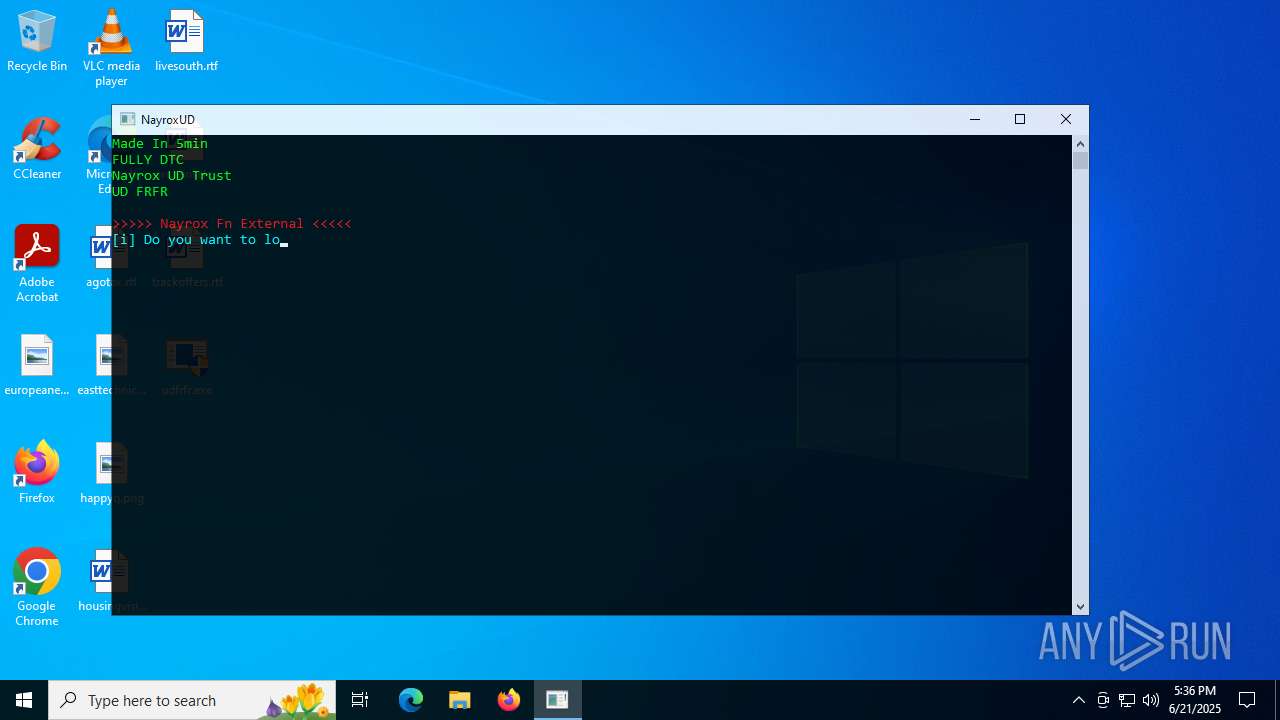
| File name: | udfrfr.exe |
| Full analysis: | https://app.any.run/tasks/115e68f6-3e23-4595-909f-4e10428e70f8 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 17:36:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 621BB3A73729CEEB9EF0FD6C73E52667 |
| SHA1: | 0032F33926071576E13C274E4735FA8FF4CBD6A8 |
| SHA256: | B98DBFD442581EC8A353F05863AE1AC63814314AEC4CC9C11C7FCDC69B3E0BA9 |
| SSDEEP: | 12288:5cPNJeyl+SMn7igZi7VP8tyWaDEyDLqTfn6SbWbK:5cPNJeVSw7iz8tyWIEKqTfn1 |
MALICIOUS
JEEFO has been detected
- udfrfr.exe (PID: 5644)
- icsys.icn.exe (PID: 2780)
- explorer.exe (PID: 1896)
- svchost.exe (PID: 5168)
Changes the autorun value in the registry
- explorer.exe (PID: 1896)
- svchost.exe (PID: 5168)
SUSPICIOUS
Starts application with an unusual extension
- udfrfr.exe (PID: 5644)
- udfrfr.exe (PID: 6652)
Executable content was dropped or overwritten
- udfrfr.exe (PID: 5644)
- explorer.exe (PID: 1896)
- spoolsv.exe (PID: 2076)
- icsys.icn.exe (PID: 2780)
Starts itself from another location
- udfrfr.exe (PID: 5644)
- explorer.exe (PID: 1896)
- spoolsv.exe (PID: 2076)
- svchost.exe (PID: 5168)
- icsys.icn.exe (PID: 2780)
The process creates files with name similar to system file names
- spoolsv.exe (PID: 2076)
- icsys.icn.exe (PID: 2780)
Creates or modifies Windows services
- svchost.exe (PID: 5168)
Application launched itself
- udfrfr.exe (PID: 6652)
INFO
The sample compiled with english language support
- udfrfr.exe (PID: 5644)
- explorer.exe (PID: 1896)
- spoolsv.exe (PID: 2076)
- icsys.icn.exe (PID: 2780)
Checks supported languages
- icsys.icn.exe (PID: 2780)
- udfrfr.exe (PID: 5644)
- udfrfr.exe (PID: 6652)
- udfrfr.exe (PID: 3576)
- explorer.exe (PID: 1896)
- spoolsv.exe (PID: 2076)
- svchost.exe (PID: 5168)
- spoolsv.exe (PID: 2228)
Create files in a temporary directory
- icsys.icn.exe (PID: 2780)
- udfrfr.exe (PID: 5644)
- spoolsv.exe (PID: 2076)
- svchost.exe (PID: 5168)
- explorer.exe (PID: 1896)
- spoolsv.exe (PID: 2228)
Reads the computer name
- udfrfr.exe (PID: 6652)
- svchost.exe (PID: 5168)
Manual execution by a user
- explorer.exe (PID: 1132)
- svchost.exe (PID: 1056)
Checks proxy server information
- slui.exe (PID: 2220)
Launching a file from a Registry key
- explorer.exe (PID: 1896)
- svchost.exe (PID: 5168)
Reads the software policy settings
- slui.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
147
Monitored processes
13
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 504 | "C:\Users\admin\Desktop\udfrfr.exe" | C:\Users\admin\Desktop\udfrfr.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 1056 | c:\windows\resources\svchost.exe RO | C:\Windows\Resources\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 1132 | c:\windows\resources\themes\explorer.exe RO | C:\Windows\Resources\Themes\explorer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 1896 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 2076 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2220 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2780 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | udfrfr.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3576 | c:\users\admin\desktop\udfrfr.exe | C:\Users\admin\Desktop\udfrfr.exe | — | udfrfr.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 5168 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
Total events
3 903
Read events
3 884
Write events
15
Delete events
4
Modification events
| (PID) Process: | (5168) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (5168) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (5168) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (5168) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (1896) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (1896) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (1896) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (1896) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (5644) udfrfr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (2780) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
Executable files
5
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFA5DC17E6C34AC24E.TMP | binary | |
MD5:D4C916E4E3CB87988C818ED32D1E2C85 | SHA256:83B507E7574D1F6AFA5B1108DED982CC851B799785DADF9D64CFC95C8ED7FA08 | |||
| 5644 | udfrfr.exe | C:\Users\admin\Desktop\udfrfr.exe | executable | |
MD5:1B35B13531805765809C6E40BF512D24 | SHA256:A83176B1448FA1ADB0CA2B6AAEC53F2EEDD97D2054E516EFAE85528BFFDFCDF9 | |||
| 5644 | udfrfr.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:336F960E6E4DA979B07BC45BD7415143 | SHA256:C690340793B4DBFC58D8524765D0AFE0CEC1B0090EF84848F6C6A5AA6824CE06 | |||
| 2780 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:8FB4BA482D675ACB3898155DE4D1AA8A | SHA256:F9B60428AAEA78B71B10A2C8D44BA8C0623609809FEA852BC26B7288FD791057 | |||
| 1896 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:99CD4B7A5866F9CEE67184BEE7E1C794 | SHA256:3788FC3A9AD36959359438661F1224F1F9BBAD8E6E3F45B2B9E218B54A6A66B9 | |||
| 5644 | udfrfr.exe | C:\Users\admin\AppData\Local\Temp\~DFD30893FC282E5242.TMP | binary | |
MD5:45F30BFD9DD845FC7754D94E406C5343 | SHA256:738C742499B4EE40637F1688FE8B2ACEB9F3D9A3C7F28238BF07AE9459F98648 | |||
| 2076 | spoolsv.exe | C:\Windows\Resources\svchost.exe | executable | |
MD5:976C231FFB1FD8610BEBFD2F2F15353C | SHA256:6FD07BE9B17C3E0896BC723701FEF842BFE3BA4DF4F8399F1101DAB0303418A5 | |||
| 2780 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF871C25980F266081.TMP | binary | |
MD5:9581FEE2F617C0FFF28394A081B9935A | SHA256:B48A1FE33CECA6EFE50153FF36EDE186F8B10B7353678E9B712C5975D090E1BC | |||
| 2076 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF88C17795FD9AA061.TMP | binary | |
MD5:BAEE1DEAD03B9F8605B39E9B288E6A9D | SHA256:DB2B46B5D0951D1227EF02F66A782A2D1E6809023EADF8668199D5C2D5DAB7ED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
41
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5116 | RUXIMICS.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5116 | RUXIMICS.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.128:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 200 | 20.190.159.23:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.2:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.129:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5116 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5116 | RUXIMICS.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |