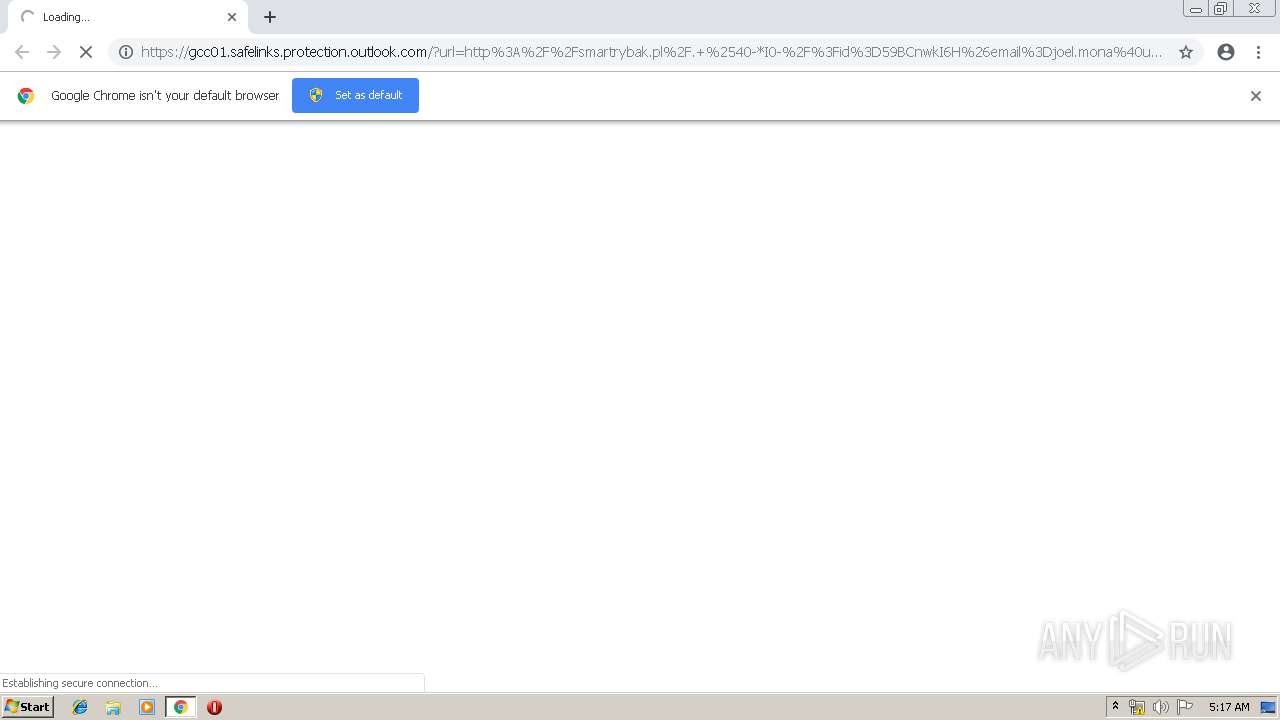
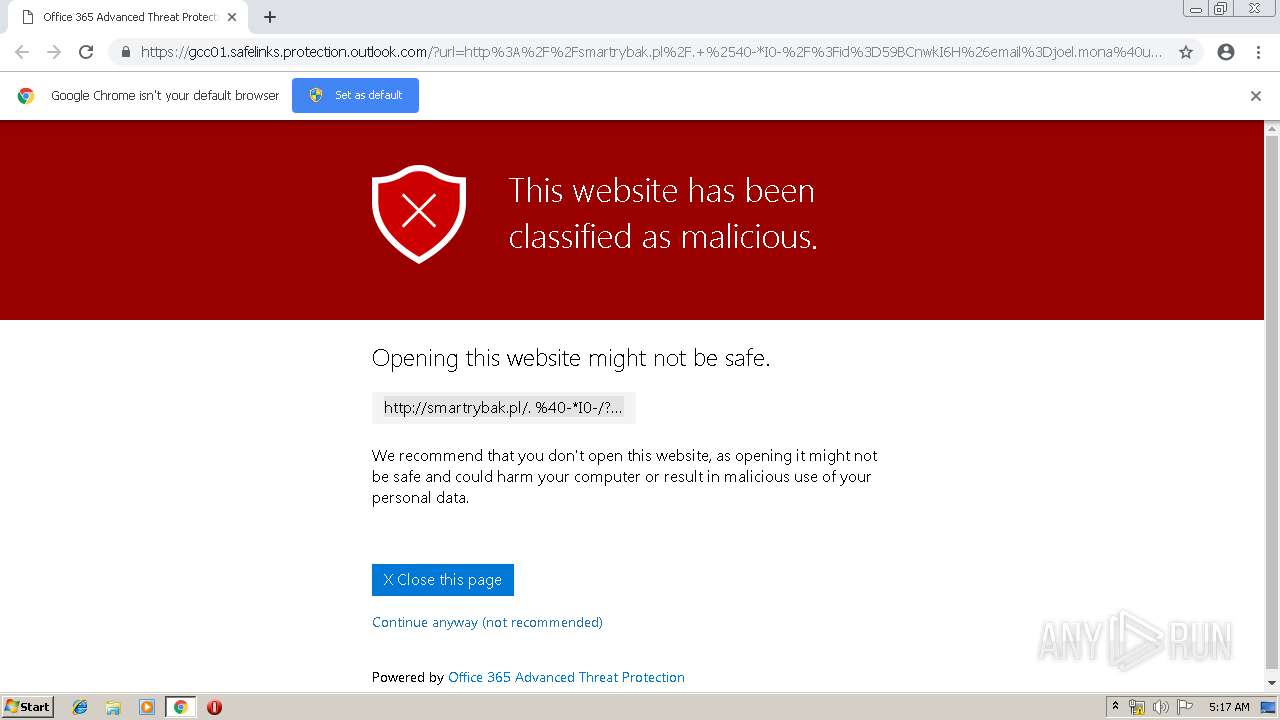
| URL: | https://gcc01.safelinks.protection.outlook.com/?url=http%3A%2F%2Fsmartrybak.pl%2F.+%2540-*I0-%2F%3Fid%3D59BCnwkI6H%26email%3Djoel.mona%40usda.gov%26opd%3DiMerC2SjgG%26kjhgdhj%3Dusda.gov%26sdfg%3DJoel.mona&data=01%7C01%7C%7C68cd3b6859a84c7e517a08d6f32d07aa%7Ced5b36e701ee4ebc867ee03cfa0d4697%7C1&sdata=tYRkI7kNi4gjZHg5Y4xsGApk3OD%2FoSAzq8ao0xbVt%2FM%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/6ab6765e-f51e-4da4-bdf5-1a9dff653d67 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2019, 04:16:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5AC32821A29B00D380592A33658B5398 |
| SHA1: | E65C30AE7DED2F9C66C5A5294B33097E0FDF5741 |
| SHA256: | B996B6DE65DCB1D4E88D5E1A42212F9EBC307AC648EFC1406671999FD168C4B8 |
| SSDEEP: | 6:2CyV9iRXPNHszcM3AtAD29gdDJgzTO1cFDUE1R633auK78Im+SHB4E8gGk6gRAV:2CyqVswM3AtAD29algzC1cFlK3aX7yCj |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3376)
INFO
Application launched itself
- chrome.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14692900212281338503 --mojo-platform-channel-handle=4132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8798071007948196207 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8798071007948196207 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15920027177994419801 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14508523020281282308 --mojo-platform-channel-handle=4180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3316 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --service-pipe-token=10543181930582881302 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10543181930582881302 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17927638945454926221 --mojo-platform-channel-handle=3348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2947738325251398840 --mojo-platform-channel-handle=4452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18425146868599523050 --mojo-platform-channel-handle=4324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10475201787745855185,11569598025373852412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16536706223392640840 --mojo-platform-channel-handle=4456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
535
Read events
461
Write events
70
Delete events
4
Modification events
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3376-13205305027837250 |
Value: 259 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3376) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3376-13205305027837250 |
Value: 259 | |||
Executable files
0
Suspicious files
15
Text files
207
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\5b4bb8eb-1635-4071-9ba4-10f83aa5375b.tmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3376 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
39
DNS requests
17
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
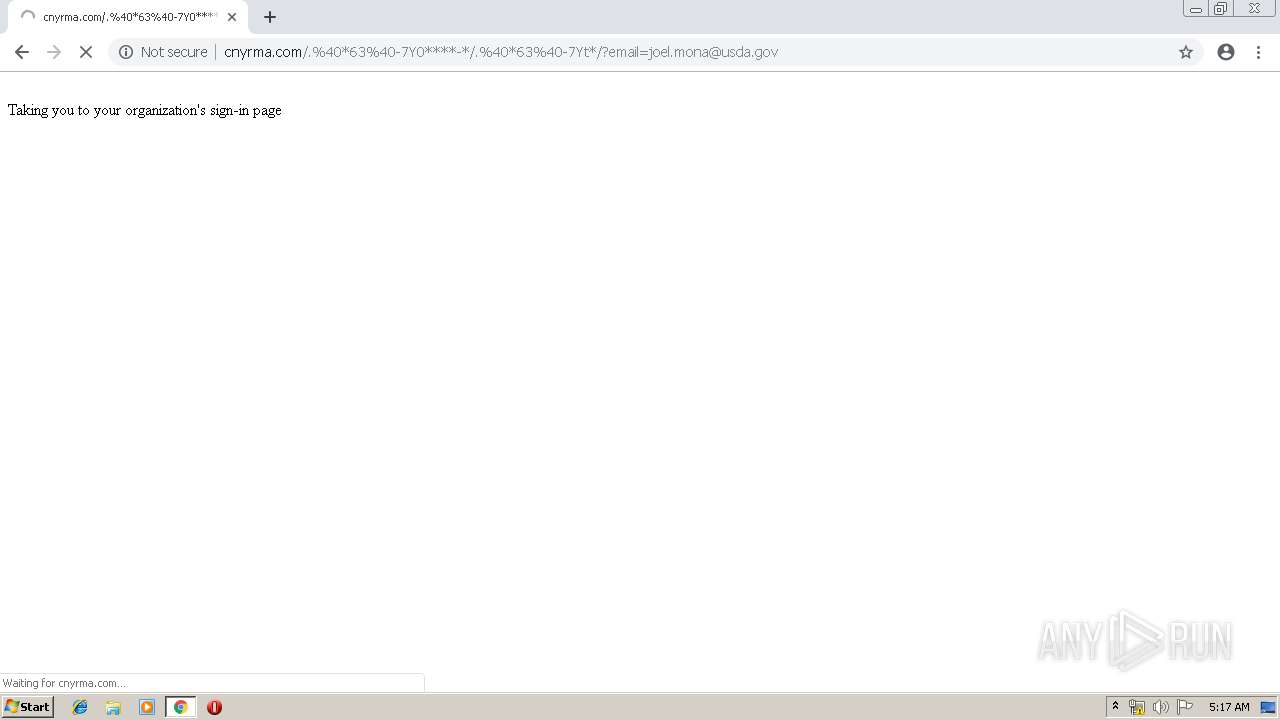
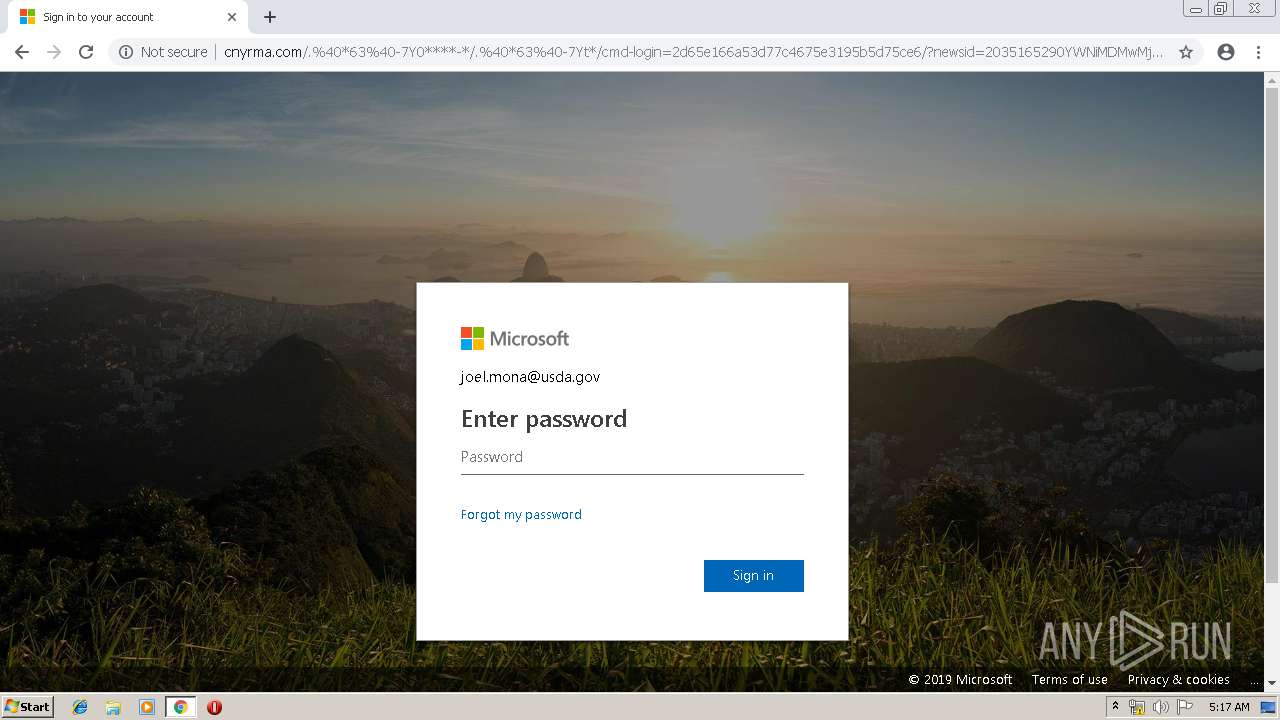
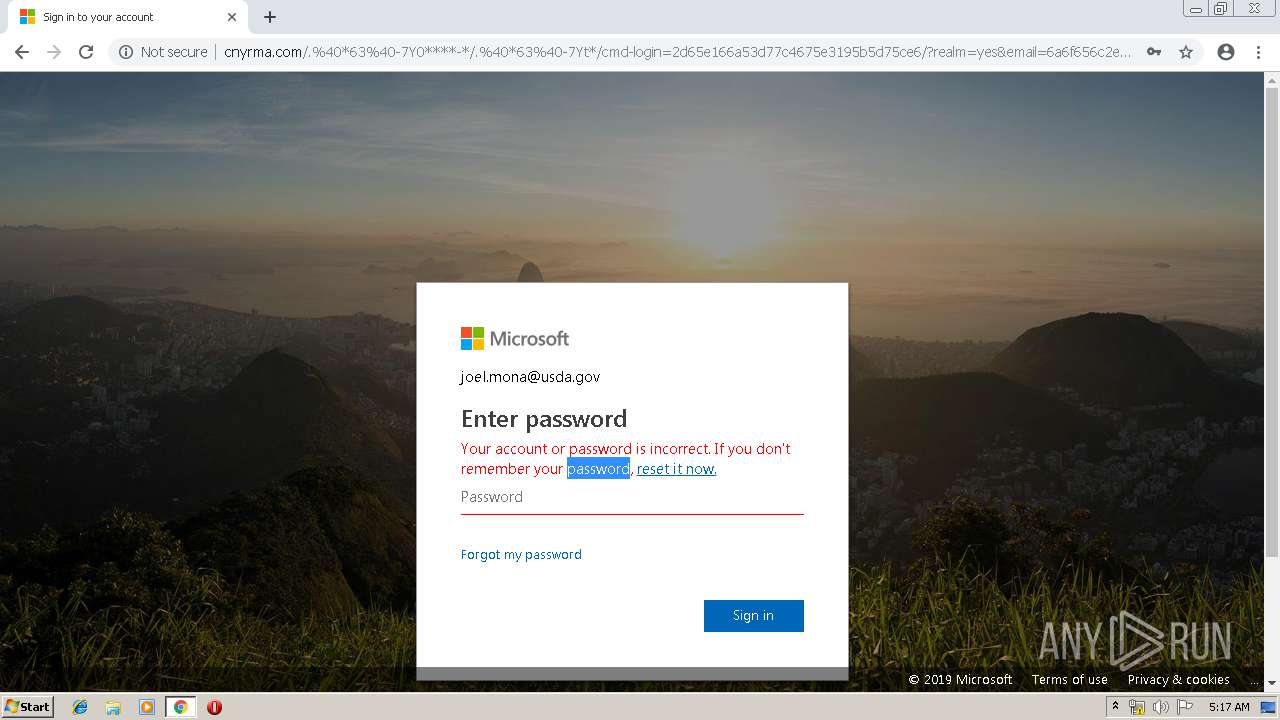
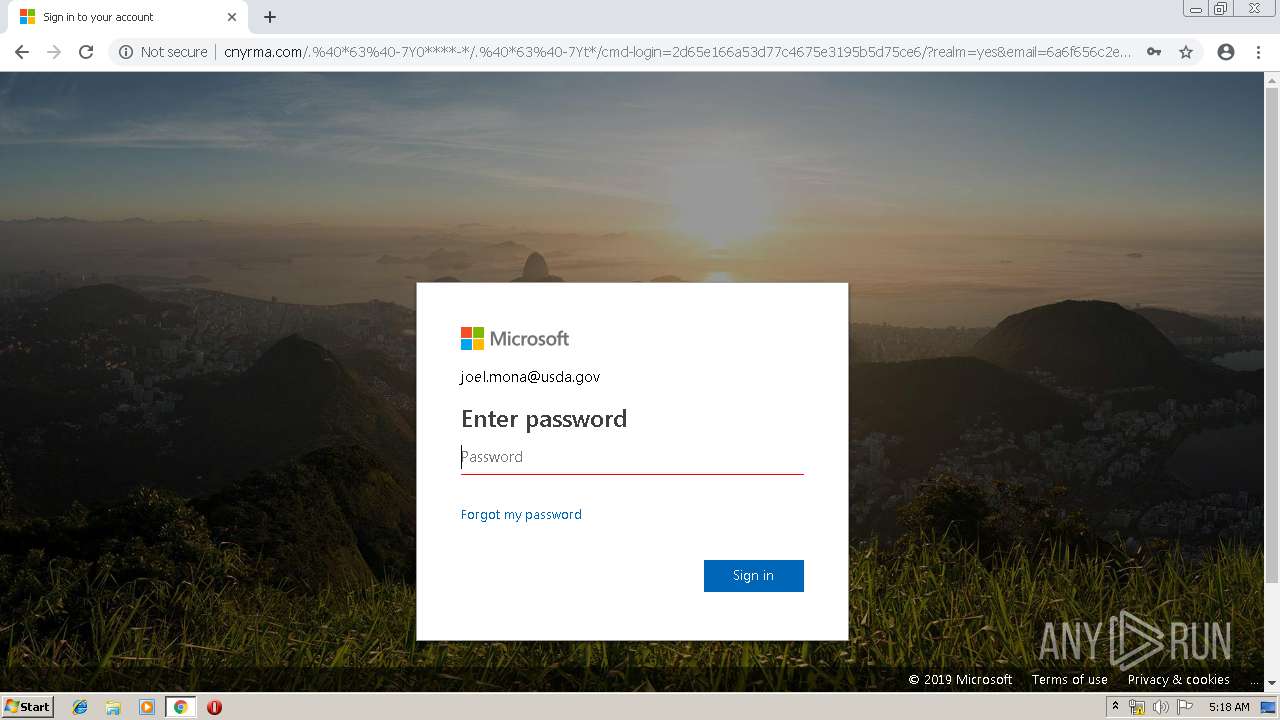
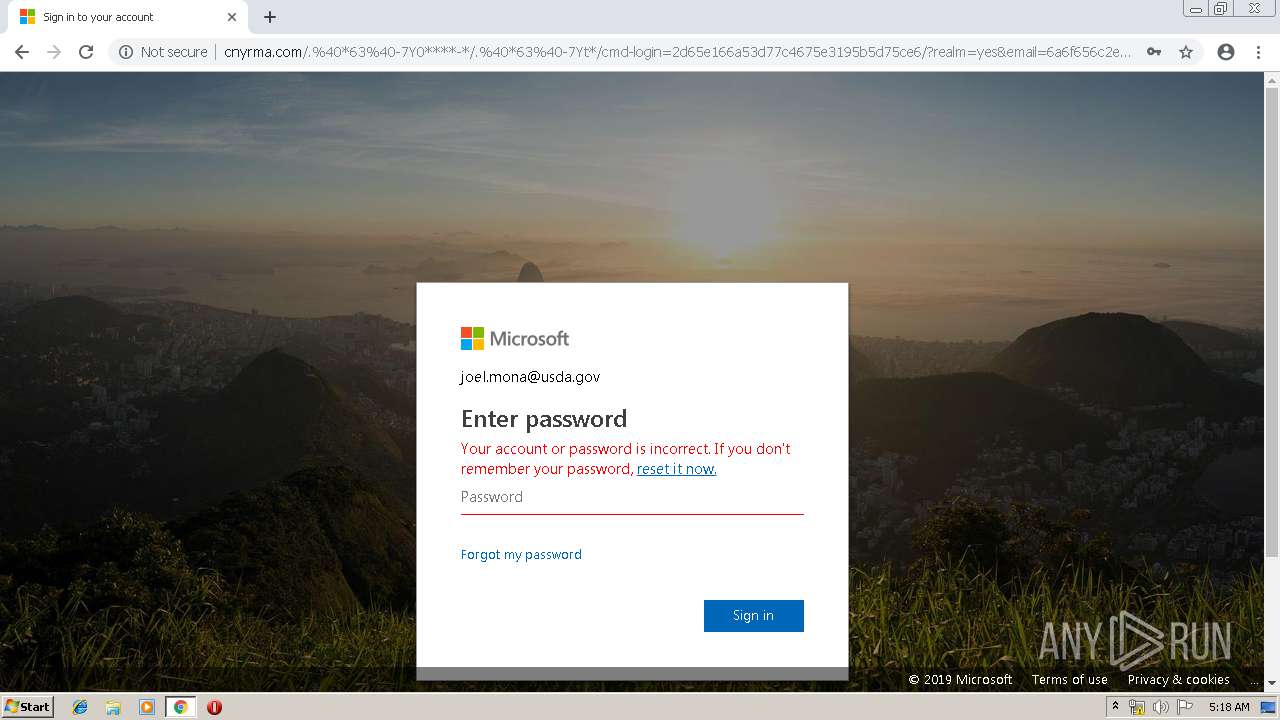
3376 | chrome.exe | GET | 304 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/0.jpg | US | — | — | suspicious |
3376 | chrome.exe | GET | — | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/arrow_left.svg?x=a9cc2824ef3517b6c4160dcf8ff7d410 | US | — | — | suspicious |
3376 | chrome.exe | GET | 200 | 87.245.198.16:80 | http://r5---sn-gxuog0-axqe.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.117.118.92&mm=28&mn=sn-gxuog0-axqe&ms=nvh&mt=1560831336&mv=m&pl=24&shardbypass=yes | RU | crx | 842 Kb | whitelisted |
3376 | chrome.exe | GET | 200 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/?newsid=2035165290YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=&email=6a6f656c2e6d6f6e6140757364612e676f76&loginpage=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=&reff=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE=YWNiMDMwMjMxMjYxYWJkMTZhNTRlODIxODc0ZDkxYzE= | US | html | 9.36 Kb | suspicious |
3376 | chrome.exe | GET | 200 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/?email=joel.mona@usda.gov | US | html | 673 b | suspicious |
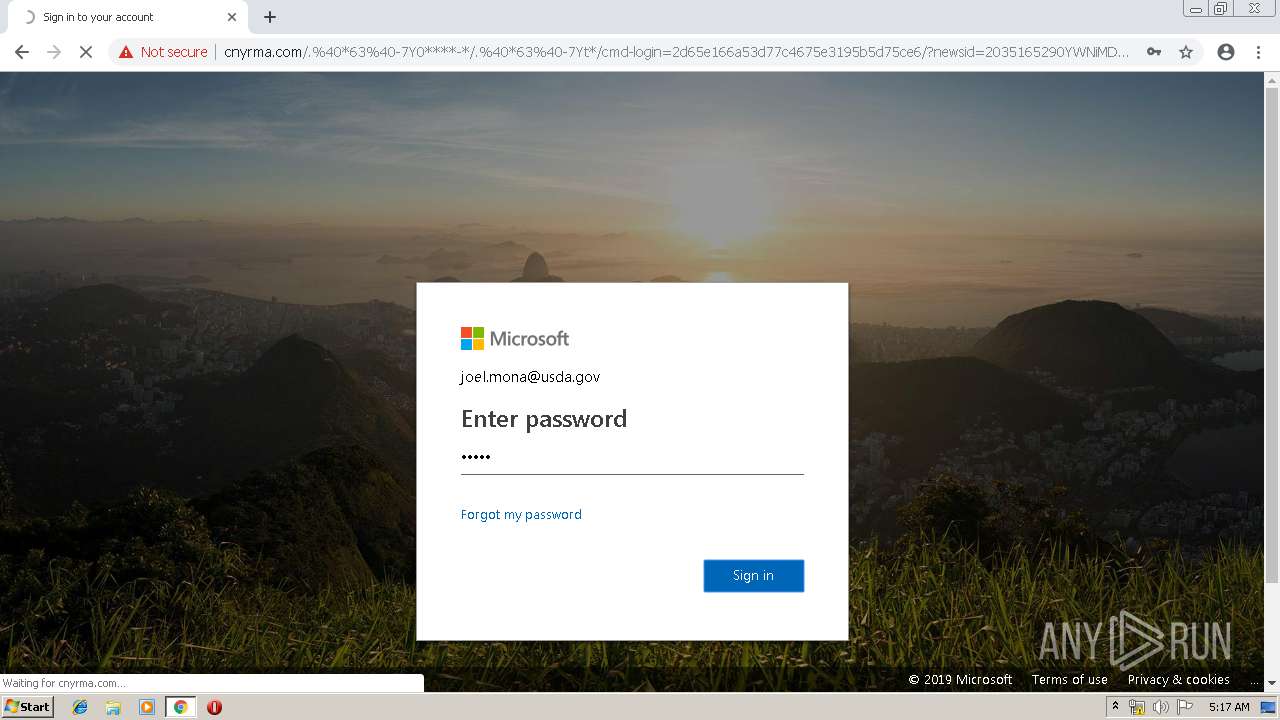
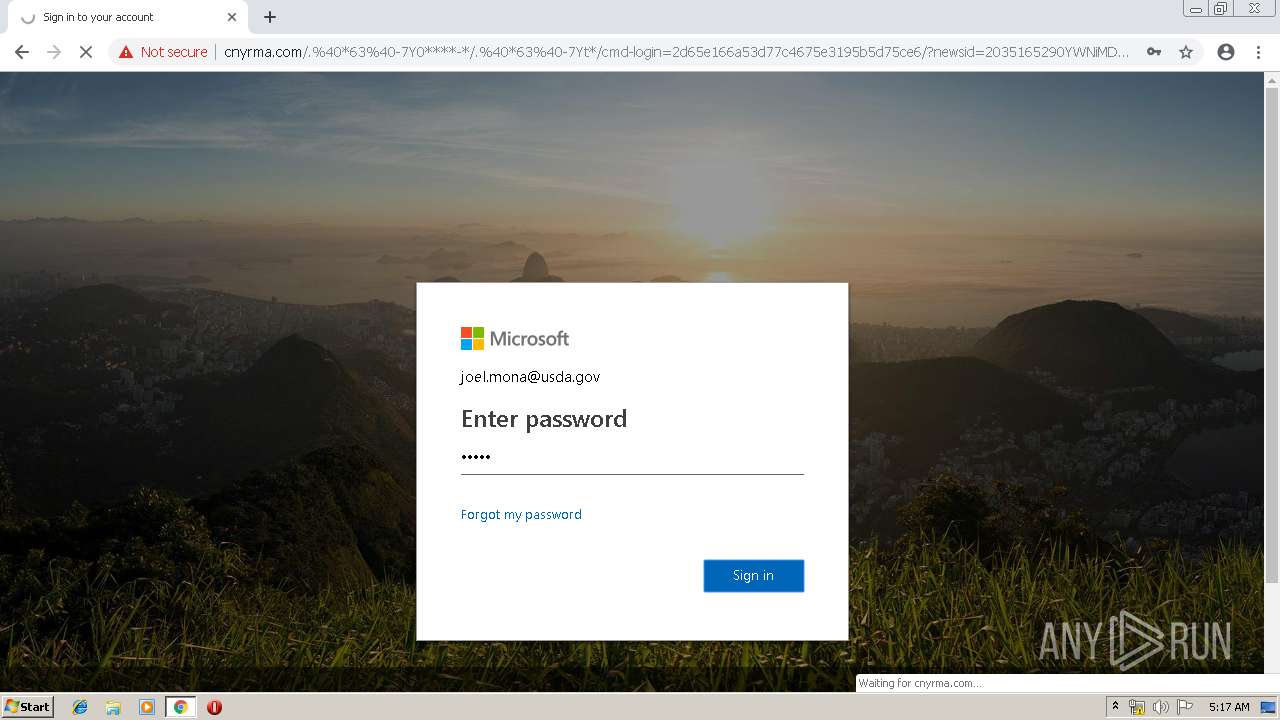
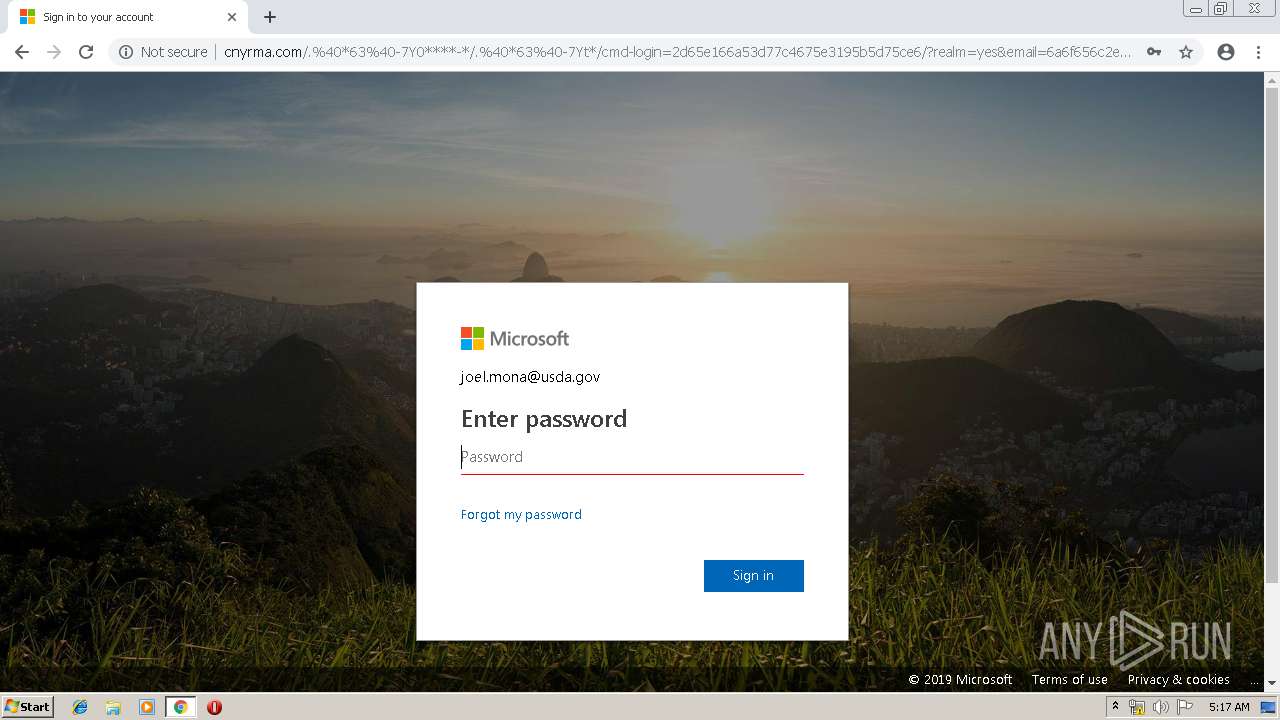
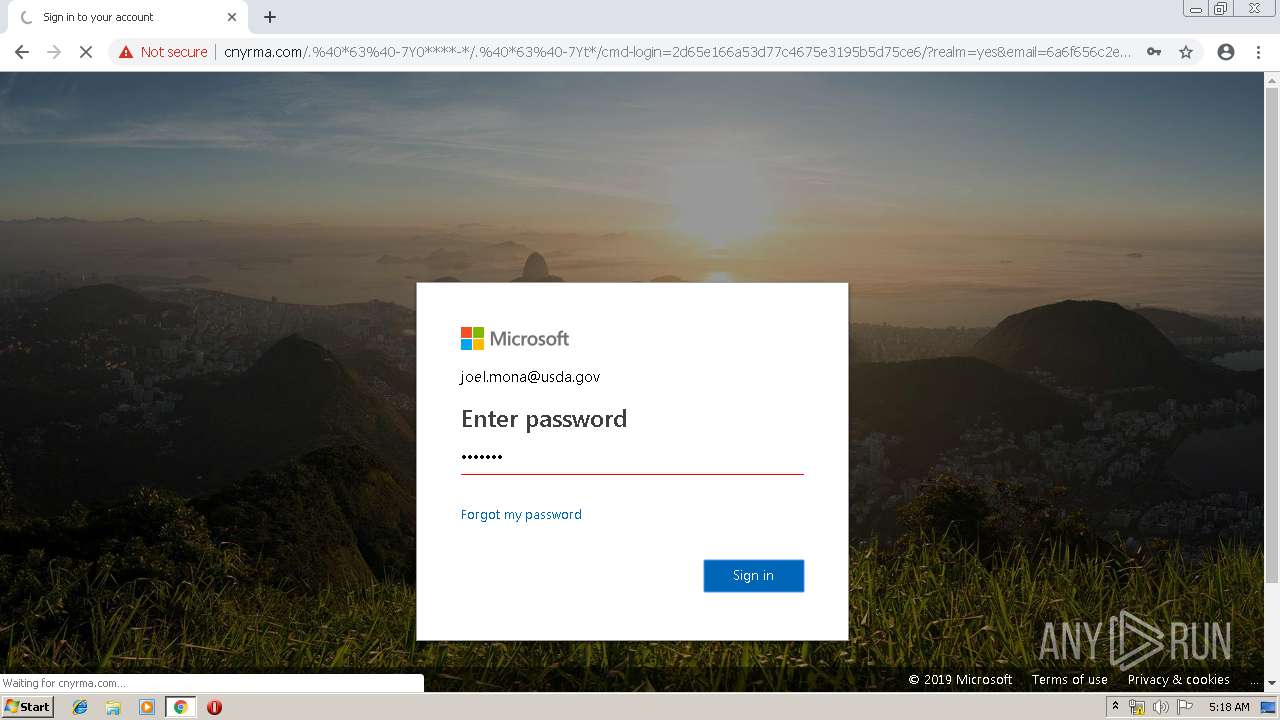
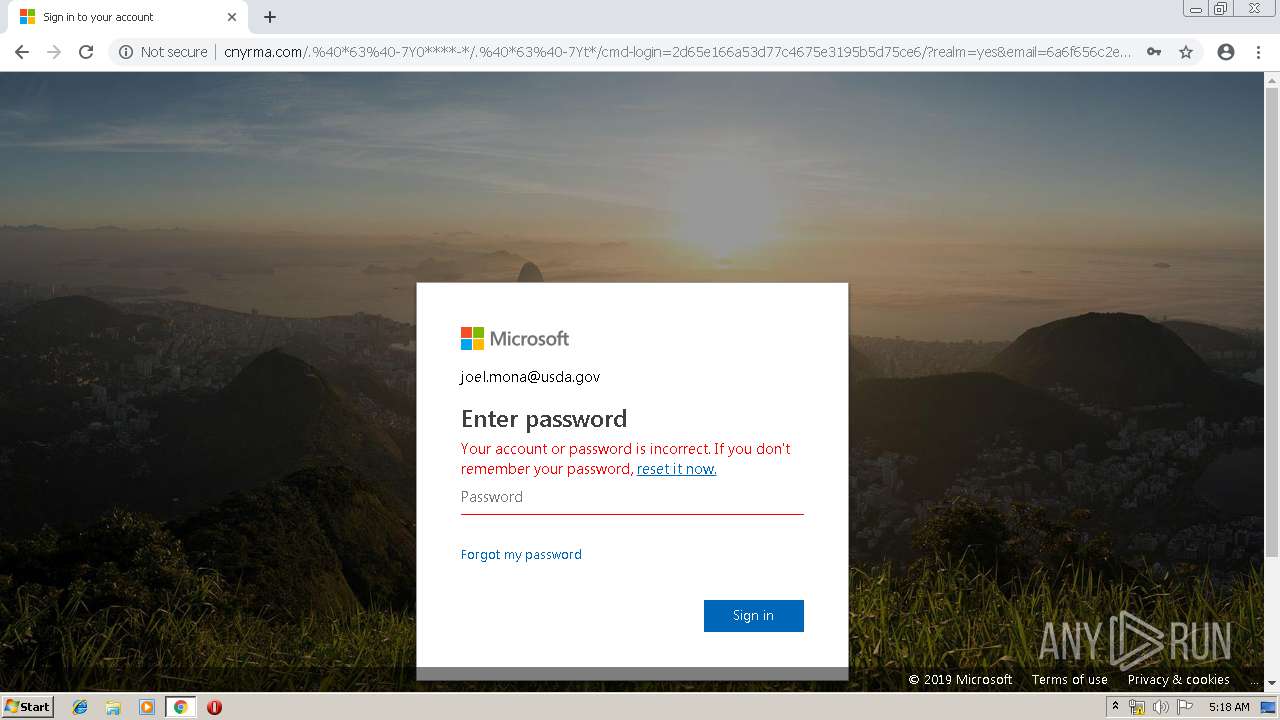
3376 | chrome.exe | POST | 302 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/?realm=yes&email=6a6f656c2e6d6f6e6140757364612e676f76&exsvurl=1&ll-cc=4105&modurl=0&path=/mail/search&id=333636313336363633363335333636333332363533363634333636363336363533363331333433303337333533373333333633343336333133323635333633373336363633373336 | US | — | — | suspicious |
3376 | chrome.exe | GET | 304 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/microsoft_logo.svg?x=ee5c8d9fb6248c938fd0dc19370e90bd | US | html | 9.60 Kb | suspicious |
3376 | chrome.exe | GET | 200 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/?realm=yes&email=6a6f656c2e6d6f6e6140757364612e676f76&exsvurl=1&ll-cc=4105&modurl=0&path=/mail/search&id=333636313336363633363335333636333332363533363634333636363336363533363331333433303337333533373333333633343336333133323635333633373336363633373336 | US | html | 9.60 Kb | suspicious |
3376 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 511 b | whitelisted |
3376 | chrome.exe | GET | 304 | 162.212.87.131:80 | http://cnyrma.com/.%40*63%40-7Y0****-*/.%40*63%40-7Yt*/cmd-login=2d65e166a53d77c4675e3195b5d75ce6/0.jpg | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3376 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 104.47.62.28:443 | gcc01.safelinks.protection.outlook.com | Microsoft Corporation | US | unknown |
3376 | chrome.exe | 172.217.23.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 185.135.88.254:80 | smartrybak.pl | LH.pl Sp. z o.o. | PL | malicious |
3376 | chrome.exe | 46.21.144.101:443 | newserviceoffice.com | Swiftway Sp. z o.o. | NL | unknown |
3376 | chrome.exe | 162.212.87.131:80 | cnyrma.com | Northland Communications | US | suspicious |
3376 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3376 | chrome.exe | 184.31.91.84:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
gcc01.safelinks.protection.outlook.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
smartrybak.pl |
| malicious |
newserviceoffice.com |
| malicious |
cnyrma.com |
| suspicious |
clients2.google.com |
| whitelisted |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3376 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
3376 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
4 ETPRO signatures available at the full report