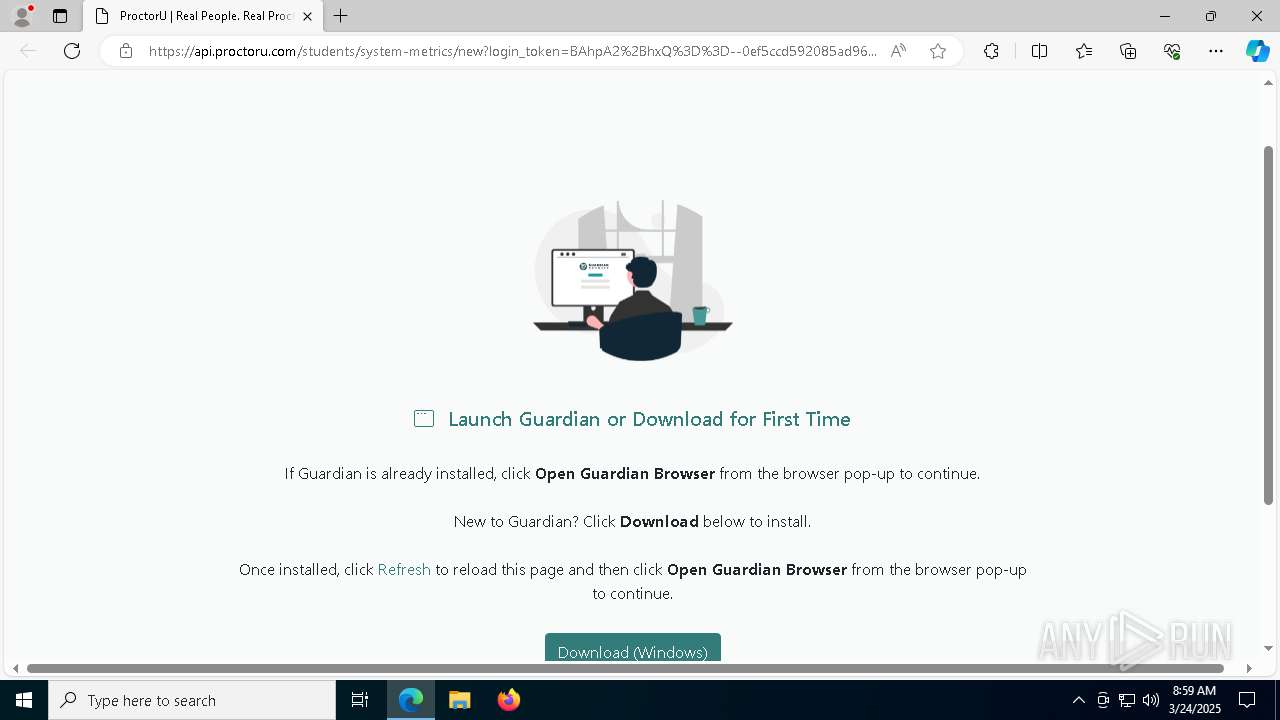
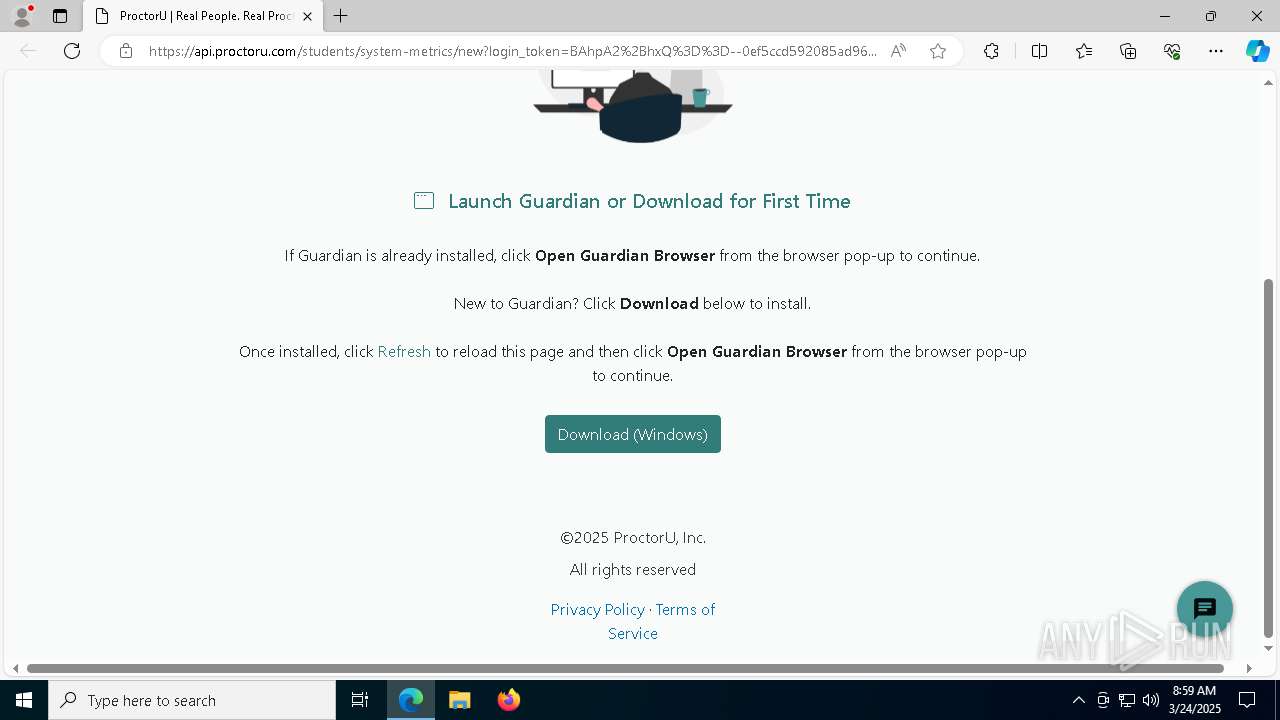
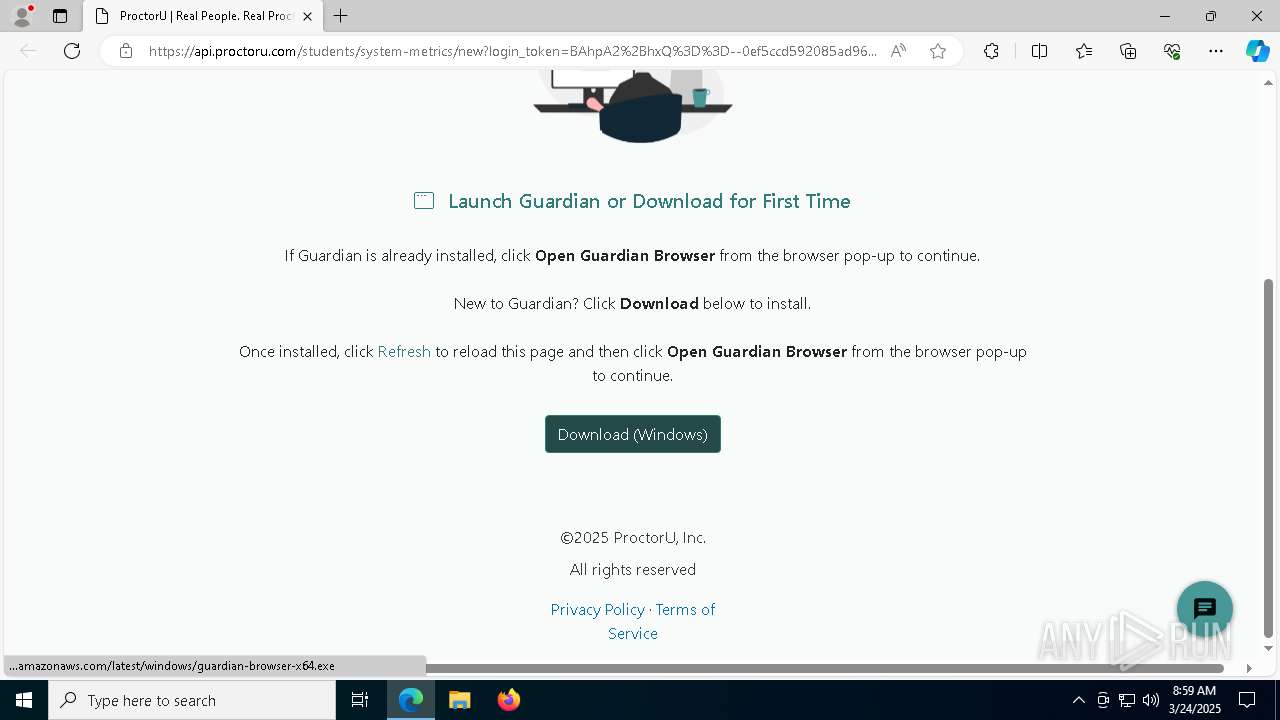
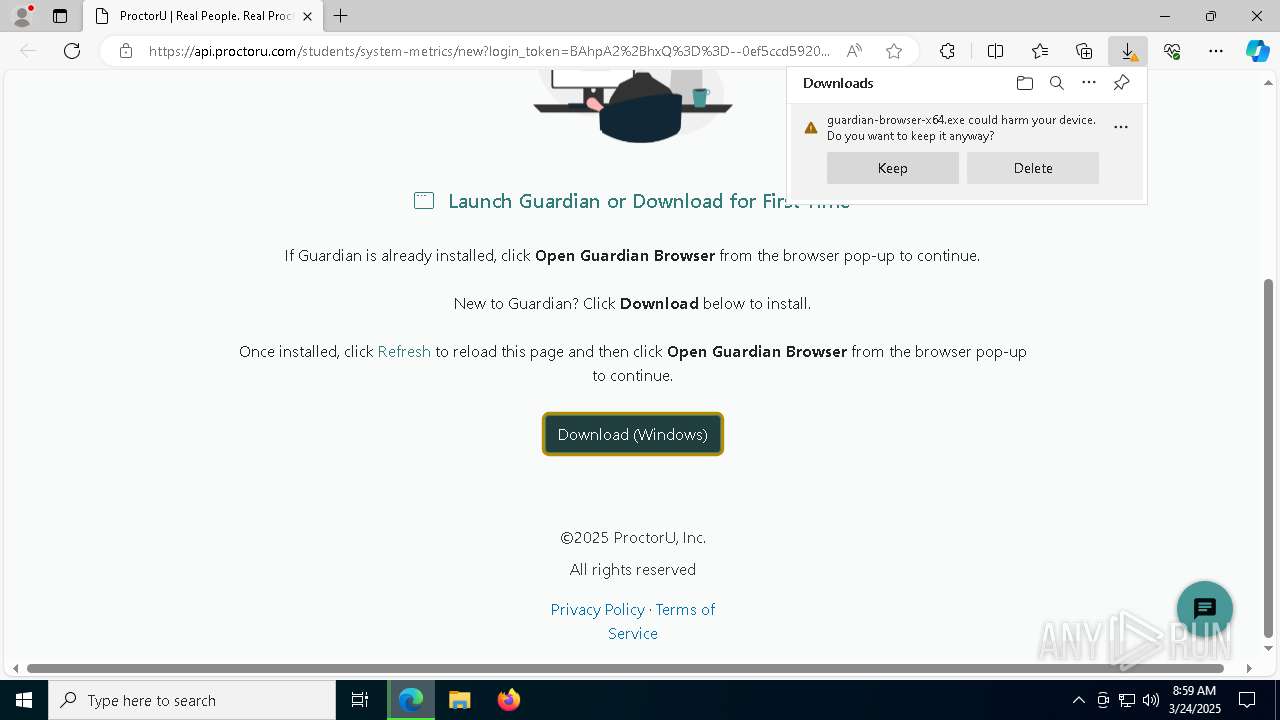
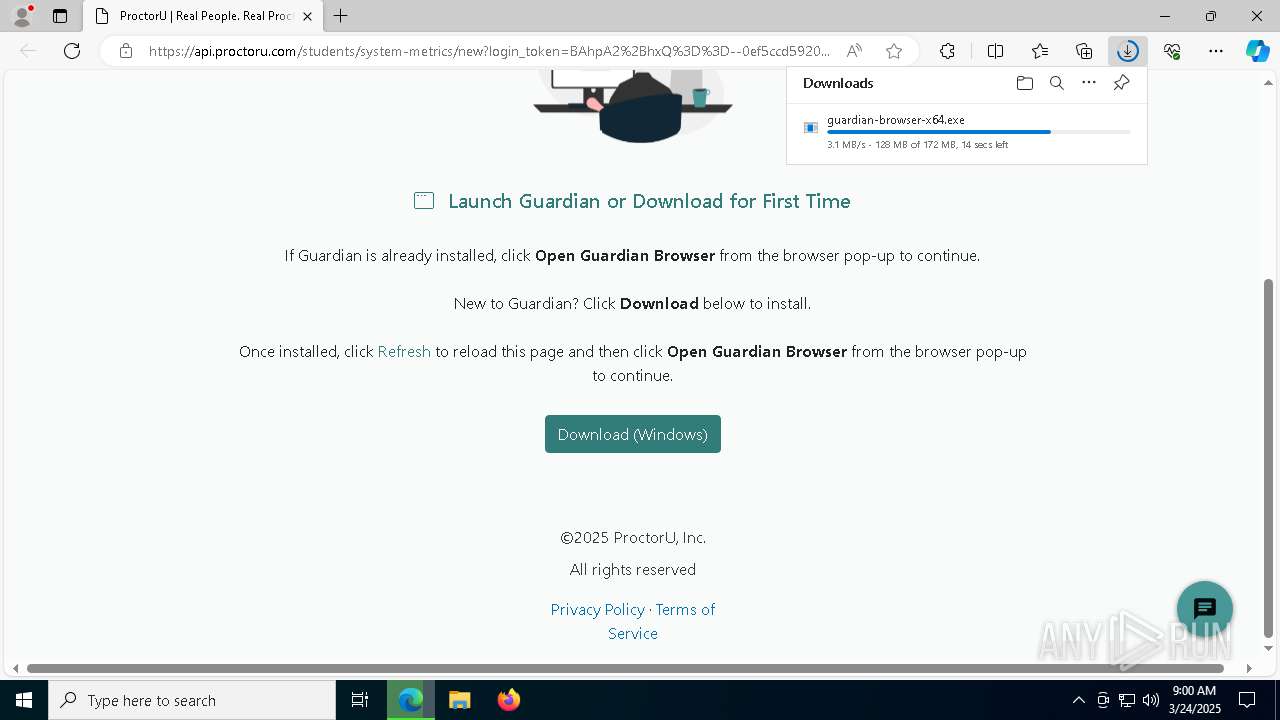
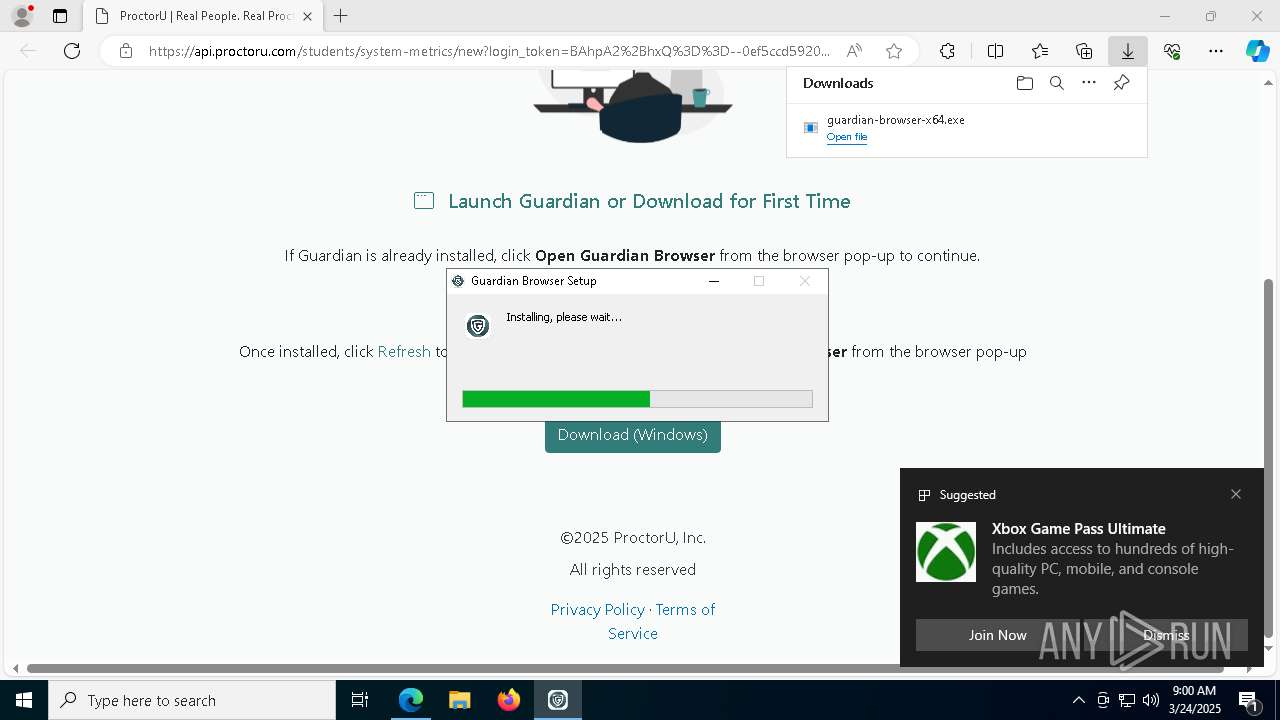
| URL: | https://api.proctoru.com/students/system-metrics/new?login_token=BAhpA2%2BhxQ%3D%3D--0ef5ccd592085ad960c0421b52aef17e387eba5a |
| Full analysis: | https://app.any.run/tasks/3b26cf0c-111f-4510-b6f0-d2ef605237f3 |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 08:59:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 3235A618DA7CA5563F97CD40B3E745E0 |
| SHA1: | 2197BE419479EA657C99A57F49CEF0787A541F12 |
| SHA256: | B985C122771006B91125BB4CAF90A1B3A648460DD7F5DEE8A6A0670AC97EACC0 |
| SSDEEP: | 3:N8DLoGRMedmBW/KxHZyY6KOuKdyNPI4bcnQ+71L5EQE:2XoGRtkBWydUY6wKd2Ibh71LaQE |
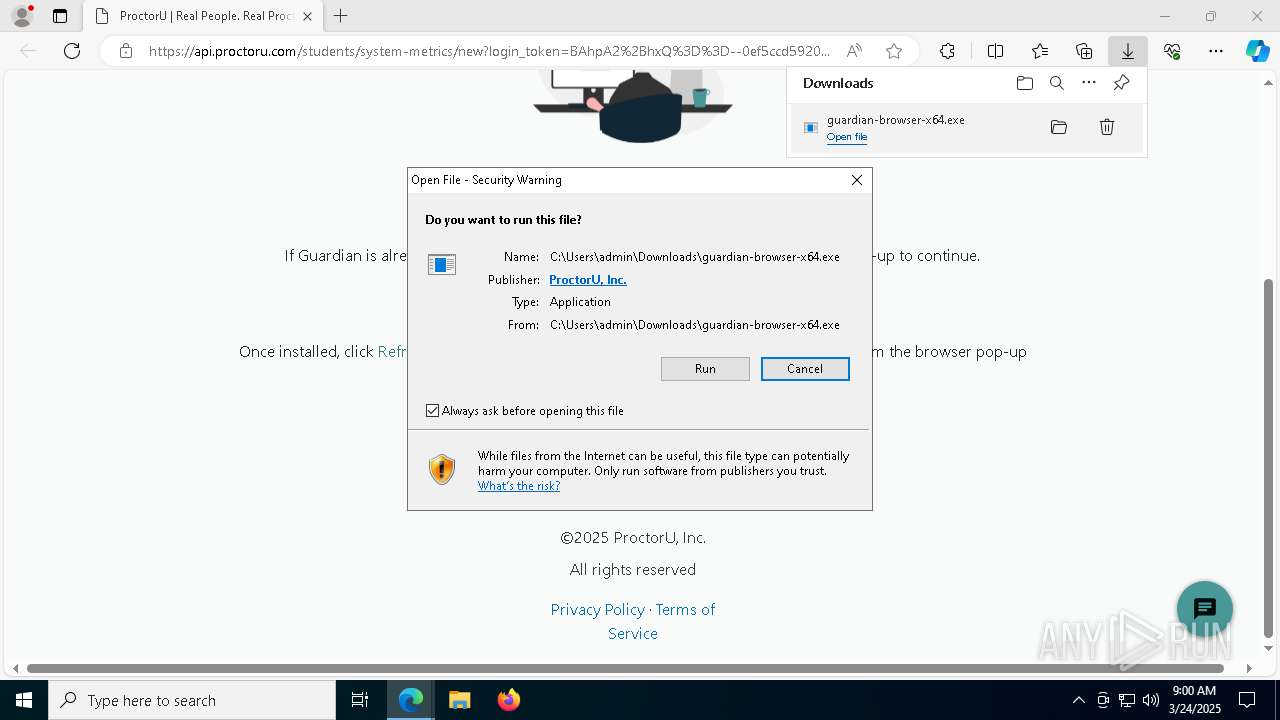
MALICIOUS
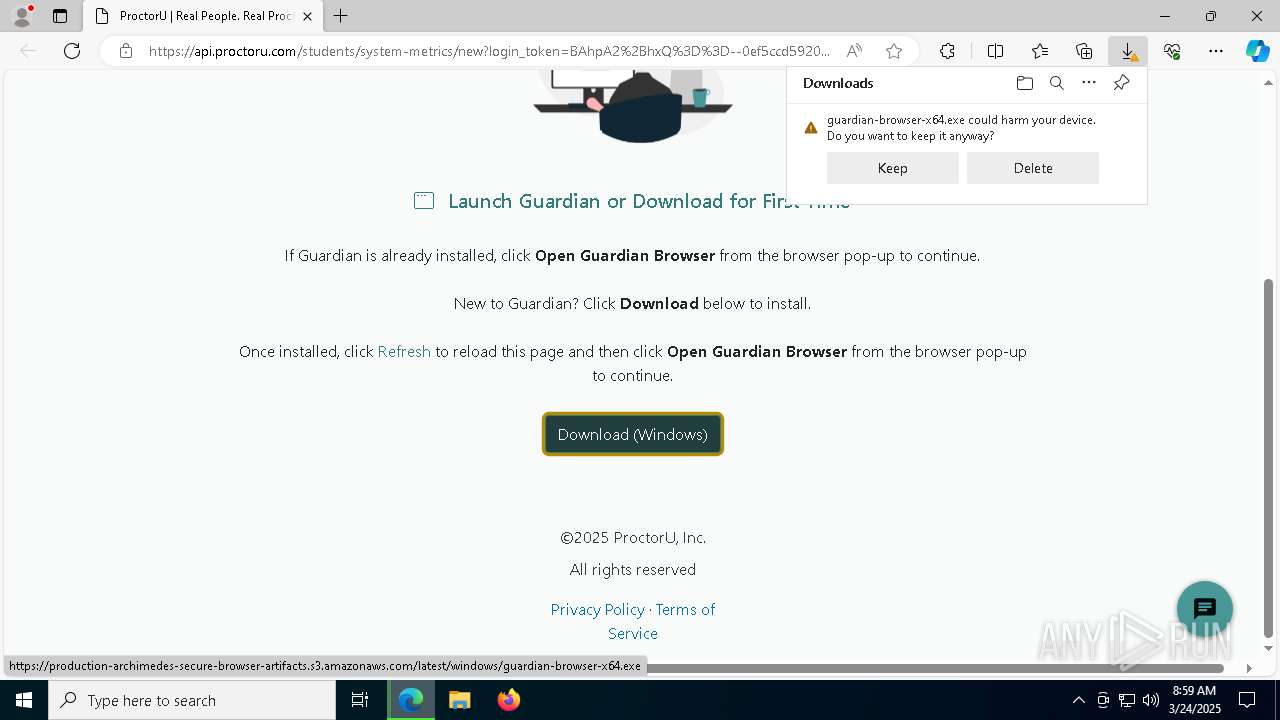
Executing a file with an untrusted certificate
- guardian-browser-x64.exe (PID: 5084)
- Guardian Browser.exe (PID: 6540)
- Guardian Browser.exe (PID: 8764)
- Guardian Browser.exe (PID: 7872)
- Guardian Browser.exe (PID: 4572)
