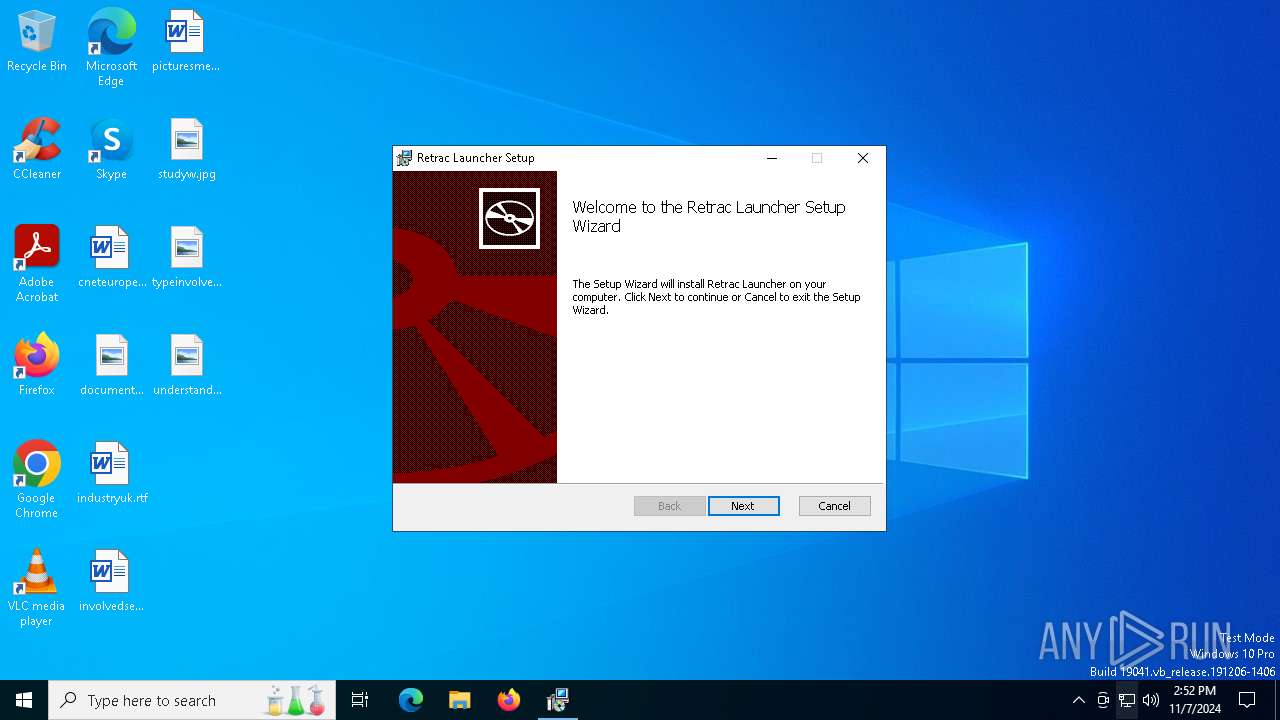
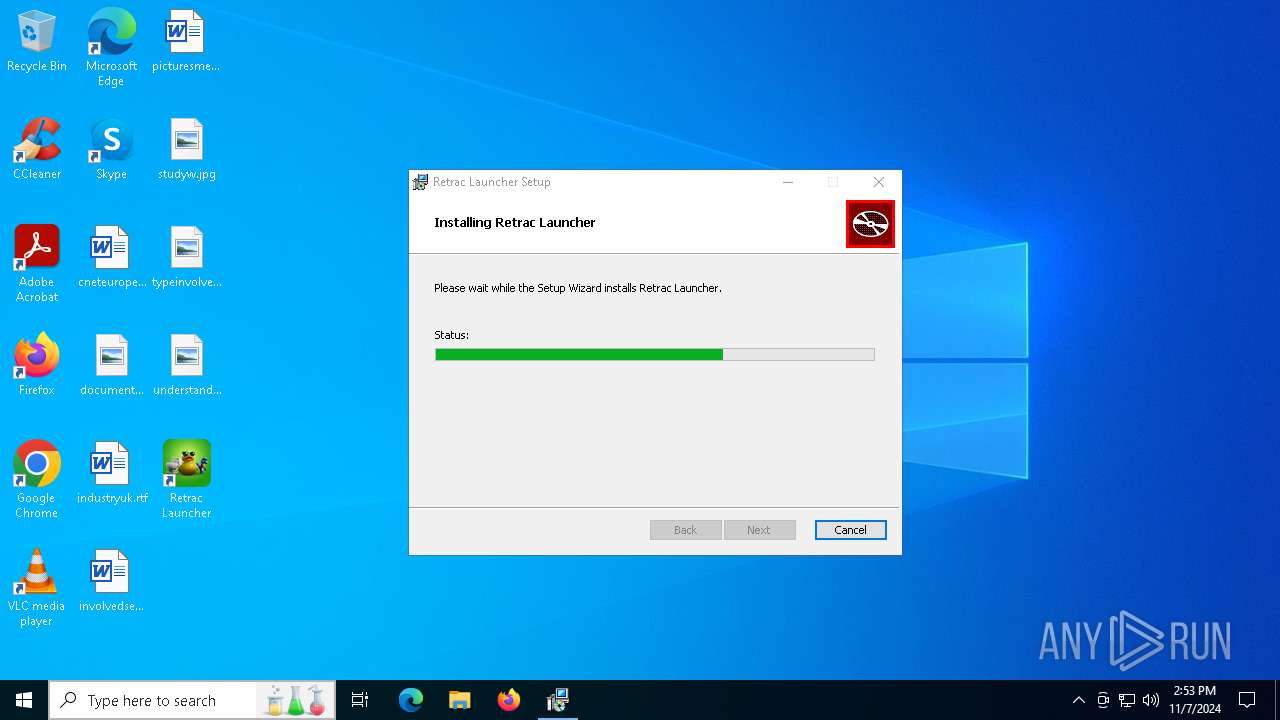
| File name: | Retrac.Launcher_1.0.14_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/a97a2364-e13a-46b9-927e-3c92aad01d83 |
| Verdict: | Malicious activity |
| Analysis date: | November 07, 2024, 14:52:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Retrac Launcher, Author: retrac, Keywords: Installer, Comments: This installer database contains the logic and data required to install Retrac Launcher., Template: x64;0, Revision Number: {4A802B18-EF7D-4D6B-8664-BD8D987F774F}, Create Time/Date: Wed Oct 30 04:22:38 2024, Last Saved Time/Date: Wed Oct 30 04:22:38 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | AE30168AA8F32E9A4F00DF855A303509 |
| SHA1: | 287B7FBA5FF1BA3F5261B8A842DA3F6B23E61E02 |
| SHA256: | B99BB0941D2258332591632921C5FD9A35BCC2487E69CF2B7A92579965DAFC2C |
| SSDEEP: | 98304:o5FfHMRFehzgMm7PL6yQID7qvRHxS7BH32oXLzbMYCnK2iAdW2VJ9uxK2+jgkYRB:hLN3I6w02eaH |
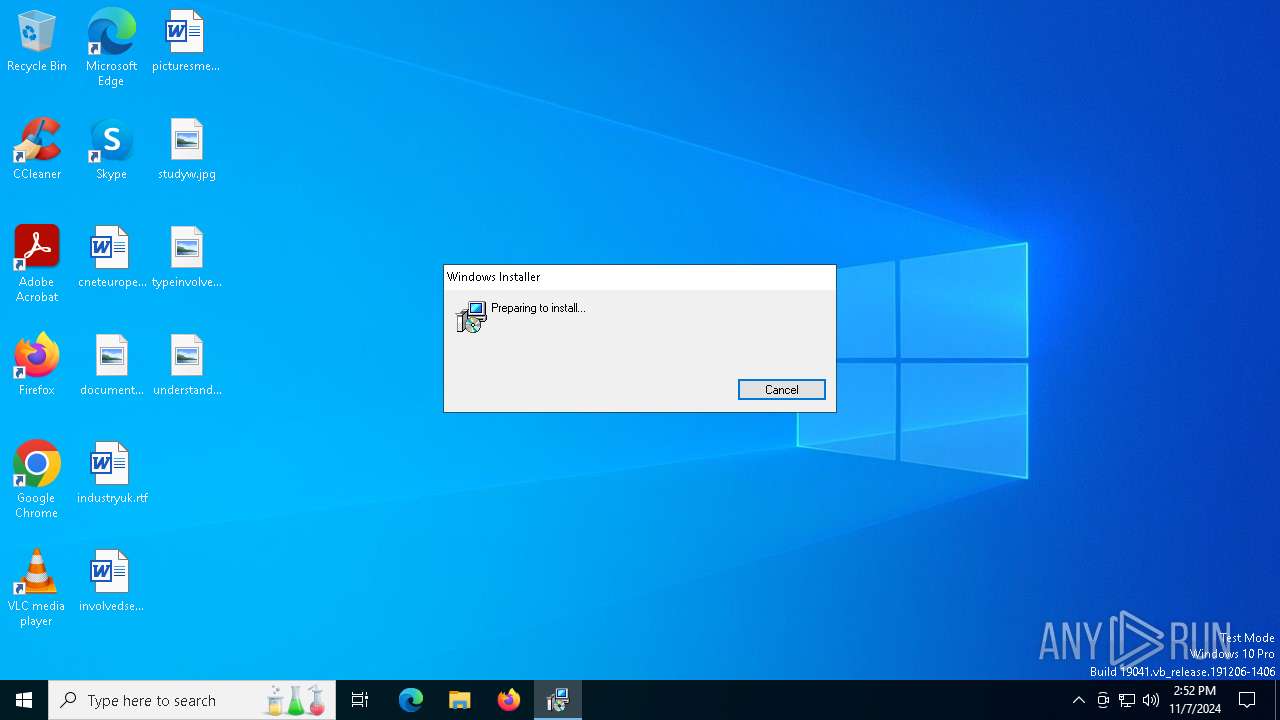
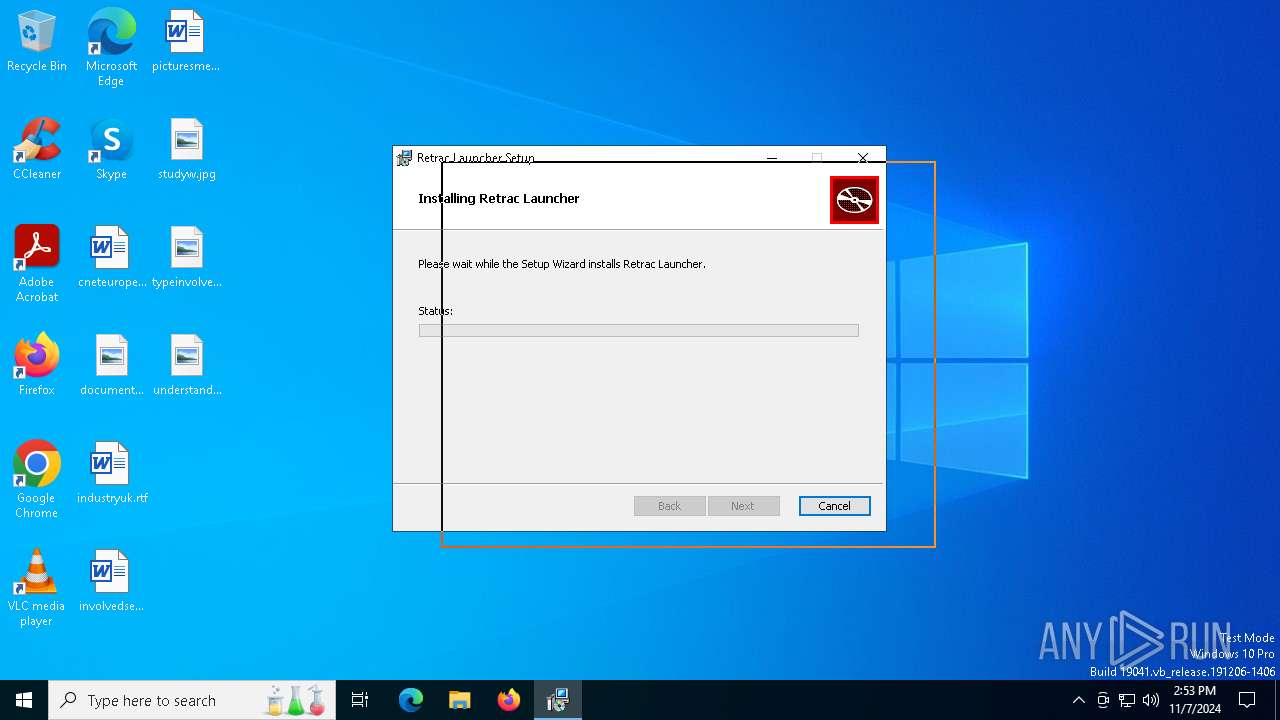
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7640)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 7768)
Executes as Windows Service
- VSSVC.exe (PID: 8124)
Downloads file from URI via Powershell
- powershell.exe (PID: 7640)
Manipulates environment variables
- powershell.exe (PID: 7640)
Starts process via Powershell
- powershell.exe (PID: 7640)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 7768)
Executable content was dropped or overwritten
- powershell.exe (PID: 7640)
