| File name: | vmpsoft.vmp.com |
| Full analysis: | https://app.any.run/tasks/ed7e0049-b21f-40e1-aed8-9248b42e0fd7 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 15:52:12 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B29695130DCAF6B051536B867D0690F2 |
| SHA1: | 1BB320C27322D42629E0CFC447AEAAF76AE4ECC7 |
| SHA256: | B96E337D6EAE6158B7F3F04DF84DEBA4DAE1A603CAA69D9ED161F8185724FFF8 |
| SSDEEP: | 24576:5JeyvwIantC7AU+5jH5TTvTbQZXqVko+f:XeyvwIantC75+BHdTvTbQRq |
MALICIOUS
Drops the executable file immediately after the start
- vmpsoft.vmp.com.exe (PID: 4152)
Create files in the Startup directory
- vmp.exe (PID: 2008)
Deletes shadow copies
- cmd.exe (PID: 4680)
- cmd.exe (PID: 3104)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 5244)
Steals credentials from Web Browsers
- vmp.exe (PID: 2008)
Modifies files in the Chrome extension folder
- vmp.exe (PID: 2008)
Actions looks like stealing of personal data
- vmp.exe (PID: 2008)
SUSPICIOUS
Reads security settings of Internet Explorer
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Reads the date of Windows installation
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Starts itself from another location
- vmpsoft.vmp.com.exe (PID: 4152)
Found regular expressions for crypto-addresses (YARA)
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Executable content was dropped or overwritten
- vmpsoft.vmp.com.exe (PID: 4152)
Executes as Windows Service
- VSSVC.exe (PID: 4024)
- vds.exe (PID: 4800)
- wbengine.exe (PID: 1320)
Starts CMD.EXE for commands execution
- vmp.exe (PID: 2008)
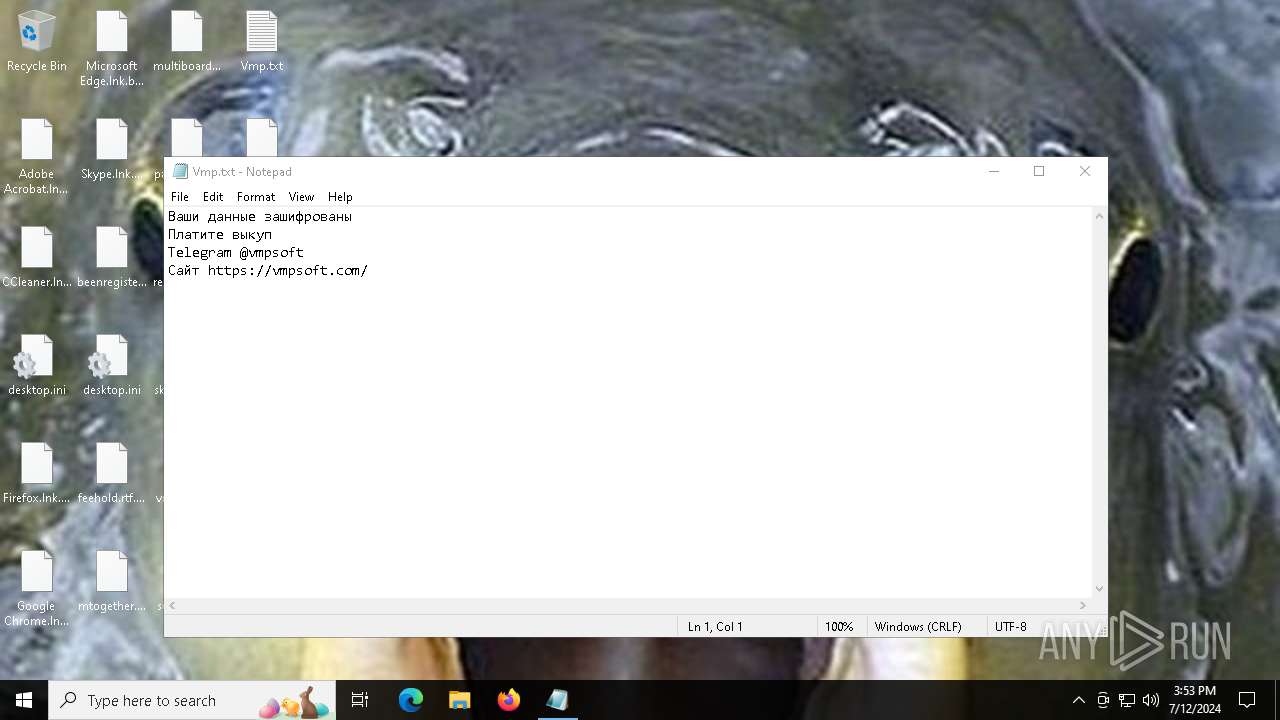
Start notepad (likely ransomware note)
- vmp.exe (PID: 2008)
INFO
Checks supported languages
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Reads the computer name
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Creates files or folders in the user directory
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Process checks computer location settings
- vmpsoft.vmp.com.exe (PID: 4152)
- vmp.exe (PID: 2008)
Reads the machine GUID from the registry
- vmp.exe (PID: 2008)
Reads Microsoft Office registry keys
- vmp.exe (PID: 2008)
Create files in a temporary directory
- vmp.exe (PID: 2008)
Creates files in the program directory
- vmp.exe (PID: 2008)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5140)
- WMIC.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:12 15:17:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 248832 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x449b9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | vmpsoft.com |
| LegalCopyright: | |
| OriginalFileName: | vmpsoft.com |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
141
Monitored processes
18
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | wbadmin delete catalog -quiet | C:\Windows\System32\wbadmin.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® BLB Backup Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1320 | "C:\WINDOWS\system32\wbengine.exe" | C:\Windows\System32\wbengine.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Block Level Backup Engine Service EXE Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1960 | C:\WINDOWS\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | "C:\Users\admin\AppData\Roaming\vmp.exe" | C:\Users\admin\AppData\Roaming\vmp.exe | vmpsoft.vmp.com.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 2404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2588 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2784 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3104 | "C:\Windows\System32\cmd.exe" /C wbadmin delete catalog -quiet | C:\Windows\System32\cmd.exe | — | vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3624 | wmic shadowcopy delete | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3868 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 102
Read events
12 024
Write events
58
Delete events
20
Modification events
| (PID) Process: | (4152) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4152) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4152) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4152) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2008) vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2008) vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2008) vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2008) vmp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2784) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2784) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Description |
| Operation: | write | Name: | FirmwareModified |
Value: 1 | |||
Executable files
1
Suspicious files
554
Text files
867
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2008 | vmp.exe | C:\$WinREAgent\Rollback.xml.kwo5 | binary | |
MD5:DFBB23D8EB1A18CDA0FAD75367429C10 | SHA256:D9B647C5ACB07E8E5D0B9AD253AF0A0D77E8213D2A20239C9B2E330B31002E37 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Backup\location.txt.lk39 | binary | |
MD5:DDC71E1E73EDAE83D457468B92217BA5 | SHA256:A0AAB60249986BC44B1756C35CE9E2730B8C73C5172ADBC949320DC264761707 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Backup\ReAgent.xml | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
| 4152 | vmpsoft.vmp.com.exe | C:\Users\admin\AppData\Roaming\vmp.exe | executable | |
MD5:B29695130DCAF6B051536B867D0690F2 | SHA256:B96E337D6EAE6158B7F3F04DF84DEBA4DAE1A603CAA69D9ED161F8185724FFF8 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Backup\ReAgent.xml.nrwb | binary | |
MD5:C7A787285D016D24A3BE2790D2A08B7E | SHA256:71D6C8966471075855D097CDF0034554C49358F9B19D36602012F392CD68FC65 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Rollback.xml | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 2008 | vmp.exe | C:\$WinREAgent\RollbackInfo.ini.u9aa | binary | |
MD5:67912C48F63DD9490025C2F613F09C87 | SHA256:B8DD148C9D405610E7628D383DA61E418BEAFC8D9463FB13903414034D944B92 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Backup\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 2008 | vmp.exe | C:\$WinREAgent\Backup\location.txt | binary | |
MD5:D1457B72C3FB323A2671125AEF3EAB5D | SHA256:8A8DE823D5ED3E12746A62EF169BCF372BE0CA44F0A1236ABC35DF05D96928E1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
32
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4392 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | GET | — | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1832 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1832 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
368 | RUXIMICS.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 92.123.104.31:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=re&setlang=en-US&cc=US&nohs=1&qfm=1&cp=2&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=886f7dfaf8a943d7ac515843550c84b9 | unknown | binary | 5.05 Kb | unknown |
— | — | GET | 200 | 92.123.104.37:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=rege&setlang=en-US&cc=US&nohs=1&qfm=1&cp=4&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=9e5ca3b8609c45288674b78f53cdefa2 | unknown | binary | 4.99 Kb | unknown |
— | — | GET | 200 | 92.123.104.24:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=reg&setlang=en-US&cc=US&nohs=1&qfm=1&cp=3&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=65838b980f4f409493f636a698a90235 | unknown | binary | 5.08 Kb | unknown |
— | — | GET | 200 | 92.123.104.37:443 | https://www.bing.com/AS/API/WindowsCortanaPane/V2/Suggestions?qry=r&setlang=en-US&cc=US&nohs=1&qfm=1&cp=1&cvid=917f2af1fe65416cbd620a4b992edbf0&ig=8217ecd434a24e319c68e41132cd851d | unknown | binary | 15.4 Kb | unknown |
— | — | POST | 204 | 92.123.104.30:443 | https://www.bing.com/threshold/xls.aspx | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1832 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
368 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4392 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4392 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1832 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4392 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
368 | RUXIMICS.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
wbadmin.exe | Invalid parameter passed to C runtime function.
|