- Guardian Browser.exe (PID: 8724)
- Guardian Browser.exe (PID: 7956)
- Guardian Browser.exe (PID: 5232)
- Guardian Browser.exe (PID: 6724)
- Guardian Browser.exe (PID: 5172)
- Guardian Browser.exe (PID: 1672)
SUSPICIOUS
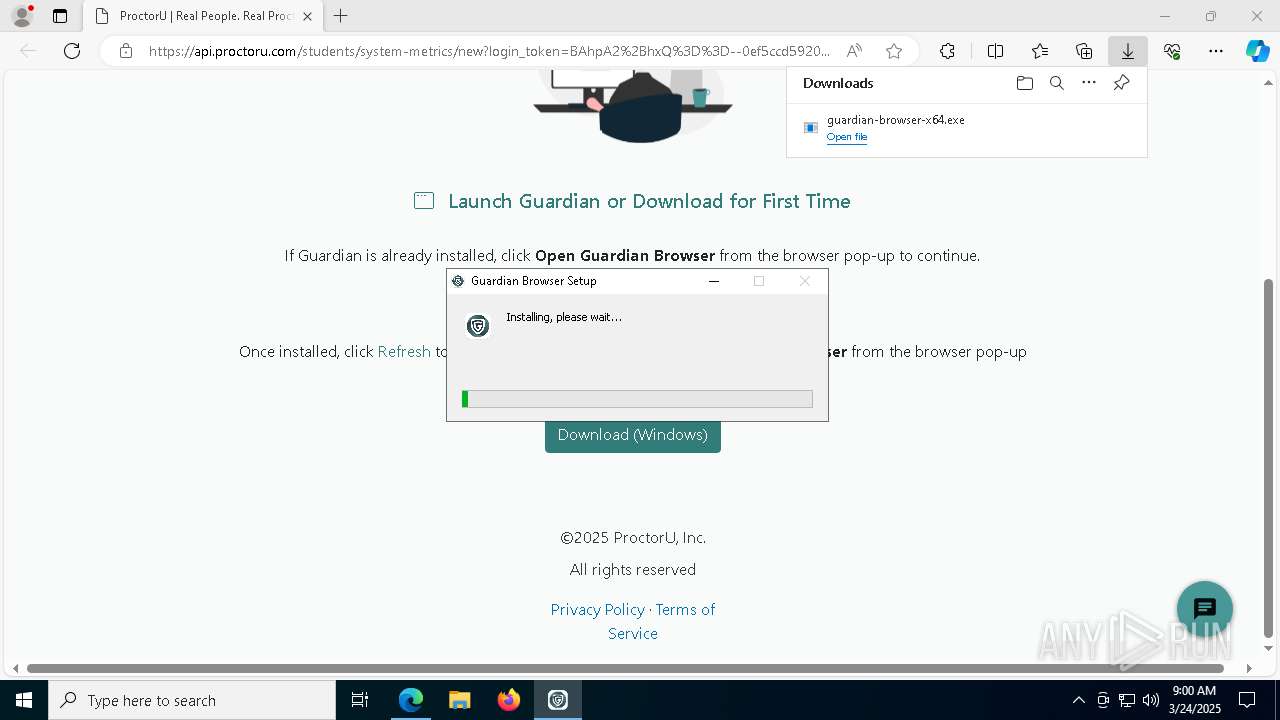
The process creates files with name similar to system file names
- guardian-browser-x64.exe (PID: 5084)
Malware-specific behavior (creating "System.dll" in Temp)
- guardian-browser-x64.exe (PID: 5084)
Starts CMD.EXE for commands execution
- guardian-browser-x64.exe (PID: 5084)
- Guardian Browser.exe (PID: 6540)
Get information on the list of running processes
- guardian-browser-x64.exe (PID: 5084)
- cmd.exe (PID: 4336)
Executable content was dropped or overwritten
- guardian-browser-x64.exe (PID: 5084)
- Guardian Browser.exe (PID: 4572)
Drops 7-zip archiver for unpacking
- guardian-browser-x64.exe (PID: 5084)
Process drops legitimate windows executable
- guardian-browser-x64.exe (PID: 5084)
Application launched itself
- Guardian Browser.exe (PID: 6540)
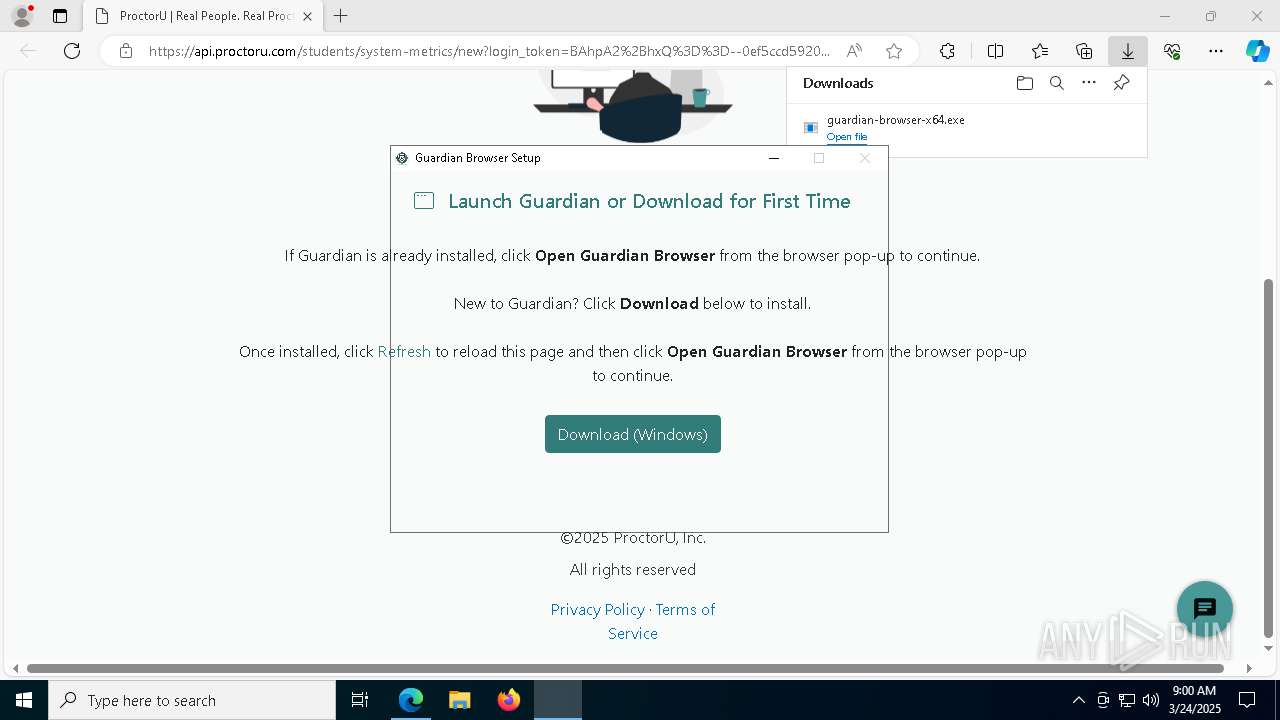
Creates a software uninstall entry
- guardian-browser-x64.exe (PID: 5084)
Starts application with an unusual extension
- cmd.exe (PID: 7768)
Checks for external IP
- svchost.exe (PID: 2196)
- Guardian Browser.exe (PID: 6724)
INFO
Reads Environment values
- identity_helper.exe (PID: 8060)
Reads the computer name
- identity_helper.exe (PID: 8060)
Checks supported languages
- identity_helper.exe (PID: 8060)
- ShellExperienceHost.exe (PID: 1184)
- Guardian Browser.exe (PID: 7872)
- Guardian Browser.exe (PID: 8764)
Executable content was dropped or overwritten
- msedge.exe (PID: 3896)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 9080)
- BackgroundTransferHost.exe (PID: 6108)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 9080)
- guardian-browser-x64.exe (PID: 5084)
- Guardian Browser.exe (PID: 6540)
- Guardian Browser.exe (PID: 8724)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 9080)
Application launched itself
- msedge.exe (PID: 3896)
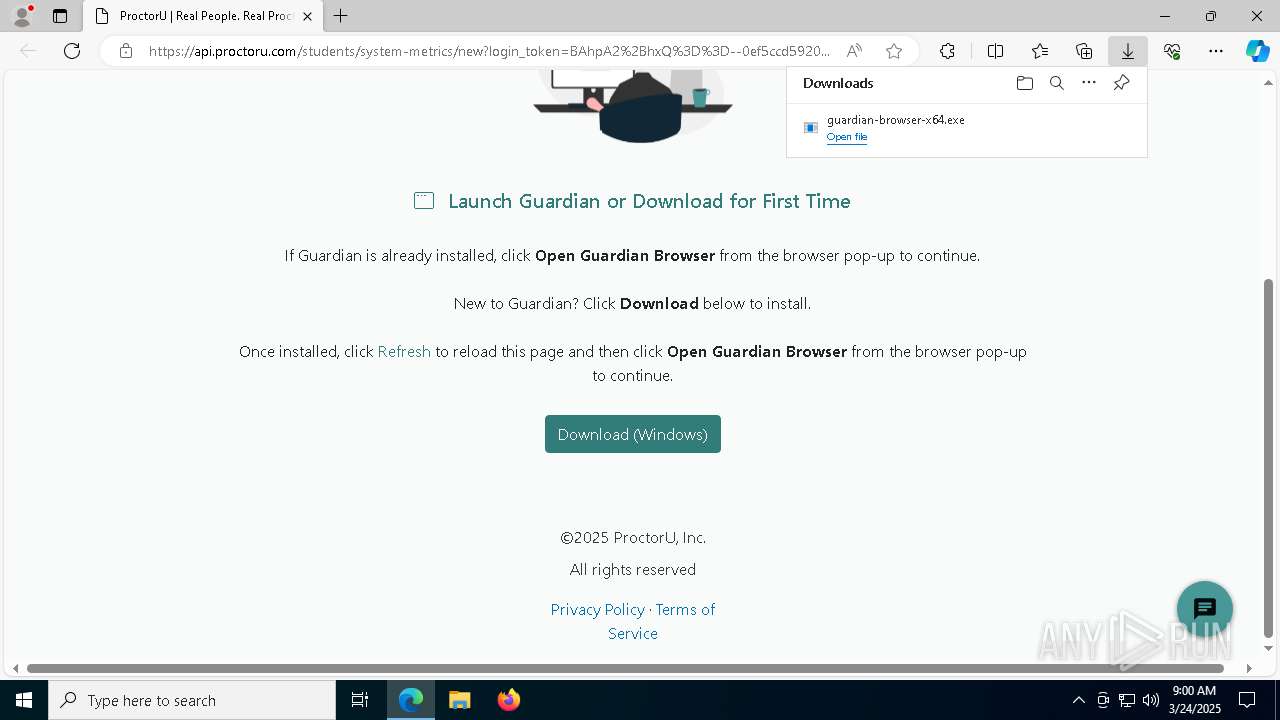
Autorun file from Downloads
- msedge.exe (PID: 300)
The sample compiled with english language support
- guardian-browser-x64.exe (PID: 5084)
Create files in a temporary directory
- guardian-browser-x64.exe (PID: 5084)
- Guardian Browser.exe (PID: 4572)
Changes the display of characters in the console
- cmd.exe (PID: 7768)
Manual execution by a user
- Guardian Browser.exe (PID: 6540)
Drops encrypted JS script (Microsoft Script Encoder)
- Guardian Browser.exe (PID: 4572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
212
Monitored processes
76
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7000 --field-trial-handle=2336,i,10928433025013956485,4062697137062589949,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5976 --field-trial-handle=2336,i,10928433025013956485,4062697137062589949,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6928 --field-trial-handle=2336,i,10928433025013956485,4062697137062589949,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7352 --field-trial-handle=2336,i,10928433025013956485,4062697137062589949,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6588 --field-trial-handle=2336,i,10928433025013956485,4062697137062589949,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Programs\guardian-browser\Guardian Browser.exe" --type=utility --utility-sub-type=video_capture.mojom.VideoCaptureService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\Guardian Browser" --secure-schemes=sentry-ipc --bypasscsp-schemes=sentry-ipc --cors-schemes=sentry-ipc --fetch-schemes=sentry-ipc --mojo-platform-channel-handle=3568 --field-trial-handle=1756,i,18044047394687777809,4840456928378050025,262144 --enable-features=kWebSQLAccess --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version /prefetch:8 | C:\Users\admin\AppData\Local\Programs\guardian-browser\Guardian Browser.exe | — | Guardian Browser.exe | |||||||||||
User: admin Company: Meazure Learning Integrity Level: MEDIUM Description: Guardian Browser Exit code: 0 Version: 2.0.1.2 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://api.proctoru.com/students/system-metrics/new?login_token=BAhpA2%2BhxQ%3D%3D--0ef5ccd592085ad960c0421b52aef17e387eba5a" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
17 490
Read events
17 420
Write events
52
Delete events
18
Modification events
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B45CA019A98F2F00 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A52CA919A98F2F00 | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {CF27797A-C059-4F5D-B07E-EB2ADFE84CAA} | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {26993B23-FFD8-440C-BB10-0440FBF95A27} | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E0BCE3E9-5293-45A7-B5FD-7827FC87DCB6} | |||
| (PID) Process: | (3896) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393874 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {413C7DF2-EBEC-4686-9749-FD2B9D9AB3AF} | |||
Executable files
38
Suspicious files
353
Text files
57
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b623.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b632.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b642.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b642.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b652.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
90
DNS requests
99
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5608 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8100 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
9080 | BackgroundTransferHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5608 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2616 | svchost.exe | HEAD | 200 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742976739&P2=404&P3=2&P4=Cu%2bxGYxjtpOppszmKiwphZ19rjyDdorzbhd83AsnMWKwgtiV6VWTxAGD7wLK5QOq1xN9lD%2fAd8XYy4SFF0AAxw%3d%3d | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742976739&P2=404&P3=2&P4=Cu%2bxGYxjtpOppszmKiwphZ19rjyDdorzbhd83AsnMWKwgtiV6VWTxAGD7wLK5QOq1xN9lD%2fAd8XYy4SFF0AAxw%3d%3d | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742976739&P2=404&P3=2&P4=Cu%2bxGYxjtpOppszmKiwphZ19rjyDdorzbhd83AsnMWKwgtiV6VWTxAGD7wLK5QOq1xN9lD%2fAd8XYy4SFF0AAxw%3d%3d | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742976739&P2=404&P3=2&P4=Cu%2bxGYxjtpOppszmKiwphZ19rjyDdorzbhd83AsnMWKwgtiV6VWTxAGD7wLK5QOq1xN9lD%2fAd8XYy4SFF0AAxw%3d%3d | unknown | — | — | whitelisted |
2616 | svchost.exe | GET | 206 | 217.20.57.36:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1742976739&P2=404&P3=2&P4=Cu%2bxGYxjtpOppszmKiwphZ19rjyDdorzbhd83AsnMWKwgtiV6VWTxAGD7wLK5QOq1xN9lD%2fAd8XYy4SFF0AAxw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3896 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7380 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 13.107.246.44:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7380 | msedge.exe | 44.240.18.69:443 | api.proctoru.com | AMAZON-02 | US | whitelisted |
7380 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
api.proctoru.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
assets.proctoru.com |
| whitelisted |
www.bing.com |
| whitelisted |
browser.sentry-cdn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
7380 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to newrelic .com |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (icanhazip .com in TLS SNI) |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (myip .opendns .com in DNS lookup) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (icanhazip .com) |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (myip .opendns .com in DNS lookup) |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (myip .opendns .com in DNS lookup) |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (myip .opendns .com in DNS lookup) |
6724 | Guardian Browser.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (myip .opendns .com in DNS lookup) |