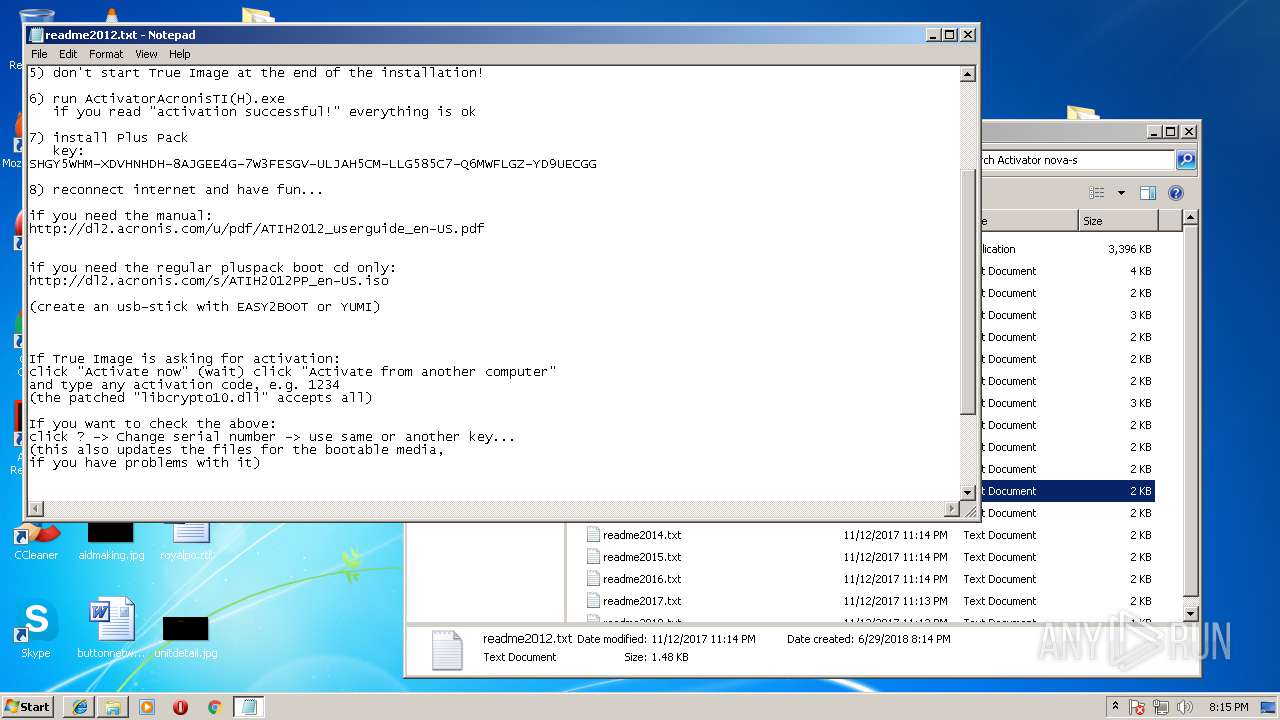
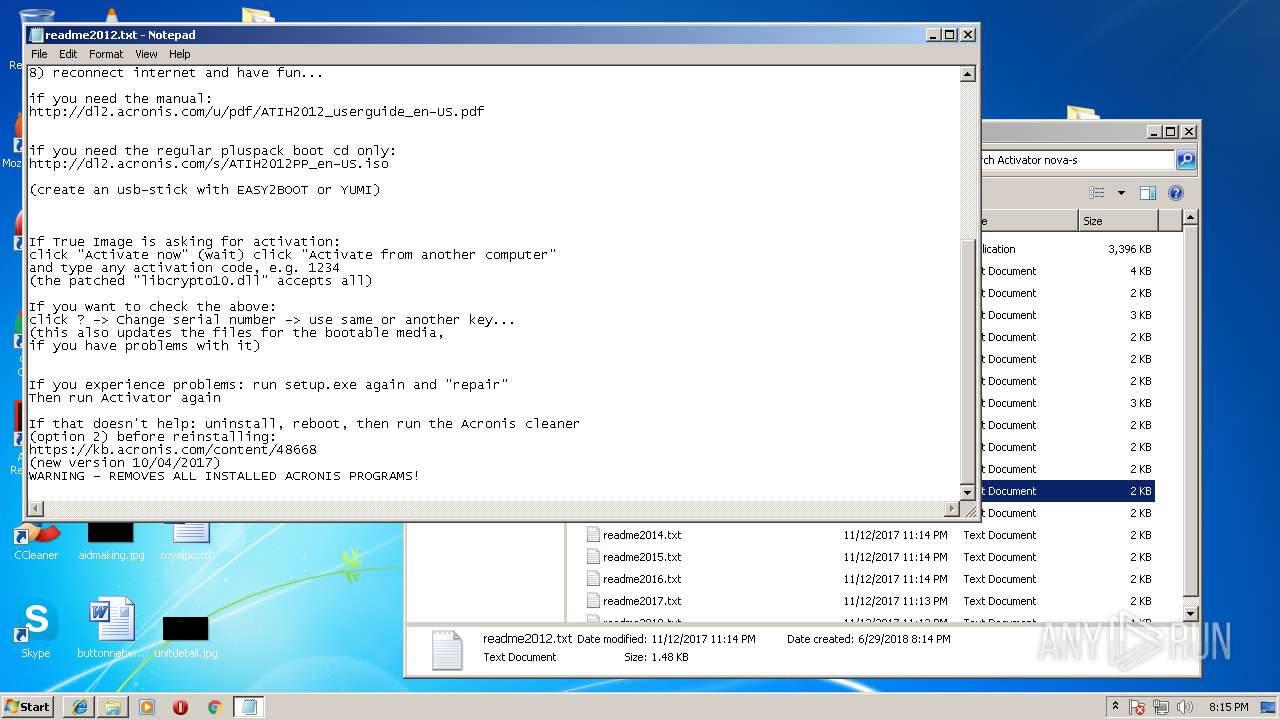
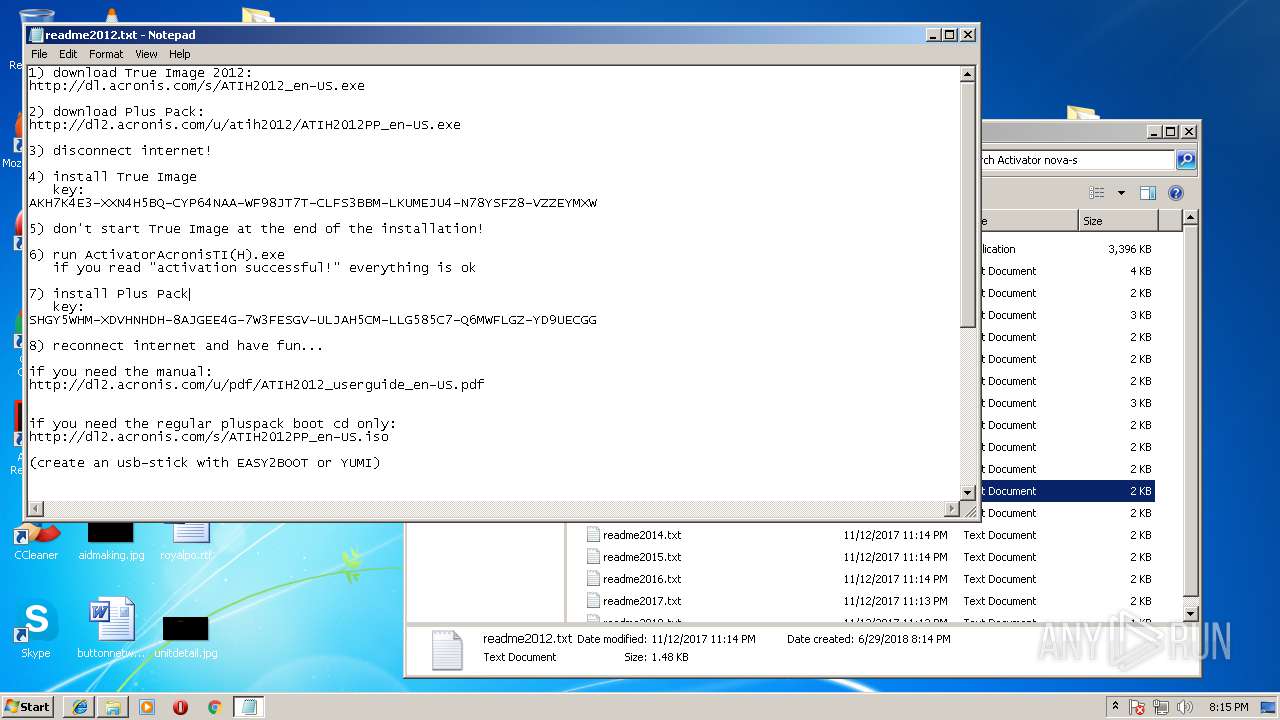
| 3188 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Activator nova-s\readme2012.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\Desktop\Activator nova-s\ActivationAcronisTI(H).exe" | C:\Users\admin\Desktop\Activator nova-s\ActivationAcronisTI(H).exe | — | explorer.exe | |||||||||||
User: admin Company: not by Acronis Integrity Level: MEDIUM Description: activates build 22.5.1.12510 and previous Exit code: 3221226540 Version: 1, 0, 0, 0 Modules
| |||||||||||||||
| 3444 | cmd /c ""C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Activation.cmd" " | C:\Windows\system32\cmd.exe | — | ActivationAcronisTI(H).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
764
Read events
698
Write events
66
Delete events
0
Modification events
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderShortcuts |
Value: | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FolderHistory |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C00410063007400690076006100740069006F006E004100540049002800480029002E007A00690070005C000000 | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath0 |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc0 |
Value: 0 | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | PanelPath1 |
Value: | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | FlatViewArc1 |
Value: 0 | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | ListMode |
Value: 771 | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Position |
Value: 1600000016000000D60300000B02000000000000 | |||
| (PID) Process: | (2188) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\7-Zip\FM |
| Operation: | write | Name: | Panels |
Value: 0100000000000000DA010000 | |||
| (PID) Process: | (4016) ActivationAcronisTI(H).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
47
Suspicious files
16
Text files
125
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
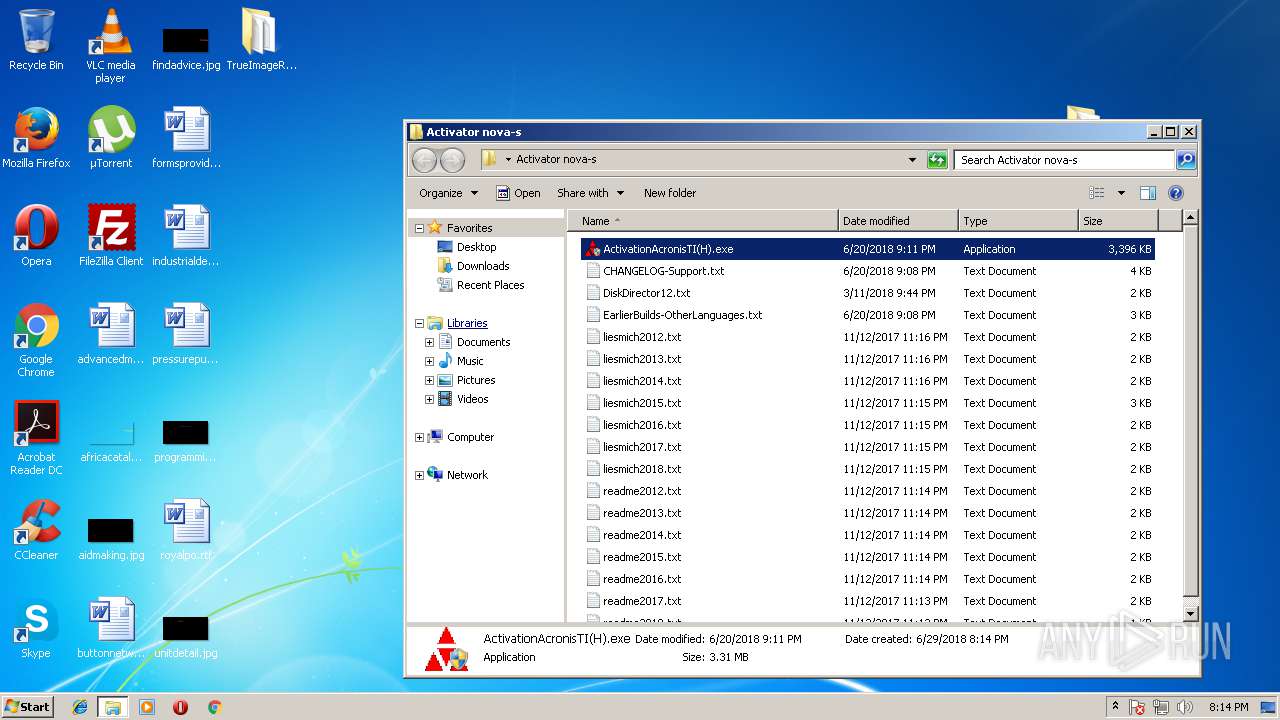
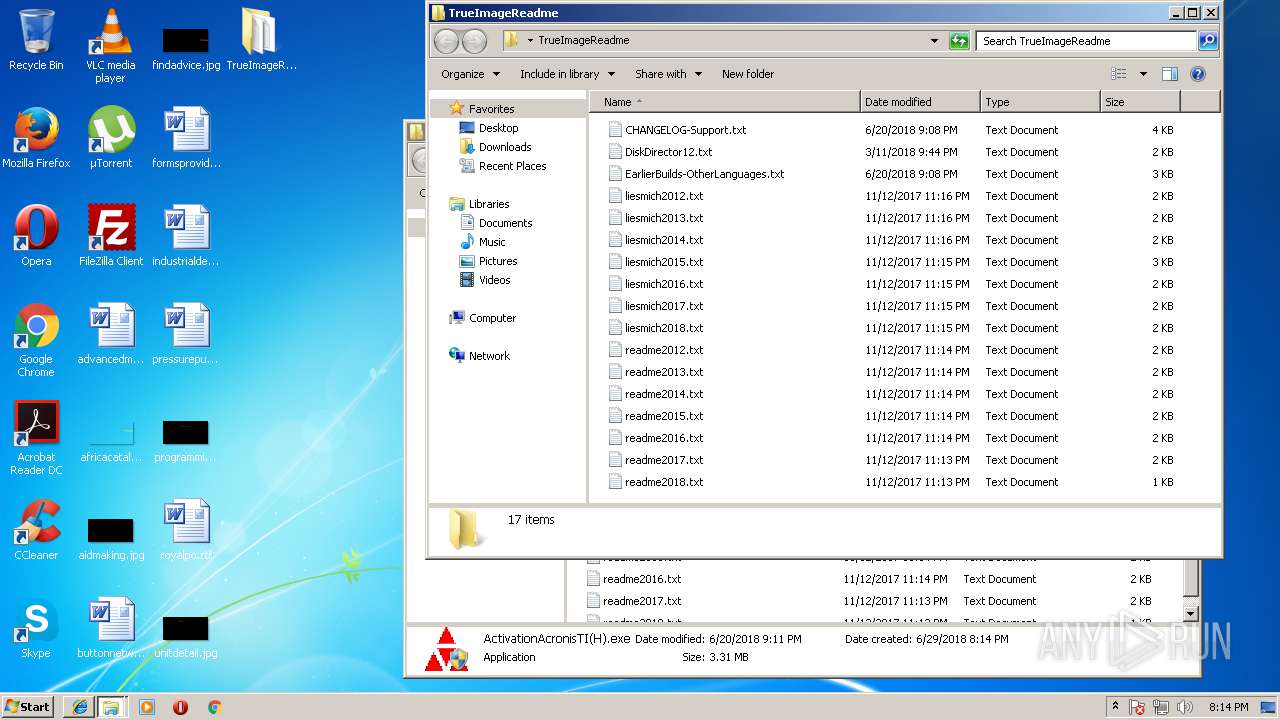
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\ActivationAcronisTI(H).exe | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\CHANGELOG-Support.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\DiskDirector12.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\EarlierBuilds-OtherLanguages.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2012.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2013.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2014.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2015.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2016.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zEC888C58A\Activator nova-s\liesmich2017.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3856 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3856 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
688 | iexplore.exe | 192.229.220.52:80 | dl.acronis.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.acronis.com |
| whitelisted |
www.bing.com |
| whitelisted |
dns.msftncsi.com |
| shared |