| File name: | vmpsoft.vmp.com |
| Full analysis: | https://app.any.run/tasks/eb62cd2e-c6fb-4b9f-84f8-8fad9e00e817 |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2024, 15:46:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B29695130DCAF6B051536B867D0690F2 |
| SHA1: | 1BB320C27322D42629E0CFC447AEAAF76AE4ECC7 |
| SHA256: | B96E337D6EAE6158B7F3F04DF84DEBA4DAE1A603CAA69D9ED161F8185724FFF8 |
| SSDEEP: | 24576:5JeyvwIantC7AU+5jH5TTvTbQZXqVko+f:XeyvwIantC75+BHdTvTbQRq |
MALICIOUS
Drops the executable file immediately after the start
- vmpsoft.vmp.com.exe (PID: 3520)
Create files in the Startup directory
- vmp.exe (PID: 540)
Deletes shadow copies
- cmd.exe (PID: 3096)
- cmd.exe (PID: 2540)
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 2504)
Steals credentials from Web Browsers
- vmp.exe (PID: 540)
Modifies files in the Chrome extension folder
- vmp.exe (PID: 540)
Actions looks like stealing of personal data
- vmp.exe (PID: 540)
SUSPICIOUS
Reads security settings of Internet Explorer
- vmpsoft.vmp.com.exe (PID: 3520)
- vmp.exe (PID: 540)
Executable content was dropped or overwritten
- vmpsoft.vmp.com.exe (PID: 3520)
Reads the Internet Settings
- vmpsoft.vmp.com.exe (PID: 3520)
- vmp.exe (PID: 540)
- WMIC.exe (PID: 3068)
Starts itself from another location
- vmpsoft.vmp.com.exe (PID: 3520)
Executes as Windows Service
- VSSVC.exe (PID: 2580)
- wbengine.exe (PID: 4016)
- vds.exe (PID: 1620)
Starts CMD.EXE for commands execution
- vmp.exe (PID: 540)
Found regular expressions for crypto-addresses (YARA)
- vmp.exe (PID: 540)
Start notepad (likely ransomware note)
- vmp.exe (PID: 540)
INFO
Reads the computer name
- vmpsoft.vmp.com.exe (PID: 3520)
- vmp.exe (PID: 540)
Creates files or folders in the user directory
- vmpsoft.vmp.com.exe (PID: 3520)
- vmp.exe (PID: 540)
Checks supported languages
- vmpsoft.vmp.com.exe (PID: 3520)
- vmp.exe (PID: 540)
Create files in a temporary directory
- vmp.exe (PID: 540)
Reads the machine GUID from the registry
- vmp.exe (PID: 540)
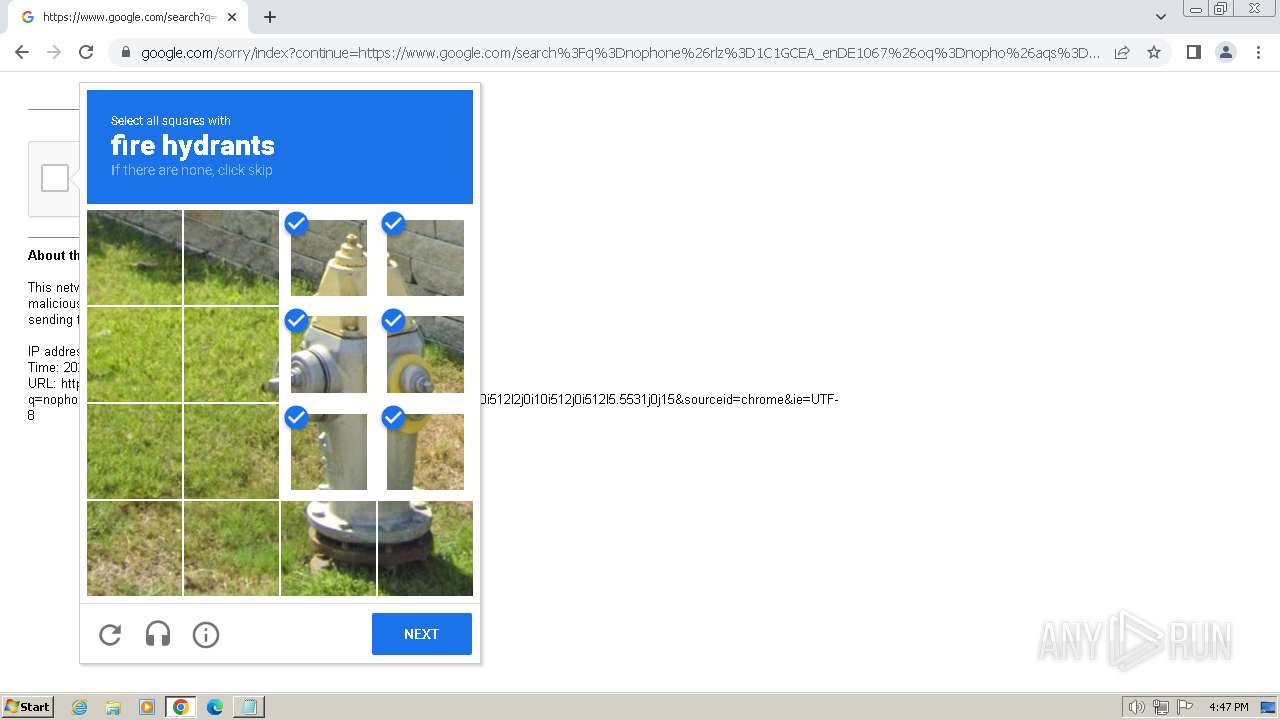
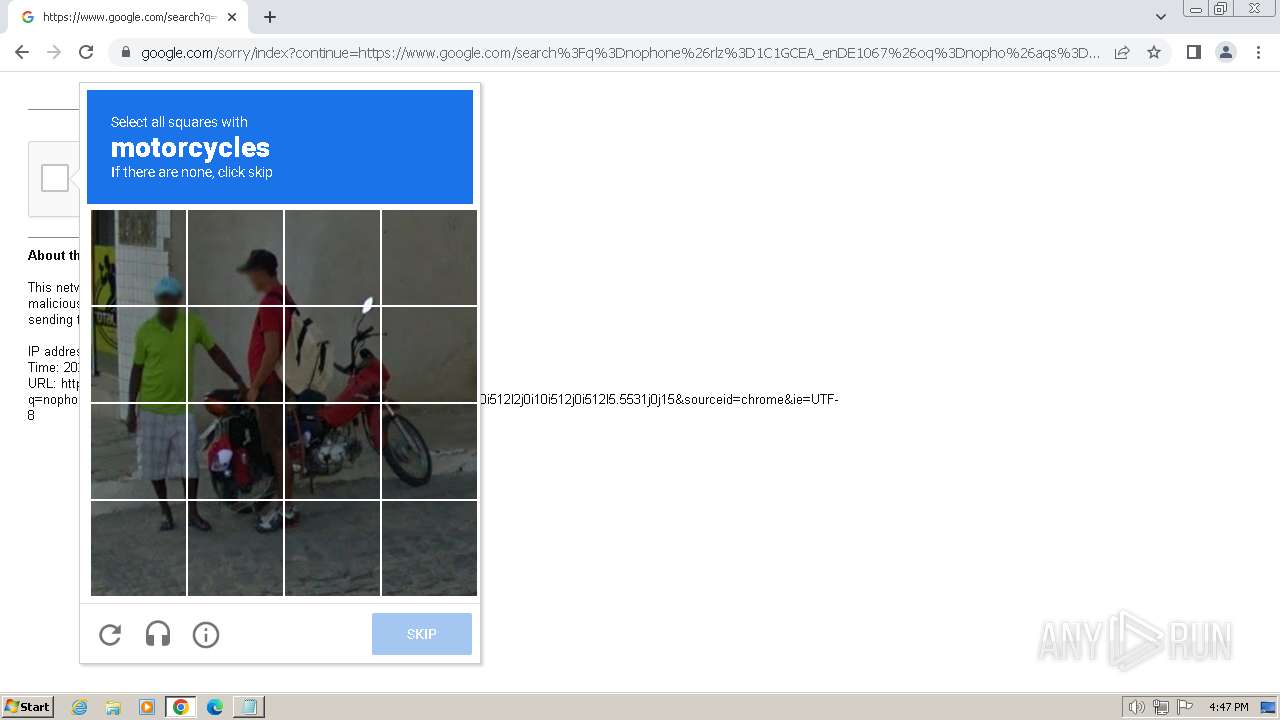
Manual execution by a user
- chrome.exe (PID: 3140)
Application launched itself
- chrome.exe (PID: 3140)
Creates files in the program directory
- vmp.exe (PID: 540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:12 15:17:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 248832 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x449b9 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | vmpsoft.com |
| LegalCopyright: | |
| OriginalFileName: | vmpsoft.com |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
73
Monitored processes
29
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | bcdedit /set {default} recoveryenabled no | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 524 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 540 | "C:\Users\admin\AppData\Roaming\vmp.exe" | C:\Users\admin\AppData\Roaming\vmp.exe | vmpsoft.vmp.com.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 0.0.0.0 Modules
| |||||||||||||||
| 568 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | vssadmin delete shadows /all /quiet | C:\Windows\System32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1620 | C:\Windows\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6a378b38,0x6a378b48,0x6a378b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2504 | "C:\Windows\System32\cmd.exe" /C bcdedit /set {default} bootstatuspolicy ignoreallfailures & bcdedit /set {default} recoveryenabled no | C:\Windows\System32\cmd.exe | — | vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2540 | "C:\Windows\System32\cmd.exe" /C wbadmin delete catalog -quiet | C:\Windows\System32\cmd.exe | — | vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2580 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 690
Read events
12 624
Write events
66
Delete events
0
Modification events
| (PID) Process: | (3520) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3520) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3520) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3520) vmpsoft.vmp.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (540) vmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (540) vmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (540) vmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (540) vmp.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (524) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\250000e0 |
| Operation: | write | Name: | Element |
Value: 0100000000000000 | |||
| (PID) Process: | (312) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{345b46fd-a9f9-11e7-a83c-e8a4f72b1d33}\Elements\16000009 |
| Operation: | write | Name: | Element |
Value: 00 | |||
Executable files
1
Suspicious files
707
Text files
477
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3520 | vmpsoft.vmp.com.exe | C:\Users\admin\AppData\Roaming\vmp.exe | executable | |
MD5:B29695130DCAF6B051536B867D0690F2 | SHA256:B96E337D6EAE6158B7F3F04DF84DEBA4DAE1A603CAA69D9ED161F8185724FFF8 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\vmp.url | url | |
MD5:80FC21F18443E8A2FC92CDD50D3C9E8A | SHA256:8875038BEA7A3677C88CBE6AE55EDC7618B079D6B7462E64E9F7A57DC903B83B | |||
| 540 | vmp.exe | C:\Users\admin\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\Adobe\A0A2C719-B8B1-4DC7-B33B-C50E709F20B0\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\SOPHIA\Reader\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\Diagnostics\733862231\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
| 540 | vmp.exe | C:\Users\admin\AppData\Local\CEF\User Data\Crashpad\Vmp.txt | text | |
MD5:FC5DC6BFB17F51182963FE81FFFCF6AA | SHA256:EC18A8D0CD5D92FF64F9D38CAAC4525F69CFDE1926D04B865B5B3161F478BE35 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
31
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1060 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
844 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1372 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |