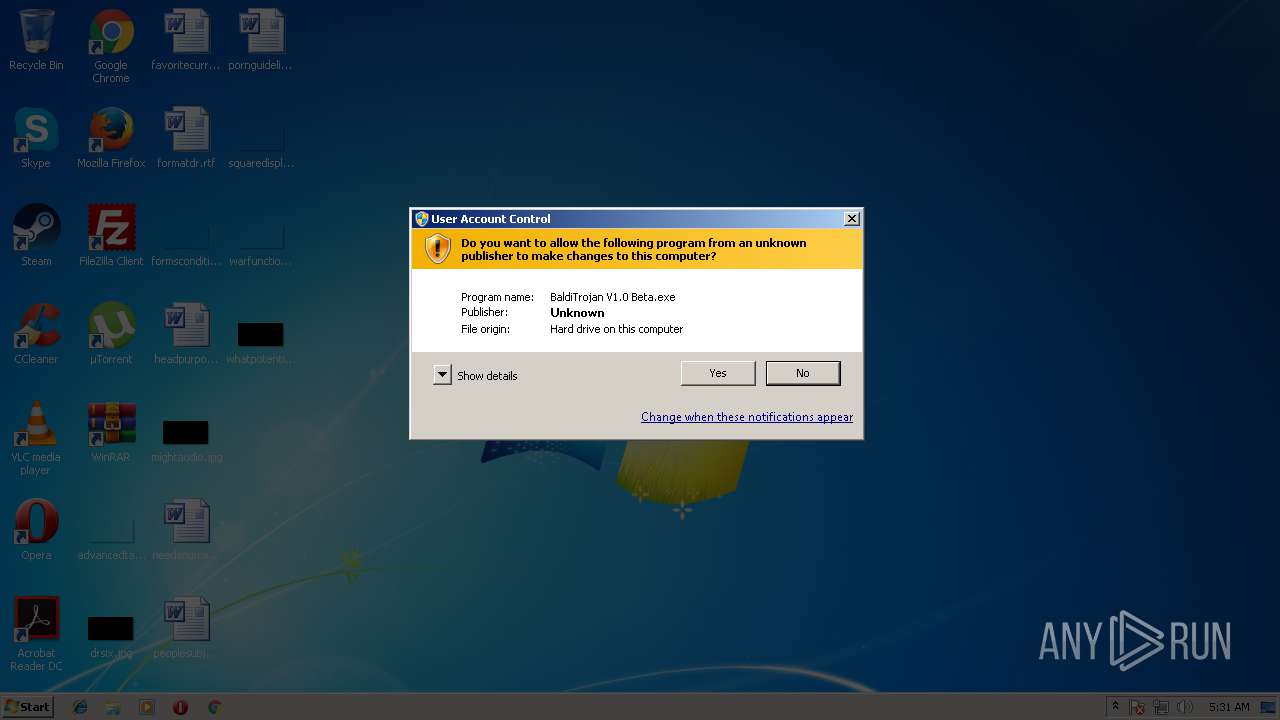
| File name: | BaldiTrojan V1.0 Beta.exe |
| Full analysis: | https://app.any.run/tasks/1aec54a5-bd9b-4d5f-beeb-968c8cd8e376 |
| Verdict: | Suspicious activity |
| Analysis date: | August 23, 2018, 04:31:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 735745A952473FAF5306551A24C95050 |
| SHA1: | 33033EAFC110A7FBFF26BE5B12E756564ECA032B |
| SHA256: | B9856DE14002BAFEC77DD5337E2DE2CC95CE795EDC2A4A0A00F055D438F3ABD8 |
| SSDEEP: | 12288:6vuX/f3+Fso9uLSTG7B9+TdVUOzUUOyCE1T9W:TX3+9mqG7L+xV99h31k |
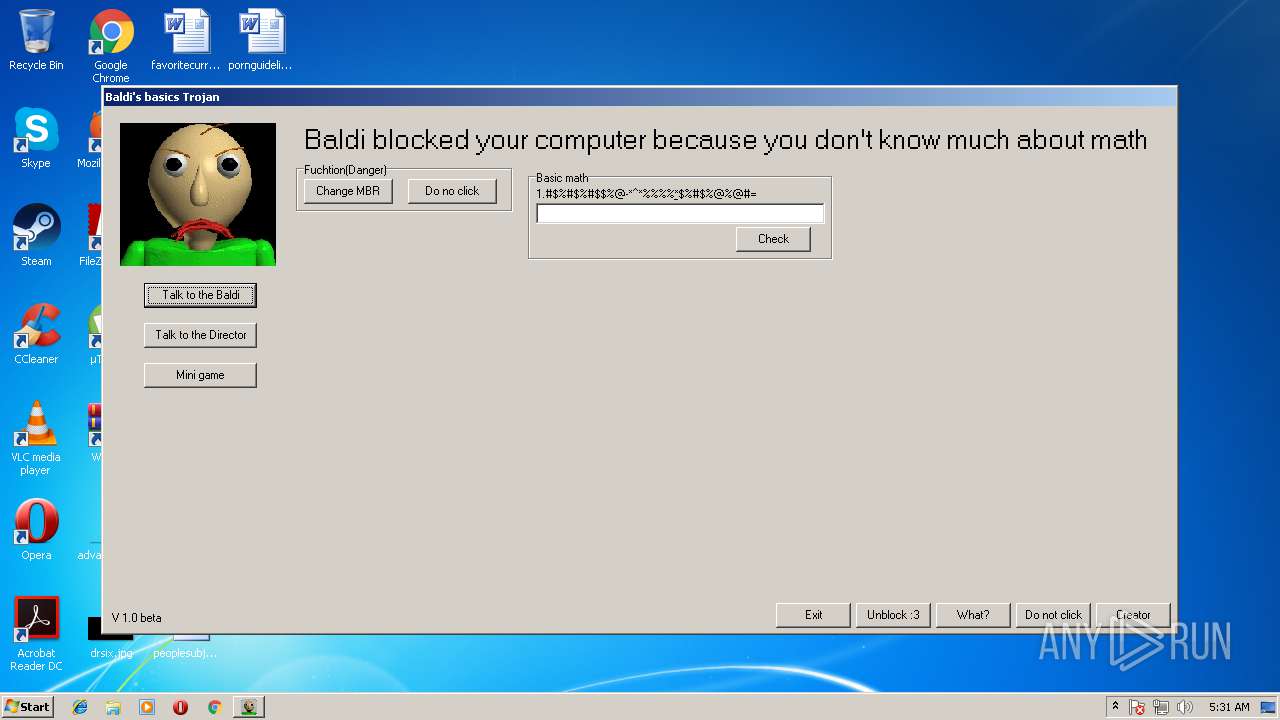
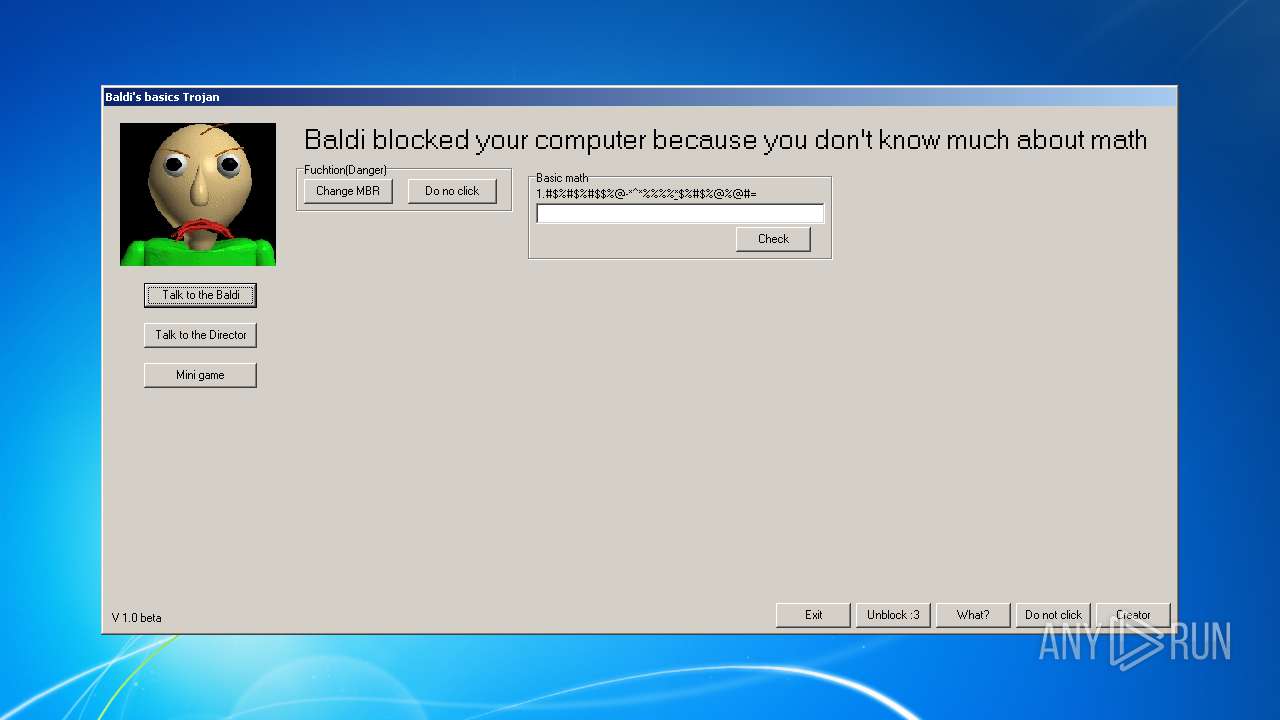
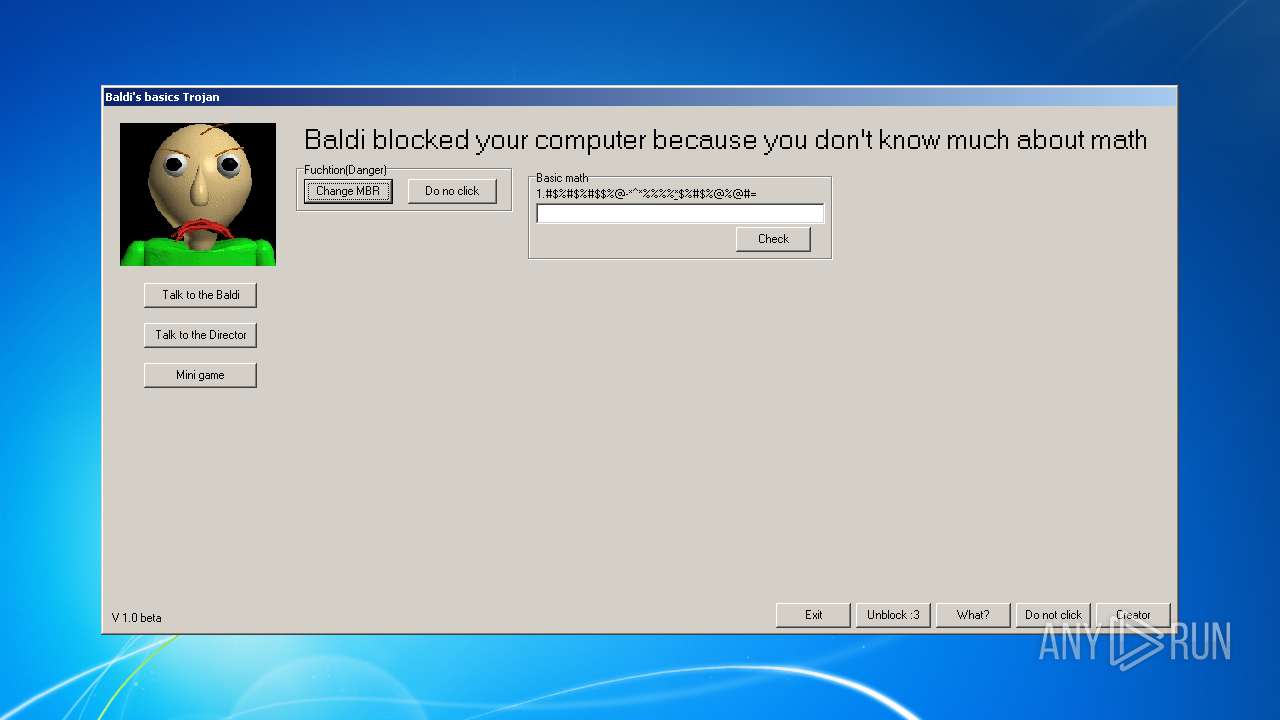
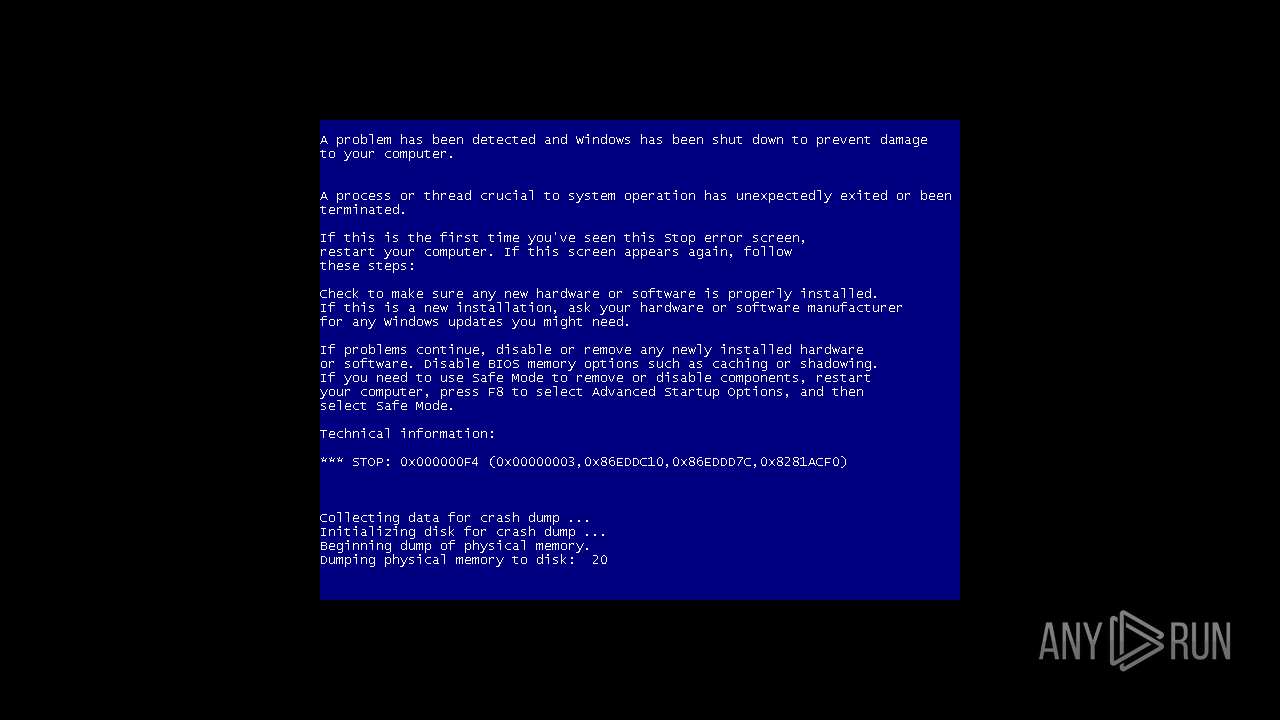
MALICIOUS
Task Manager has been disabled (taskmgr)
- Baldi.exe (PID: 3168)
Changes the autorun value in the registry
- Baldi.exe (PID: 3168)
Application was dropped or rewritten from another process
- Baldi.exe (PID: 3168)
SUSPICIOUS
Executable content was dropped or overwritten
- BaldiTrojan V1.0 Beta.exe (PID: 1464)
Creates files in the program directory
- BaldiTrojan V1.0 Beta.exe (PID: 1464)
Starts CMD.EXE for commands execution
- BaldiTrojan V1.0 Beta.exe (PID: 1464)
Uses TASKKILL.EXE to kill process
- Baldi.exe (PID: 3168)
INFO
Dropped object may contain URL's
- BaldiTrojan V1.0 Beta.exe (PID: 1464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | DSGame |
| FileDescription: | Clean your PC |
| FileVersion: | 1.0.0.0 |
| Info: | Данный пакет был создан с помощью SFX Creator |
| LegalCopyright: | DSGame |
| ProductName: | CleanZ |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:41 |
| Detected languages: |
|
| CompanyName: | DSGame |
| FileDescription: | Clean your PC |
| FileVersion: | 1.0.0.0 |
| Info: | Данный пакет был создан с помощью SFX Creator |
| LegalCopyright: | DSGame |
| ProductName: | CleanZ |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002E000 | 0x00004898 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.20945 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.51738 | 592 | UNKNOWN | Russian - Russia | RT_VERSION |
5 | 3.20086 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
44
Monitored processes
5
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | cmd /c CleanZUpdater.bat | C:\Windows\system32\cmd.exe | — | BaldiTrojan V1.0 Beta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\Desktop\BaldiTrojan V1.0 Beta.exe" | C:\Users\admin\Desktop\BaldiTrojan V1.0 Beta.exe | explorer.exe | ||||||||||||
User: admin Company: DSGame Integrity Level: HIGH Description: Clean your PC Exit code: 2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1952 | "C:\Windows\System32\taskkill.exe" /f /im explorer.exe | C:\Windows\System32\taskkill.exe | — | Baldi.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3168 | C:\Baldi\Baldi.exe | C:\Baldi\Baldi.exe | cmd.exe | ||||||||||||
User: admin Company: DSINC Integrity Level: HIGH Description: Baldi evil... Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3644 | "C:\Users\admin\Desktop\BaldiTrojan V1.0 Beta.exe" | C:\Users\admin\Desktop\BaldiTrojan V1.0 Beta.exe | — | explorer.exe | |||||||||||
User: admin Company: DSGame Integrity Level: MEDIUM Description: Clean your PC Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
99
Read events
91
Write events
8
Delete events
0
Modification events
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\softwaremicrosoftwindowscurrentversionpoliciesexplorer |
| Operation: | write | Name: | noclose |
Value: 1 | |||
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\softwaremicrosoftwindowscurrentversionpoliciesexplorer |
| Operation: | write | Name: | nologoff |
Value: 1 | |||
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableTaskMgr |
Value: 1 | |||
| (PID) Process: | (3168) Baldi.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GG.exe |
Value: C:\Baldi\Baldi.exe | |||
Executable files
4
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Users\admin\AppData\Local\Temp\nsh70CA.tmp\ExecDos.dll | — | |
MD5:— | SHA256:— | |||
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Baldi\kill.exe | executable | |
MD5:58F681015149CE6C120E5B9F55761D2C | SHA256:C09D5F30C31A01A4E0F8EA829278D8D4E99A20E122EACD7648E5C9C605256290 | |||
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Baldi\Baldi.exe | executable | |
MD5:244F3207D60273F5E71A7AB4FCBAAA34 | SHA256:05474710A8A715FC3DAA05675CF9F492FD68ADA10FC8D9B22FE9A2981465641F | |||
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Baldi\DisableUAC.exe | executable | |
MD5:9AD923E0B582D7520DBD655C36C1CDD5 | SHA256:F5ADD589DA4BFB1492531306D12E84EF27BFCB0C31FF51FED710215765AC95F4 | |||
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Baldi\mbr.exe | executable | |
MD5:74E58B34423DDF2A72789D9927C5578D | SHA256:28DEDDCA10A4D9081BDF3BAB9E7E66A53B5DE493B062B1FD124BDF41F386AED1 | |||
| 1464 | BaldiTrojan V1.0 Beta.exe | C:\Program Files\CleanZUpdater.bat | text | |
MD5:B54E64A1F0B58D09CF57D983D7BA7361 | SHA256:2683D451AB3423E25BCBECA902E6B586D0D9E8689C9C1BB6DCA47BFAE547A7D7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report