- MicrosoftEdgeWebview2Setup.exe (PID: 7616)
- MicrosoftEdgeUpdate.exe (PID: 6832)
Process drops legitimate windows executable
- powershell.exe (PID: 7640)
- MicrosoftEdgeWebview2Setup.exe (PID: 7616)
- MicrosoftEdgeUpdate.exe (PID: 6832)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 7616)
- MicrosoftEdgeUpdate.exe (PID: 6832)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 6832)
INFO
Reads the computer name
- msiexec.exe (PID: 7768)
An automatically generated document
- msiexec.exe (PID: 7712)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7712)
- msiexec.exe (PID: 7768)
Manages system restore points
- SrTasks.exe (PID: 7252)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 7616)
Checks supported languages
- msiexec.exe (PID: 7768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Retrac Launcher |
| Author: | retrac |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Retrac Launcher. |
| Template: | x64;0 |
| RevisionNumber: | {4A802B18-EF7D-4D6B-8664-BD8D987F774F} |
| CreateDate: | 2024:10:30 04:22:38 |
| ModifyDate: | 2024:10:30 04:22:38 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
141
Monitored processes
17
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 6660 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.31\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.31\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.31 | ||||
| 6832 | C:\Users\admin\AppData\Local\Temp\EUBE14.tmp\MicrosoftEdgeUpdate.exe /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Users\admin\AppData\Local\Temp\EUBE14.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.31 | ||||
| 7004 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{3ADCC149-350C-4806-983D-7EEC0E368A02}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.31 | ||||
| 7140 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" -Embedding | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.31 | ||||
| 7244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 7252 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 7280 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.31\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.31\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.31 | ||||
| 7284 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.31 | ||||
| 7616 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.31 | ||||
| 7640 | powershell.exe -NoProfile -windowstyle hidden try { [Net.ServicePointManager]::SecurityProtocol = [Net.SecurityProtocolType]::Tls12 } catch {}; Invoke-WebRequest -Uri "https://go.microsoft.com/fwlink/p/?LinkId=2124703" -OutFile "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" ; Start-Process -FilePath "$env:TEMP\MicrosoftEdgeWebview2Setup.exe" -ArgumentList ('/silent', '/install') -Wait | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
1 373
Read events
1 339
Write events
25
Delete events
9
Modification events
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000008F1C7FBE2431DB01581E0000AC1F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000005D7886BE2431DB01581E0000AC1F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000006B1B2FBF2431DB01581E0000AC1F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000006B1B2FBF2431DB01581E0000AC1F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000A43636BF2431DB01581E0000AC1F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000DA1A3BBF2431DB01581E0000AC1F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000CFED13C02431DB01581E0000AC1F0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7768) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000002DD51BC02431DB01581E0000D0180000E80300000100000000000000000000002453E720992EB242BE32B35E46482E6C00000000000000000000000000000000 | |||
| (PID) Process: | (8124) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009E5338C02431DB01BC1F0000DC1F0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
204
Suspicious files
14
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7768 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7768 | msiexec.exe | C:\Windows\Installer\987f1.msi | — | |
MD5:— | SHA256:— | |||
| 7768 | msiexec.exe | C:\Windows\Installer\987f3.msi | — | |
MD5:— | SHA256:— | |||
| 7712 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIE5C.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 7768 | msiexec.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Retrac Launcher\~etrac Launcher.tmp | binary | |
MD5:88B6F87642333127AC4CDEB7BAC06FEE | SHA256:36E0126F69E9B2E56B30408382B8846C93CC5558AEF6C3968B6EA7AA10DEDAB3 | |||
| 7768 | msiexec.exe | C:\Windows\Temp\~DFD3272D013880C694.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 7768 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:1CE8979A565C496ACB2E223B2E07CB61 | SHA256:DB364FA4620CE16FDE609516B9208357D92354E8BB8D63D0A4827413EA5F6DB7 | |||
