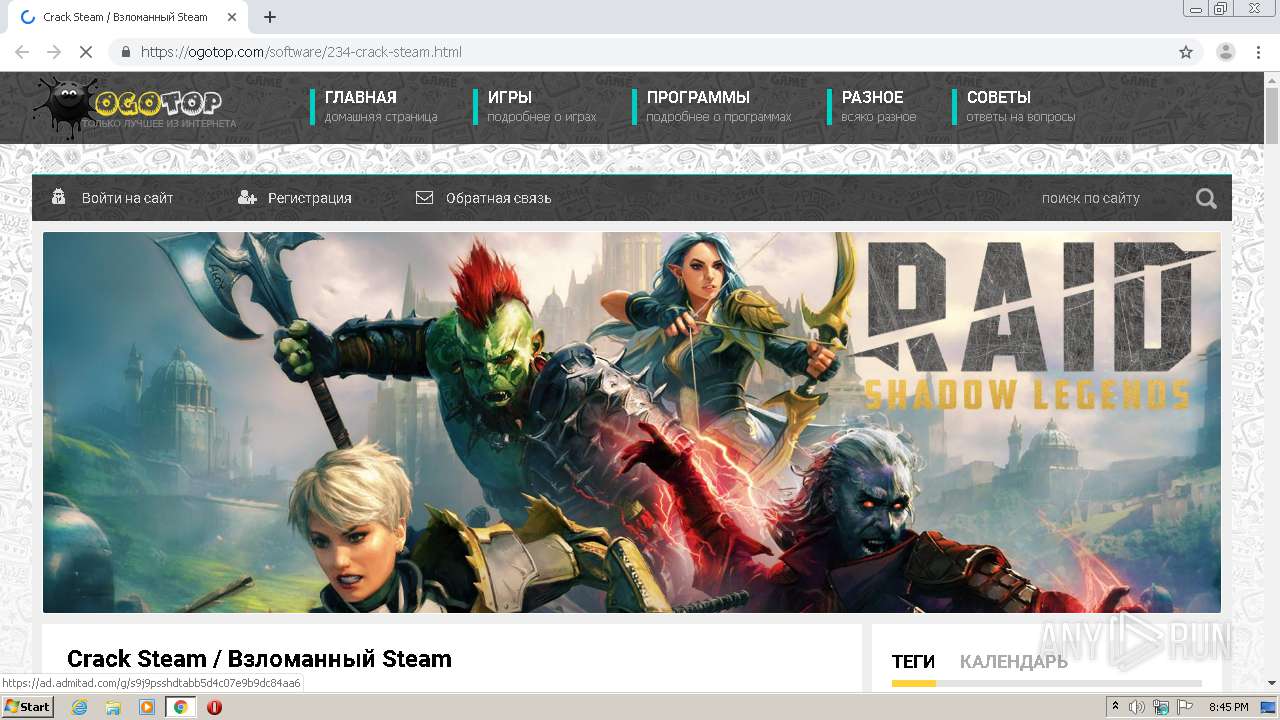
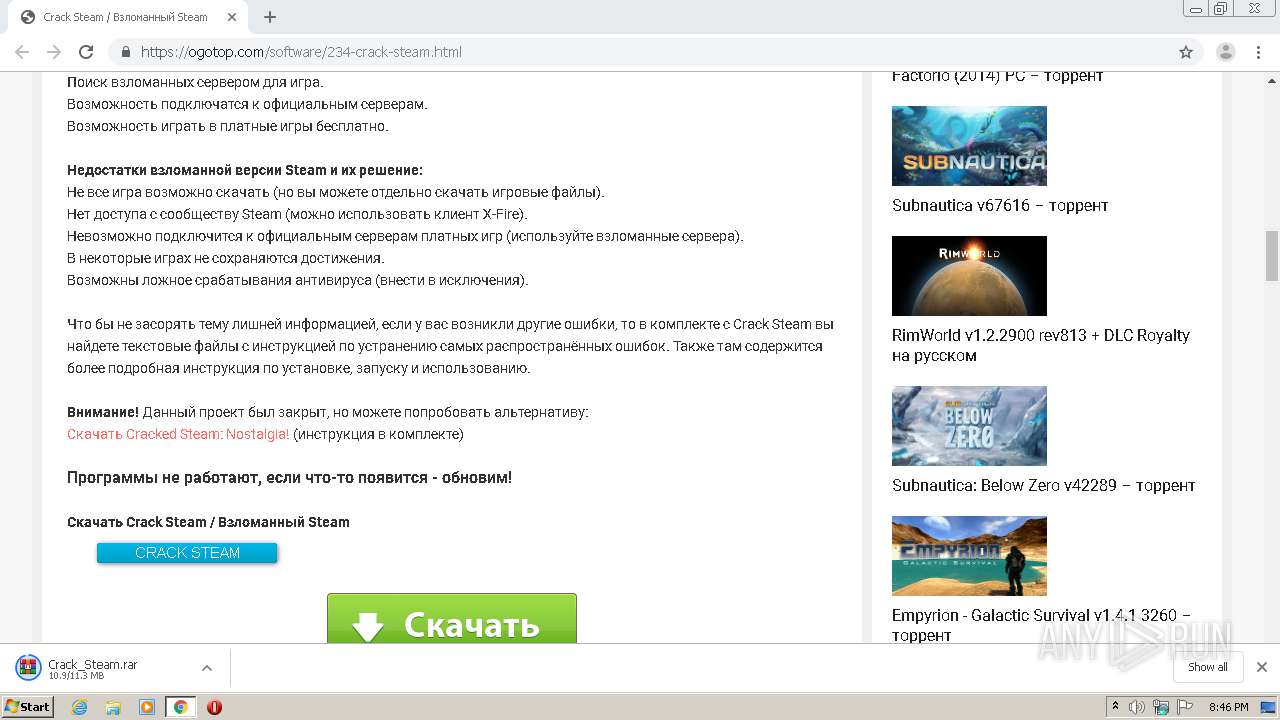
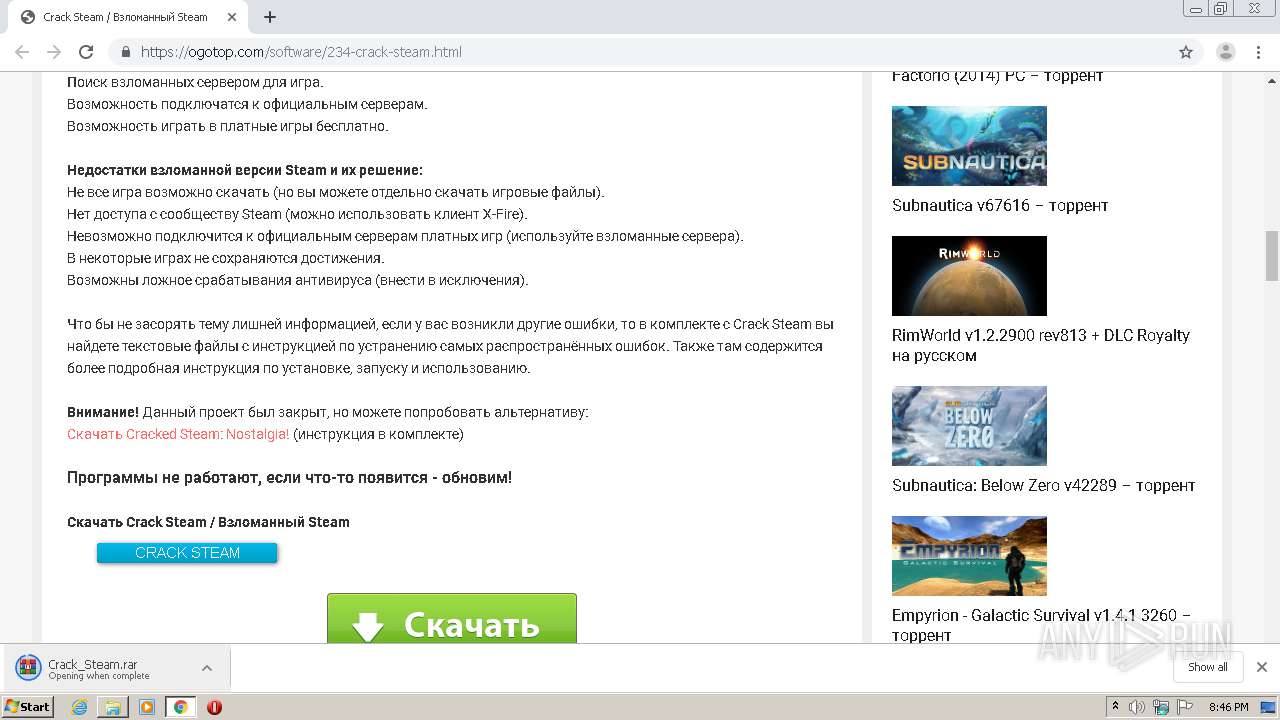
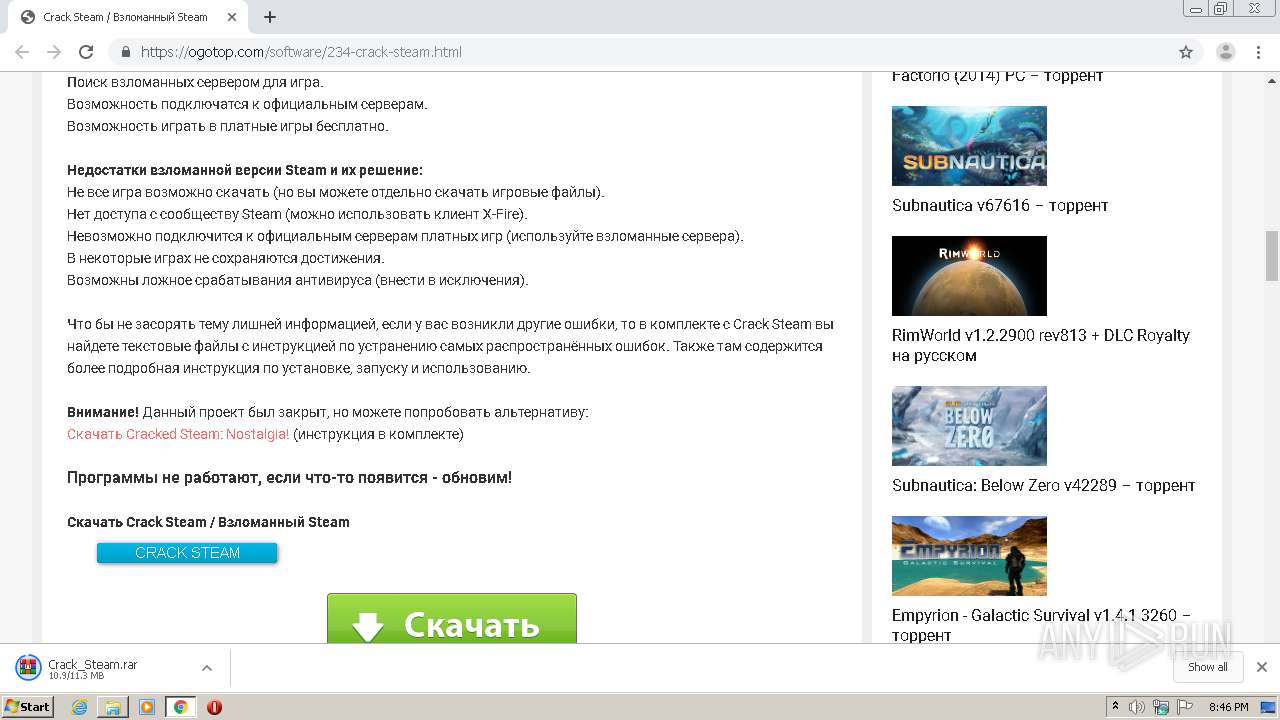
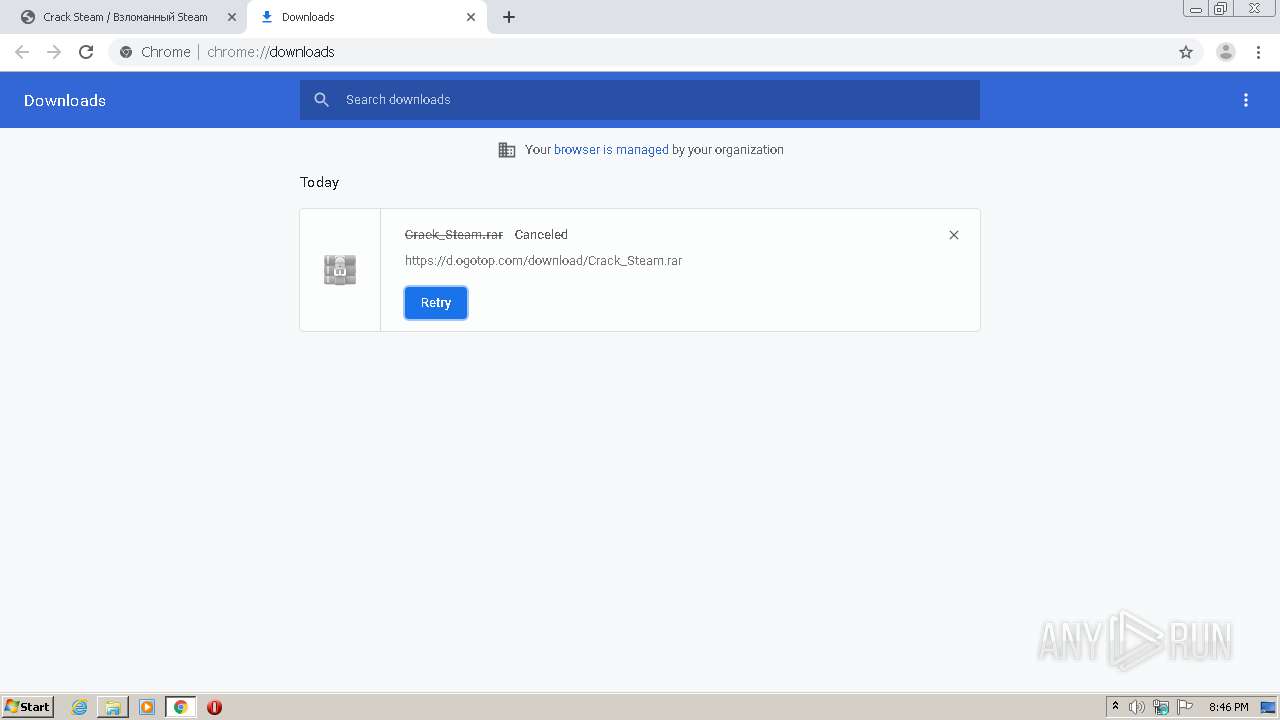
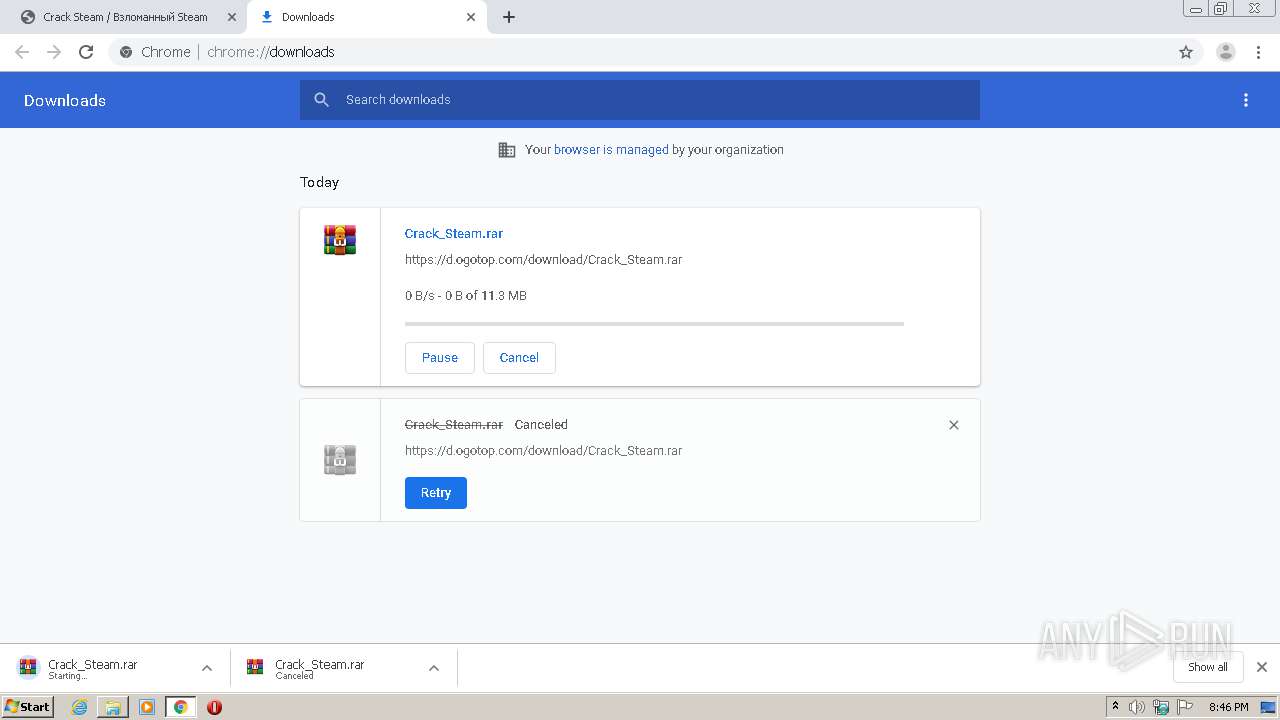
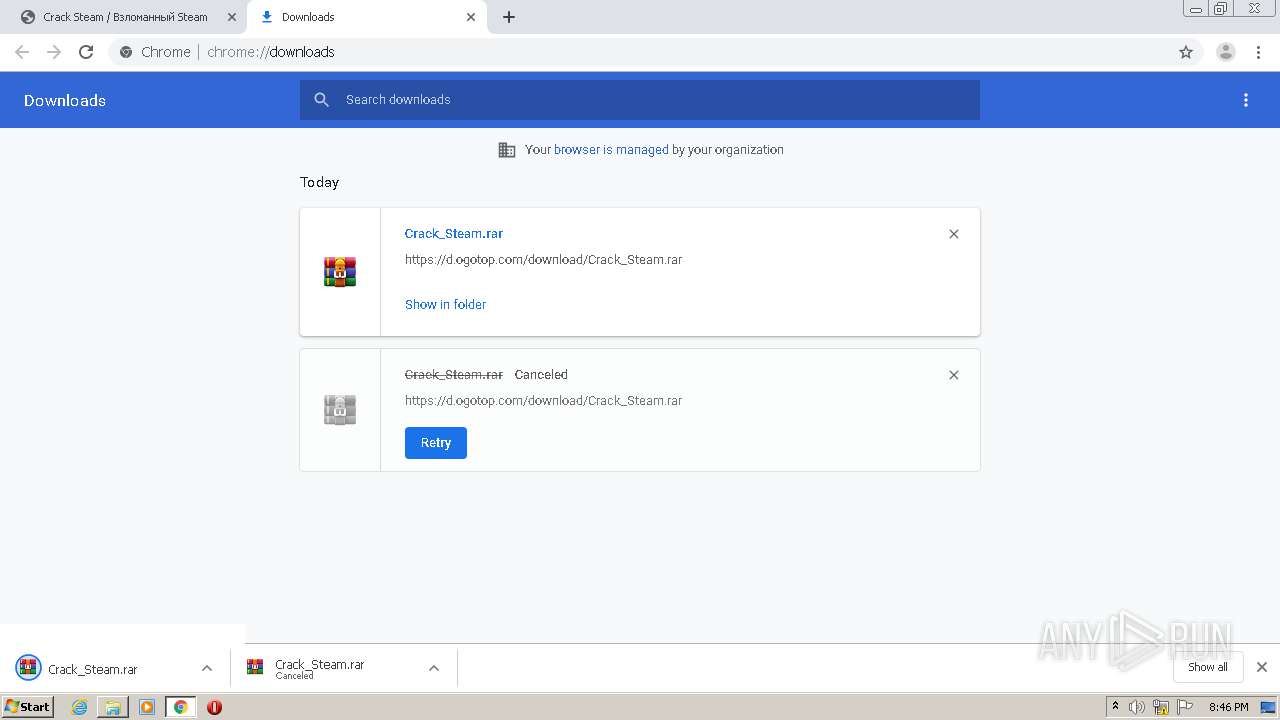
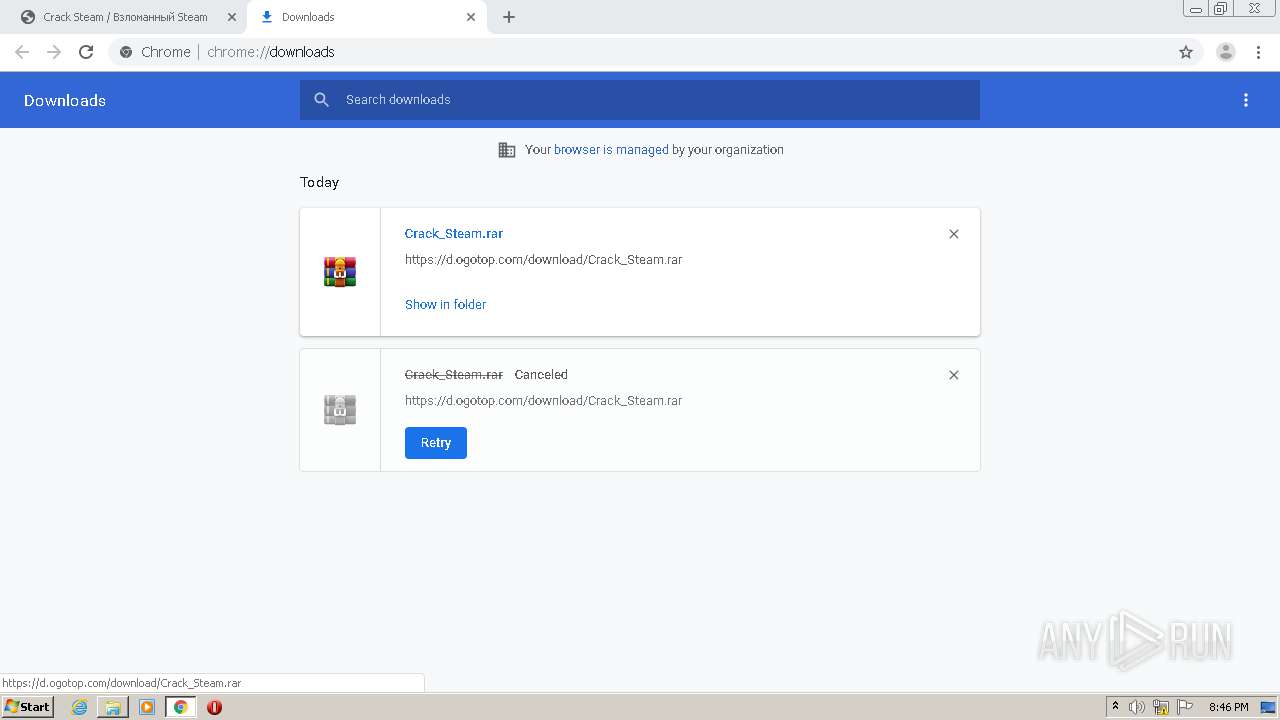
| URL: | https://ogotop.com/software/234-crack-steam.html |
| Full analysis: | https://app.any.run/tasks/417dfbb8-ab71-4d63-8e19-3d73415bf392 |
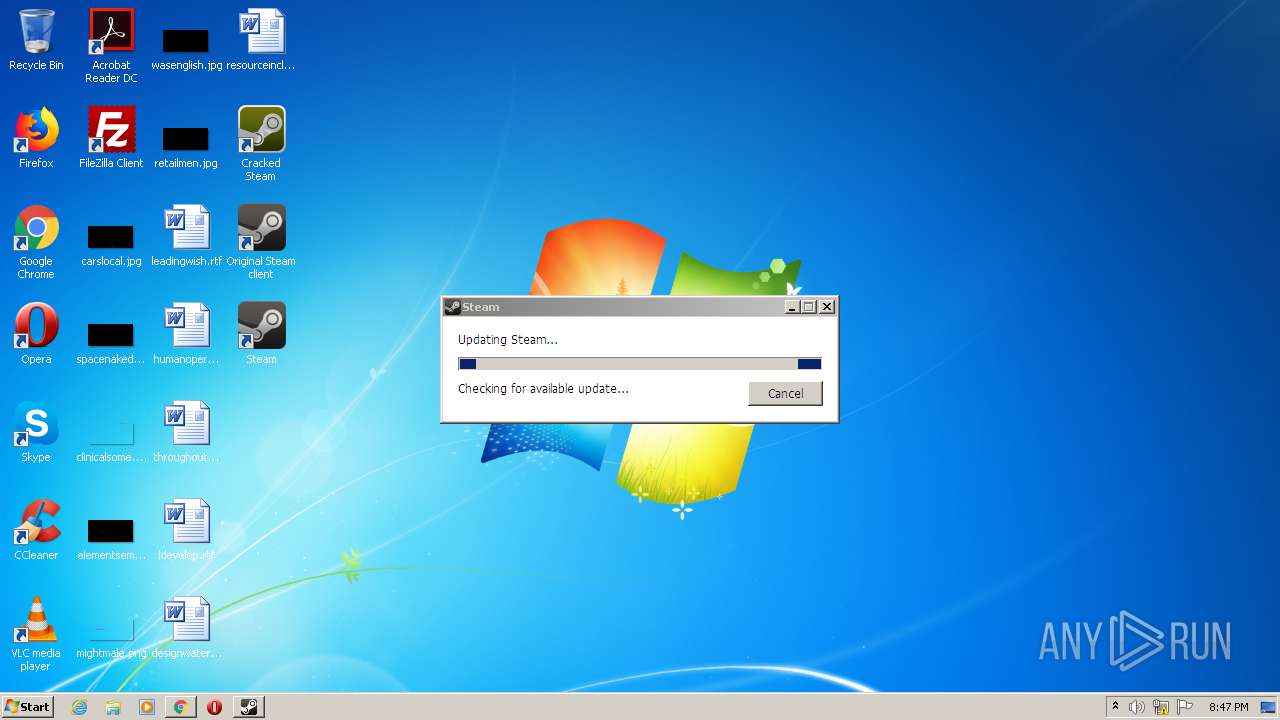
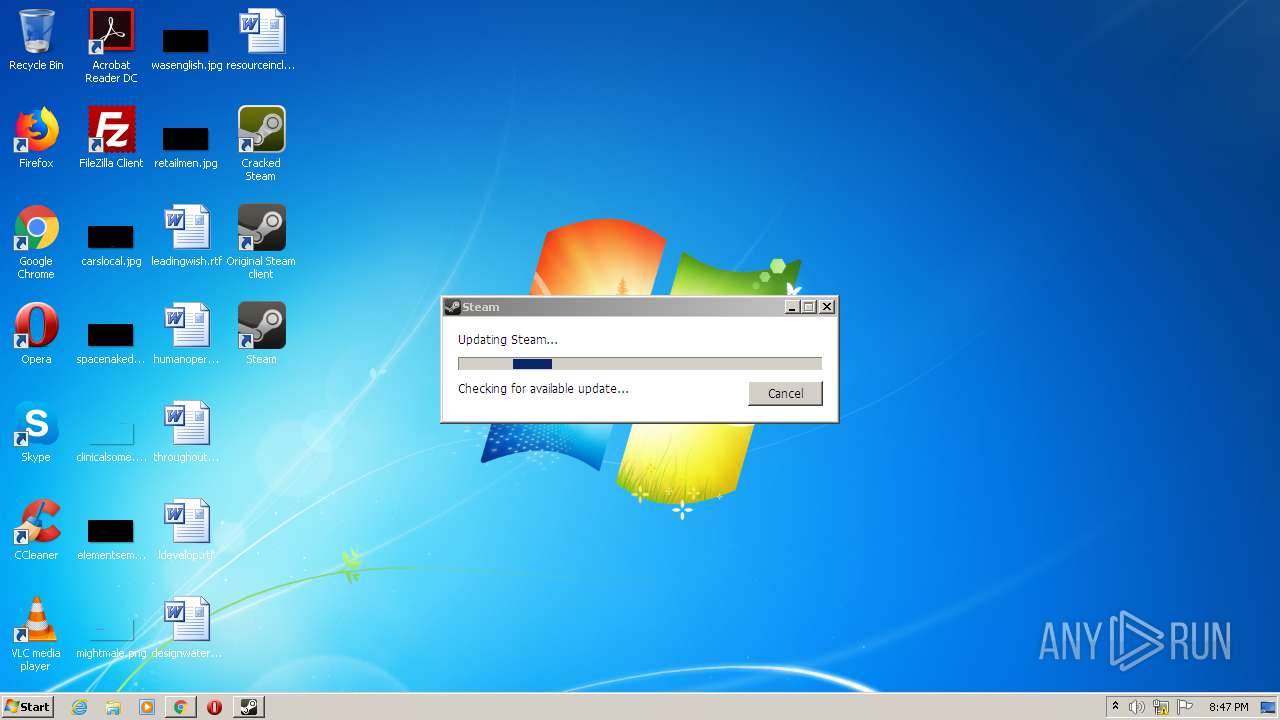
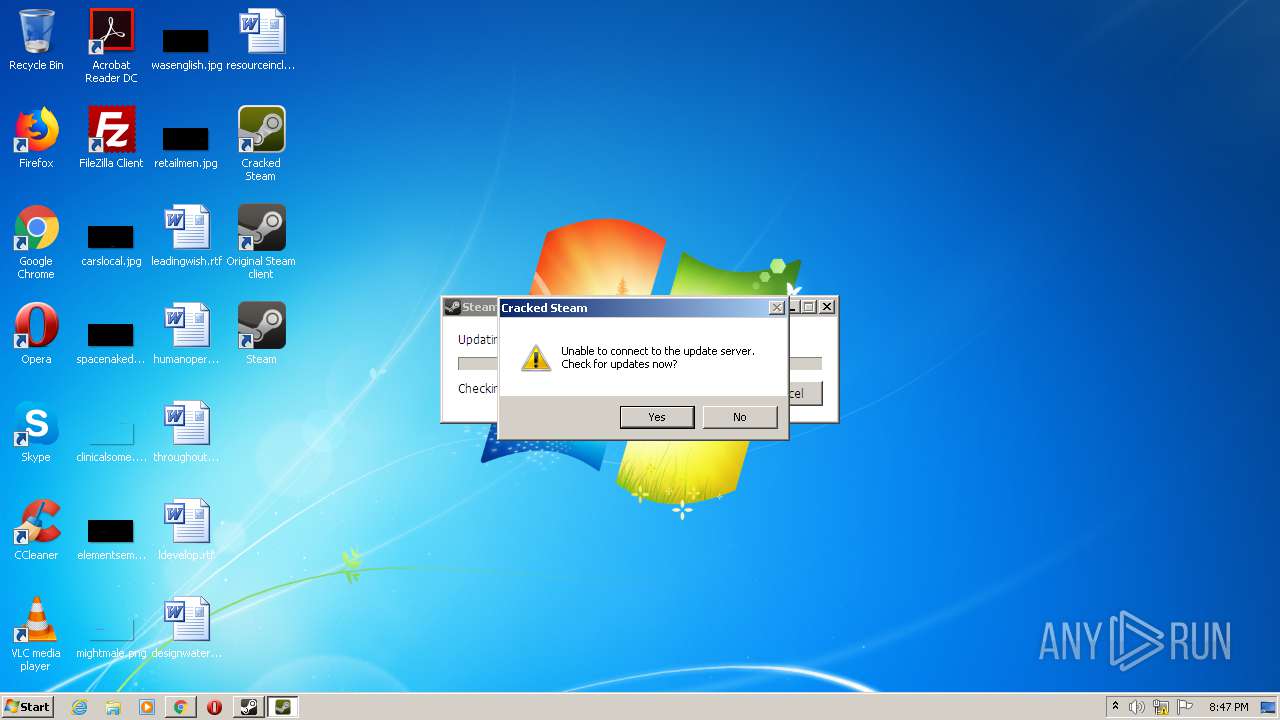
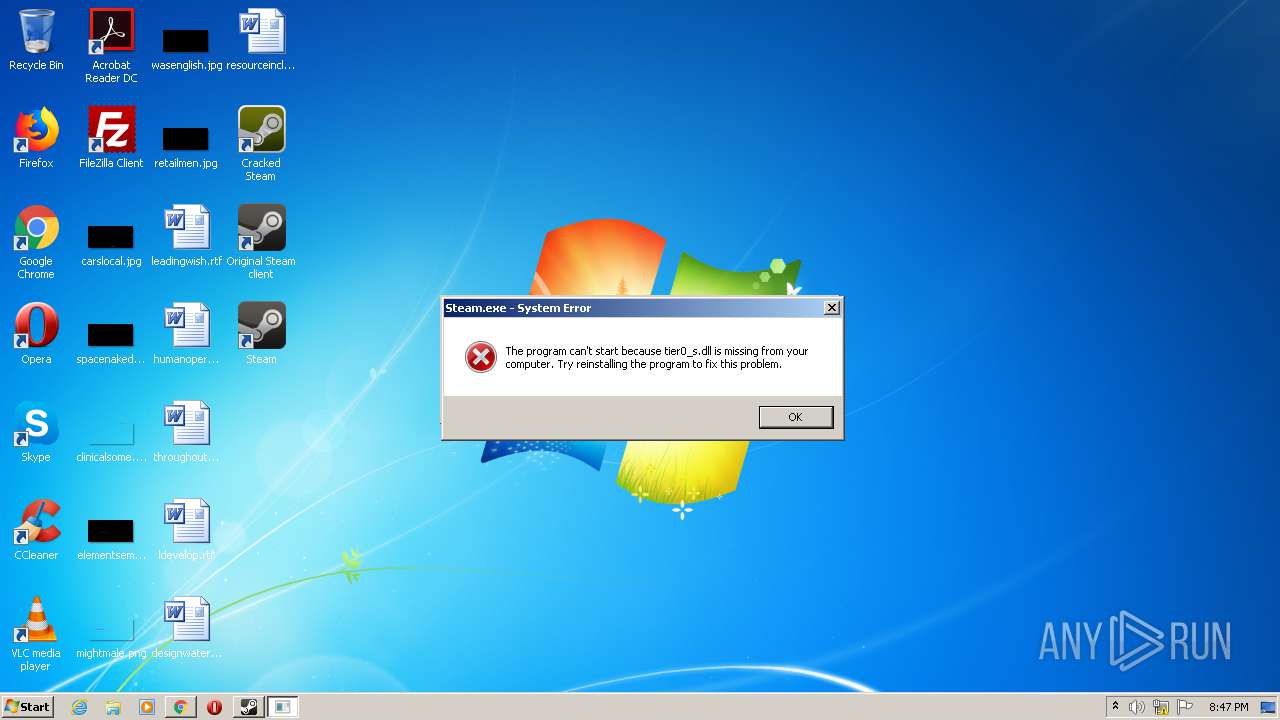
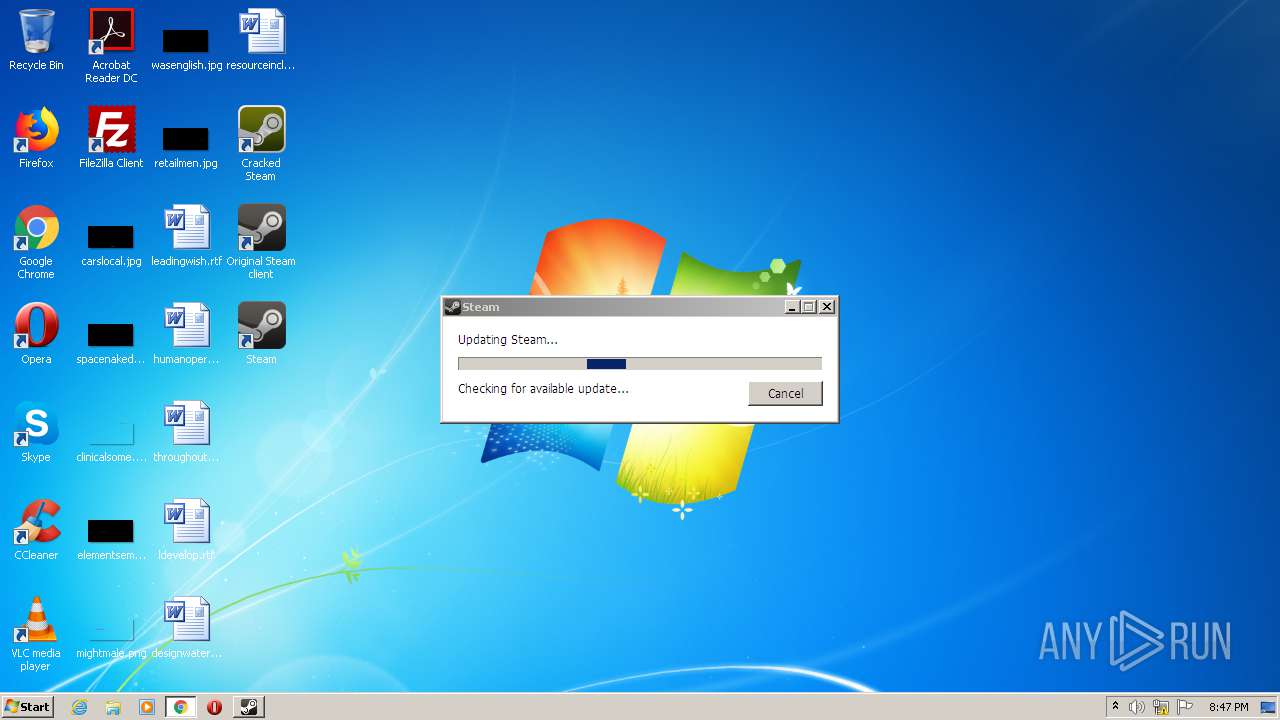
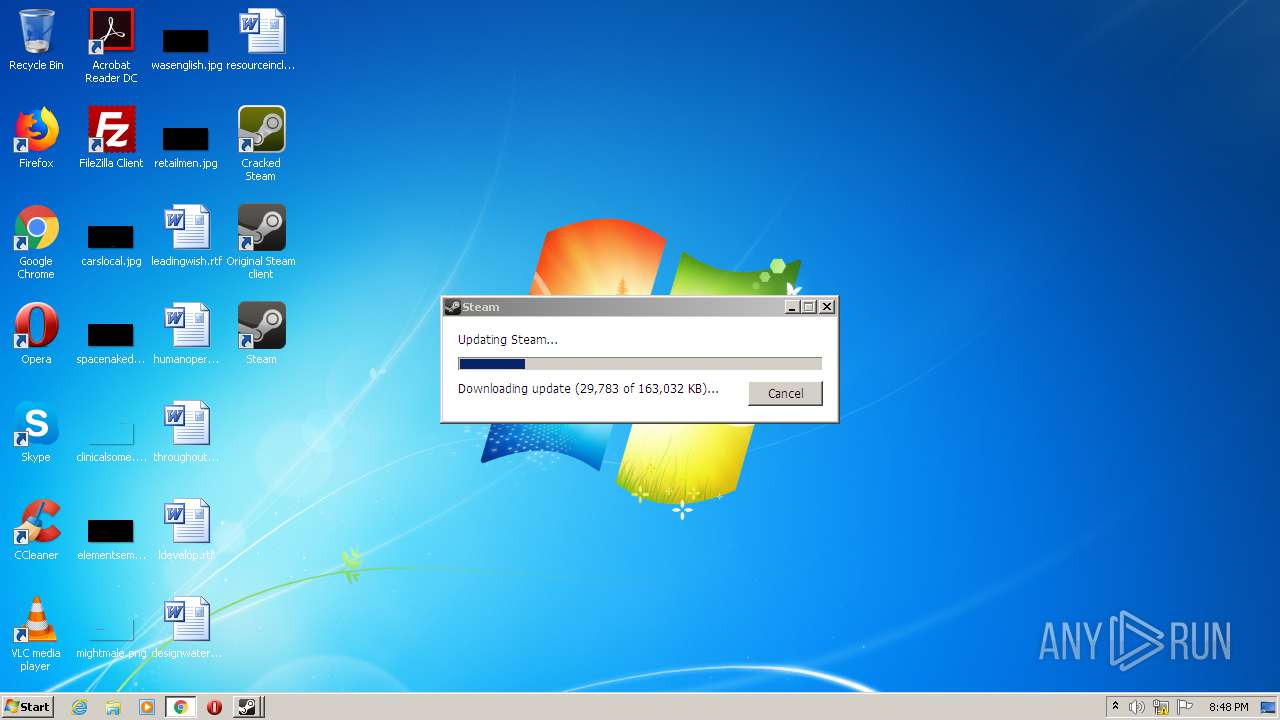
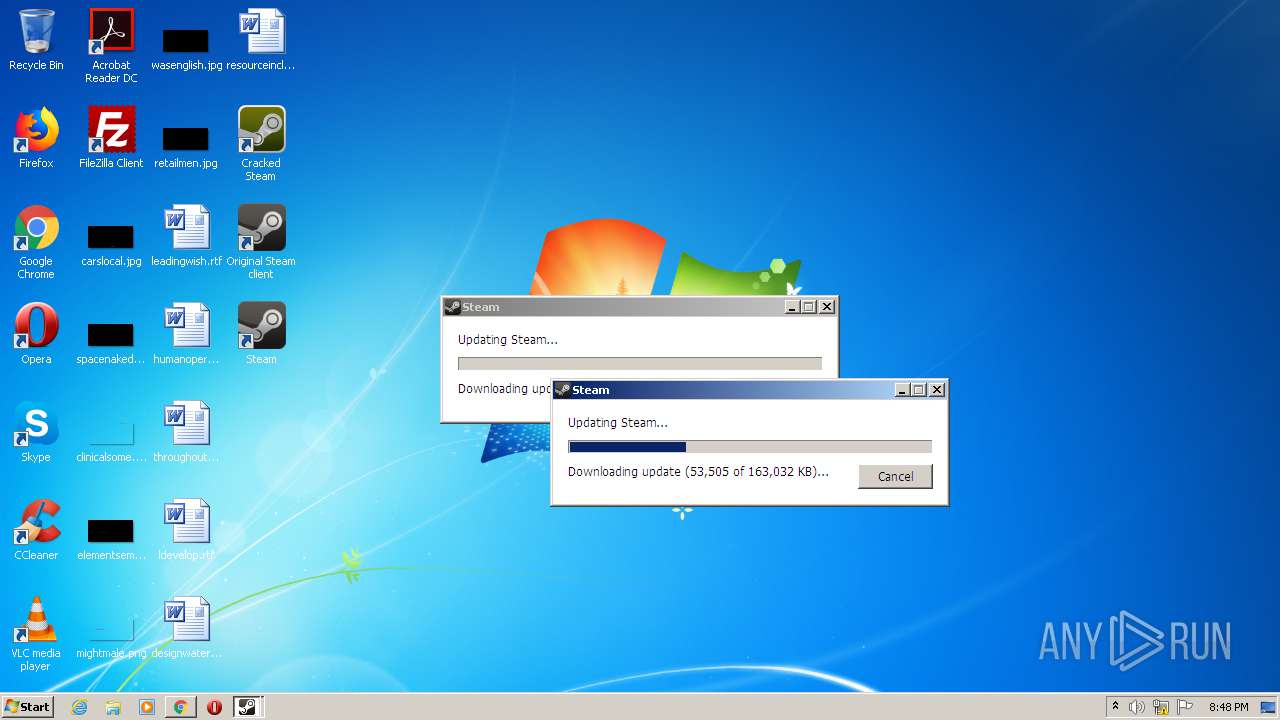
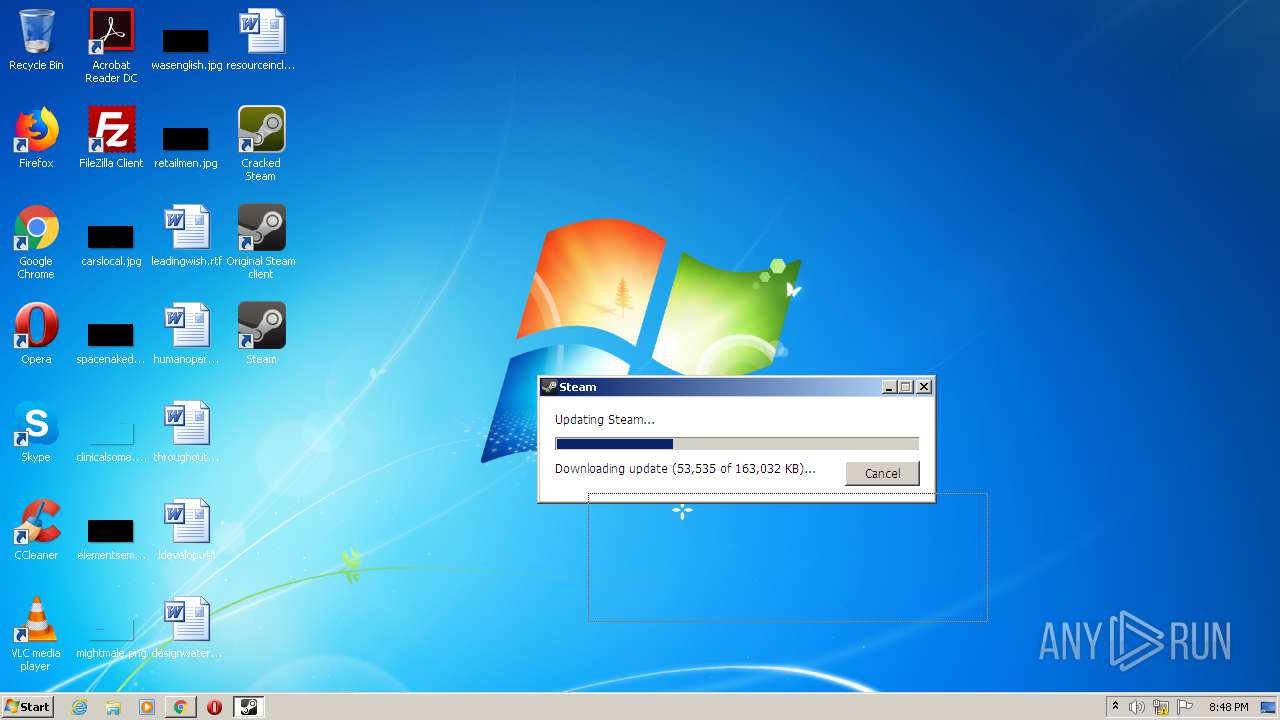
| Verdict: | Malicious activity |
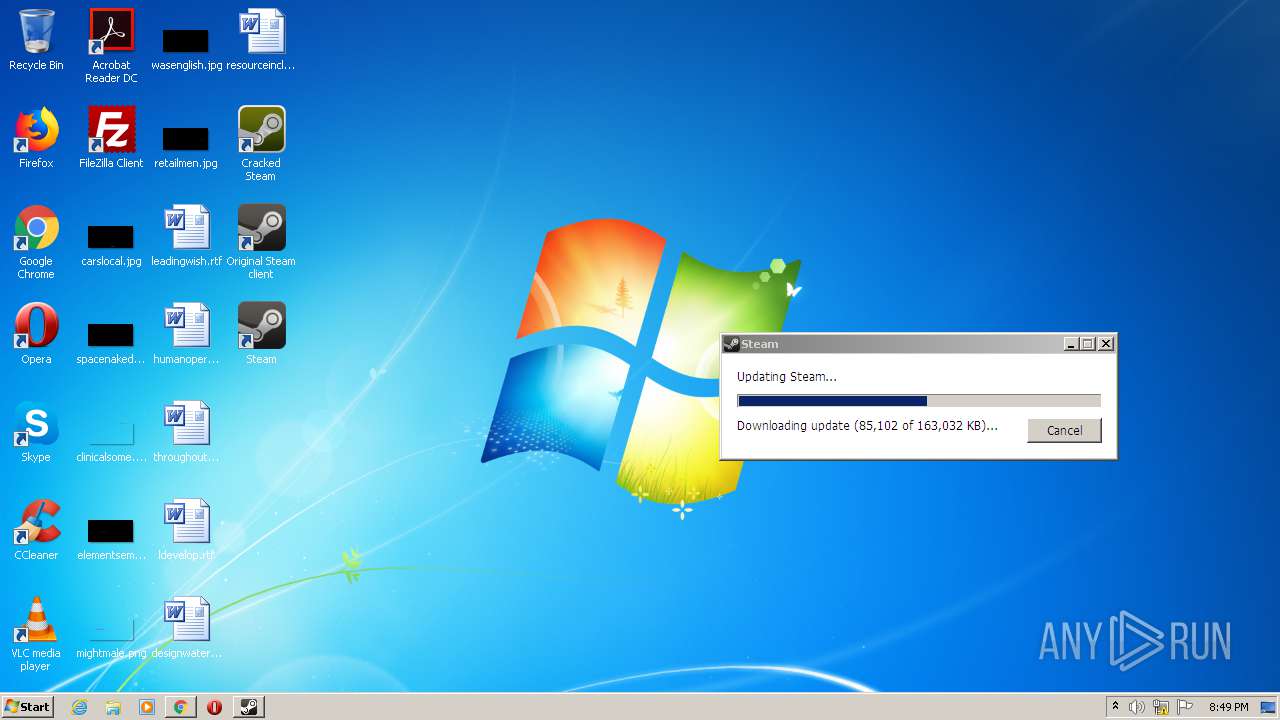
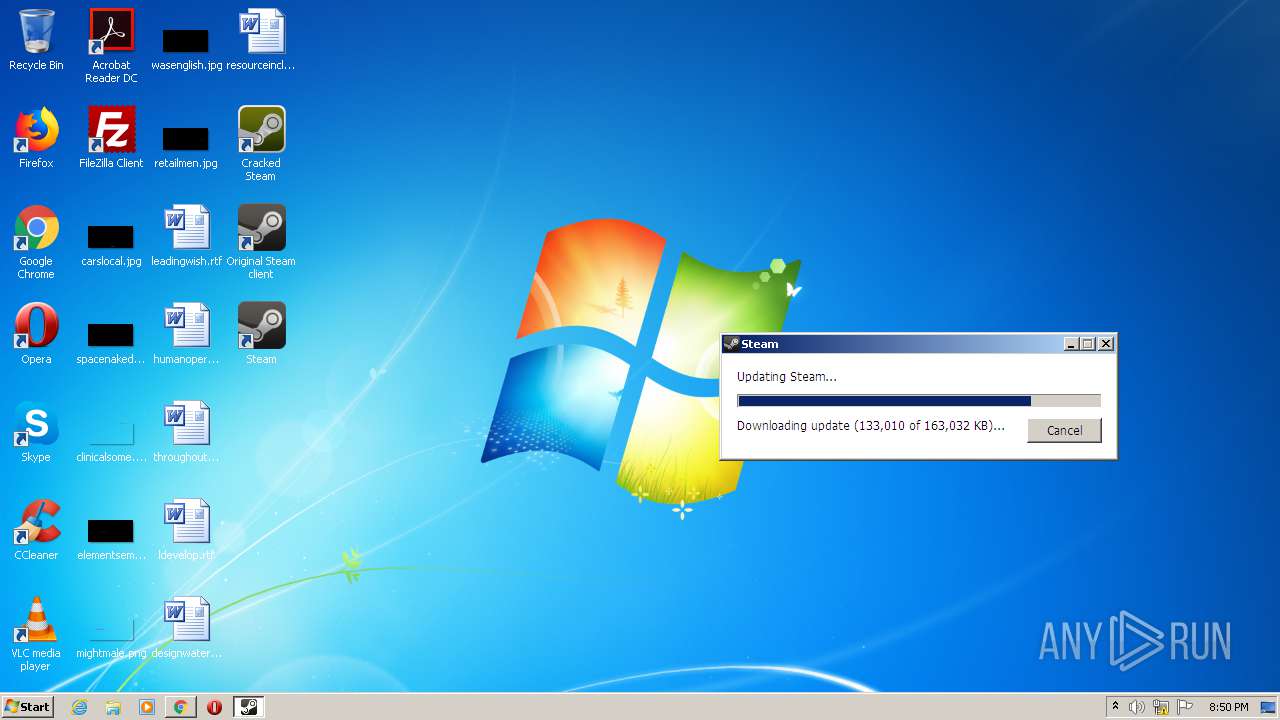
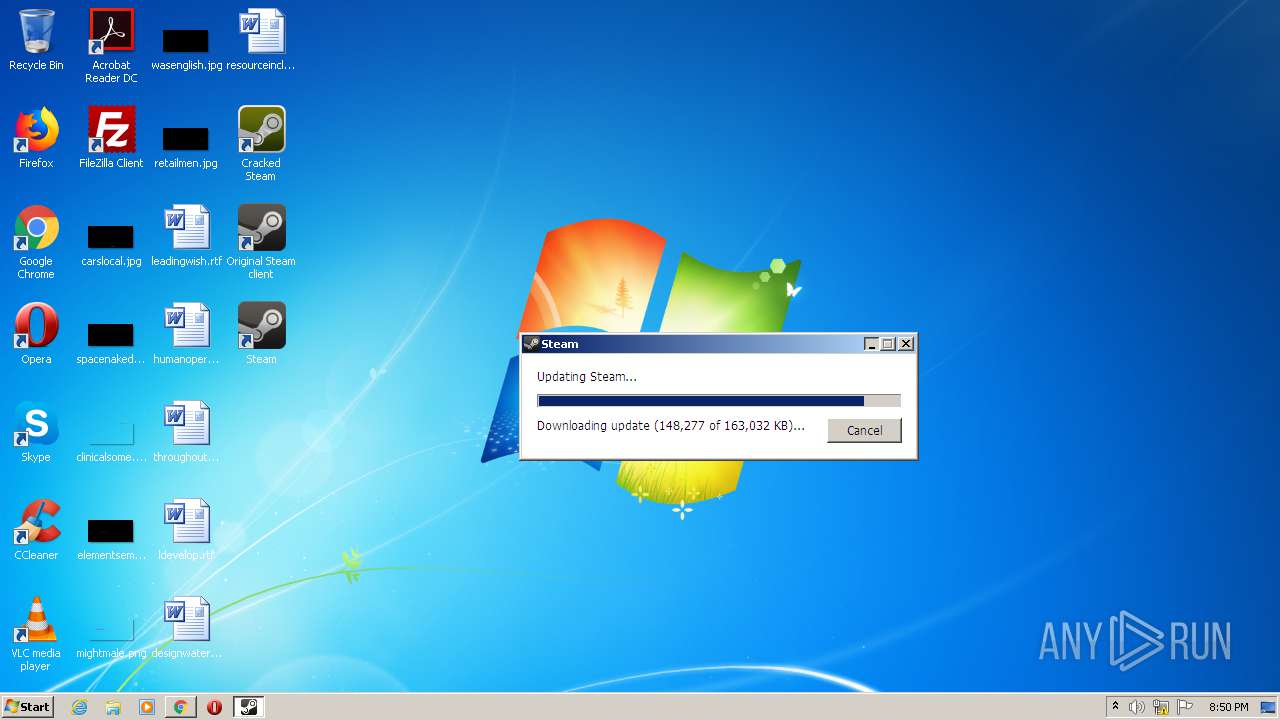
| Analysis date: | February 11, 2021, 20:45:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F6D93BD4601FD285E1D0E7F874925598 |
| SHA1: | EB0DB2DBFE3857E5F6449421F603B2608A1F3233 |
| SHA256: | B98400CAFFA31771C350CE35541CFC8300DE7BE9BCBC1139ECB6CCBE9A7F44AC |
| SSDEEP: | 3:N8LzyKIKNlWtvuJ:2vyTKetvG |
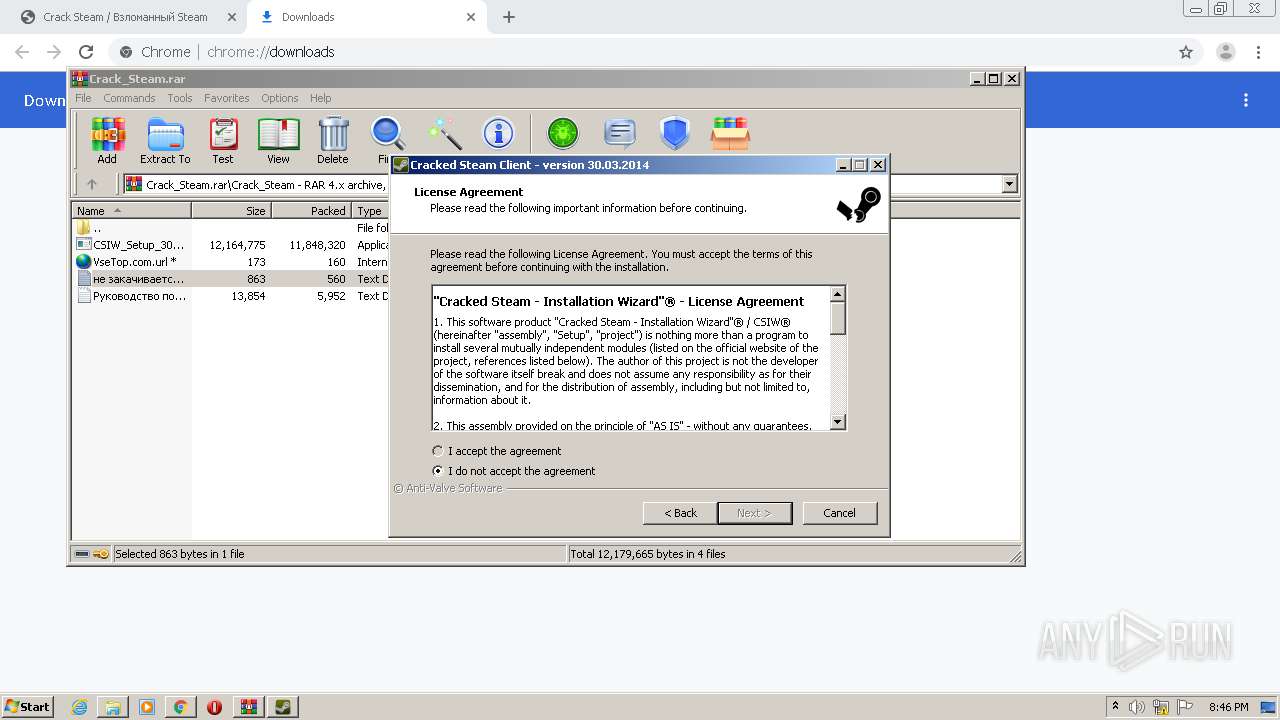
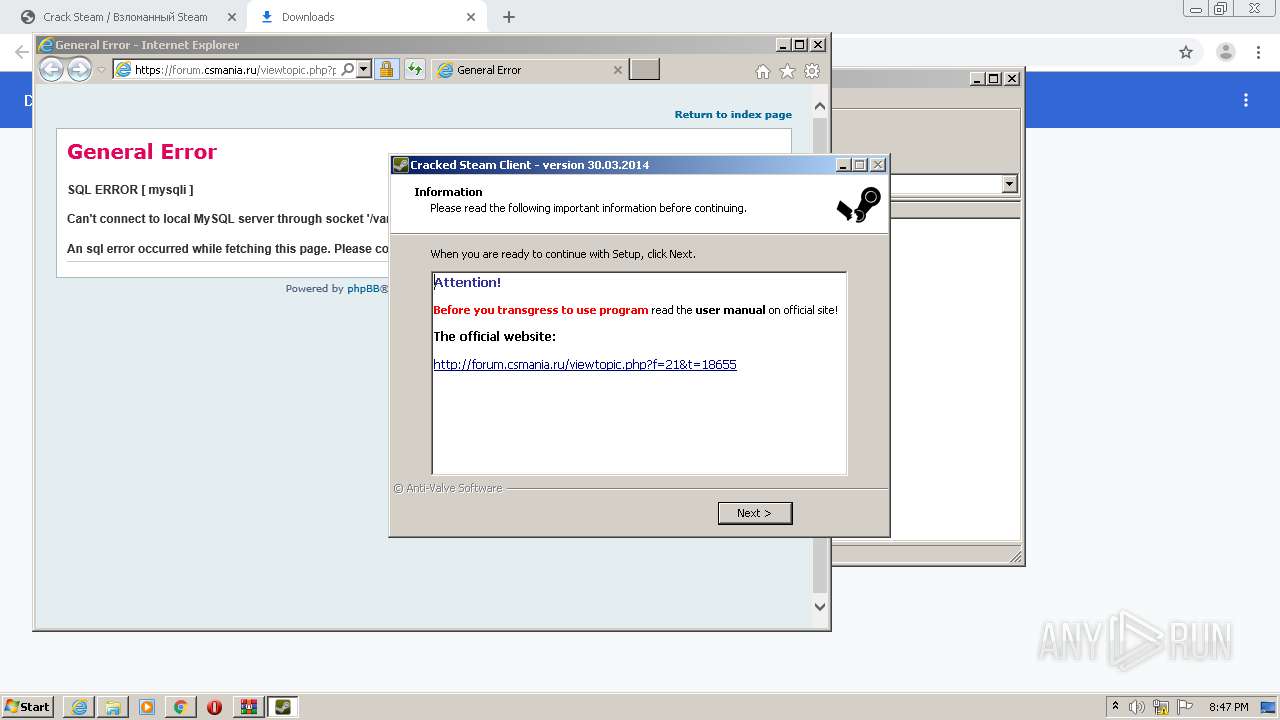
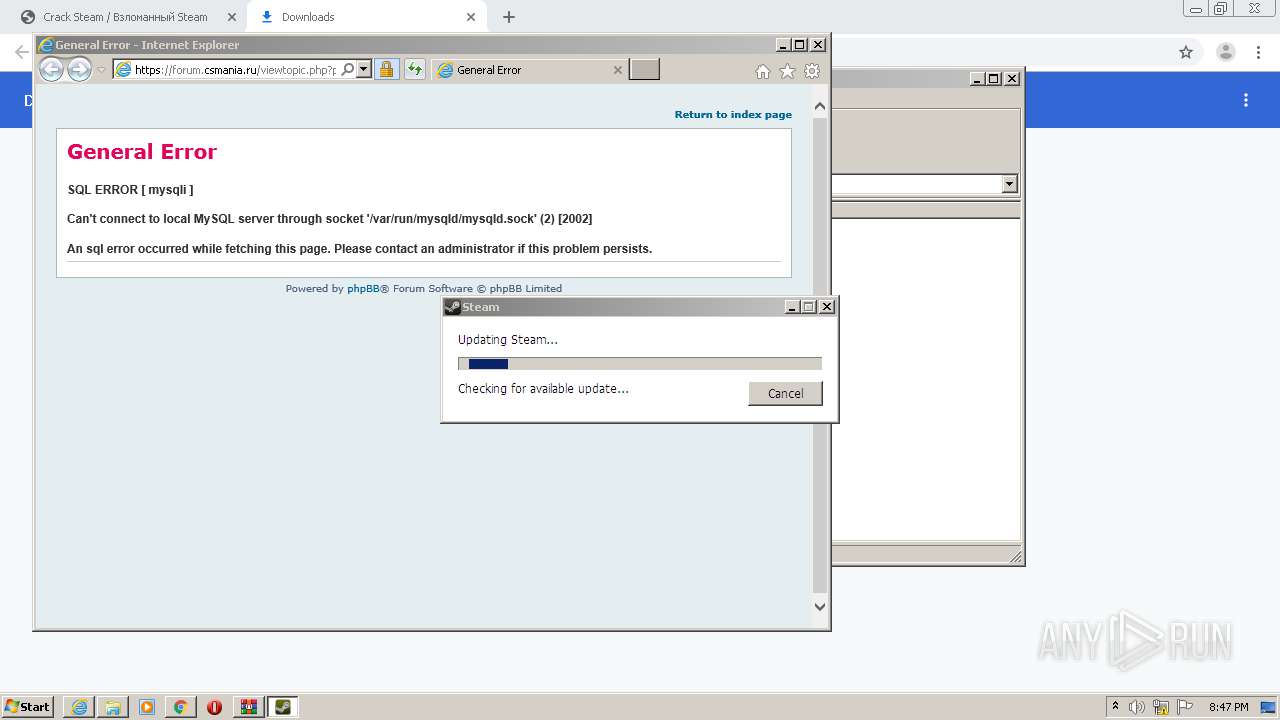
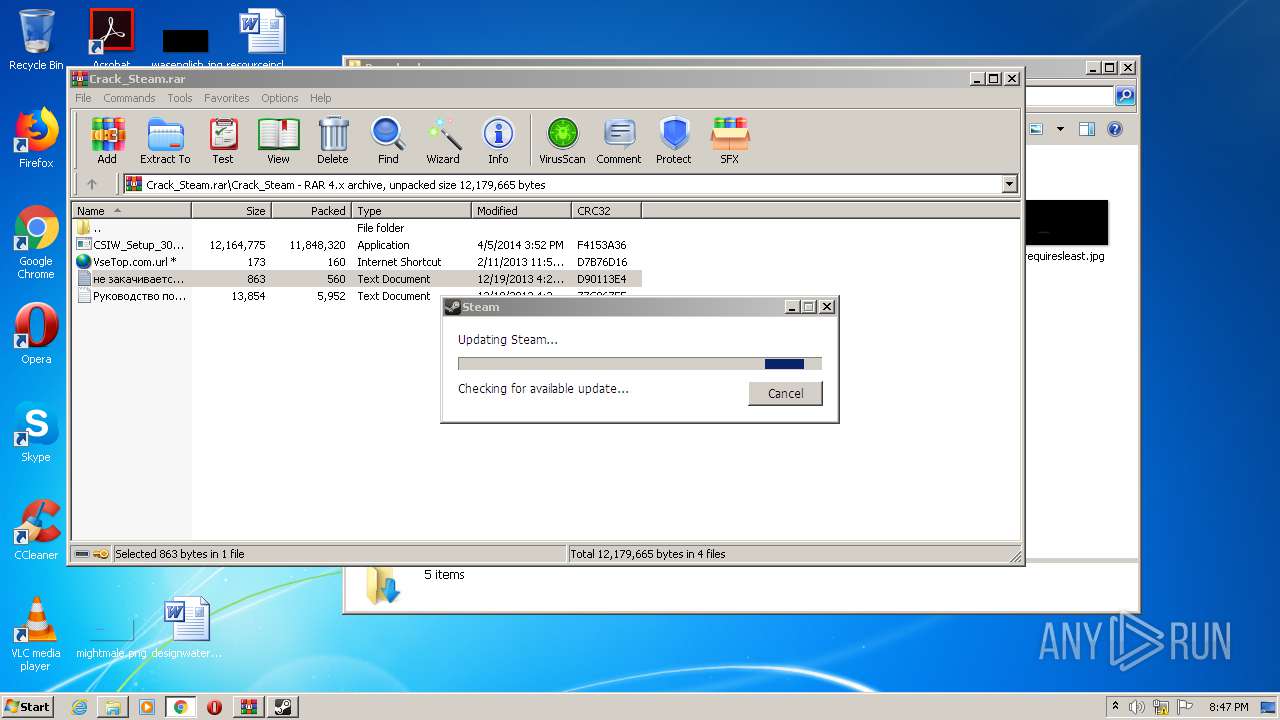
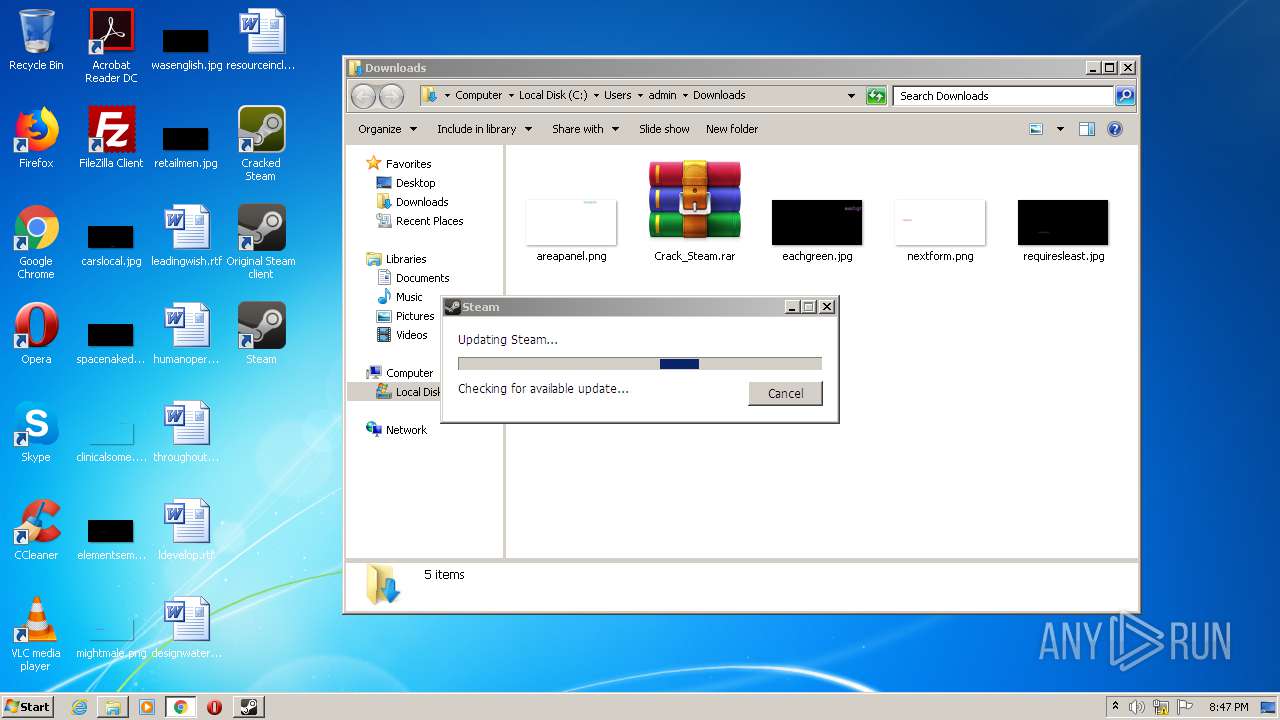
MALICIOUS
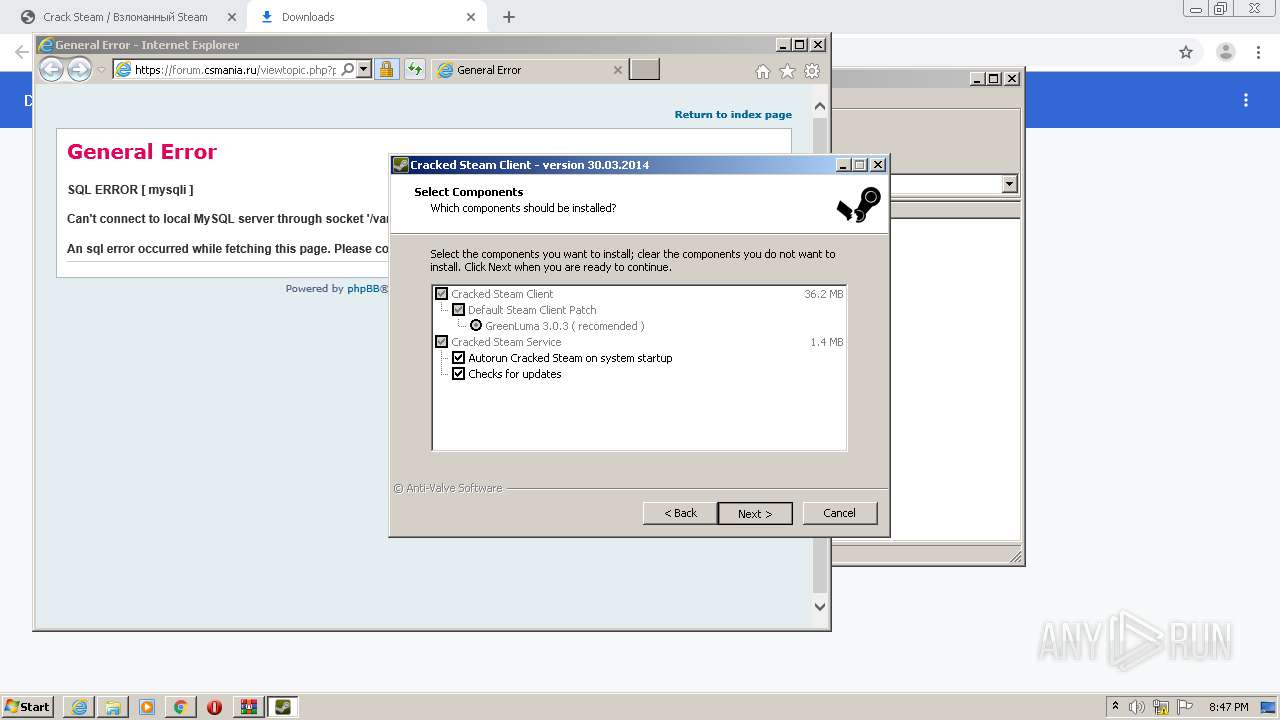
Application was dropped or rewritten from another process
- CSIW_Setup_30_March_2014.exe (PID: 1708)
- CSIW_Setup_30_March_2014.exe (PID: 2992)
- SteamService.exe (PID: 3012)
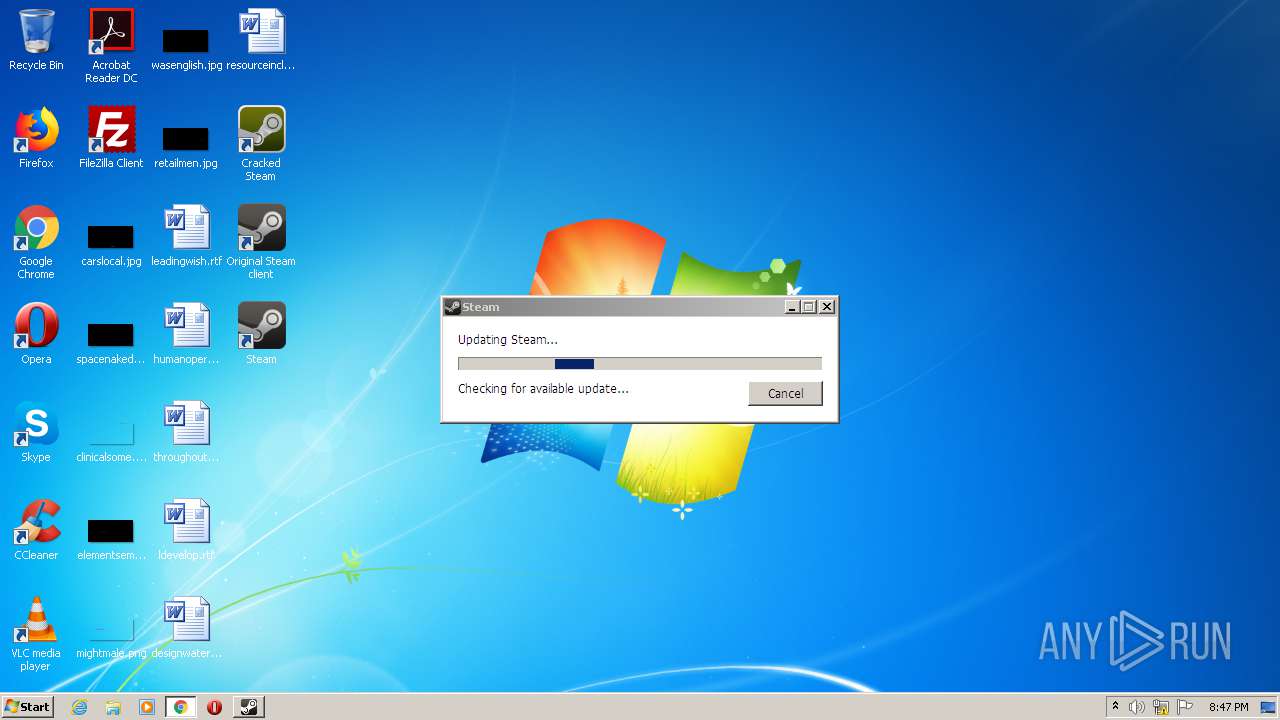
- Steam.exe (PID: 2092)
- Cracked Steam.exe (PID: 3452)
- wget.exe (PID: 3316)
- AntiSteam.exe (PID: 2888)
- Steam.exe (PID: 2668)
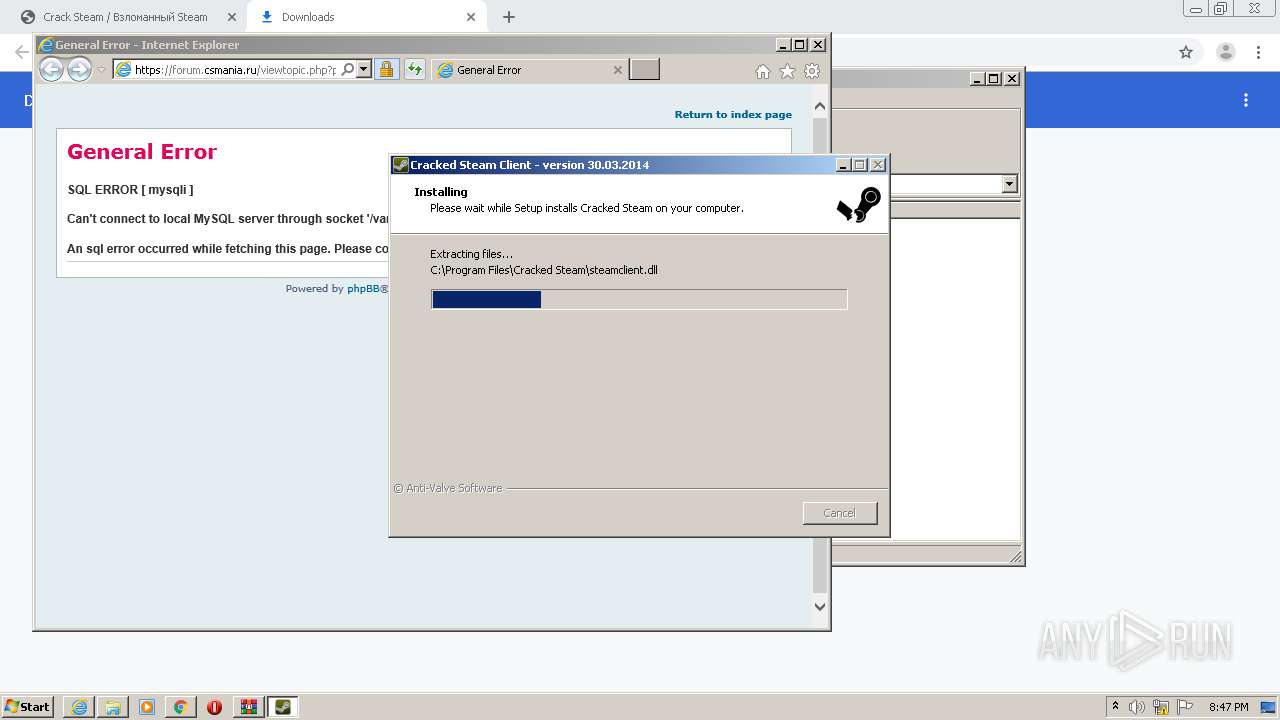
Drops executable file immediately after starts
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Cracked Steam.tmp (PID: 532)
Changes the autorun value in the registry
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Cracked Steam.tmp (PID: 532)
Loads dropped or rewritten executable
- AntiSteam.exe (PID: 2888)
- Steam.exe (PID: 2668)
SUSPICIOUS
Drops a file with too old compile date
- WinRAR.exe (PID: 1308)
- CSIW_Setup_30_March_2014.exe (PID: 2992)
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- CSIW_Setup_30_March_2014.exe (PID: 1708)
- Cracked Steam.exe (PID: 3452)
- Cracked Steam.tmp (PID: 532)
Executable content was dropped or overwritten
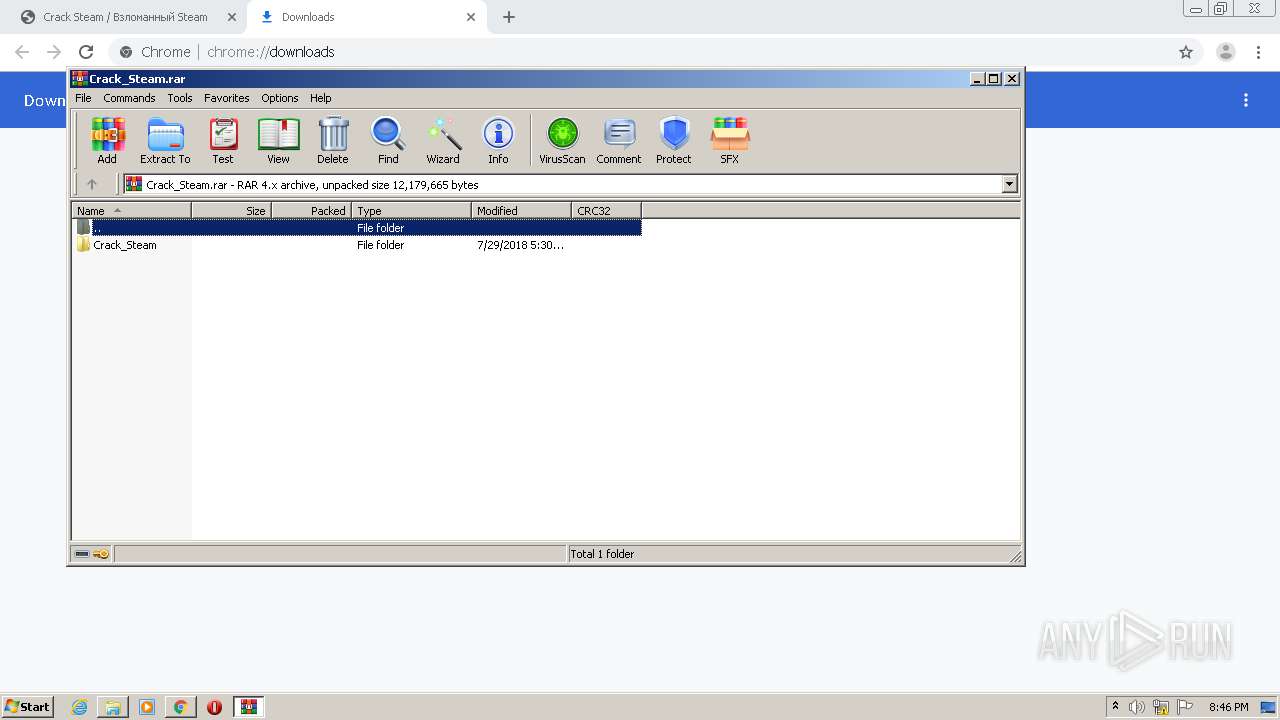
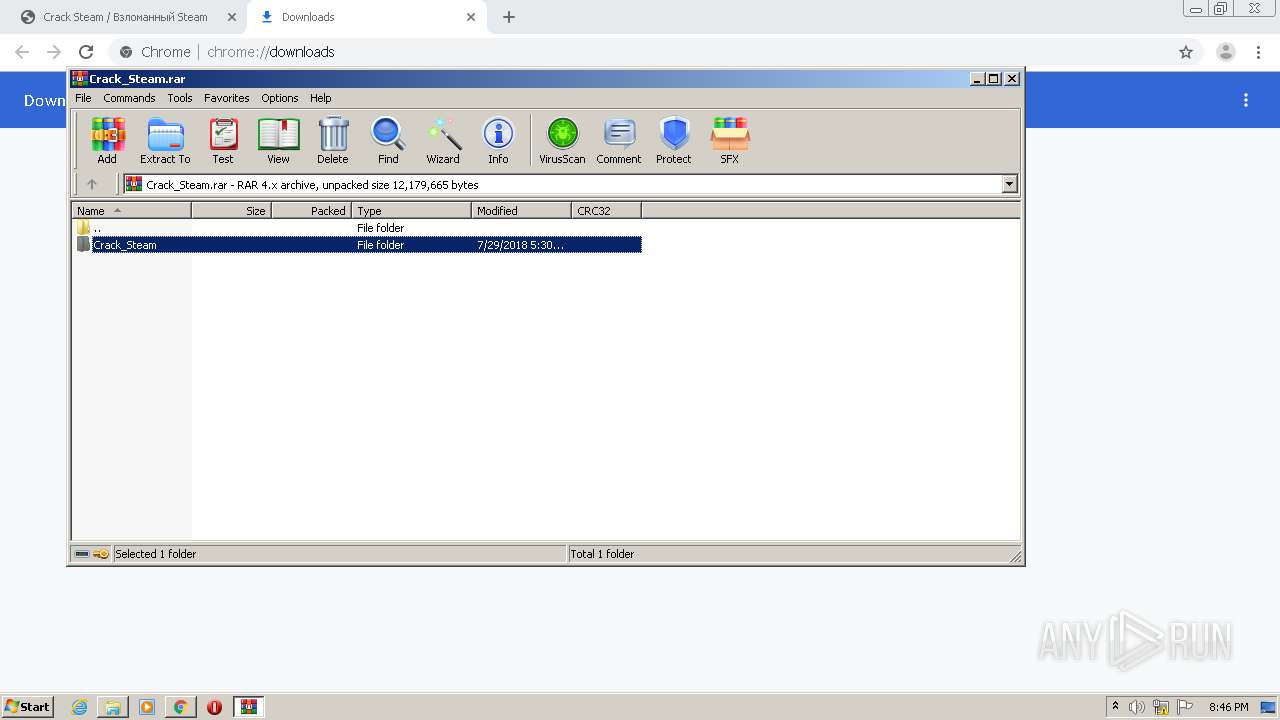
- WinRAR.exe (PID: 1308)
- CSIW_Setup_30_March_2014.exe (PID: 1708)
- CSIW_Setup_30_March_2014.exe (PID: 2992)
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- SteamService.exe (PID: 3012)
- Cracked Steam.exe (PID: 3452)
- Cracked Steam.tmp (PID: 532)
Drops a file that was compiled in debug mode
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- SteamService.exe (PID: 3012)
- Cracked Steam.tmp (PID: 532)
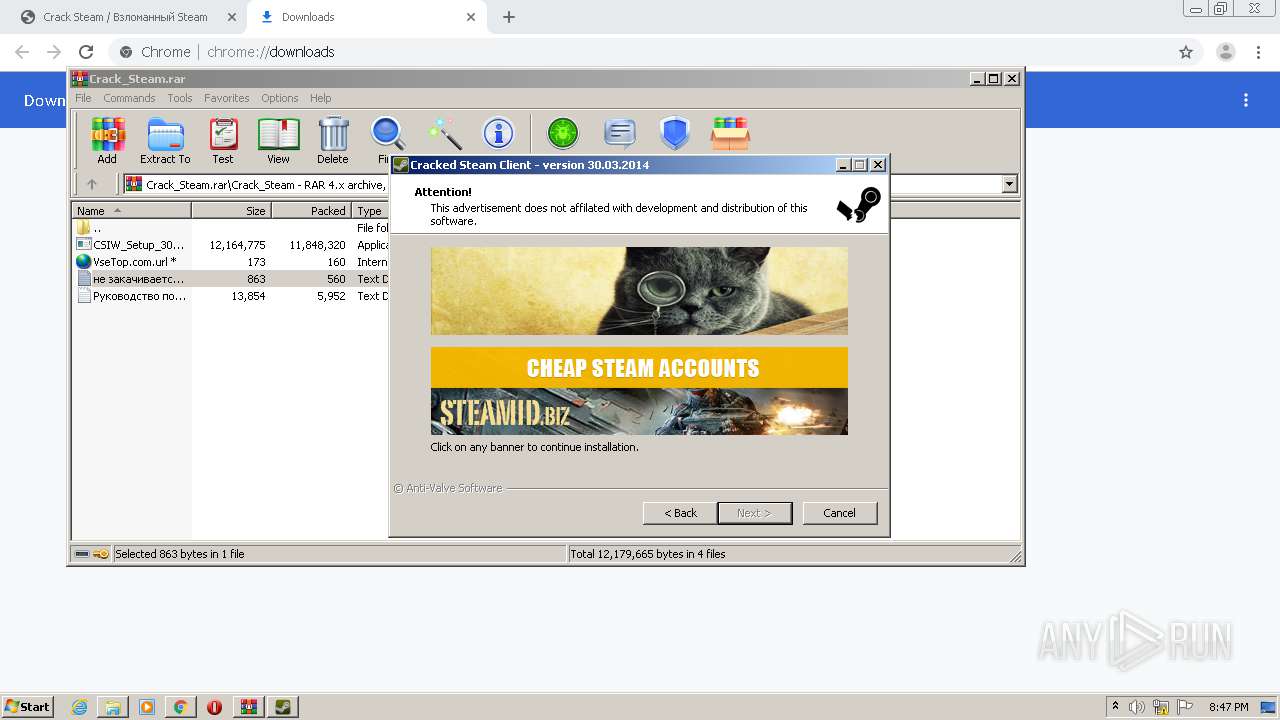
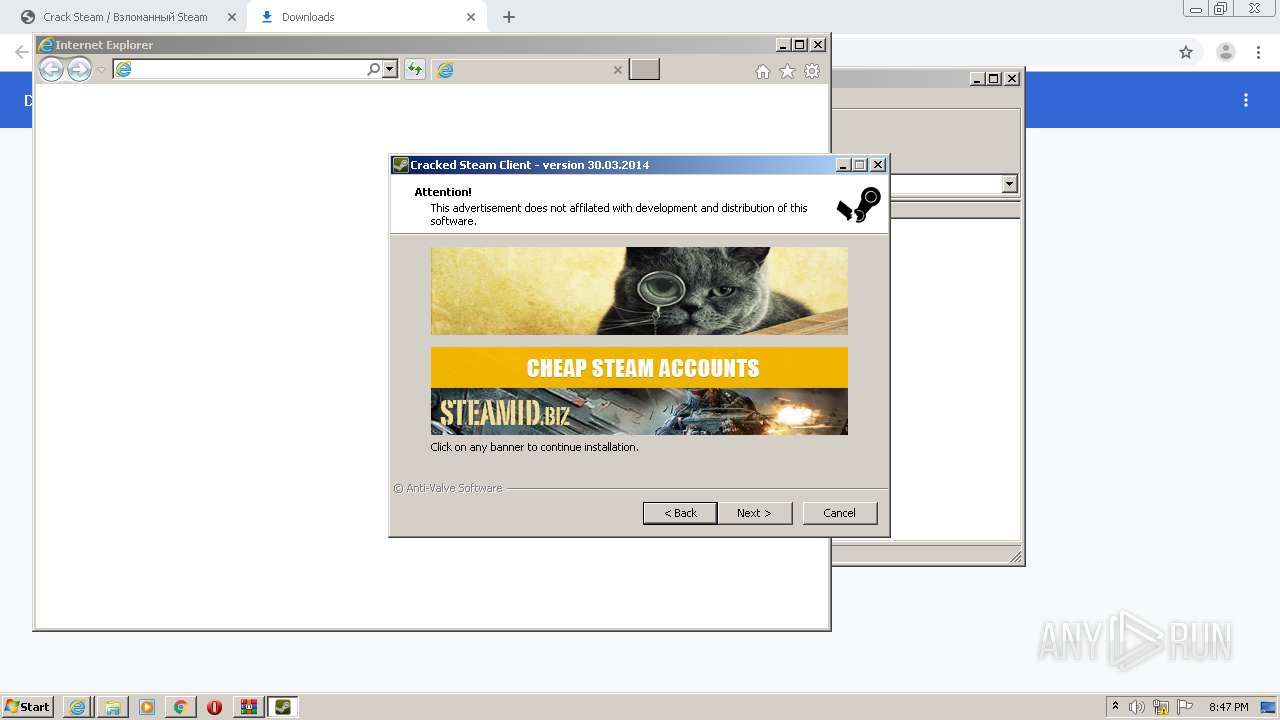
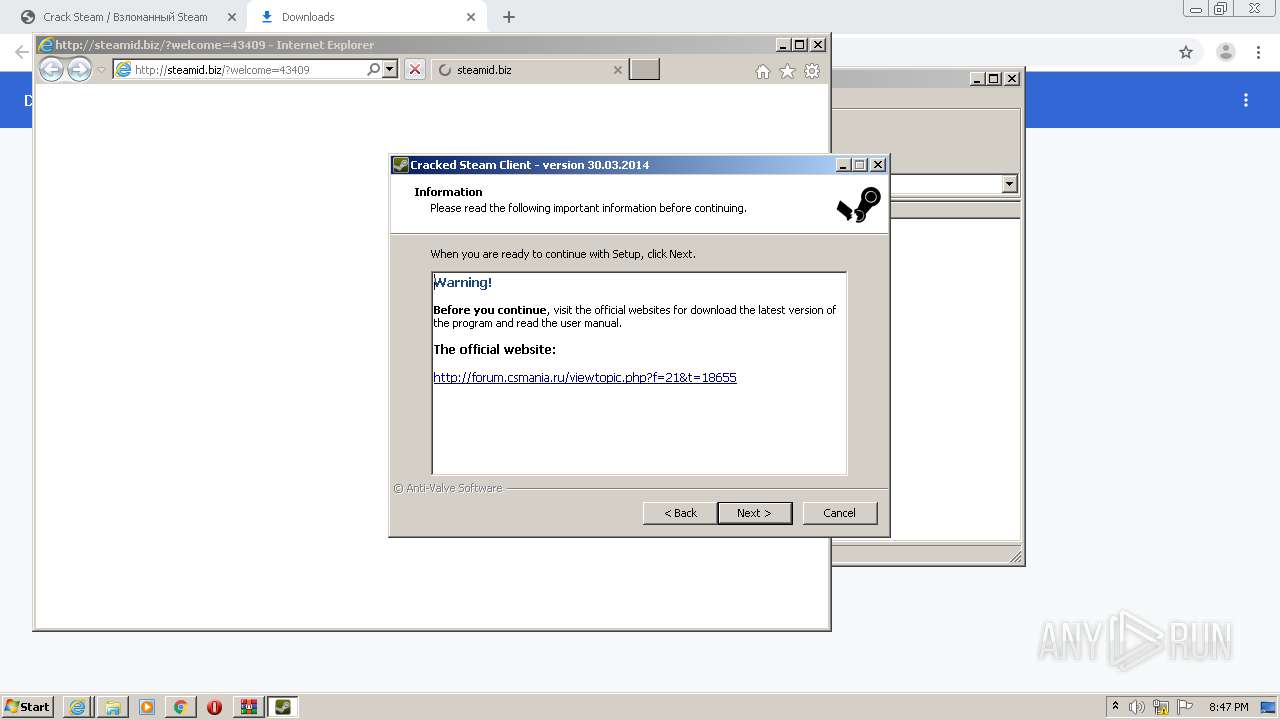
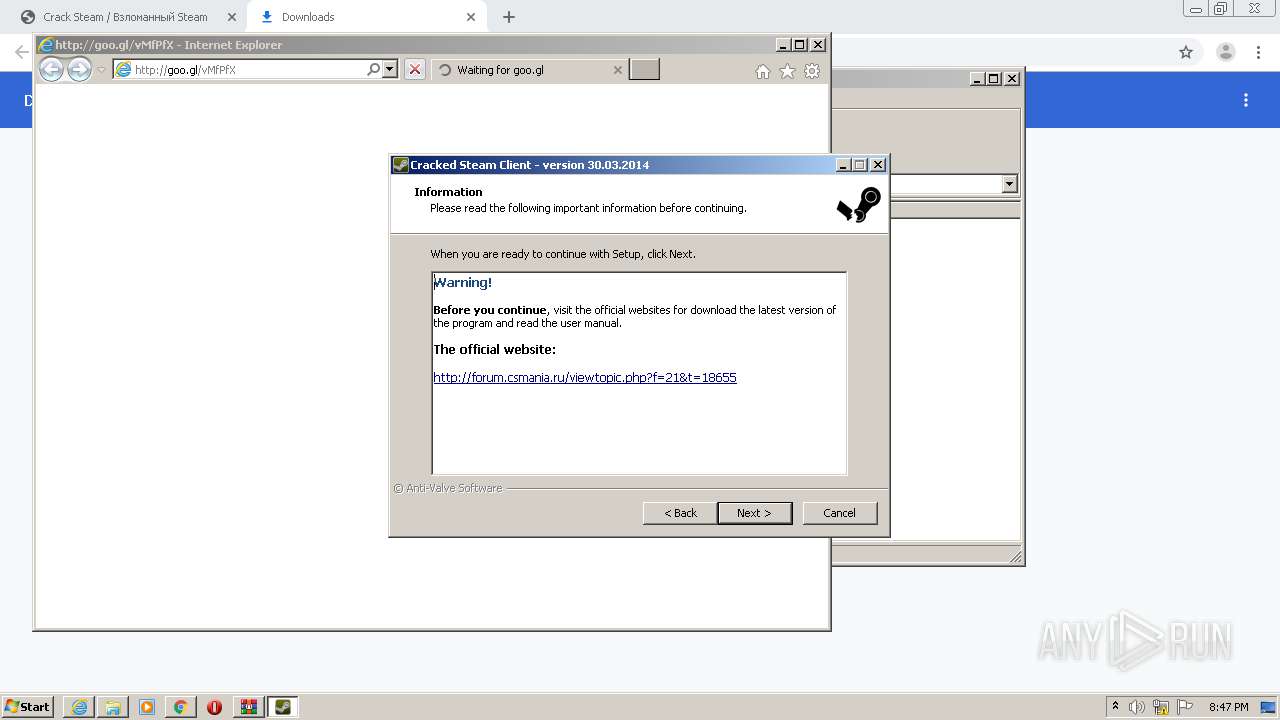
Starts Internet Explorer
- CSIW_Setup_30_March_2014.tmp (PID: 4064)
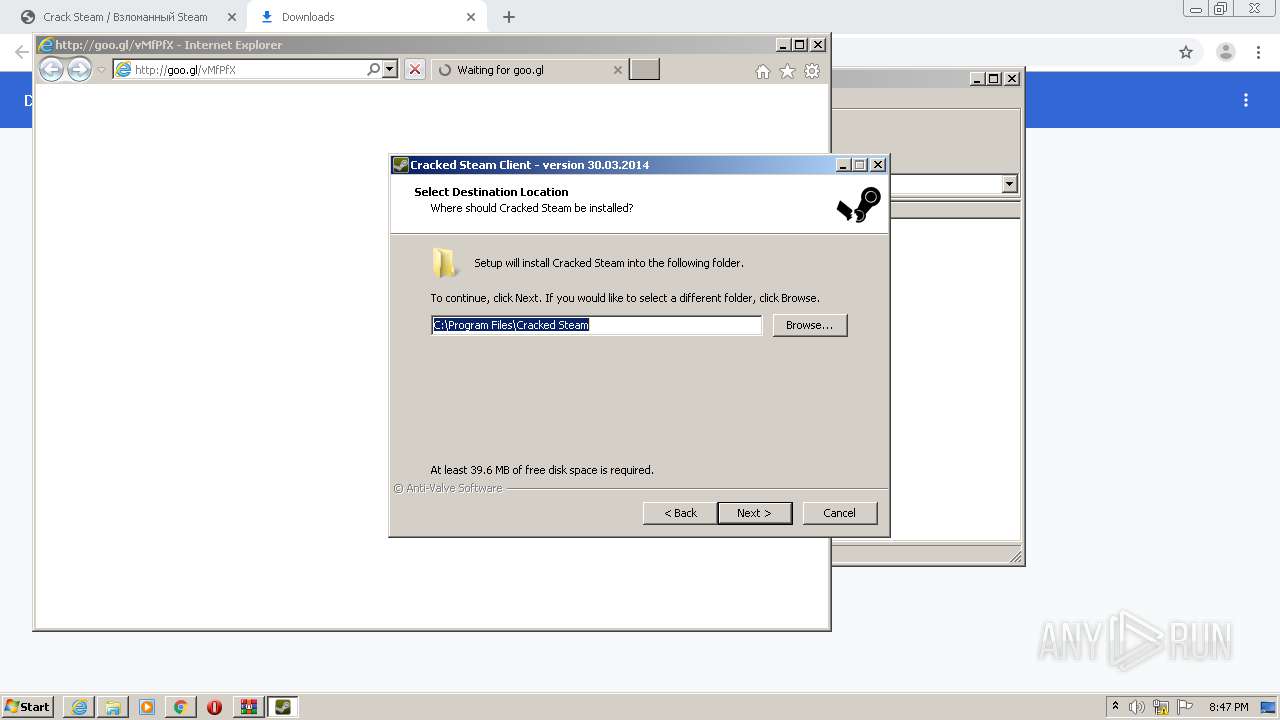
Creates a directory in Program Files
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Steam.exe (PID: 2092)
Changes default file association
- SteamService.exe (PID: 3012)
Creates files in the program directory
- SteamService.exe (PID: 3012)
- Steam.exe (PID: 2092)
- Steam.exe (PID: 2668)
INFO
Reads the hosts file
- chrome.exe (PID: 4040)
- chrome.exe (PID: 1584)
Application launched itself
- chrome.exe (PID: 1584)
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 3056)
Application was dropped or rewritten from another process
- CSIW_Setup_30_March_2014.tmp (PID: 4064)
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Cracked Steam.tmp (PID: 532)
Loads dropped or rewritten executable
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Cracked Steam.tmp (PID: 532)
Changes internet zones settings
- iexplore.exe (PID: 3056)
- iexplore.exe (PID: 3184)
Creates files in the user directory
- iexplore.exe (PID: 2836)
- iexplore.exe (PID: 2140)
- iexplore.exe (PID: 3184)
Reads internet explorer settings
- iexplore.exe (PID: 2836)
- iexplore.exe (PID: 2140)
Creates files in the program directory
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
- Cracked Steam.tmp (PID: 532)
Creates a software uninstall entry
- CSIW_Setup_30_March_2014.tmp (PID: 2216)
Reads settings of System Certificates
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 3056)
Changes settings of System certificates
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 3056)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3184)
- iexplore.exe (PID: 3056)
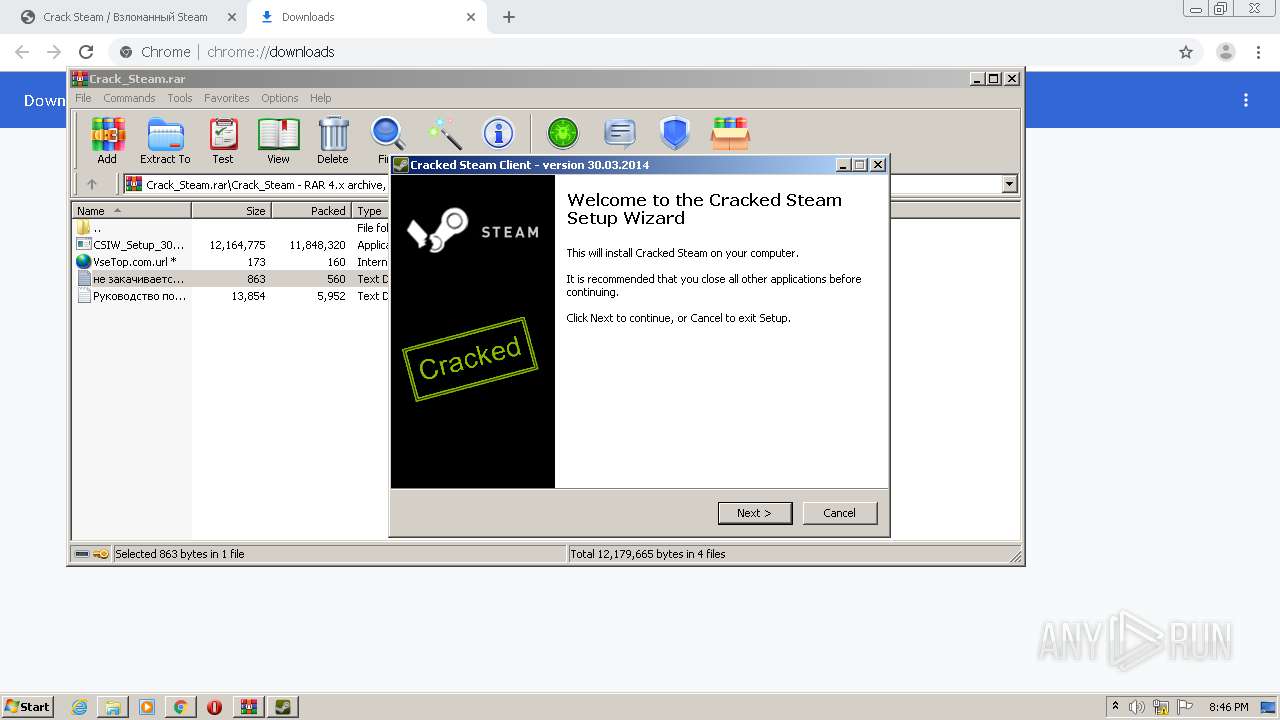
Manual execution by user
- Cracked Steam.exe (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
30
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14006674010220145598,7217134758164823608,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3024265176455468508 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\is-U6USJ.tmp\Cracked Steam.tmp" /SL5="$40272,424795,422400,C:\Program Files\Cracked Steam\Cracked Steam.exe" | C:\Users\admin\AppData\Local\Temp\is-U6USJ.tmp\Cracked Steam.tmp | Cracked Steam.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 1 Version: 51.52.0.0 Modules
| |||||||||||||||
| 788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1096 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
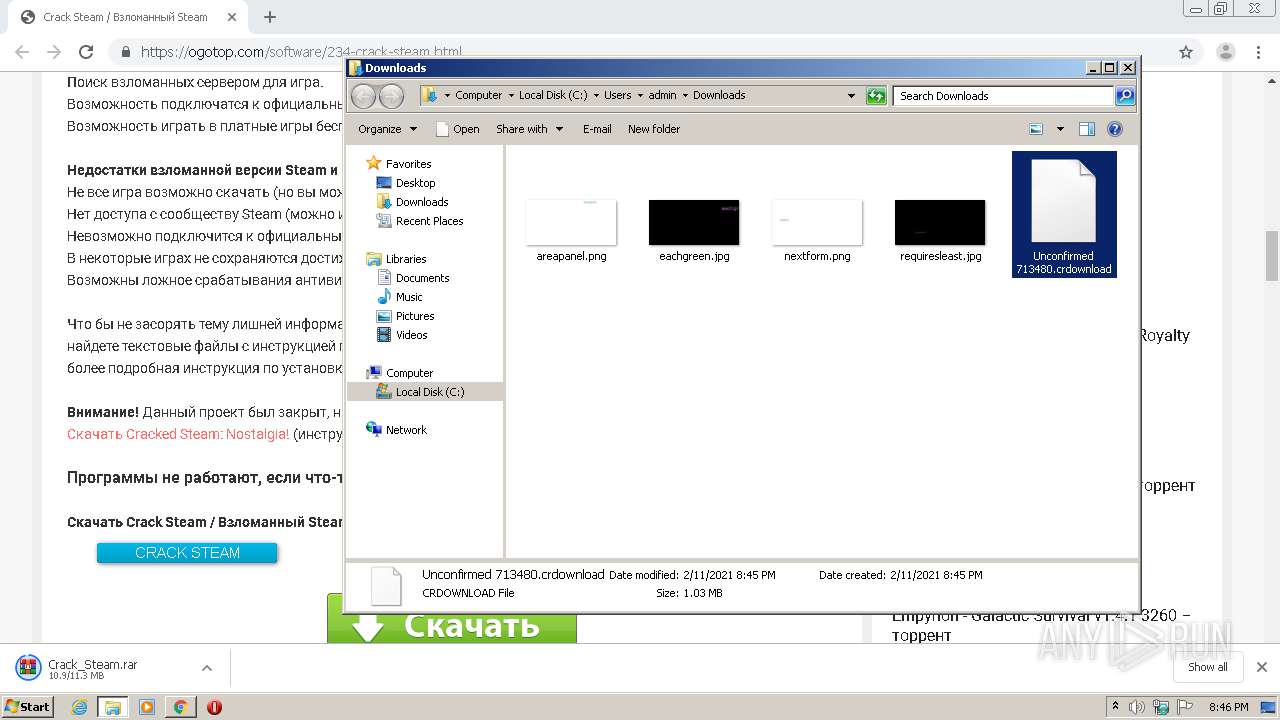
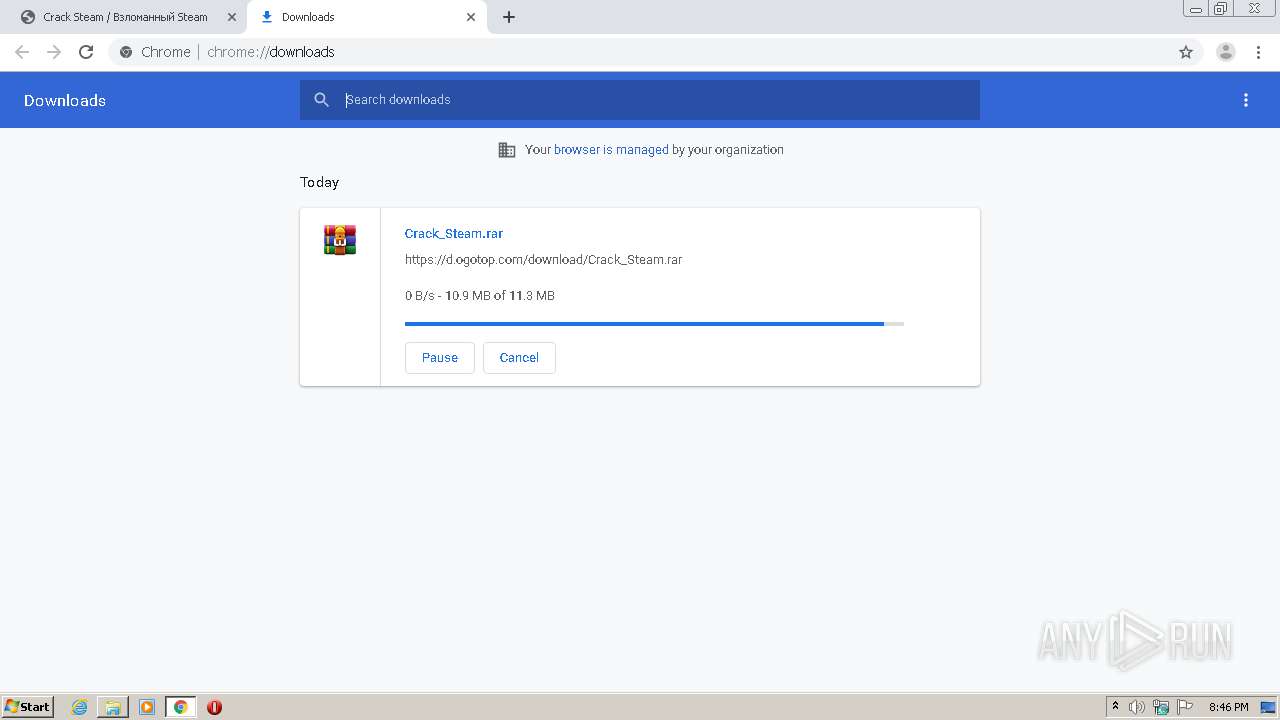
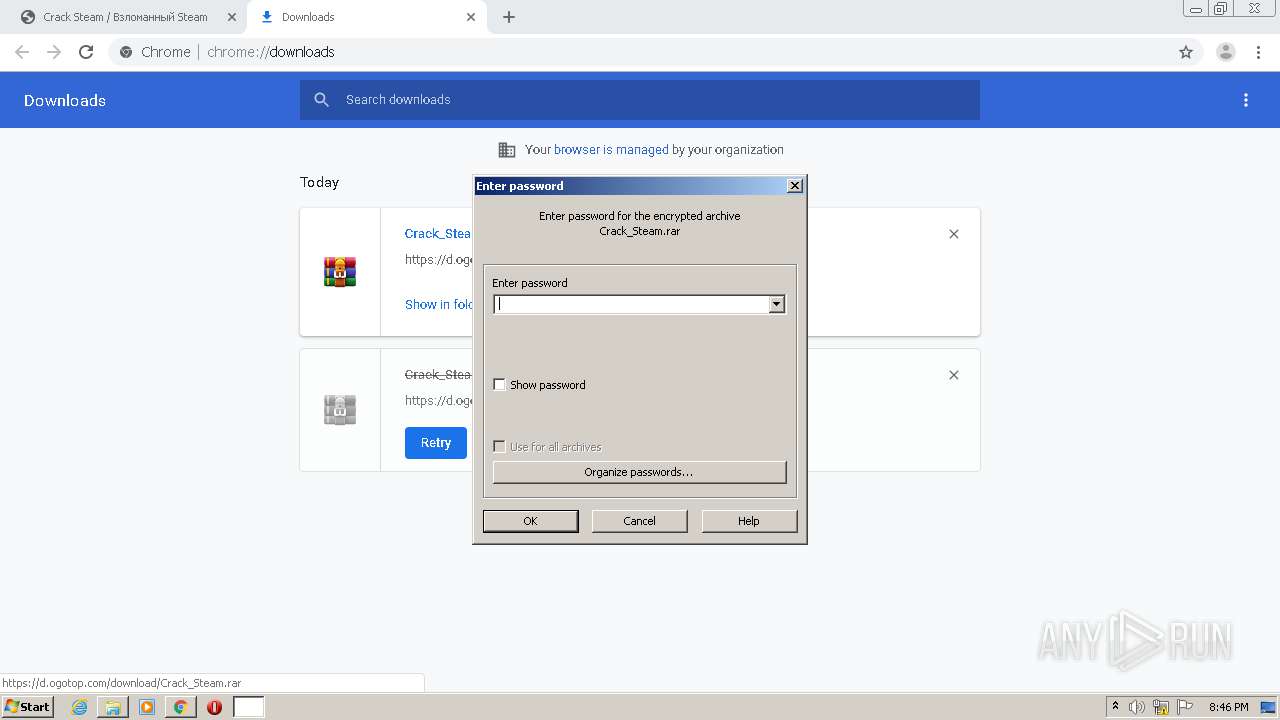
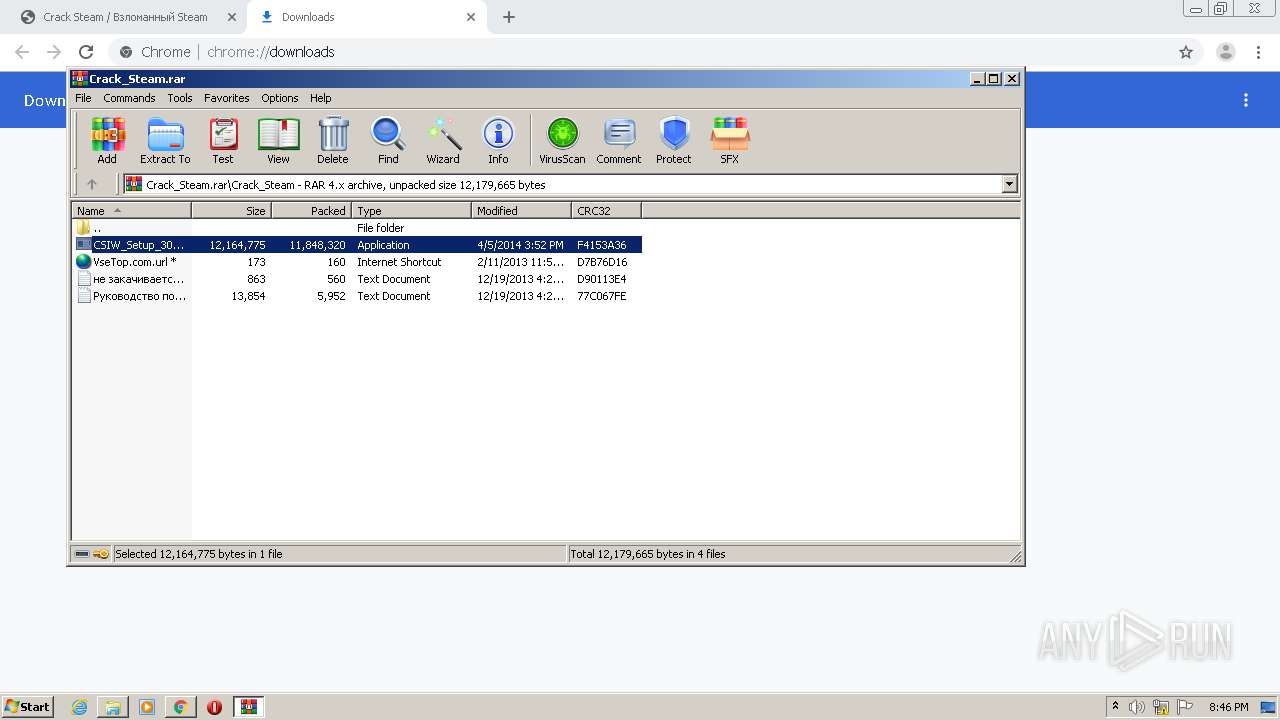
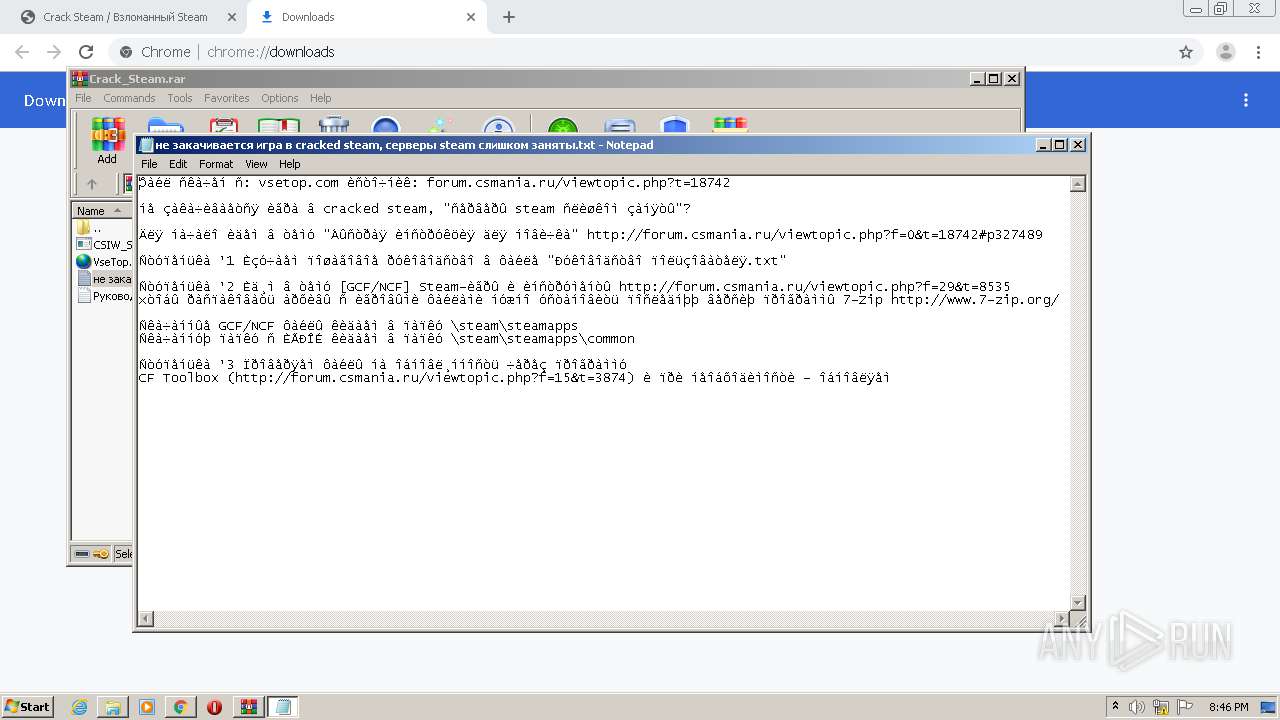
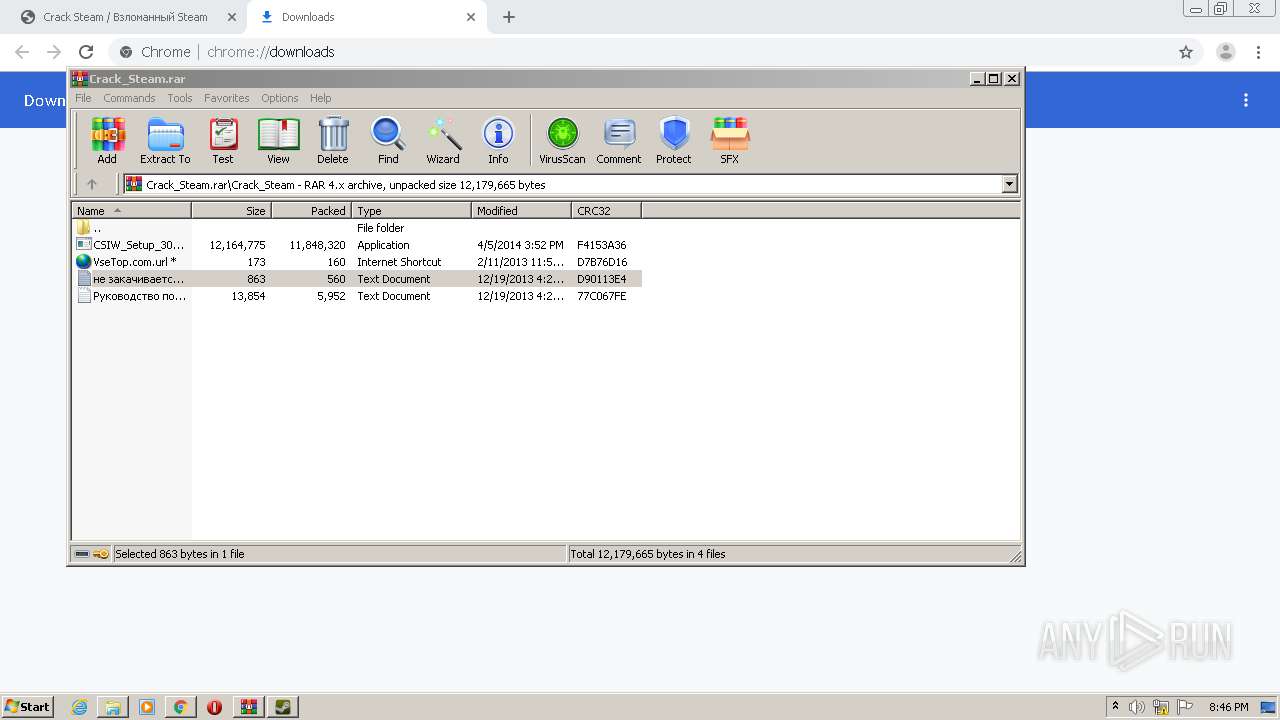
| 1308 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\Crack_Steam.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,14006674010220145598,7217134758164823608,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5998569697862339220 --mojo-platform-channel-handle=2788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://ogotop.com/software/234-crack-steam.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,14006674010220145598,7217134758164823608,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14324355070672097189 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb1308.24128\Crack_Steam\CSIW_Setup_30_March_2014.exe" /SPAWNWND=$30210 /NOTIFYWND=$501AA | C:\Users\admin\AppData\Local\Temp\Rar$EXb1308.24128\Crack_Steam\CSIW_Setup_30_March_2014.exe | CSIW_Setup_30_March_2014.tmp | ||||||||||||
User: admin Company: Anti-Valve Software Integrity Level: HIGH Description: Cracked Steam Setup Exit code: 0 Version: 30.03.2014 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,14006674010220145598,7217134758164823608,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13261349800254352600 --mojo-platform-channel-handle=3564 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Cracked Steam\Steam.exe" | C:\Program Files\Cracked Steam\Steam.exe | CSIW_Setup_30_March_2014.tmp | ||||||||||||
User: admin Company: Valve Corporation Integrity Level: MEDIUM Description: Steam Client Bootstrapper Exit code: 0 Version: 02.14.07.36 Modules
| |||||||||||||||
Total events
3 081
Read events
2 801
Write events
259
Delete events
21
Modification events
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (788) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1584-13257549940106625 |
Value: 259 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1584) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
25
Suspicious files
58
Text files
127
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60259775-630.pma | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\eacf3b2e-c852-4495-8d62-6d10f6c902c1.tmp | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF14462f.TMP | text | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF14462f.TMP | text | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1584 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF14492d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
74
DNS requests
32
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2140 | iexplore.exe | GET | 301 | 172.217.18.110:80 | http://goo.gl/vMfPfX | US | — | — | shared |
2140 | iexplore.exe | GET | 301 | 172.67.211.106:80 | http://forum.csmania.ru/viewtopic.php?p=837227&f=1 | US | — | — | suspicious |
2092 | Steam.exe | GET | 302 | 205.196.6.229:80 | http://client-download.steampowered.com/client/steam_client_win32 | US | — | — | whitelisted |
3316 | wget.exe | GET | — | 104.21.85.215:80 | http://forum.csmania.ru/update.inf | US | — | — | suspicious |
2140 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDE6pjqfl4fQwIAAAAAhwGC | US | der | 472 b | whitelisted |
2836 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.steamid.biz/ | US | html | 3.99 Kb | malicious |
2140 | iexplore.exe | GET | 200 | 23.32.238.18:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
2836 | iexplore.exe | GET | 200 | 199.59.242.153:80 | http://ww1.steamid.biz/glp?r=&u=http%3A%2F%2Fww1.steamid.biz%2F&rw=1280&rh=720&ww=792&wh=544 | US | text | 9.79 Kb | malicious |
3056 | iexplore.exe | GET | 404 | 199.59.242.153:80 | http://ww1.steamid.biz/favicon.ico | US | html | 3.99 Kb | malicious |
2092 | Steam.exe | GET | 200 | 2.16.186.90:80 | http://media4.steampowered.com/client/steam_client_win32?1612810276 | unknown | text | 4.40 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | chrome.exe | 142.250.185.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
4040 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
4040 | chrome.exe | 185.43.220.60:443 | ogotop.com | WIBO Baltic UAB | LT | unknown |
4040 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4040 | chrome.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2836 | iexplore.exe | 199.115.115.102:80 | steamid.biz | Leaseweb USA, Inc. | US | malicious |
2140 | iexplore.exe | 172.217.18.110:80 | goo.gl | Google Inc. | US | whitelisted |
2140 | iexplore.exe | 172.217.18.110:443 | goo.gl | Google Inc. | US | whitelisted |
2140 | iexplore.exe | 142.250.185.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2836 | iexplore.exe | 199.59.242.153:80 | ww1.steamid.biz | Bodis, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ogotop.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
yastatic.net |
| whitelisted |
counter.yadro.ru |
| whitelisted |
mc.yandex.ru |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
d.ogotop.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2836 | iexplore.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |
2092 | Steam.exe | Potential Corporate Privacy Violation | ET USER_AGENTS Steam HTTP Client User-Agent |
3316 | wget.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2092 | Steam.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2092 | Steam.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |