| File name: | AnyDesk.exe |
| Full analysis: | https://app.any.run/tasks/f1a7257c-dbc0-4000-8a41-e8cef22b2eb2 |
| Verdict: | Suspicious activity |
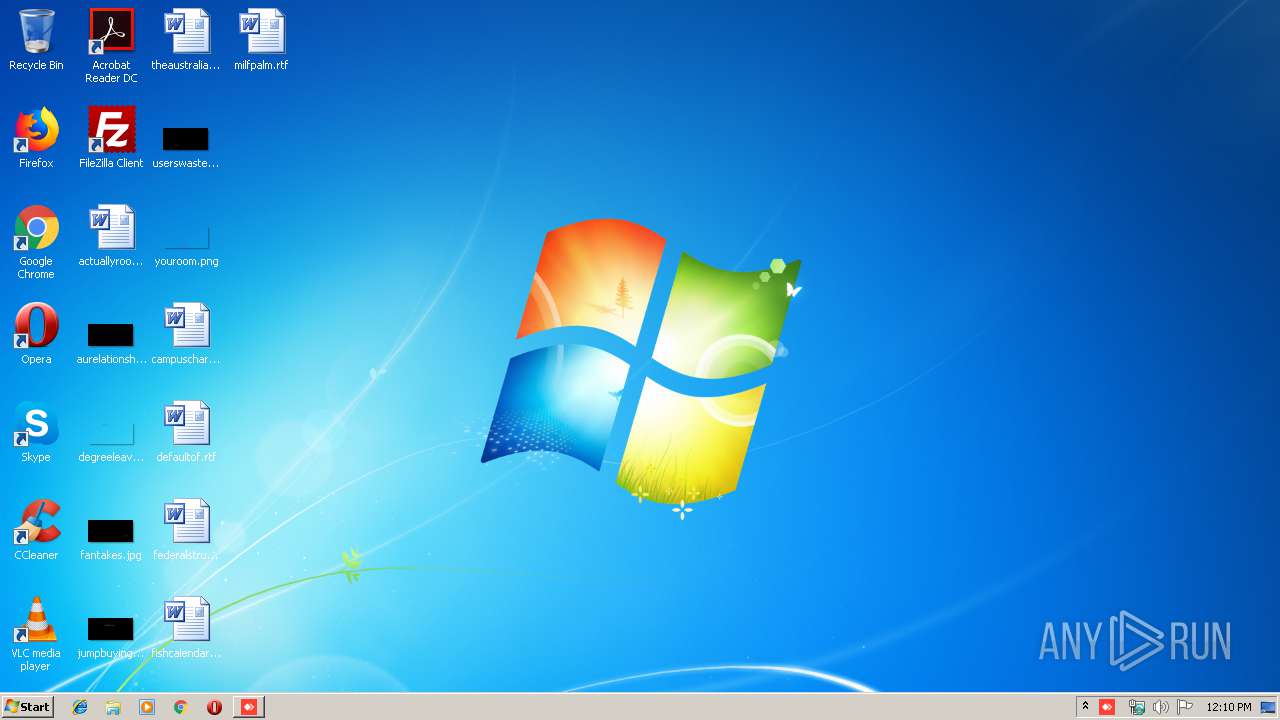
| Analysis date: | January 09, 2020, 12:10:22 |
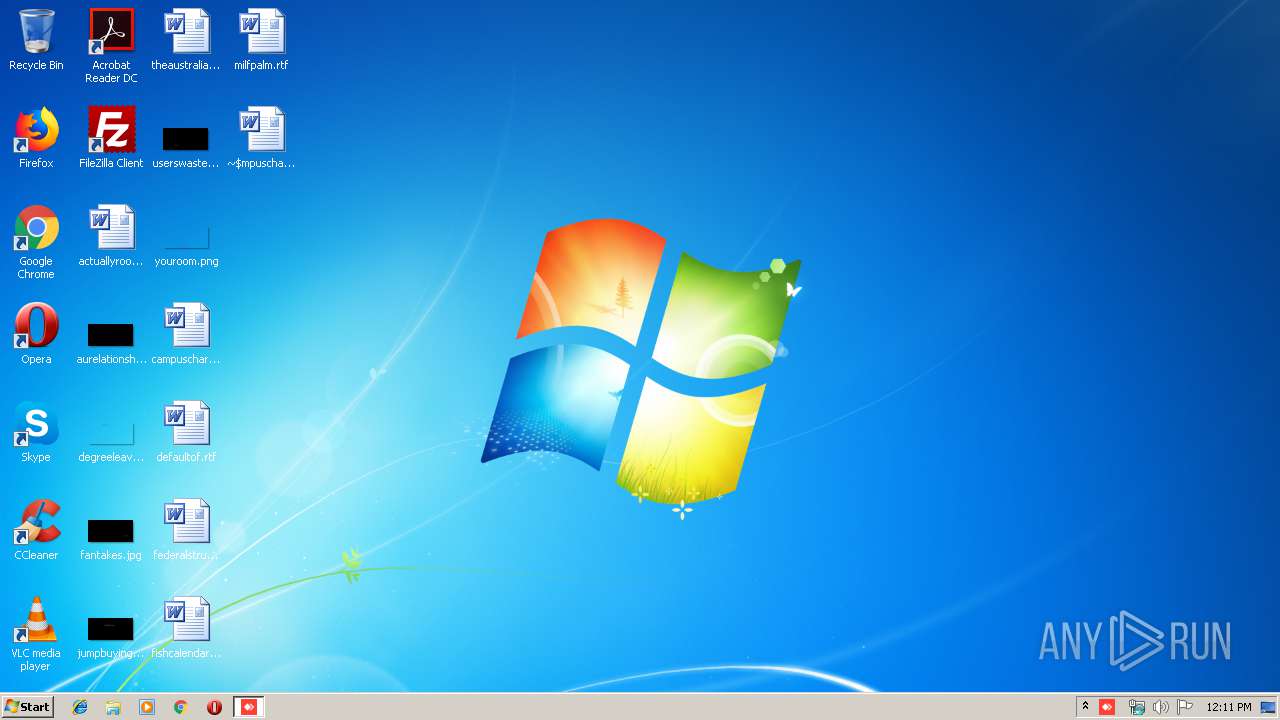
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EB80F7BDDB699784BAA9FBF2941EAF4A |
| SHA1: | DF6ABBFD20E731689F3C7D2A55F45AC83FBBC40B |
| SHA256: | B9AD79EAF7A4133F95F24C3B9D976C72F34264DC5C99030F0E57992CB5621F78 |
| SSDEEP: | 98304:6aJXyQTrRGlSMoIuORmKBQielvZlpkiSti:3olMcR9BTY3WS |
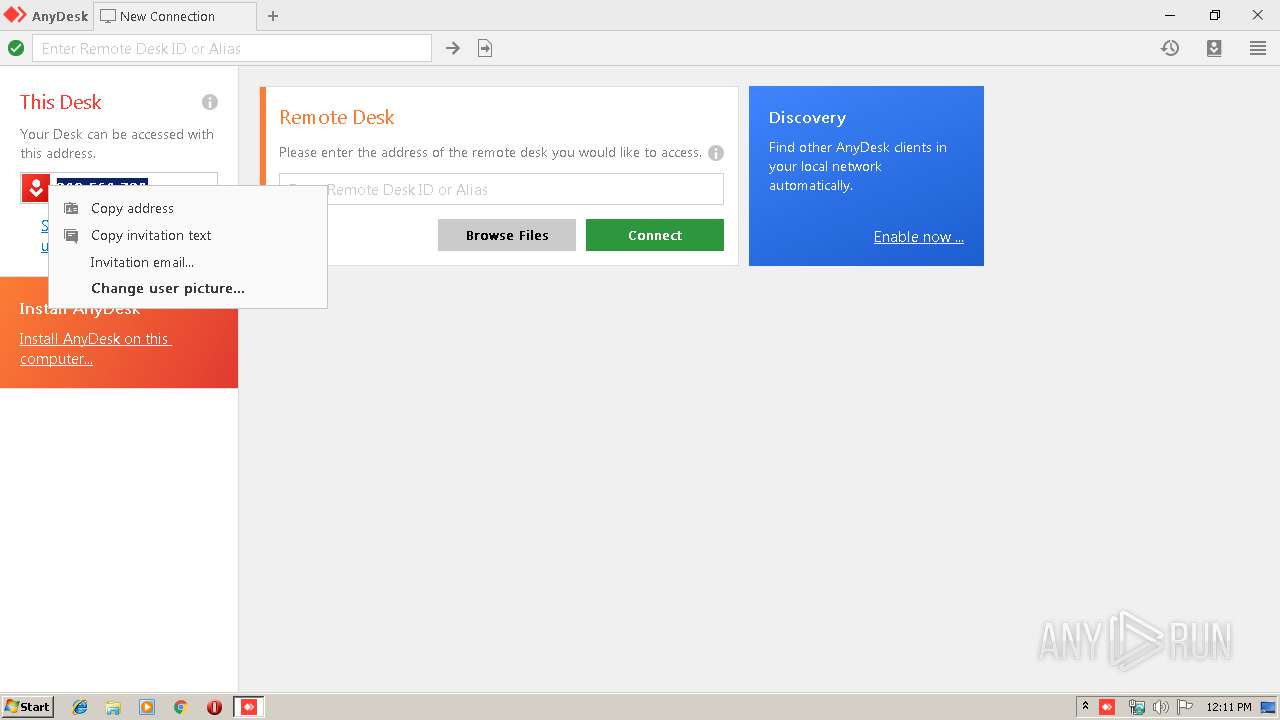
MALICIOUS
Loads dropped or rewritten executable
- AnyDesk.exe (PID: 2524)
- AnyDesk.exe (PID: 2408)
SUSPICIOUS
Creates files in the user directory
- AnyDesk.exe (PID: 940)
- AnyDesk.exe (PID: 2408)
Executable content was dropped or overwritten
- AnyDesk.exe (PID: 2408)
Application launched itself
- AnyDesk.exe (PID: 940)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2868)
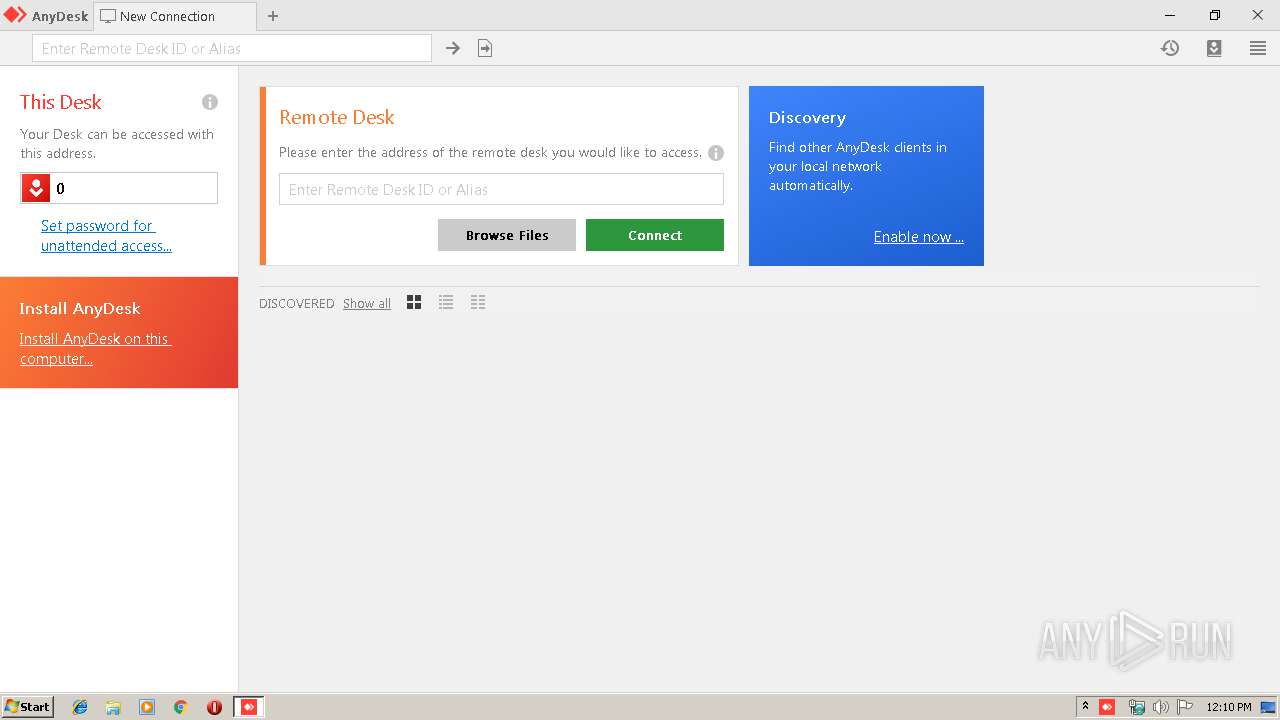
Manual execution by user
- WINWORD.EXE (PID: 2868)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:17 19:54:45+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 10752 |
| InitializedDataSize: | 3128832 |
| UninitializedDataSize: | 9496576 |
| EntryPoint: | 0x1ce9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.4.2.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Unknown (0) |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.4.2.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.4 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Dec-2019 18:54:45 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | philandro Software GmbH |
| FileDescription: | AnyDesk |
| FileVersion: | 5.4.2.0 |
| ProductName: | AnyDesk |
| ProductVersion: | 5.4 |
| LegalCopyright: | (C) 2019 philandro Software GmbH |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Dec-2019 18:54:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002835 | 0x00002A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5055 |
.itext | 0x00004000 | 0x0090E800 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00913000 | 0x000002FE | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66942 |
.data | 0x00914000 | 0x002F8084 | 0x002F7E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99994 |
.rsrc | 0x00C0D000 | 0x00003290 | 0x00003400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.68468 |
.reloc | 0x00C11000 | 0x00000300 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.18127 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.39339 | 1543 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.29968 | 1640 | UNKNOWN | English - United States | RT_ICON |
3 | 3.6735 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 2.73746 | 488 | UNKNOWN | English - United States | RT_ICON |
5 | 3.69265 | 296 | UNKNOWN | English - United States | RT_ICON |
1000 | 2.78538 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
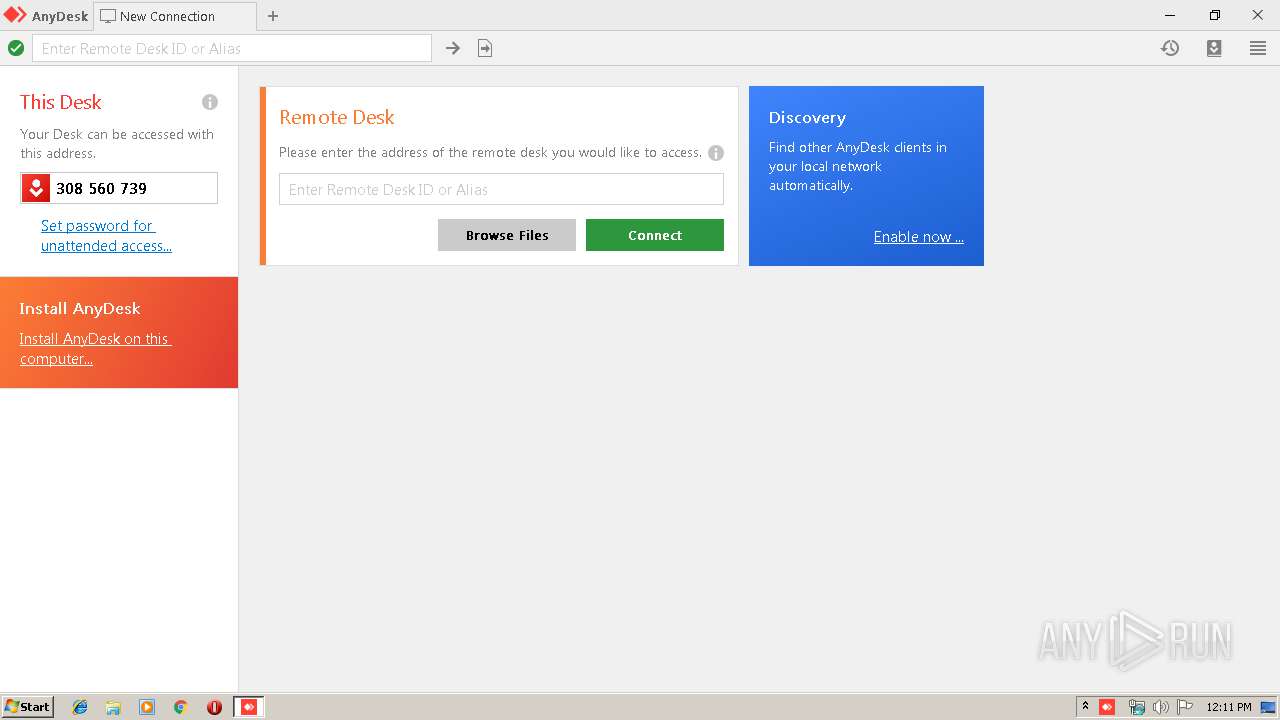
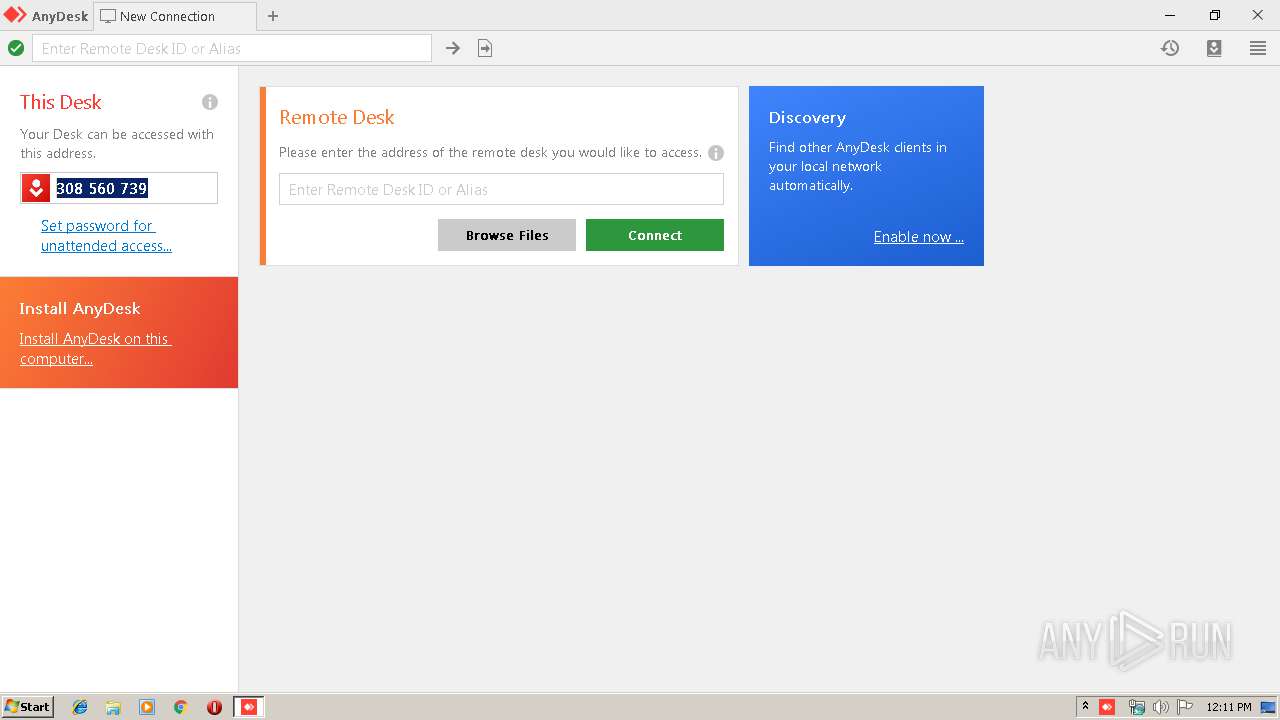
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 940 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | — | explorer.exe | |||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 5.4.2.0 Modules
| |||||||||||||||
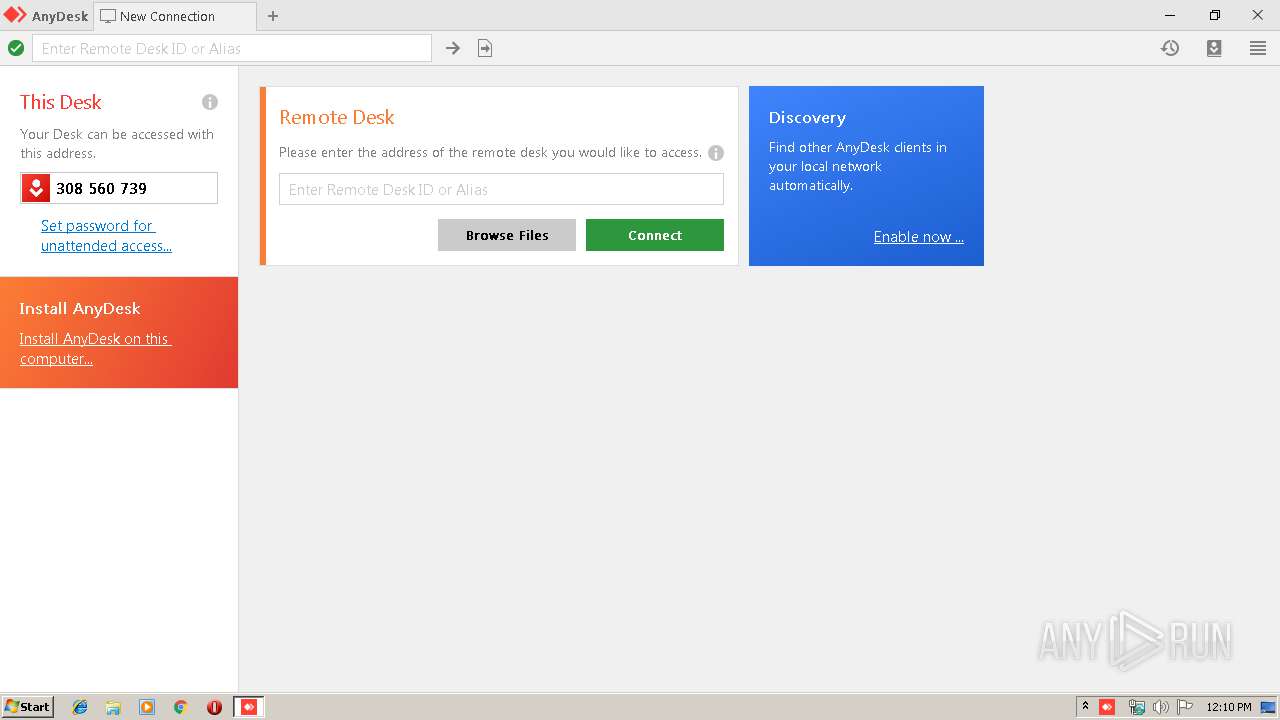
| 2408 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" --local-service | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | AnyDesk.exe | ||||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 5.4.2.0 Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Local\Temp\AnyDesk.exe" --local-control | C:\Users\admin\AppData\Local\Temp\AnyDesk.exe | — | AnyDesk.exe | |||||||||||
User: admin Company: philandro Software GmbH Integrity Level: MEDIUM Description: AnyDesk Exit code: 0 Version: 5.4.2.0 Modules
| |||||||||||||||
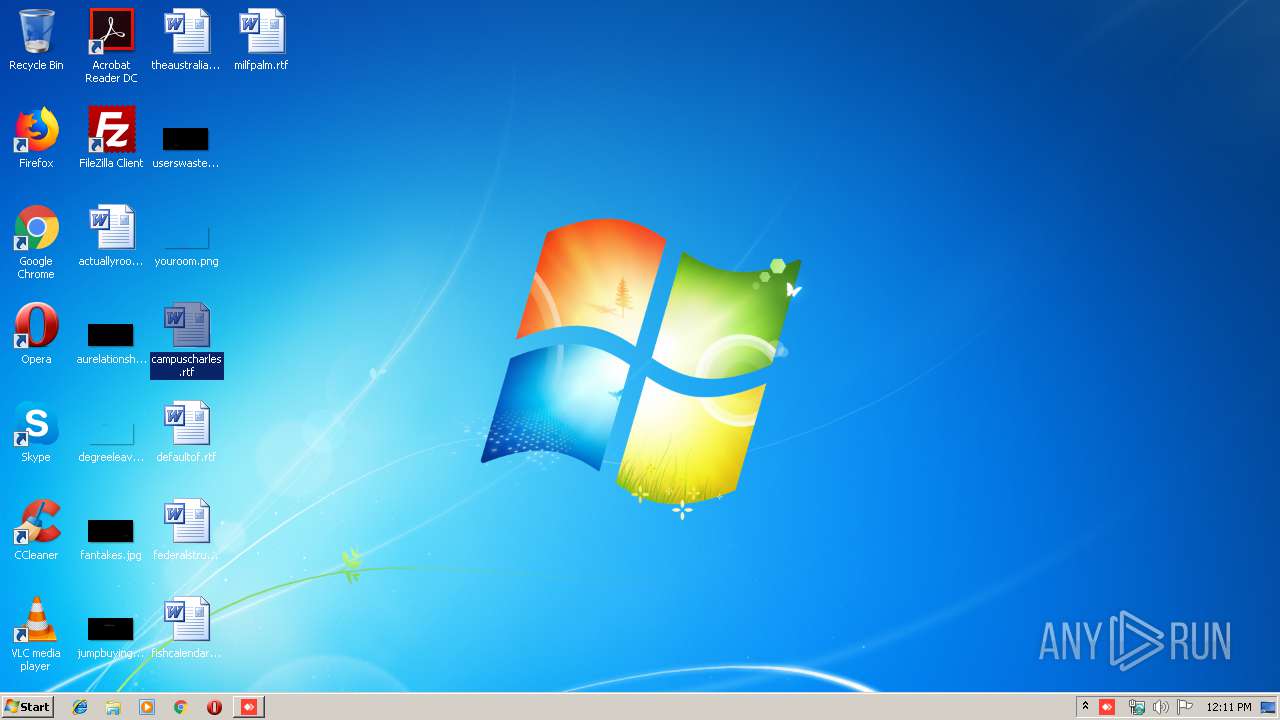
| 2868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\campuscharles.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 145
Read events
866
Write events
132
Delete events
147
Modification events
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | qqg |
Value: 71716700340B0000010000000000000000000000 | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1344864319 | |||
Executable files
1
Suspicious files
1
Text files
26
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 940 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U5NE5THAJ0O2G3QDL1V3.temp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDD1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5269613A-40E0-4ADD-A5CA-DEE7B524BD71}.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{EEEA7242-1AC2-4EB5-8E2E-1EDF750341E6}.tmp | — | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{EE54EA65-20DB-42BA-BA88-84AE958BC0F8}.tmp | — | |
MD5:— | SHA256:— | |||
| 2408 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\service.conf | text | |
MD5:— | SHA256:— | |||
| 2868 | WINWORD.EXE | C:\Users\admin\Desktop\~$mpuscharles.rtf | pgc | |
MD5:— | SHA256:— | |||
| 940 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\75fdacd8330bac18.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2408 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\system.conf | text | |
MD5:— | SHA256:— | |||
| 940 | AnyDesk.exe | C:\Users\admin\AppData\Roaming\AnyDesk\user.conf | text | |
MD5:5059D0251F3292C45A54E0AB40CCA733 | SHA256:88D22B3A6A8BCB3AB03CFAC5EEF7FDF1CF4C99E17576D05997D2F0DFC96B8189 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
4
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2408 | AnyDesk.exe | POST | 200 | 52.33.64.96:80 | http://api.playanext.com/httpapi | US | text | 7 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
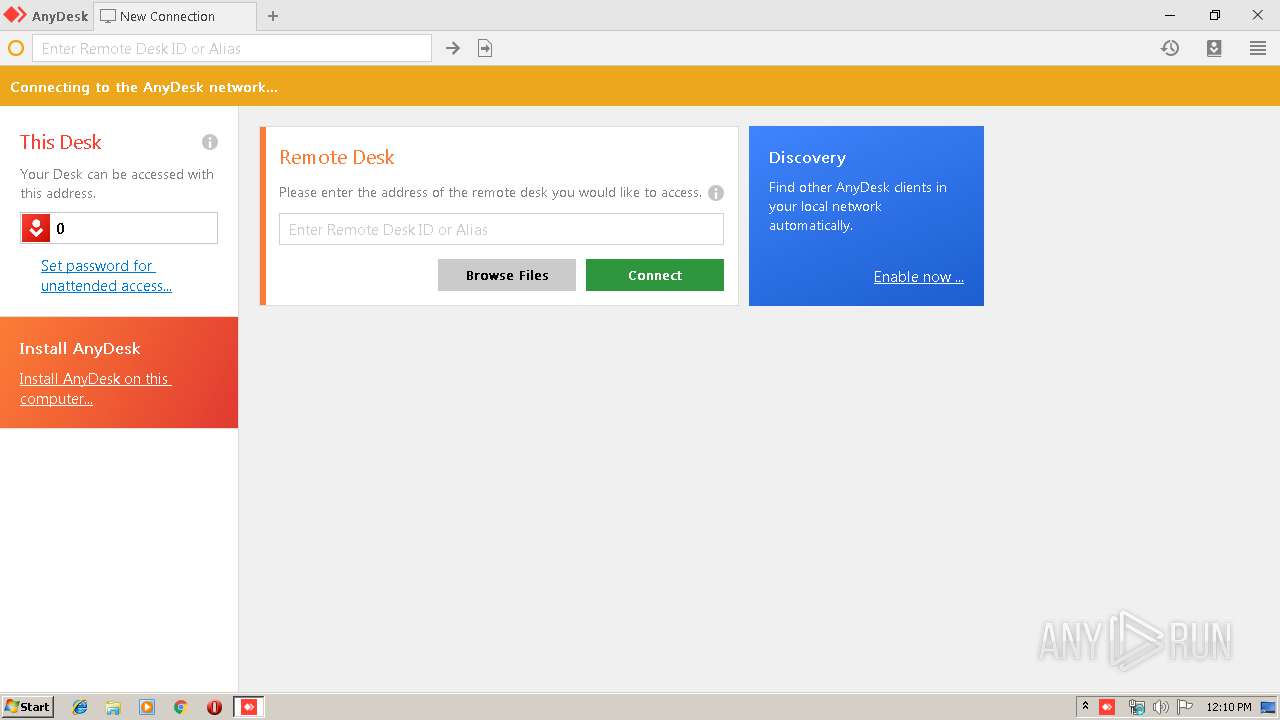
2408 | AnyDesk.exe | 92.42.110.45:80 | boot-01.net.anydesk.com | velia.net Internetdienste GmbH | DE | suspicious |
2408 | AnyDesk.exe | 92.42.110.45:443 | boot-01.net.anydesk.com | velia.net Internetdienste GmbH | DE | suspicious |
2408 | AnyDesk.exe | 134.119.220.101:80 | relay-b340c7f0.net.anydesk.com | velia.net Internetdienste GmbH | FR | unknown |
2408 | AnyDesk.exe | 52.33.64.96:80 | api.playanext.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
boot-01.net.anydesk.com |
| whitelisted |
relay-b340c7f0.net.anydesk.com |
| unknown |
api.playanext.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2408 | AnyDesk.exe | Potential Corporate Privacy Violation | ET POLICY SSL/TLS Certificate Observed (AnyDesk Remote Desktop Software) |