| 7768 | msiexec.exe | C:\Windows\Temp\~DFD66E376D906F9DBD.TMP | binary | |
MD5:F304BCA506B1963E4B2929F5E6304341 | SHA256:32B3B6BF07FAB55A5FA477410870DE894531F73EB7D914C5CDDFC11DA496C5EA | |||
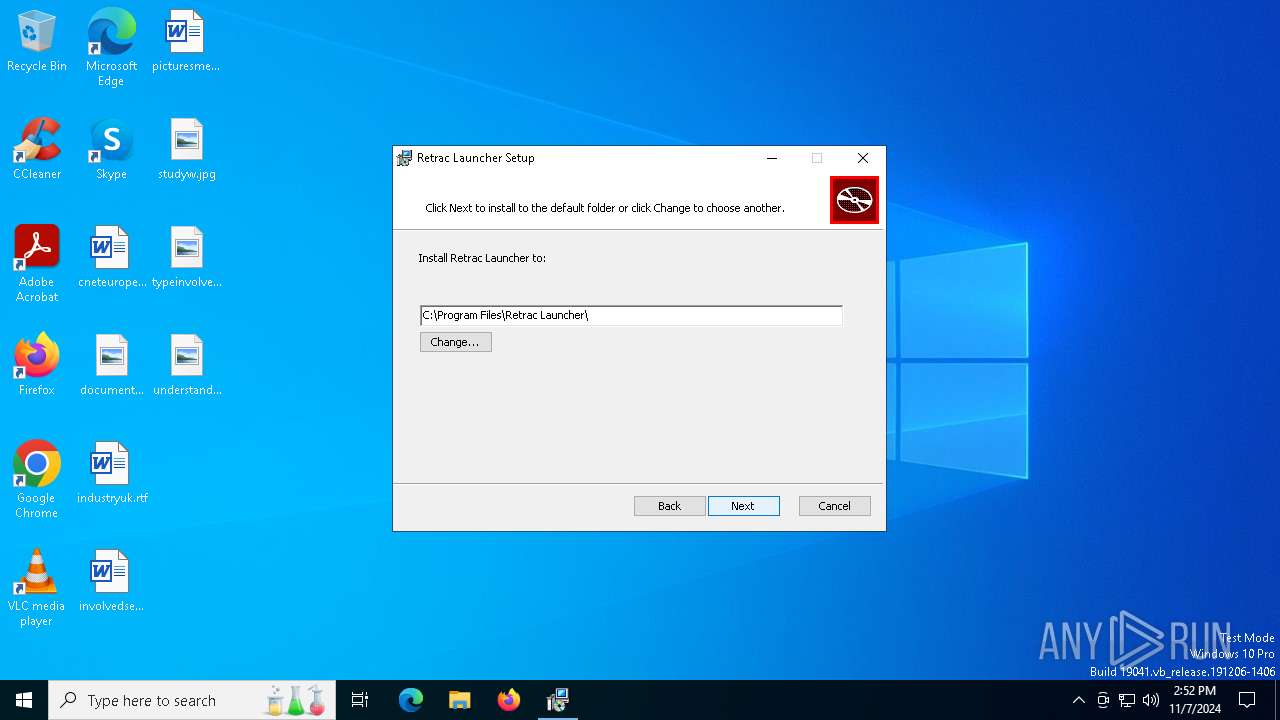
| 7768 | msiexec.exe | C:\Program Files\Retrac Launcher\Retrac Launcher.exe | executable | |
MD5:581DB83F7EC4B6D773ABBF1F5CE67B64 | SHA256:36657FD756A26C855923E601E239C855E36593C2A7FFCA04A7D9629CDC0C6CA3 | |||
| 7640 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hodyjcww.far.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
37
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4236 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 217.20.57.34:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/346ad9d1-746e-45c7-8fe0-d6c87a73a261?P1=1731596030&P2=404&P3=2&P4=CIRX2mwUwleyuikNzy7b%2bCkoucW8Ug18YVpr%2f6utrJHp6XdFd5zScMBFcilfH%2b1vpXGWbyqI4eUn5Ai%2bjdCA8Q%3d%3d | unknown | — | — | whitelisted |
— | — | GET | — | 217.20.57.34:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/346ad9d1-746e-45c7-8fe0-d6c87a73a261?P1=1731596030&P2=404&P3=2&P4=CIRX2mwUwleyuikNzy7b%2bCkoucW8Ug18YVpr%2f6utrJHp6XdFd5zScMBFcilfH%2b1vpXGWbyqI4eUn5Ai%2bjdCA8Q%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.48.23.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1744 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 104.126.37.154:443 | th.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |