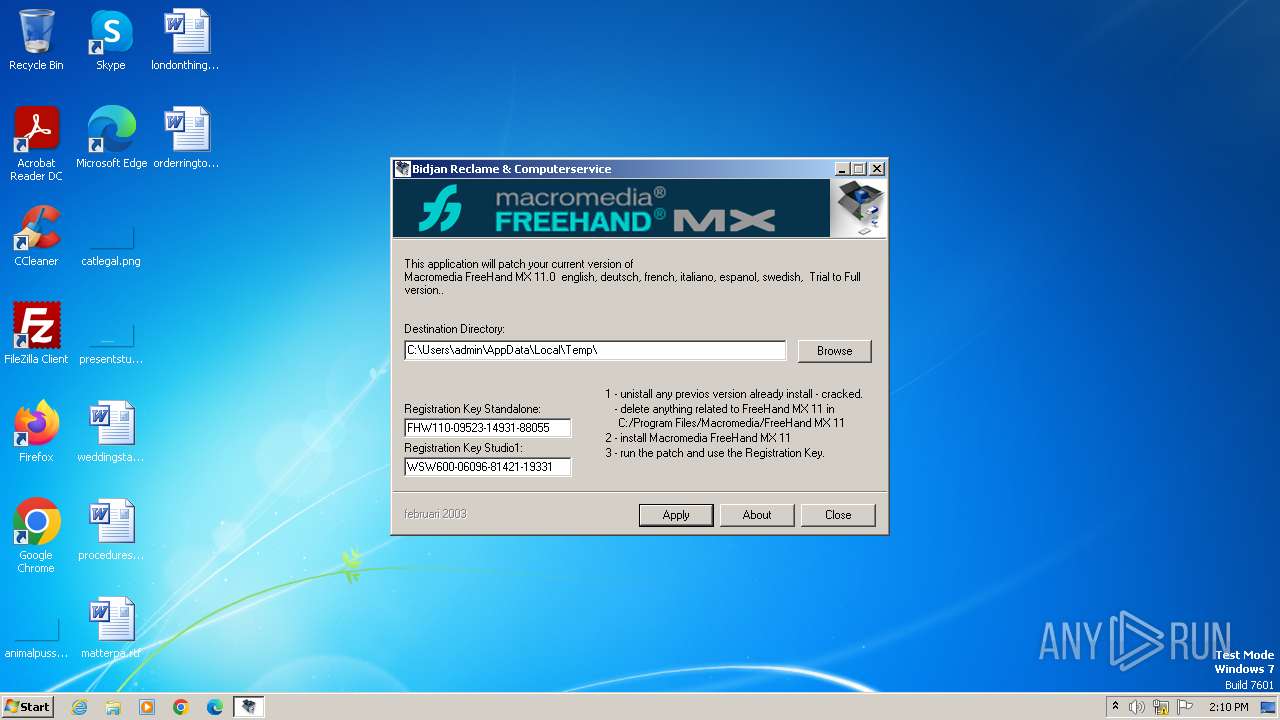
| File name: | Patch.exe |
| Full analysis: | https://app.any.run/tasks/cb2c4ab0-7bde-4fd9-bccd-134ea07e998b |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2023, 14:10:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | DF353E69EBAEA9D37F639C28B276C588 |
| SHA1: | 0CB71C2CD09BDBEB78A191353E163235FBEB8A52 |
| SHA256: | B9B010DA5A38391D76364953C819C67A477FF63A57C1FD2DC8AD6D0E1B9A1DC9 |
| SSDEEP: | 98304:4rqS1iB2SP7xH/kKGbDVIlE+SpVTw3WK5+pMyRYziu+41MK7z5xNuFDhK1jJgI3b:6w3Aj2 |
MALICIOUS
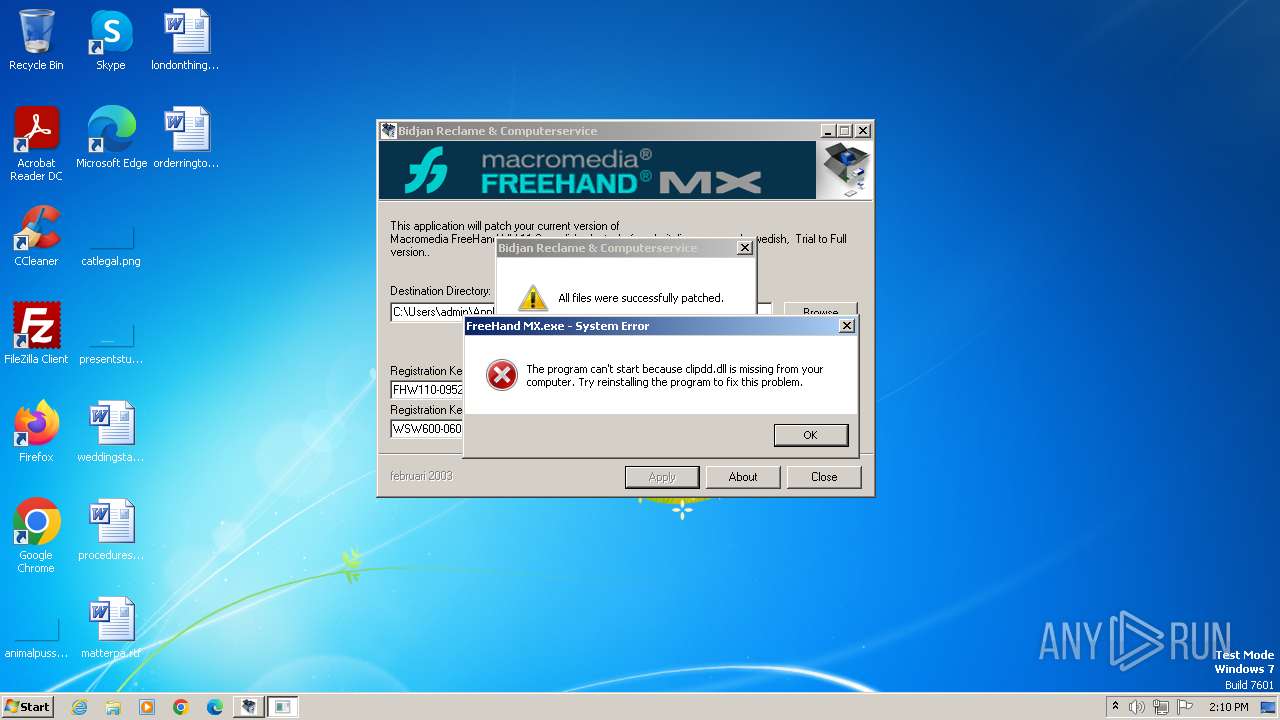
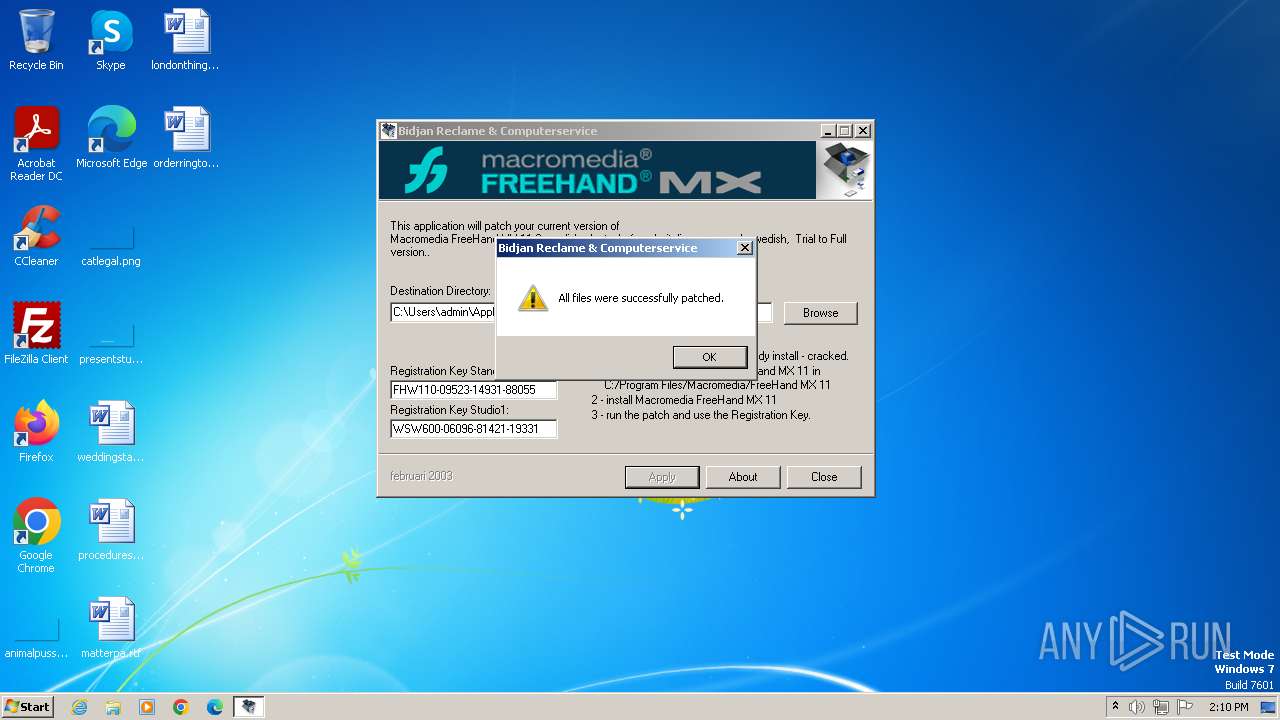
Drops the executable file immediately after the start
- Patch.exe (PID: 3496)
SUSPICIOUS
Reads the Internet Settings
- Patch.exe (PID: 3496)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 3500)
- Patch.exe (PID: 3496)
- wmpnscfg.exe (PID: 3660)
Manual execution by a user
- wmpnscfg.exe (PID: 3500)
- wmpnscfg.exe (PID: 3660)
Reads the computer name
- wmpnscfg.exe (PID: 3500)
- Patch.exe (PID: 3496)
- wmpnscfg.exe (PID: 3660)
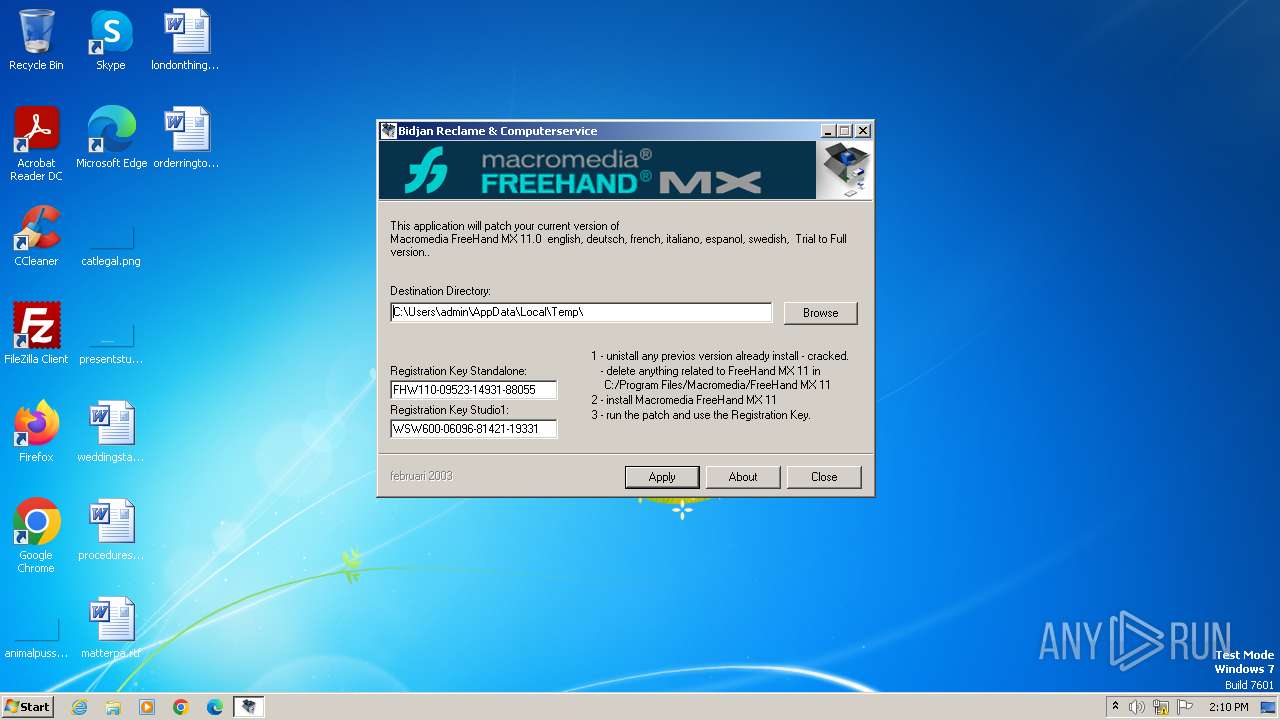
Create files in a temporary directory
- Patch.exe (PID: 3496)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3500)
- wmpnscfg.exe (PID: 3660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:05:25 17:28:52+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 5.1 |
| CodeSize: | 57344 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 163840 |
| EntryPoint: | 0x36250 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.2.0.0 |
| ProductVersionNumber: | 0.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | |
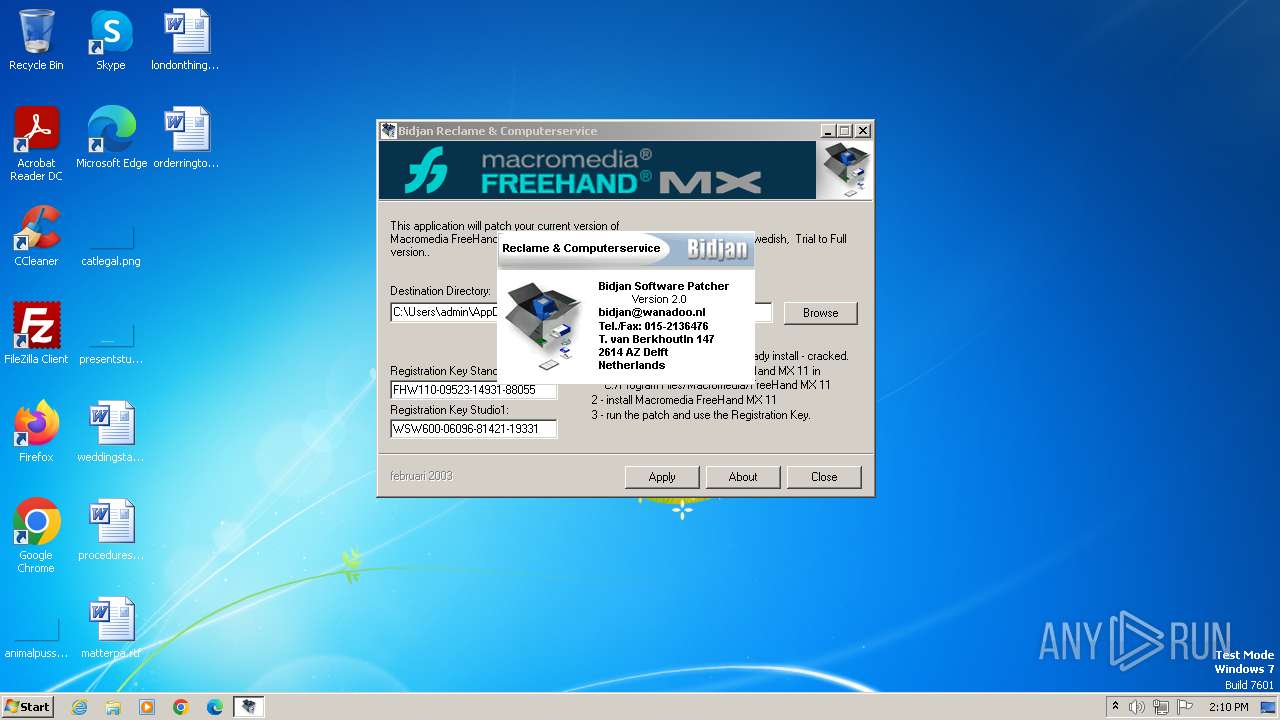
| CompanyName: | Bidjan Reclame & Computerservice |
| FileDescription: | Bidjan reclame & Computerservice |
| FileVersion: | 2 |
| InternalName: | PATCH |
| LegalCopyright: | © 2002 Bidjan Reclame & Computerservice |
| LegalTrademarks: | Bidjan Reclame & Computerservice |
| OriginalFileName: | PATCH.EXE |
| ProductName: | Patch Application |
| ProductVersion: | 2 |
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3440 | "C:\Users\admin\AppData\Local\Temp\Patch.exe" | C:\Users\admin\AppData\Local\Temp\Patch.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3488 | "C:\Users\admin\AppData\Local\Temp\FreeHand MX.exe" | C:\Users\admin\AppData\Local\Temp\FreeHand MX.exe | — | Patch.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225781 Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\Patch.exe" | C:\Users\admin\AppData\Local\Temp\Patch.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3500 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
781
Read events
767
Write events
8
Delete events
6
Modification events
| (PID) Process: | (3500) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{D3F2CF7B-DD53-46F9-A60E-E0F1FFA013F9}\{2AC32636-B2FA-463B-B16C-03DE1BDD48D2} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3500) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{D3F2CF7B-DD53-46F9-A60E-E0F1FFA013F9} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3500) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{5E4E2DE8-0D7B-4406-BA9E-62A1C2EF7032} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3496) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3496) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3496) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3496) Patch.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3660) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{02E9C5FC-8EDB-47A4-ADEA-3A883C0EB872}\{1EECF61B-0603-4D40-9F31-09AFCDBCAC95} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3660) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{02E9C5FC-8EDB-47A4-ADEA-3A883C0EB872} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3660) wmpnscfg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\MediaPlayer\Health\{77A2CE13-EFDA-4B87-9046-A4E819826BB8} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3496 | Patch.exe | C:\Users\admin\AppData\Local\Temp\FSDATA.DA1 | compressed | |
MD5:3B5677F06D12515C6744383C1B8569F3 | SHA256:F04021D2E652DA46E3FFECEBCD0C26CC682997AD76A792AC15C7CB4031C60BD8 | |||
| 3496 | Patch.exe | C:\Users\admin\AppData\Local\Temp\FS17CD.tmp | executable | |
MD5:04A08EAFD6F7D41D7389A23E3F952F1B | SHA256:20D967B261EB3548DED774D205A84A47E9A41DD09EE5A2A221147095FBFB7EA9 | |||
| 3496 | Patch.exe | C:\Users\admin\AppData\Local\Temp\FS187A.tmp | text | |
MD5:F027DBD22BFF24924D85094CDDFAD5FC | SHA256:4A318CE9DD7D1523C06763660B97EF1D1942F1E61C35A02E48CF49002AA4A3C0 | |||
| 3496 | Patch.exe | C:\Users\admin\AppData\Local\Temp\FreeHand MX.exe | executable | |
MD5:04A08EAFD6F7D41D7389A23E3F952F1B | SHA256:20D967B261EB3548DED774D205A84A47E9A41DD09EE5A2A221147095FBFB7EA9 | |||
| 3496 | Patch.exe | C:\Users\admin\AppData\Local\Temp\FSPATCH.DAT | binary | |
MD5:0B4FB8BA571F1BA77FC0D7E8A18DDE13 | SHA256:7716DEE10DC34CA96684D28E4989BE1E218C0F343B2066EDE56912EC4087B473 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 95.101.148.135:80 | — | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 23.35.228.137:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |